| File name: | BakkesMod.exe |
| Full analysis: | https://app.any.run/tasks/f629ac8e-e9c1-4148-a3ea-21225fc43c9b |
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2020, 19:51:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D9762F30711EB107399087E52C816636 |
| SHA1: | 9A22C7856802A668C9F9B59F0A3EB21F1AF719E1 |
| SHA256: | F6D70B60C30925D32E2DAE45E010A11B6D4D58E53D7E81FF0708413F679FDAC0 |
| SSDEEP: | 98304:ykxz4aHExM2xHp5Oj6bxt+z2rWyXC9etbPdRALLtpTebbEzho5N5iJsv6tWKFduJ:d8HrbW0VRcp9zhSiJsv6tWKFdu9C6H |
MALICIOUS
Changes the autorun value in the registry
- BakkesMod.exe (PID: 2548)
- CCleaner.exe (PID: 2140)
Loads the Task Scheduler COM API
- CCleaner.exe (PID: 2672)
- CCleaner.exe (PID: 3584)
- CCleaner.exe (PID: 2140)
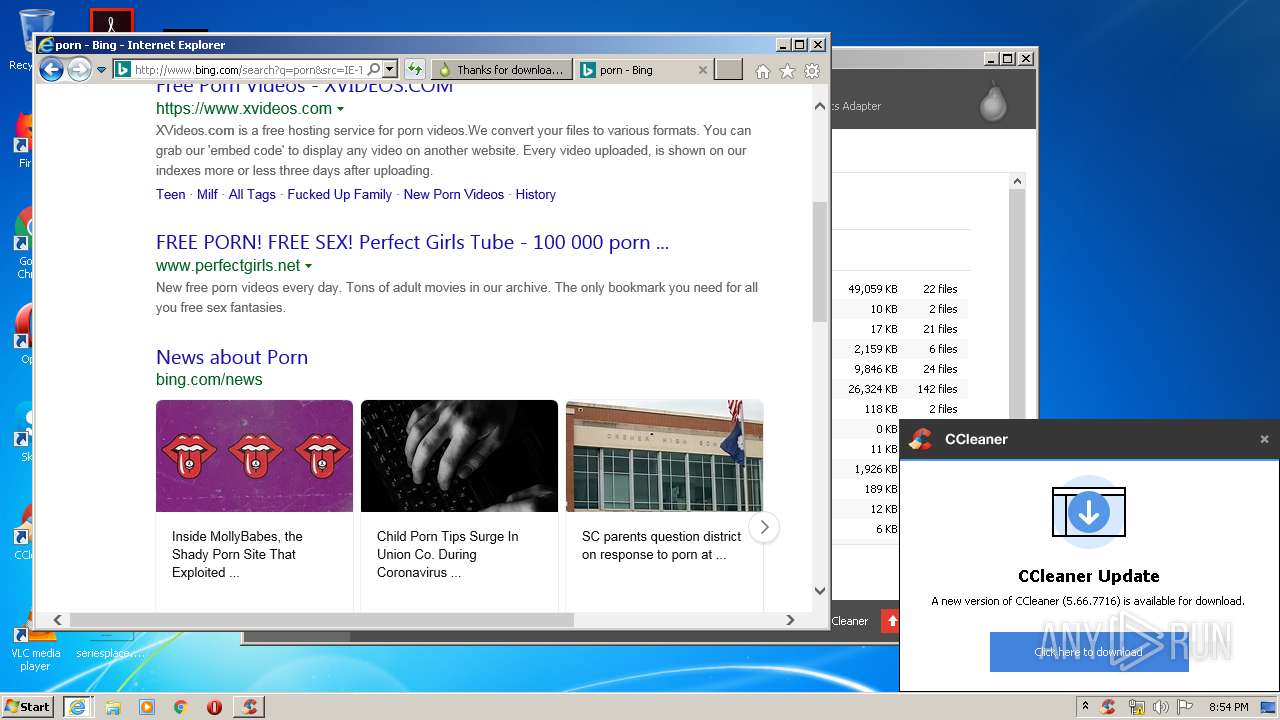
Actions looks like stealing of personal data
- CCleaner.exe (PID: 3584)
- CCleaner.exe (PID: 2140)
Changes settings of System certificates
- CCleaner.exe (PID: 3584)
SUSPICIOUS
Creates files in the program directory
- BakkesMod.exe (PID: 2548)
Executed via COM
- DllHost.exe (PID: 4072)
Executed as Windows Service
- taskhost.exe (PID: 3800)
- taskhost.exe (PID: 1832)
- taskhost.exe (PID: 2124)
- taskhost.exe (PID: 2252)
Executed via Task Scheduler
- CCleaner.exe (PID: 3584)
Reads internet explorer settings
- CCleaner.exe (PID: 3584)
- CCleaner.exe (PID: 2140)
Application launched itself
- CCleaner.exe (PID: 3584)
Reads the cookies of Mozilla Firefox
- CCleaner.exe (PID: 3584)
Creates files in the user directory
- CCleaner.exe (PID: 3584)
Reads the cookies of Google Chrome
- CCleaner.exe (PID: 3584)
Executable content was dropped or overwritten
- BakkesMod.exe (PID: 2548)
Low-level read access rights to disk partition
- CCleaner.exe (PID: 3584)
Reads Internet Cache Settings
- taskhost.exe (PID: 3800)
- CCleaner.exe (PID: 3584)
- taskhost.exe (PID: 2124)
- taskhost.exe (PID: 2252)
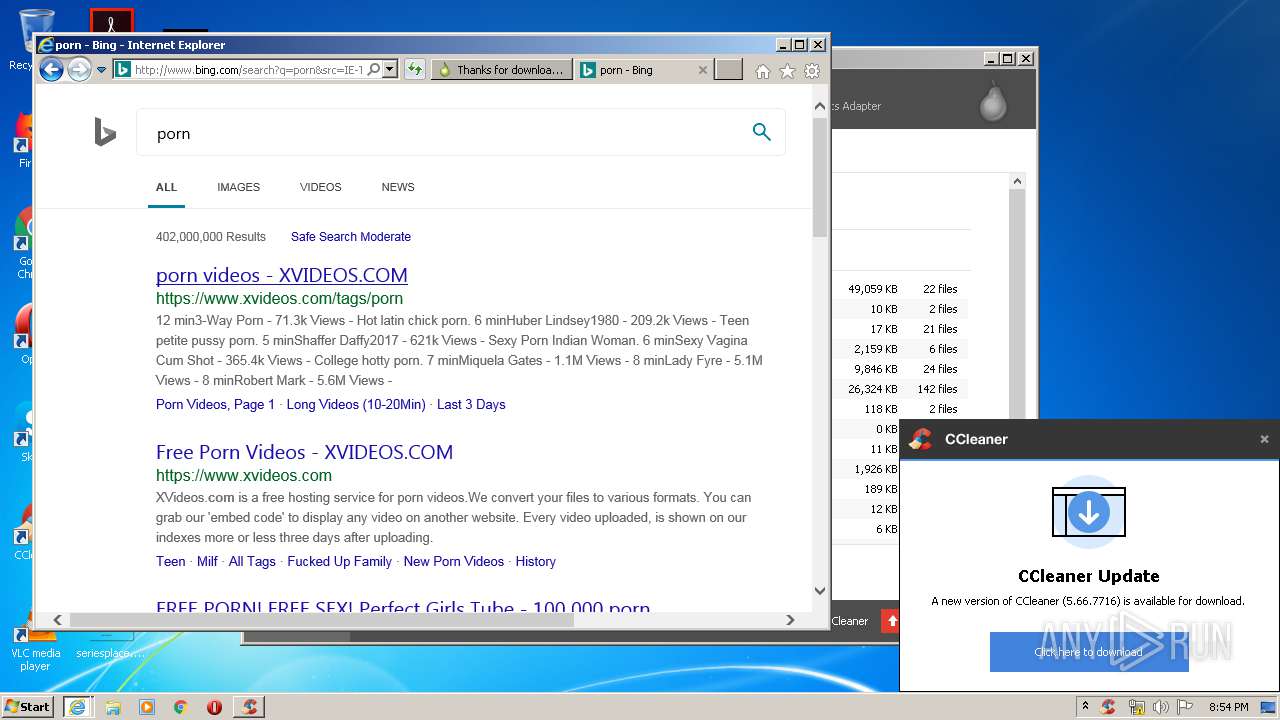
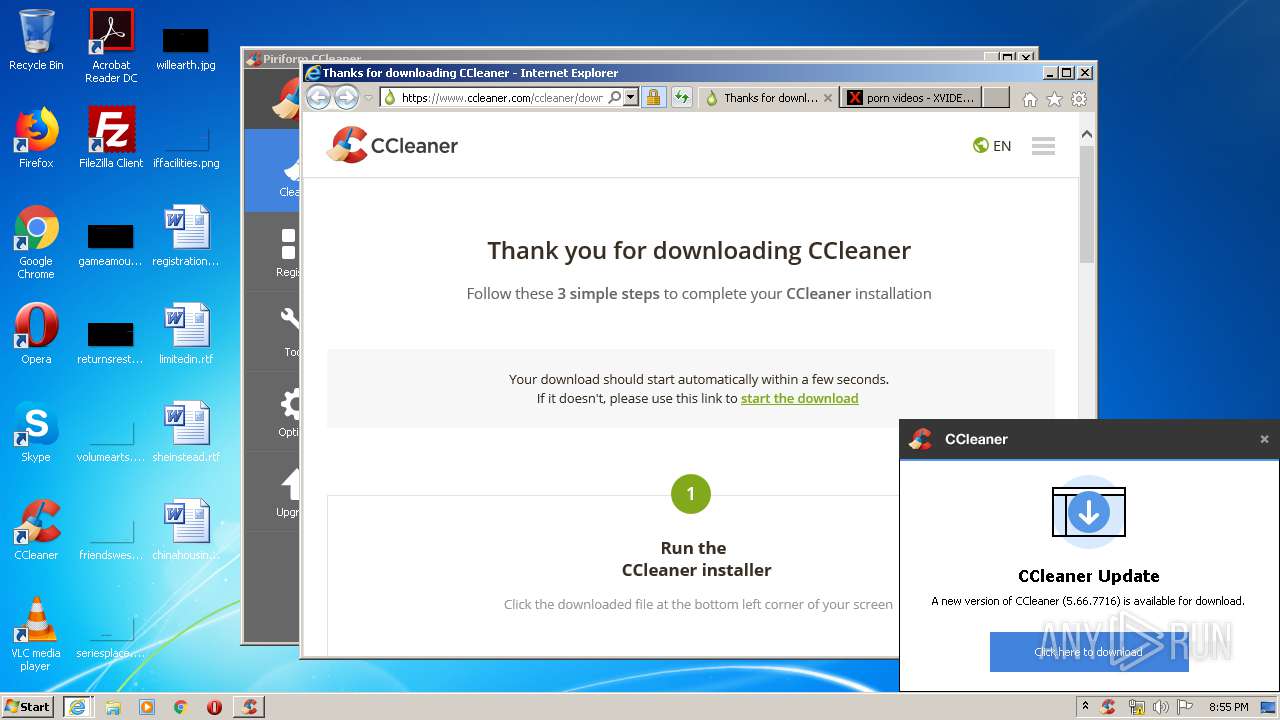
Starts Internet Explorer
- CCleaner.exe (PID: 3584)
Removes files from Windows directory
- CCleaner.exe (PID: 3584)
Adds / modifies Windows certificates
- CCleaner.exe (PID: 3584)
INFO
Manual execution by user
- ntvdm.exe (PID: 2732)
- CCleaner.exe (PID: 2672)
- explorer.exe (PID: 2940)
Dropped object may contain Bitcoin addresses
- BakkesMod.exe (PID: 2548)
- taskhost.exe (PID: 2252)
Reads Internet Cache Settings
- iexplore.exe (PID: 2068)
- iexplore.exe (PID: 1156)
- iexplore.exe (PID: 1944)
Changes internet zones settings
- iexplore.exe (PID: 2068)
Reads Microsoft Office registry keys
- CCleaner.exe (PID: 3584)
Creates files in the user directory
- iexplore.exe (PID: 1156)
- iexplore.exe (PID: 1944)
- iexplore.exe (PID: 2068)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1156)
- iexplore.exe (PID: 1944)
Reads internet explorer settings
- iexplore.exe (PID: 1156)
- iexplore.exe (PID: 1944)
Application launched itself
- iexplore.exe (PID: 2068)
Changes settings of System certificates
- iexplore.exe (PID: 1156)
- iexplore.exe (PID: 1944)
Reads settings of System Certificates
- CCleaner.exe (PID: 3584)
- iexplore.exe (PID: 1156)
- iexplore.exe (PID: 1944)
- iexplore.exe (PID: 2068)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (83) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (9) |
| .exe | | | Generic Win/DOS Executable (3.9) |
| .exe | | | DOS Executable Generic (3.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:10:24 03:30:34+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.22 |
| CodeSize: | 7578112 |
| InitializedDataSize: | 3736576 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3e309 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Oct-2019 01:30:34 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000130 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 24-Oct-2019 01:30:34 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0073A040 | 0x0073A200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59138 |
.rdata | 0x0073C000 | 0x0030BC20 | 0x0030BE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.44446 |
.data | 0x00A48000 | 0x0001C250 | 0x00011000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.58452 |
.qtmetadL\x02 | 0x00A65000 | 0x0000024C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 3.15593 |
_RDATA | 0x00A66000 | 0x00000124 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.51793 |
.rsrc | 0x00A67000 | 0x00028828 | 0x00028A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.30849 |
.reloc | 0x00A90000 | 0x0003F090 | 0x0003F200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.6046 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.80808 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 5.29188 | 9640 | UNKNOWN | English - United States | RT_ICON |
4 | 4.71718 | 16936 | UNKNOWN | English - United States | RT_ICON |
5 | 4.2864 | 67624 | UNKNOWN | English - United States | RT_ICON |
6 | 7.98433 | 65376 | UNKNOWN | English - United States | RT_ICON |
AAA | 2.79908 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
CRYPT32.dll |
GDI32.dll |
IMM32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
WINMM.dll |
Total processes
67
Monitored processes
14
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1156 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2068 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1832 | "taskhost.exe" | C:\Windows\system32\taskhost.exe | — | services.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1944 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2068 CREDAT:2503724 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2068 | "C:\Program Files\Internet Explorer\iexplore.exe" http://www.piriform.com/ccleaner/update?a=0&v=5.35.6210&l=1033&o=6.1W3&t=4&au=1 | C:\Program Files\Internet Explorer\iexplore.exe | CCleaner.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2124 | "taskhost.exe" | C:\Windows\system32\taskhost.exe | — | services.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2140 | "C:\Program Files\CCleaner\CCleaner.exe" /monitor | C:\Program Files\CCleaner\CCleaner.exe | CCleaner.exe | ||||||||||||
User: admin Company: Piriform Ltd Integrity Level: HIGH Description: CCleaner Exit code: 0 Version: 5, 35, 0, 6210 Modules
| |||||||||||||||
| 2252 | "taskhost.exe" | C:\Windows\system32\taskhost.exe | — | services.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2548 | "C:\Users\admin\AppData\Local\Temp\BakkesMod.exe" | C:\Users\admin\AppData\Local\Temp\BakkesMod.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2672 | "C:\Program Files\CCleaner\CCleaner.exe" | C:\Program Files\CCleaner\CCleaner.exe | — | explorer.exe | |||||||||||
User: admin Company: Piriform Ltd Integrity Level: MEDIUM Description: CCleaner Exit code: 0 Version: 5, 35, 0, 6210 Modules
| |||||||||||||||
| 2732 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\system32\ntvdm.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 255 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
6 995
Read events
4 424
Write events
2 485
Delete events
86
Modification events
| (PID) Process: | (2548) BakkesMod.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2548) BakkesMod.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 070000000100000002000000000000000A000000090000000800000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (2548) BakkesMod.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\103\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Generic | |||
| (PID) Process: | (2548) BakkesMod.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2548) BakkesMod.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12D\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2548) BakkesMod.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | 1 |
Value: 420061006B006B00650073004D006F0064002E0065007800650000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000E5010000BE000000650400009E020000000000000000000000000000000000000100000000000000 | |||
| (PID) Process: | (2548) BakkesMod.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | delete value | Name: | 1 |
Value: 420061006B006B00650073004D006F0064002E0065007800650000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000E5010000BE000000650400009E020000000000000000000000000000000000000100000000000000 | |||
| (PID) Process: | (2548) BakkesMod.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | 1 |
Value: 420061006B006B00650073004D006F0064002E006500780065000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000E1010000180100001F0300008801000000000000000000000000000000000000E5010000BE000000650400009E020000000000000000000000000000000000000100000000000000 | |||
| (PID) Process: | (2548) BakkesMod.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0100000000000000FFFFFFFF | |||
| (PID) Process: | (2548) BakkesMod.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\103\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | Mode |
Value: 4 | |||
Executable files
20
Suspicious files
223
Text files
385
Unknown types
81
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2548 | BakkesMod.exe | C:\Users\admin\AppData\Local\Temp\bmupdate.zip | compressed | |
MD5:808252211C3AFB4271B04715F050BA02 | SHA256:30A5BC92F84A79D1B01FABA5F3FF094CE492C6EDA092FB1C0EDEB74DA910018E | |||
| 2548 | BakkesMod.exe | C:\Users\admin\Pictures\RocketLeague.exe | jnt | |
MD5:5B944604BE1CC246C826A7F4BD59F4E1 | SHA256:DFB3EC3500A2F4939BAF96322E3BDAAA18CC6F787003D7155E56C617CB4BBD26 | |||
| 2548 | BakkesMod.exe | C:\Users\admin\Pictures\bakkesmod\bakkesmodsdk\include\bakkesmod\plugin\bakkesmodplugin.h | text | |
MD5:D087EF86B91D5B9B63AB3B8A8BE5674B | SHA256:7C67FB32C40AF0AC7F03FD1E45136406750183629BF6DB62A00C0CBCEE52E742 | |||
| 2548 | BakkesMod.exe | C:\Users\admin\Pictures\bakkesmod\bakkesmodsdk\include\bakkesmod\plugin\botplugin.h | text | |
MD5:CF5F2B0D7CD32EA96B6D031F403A28AF | SHA256:03CC5682F93670E710A43A5F6A517FC655EA8683C677F97D561EA960D9BE3D07 | |||
| 2548 | BakkesMod.exe | C:\Users\admin\Pictures\bakkesmod\bakkesmodsdk\include\bakkesmod\plugin\bakkesmodsdk.h | text | |
MD5:24085FA76EB73B5C298FB471955E3B52 | SHA256:BE3492AAC1949E76C4DE6EAD89252C2CB7DAF640BB8DA3C9C21848875B1B2A8F | |||
| 2548 | BakkesMod.exe | C:\Users\admin\Pictures\bakkesmod\bakkesmod.dll | executable | |
MD5:B02DFB8A555D431E37D29F4F70DE4F04 | SHA256:CA99D1600723511C8A637AA392BE8BE60694087D73240FAD6319F33D38D65572 | |||
| 2548 | BakkesMod.exe | C:\Users\admin\Pictures\bakkesmod\bakkesmodsdk\include\bakkesmod\wrappers\arraywrapper.h | text | |
MD5:354D092541018CBF27A6D5ABFFD5DBAA | SHA256:75BC8E60B1CEF162CF8424C7561A891CBA90386BD2586B4CAA45A95790F6FC55 | |||
| 2548 | BakkesMod.exe | C:\Users\admin\Pictures\bakkesmod\bakkesmodsdk\include\bakkesmod\wrappers\canvaswrapper.h | text | |
MD5:F4597D409673C129A01518F46A62F213 | SHA256:0BE7B0D77F0CD4A4D1AD7D7DCAA9487CD3ABC79BDF1E4C1C75D055D62F1FCAED | |||
| 2548 | BakkesMod.exe | C:\Users\admin\Pictures\bakkesmod\64bitbminjector.exe | executable | |
MD5:BC58339C62B92FDA51DA1241B9365D8E | SHA256:DE20B80F7393A795FF48FD7FB42A9C7AEDF43FCAD42FED2066D03F55D879FE10 | |||
| 2548 | BakkesMod.exe | C:\Users\admin\Pictures\bakkesmod\bakkesmodsdk\bakkes_patchplugin.py | text | |
MD5:C0716A3B133F0288F3AEF1A5F4F689D5 | SHA256:9792F8FC591C0C413E7E78A91E4E4CF83600E1E3F0D06EE2104E7B7E2F2E150E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
174
TCP/UDP connections
184
DNS requests
65
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3584 | CCleaner.exe | GET | 200 | 151.101.2.109:80 | http://license.piriform.com/verify/?p=ccpro&c=cc&cv=5.35.6210&l=1033&lk=CJ9T-J7CU-SPNV-GWMB-WBEC&mk=IJR6-W5SV-5KYR-QBZD-6BY4-RN5Z-WAV9-RVK2-VJCA&mx=97B7721C4994E2556FF6A439510F665DB45337A341A47E15F4997584423BF714&gu=00000000-0000-4000-8000-d6f7f2be5127 | US | text | 17 b | whitelisted |
1156 | iexplore.exe | GET | 301 | 151.101.0.64:80 | http://www.piriform.com/ccleaner/update?a=0&v=5.35.6210&l=1033&o=6.1W3&t=4&au=1 | US | — | — | whitelisted |
3584 | CCleaner.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/rootr1/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDkbwjNvPLFRm7zMB3V80 | US | der | 1.49 Kb | whitelisted |
1156 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
1156 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
1156 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
1156 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
1156 | iexplore.exe | GET | 200 | 172.217.22.99:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1156 | iexplore.exe | GET | 200 | 172.217.22.99:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1156 | iexplore.exe | GET | 200 | 172.217.22.99:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3584 | CCleaner.exe | 151.101.0.64:80 | — | Fastly | US | whitelisted |
2548 | BakkesMod.exe | 149.210.150.107:80 | — | Transip B.V. | NL | suspicious |
3584 | CCleaner.exe | 151.101.2.202:443 | www.ccleaner.com | Fastly | US | suspicious |
3584 | CCleaner.exe | 151.101.2.109:443 | www.piriform.com | Fastly | US | suspicious |
3584 | CCleaner.exe | 151.101.0.64:443 | — | Fastly | US | whitelisted |
3584 | CCleaner.exe | 104.18.20.226:80 | ocsp.globalsign.com | Cloudflare Inc | US | shared |
1156 | iexplore.exe | 151.101.0.64:80 | — | Fastly | US | whitelisted |
3584 | CCleaner.exe | 151.101.2.109:80 | www.piriform.com | Fastly | US | suspicious |
1156 | iexplore.exe | 151.139.237.73:443 | s1.pir.fm | netDNA | US | unknown |
1156 | iexplore.exe | 151.101.2.202:443 | www.ccleaner.com | Fastly | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.piriform.com |
| whitelisted |
www.ccleaner.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
license.piriform.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
s1.pir.fm |
| suspicious |
www.google.com |
| malicious |
s7.addthis.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2548 | BakkesMod.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host ZIP Request |
1156 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1156 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
BakkesMod.exe | QObject::connect: No such signal QNetworkAccessManager::error(QNetworkReply::NetworkError)
|
BakkesMod.exe | QObject::connect: No such signal QNetworkAccessManager::downloadProgress(qint64, qint64)
|