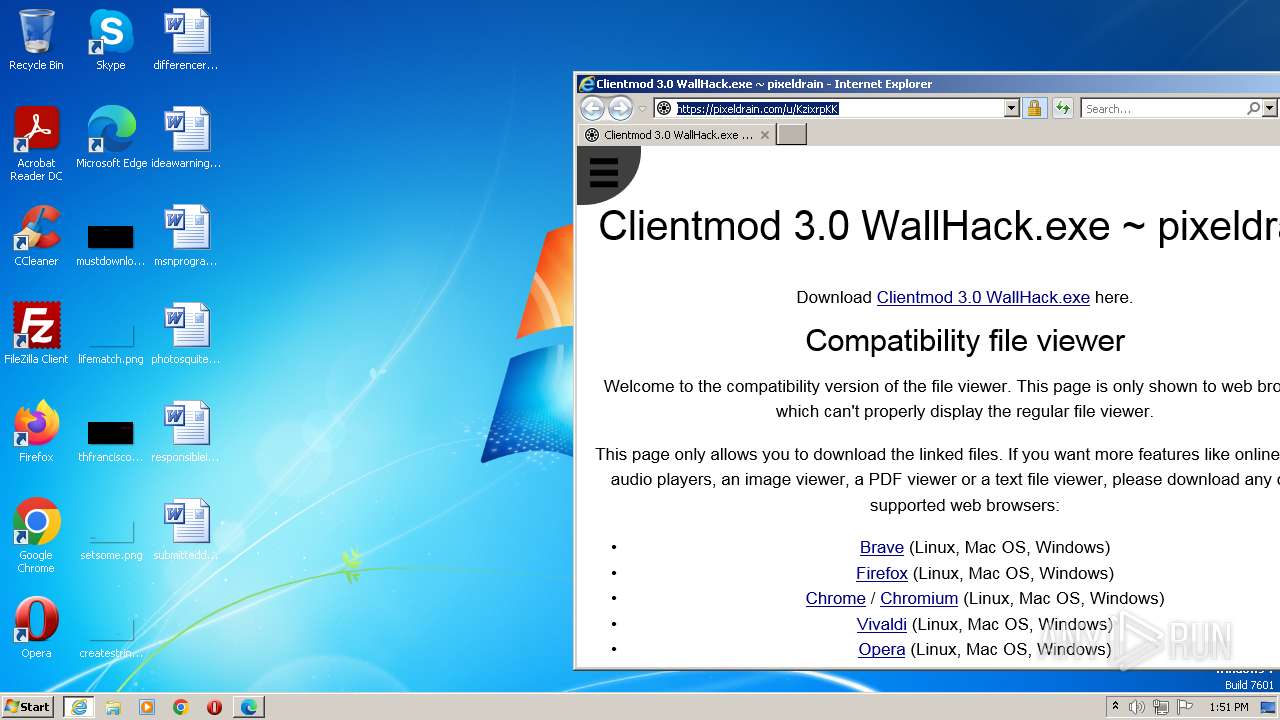
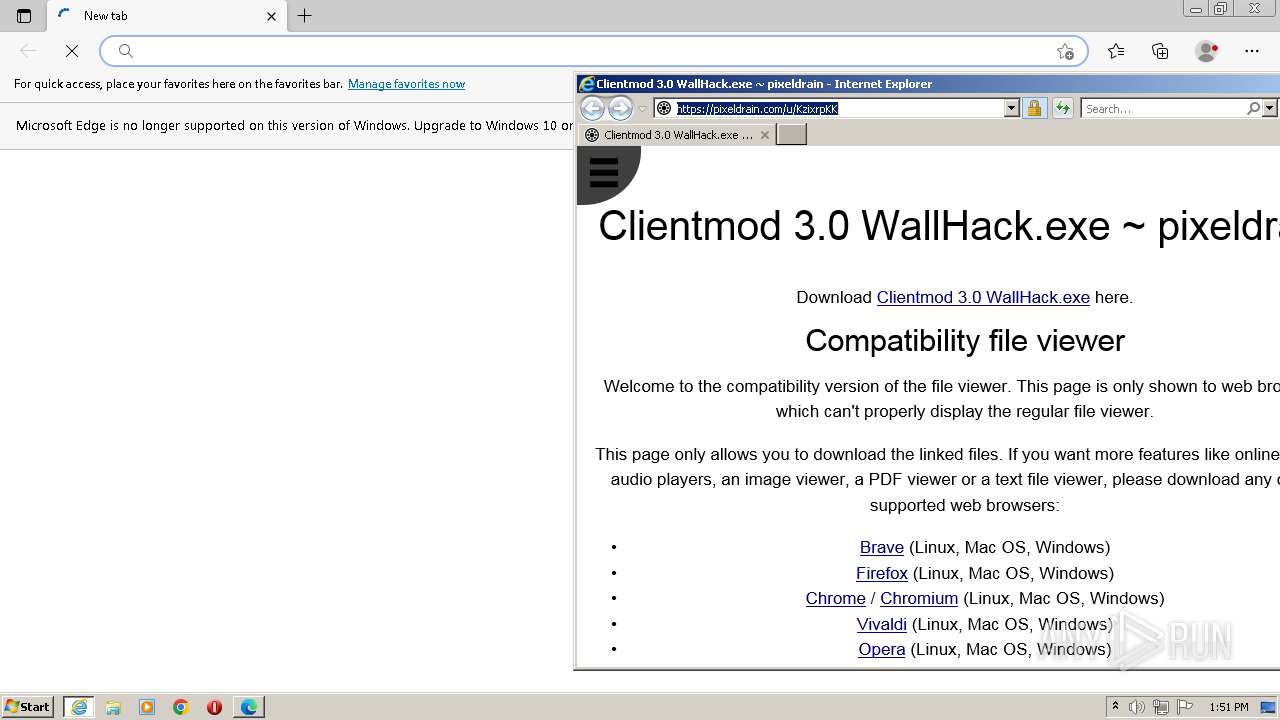
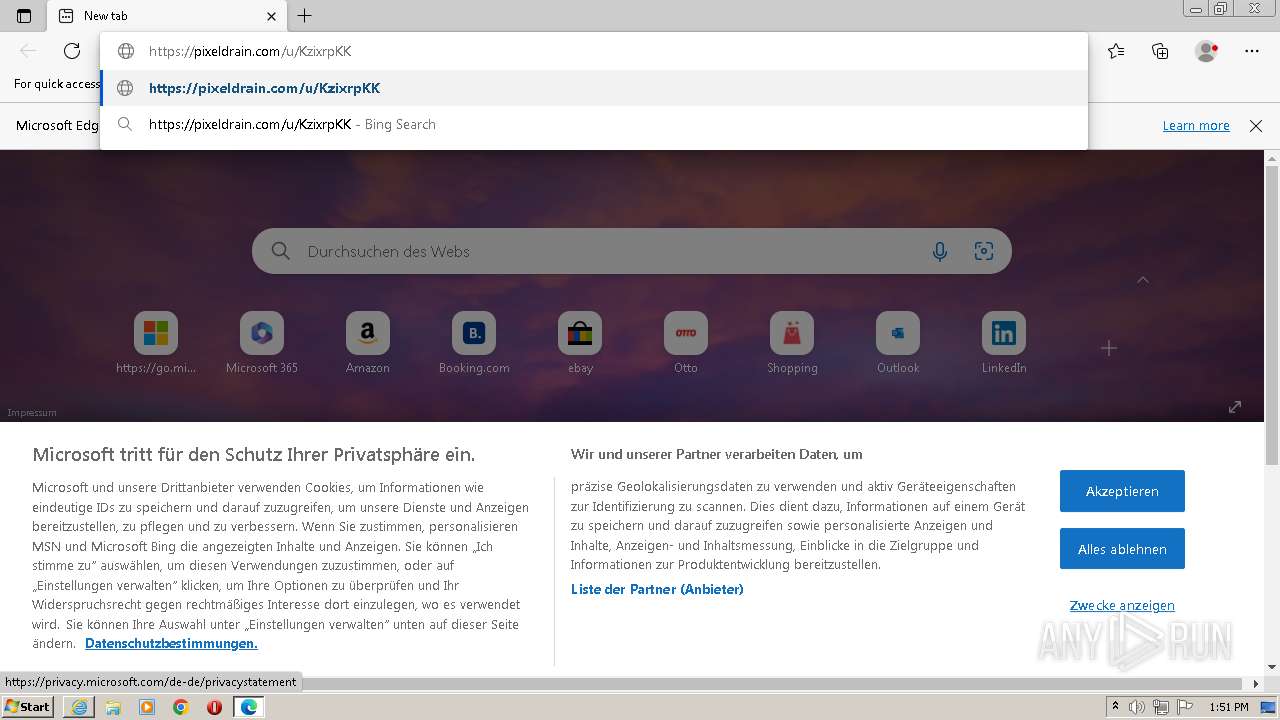
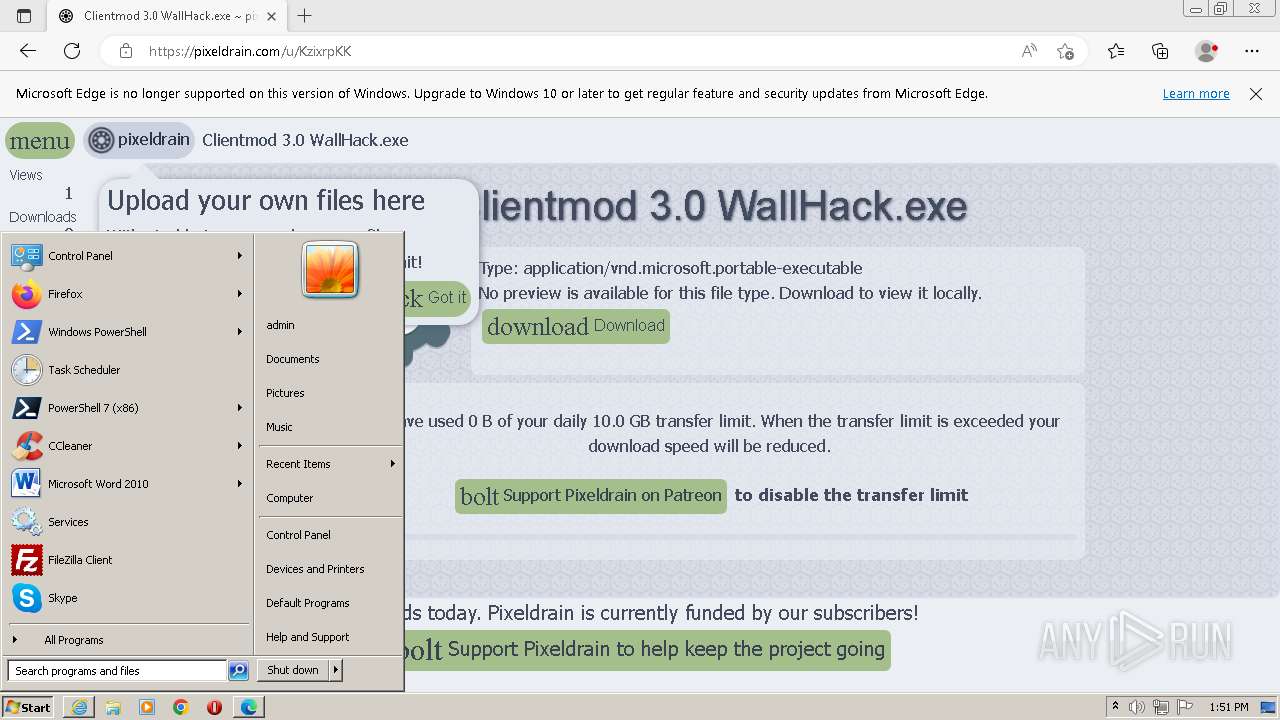
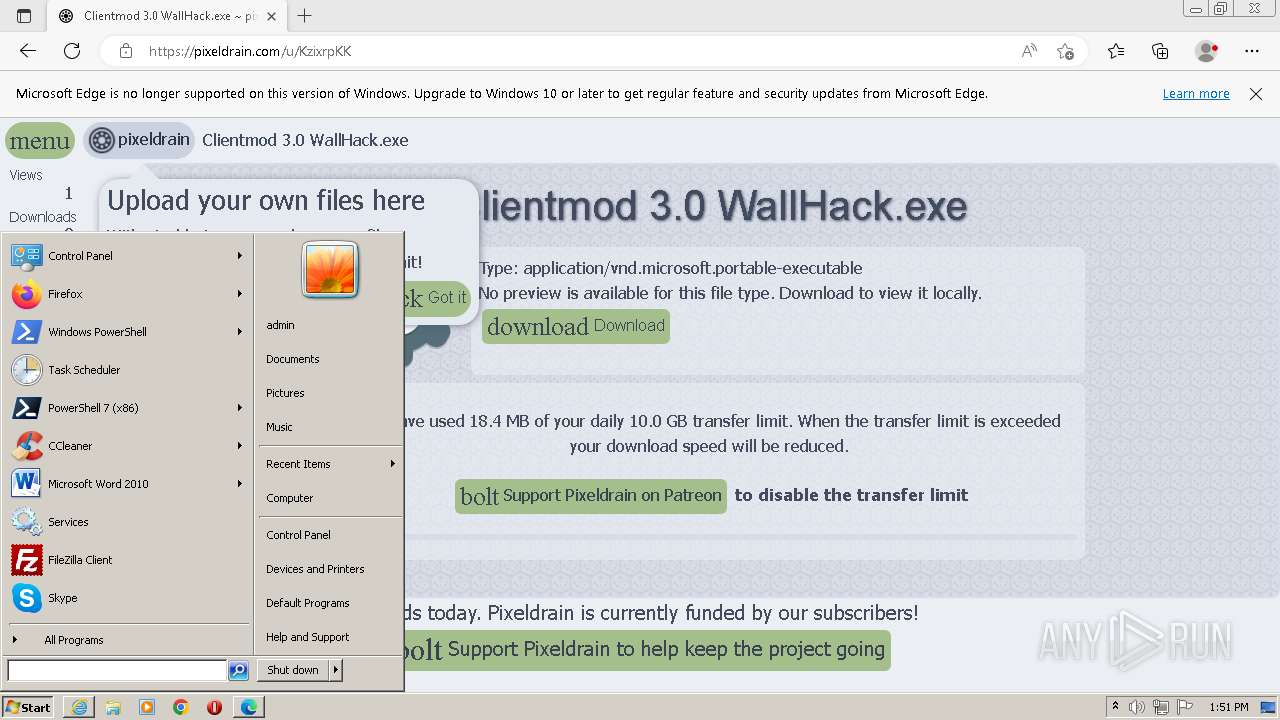
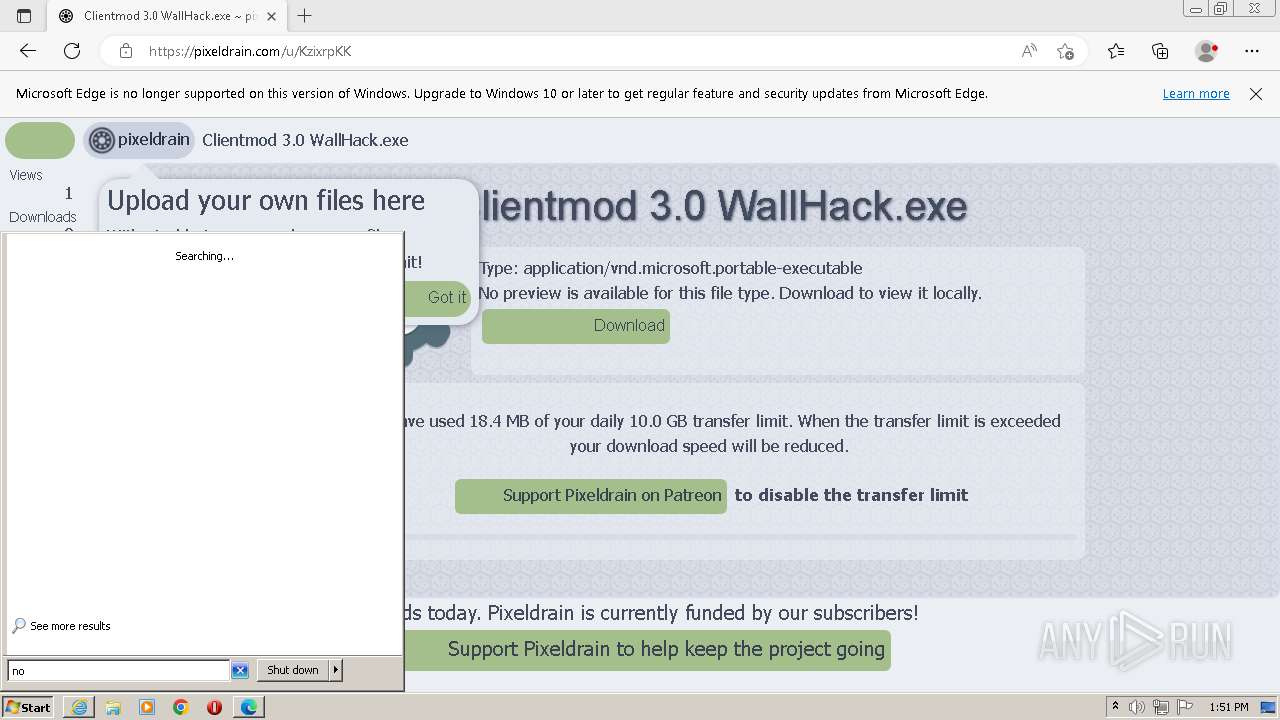
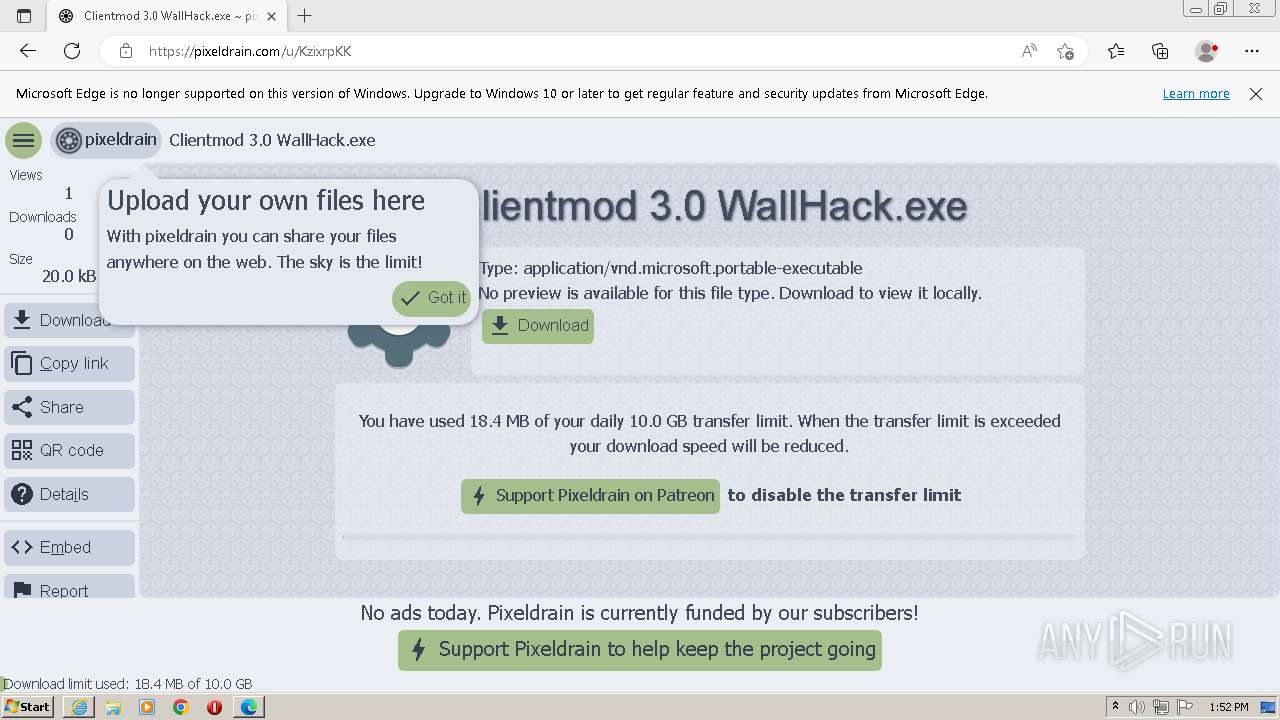
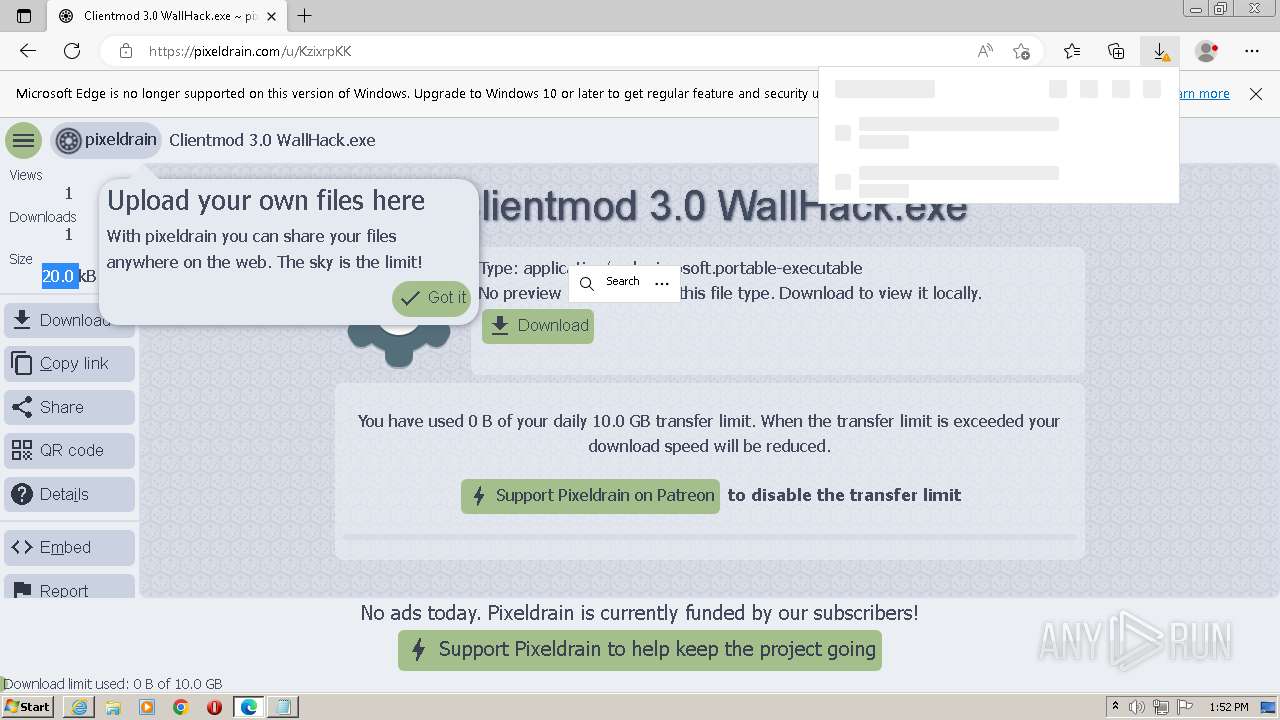
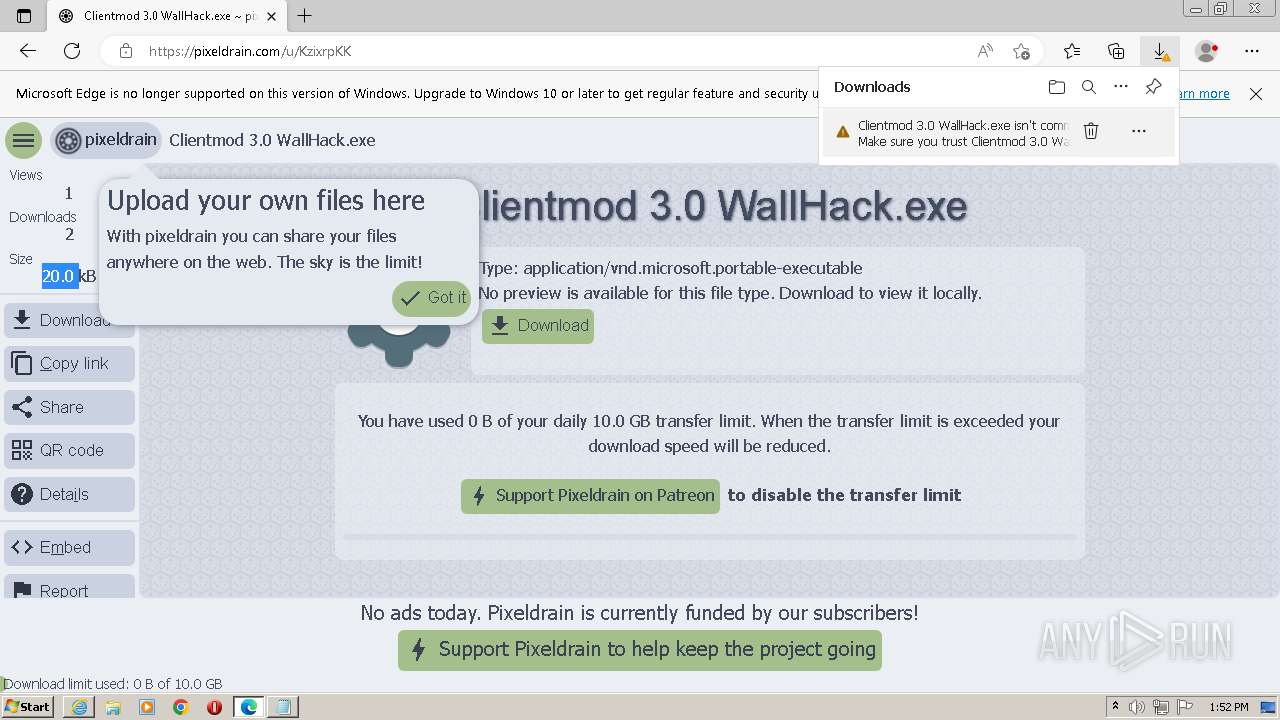
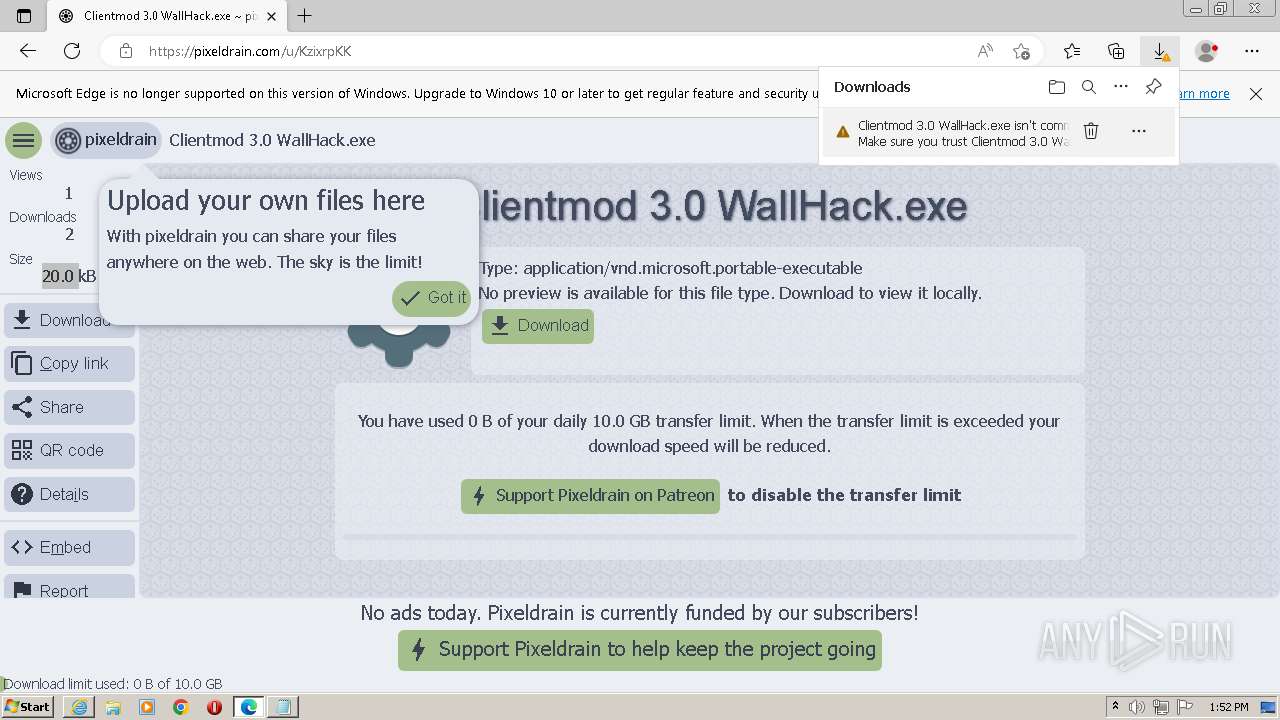
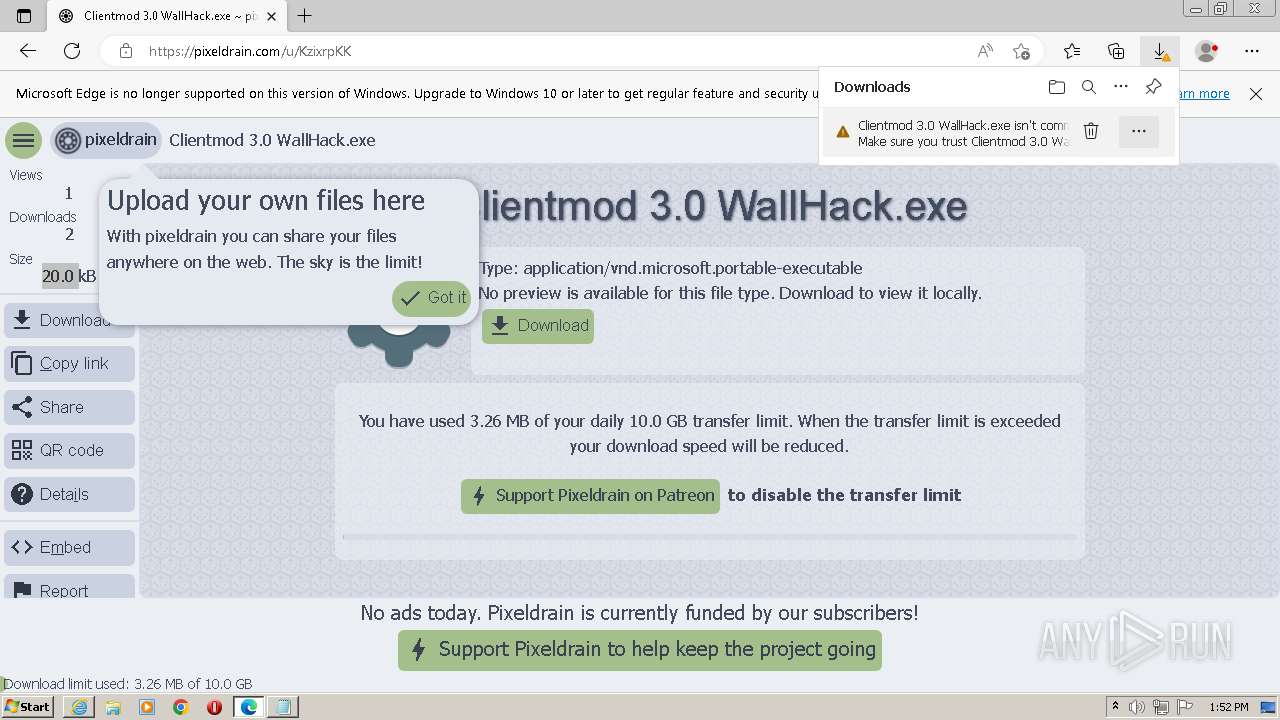
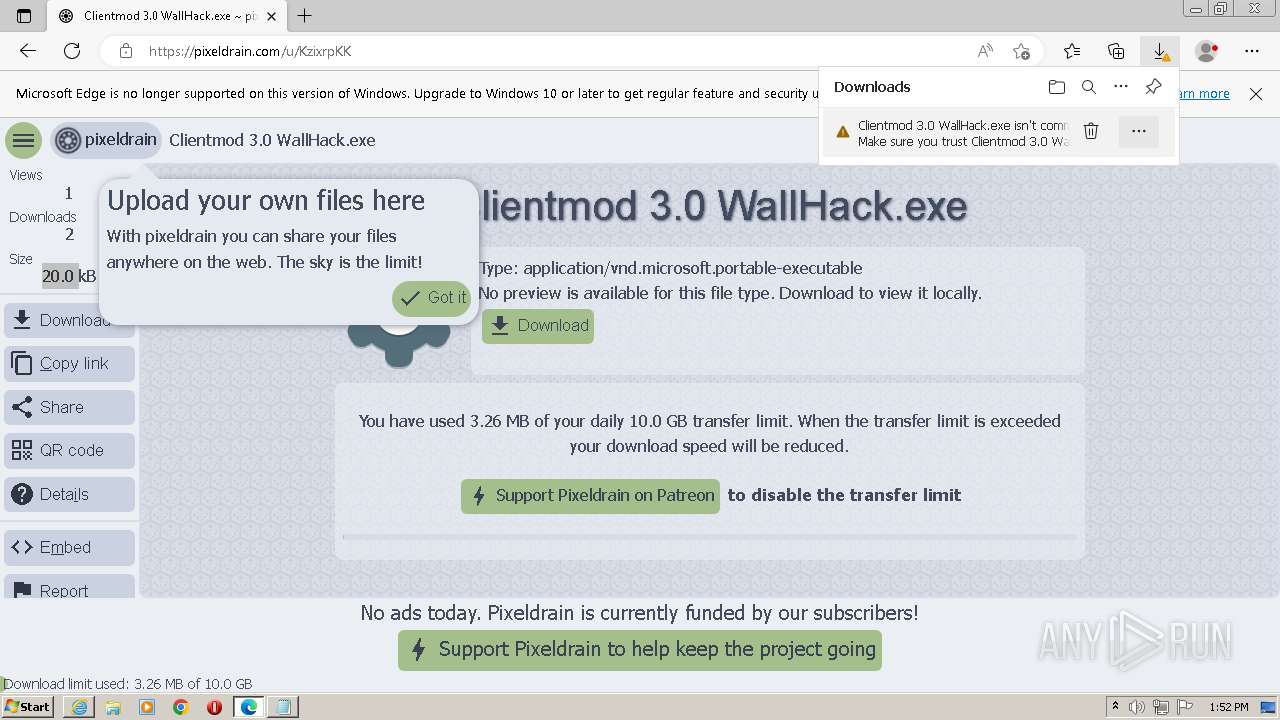
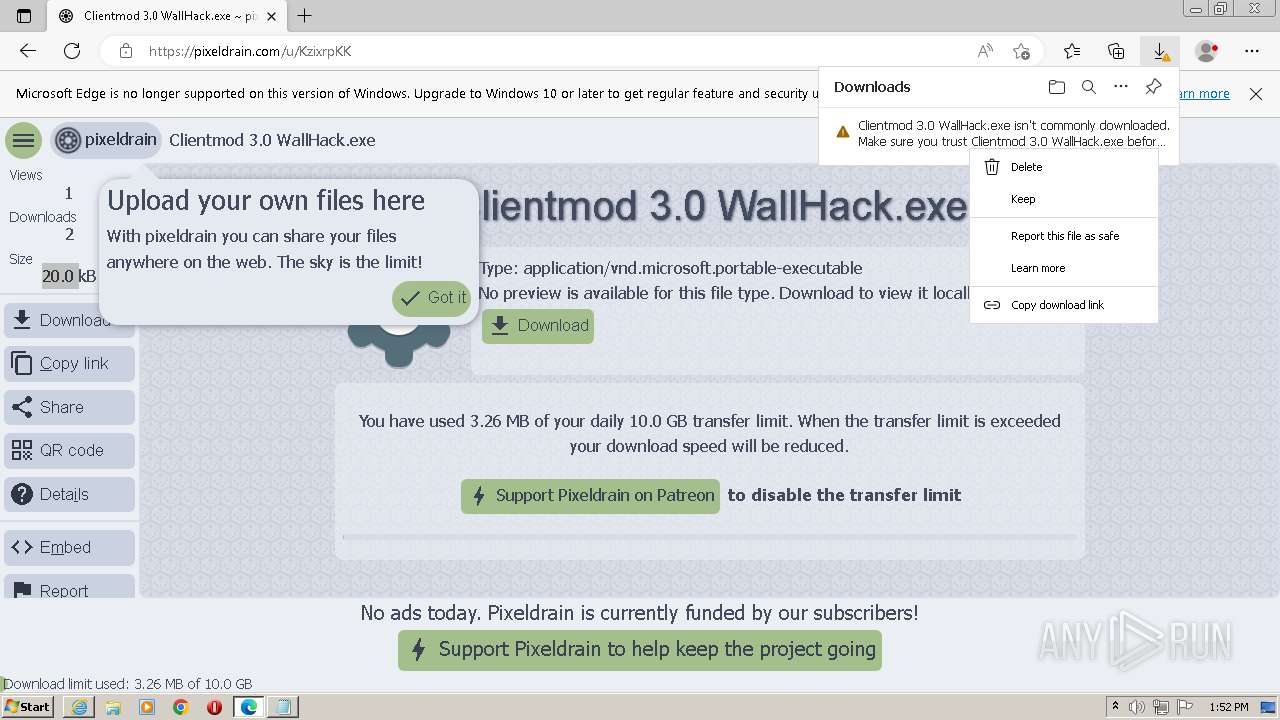
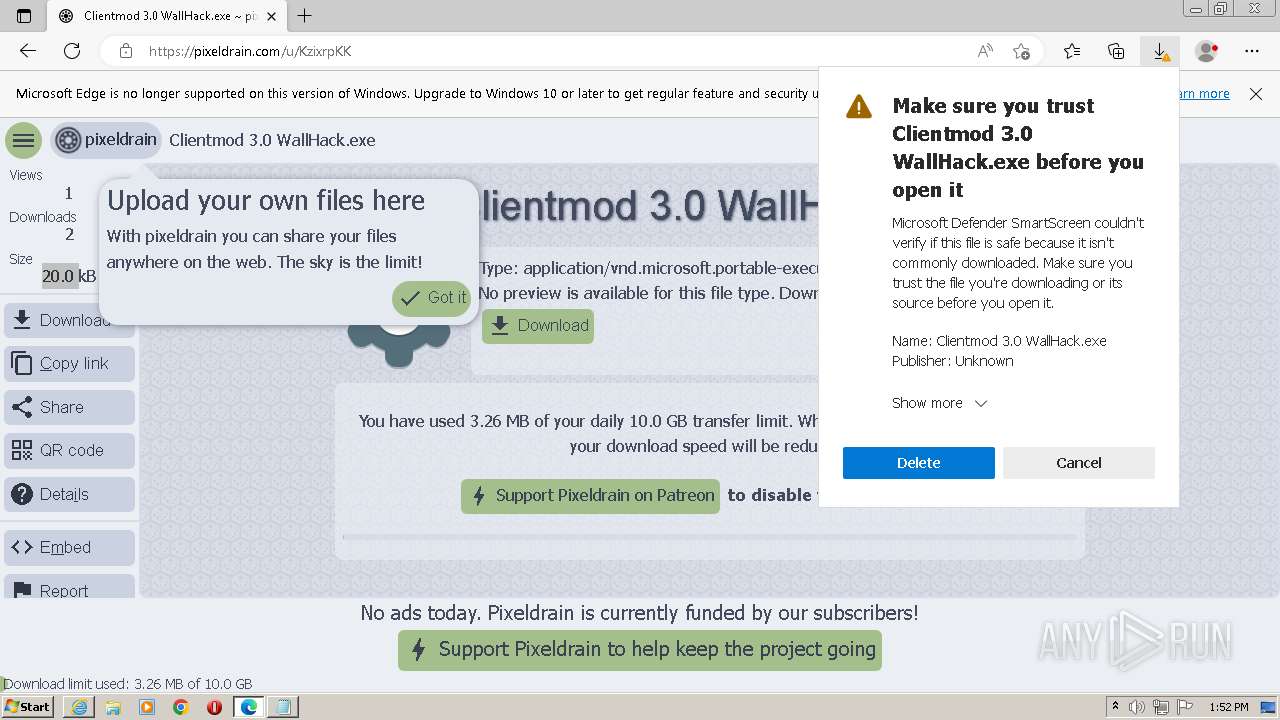
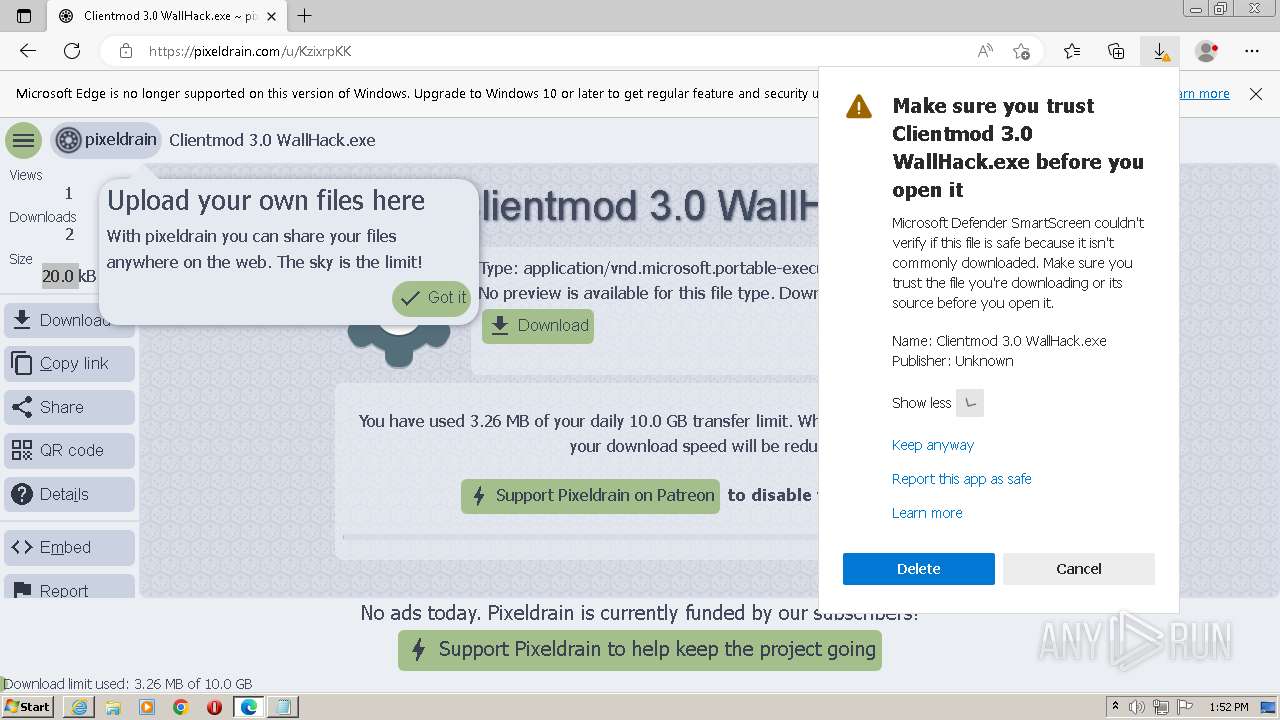
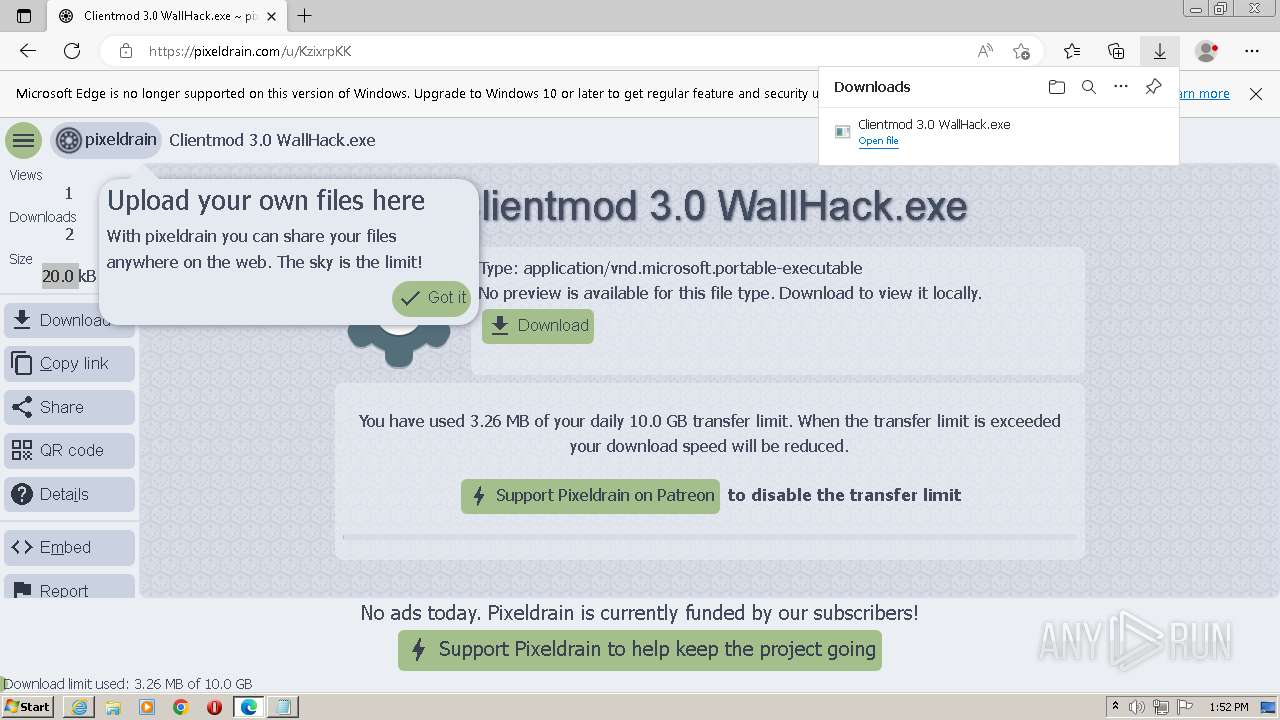
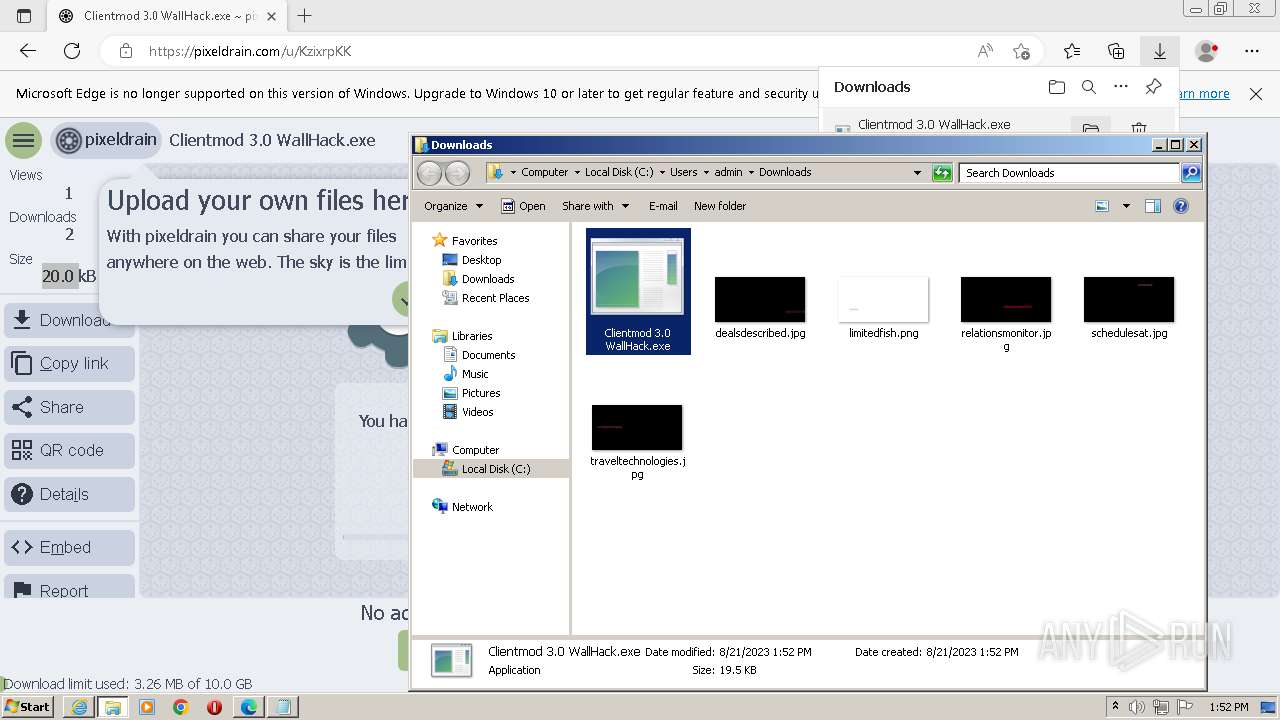
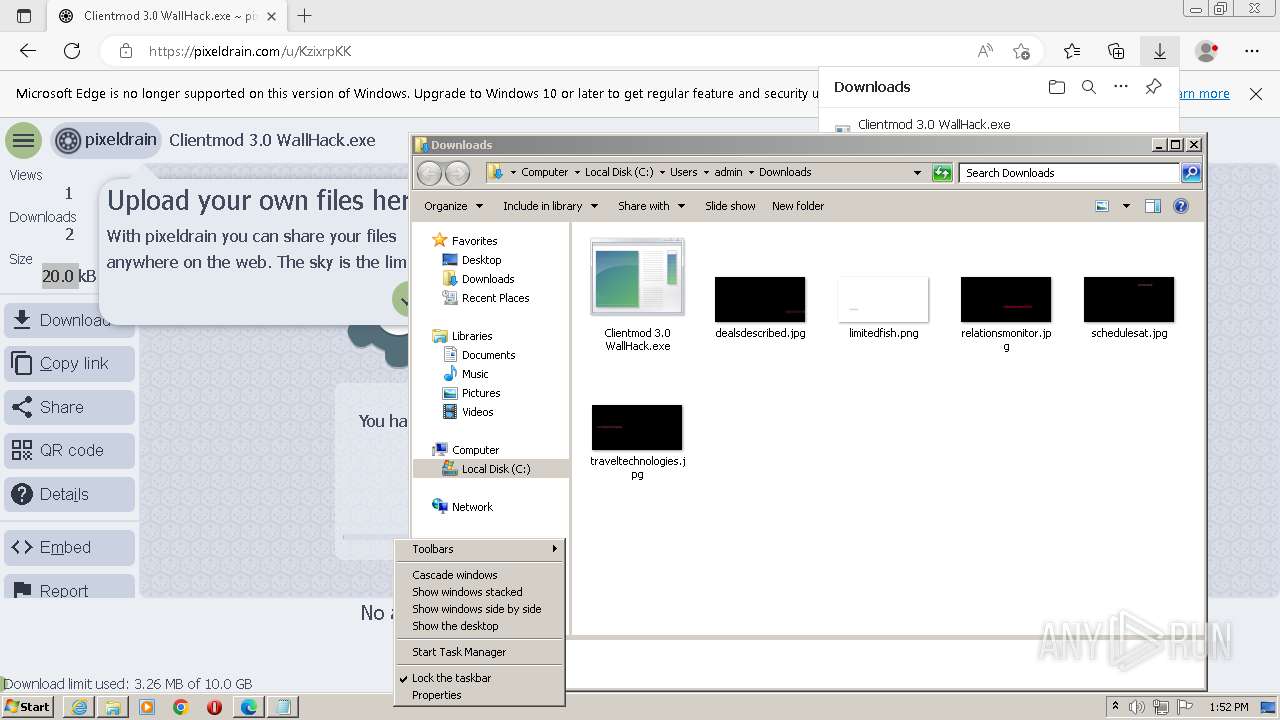
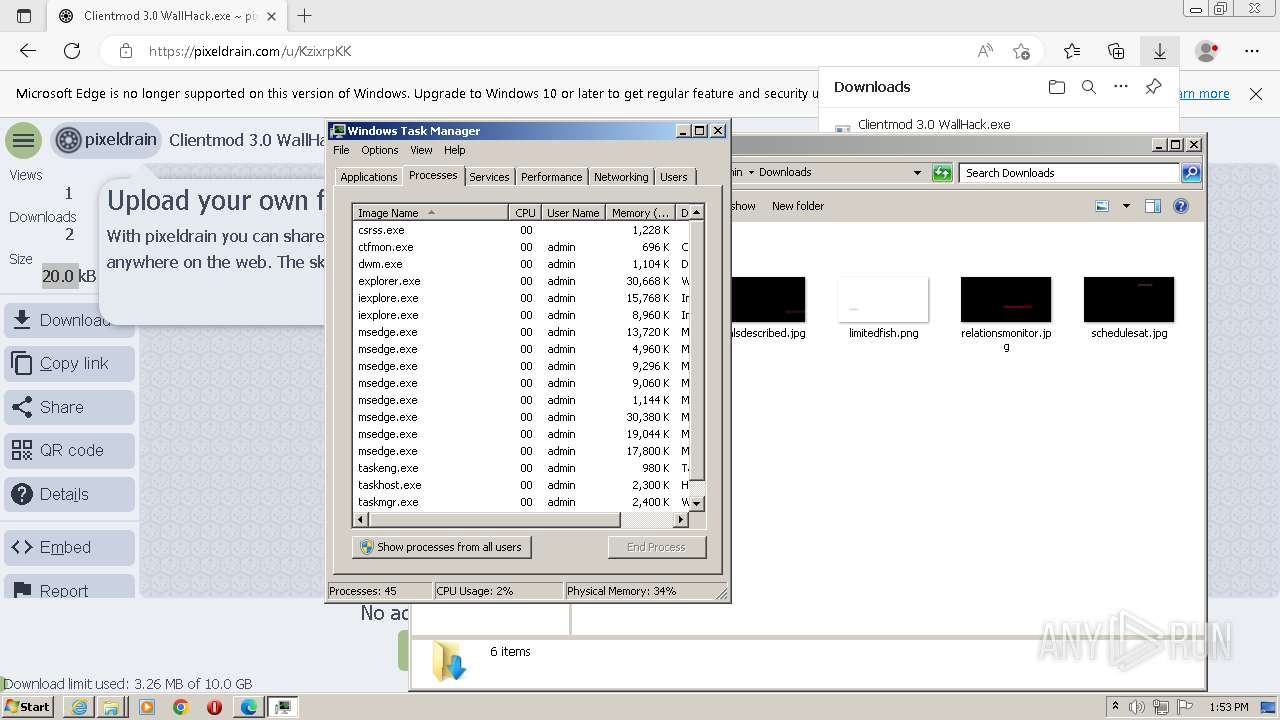
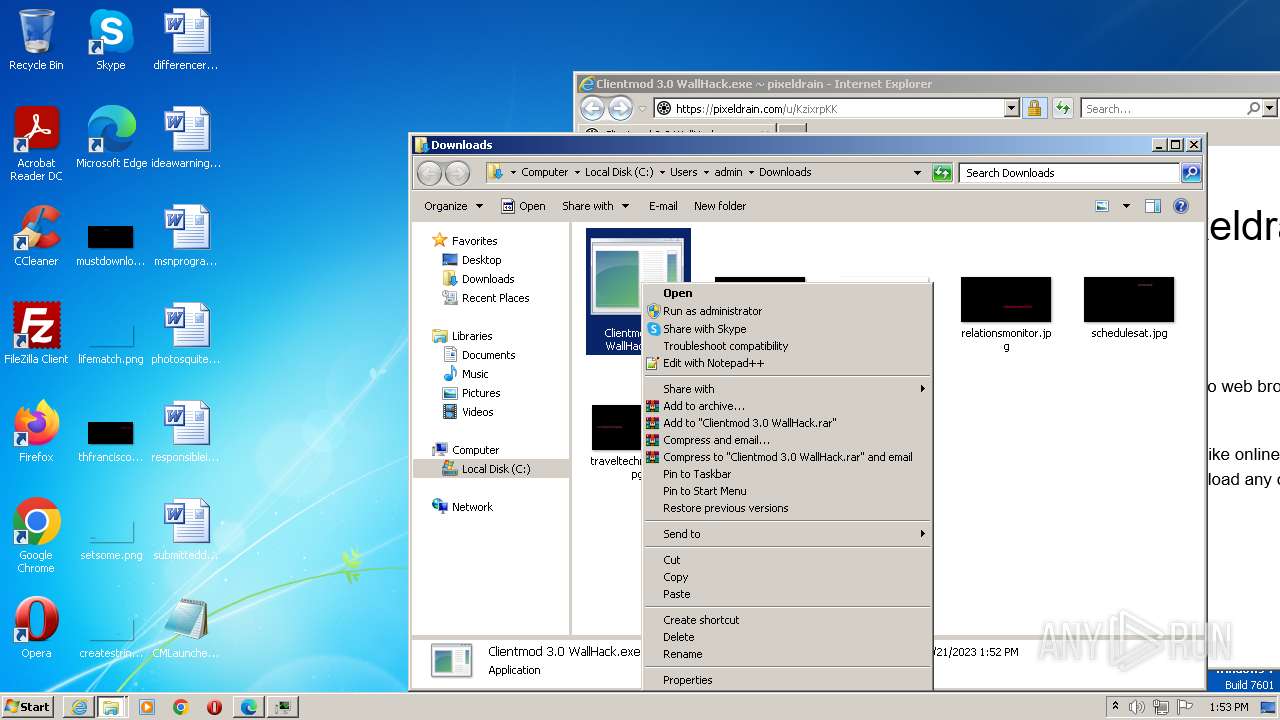
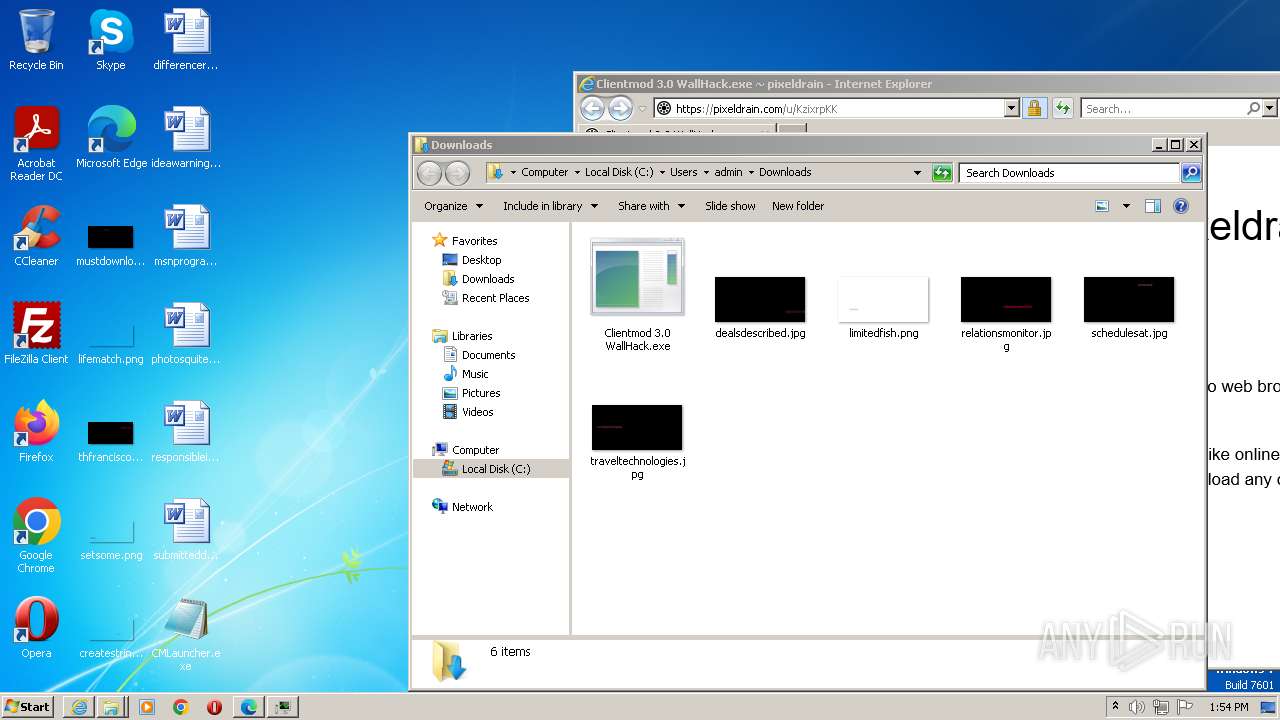
| URL: | https://pixeldrain.com/u/KzixrpKK |
| Full analysis: | https://app.any.run/tasks/934ed242-4808-416e-98db-0c97a3497999 |
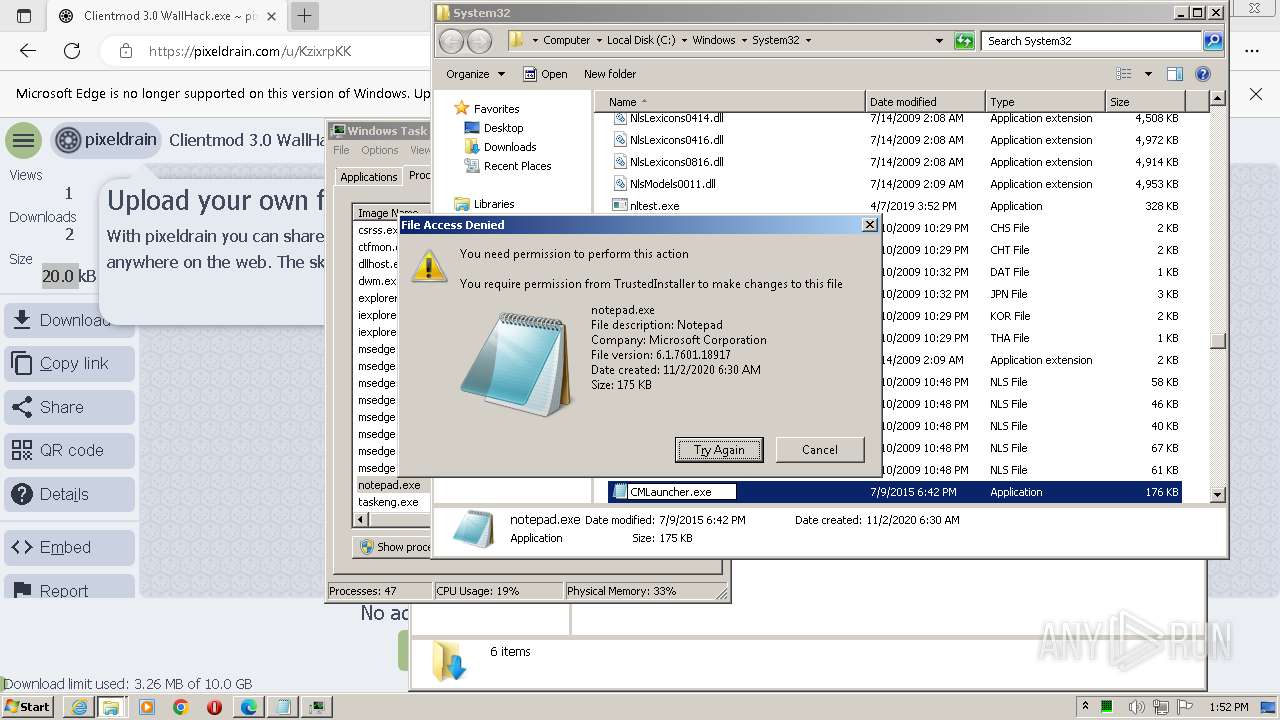
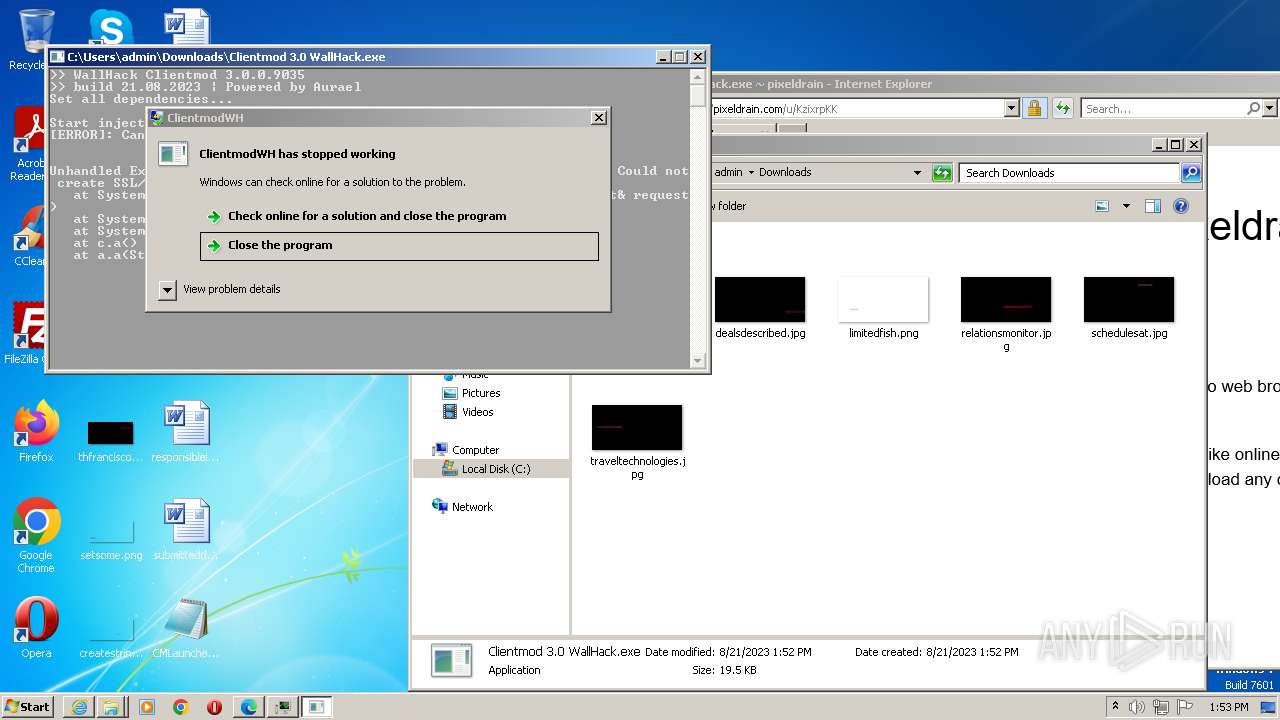
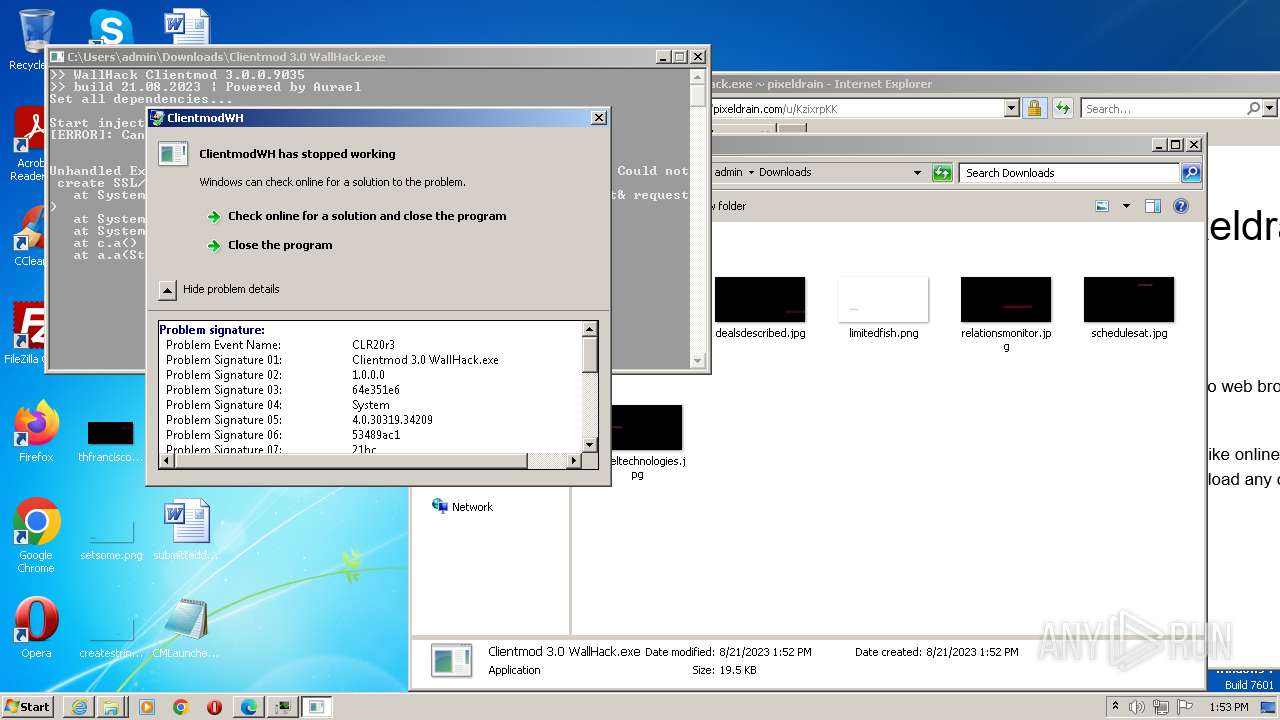
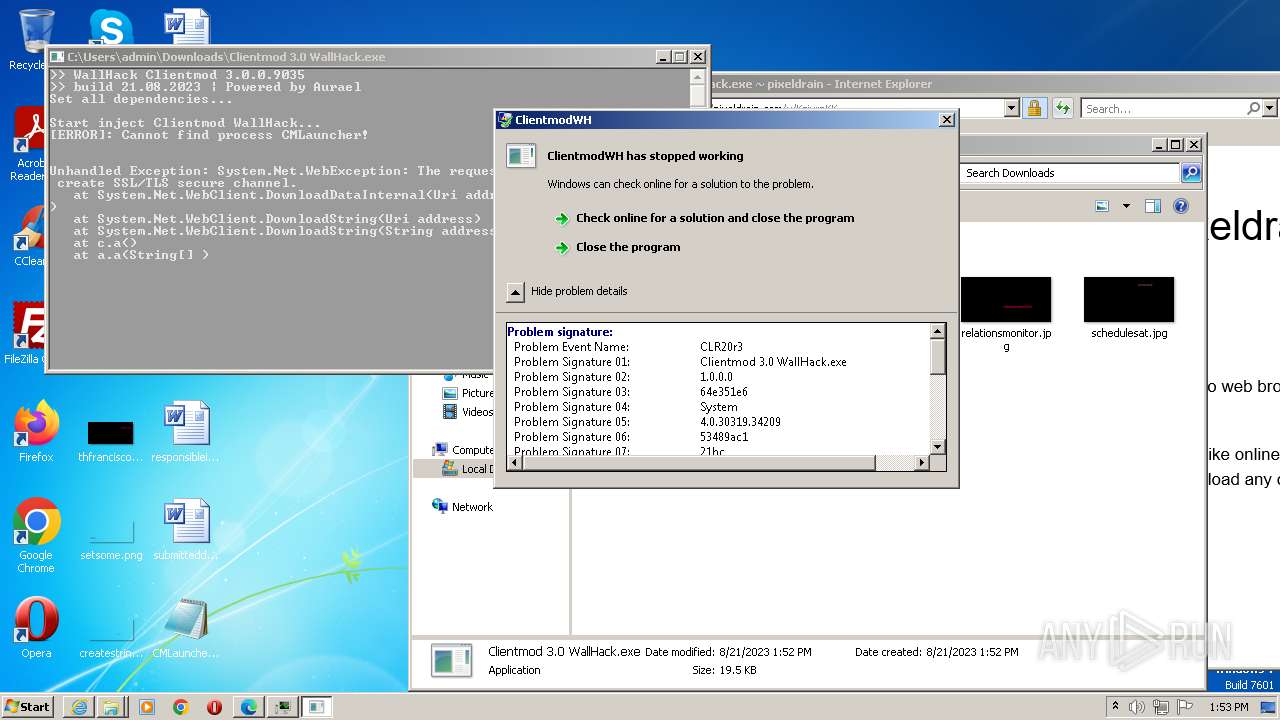
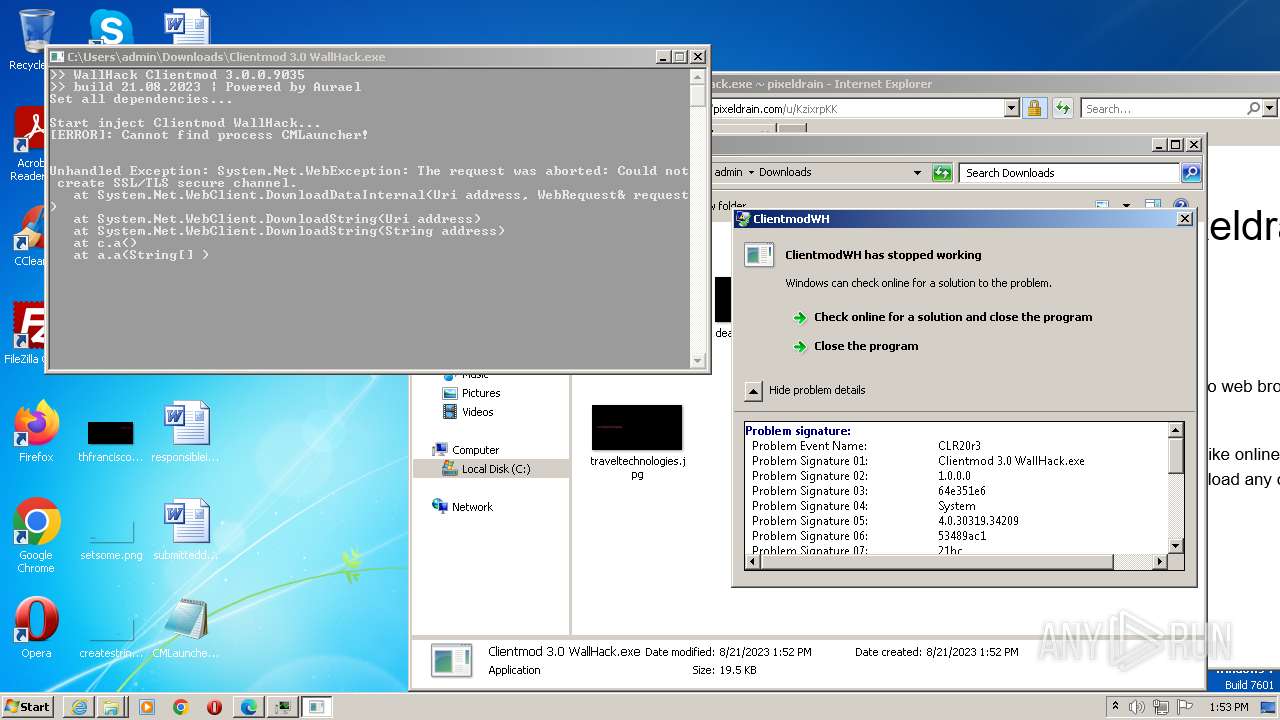
| Verdict: | Malicious activity |
| Analysis date: | August 21, 2023, 12:50:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 9B909B98377B81A1438C55FEF499CF97 |
| SHA1: | 166F49B9CD6DA8D650AA5F2B56B2B980A79B2360 |
| SHA256: | F6D2D456016BB43CE2AA7DABE18BDB6DDC46F6B4CE8794FCDDA3A24C7C76B56C |
| SSDEEP: | 3:N8Icl/GKgVmEu:2IG/dgVmEu |
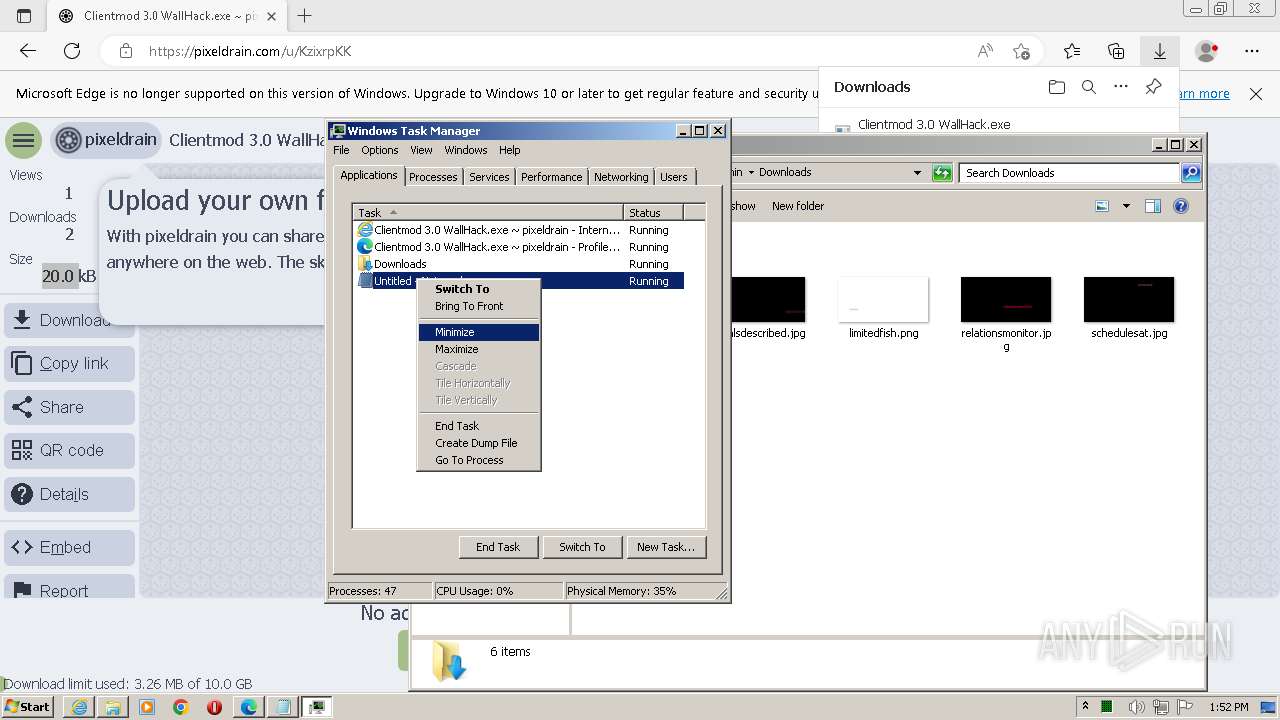
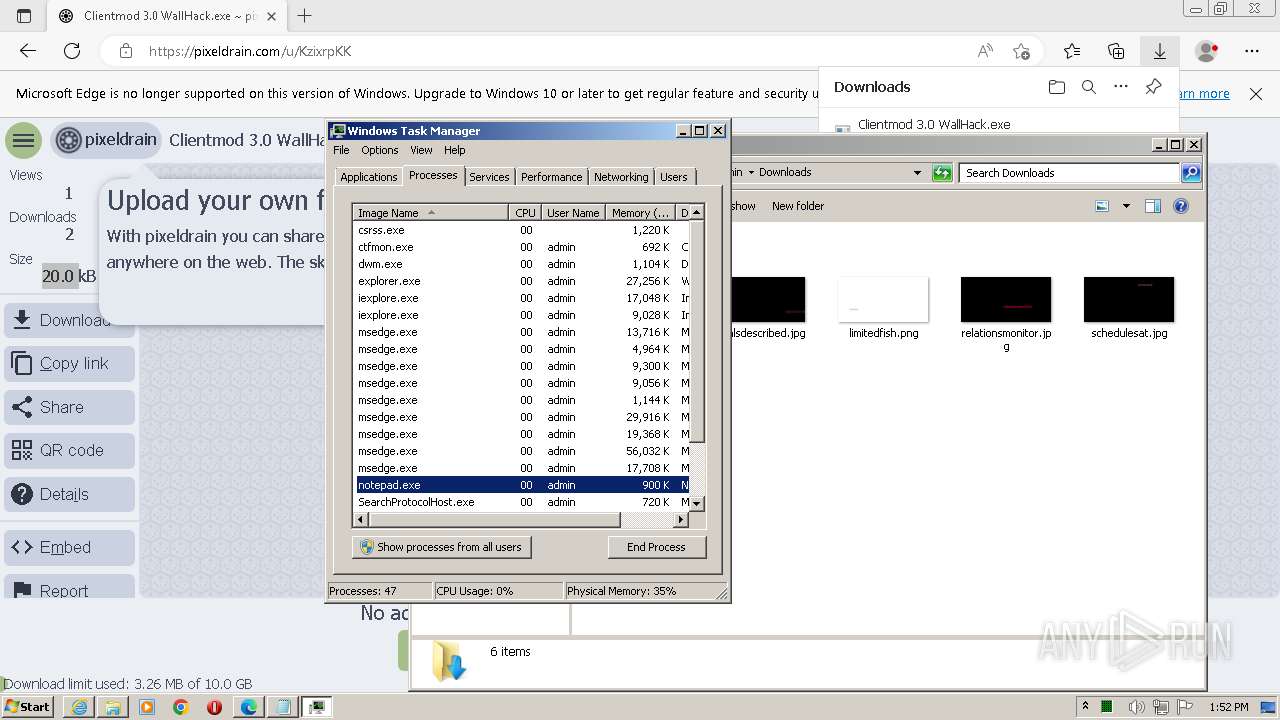
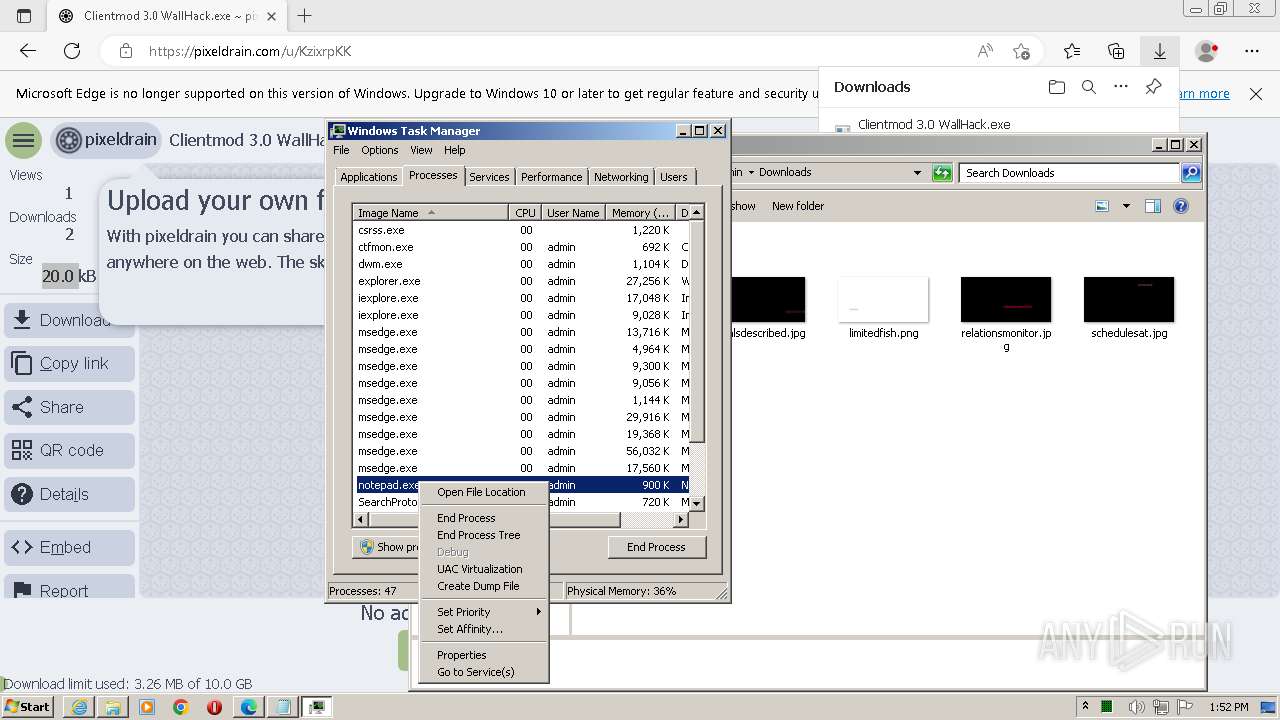
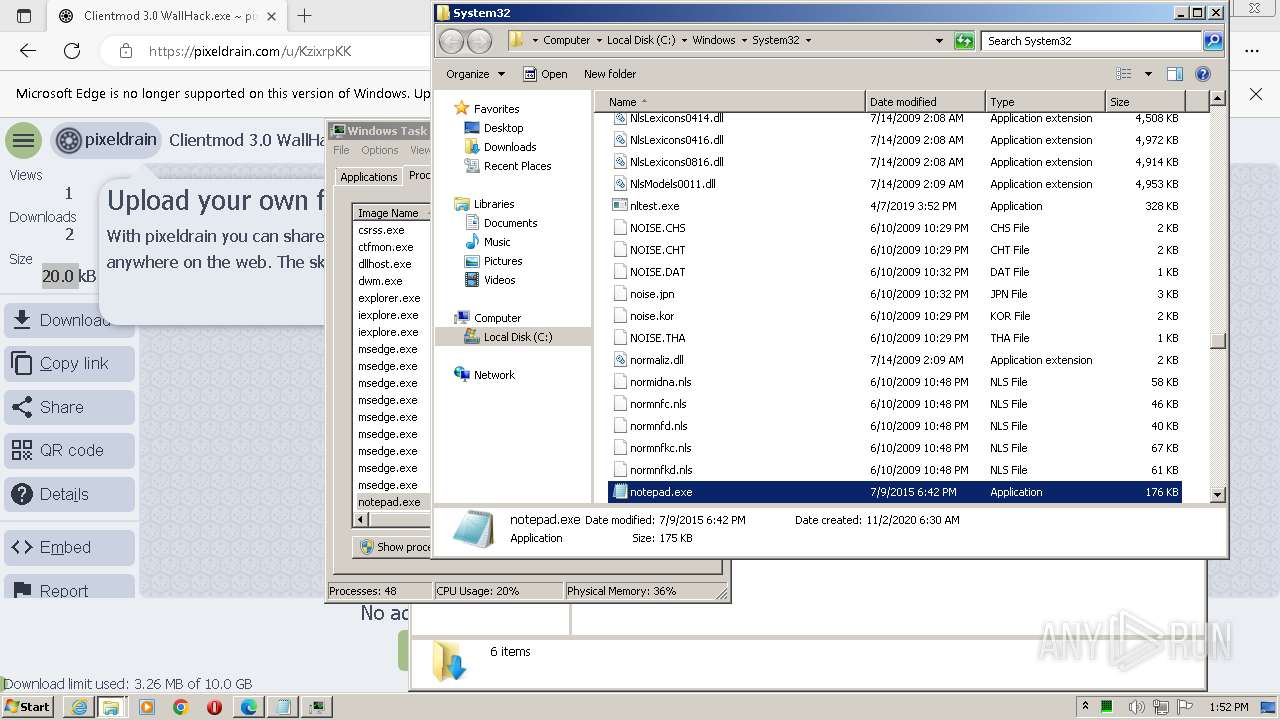
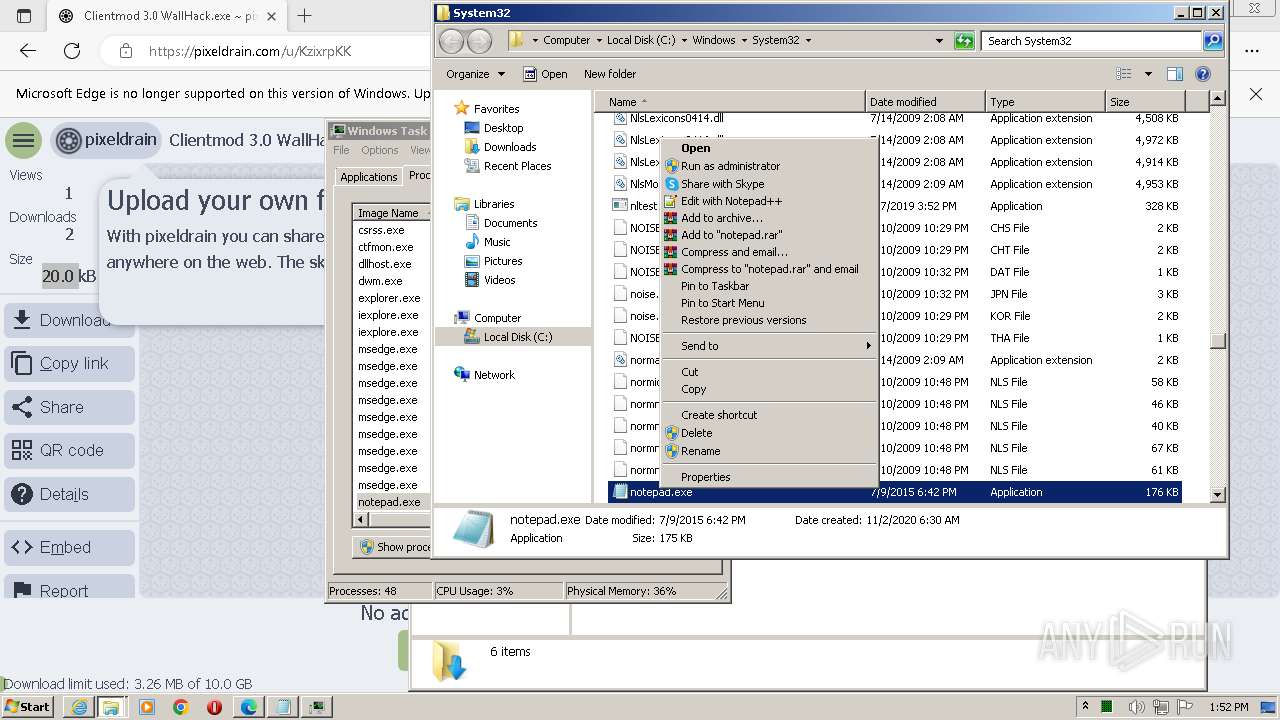
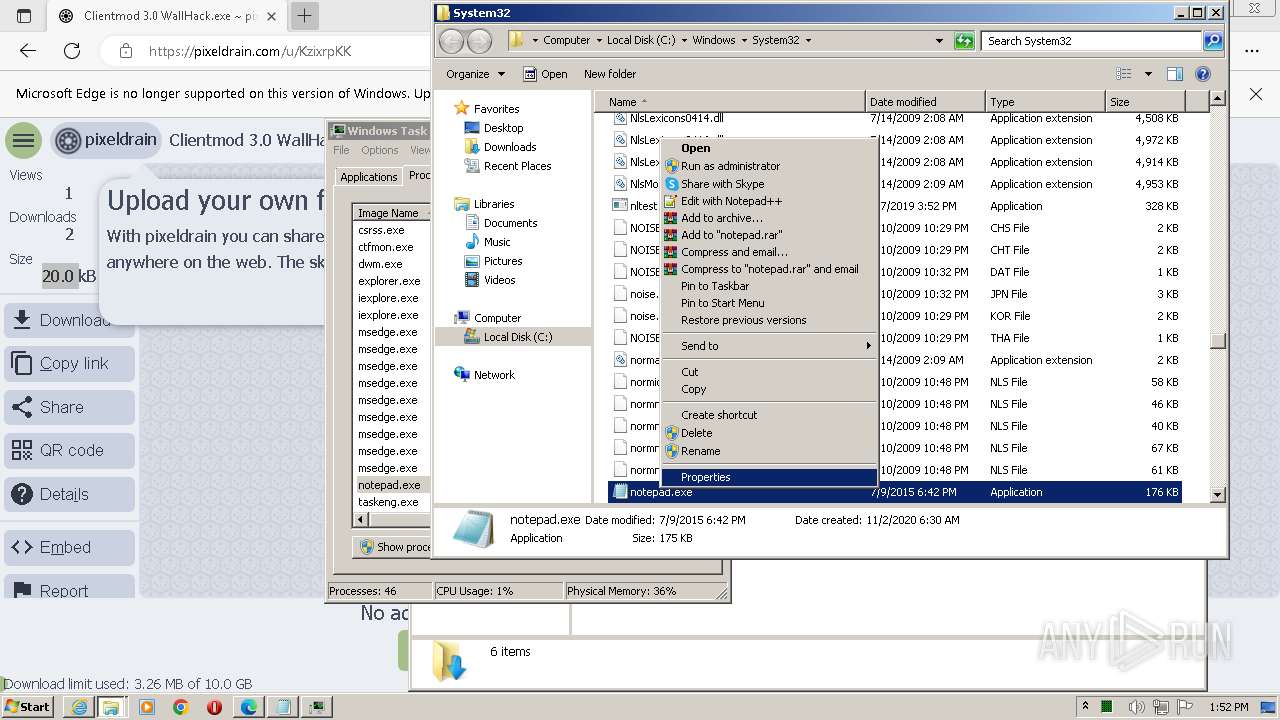
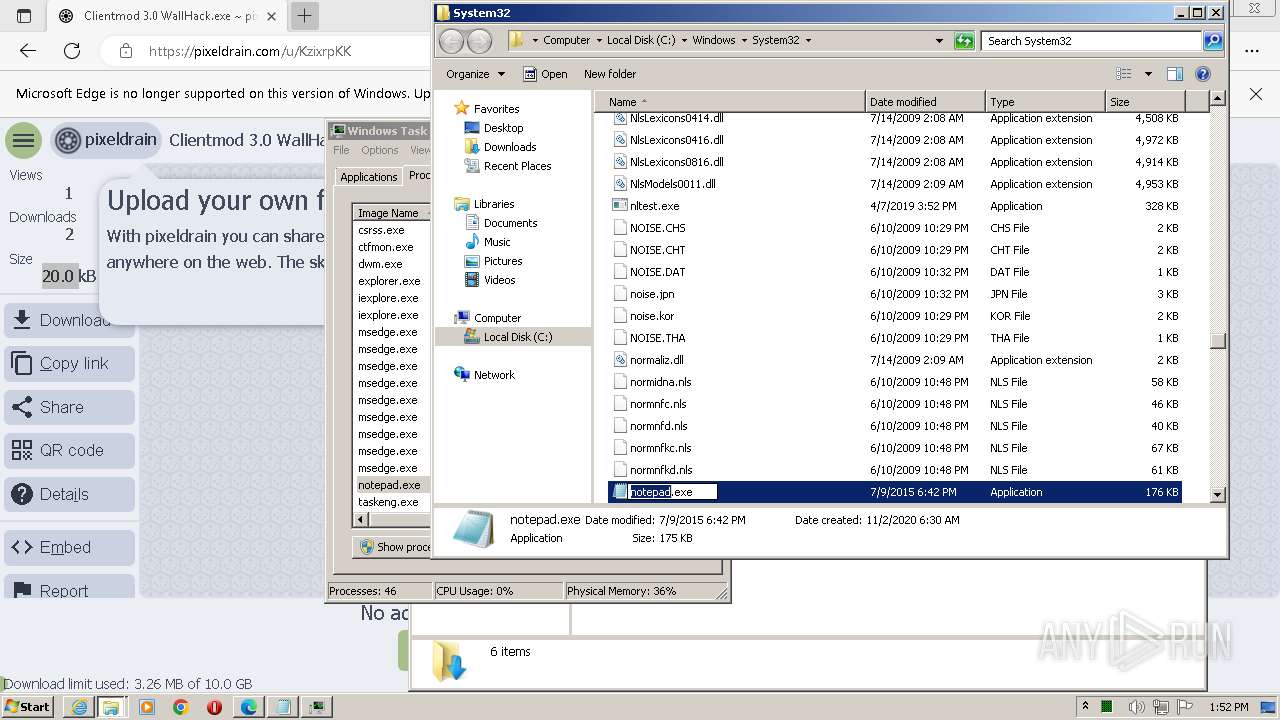
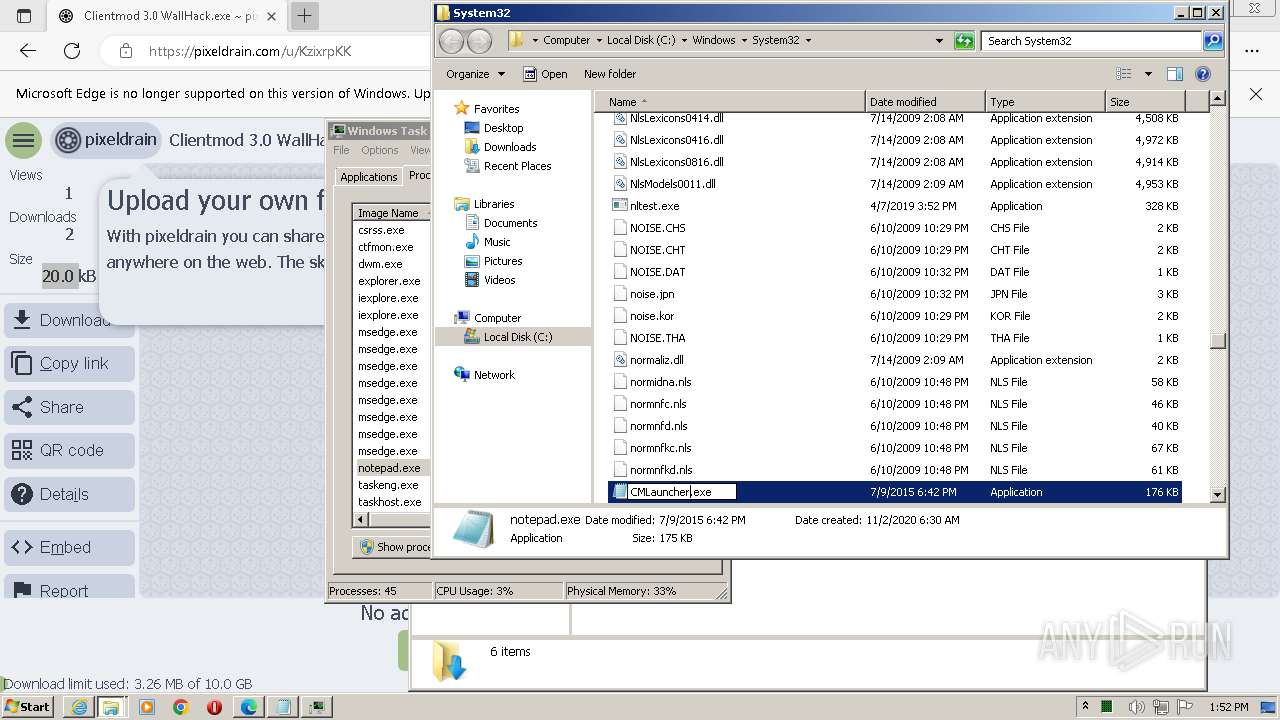
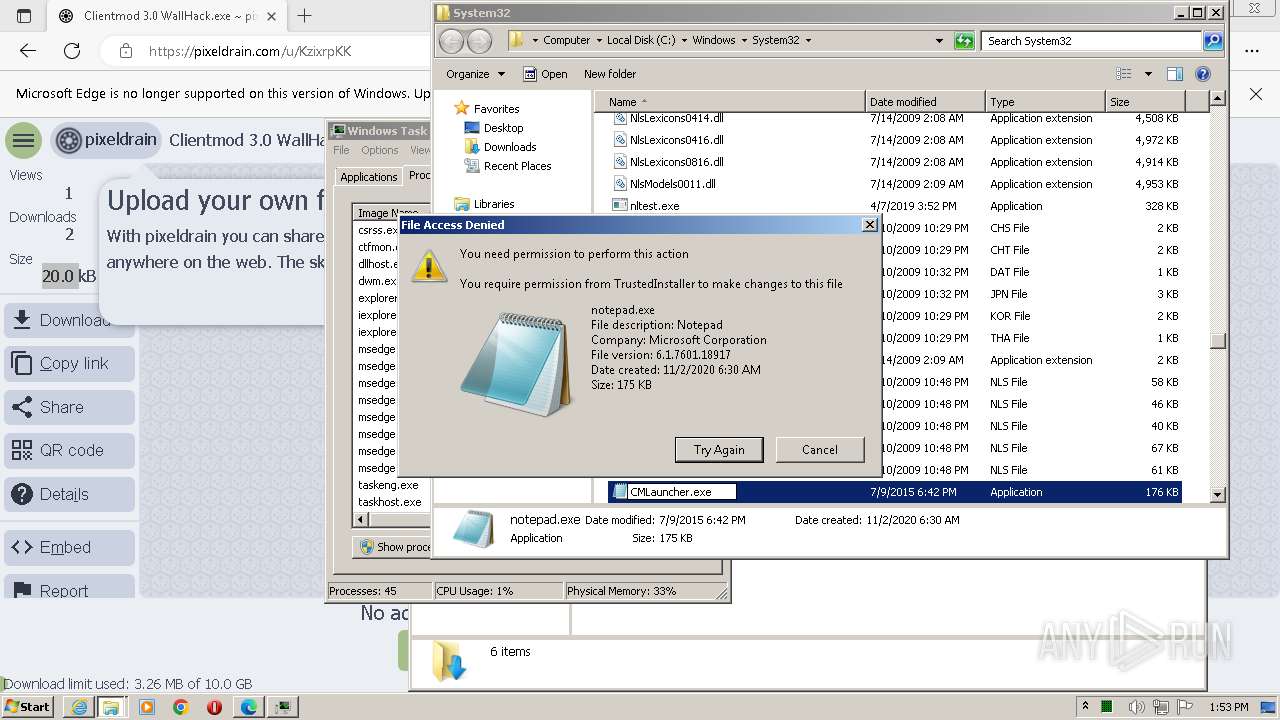
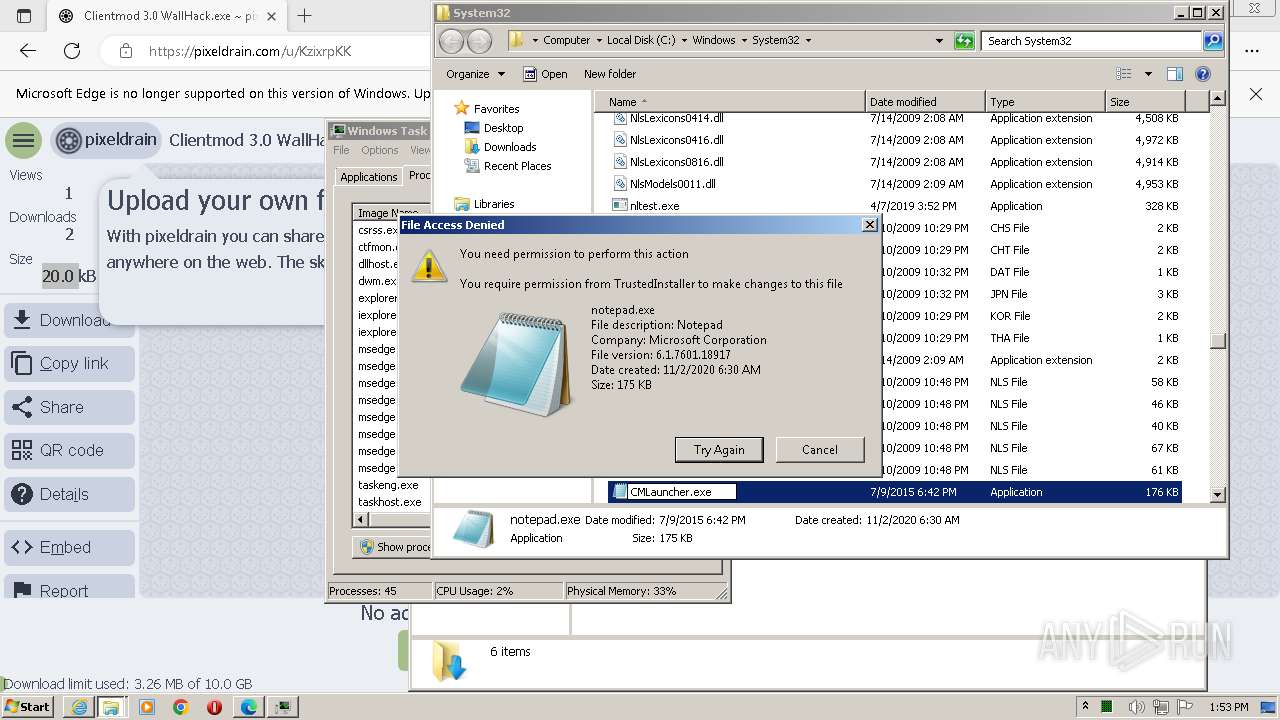
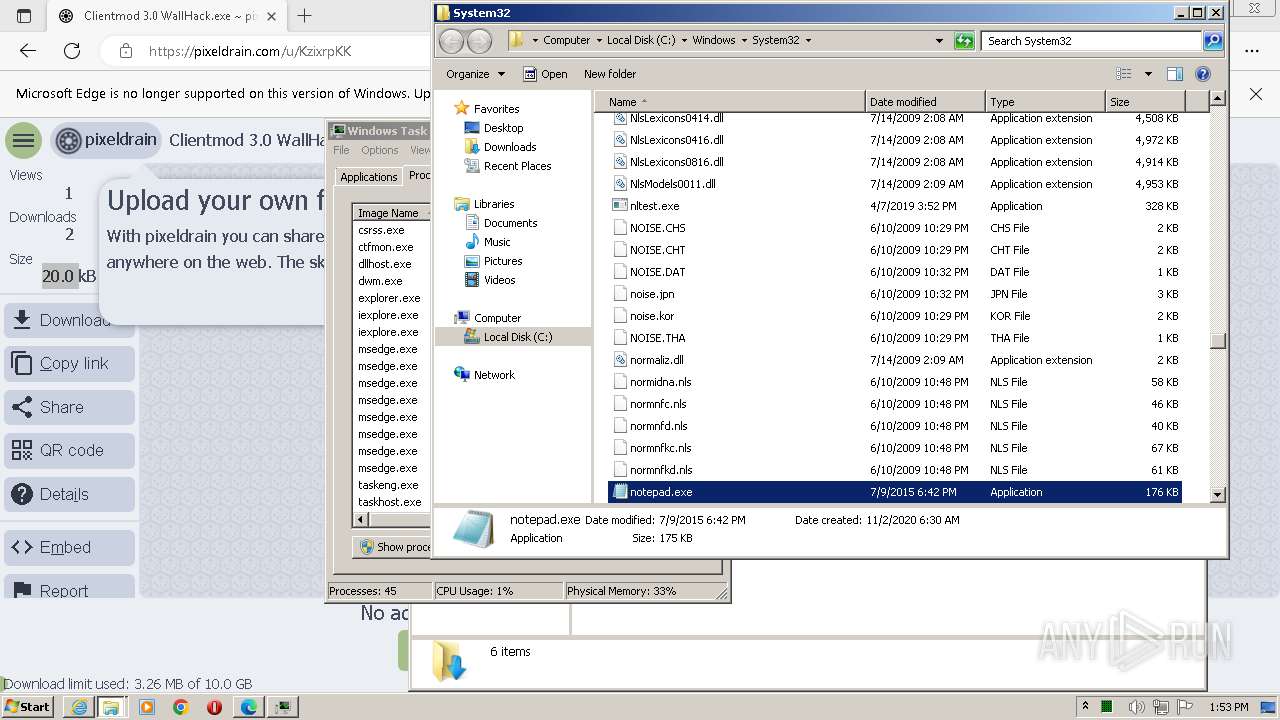
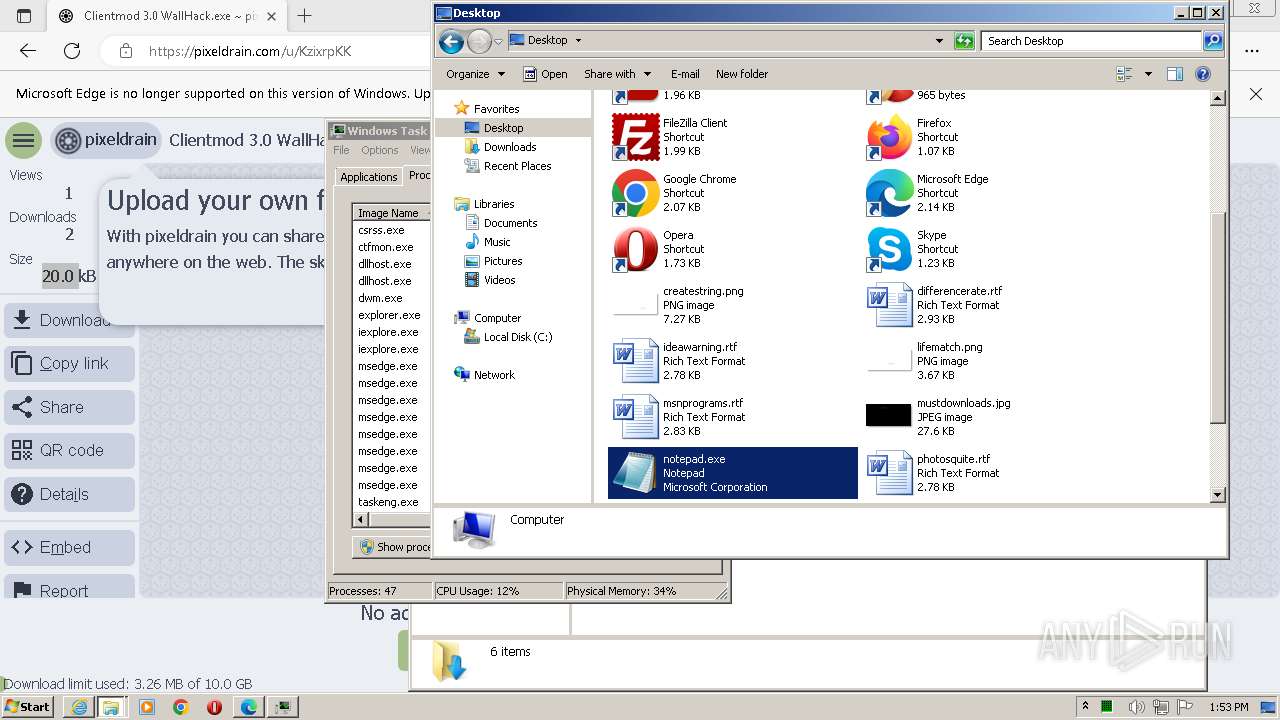
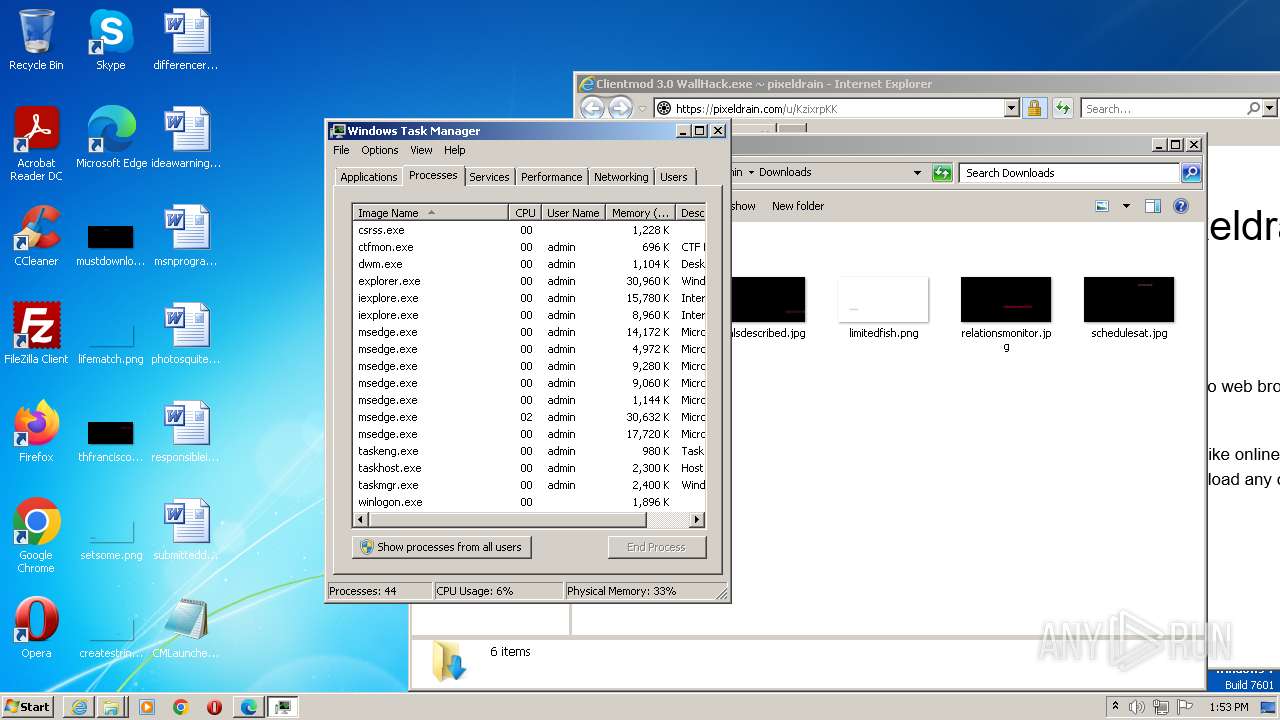
MALICIOUS
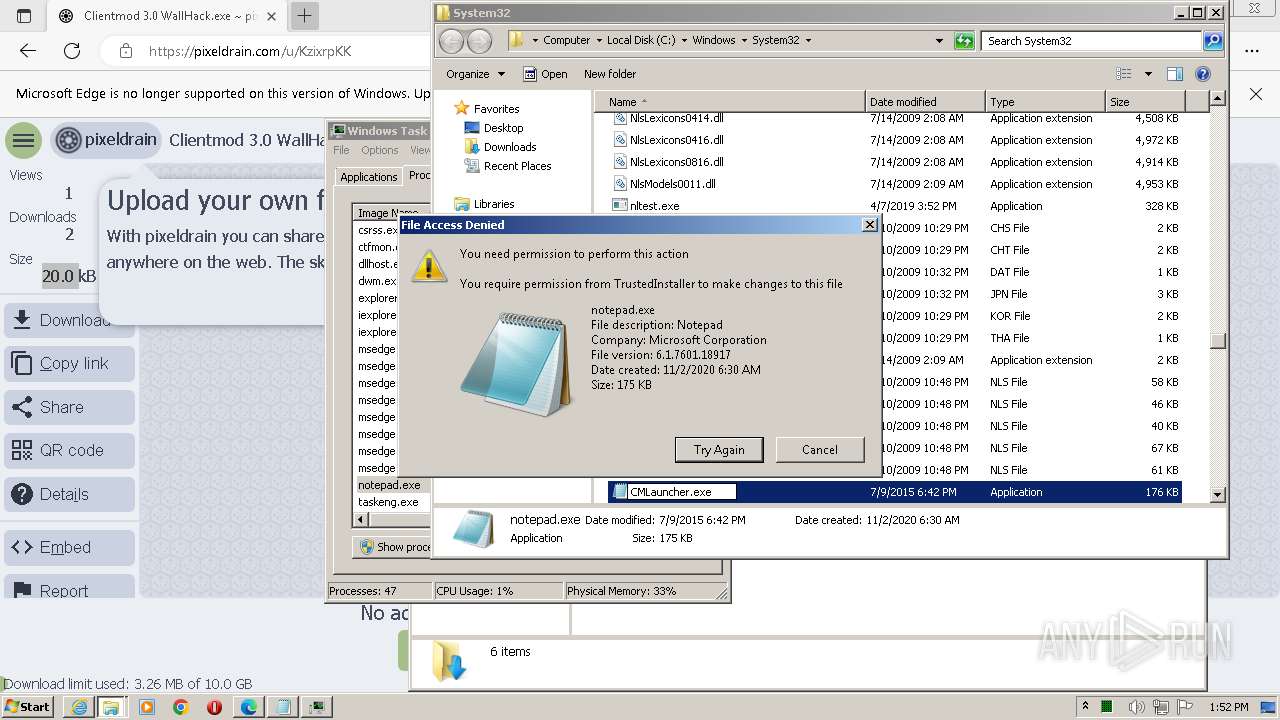
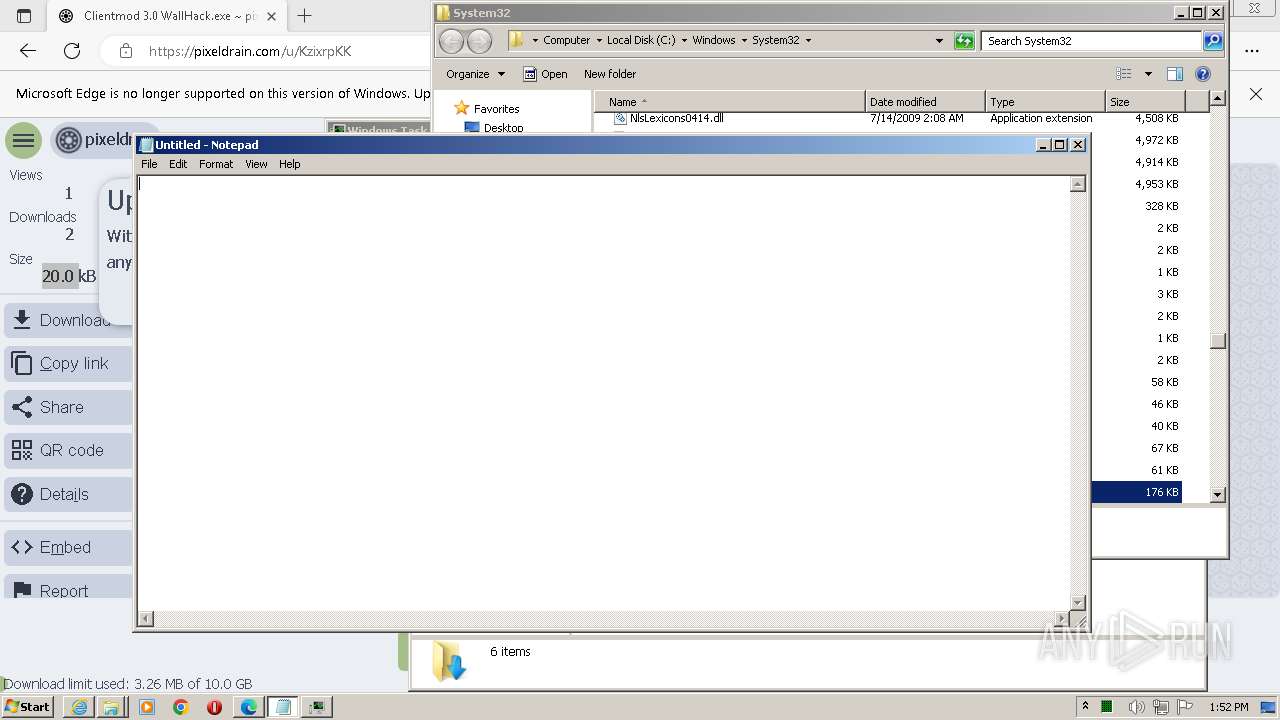
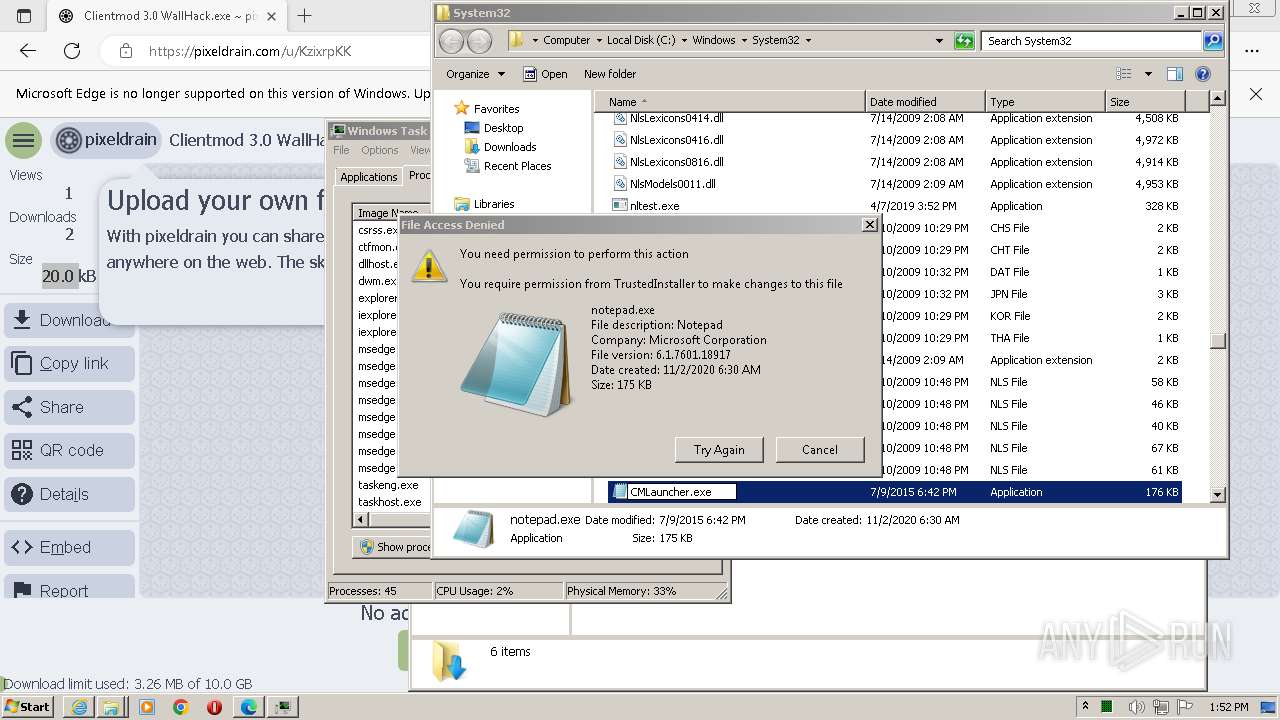
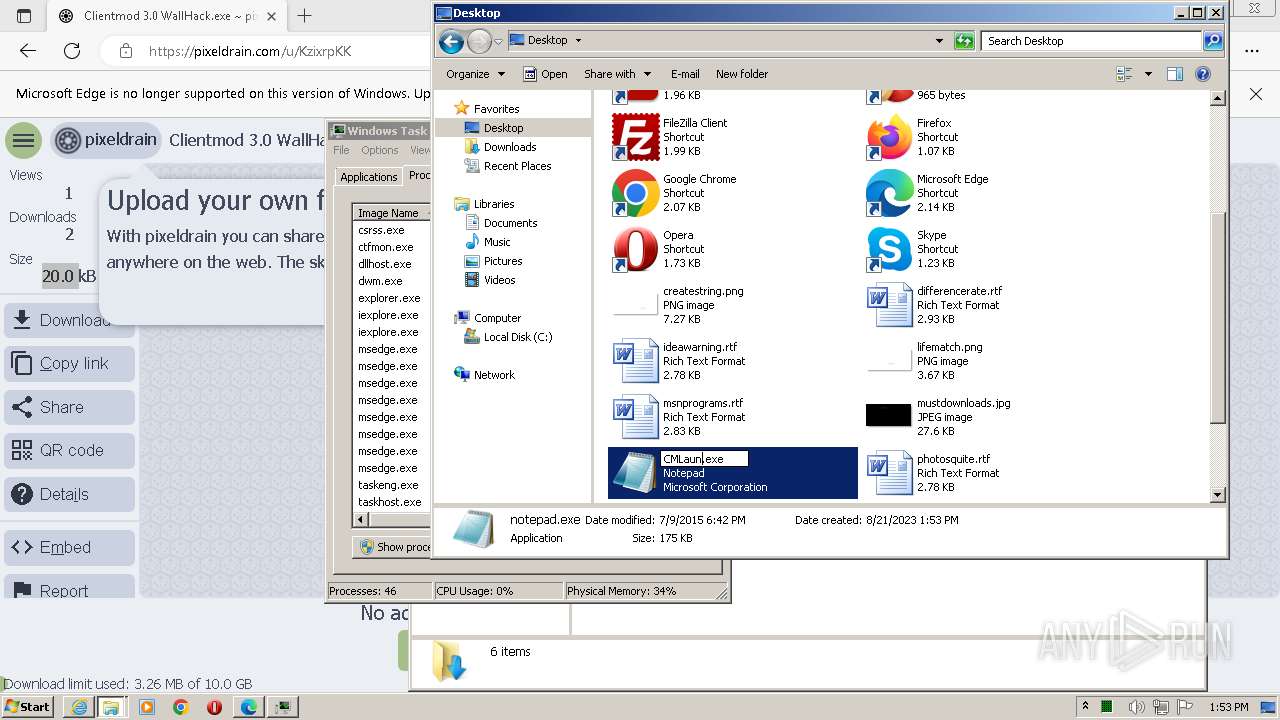
Application was dropped or rewritten from another process
- notepad.exe (PID: 2752)
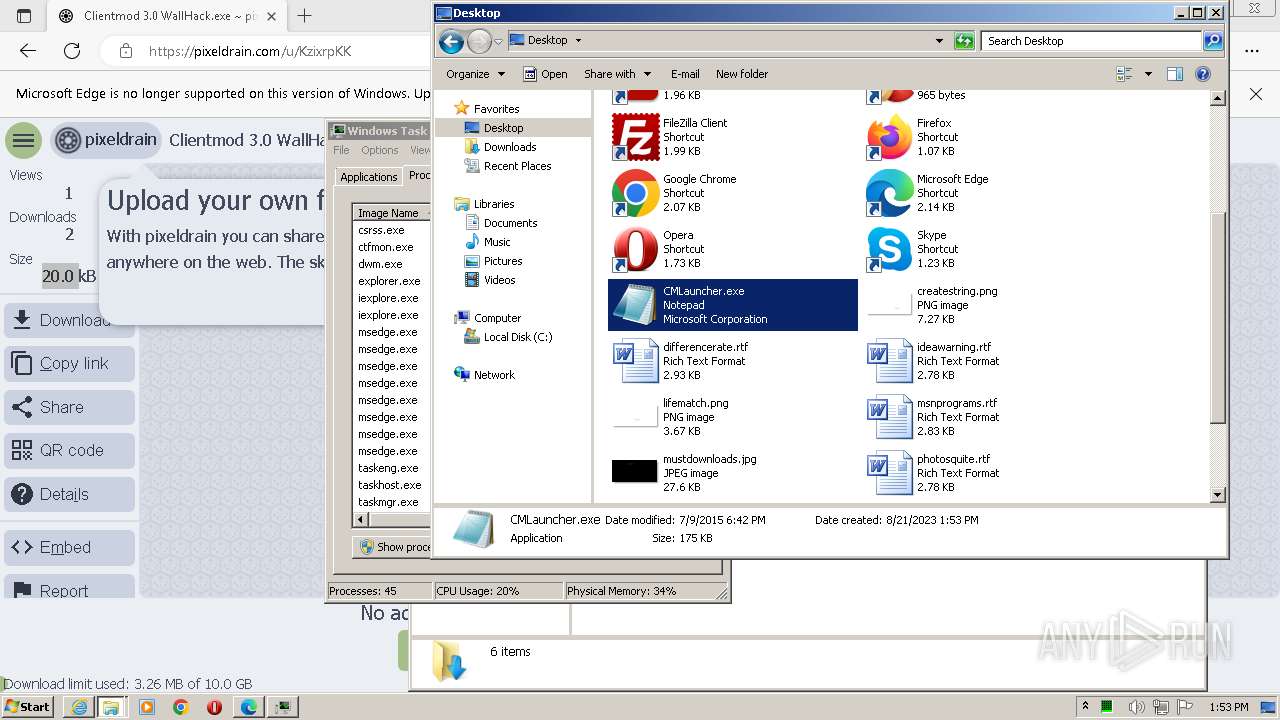
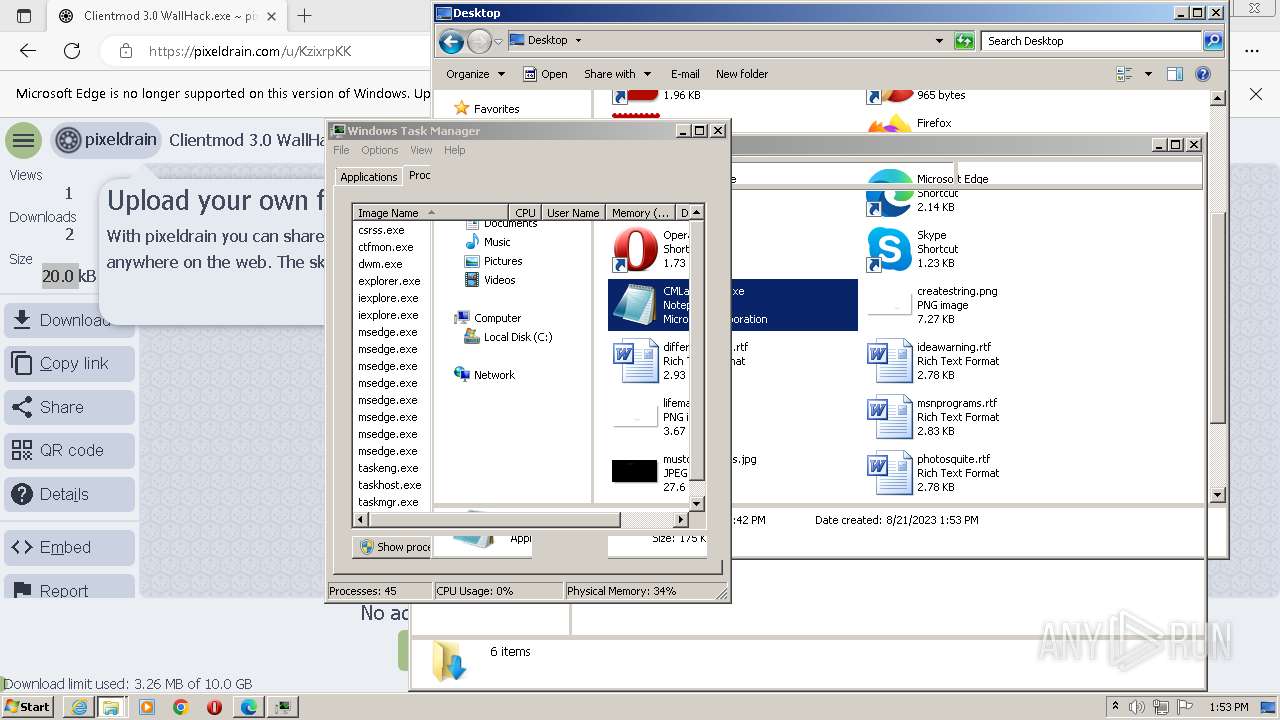
- CMLauncher.exe (PID: 476)
- CMLauncher.exe (PID: 1680)
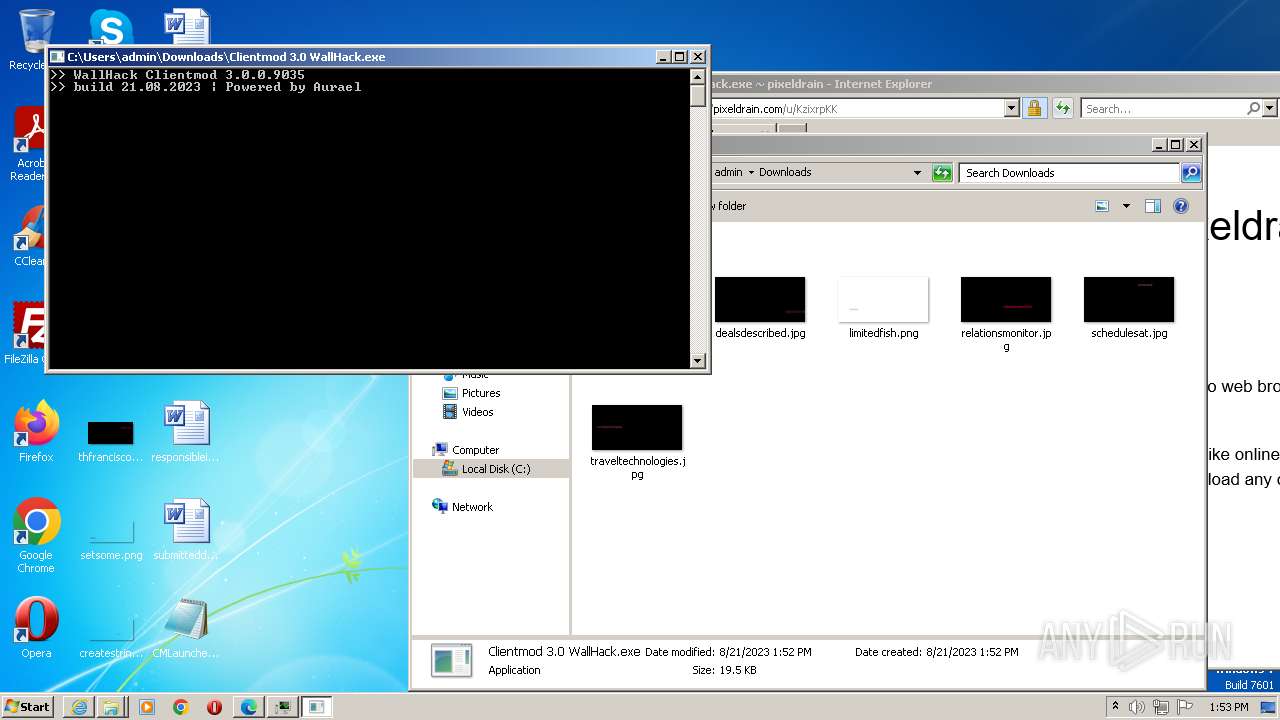
- Clientmod 3.0 WallHack.exe (PID: 2404)
SUSPICIOUS
Reads the Internet Settings
- Clientmod 3.0 WallHack.exe (PID: 2404)
Reads settings of System Certificates
- Clientmod 3.0 WallHack.exe (PID: 2404)
INFO
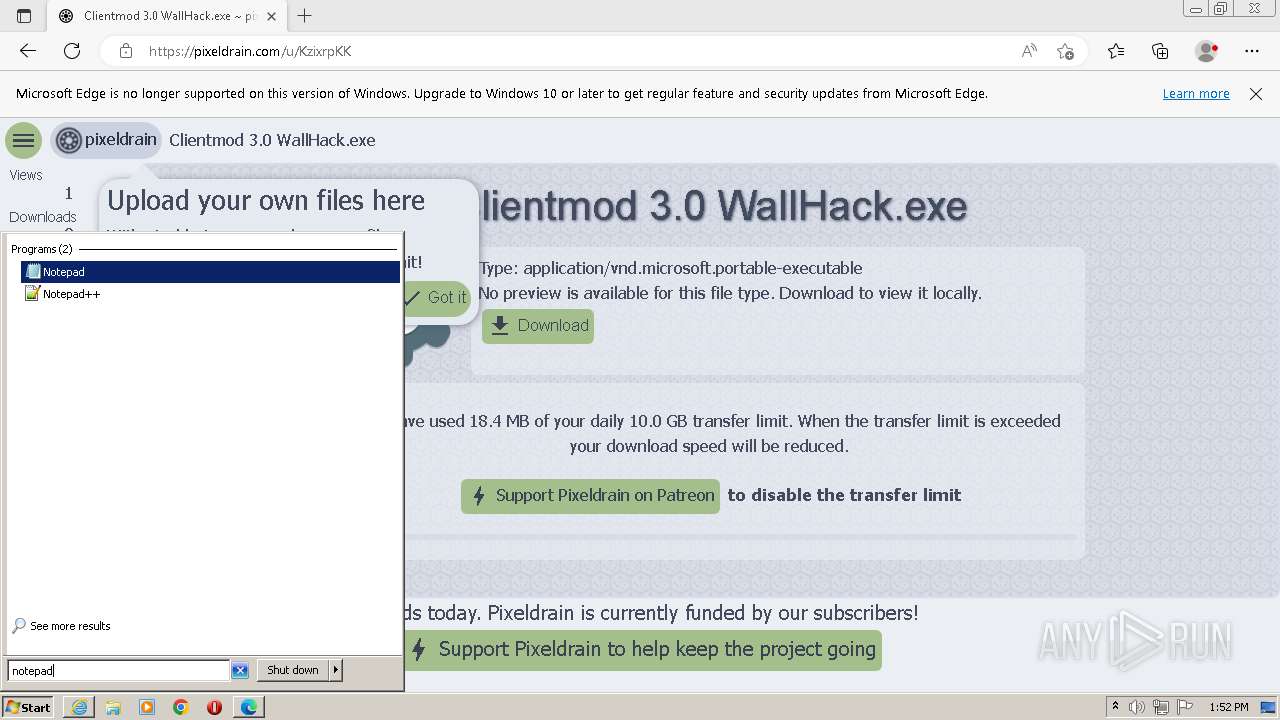
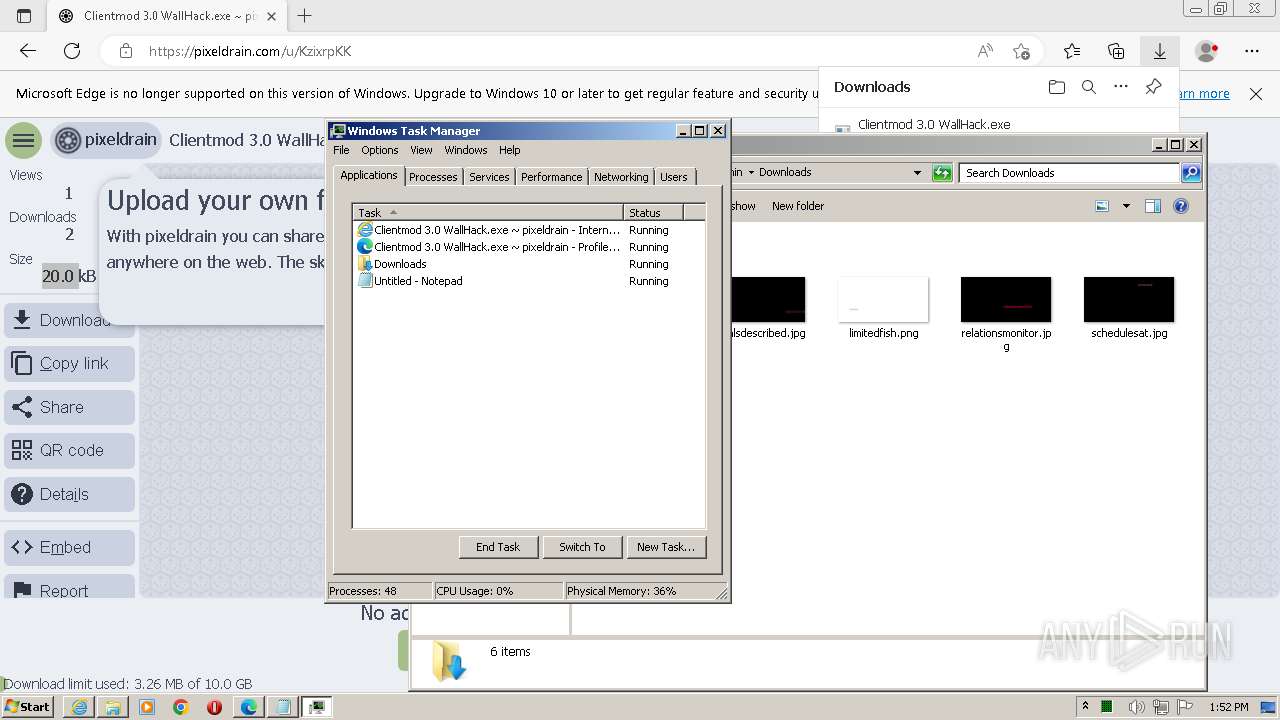
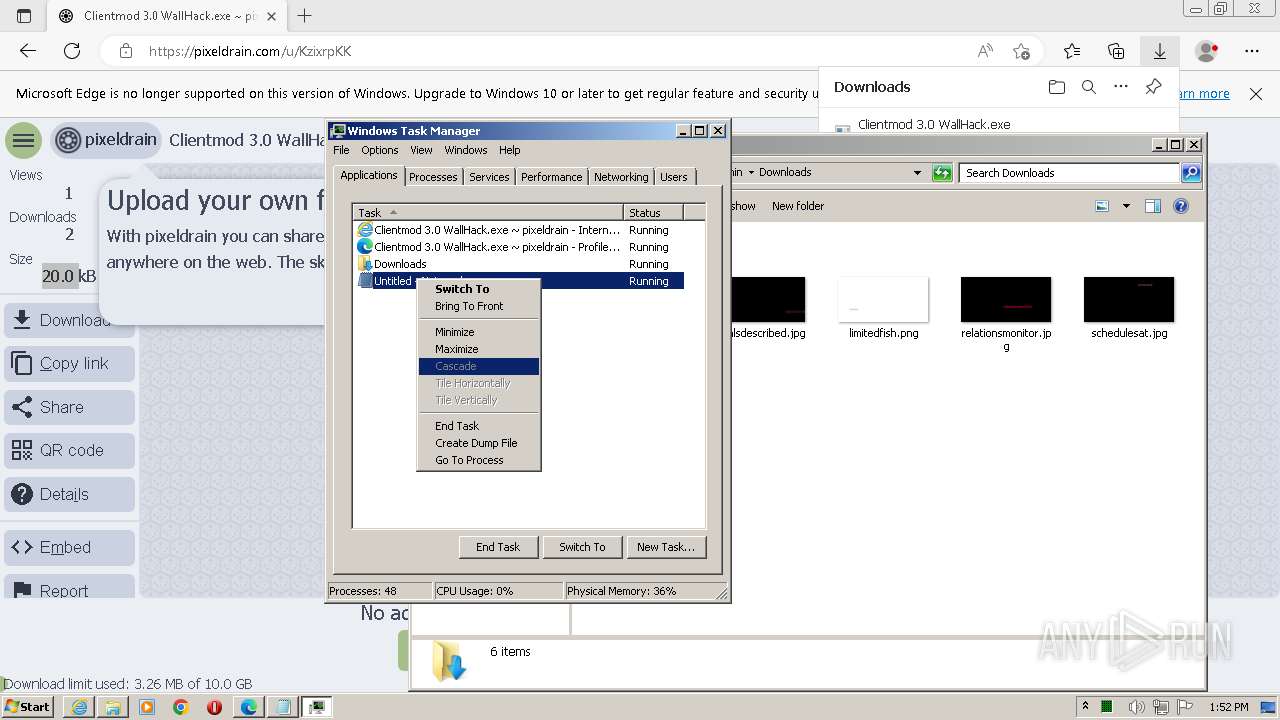
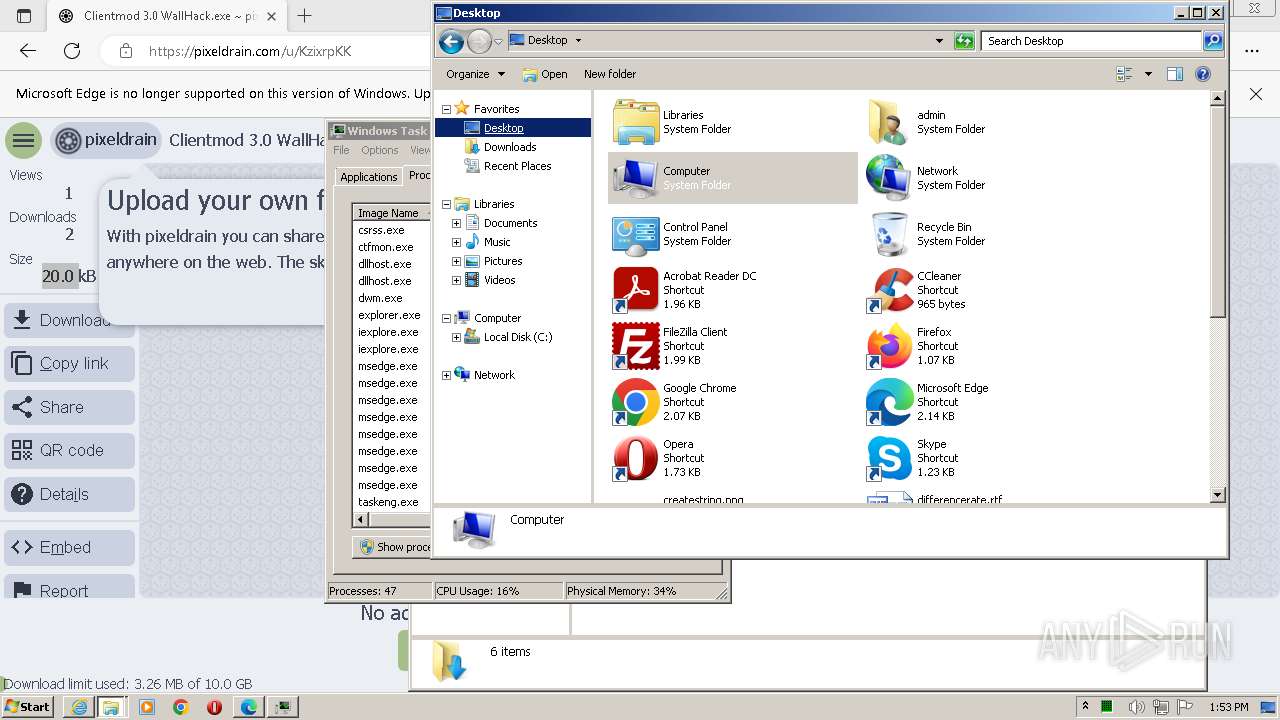
Manual execution by a user
- notepad.exe (PID: 2752)
- taskmgr.exe (PID: 3852)
- msedge.exe (PID: 2436)
- CMLauncher.exe (PID: 476)
- CMLauncher.exe (PID: 1680)
- Clientmod 3.0 WallHack.exe (PID: 2404)
Application launched itself
- msedge.exe (PID: 2436)
- iexplore.exe (PID: 3648)
The process uses the downloaded file
- msedge.exe (PID: 2836)
Executable content was dropped or overwritten
- msedge.exe (PID: 1904)
- msedge.exe (PID: 2436)
Checks supported languages
- CMLauncher.exe (PID: 476)
- CMLauncher.exe (PID: 1680)
- Clientmod 3.0 WallHack.exe (PID: 2404)
Reads the computer name
- Clientmod 3.0 WallHack.exe (PID: 2404)
Reads Environment values
- Clientmod 3.0 WallHack.exe (PID: 2404)
Reads the machine GUID from the registry
- Clientmod 3.0 WallHack.exe (PID: 2404)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
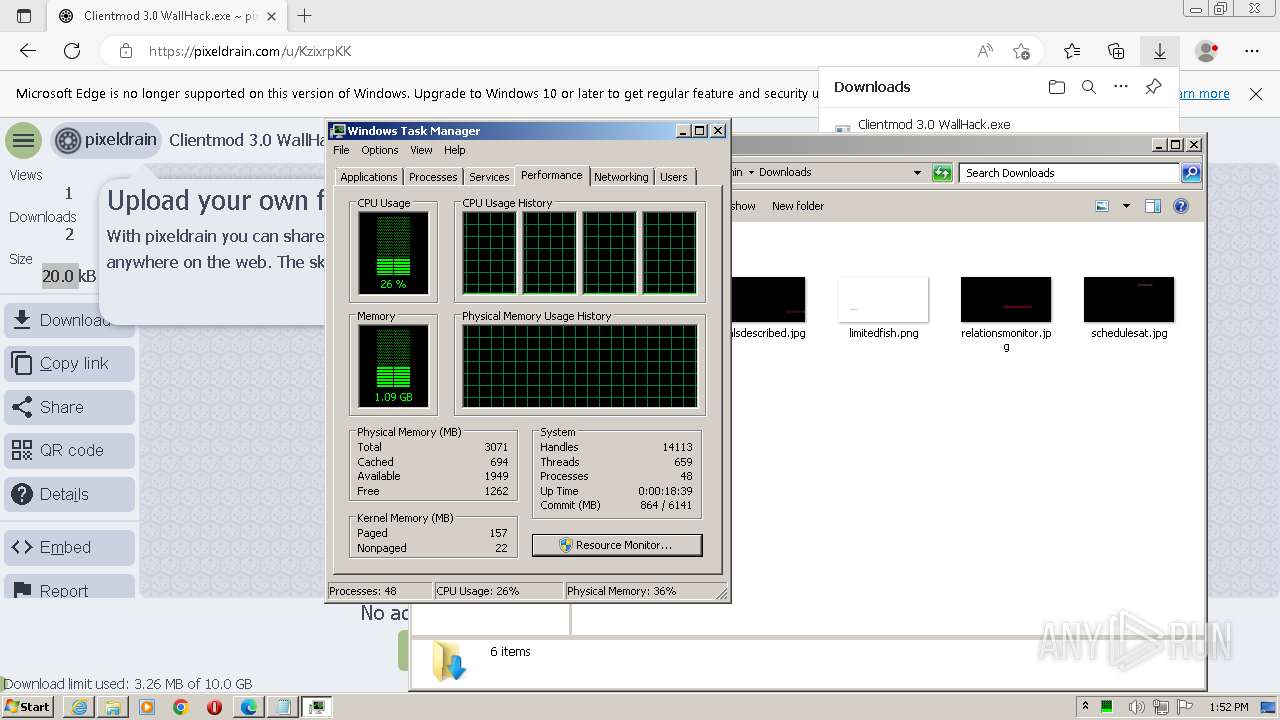
Total processes
84
Monitored processes
35
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 476 | "C:\Users\admin\Desktop\CMLauncher.exe" | C:\Users\admin\Desktop\CMLauncher.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7601.18917 (win7sp1_gdr.150709-0600) Modules
| |||||||||||||||
| 596 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1076 --field-trial-handle=1364,i,4149434420465254521,2591707302532421346,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 756 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1084 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4420 --field-trial-handle=1364,i,4149434420465254521,2591707302532421346,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1084 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4748 --field-trial-handle=1364,i,4149434420465254521,2591707302532421346,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1184 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4024 --field-trial-handle=1364,i,4149434420465254521,2591707302532421346,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1680 | "C:\Users\admin\Desktop\CMLauncher.exe" | C:\Users\admin\Desktop\CMLauncher.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7601.18917 (win7sp1_gdr.150709-0600) Modules
| |||||||||||||||
| 1736 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4496 --field-trial-handle=1364,i,4149434420465254521,2591707302532421346,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1820 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=1628 --field-trial-handle=1364,i,4149434420465254521,2591707302532421346,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1904 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1320 --field-trial-handle=1364,i,4149434420465254521,2591707302532421346,131072 /prefetch:3 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
25 081
Read events
24 972
Write events
106
Delete events
3
Modification events
| (PID) Process: | (3648) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (3648) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (3648) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (3648) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3648) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3648) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3648) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3648) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3648) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3648) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
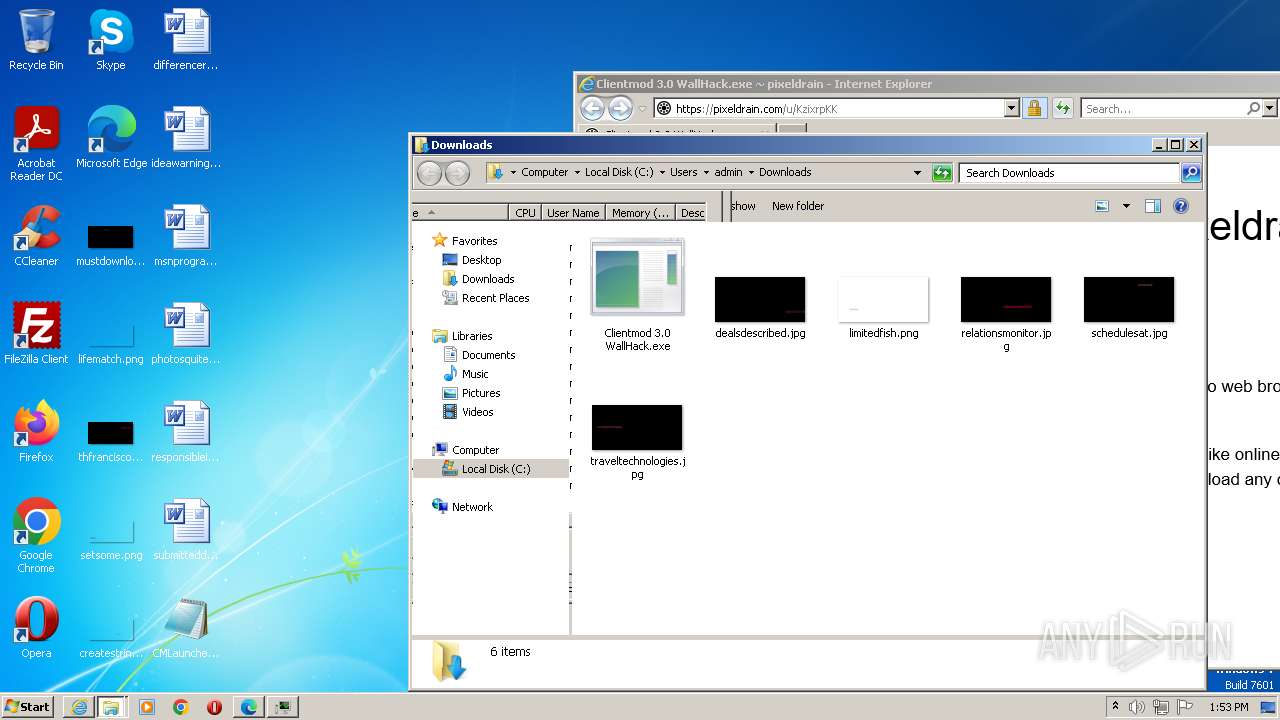
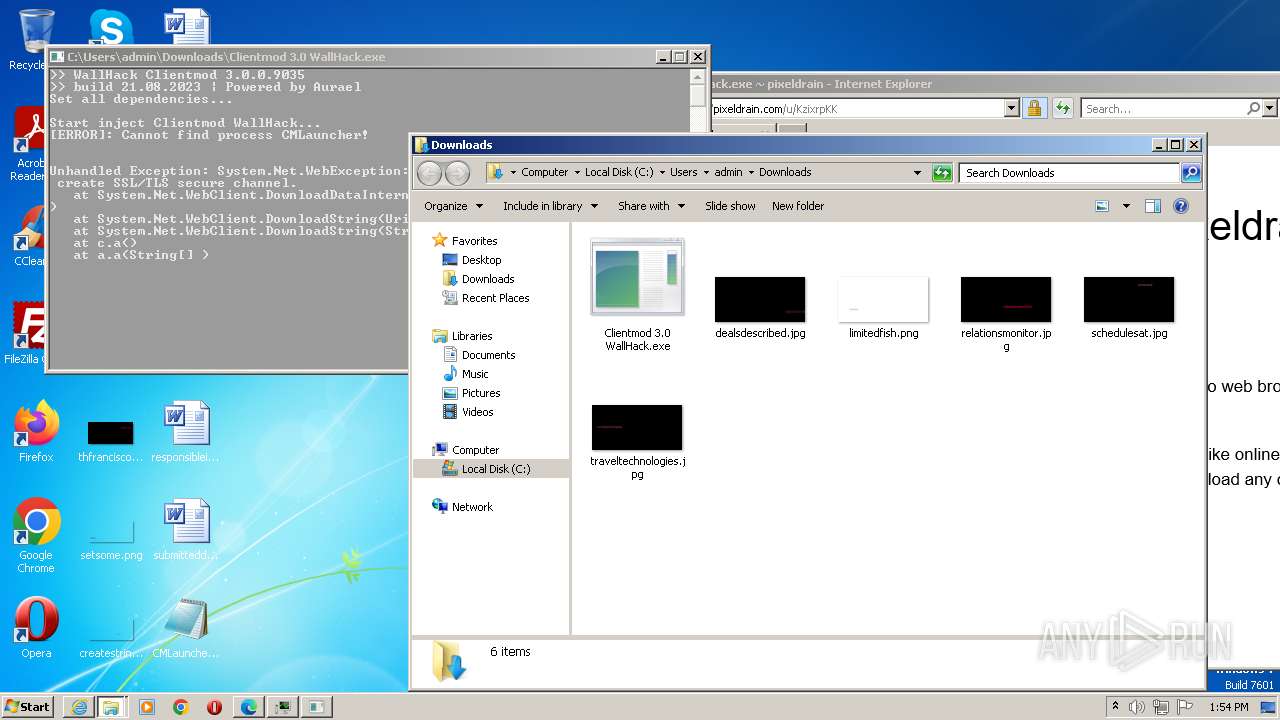
Executable files
4
Suspicious files
1 198
Text files
213
Unknown types
15
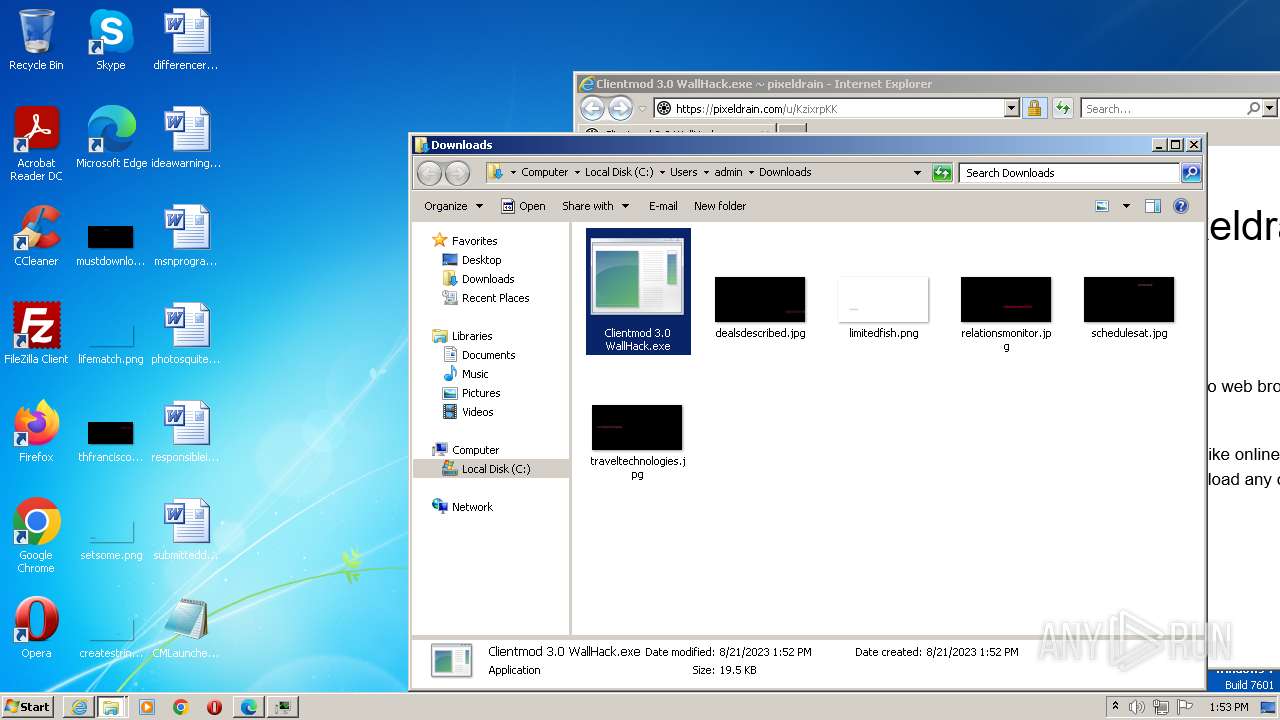
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3648 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:A6CEB7511594BF1E07DB70B349C8F379 | SHA256:4653DECACF2690013911660CADCC063C9C0AF4BE0F89DE063DF13A8644684E3B | |||
| 3648 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 2332 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:3AC860860707BAAF32469FA7CC7C0192 | SHA256:D015145D551ECD14916270EFAD773BBC9FD57FAD2228D2C24559F696C961D904 | |||
| 2332 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabC74E.tmp | compressed | |
MD5:3AC860860707BAAF32469FA7CC7C0192 | SHA256:D015145D551ECD14916270EFAD773BBC9FD57FAD2228D2C24559F696C961D904 | |||
| 3648 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:9397CB722DAF81E15B1AF946D5D1DAC2 | SHA256:8C6F80D8DA1EC337D7649C174EEF10DACF9E9851267610611E4C0BE6C8D0DA3F | |||
| 3648 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 2332 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\KzixrpKK[1].htm | html | |
MD5:0BBE59814BACA9D5E7C762F668A3F92A | SHA256:02F4281FC6604D9824186E27CB98C2E282405A4BA6DFCDF5597EC8AD877719B6 | |||
| 3648 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:13586A648B0E997DD419742BEB10BF26 | SHA256:61D827144E40D4640F9CAEC85A4BB942E4F6833E83C65566025CF7D7709956F1 | |||
| 2332 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EA4A96F1C1A0D885D47206DD5B00943F | der | |
MD5:1CC308A1A1C47CF89AAF9F14F6F89E5E | SHA256:AABFC9FA324FE729ECD9414E5314352AAE607A2B7A12659765B0BA007E3141E0 | |||
| 2332 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | der | |
MD5:60FE01DF86BE2E5331B0CDBE86165686 | SHA256:C08CCBC876CD5A7CDFA9670F9637DA57F6A1282198A9BC71FC7D7247A6E5B7A8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
59
DNS requests
90
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3648 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | US | binary | 471 b | whitelisted |
868 | svchost.exe | GET | — | 209.197.3.8:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/aa819b28-c504-459e-9144-7f691befc78a?P1=1693003679&P2=404&P3=2&P4=mUHJqPz%2fN%2b3TPB3bV83eRXS9tcoueq2Tud5FUTf5sVlXjj%2fJho%2bjTr0yp3fmacj07A6SDv1EwXK73Pbdyv57rw%3d%3d | US | — | — | whitelisted |
868 | svchost.exe | GET | — | 209.197.3.8:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/aa819b28-c504-459e-9144-7f691befc78a?P1=1693003679&P2=404&P3=2&P4=mUHJqPz%2fN%2b3TPB3bV83eRXS9tcoueq2Tud5FUTf5sVlXjj%2fJho%2bjTr0yp3fmacj07A6SDv1EwXK73Pbdyv57rw%3d%3d | US | — | — | whitelisted |
868 | svchost.exe | GET | — | 209.197.3.8:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/aa819b28-c504-459e-9144-7f691befc78a?P1=1693003679&P2=404&P3=2&P4=mUHJqPz%2fN%2b3TPB3bV83eRXS9tcoueq2Tud5FUTf5sVlXjj%2fJho%2bjTr0yp3fmacj07A6SDv1EwXK73Pbdyv57rw%3d%3d | US | — | — | whitelisted |
868 | svchost.exe | HEAD | 200 | 209.197.3.8:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ec243c2e-e29f-46d6-92ef-c60f8cfa76e0?P1=1693003677&P2=404&P3=2&P4=Ut%2f6Ly0tT8I5WiVK34et83D9C8%2fqOcuqyief0Mw1jUExF0dBaWOlnKmNm7%2fykVMIHkEktFZMua8NdU05AS5dNg%3d%3d | US | — | 3.44 Kb | whitelisted |
868 | svchost.exe | GET | — | 209.197.3.8:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ec243c2e-e29f-46d6-92ef-c60f8cfa76e0?P1=1693003677&P2=404&P3=2&P4=Ut%2f6Ly0tT8I5WiVK34et83D9C8%2fqOcuqyief0Mw1jUExF0dBaWOlnKmNm7%2fykVMIHkEktFZMua8NdU05AS5dNg%3d%3d | US | — | — | whitelisted |
868 | svchost.exe | GET | — | 209.197.3.8:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ec243c2e-e29f-46d6-92ef-c60f8cfa76e0?P1=1693003677&P2=404&P3=2&P4=Ut%2f6Ly0tT8I5WiVK34et83D9C8%2fqOcuqyief0Mw1jUExF0dBaWOlnKmNm7%2fykVMIHkEktFZMua8NdU05AS5dNg%3d%3d | US | — | — | whitelisted |
868 | svchost.exe | GET | 206 | 209.197.3.8:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ec243c2e-e29f-46d6-92ef-c60f8cfa76e0?P1=1693003677&P2=404&P3=2&P4=Ut%2f6Ly0tT8I5WiVK34et83D9C8%2fqOcuqyief0Mw1jUExF0dBaWOlnKmNm7%2fykVMIHkEktFZMua8NdU05AS5dNg%3d%3d | US | binary | 83.2 Kb | whitelisted |
868 | svchost.exe | GET | 206 | 209.197.3.8:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ec243c2e-e29f-46d6-92ef-c60f8cfa76e0?P1=1693003677&P2=404&P3=2&P4=Ut%2f6Ly0tT8I5WiVK34et83D9C8%2fqOcuqyief0Mw1jUExF0dBaWOlnKmNm7%2fykVMIHkEktFZMua8NdU05AS5dNg%3d%3d | US | binary | 13.2 Kb | whitelisted |
868 | svchost.exe | GET | — | 209.197.3.8:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ec243c2e-e29f-46d6-92ef-c60f8cfa76e0?P1=1693003677&P2=404&P3=2&P4=Ut%2f6Ly0tT8I5WiVK34et83D9C8%2fqOcuqyief0Mw1jUExF0dBaWOlnKmNm7%2fykVMIHkEktFZMua8NdU05AS5dNg%3d%3d | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2332 | iexplore.exe | 50.7.24.66:443 | pixeldrain.com | COGENT-174 | NL | suspicious |
2332 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3648 | iexplore.exe | 184.86.251.30:443 | www.bing.com | Akamai International B.V. | DE | suspicious |
3648 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3648 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
2332 | iexplore.exe | 23.206.95.234:80 | x1.c.lencr.org | AKAMAI-AS | NL | unknown |
3648 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
2332 | iexplore.exe | 95.101.54.131:80 | r3.o.lencr.org | Akamai International B.V. | DE | suspicious |
2332 | iexplore.exe | 78.47.86.208:443 | stats.pixeldrain.com | Hetzner Online GmbH | DE | unknown |
2332 | iexplore.exe | 95.101.54.114:80 | r3.o.lencr.org | Akamai International B.V. | DE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pixeldrain.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
stats.pixeldrain.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1088 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |