| File name: | Update - 137056.zip |
| Full analysis: | https://app.any.run/tasks/41a3ec9c-cc92-4646-8a36-8629e135946d |
| Verdict: | Malicious activity |
| Analysis date: | May 28, 2024, 21:09:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
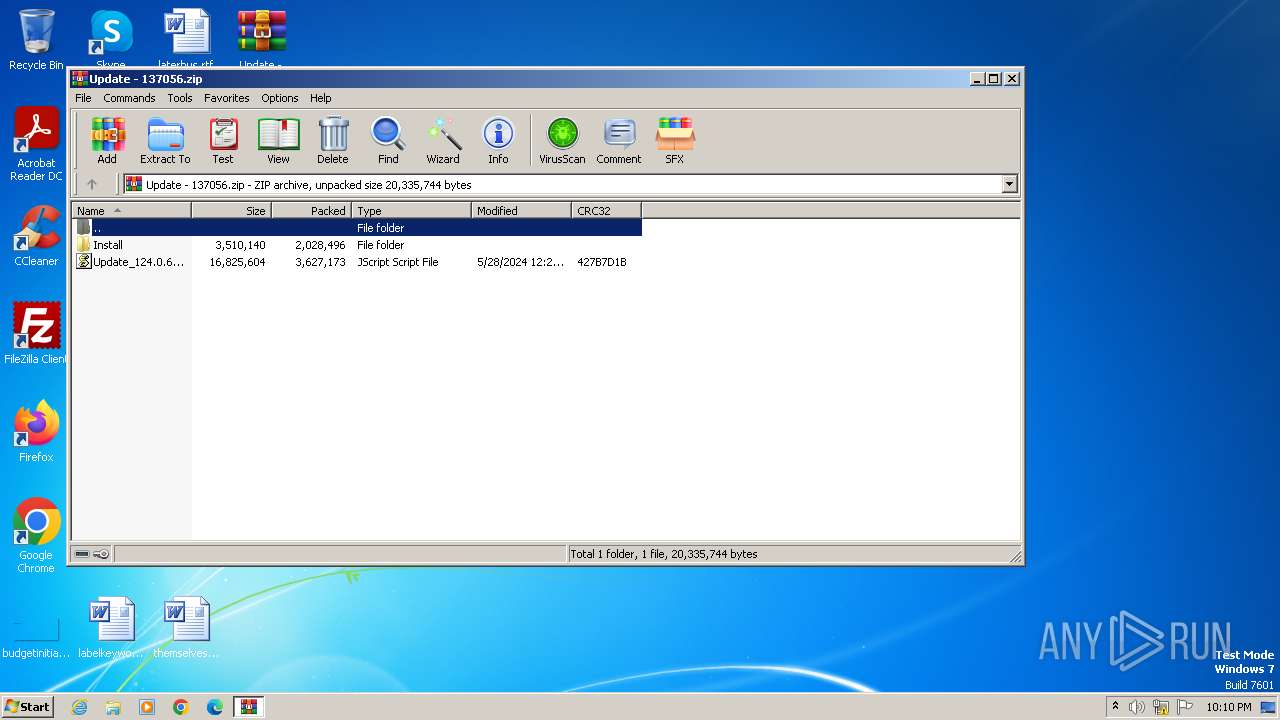
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 29B268E800761E600707B806A3A5CDD2 |
| SHA1: | A690CF76421FEFF1EB9FA6C95DE6517DB131136D |
| SHA256: | F6CCFC907F62BC7F8FDB6810FE0A3B34D7B95A993D5AC524F91430666D97FF46 |
| SSDEEP: | 98304:HQBC+sKBBtJfuRE1Nfm27UmJbe3ro51n1adUYJiLNVRC40/jxlRp8u4TfRTSBJSo:VG9sE7gBbKIeAf/oS |
MALICIOUS
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 4064)
Unusual connection from system programs
- wscript.exe (PID: 4064)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 4064)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3972)
The process executes JS scripts
- WinRAR.exe (PID: 3972)
Adds/modifies Windows certificates
- wscript.exe (PID: 4064)
Reads the Internet Settings
- wscript.exe (PID: 4064)
INFO
Checks proxy server information
- wscript.exe (PID: 4064)
Manual execution by a user
- wmpnscfg.exe (PID: 1432)
Reads the computer name
- wmpnscfg.exe (PID: 1432)
Checks supported languages
- wmpnscfg.exe (PID: 1432)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0002 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:05:28 12:23:58 |
| ZipCRC: | 0x427b7d1b |
| ZipCompressedSize: | 3627173 |
| ZipUncompressedSize: | 16825604 |
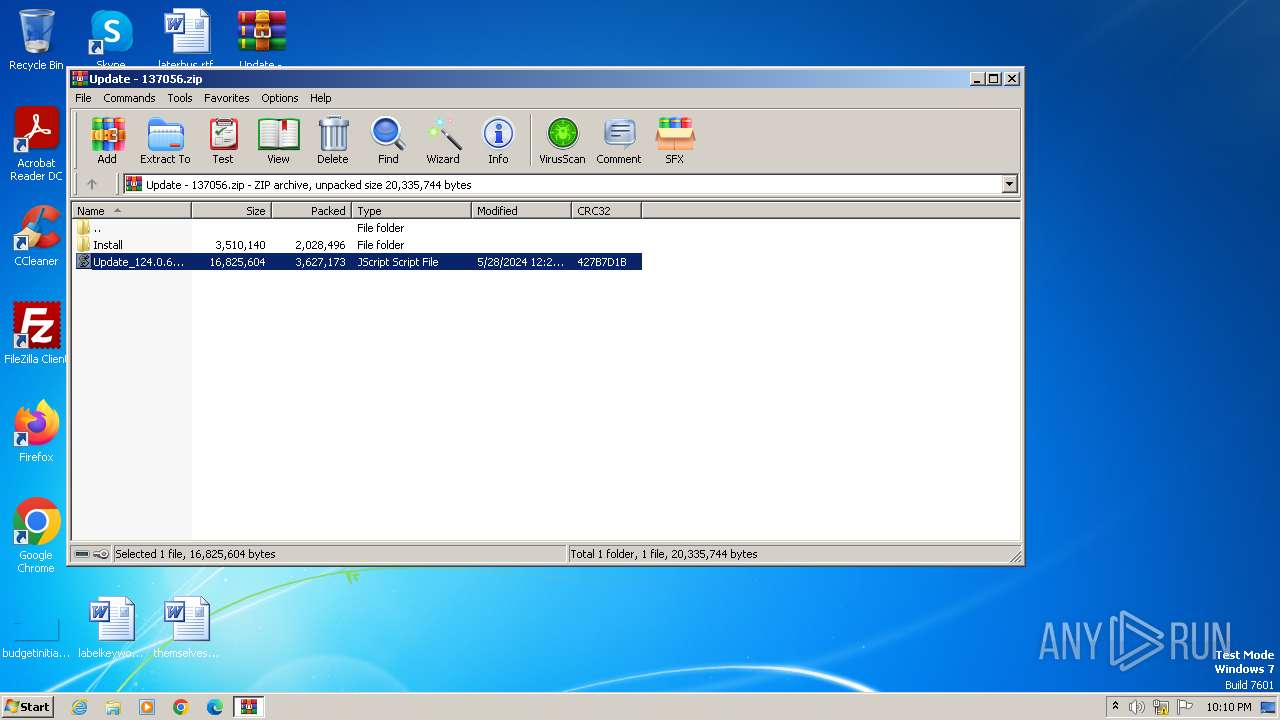
| ZipFileName: | Update_124.0.6367.158.js |
Total processes
36
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1432 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3972 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Update - 137056.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 4064 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa3972.41999\Update_124.0.6367.158.js" | C:\Windows\System32\wscript.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
7 787
Read events
7 670
Write events
85
Delete events
32
Modification events
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Update - 137056.zip | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
0
Suspicious files
5
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3972 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa3972.41999\Update_124.0.6367.158.js | — | |
MD5:— | SHA256:— | |||
| 4064 | wscript.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\3AB24A2756EC9C1322D47195FBEF166E | binary | |
MD5:E23F3E1A9B058A51180DA4CA10B74928 | SHA256:86020F8152D59B8D09D6D30F144786FCA5F2084A4D362EF993EB771B5B9D021C | |||
| 4064 | wscript.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:676FEF9148ED2E6F4154C2826DA8B4F0 | SHA256:FE537E5B2548017B54166914EB330C5C5C955F5D08D56DAD8EC9B1D52DB57C2D | |||
| 4064 | wscript.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:822467B728B7A66B081C91795373789A | SHA256:AF2343382B88335EEA72251AD84949E244FF54B6995063E24459A7216E9576B9 | |||
| 4064 | wscript.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\3AB24A2756EC9C1322D47195FBEF166E | binary | |
MD5:FD1B8FE7098310E018732D46620C9EFC | SHA256:B01337C60F7FE32055D8CE603F3B748DA479C1582BDC24EBD07C4F58DF98462D | |||
| 4064 | wscript.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:163FE88F4734ED2C6FB7B526E2CE1CF3 | SHA256:7CEC293DA3975CB949EEC1D8518FEB53D843F876C9CBF4B1FAD74906963C50A2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
8
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 304 | 2.19.126.137:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?cfe7fb20112320ef | unknown | — | — | unknown |
— | — | GET | 200 | 2.23.197.184:80 | http://x1.c.lencr.org/ | unknown | — | — | unknown |
— | — | GET | 200 | 95.101.54.195:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgMOT9gS9afrHl9rReaE8R%2FLrA%3D%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4064 | wscript.exe | 103.35.188.64:443 | bookmycooks.com | ARTERIA Networks Corporation | JP | unknown |
4064 | wscript.exe | 2.19.126.137:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
4064 | wscript.exe | 2.23.197.184:80 | x1.c.lencr.org | CW Vodafone Group PLC | GB | unknown |
4064 | wscript.exe | 95.101.54.195:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bookmycooks.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |