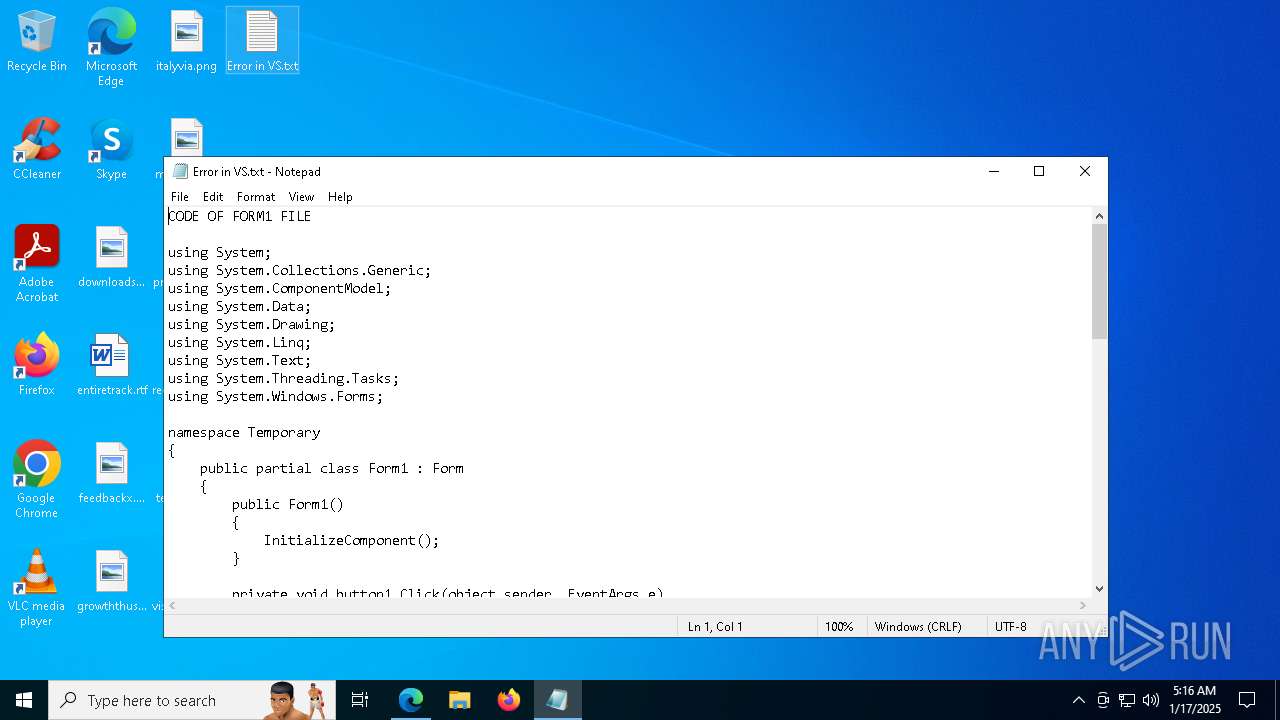
| File name: | Error in VS.txt |
| Full analysis: | https://app.any.run/tasks/b4073179-6714-4aea-9f87-fcb8f2094174 |
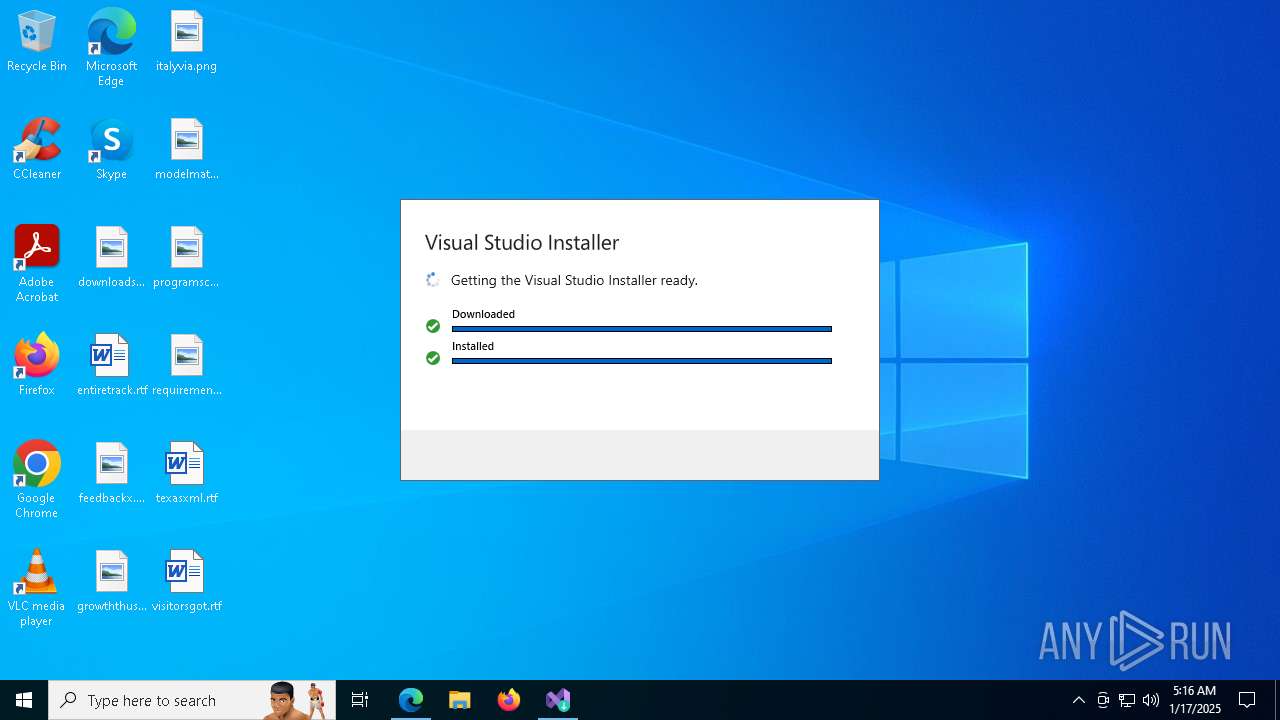
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2025, 05:12:44 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
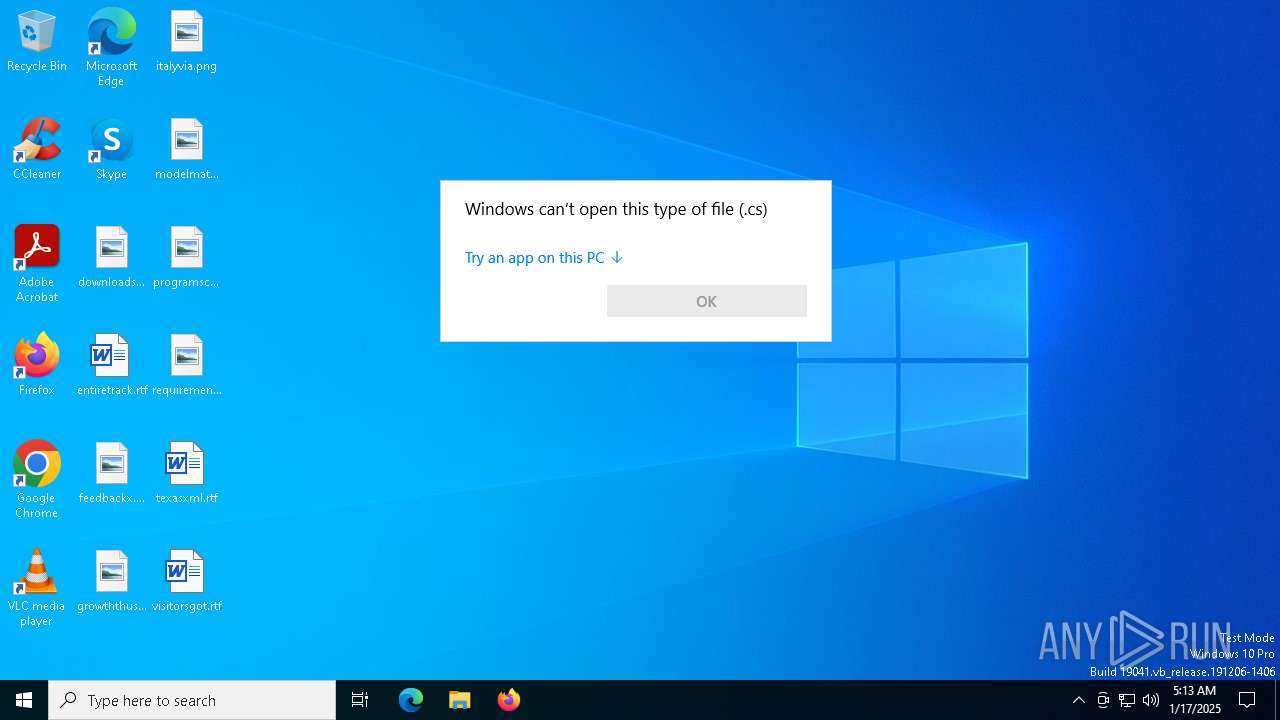
| MIME: | text/x-c++ |
| File info: | C++ source, ASCII text, with CRLF line terminators |
| MD5: | 53996C445C7D434A5E5052B2BD999F0C |
| SHA1: | 37E434E1B3BFE1B2DEDD8DB4B7A2BD0AA3BFA49A |
| SHA256: | F6CB16A96D51F03D536BA3C3F4C2D27AECF053DA84431953514772E15CFD1FC7 |
| SSDEEP: | 24:nfo4KM4Kc1Cz02nkqVg4K3Nn71rFe+HVFnT+HHJnYoo4KM4Kc1Cz02nkqVg4K3uQ:fo4h4Dcz02nXVgLN8Zo4h4Dcz02nXVgp |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates file in the systems drive root
- OpenWith.exe (PID: 6980)
Reads security settings of Internet Explorer
- vs_setup_bootstrapper.exe (PID: 6372)
- setup.exe (PID: 7408)
- setup.exe (PID: 7928)
- setup.exe (PID: 5872)
- setup.exe (PID: 6484)
- setup.exe (PID: 3080)
Found regular expressions for crypto-addresses (YARA)
- vs_setup_bootstrapper.exe (PID: 6372)
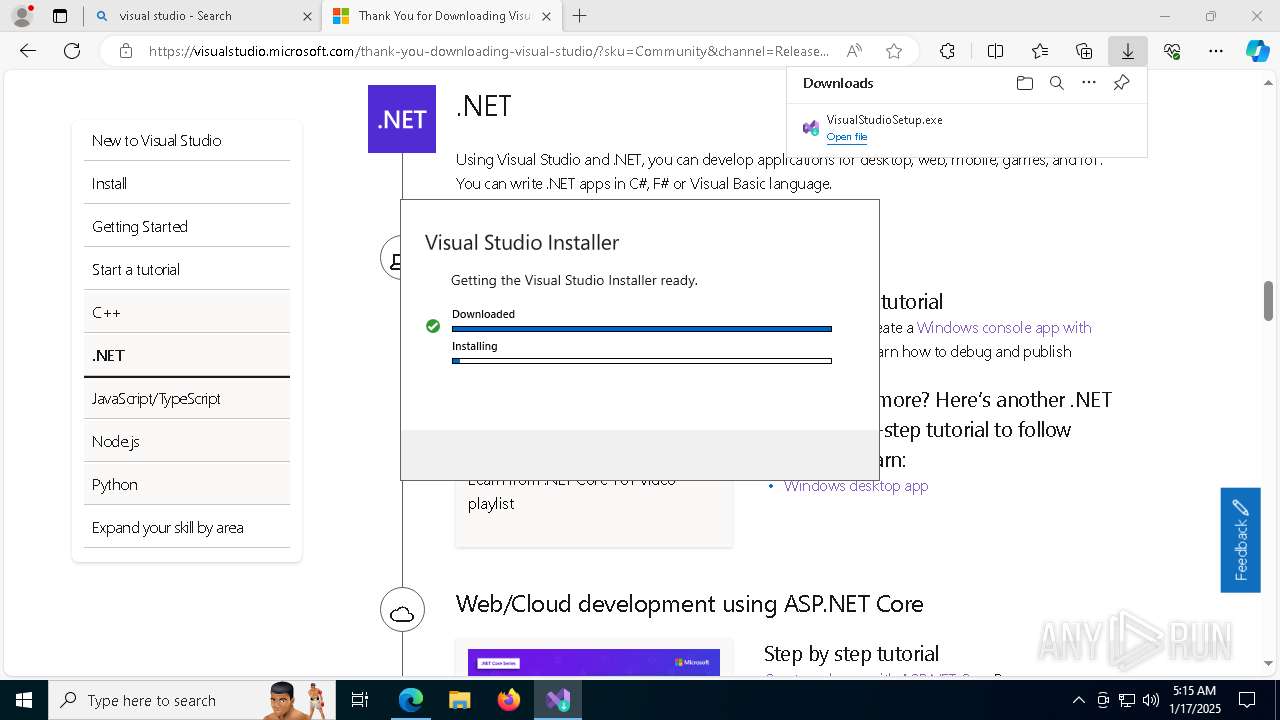
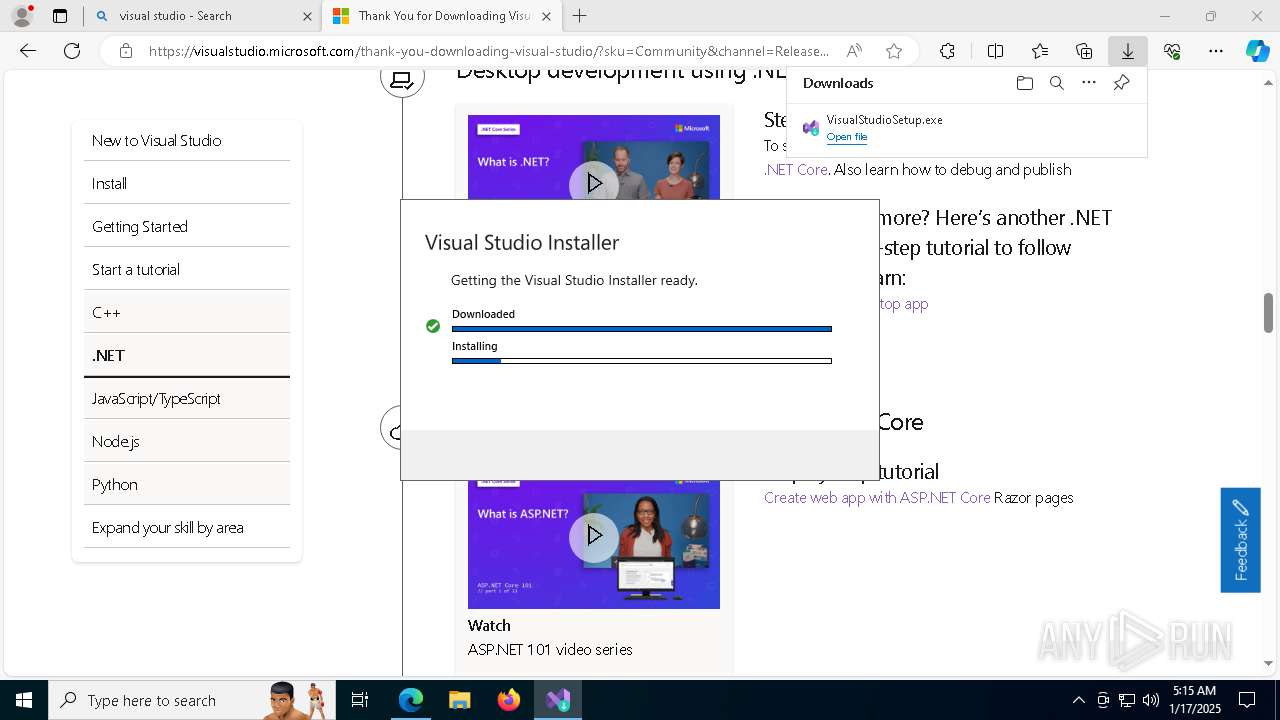
Process drops legitimate windows executable
- vs_setup_bootstrapper.exe (PID: 6372)
- setup.exe (PID: 5872)
- vs_setup_bootstrapper.exe (PID: 5252)
- setup.exe (PID: 3080)
The process drops C-runtime libraries
- vs_setup_bootstrapper.exe (PID: 6372)
- setup.exe (PID: 5872)
- setup.exe (PID: 3080)
Executable content was dropped or overwritten
- vs_setup_bootstrapper.exe (PID: 6372)
- setup.exe (PID: 5872)
- vs_setup_bootstrapper.exe (PID: 5252)
- setup.exe (PID: 3080)
Creates a software uninstall entry
- vs_installer.windows.exe (PID: 7868)
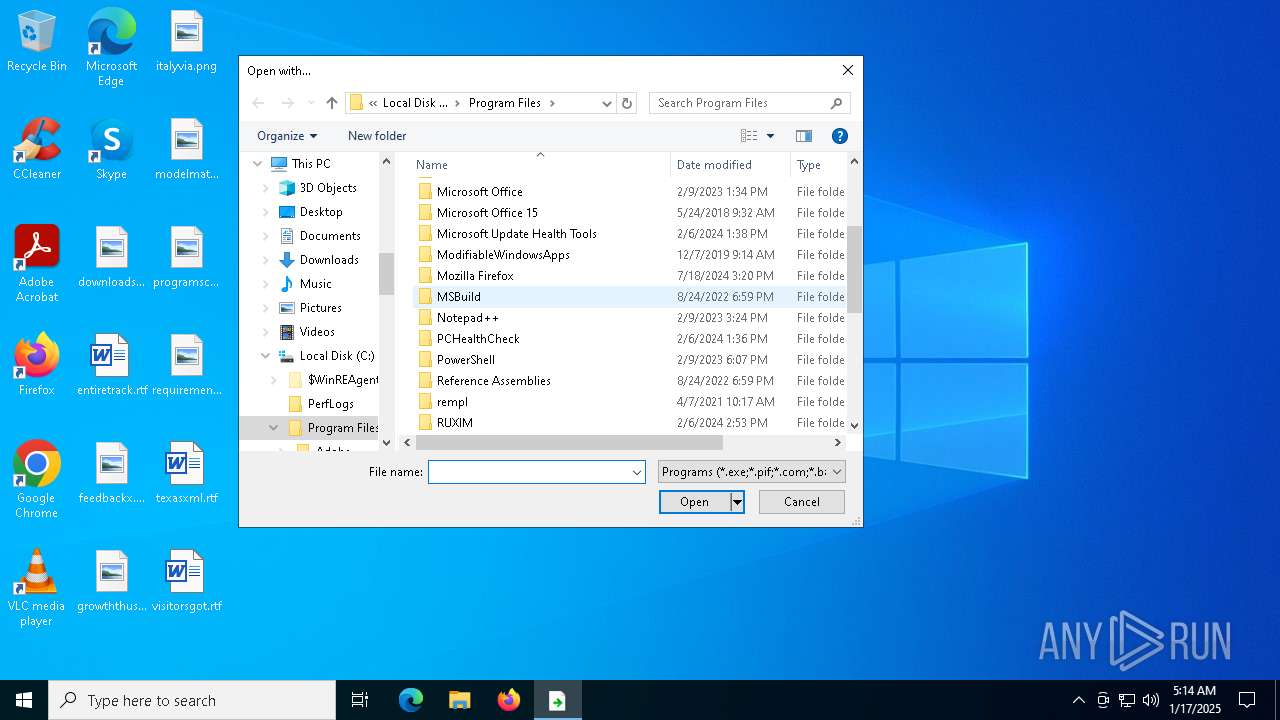
Searches for installed software
- vs_installer.windows.exe (PID: 7868)
Application launched itself
- setup.exe (PID: 7928)
Reads the date of Windows installation
- setup.exe (PID: 7928)
Checks Windows Trust Settings
- setup.exe (PID: 5872)
- setup.exe (PID: 7928)
- setup.exe (PID: 6484)
- setup.exe (PID: 3080)
Starts a Microsoft application from unusual location
- vs_setup_bootstrapper.exe (PID: 5252)
The process creates files with name similar to system file names
- setup.exe (PID: 5872)
- setup.exe (PID: 3080)
INFO
Reads the machine GUID from the registry
- SearchApp.exe (PID: 5064)
- vs_setup_bootstrapper.exe (PID: 6372)
- setup.exe (PID: 7408)
- setup.exe (PID: 7928)
- setup.exe (PID: 5872)
- setup.exe (PID: 6484)
- setup.exe (PID: 3080)
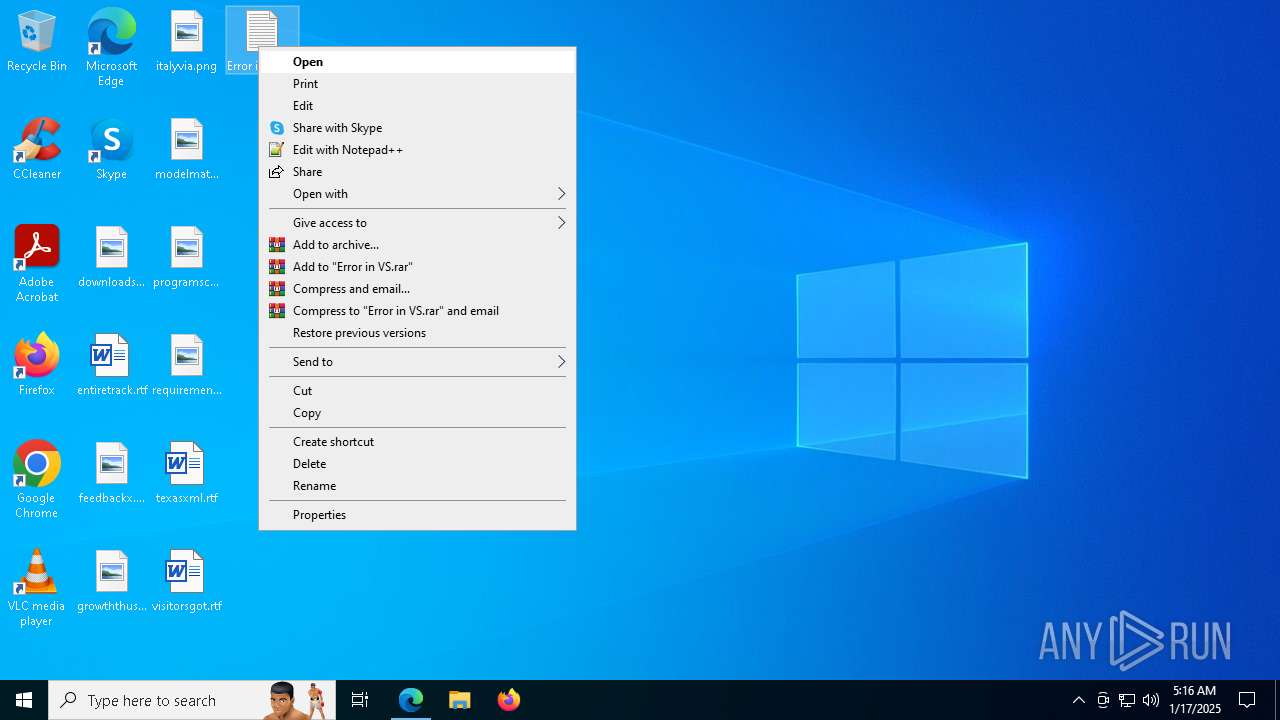
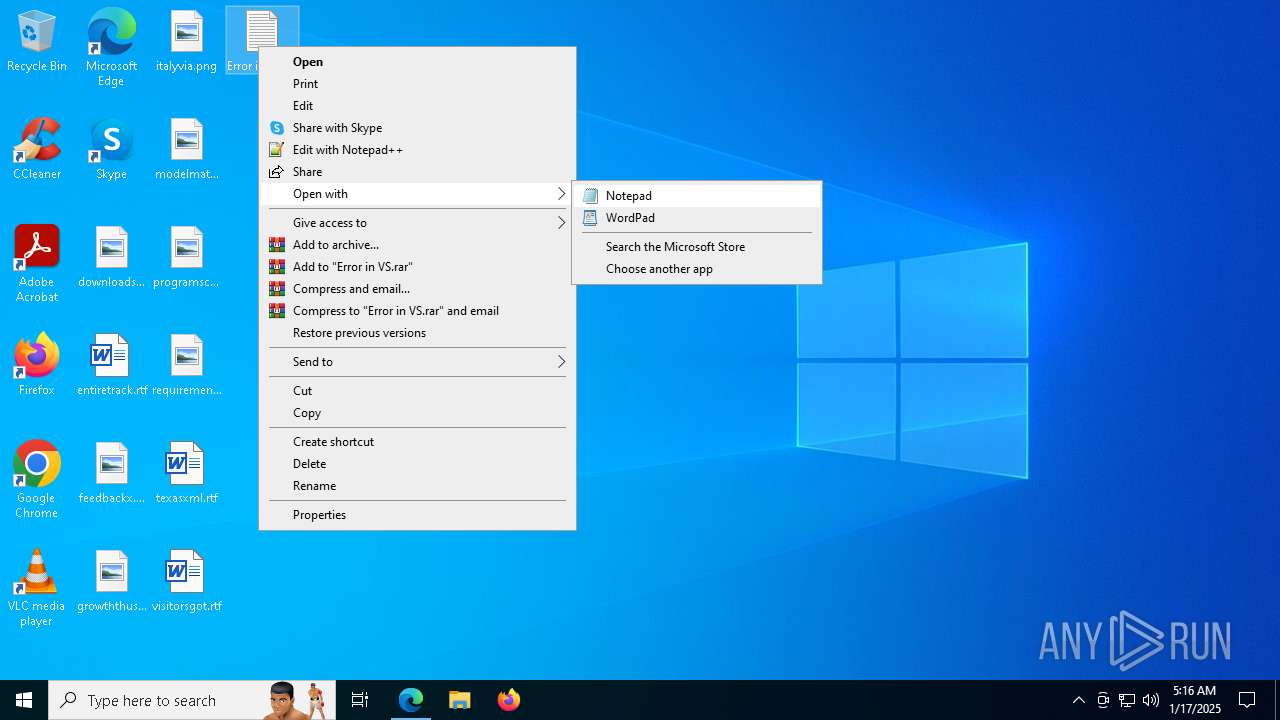
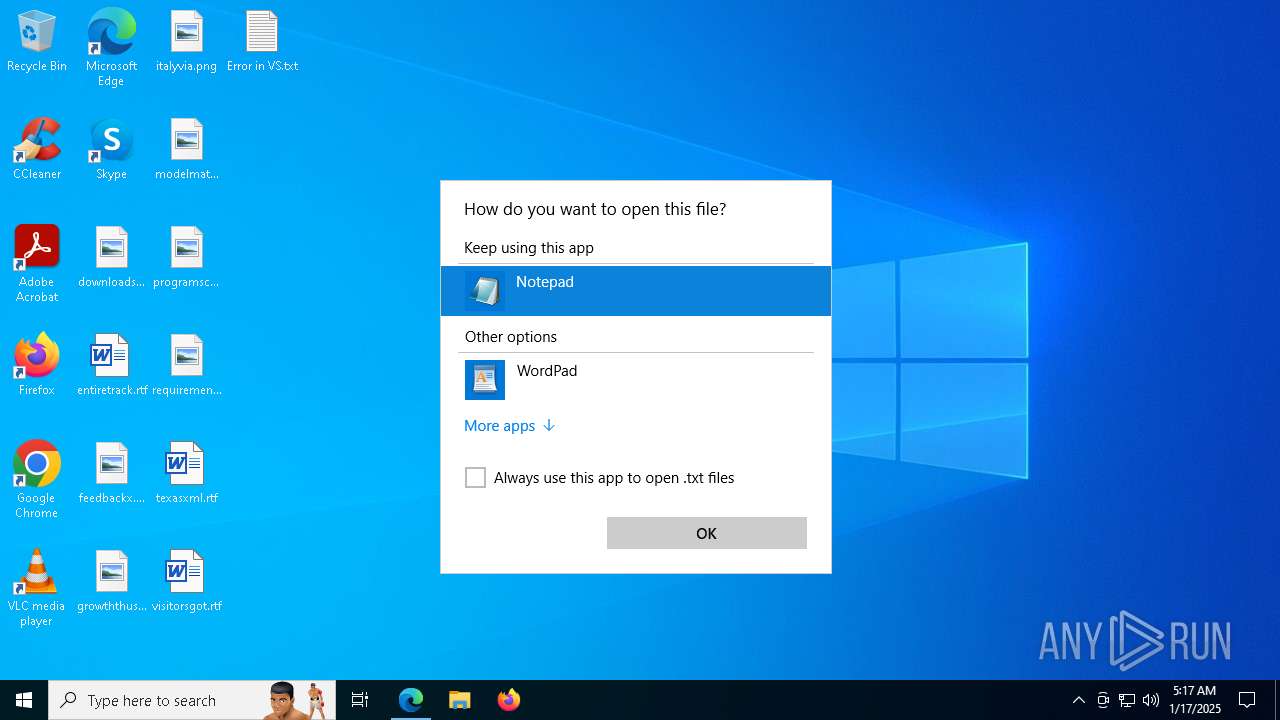
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 6980)
- OpenWith.exe (PID: 7368)
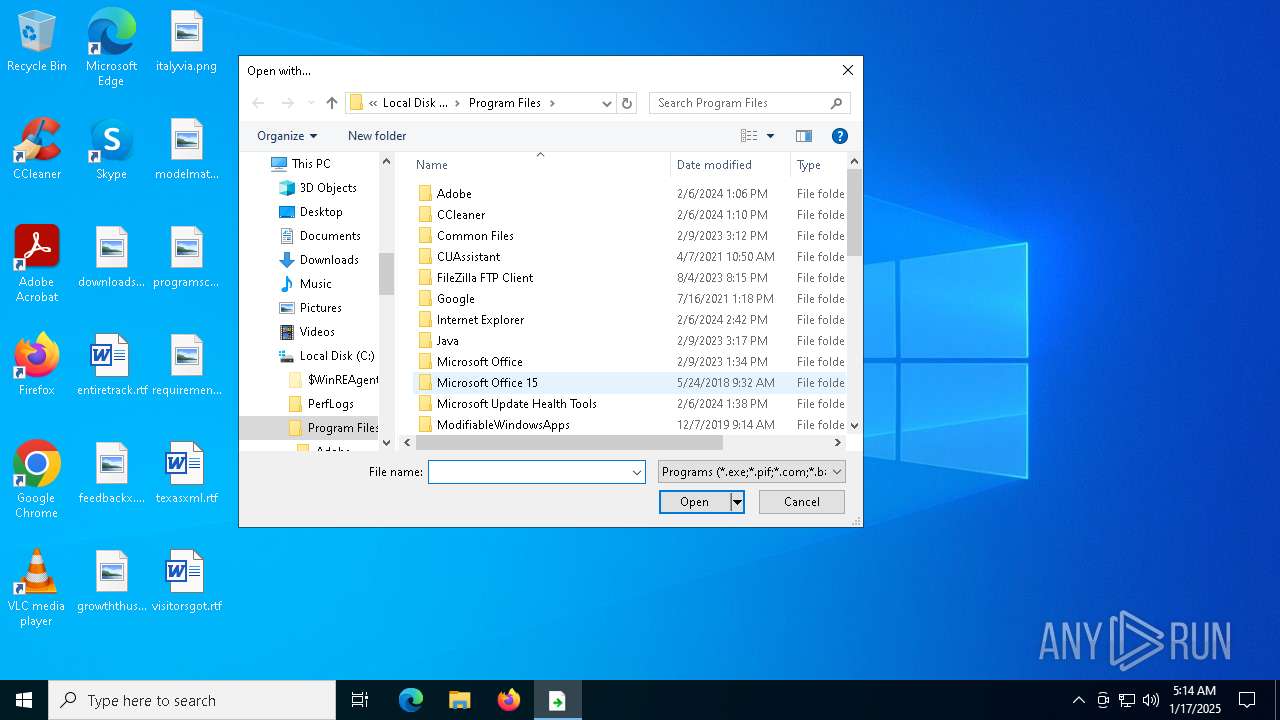
Creates files in the program directory
- vs_setup_bootstrapper.exe (PID: 6372)
- setup.exe (PID: 7408)
- setup.exe (PID: 7928)
- setup.exe (PID: 5872)
- setup.exe (PID: 6484)
- setup.exe (PID: 3080)
Reads the software policy settings
- SearchApp.exe (PID: 5064)
- vs_setup_bootstrapper.exe (PID: 6372)
- setup.exe (PID: 7408)
- setup.exe (PID: 7928)
- setup.exe (PID: 5872)
- setup.exe (PID: 3080)
- setup.exe (PID: 6484)
Reads CPU info
- vs_setup_bootstrapper.exe (PID: 6372)
- setup.exe (PID: 7408)
- setup.exe (PID: 7928)
Process checks computer location settings
- SearchApp.exe (PID: 5064)
- setup.exe (PID: 7928)
Checks supported languages
- vs_setup_bootstrapper.exe (PID: 6372)
- SearchApp.exe (PID: 5064)
- vs_installer.windows.exe (PID: 7868)
- setup.exe (PID: 7408)
- setup.exe (PID: 7928)
- setup.exe (PID: 5872)
- vs_setup_bootstrapper.exe (PID: 5252)
- setup.exe (PID: 6484)
- setup.exe (PID: 3080)
Disables trace logs
- vs_setup_bootstrapper.exe (PID: 6372)
- setup.exe (PID: 7408)
- setup.exe (PID: 7928)
- setup.exe (PID: 5872)
- setup.exe (PID: 6484)
Creates files or folders in the user directory
- vs_setup_bootstrapper.exe (PID: 6372)
- setup.exe (PID: 7408)
- setup.exe (PID: 7928)
The sample compiled with german language support
- vs_setup_bootstrapper.exe (PID: 6372)
- vs_setup_bootstrapper.exe (PID: 5252)
- setup.exe (PID: 5872)
- setup.exe (PID: 3080)
Reads security settings of Internet Explorer
- OpenWith.exe (PID: 6980)
- notepad.exe (PID: 7304)
Reads the computer name
- vs_setup_bootstrapper.exe (PID: 6372)
- setup.exe (PID: 7408)
- vs_installer.windows.exe (PID: 7868)
- setup.exe (PID: 5872)
- vs_setup_bootstrapper.exe (PID: 5252)
- setup.exe (PID: 7928)
- setup.exe (PID: 6484)
- setup.exe (PID: 3080)
Displays MAC addresses of computer network adapters
- getmac.exe (PID: 6828)
Checks proxy server information
- vs_setup_bootstrapper.exe (PID: 6372)
- setup.exe (PID: 7408)
- setup.exe (PID: 3080)
The sample compiled with czech language support
- vs_setup_bootstrapper.exe (PID: 6372)
- vs_setup_bootstrapper.exe (PID: 5252)
- setup.exe (PID: 5872)
- setup.exe (PID: 3080)
The sample compiled with english language support
- vs_setup_bootstrapper.exe (PID: 6372)
- setup.exe (PID: 5872)
- vs_setup_bootstrapper.exe (PID: 5252)
- setup.exe (PID: 3080)
The sample compiled with spanish language support
- vs_setup_bootstrapper.exe (PID: 6372)
- vs_setup_bootstrapper.exe (PID: 5252)
- setup.exe (PID: 5872)
- setup.exe (PID: 3080)
The sample compiled with turkish language support
- vs_setup_bootstrapper.exe (PID: 6372)
- vs_setup_bootstrapper.exe (PID: 5252)
- setup.exe (PID: 5872)
- setup.exe (PID: 3080)
The sample compiled with polish language support
- vs_setup_bootstrapper.exe (PID: 6372)
- vs_setup_bootstrapper.exe (PID: 5252)
- setup.exe (PID: 5872)
- setup.exe (PID: 3080)
The sample compiled with japanese language support
- vs_setup_bootstrapper.exe (PID: 6372)
- vs_setup_bootstrapper.exe (PID: 5252)
- setup.exe (PID: 5872)
- setup.exe (PID: 3080)
The sample compiled with Italian language support
- vs_setup_bootstrapper.exe (PID: 6372)
- vs_setup_bootstrapper.exe (PID: 5252)
- setup.exe (PID: 5872)
- setup.exe (PID: 3080)
The sample compiled with korean language support
- vs_setup_bootstrapper.exe (PID: 6372)
- vs_setup_bootstrapper.exe (PID: 5252)
- setup.exe (PID: 5872)
- setup.exe (PID: 3080)
The sample compiled with russian language support
- vs_setup_bootstrapper.exe (PID: 6372)
- vs_setup_bootstrapper.exe (PID: 5252)
- setup.exe (PID: 5872)
- setup.exe (PID: 3080)
The sample compiled with french language support
- vs_setup_bootstrapper.exe (PID: 6372)
- vs_setup_bootstrapper.exe (PID: 5252)
- setup.exe (PID: 5872)
- setup.exe (PID: 3080)
The sample compiled with chinese language support
- vs_setup_bootstrapper.exe (PID: 6372)
- vs_setup_bootstrapper.exe (PID: 5252)
- setup.exe (PID: 5872)
- setup.exe (PID: 3080)
The sample compiled with portuguese language support
- vs_setup_bootstrapper.exe (PID: 6372)
- vs_setup_bootstrapper.exe (PID: 5252)
- setup.exe (PID: 5872)
- setup.exe (PID: 3080)
Reads Environment values
- setup.exe (PID: 7408)
- setup.exe (PID: 7928)
- setup.exe (PID: 5872)
- setup.exe (PID: 6484)
- setup.exe (PID: 3080)
Create files in a temporary directory
- setup.exe (PID: 7408)
- setup.exe (PID: 7928)
- setup.exe (PID: 5872)
- setup.exe (PID: 6484)
- vs_setup_bootstrapper.exe (PID: 5252)
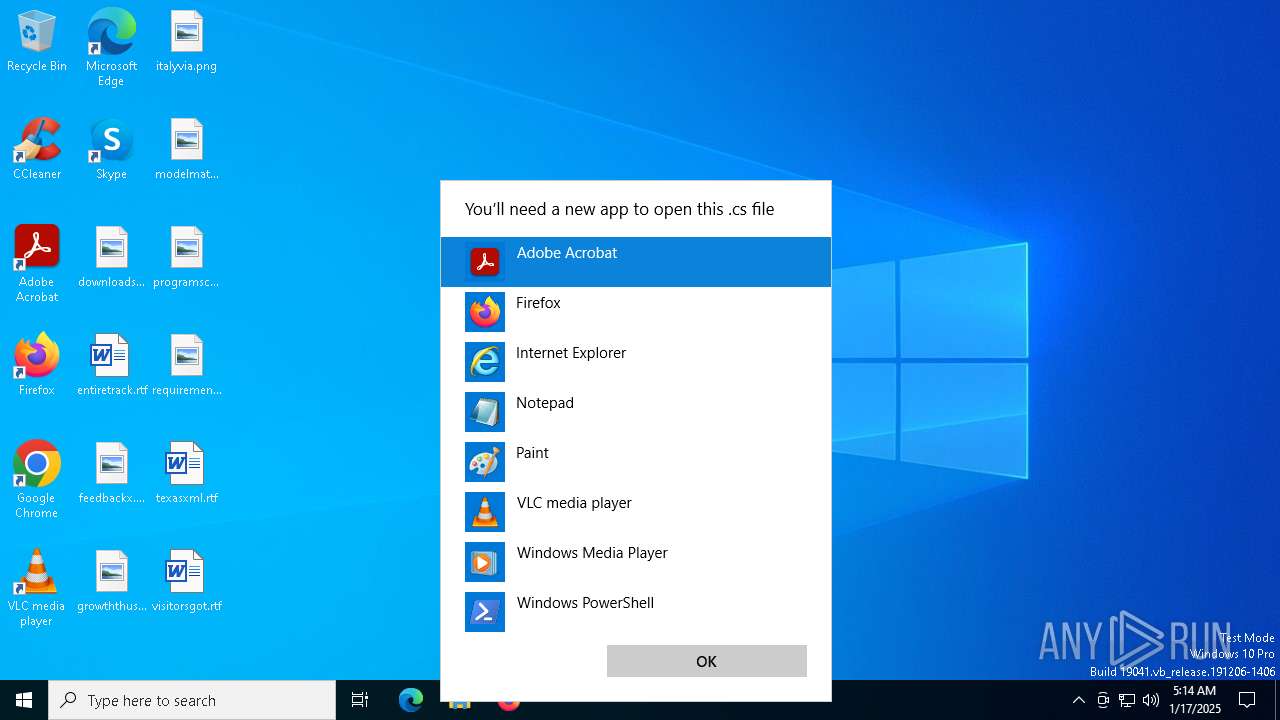
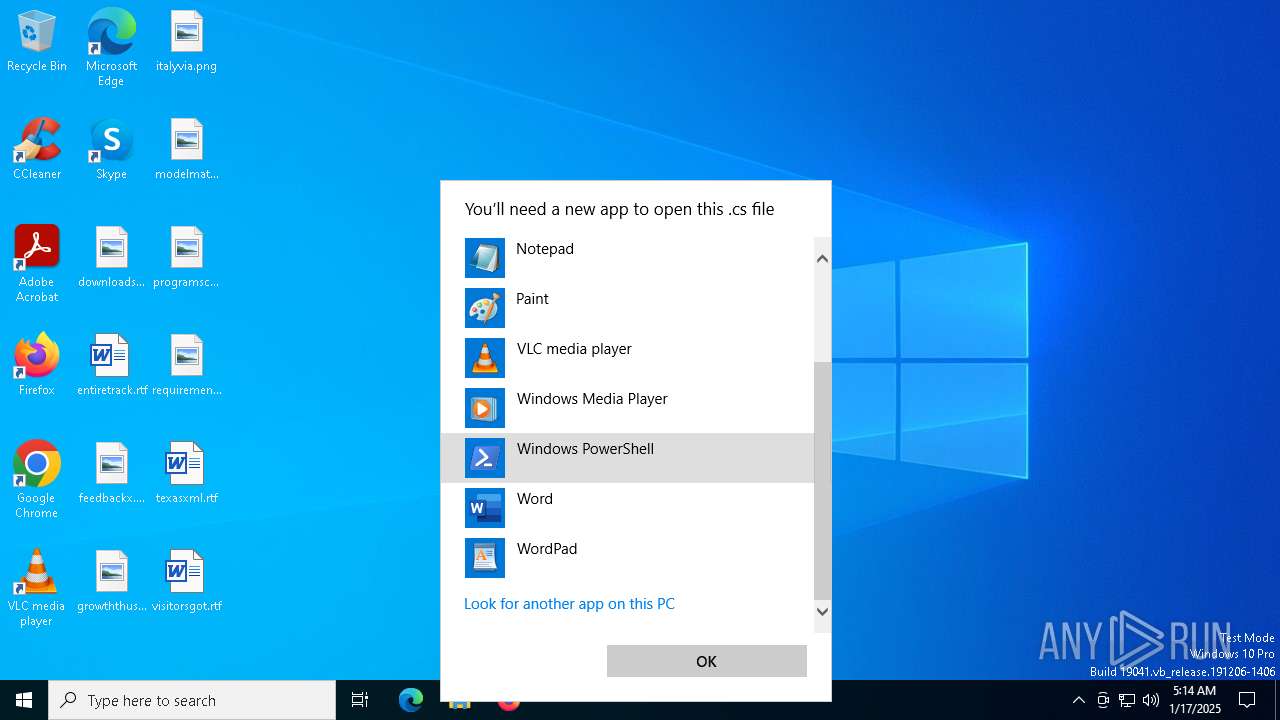
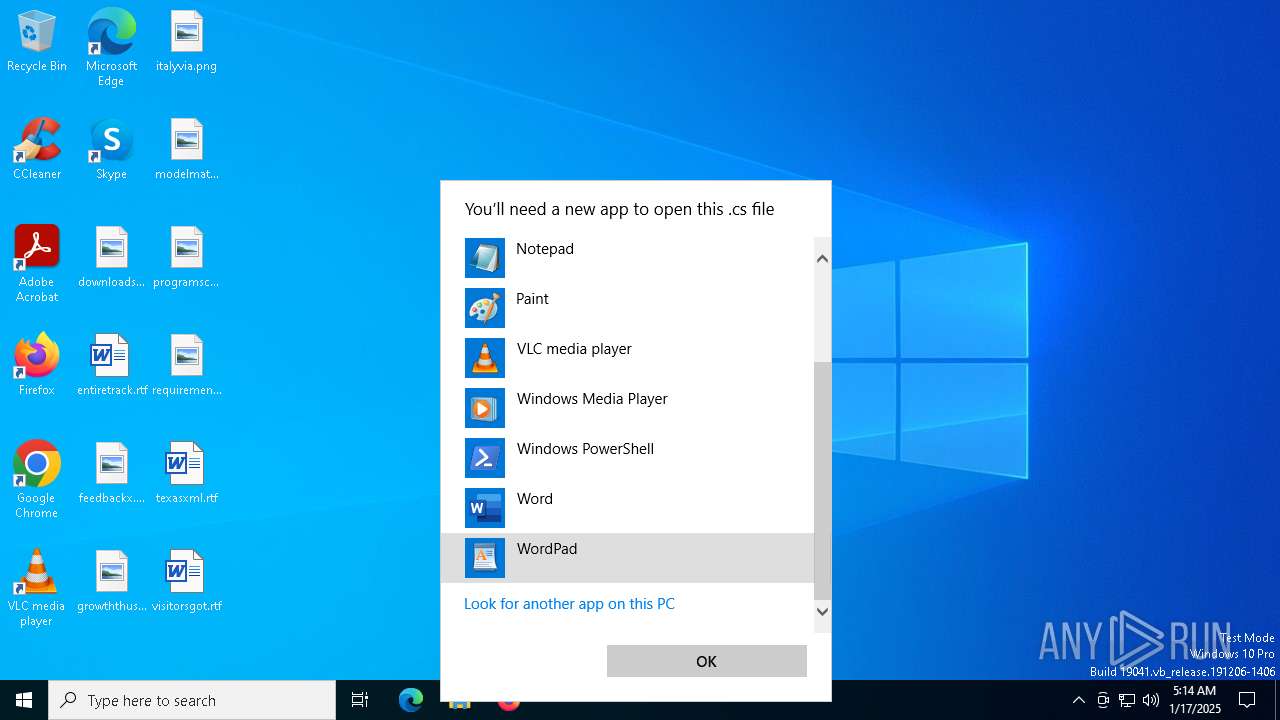
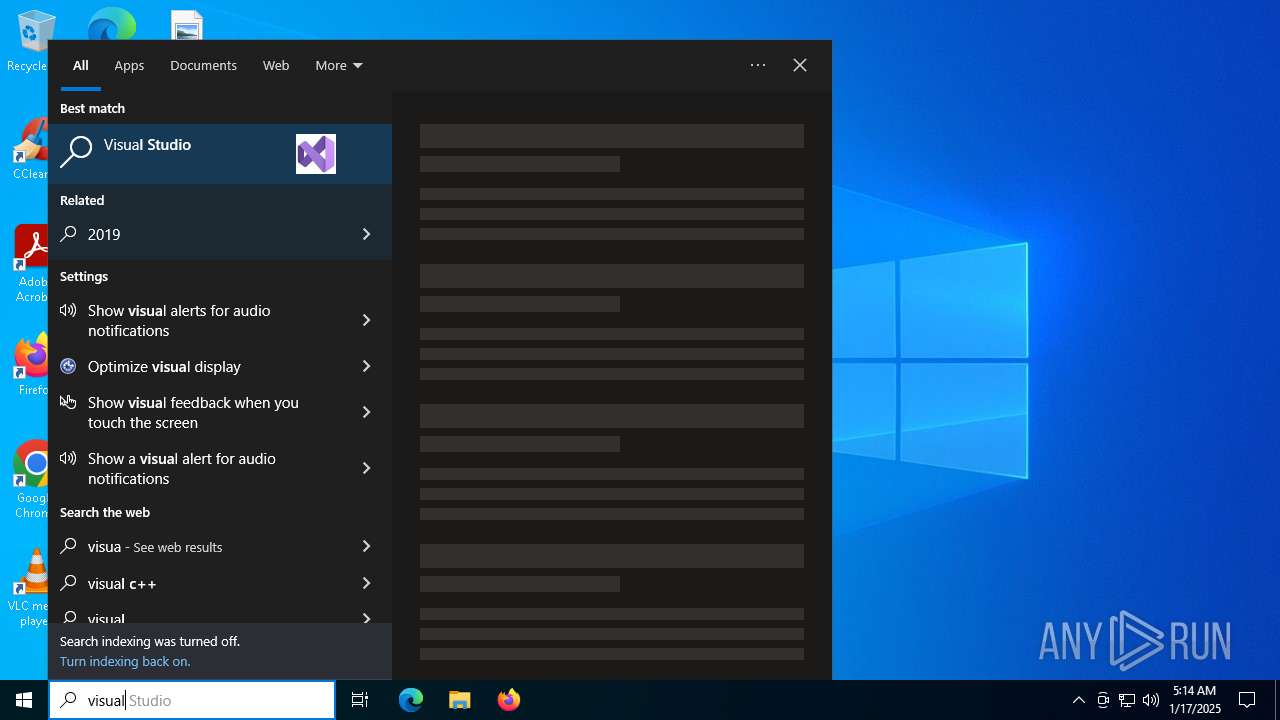
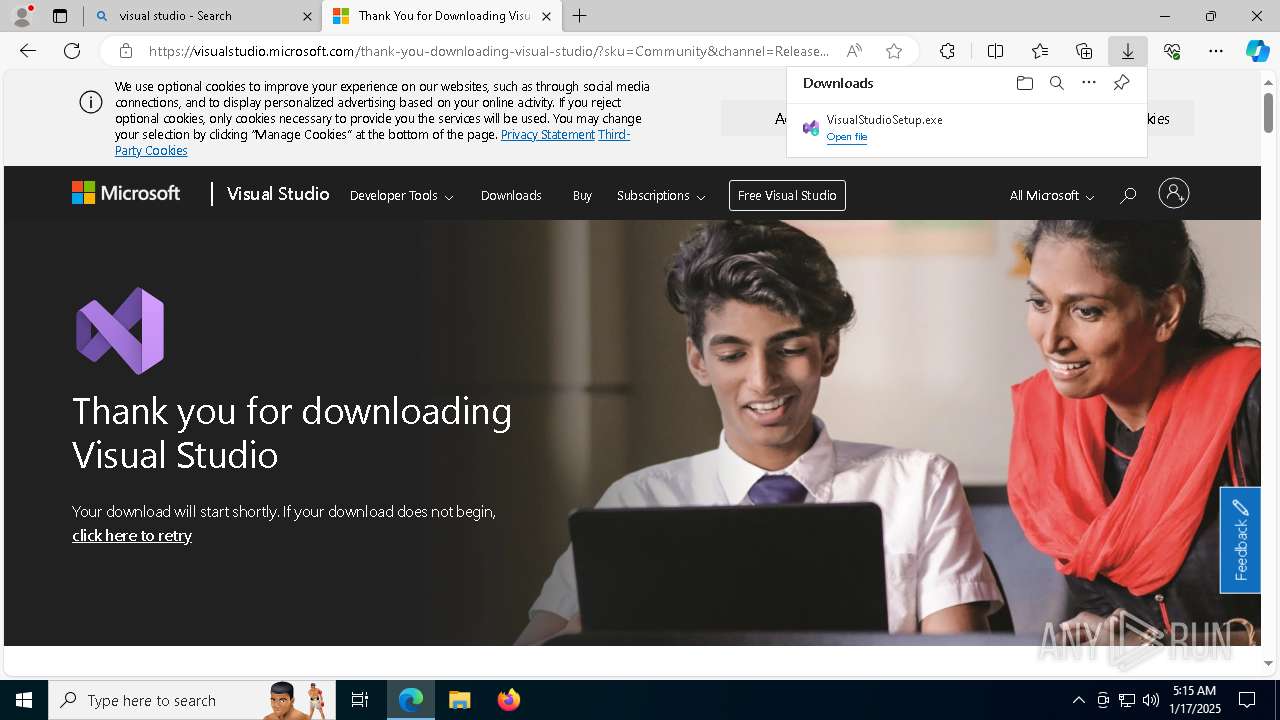
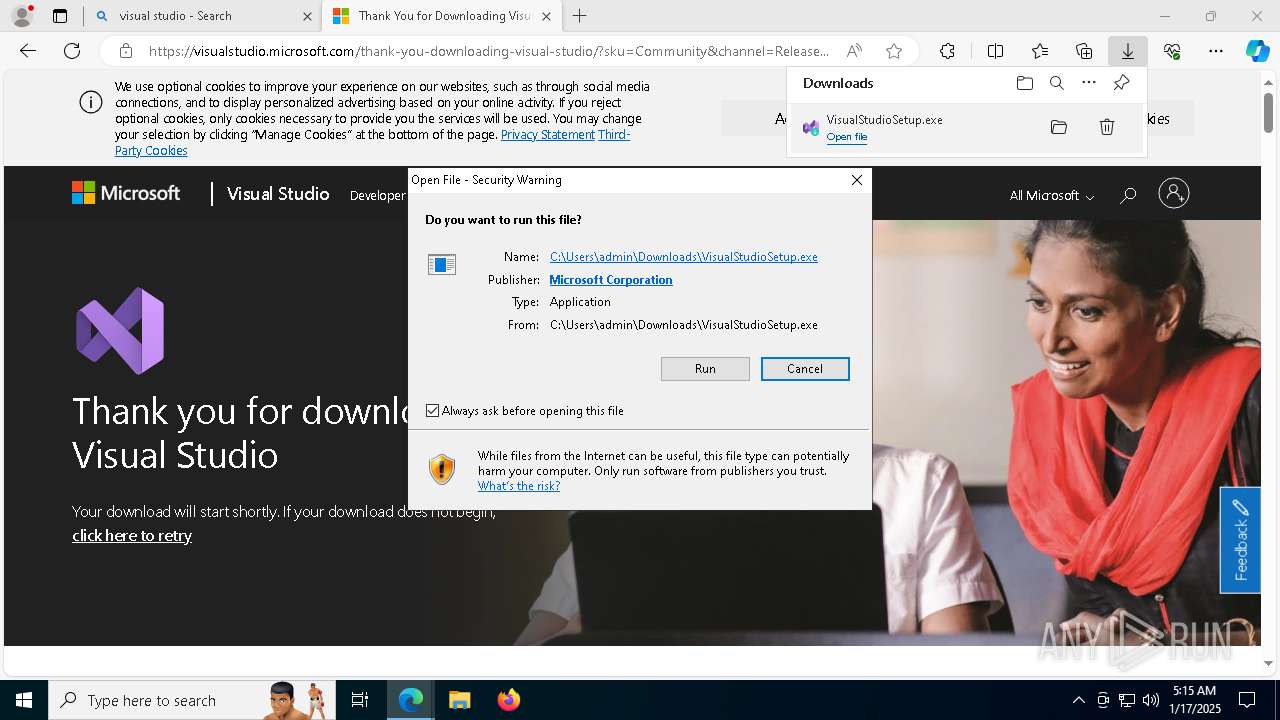
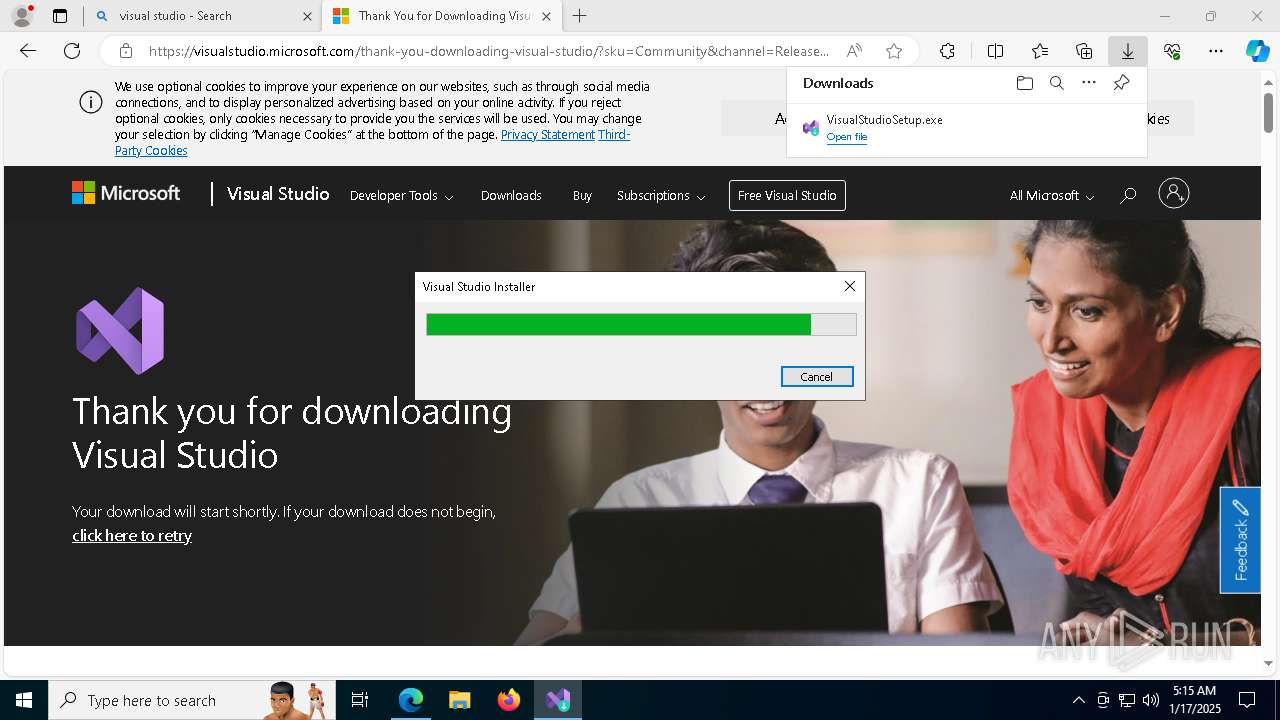
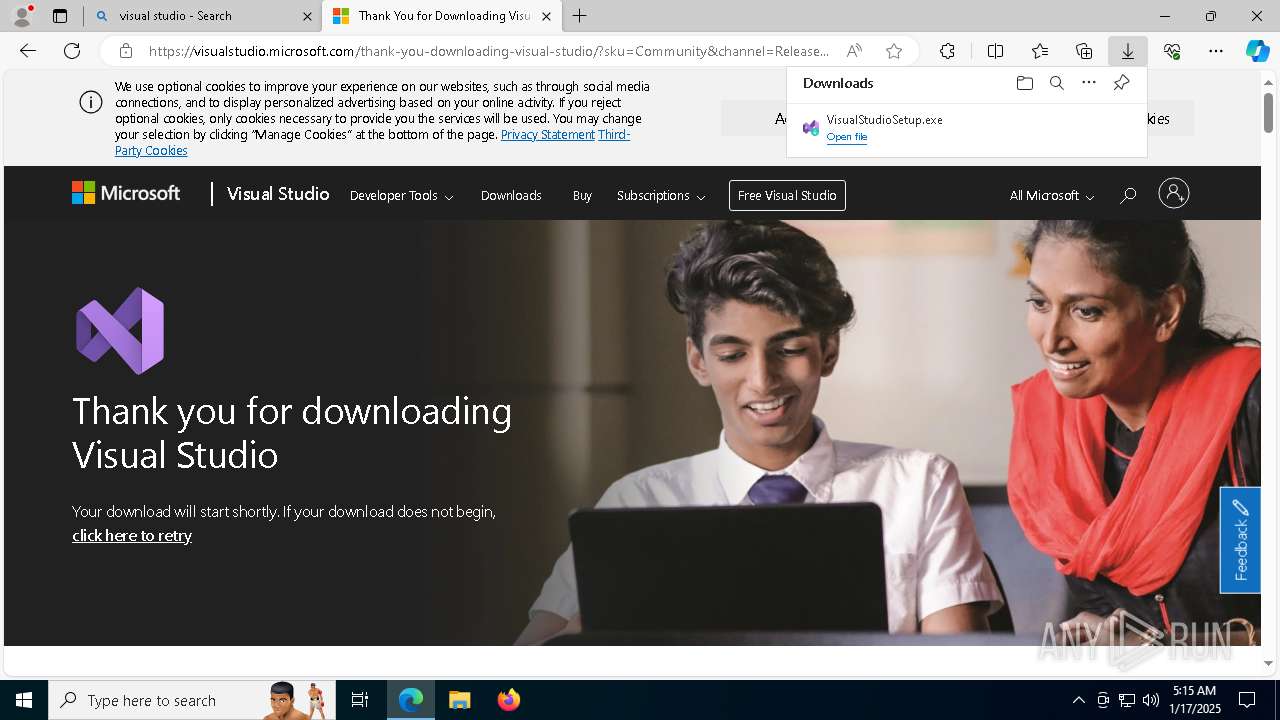
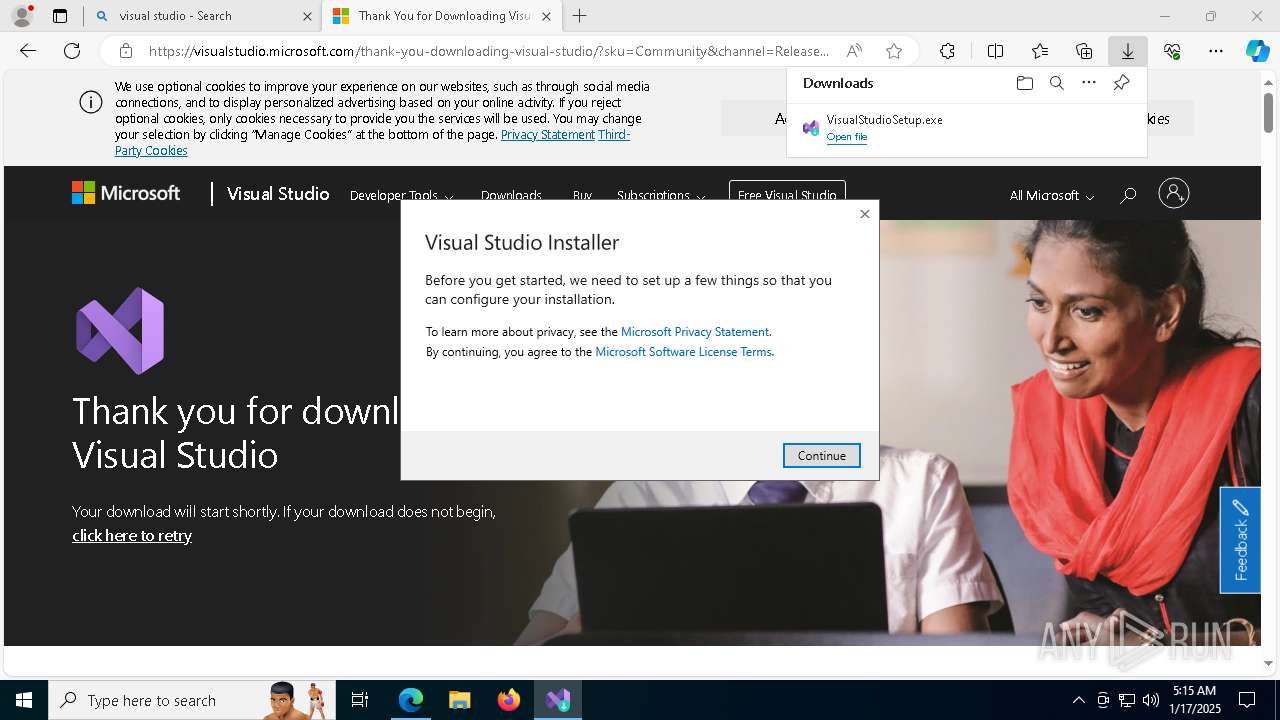
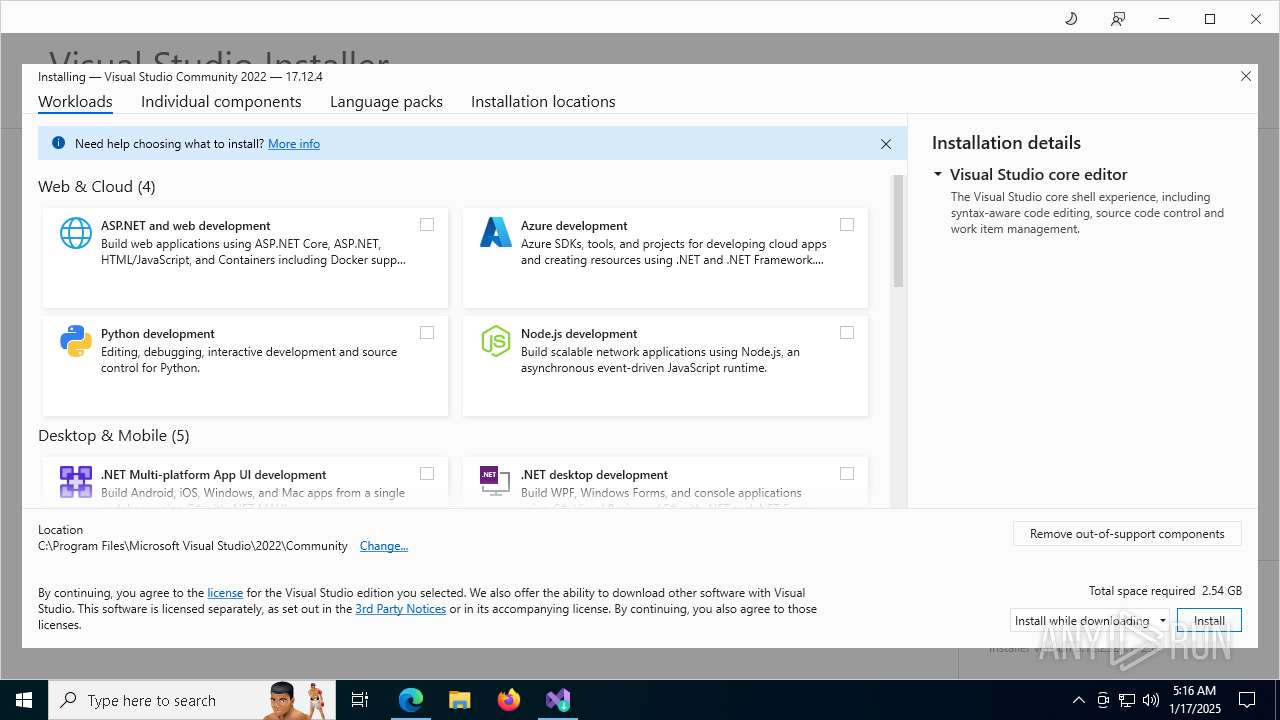
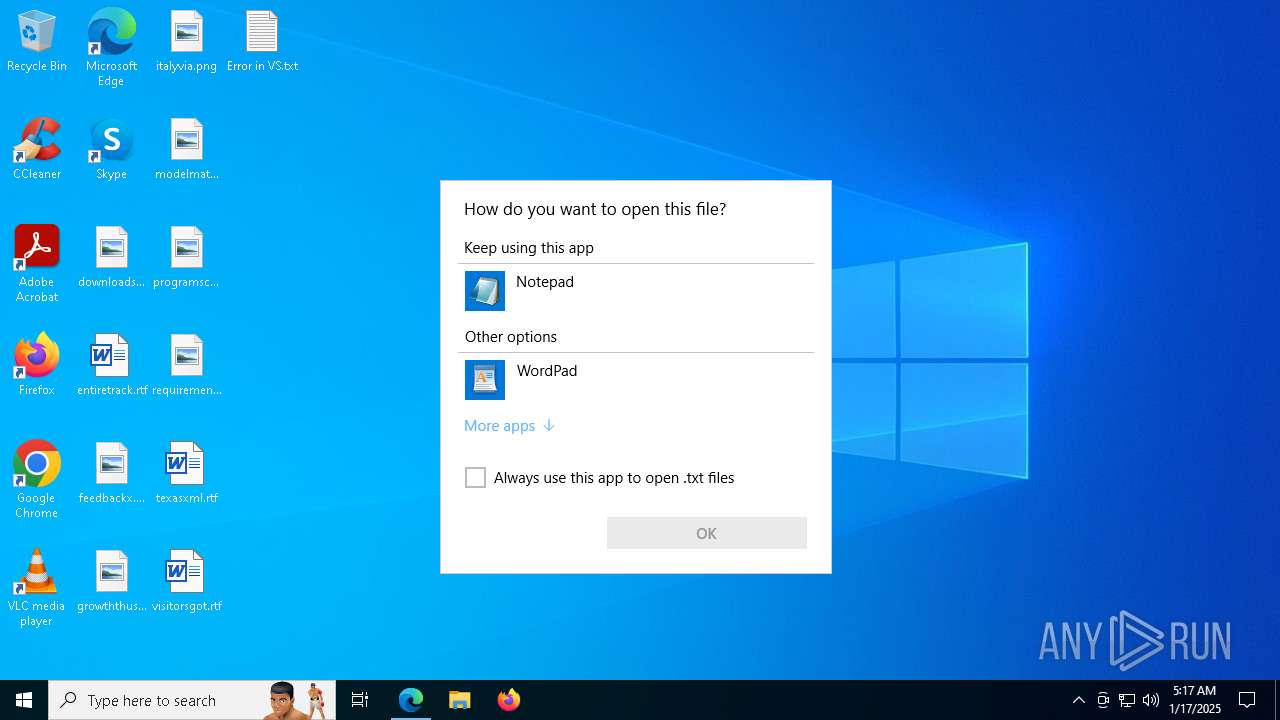
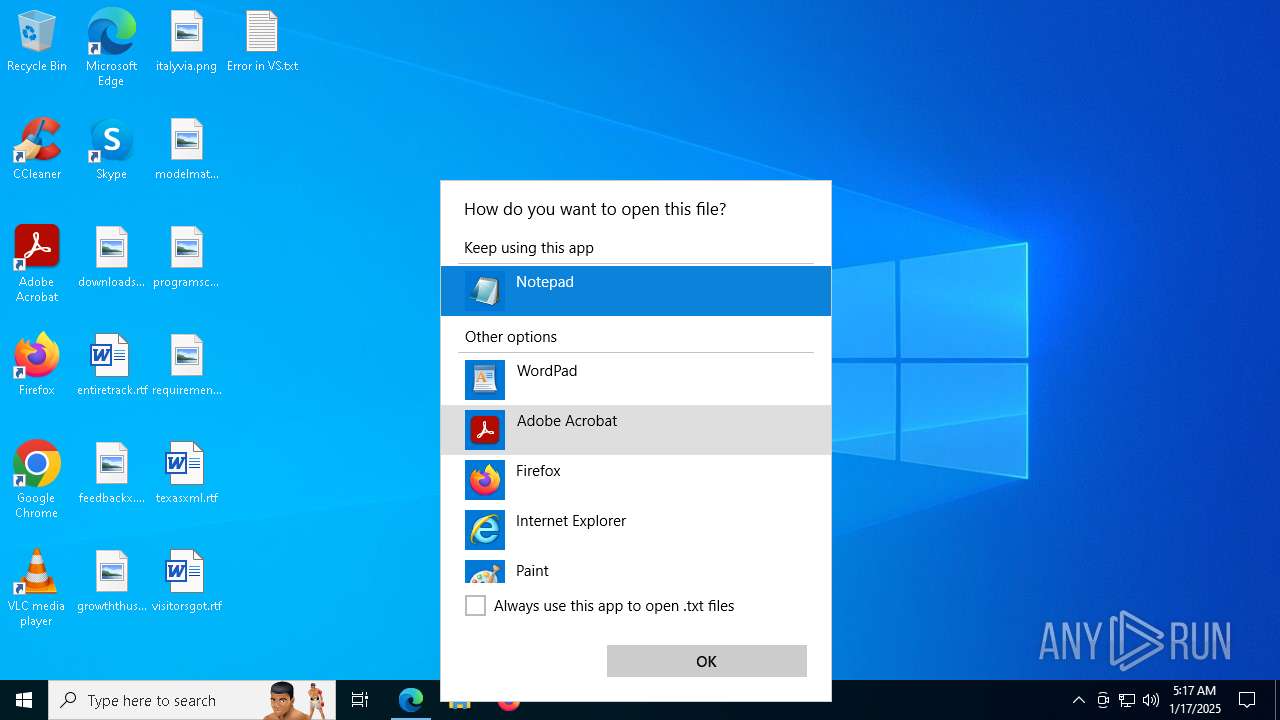
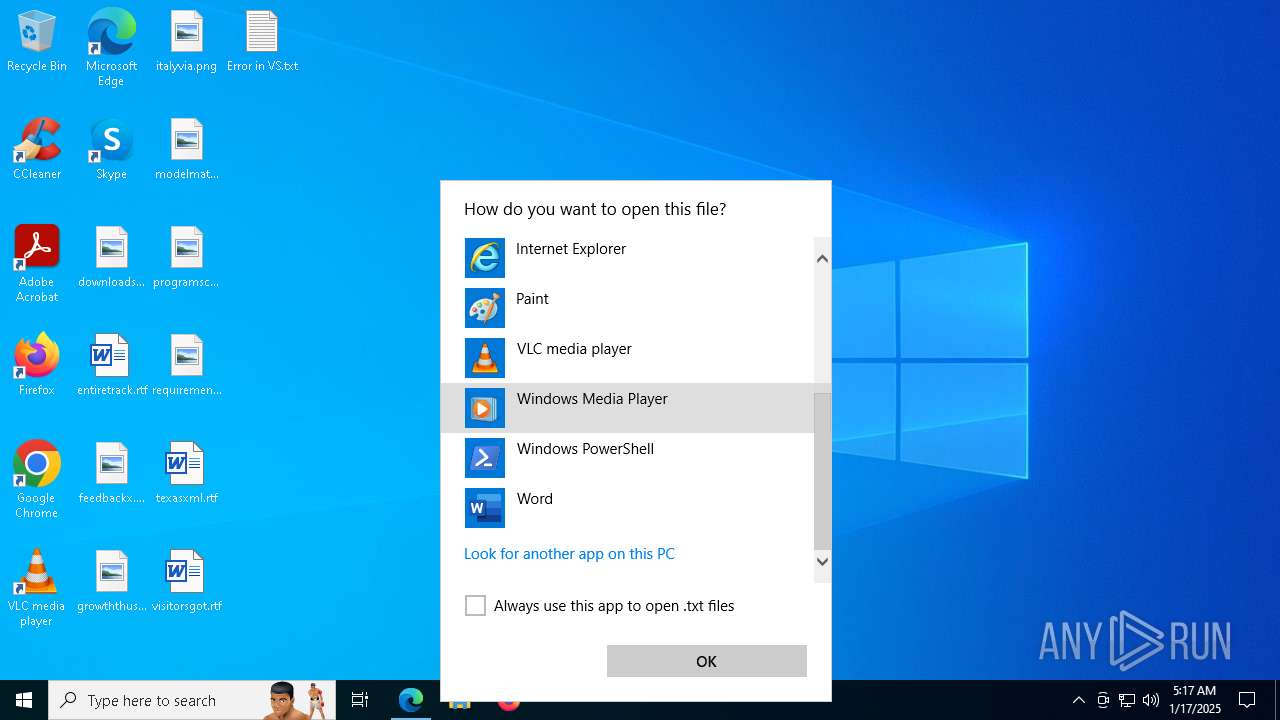
Manual execution by a user
- notepad.exe (PID: 7304)
- setup.exe (PID: 7928)
The process uses the downloaded file
- setup.exe (PID: 7928)
- setup.exe (PID: 7408)
- setup.exe (PID: 5872)
- setup.exe (PID: 6484)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
202
Monitored processes
15
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3080 | "C:\Program Files (x86)\Microsoft Visual Studio\Installer.f816a754231d43d68166005669020746\setup.exe" elevate --activityId 0daf74a5-40a4-49fa-91d9-88c9b7c29e68 --handle 459546 --locale en-US --pid 6484 --pipeName a486bc3c33bd48c38143a882b03c6ba4 --serializedSession "{\"TelemetryLevel\":null,\"IsOptedIn\":true,\"HostName\":\"Default\",\"AppInsightsInstrumentationKey\":\"f144292e-e3b2-4011-ac90-20e5c03fbce5\",\"AsimovInstrumentationKey\":\"AIF-312cbd79-9dbb-4c48-a7da-3cc2a931cb70\",\"CollectorApiKey\":\"f3e86b4023cc43f0be495508d51f588a-f70d0e59-0fb0-4473-9f19-b4024cc340be-7296\",\"AppId\":1000,\"UserId\":\"cf6ac4dc-0918-4271-ab7e-b19055d556f3\",\"Id\":\"e7b461be-f958-48d9-bd42-ff9e561cf3f0\",\"ProcessStartTime\":638726878619039607,\"SkuName\":null,\"VSExeVersion\":null,\"BucketFiltersToEnableWatsonForFaults\":[{\"AdditionalProperties\":[],\"Id\":\"a02930d9-c607-41c3-8698-0fd9196735a5\",\"WatsonEventType\":\"VisualStudioNonFatalErrors2\",\"BucketParameterFilters\":[null,null,\"(?i)vs\\.setup.*\",null,null,null,null,null,null,null]},{\"AdditionalProperties\":[],\"Id\":\"64a13603-6d89-42e4-a299-13f77e5ad306\",\"WatsonEventType\":\"VisualStudioNonFatalErrors2\",\"BucketParameterFilters\":[null,null,\"(?i)vs\\.willow.*\",null,null,null,null,null,null,null]}],\"BucketFiltersToAddDumpsToFaults\":[]}" | C:\Program Files (x86)\Microsoft Visual Studio\Installer.f816a754231d43d68166005669020746\setup.exe | setup.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: HIGH Description: Visual Studio Installer Version: 3.13.1044.14880 Modules
| |||||||||||||||
| 5064 | "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Search application Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5092 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | getmac.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5252 | "C:\Users\admin\AppData\Local\Temp\9982fb1247c645e09ce60da98afdafa7\vs_setup_bootstrapper.exe" -x:"C:\Users\admin\AppData\Local\Temp\2779d66db8c541f183309d4138371bdd" -q | C:\Users\admin\AppData\Local\Temp\9982fb1247c645e09ce60da98afdafa7\vs_setup_bootstrapper.exe | setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual Studio Installer Exit code: 0 Version: 17.13.35617.110 Modules
| |||||||||||||||
| 5872 | "C:\Program Files (x86)\Microsoft Visual Studio\Installer\setup.exe" elevate --activityId 0daf74a5-40a4-49fa-91d9-88c9b7c29e68 --handle 459546 --locale en-US --pid 7928 --pipeName 8e76655c1af342c3a1b5e3cbd8bb3ad1 --serializedSession "{\"TelemetryLevel\":null,\"IsOptedIn\":true,\"HostName\":\"Default\",\"AppInsightsInstrumentationKey\":\"f144292e-e3b2-4011-ac90-20e5c03fbce5\",\"AsimovInstrumentationKey\":\"AIF-312cbd79-9dbb-4c48-a7da-3cc2a931cb70\",\"CollectorApiKey\":\"f3e86b4023cc43f0be495508d51f588a-f70d0e59-0fb0-4473-9f19-b4024cc340be-7296\",\"AppId\":1000,\"UserId\":\"cf6ac4dc-0918-4271-ab7e-b19055d556f3\",\"Id\":\"e7b461be-f958-48d9-bd42-ff9e561cf3f0\",\"ProcessStartTime\":638726878619039607,\"SkuName\":null,\"VSExeVersion\":null,\"BucketFiltersToEnableWatsonForFaults\":[{\"AdditionalProperties\":[],\"Id\":\"a02930d9-c607-41c3-8698-0fd9196735a5\",\"WatsonEventType\":\"VisualStudioNonFatalErrors2\",\"BucketParameterFilters\":[null,null,\"(?i)vs\\.setup.*\",null,null,null,null,null,null,null]},{\"AdditionalProperties\":[],\"Id\":\"64a13603-6d89-42e4-a299-13f77e5ad306\",\"WatsonEventType\":\"VisualStudioNonFatalErrors2\",\"BucketParameterFilters\":[null,null,\"(?i)vs\\.willow.*\",null,null,null,null,null,null,null]}],\"BucketFiltersToAddDumpsToFaults\":[]}" | C:\Program Files (x86)\Microsoft Visual Studio\Installer\setup.exe | setup.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: HIGH Description: Visual Studio Installer Exit code: 0 Version: 3.12.2320.19252 Modules
| |||||||||||||||
| 6372 | "C:\Users\admin\AppData\Local\Temp\892c9219ee9443bdaa6a\vs_bootstrapper_d15\vs_setup_bootstrapper.exe" --env "_SFX_CAB_EXE_PACKAGE:C:\Users\admin\Downloads\VisualStudioSetup.exe _SFX_CAB_EXE_ORIGINALWORKINGDIR:C:\Users\admin\Downloads" | C:\Users\admin\AppData\Local\Temp\892c9219ee9443bdaa6a\vs_bootstrapper_d15\vs_setup_bootstrapper.exe | VisualStudioSetup.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: HIGH Description: Visual Studio Installer Exit code: 0 Version: 3.12.2320.19252 Modules
| |||||||||||||||
| 6484 | "C:\Program Files (x86)\Microsoft Visual Studio\Installer.f816a754231d43d68166005669020746\setup.exe" install --activate --activityId 0daf74a5-40a4-49fa-91d9-88c9b7c29e68 --cache --channelId VisualStudio.17.Preview --contextSubDirectory f88238aa9a404be0b33d410c94759998 --continue --installerOnlyUpdate --installerPipe a486bc3c33bd48c38143a882b03c6ba4 --installerPipeHandshake dfc1c6875fdc4877a936934512dc1a44 --locale en-US --parent 459546 --path cache=C:\ProgramData\Microsoft\VisualStudio\Packages "shared=C:\Program Files (x86)\Microsoft Visual Studio\Shared" --pipe bcd16687-2b34-4103-8254-728d90666508 --productId Microsoft.VisualStudio.Product.Enterprise --serializedSession "{\"TelemetryLevel\":null,\"IsOptedIn\":true,\"HostName\":\"Default\",\"AppInsightsInstrumentationKey\":\"f144292e-e3b2-4011-ac90-20e5c03fbce5\",\"AsimovInstrumentationKey\":\"AIF-312cbd79-9dbb-4c48-a7da-3cc2a931cb70\",\"CollectorApiKey\":\"f3e86b4023cc43f0be495508d51f588a-f70d0e59-0fb0-4473-9f19-b4024cc340be-7296\",\"AppId\":1000,\"UserId\":\"cf6ac4dc-0918-4271-ab7e-b19055d556f3\",\"Id\":\"e7b461be-f958-48d9-bd42-ff9e561cf3f0\",\"ProcessStartTime\":638726878619039607,\"SkuName\":null,\"VSExeVersion\":null,\"BucketFiltersToEnableWatsonForFaults\":[{\"AdditionalProperties\":[],\"Id\":\"a02930d9-c607-41c3-8698-0fd9196735a5\",\"WatsonEventType\":\"VisualStudioNonFatalErrors2\",\"BucketParameterFilters\":[null,null,\"(?i)vs\\.setup.*\",null,null,null,null,null,null,null]},{\"AdditionalProperties\":[],\"Id\":\"64a13603-6d89-42e4-a299-13f77e5ad306\",\"WatsonEventType\":\"VisualStudioNonFatalErrors2\",\"BucketParameterFilters\":[null,null,\"(?i)vs\\.willow.*\",null,null,null,null,null,null,null]}],\"BucketFiltersToAddDumpsToFaults\":[]}" --sessionTheme Light | C:\Program Files (x86)\Microsoft Visual Studio\Installer.f816a754231d43d68166005669020746\setup.exe | setup.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: Visual Studio Installer Version: 3.13.1044.14880 Modules
| |||||||||||||||
| 6828 | "getmac" | C:\Windows\SysWOW64\getmac.exe | — | vs_setup_bootstrapper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Displays NIC MAC information Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
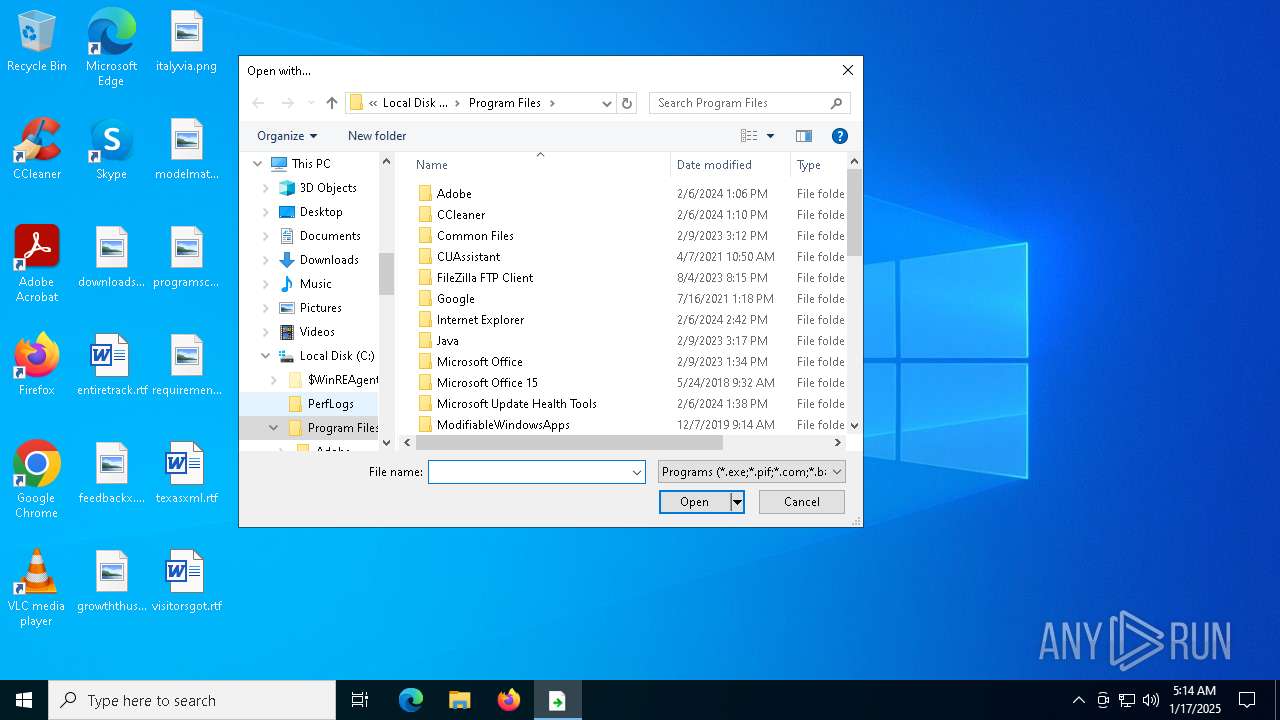
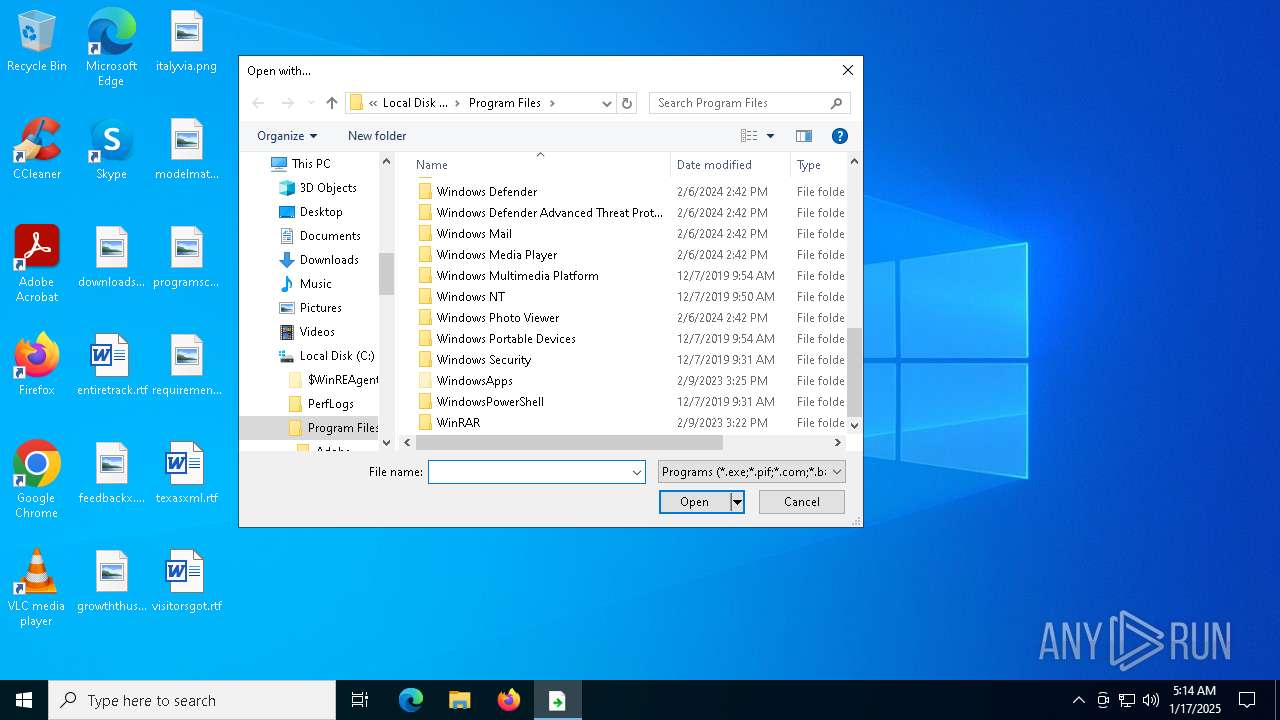
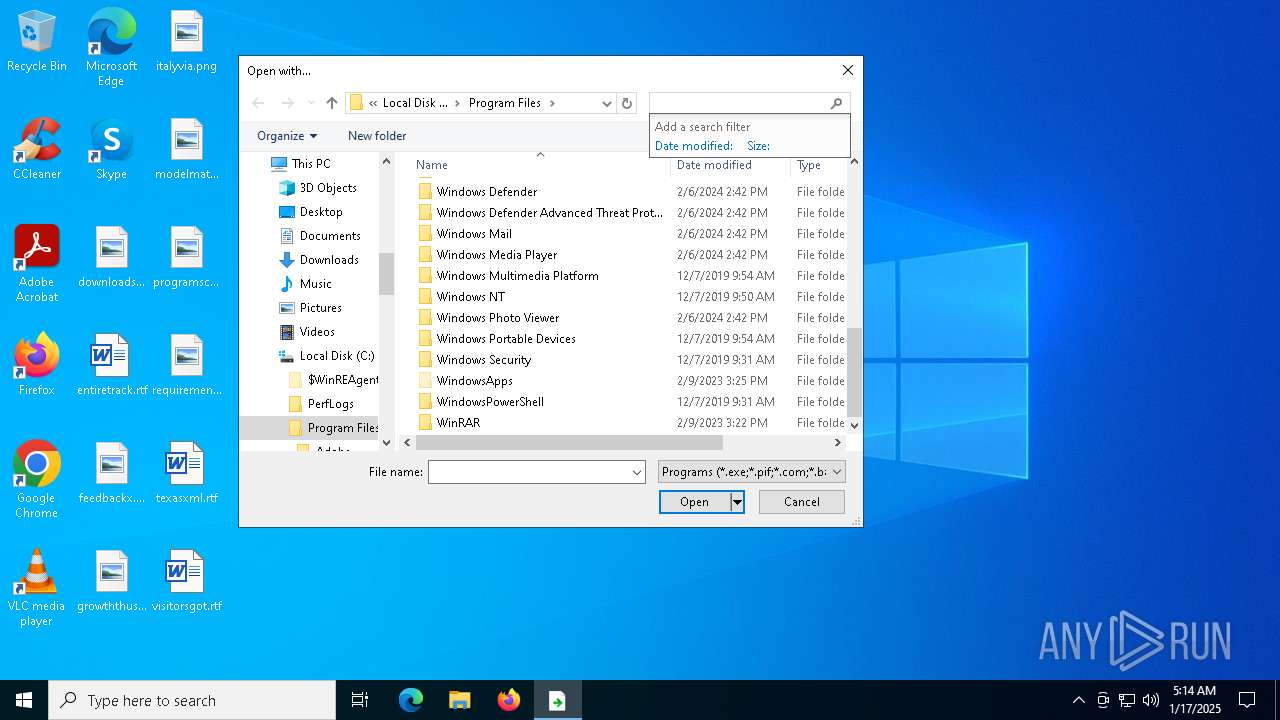
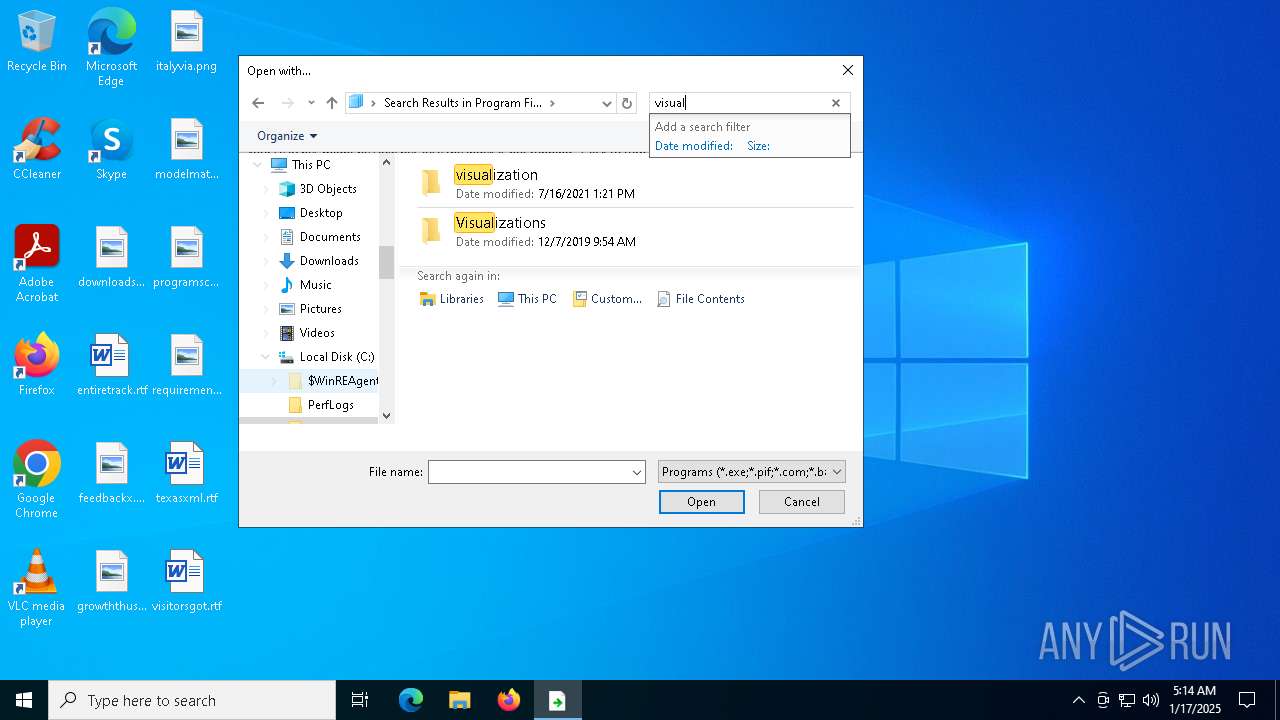
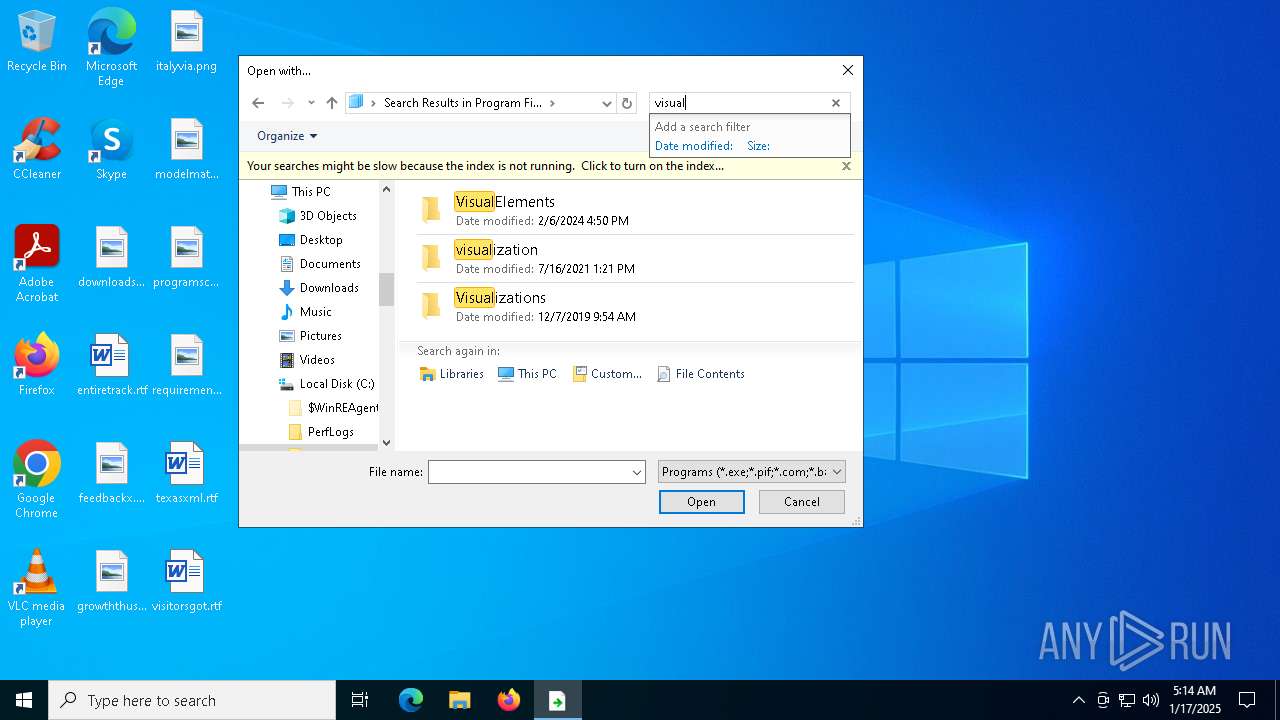
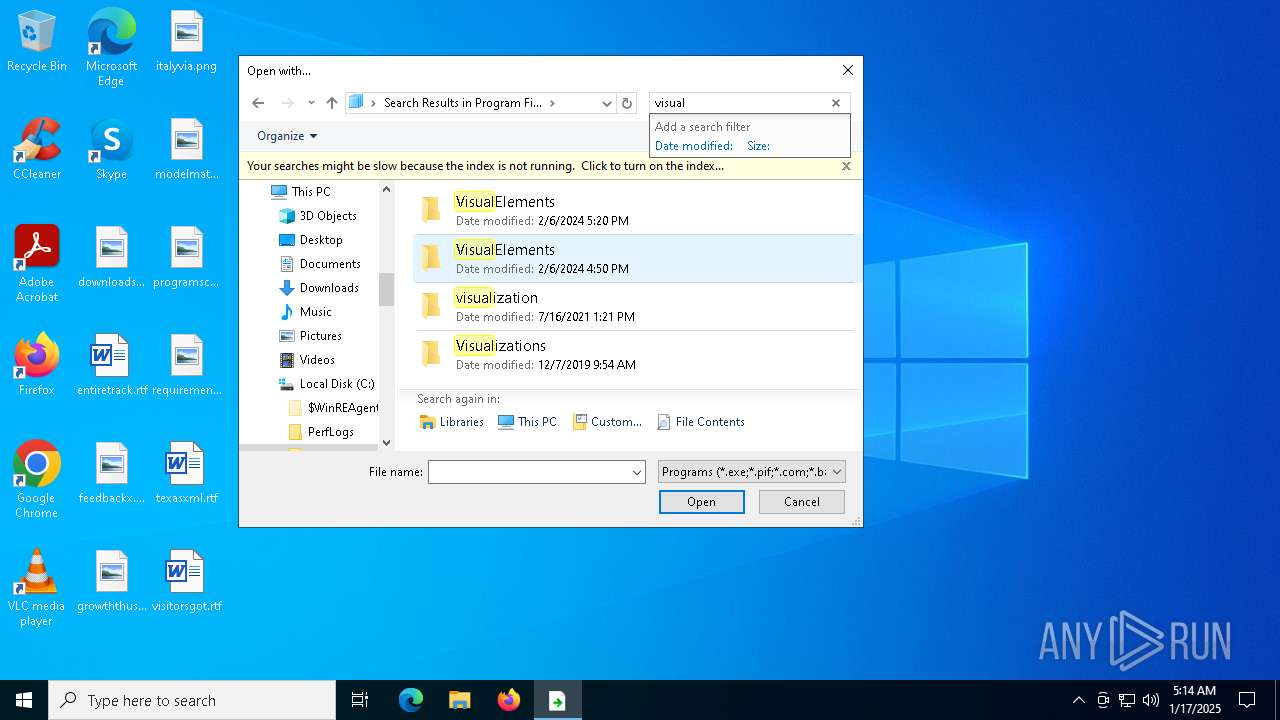
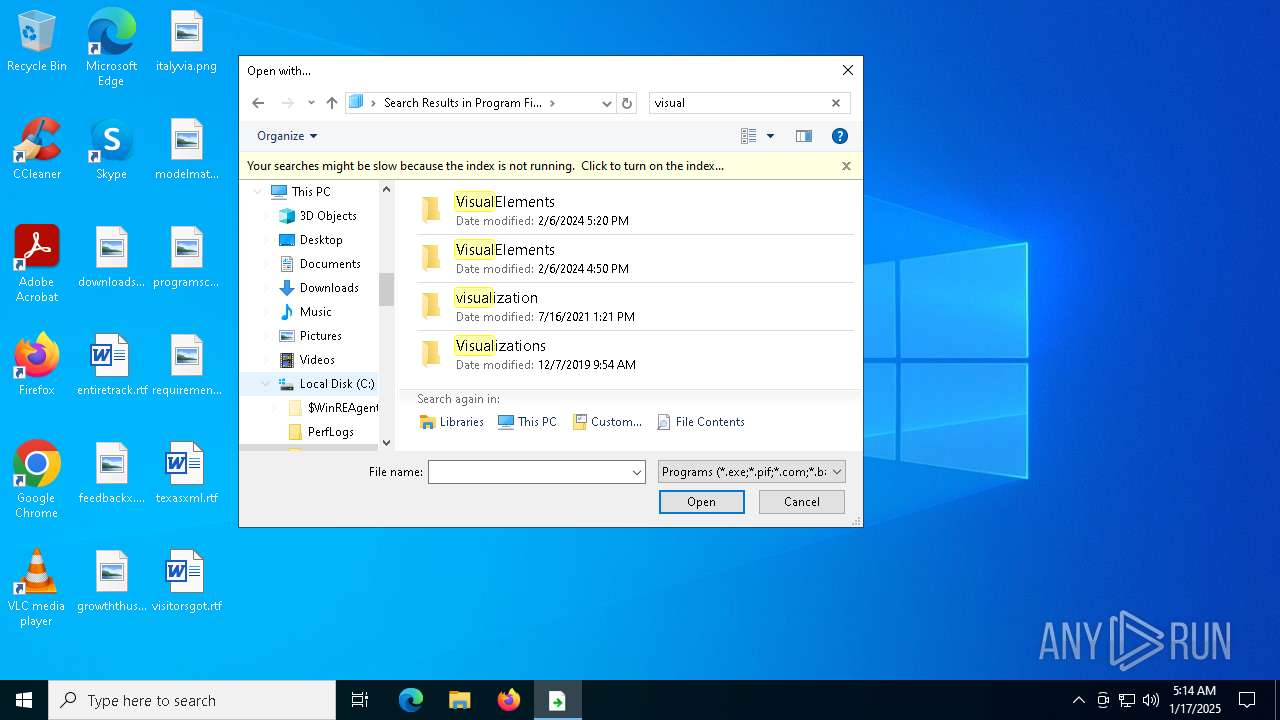
| 6980 | "C:\WINDOWS\System32\OpenWith.exe" "C:\Users\admin\AppData\Local\Temp\Error in VS.txt.cs" | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7304 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\Error in VS.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
59 286
Read events
58 847
Write events
415
Delete events
24
Modification events
| (PID) Process: | (6980) OpenWith.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (6980) OpenWith.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 040000000E0000000300000000000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (6980) OpenWith.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\40\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Generic | |||
| (PID) Process: | (6980) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 105 | |||
| (PID) Process: | (6980) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: 2BE7896700000000 | |||
| (PID) Process: | (6980) OpenWith.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\40\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | Mode |
Value: 4 | |||
| (PID) Process: | (6980) OpenWith.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\40\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | LogicalViewMode |
Value: 1 | |||
| (PID) Process: | (6980) OpenWith.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\40\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | FFlags |
Value: | |||
| (PID) Process: | (6980) OpenWith.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\40\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | IconSize |
Value: 16 | |||
| (PID) Process: | (6980) OpenWith.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\40\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | Sort |
Value: 000000000000000000000000000000000100000030F125B7EF471A10A5F102608C9EEBAC0A00000001000000 | |||
Executable files
915
Suspicious files
161
Text files
457
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5064 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\67\mIBK4Tj4MH4TuENc-SRjlybWA2M[1].css | text | |
MD5:61218F90D3B3B1F74B9253D4E5DDF682 | SHA256:0553F7C64CC8A8034532FF32F86F5B0DDB061D03843B66C0868CDCA1674E03CC | |||
| 5064 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\67\wU-YmSK-j9YaNg2gj_x4wAl_UoI[1].css | text | |
MD5:C1AC4CCA38EA836717738D7CF72B45B9 | SHA256:E4C0BF089E674482FA2FE7D558F64F9D3EBDD414EAED18908E34A6140D09B727 | |||
| 5064 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\67\Cj4mQnDN_eMyYEqsEbjRrJ2Ttec.br[1].js | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 5064 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\Microsoft\Internet Explorer\DOMStore\ZWUI0EBX\www.bing[1].xml | text | |
MD5:BACA85B7095DF5221B5FA782D7C2FA2A | SHA256:67D0DDE2CF03B1C600C5D31715D3091EAF1FED2C2F8CCBB3252328ED42C41FFC | |||
| 5064 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\67\vOJNaIfAXvJzmnBm845ss-M9YR8[1].css | text | |
MD5:87BBB1A289EDC24C9F06B88229765467 | SHA256:85B291C46F9D1EEEC71DB839F649D748F48B203EA836F3ACE3B9B761947D960C | |||
| 5064 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\67\4BpQ1bD8vX1mXuJObN-gg9RqkyQ.br[1].js | binary | |
MD5:8465A334065673EB6A6487C8D87539DB | SHA256:84ED6C495B322B0F2213CC33EC6C652D84D82E010C928B1141DB2290D4365F3D | |||
| 5064 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\67\QNBBNqWD9F_Blep-UqQSqnMp-FI[1].css | text | |
MD5:77373397A17BD1987DFCA2E68D022ECF | SHA256:A319AF2E953E7AFDA681B85A62F629A5C37344AF47D2FCD23AB45E1D99497F13 | |||
| 5064 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\67\0u2b9EXo8LdXut1MFm4AD0phBuM.br[1].js | binary | |
MD5:8C0F73D4C854DC52B555898FEF7EDB54 | SHA256:B652F917E744E7A4EADB5DF108D622FD18C793E80445FAA69B1BFFC97BE2529E | |||
| 5064 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\67\76h-lqe82bg-bnu-ApkwUALogkQ.br[1].js | binary | |
MD5:88B4876820BB8069FE375BC4577DAFC9 | SHA256:19BAD3107546F7914AB0F1CE545F187D7DD26F90D05F26C3C326D1BD941F0EA8 | |||
| 5064 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\TokenBroker\Cache\95d9a2a97a42f02325559b453ba7f8fe839baa18.tbres | binary | |
MD5:E74E230F5AF46D0DE5CA102D84448BF8 | SHA256:9C2A8980300FC73F42F78C2B689DB79B3AF702D3EB46239318EA679A578E82F4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
63
TCP/UDP connections
238
DNS requests
202
Threats
21
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3576 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.72:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3576 | svchost.exe | GET | 200 | 2.16.164.72:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2072 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.16.164.72:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
3576 | svchost.exe | 2.16.164.72:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
3576 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5064 | SearchApp.exe | 2.23.227.208:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
5064 | SearchApp.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1176 | svchost.exe | 20.190.160.22:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6372 | vs_setup_bootstrapper.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
6372 | vs_setup_bootstrapper.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
6372 | vs_setup_bootstrapper.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
7408 | setup.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
7408 | setup.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
7408 | setup.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
7408 | setup.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
7928 | setup.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
7928 | setup.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
7928 | setup.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |