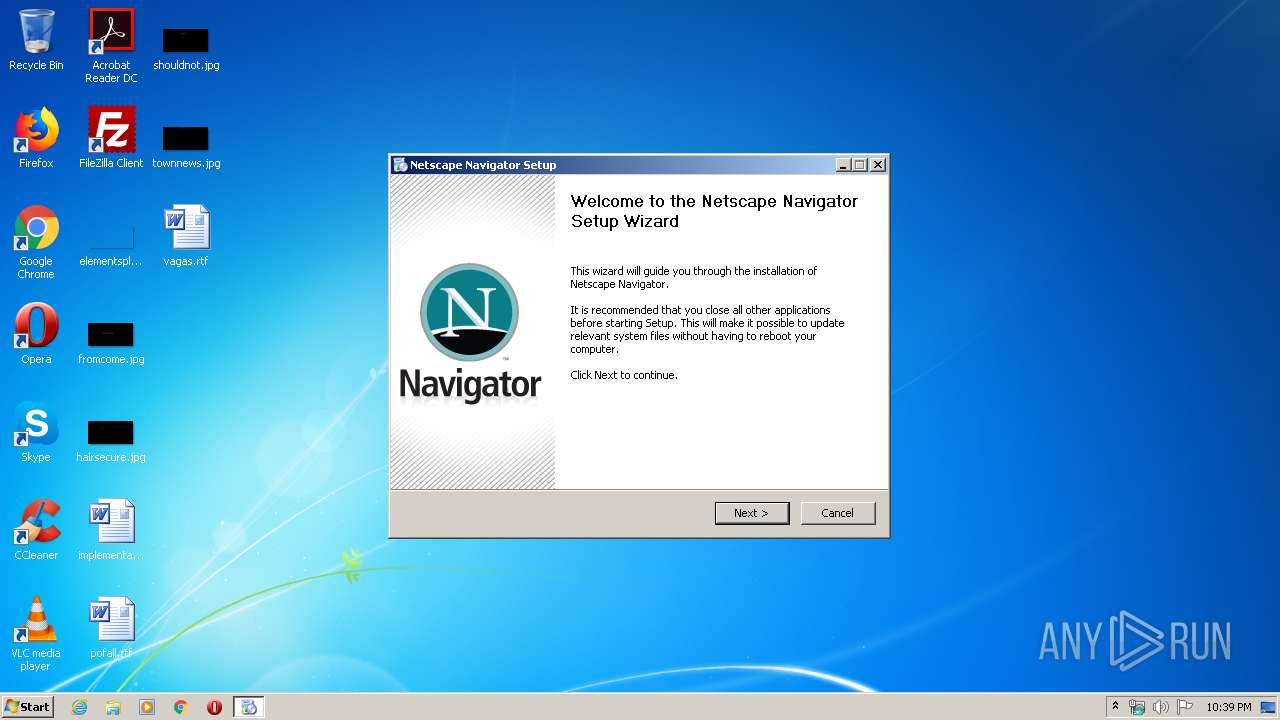
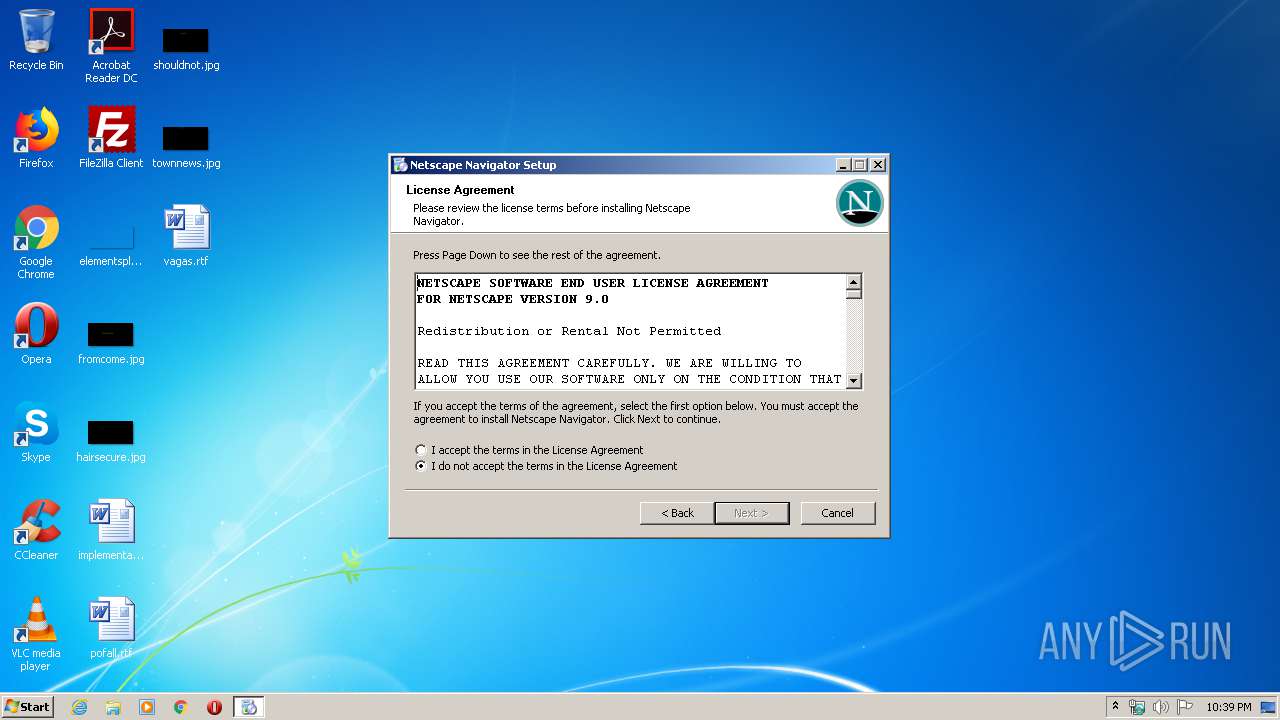
| File name: | netscape-navigator-9.0.0.6.exe |
| Full analysis: | https://app.any.run/tasks/54325448-dd70-4c68-96e1-0e19655a4936 |
| Verdict: | Malicious activity |
| Analysis date: | May 23, 2020, 21:39:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 6BE00105F6D010D99EFCC09B1AB180CB |
| SHA1: | B894014187511C79EDEB9AF19A7C3842E15E7A95 |
| SHA256: | F6CD7352D96FA8C8668E4F77751CF748212C237436B9B02F808190CF26A59FE7 |
| SSDEEP: | 98304:nk7sW4osyvzR6QCkHuGDBXpT8Y3RaZ8OnvDm016wOXxVlyXvB6ptIT0DcaF6Fz:kN4ojvzkQC6lphEZnnbz1XOXkXZ6dF6J |
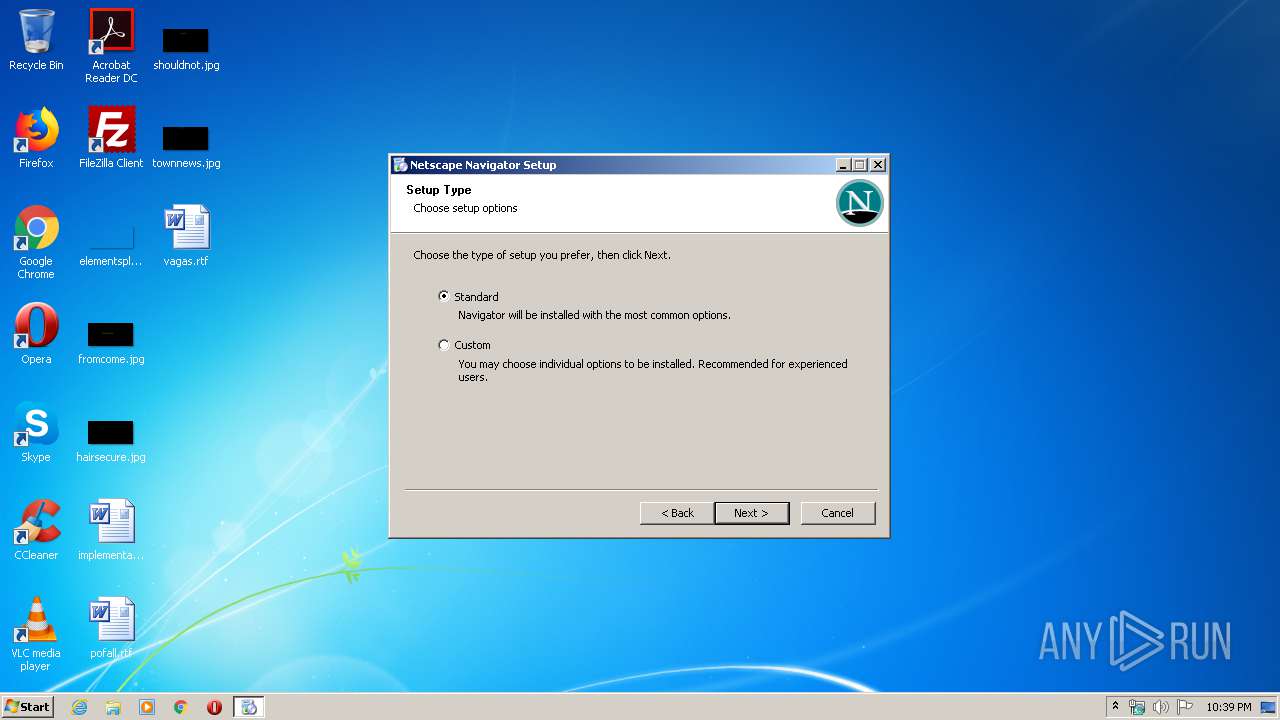
MALICIOUS
Actions looks like stealing of personal data
- netscape-navigator-9.0.0.6.exe (PID: 1468)
- setup.exe (PID: 1444)
Application was dropped or rewritten from another process
- setup.exe (PID: 1444)
Loads dropped or rewritten executable
- setup.exe (PID: 1444)
SUSPICIOUS
Executable content was dropped or overwritten
- netscape-navigator-9.0.0.6.exe (PID: 1468)
- setup.exe (PID: 1444)
Creates COM task schedule object
- setup.exe (PID: 1444)
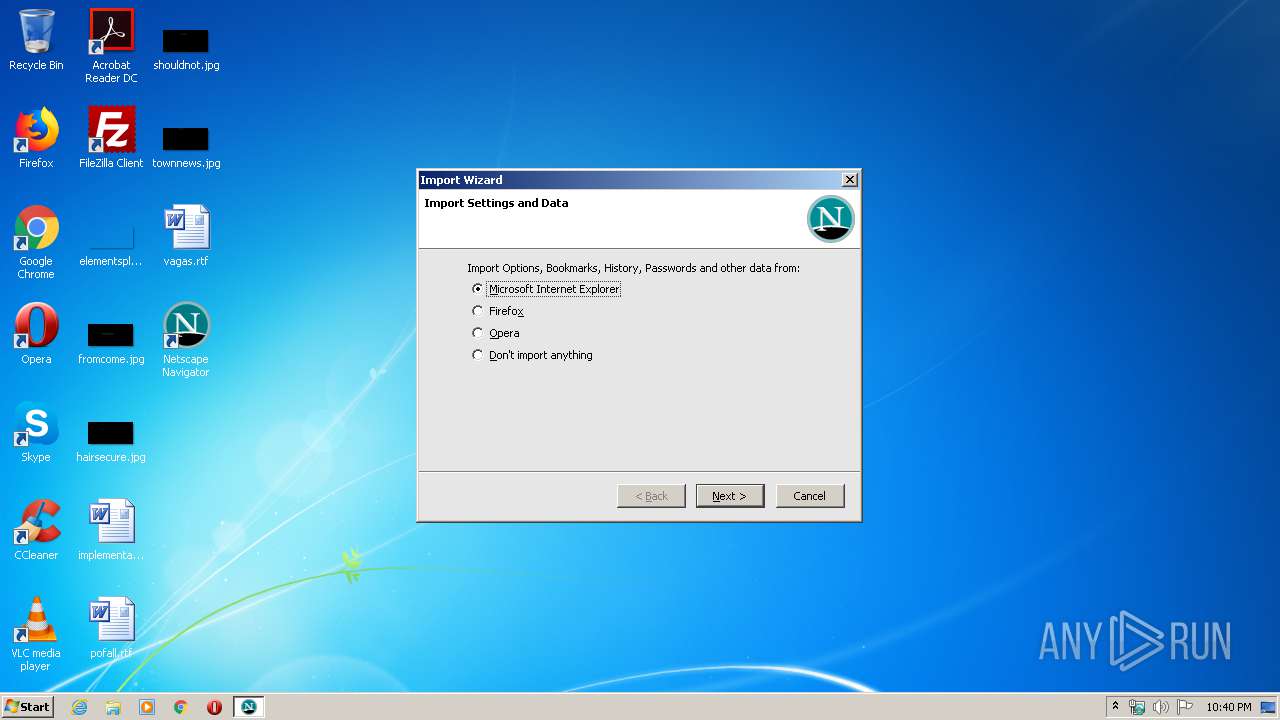
Searches for installed software
- setup.exe (PID: 1444)
Modifies the open verb of a shell class
- setup.exe (PID: 1444)
Creates files in the user directory
- setup.exe (PID: 1444)
Creates a software uninstall entry
- setup.exe (PID: 1444)
Creates files in the program directory
- setup.exe (PID: 1444)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (28.6) |
|---|---|---|
| .exe | | | UPX compressed Win32 Executable (28) |
| .exe | | | Win32 EXE Yoda's Crypter (27.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (6.8) |
| .exe | | | Win32 Executable (generic) (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2006:08:16 00:27:50+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 40960 |
| InitializedDataSize: | 28672 |
| UninitializedDataSize: | 94208 |
| EntryPoint: | 0x21cf0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.42.0.0 |
| ProductVersionNumber: | 4.42.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Mozilla |
| FileDescription: | Firefox |
| FileVersion: | 4.42 |
| InternalName: | 7zS.sfx |
| LegalCopyright: | Mozilla |
| OriginalFileName: | 7zS.sfx.exe |
| ProductName: | Firefox |
| ProductVersion: | 4.42 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Aug-2006 22:27:50 |
| Detected languages: |
|
| CompanyName: | Mozilla |
| FileDescription: | Firefox |
| FileVersion: | 4.42 |
| InternalName: | 7zS.sfx |
| LegalCopyright: | Mozilla |
| OriginalFilename: | 7zS.sfx.exe |
| ProductName: | Firefox |
| ProductVersion: | 4.42 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 15-Aug-2006 22:27:50 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00017000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00018000 | 0x0000A000 | 0x0000A000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.88047 |
.rsrc | 0x00022000 | 0x00007000 | 0x00006A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.77109 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.25849 | 628 | UNKNOWN | English - United States | RT_VERSION |
2 | 3.89724 | 744 | UNKNOWN | English - United States | RT_ICON |
3 | 3.68656 | 1640 | UNKNOWN | English - United States | RT_ICON |
4 | 5.62942 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 5.50813 | 52 | UNKNOWN | English - United States | RT_STRING |
6 | 6.5168 | 3752 | UNKNOWN | English - United States | RT_ICON |
7 | 6.07002 | 1128 | UNKNOWN | English - United States | RT_ICON |
8 | 5.6303 | 4264 | UNKNOWN | English - United States | RT_ICON |
9 | 5.12163 | 9640 | UNKNOWN | English - United States | RT_ICON |
159 | 2.89097 | 132 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
COMCTL32.dll |
KERNEL32.DLL |
MSVCRT.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
Total processes
47
Monitored processes
4
Malicious processes
2
Suspicious processes
0
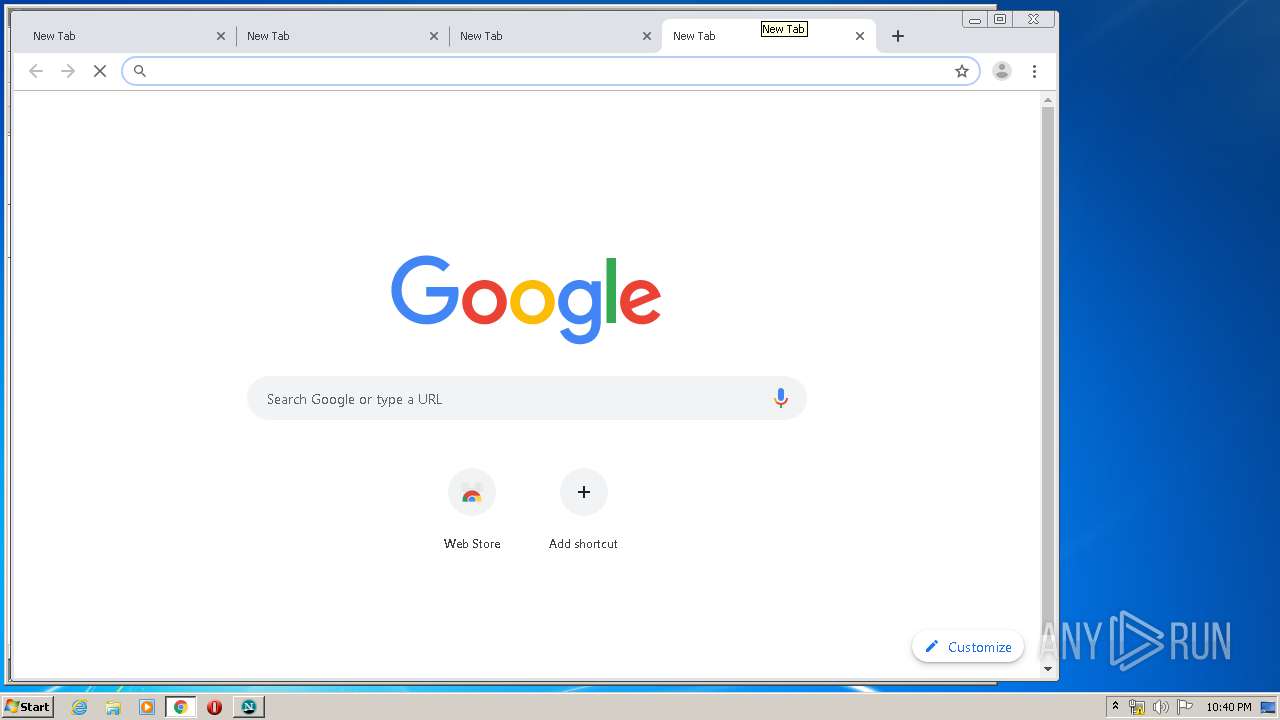
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
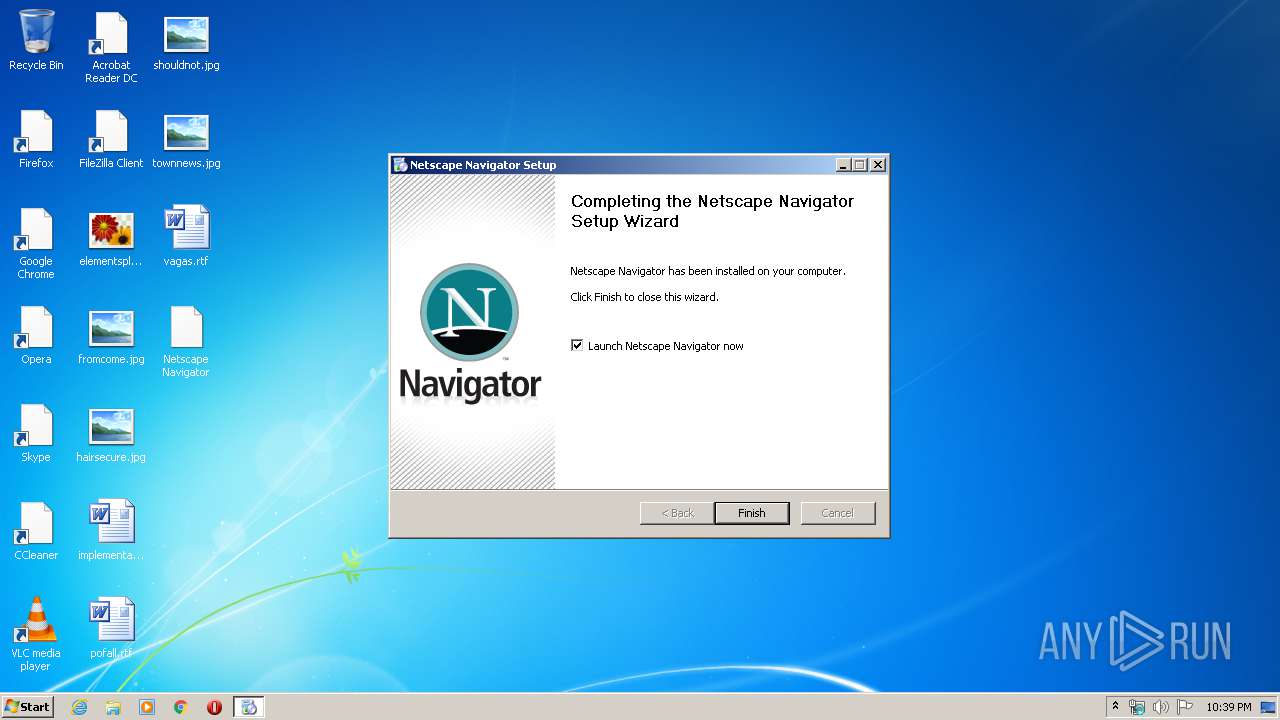
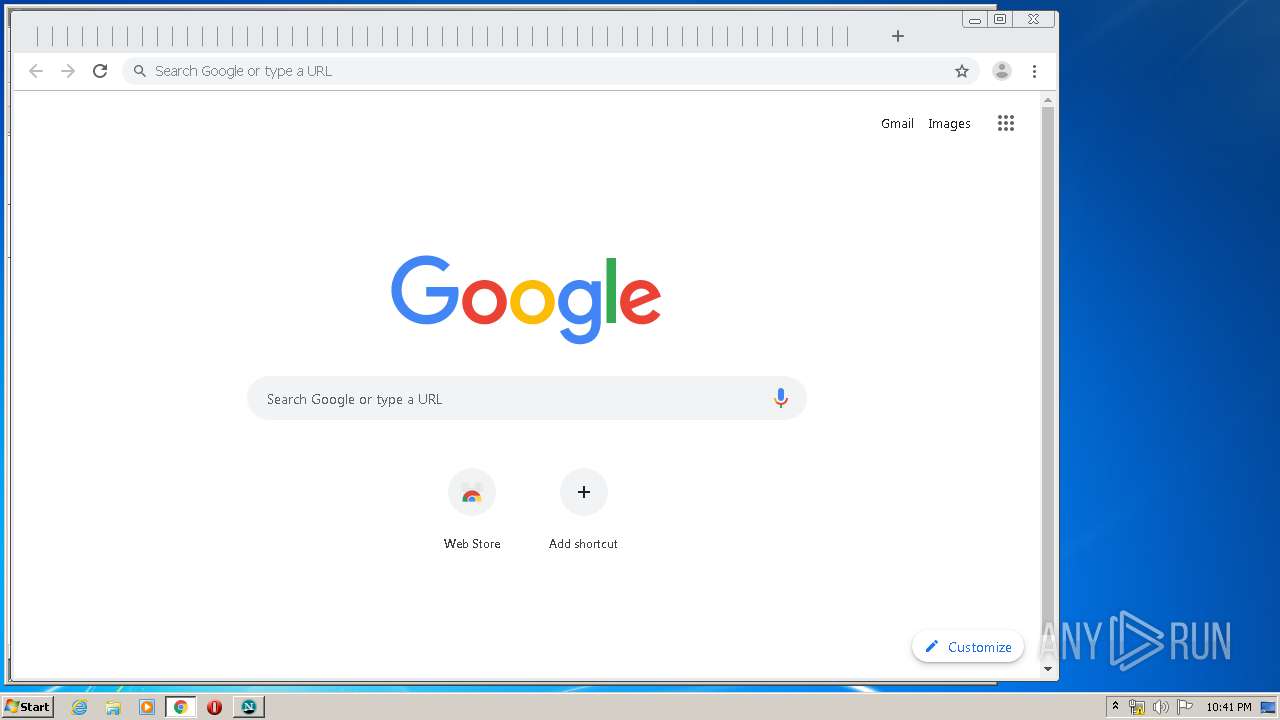
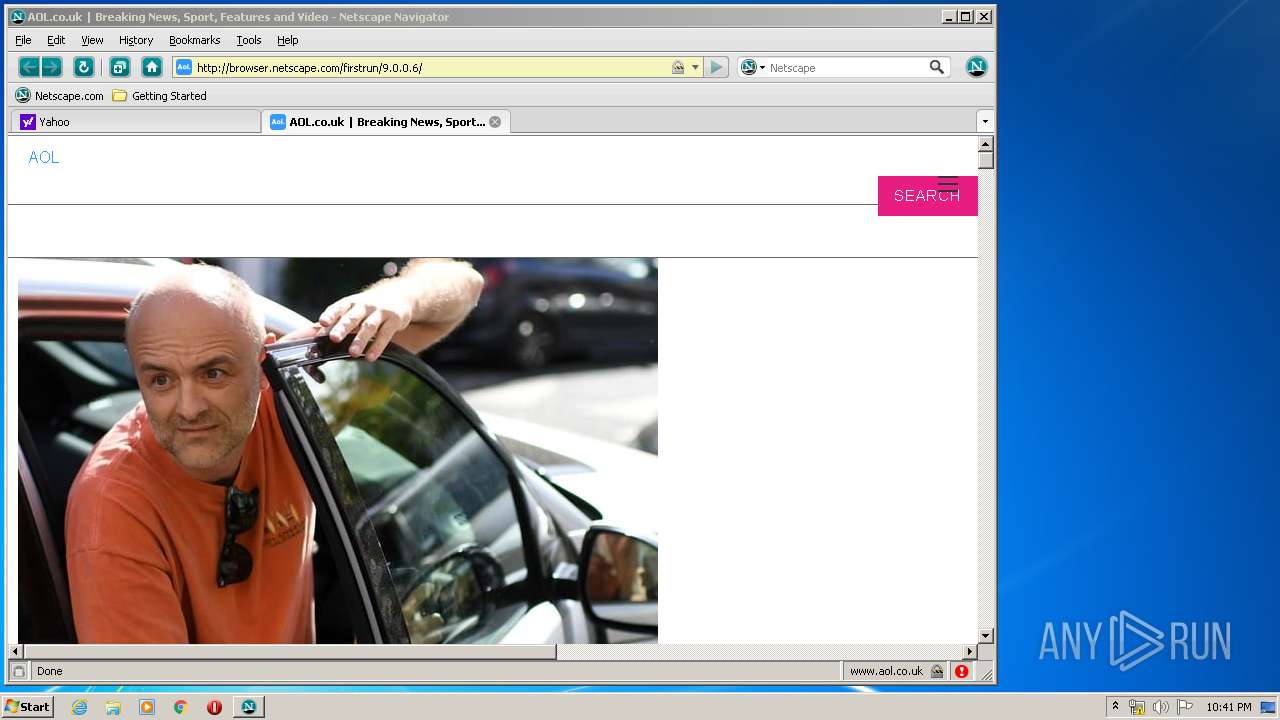
| 988 | "C:\Program Files\Netscape\Navigator 9\navigator.exe" | C:\Program Files\Netscape\Navigator 9\navigator.exe | — | setup.exe | |||||||||||
User: admin Company: Netscape Integrity Level: HIGH Description: Navigator Exit code: 0 Version: Personal | |||||||||||||||
| 1444 | .\setup.exe | C:\Users\admin\AppData\Local\Temp\7zS7DD9.tmp\setup.exe | netscape-navigator-9.0.0.6.exe | ||||||||||||
User: admin Company: Netscape Integrity Level: HIGH Description: Navigator Installer Exit code: 0 Version: 9.0 Modules
| |||||||||||||||
| 1468 | "C:\Users\admin\AppData\Local\Temp\netscape-navigator-9.0.0.6.exe" | C:\Users\admin\AppData\Local\Temp\netscape-navigator-9.0.0.6.exe | explorer.exe | ||||||||||||
User: admin Company: Mozilla Integrity Level: HIGH Description: Firefox Exit code: 0 Version: 4.42 Modules
| |||||||||||||||
| 3160 | "C:\Users\admin\AppData\Local\Temp\netscape-navigator-9.0.0.6.exe" | C:\Users\admin\AppData\Local\Temp\netscape-navigator-9.0.0.6.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Integrity Level: MEDIUM Description: Firefox Exit code: 3221226540 Version: 4.42 Modules
| |||||||||||||||
Total events
481
Read events
385
Write events
95
Delete events
1
Modification events
| (PID) Process: | (1444) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{0D68D6D0-D93D-4D08-A30D-F00DD1F45B24}\InProcServer32 |
| Operation: | write | Name: | |
Value: C:\Program Files\Netscape\Navigator 9\AccessibleMarshal.dll | |||
| (PID) Process: | (1444) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{0D68D6D0-D93D-4D08-A30D-F00DD1F45B24}\InProcServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (1444) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{0D68D6D0-D93D-4D08-A30D-F00DD1F45B24} |
| Operation: | write | Name: | |
Value: PSFactoryBuffer | |||
| (PID) Process: | (1444) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{0D68D6D0-D93D-4D08-A30D-F00DD1F45B24}\ProxyStubClsid32 |
| Operation: | write | Name: | |
Value: {0D68D6D0-D93D-4D08-A30D-F00DD1F45B24} | |||
| (PID) Process: | (1444) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{0D68D6D0-D93D-4D08-A30D-F00DD1F45B24} |
| Operation: | write | Name: | |
Value: ISimpleDOMDocument | |||
| (PID) Process: | (1444) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{0D68D6D0-D93D-4D08-A30D-F00DD1F45B24}\NumMethods |
| Operation: | write | Name: | |
Value: 9 | |||
| (PID) Process: | (1444) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{1814CEEB-49E2-407F-AF99-FA755A7D2607}\ProxyStubClsid32 |
| Operation: | write | Name: | |
Value: {0D68D6D0-D93D-4D08-A30D-F00DD1F45B24} | |||
| (PID) Process: | (1444) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{1814CEEB-49E2-407F-AF99-FA755A7D2607} |
| Operation: | write | Name: | |
Value: ISimpleDOMNode | |||
| (PID) Process: | (1444) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{1814CEEB-49E2-407F-AF99-FA755A7D2607}\NumMethods |
| Operation: | write | Name: | |
Value: 18 | |||
| (PID) Process: | (1444) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{4E747BE5-2052-4265-8AF0-8ECAD7AAD1C0}\ProxyStubClsid32 |
| Operation: | write | Name: | |
Value: {0D68D6D0-D93D-4D08-A30D-F00DD1F45B24} | |||
Executable files
39
Suspicious files
15
Text files
195
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1468 | netscape-navigator-9.0.0.6.exe | C:\Users\admin\AppData\Local\Temp\7zS7DD9.tmp\nonlocalized\res\html.css | text | |
MD5:7307C19745455B4321B977E531A3DEBE | SHA256:01392EC8FC14F1BA2CC821FF7E67F2550729557FA125376EE15584B56485605F | |||
| 1468 | netscape-navigator-9.0.0.6.exe | C:\Users\admin\AppData\Local\Temp\7zS7DD9.tmp\localized\dictionaries\en-US.aff | text | |
MD5:0836DA9065E3F2D4D11DB79F1759F019 | SHA256:66DB43EC9D39DD0875402A900936EDC037936C59AD43E24CA086A1AEC75314DA | |||
| 1468 | netscape-navigator-9.0.0.6.exe | C:\Users\admin\AppData\Local\Temp\7zS7DD9.tmp\nonlocalized\LICENSE | text | |
MD5:48FF35A6E75247E702019CDDD0EACC21 | SHA256:C2AA7D58CEBD24CB877BBF11D6B13A4BB7CD08B9D7DB5D3037CA06C46BF4CFD8 | |||
| 1468 | netscape-navigator-9.0.0.6.exe | C:\Users\admin\AppData\Local\Temp\7zS7DD9.tmp\localized\defaults\profile\chrome\userChrome-example.css | text | |
MD5:4788FDAA51B0A238CB21F5C2877EF06D | SHA256:BBAA6DE3247C9D5C9991F8D14B9022491578E603A6B2E2838E760A87C658A719 | |||
| 1468 | netscape-navigator-9.0.0.6.exe | C:\Users\admin\AppData\Local\Temp\7zS7DD9.tmp\nonlocalized\res\EditorOverride.css | text | |
MD5:4B3B5AD0B17C566819A88D54026B52FD | SHA256:4ECA3B7360E2D917B9C6C626F9BF5AAFDD5EEC1D296146BAAB32D1F3B00D7A53 | |||
| 1468 | netscape-navigator-9.0.0.6.exe | C:\Users\admin\AppData\Local\Temp\7zS7DD9.tmp\localized\dictionaries\en-US.dic | text | |
MD5:508A7BF30B716CCF59C662EBB7D910AE | SHA256:6F90F900A772CC49D96B061C489671E217D68AB9B533BCDB854682631FE4D303 | |||
| 1468 | netscape-navigator-9.0.0.6.exe | C:\Users\admin\AppData\Local\Temp\7zS7DD9.tmp\nonlocalized\res\viewsource.css | text | |
MD5:E60552A13E4F1F44416EB9E53CE85143 | SHA256:4C7068FE21E3E0D09757B66BBA44F4C426E34CDC32D32E96722316F7B77FC6C1 | |||
| 1468 | netscape-navigator-9.0.0.6.exe | C:\Users\admin\AppData\Local\Temp\7zS7DD9.tmp\localized\defaults\profile\chrome\userContent-example.css | text | |
MD5:D3765C7D2DE5626529195007F4B7144A | SHA256:10CD5C7D7FB1F6F1123893530099888822C6CB8A4A41584534C2D2EBA38F5BA9 | |||
| 1468 | netscape-navigator-9.0.0.6.exe | C:\Users\admin\AppData\Local\Temp\7zS7DD9.tmp\nonlocalized\res\forms.css | text | |
MD5:43C717453B00DBA083428B8E3583B588 | SHA256:6DE94BF45EE501DFFD9FCFF3F4FCDFD85E2452CDBCE630813381BFFF77F777D5 | |||
| 1468 | netscape-navigator-9.0.0.6.exe | C:\Users\admin\AppData\Local\Temp\7zS7DD9.tmp\nonlocalized\js3250.dll | executable | |
MD5:3B808914DB411389D9ECBDCB4FA1C1BB | SHA256:2B6A59C020E48A2308587D773607DA0FB3D94F79AF0EACFFA47CFEFF10ACDCE8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
44
DNS requests
35
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 301 | 188.125.72.165:80 | http://www.netscape.com/ | CH | — | — | malicious |
— | — | GET | 200 | 173.194.5.42:80 | http://r5---sn-aigzrn7e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Qx&mip=185.92.25.187&mm=28&mn=sn-aigzrn7e&ms=nvh&mt=1590269954&mv=m&mvi=4&pl=24&shardbypass=yes | US | crx | 816 Kb | whitelisted |
— | — | GET | 302 | 216.58.212.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 519 b | whitelisted |
— | — | GET | 302 | 216.58.212.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 524 b | whitelisted |
— | — | GET | 200 | 173.194.135.103:80 | http://r2---sn-aigzrn7z.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=185.92.25.187&mm=28&mn=sn-aigzrn7z&ms=nvh&mt=1590270013&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
— | — | GET | 200 | 188.125.72.139:80 | http://geo.yahoo.com/b?s=1197757129&t=1590270019192&err_url=http%3A%2F%2Fbrowser.netscape.com%2Ffirstrun%2F9.0.0.6%2F&err=%25%3Cpssc%3E&test=%25%3C%7BY-Bucket%7Dcqh%5B%3A200%5D%3E&ats_host=%25%3Cphn%3E&rid=%25%3C%7BY-RID%7Dpqh%3E&message=Web%20Server%20Error&source=brb | CH | image | 43 b | whitelisted |
— | — | GET | 200 | 212.82.100.150:80 | http://browser.netscape.com/favicon.ico | CH | image | 2.19 Kb | whitelisted |
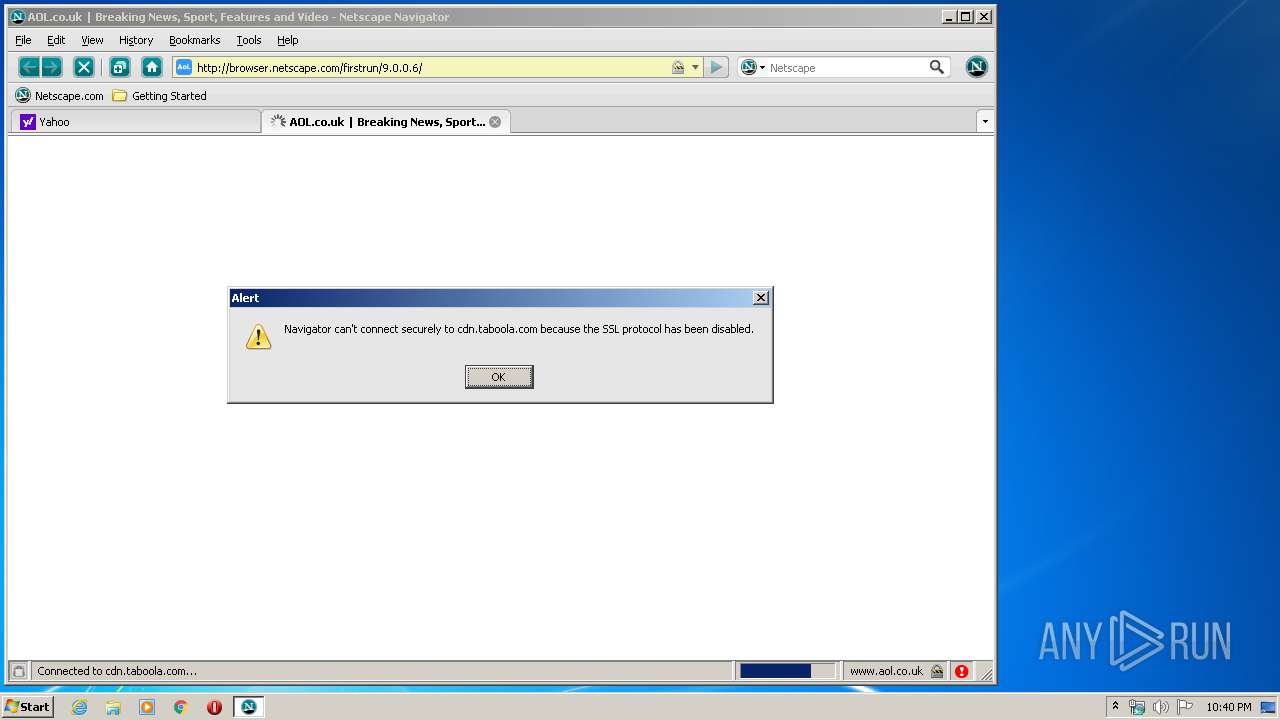
— | — | GET | 400 | 212.82.100.150:80 | http://browser.netscape.com/firstrun/%VERSION%/ | CH | html | 3.11 Kb | whitelisted |
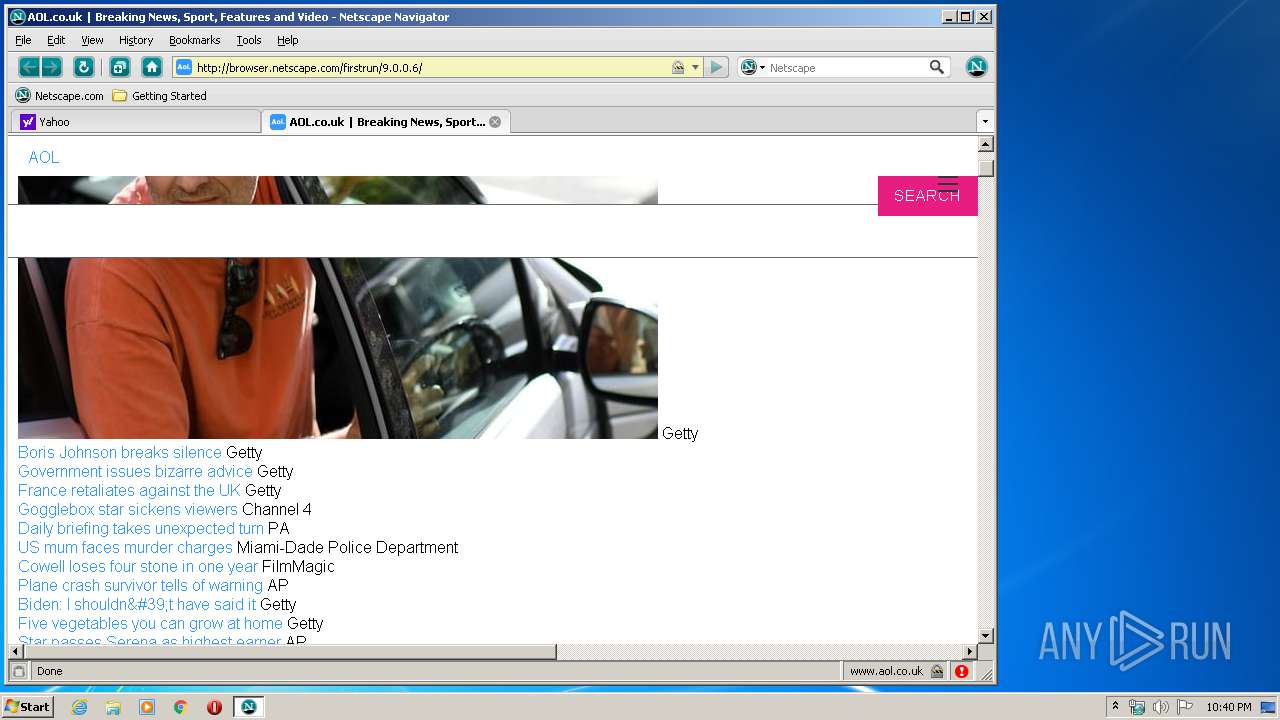
— | — | GET | 200 | 212.82.100.150:80 | http://browser.netscape.com/firstrun/9.0.0.6/ | CH | html | 1.66 Kb | whitelisted |
— | — | GET | 404 | 216.58.207.46:80 | http://sb.google.com/safebrowsing/update?client=Navigator&appver=9.0.0.6&version=goog-white-domain:1:-1,goog-white-url:1:-1,goog-black-url:1:-1,goog-black-enchash:1:-1 | US | html | 1.54 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 212.82.100.150:80 | — | Yahoo! UK Services Limited | CH | shared |
— | — | 188.125.72.165:80 | www.netscape.com | — | CH | unknown |
— | — | 87.248.118.22:443 | s.yimg.com | Yahoo! UK Services Limited | GB | shared |
— | — | 54.171.161.206:80 | bcn.fp.yahoo.com | Amazon.com, Inc. | IE | suspicious |
— | — | 188.125.72.139:80 | geo.yahoo.com | — | CH | suspicious |
— | — | 188.125.72.167:443 | www.aol.com | — | CH | unknown |
— | — | 192.229.220.136:443 | s.blogsmithmedia.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | unknown |
— | — | 216.58.207.46:80 | sb.google.com | Google Inc. | US | whitelisted |
— | — | 18.205.137.123:443 | delivery.vidible.tv | — | US | unknown |
— | — | 151.101.1.44:443 | cdn.taboola.com | Fastly | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
browser.netscape.com |
| whitelisted |
www.netscape.com |
| malicious |
s.yimg.com |
| shared |
geo.yahoo.com |
| whitelisted |
bcn.fp.yahoo.com |
| suspicious |
www.aol.com |
| whitelisted |
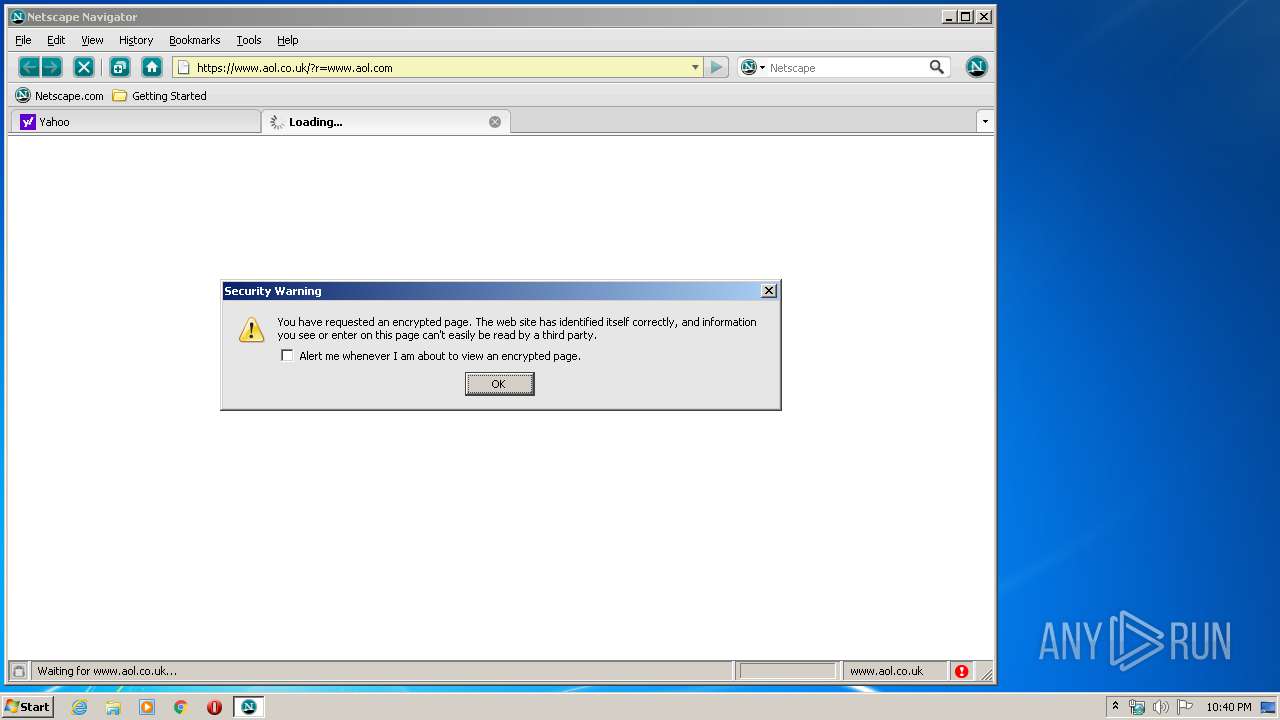
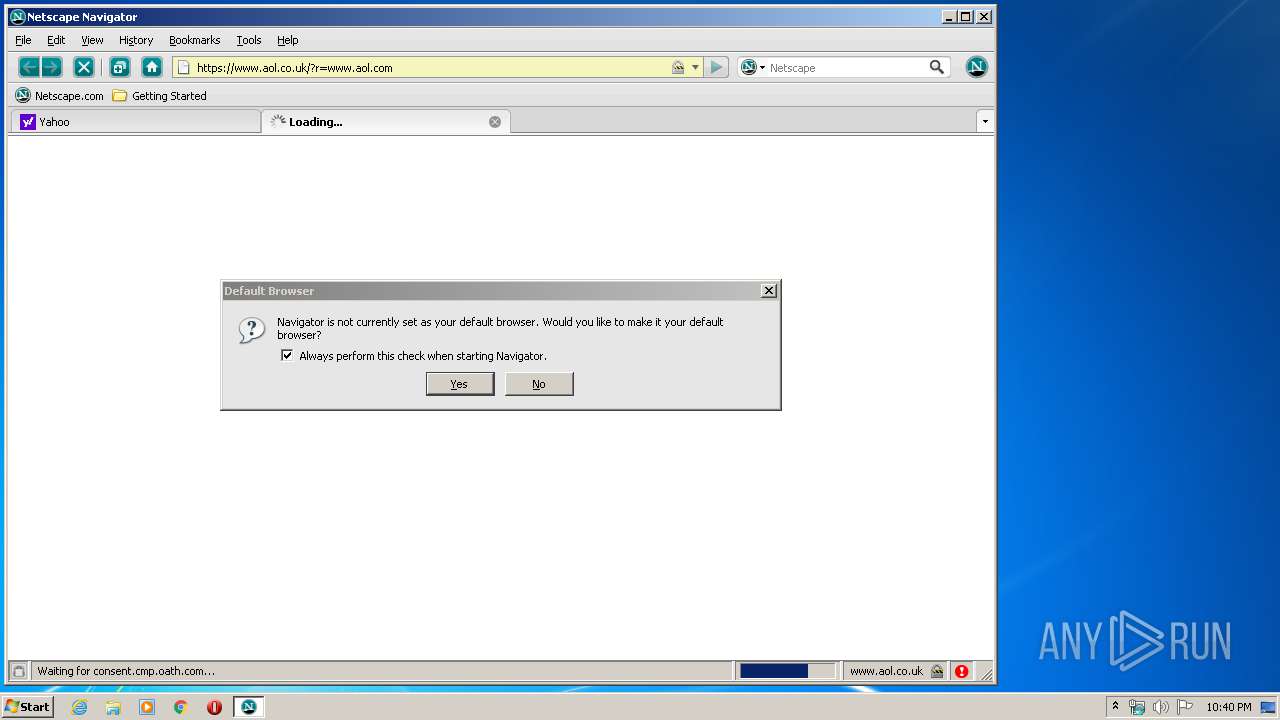
www.aol.co.uk |
| unknown |
s.aolcdn.com |
| whitelisted |
consent.cmp.oath.com |
| whitelisted |
s.blogsmithmedia.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake FireFox Version 2. |
— | — | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake FireFox Version 2. |