| File name: | 2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn |
| Full analysis: | https://app.any.run/tasks/4458e0c9-d1e2-4aa7-a2f3-8aa046653811 |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 05:53:26 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | 61C0CDA2C9D7E328283895F9E9D65F04 |
| SHA1: | 6574202BCF31F1F9F47659CE336934F3739ECDE6 |
| SHA256: | F69939FA686A9556C68AE1F04EB4BC86D935ED19B998E309D5D8ED06610F51B0 |
| SSDEEP: | 49152:5c5T3FD9OvO9O/FltgXY6LB6wXe/CZ8ILhCGKbEvwpDcbIh49tuGOU/QV4jWfWW/:5c59EGMNltgJLB6wXdZdUGKbQ3s4jufl |
MALICIOUS
JEEFO has been detected
- 2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe (PID: 7660)
- icsys.icn.exe (PID: 7936)
- explorer.exe (PID: 7956)
- svchost.exe (PID: 8000)
Changes the autorun value in the registry
- explorer.exe (PID: 7956)
- svchost.exe (PID: 8000)
SUSPICIOUS
Executable content was dropped or overwritten
- 2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe (PID: 7660)
- 2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe (PID: 7696)
- spoolsv.exe (PID: 7976)
- icsys.icn.exe (PID: 7936)
- explorer.exe (PID: 7956)
Process drops legitimate windows executable
- 2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe (PID: 7660)
- 2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe (PID: 7696)
- MicrosoftEdgeUpdate.exe (PID: 7824)
Starts application with an unusual extension
- 2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe (PID: 7660)
Starts a Microsoft application from unusual location
- 2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe (PID: 7696)
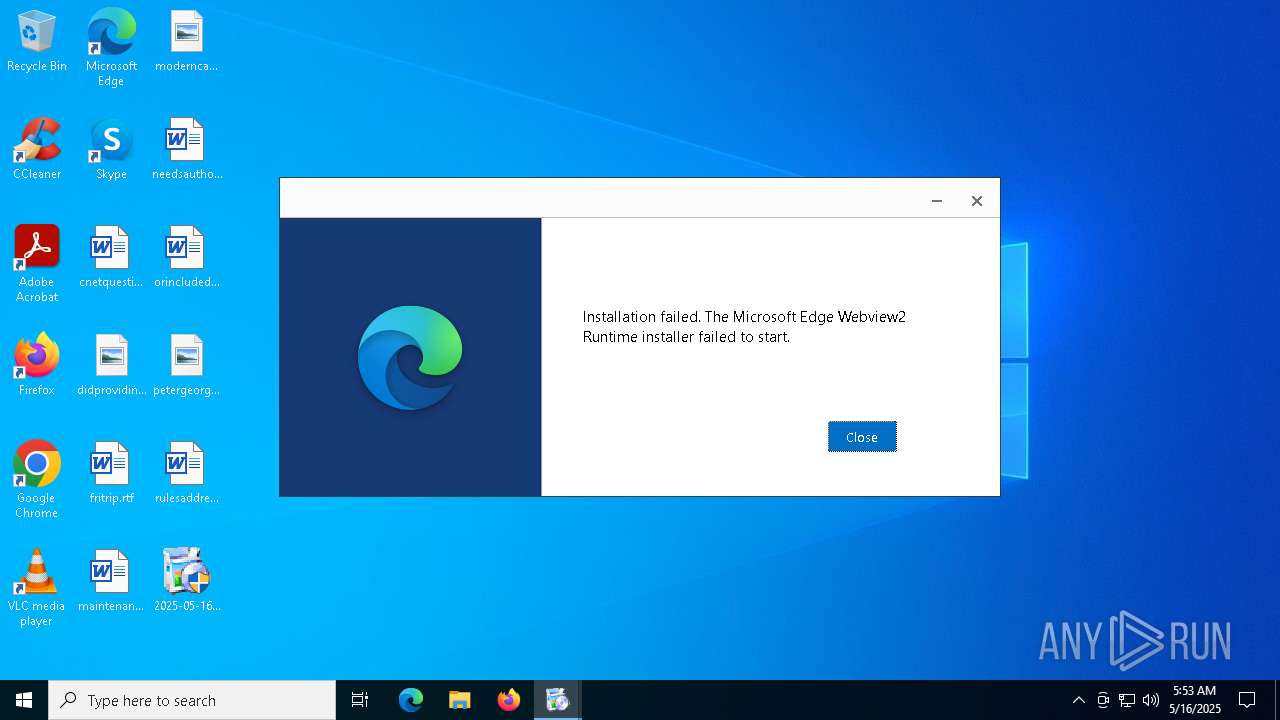
Disables SEHOP
- MicrosoftEdgeUpdate.exe (PID: 7824)
Starts itself from another location
- 2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe (PID: 7660)
- explorer.exe (PID: 7956)
- icsys.icn.exe (PID: 7936)
- spoolsv.exe (PID: 7976)
- svchost.exe (PID: 8000)
The process creates files with name similar to system file names
- icsys.icn.exe (PID: 7936)
- spoolsv.exe (PID: 7976)
Reads security settings of Internet Explorer
- MicrosoftEdgeUpdate.exe (PID: 7824)
Creates or modifies Windows services
- svchost.exe (PID: 8000)
INFO
The sample compiled with english language support
- 2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe (PID: 7660)
- 2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe (PID: 7696)
- MicrosoftEdgeUpdate.exe (PID: 7824)
- spoolsv.exe (PID: 7976)
- icsys.icn.exe (PID: 7936)
- explorer.exe (PID: 7956)
Create files in a temporary directory
- 2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe (PID: 7660)
- explorer.exe (PID: 7956)
- spoolsv.exe (PID: 7976)
- svchost.exe (PID: 8000)
- spoolsv.exe (PID: 8020)
- icsys.icn.exe (PID: 7936)
Checks supported languages
- 2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe (PID: 7660)
- 2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe (PID: 7696)
- MicrosoftEdgeUpdate.exe (PID: 7824)
- icsys.icn.exe (PID: 7936)
- explorer.exe (PID: 7956)
- spoolsv.exe (PID: 7976)
- svchost.exe (PID: 8000)
- spoolsv.exe (PID: 8020)
Creates files in the program directory
- 2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe (PID: 7696)
Checks proxy server information
- MicrosoftEdgeUpdate.exe (PID: 7824)
- slui.exe (PID: 7204)
Reads the computer name
- MicrosoftEdgeUpdate.exe (PID: 7824)
- svchost.exe (PID: 8000)
Reads Environment values
- MicrosoftEdgeUpdate.exe (PID: 7824)
Process checks computer location settings
- MicrosoftEdgeUpdate.exe (PID: 7824)
Reads the software policy settings
- MicrosoftEdgeUpdate.exe (PID: 7824)
- slui.exe (PID: 7204)
Auto-launch of the file from Registry key
- explorer.exe (PID: 7956)
- svchost.exe (PID: 8000)
Manual execution by a user
- explorer.exe (PID: 8104)
- svchost.exe (PID: 8120)
- explorer.exe (PID: 8140)
- svchost.exe (PID: 8188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:04:01 07:08:22+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 106496 |
| InitializedDataSize: | 12288 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x290c |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| ProductName: | Project1 |
| FileVersion: | 1 |
| ProductVersion: | 1 |
| InternalName: | TJprojMain |
| OriginalFileName: | TJprojMain.exe |
Total processes
138
Monitored processes
14
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7204 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7572 | "C:\Users\admin\Desktop\2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe" | C:\Users\admin\Desktop\2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.00 Modules
| |||||||||||||||
| 7660 | "C:\Users\admin\Desktop\2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe" | C:\Users\admin\Desktop\2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 7696 | c:\users\admin\desktop\2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe | C:\Users\admin\Desktop\2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe | 2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Update Setup Version: 1.3.195.45 Modules
| |||||||||||||||
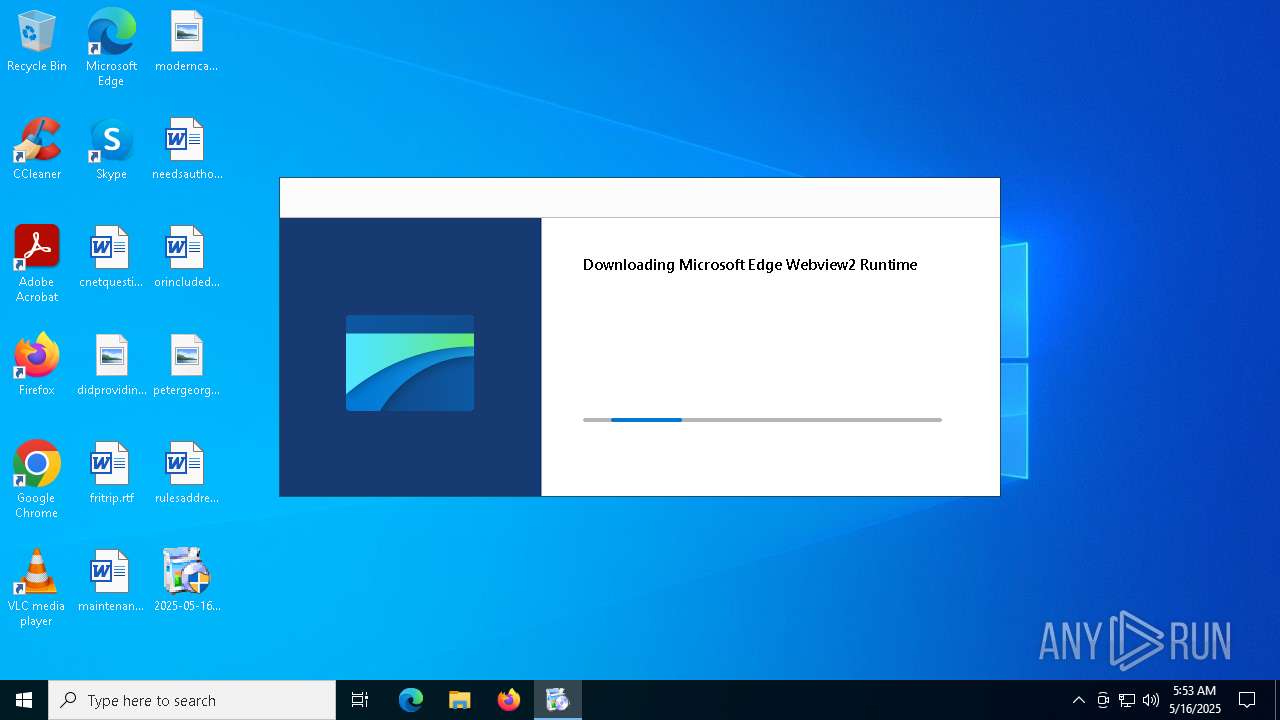
| 7824 | "C:\Program Files (x86)\Microsoft\Temp\EUDAE1.tmp\MicrosoftEdgeUpdate.exe" /installsource taggedmi /install "appguid={F3017226-FE2A-4295-8BDF-00C3A9A7E4C5}&appname=Microsoft%20Edge%20Webview2%20Runtime&needsadmin=prefers" | C:\Program Files (x86)\Microsoft\Temp\EUDAE1.tmp\MicrosoftEdgeUpdate.exe | 2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 7936 | C:\Windows\Resources\Themes\icsys.icn.exe | C:\Windows\Resources\Themes\icsys.icn.exe | 2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 7956 | c:\windows\resources\themes\explorer.exe | C:\Windows\Resources\Themes\explorer.exe | icsys.icn.exe | ||||||||||||
User: admin Integrity Level: HIGH Version: 1.00 Modules
| |||||||||||||||
| 7976 | c:\windows\resources\spoolsv.exe SE | C:\Windows\Resources\spoolsv.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 8000 | c:\windows\resources\svchost.exe | C:\Windows\Resources\svchost.exe | spoolsv.exe | ||||||||||||
User: admin Integrity Level: HIGH Version: 1.00 Modules
| |||||||||||||||
| 8020 | c:\windows\resources\spoolsv.exe PR | C:\Windows\Resources\spoolsv.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
Total events
7 429
Read events
7 405
Write events
19
Delete events
5
Modification events
| (PID) Process: | (7660) 2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\VB and VBA Program Settings\Explorer\Process |
| Operation: | write | Name: | LO |
Value: 1 | |||
| (PID) Process: | (7824) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MicrosoftEdgeUpdate.exe |
| Operation: | write | Name: | DisableExceptionChainValidation |
Value: 0 | |||
| (PID) Process: | (7824) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\PersistedPings\{495C309D-B3AC-4ACC-A0C7-71746E411BC8} |
| Operation: | write | Name: | PersistedPingString |
Value: <?xml version="1.0" encoding="UTF-8"?><request protocol="3.0" updater="Omaha" updaterversion="1.3.195.45" shell_version="1.3.147.37" ismachine="1" sessionid="{511A7A5C-7B8A-4BF0-A7AA-BEE5512B0492}" userid="{FD984739-A122-4DB0-BE5B-46E3E09D84E4}" installsource="taggedmi" requestid="{495C309D-B3AC-4ACC-A0C7-71746E411BC8}" dedup="cr" domainjoined="0"><hw logical_cpus="4" physmemory="4" disk_type="2" sse="1" sse2="1" sse3="1" ssse3="1" sse41="1" sse42="1" avx="1"/><os platform="win" version="10.0.19045.4046" sp="" arch="x64" product_type="48" is_wip="0" is_in_lockdown_mode="0"/><oem product_manufacturer="DELL" product_name="DELL"/><exp etag=""r452t1+k2Tgq/HXzjvFNBRhopBWR9sbjXxqeUDH9uX0=""/><app appid="{F3C4FE00-EFD5-403B-9569-398A20F1BA4A}" version="1.3.185.17" nextversion="1.3.195.45" lang="" brand="" client=""><event eventtype="2" eventresult="1" errorcode="0" extracode1="0" system_uptime_ticks="9770538006" install_time_ms="953"/></app></request> | |||
| (PID) Process: | (7824) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\PersistedPings\{495C309D-B3AC-4ACC-A0C7-71746E411BC8} |
| Operation: | write | Name: | PersistedPingTime |
Value: 133918484226104895 | |||
| (PID) Process: | (7824) MicrosoftEdgeUpdate.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\proxy |
| Operation: | write | Name: | source |
Value: auto | |||
| (PID) Process: | (7824) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\PersistedPings\{495C309D-B3AC-4ACC-A0C7-71746E411BC8} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7936) icsys.icn.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\VB and VBA Program Settings\Explorer\Process |
| Operation: | write | Name: | LO |
Value: 1 | |||
| (PID) Process: | (7956) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Explorer |
Value: c:\windows\resources\themes\explorer.exe RO | |||
| (PID) Process: | (7956) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Svchost |
Value: c:\windows\resources\svchost.exe RO | |||
| (PID) Process: | (7956) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Explorer |
Value: | |||
Executable files
205
Suspicious files
6
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7696 | 2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe | C:\Program Files (x86)\Microsoft\Temp\EUDAE1.tmp\psmachine_64.dll | executable | |
MD5:3B2B8EC44DB32FCAFC374106E06AFDB2 | SHA256:C185A9DFFAE4D15C8E5A540C959AF1C88CE1D28E63D623B67BE639A64CDF5CFF | |||
| 7696 | 2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe | C:\Program Files (x86)\Microsoft\Temp\EUDAE1.tmp\MicrosoftEdgeUpdateComRegisterShell64.exe | executable | |
MD5:0857CFD39400CD28176599CC0AFD35CB | SHA256:09358F21AD991269DFF34C97F377472B3908D505A1D5A2CF35E1507C789D9562 | |||
| 7696 | 2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe | C:\Program Files (x86)\Microsoft\Temp\EUDAE1.tmp\psuser.dll | executable | |
MD5:4455FB878B1F372F5606E8163043889E | SHA256:D030861A5DCC7502CEAF33A7254628D51339D69ADB17D0CC1652946B8BD86CF9 | |||
| 7696 | 2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe | C:\Program Files (x86)\Microsoft\Temp\EUDAE1.tmp\psmachine.dll | executable | |
MD5:75E238DAE9A5C2F276A47979B44557ED | SHA256:BDF767EC157F985AD03EFC335854EED97040F3997208D25CA35F82B1C1A02B50 | |||
| 7696 | 2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe | C:\Program Files (x86)\Microsoft\Temp\EUDAE1.tmp\NOTICE.TXT | text | |
MD5:6DD5BF0743F2366A0BDD37E302783BCD | SHA256:91D3FC490565DED7621FF5198960E501B6DB857D5DD45AF2FE7C3ECD141145F5 | |||
| 7696 | 2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe | C:\Program Files (x86)\Microsoft\Temp\EUDAE1.tmp\msedgeupdateres_ar.dll | executable | |
MD5:BC506850978F0698212F38C9234DCDC3 | SHA256:B570C79149D8D2B376E011DDABFBBE4312672912C9583B123D3DD13CFBDA0A64 | |||
| 7696 | 2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe | C:\Program Files (x86)\Microsoft\Temp\EUDAE1.tmp\MicrosoftEdgeUpdateCore.exe | executable | |
MD5:54C6470933C9F2BCCF2977C1C6E3B01A | SHA256:A0FFA052C029C0DCF6CCFEFAE8DFD898E8C8397CF2F42E4FA95A80B866981AA5 | |||
| 7696 | 2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe | C:\Program Files (x86)\Microsoft\Temp\EUDAE1.tmp\psuser_arm64.dll | executable | |
MD5:9D5CF15D06AA8E039B191C73D8198ECD | SHA256:9220EE9085AA6214F8F5A89B5E51278368D943B5D78C67D8D50FF9D731CDC212 | |||
| 7696 | 2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe | C:\Program Files (x86)\Microsoft\Temp\EUDAE1.tmp\EdgeUpdate.dat | binary | |
MD5:369BBC37CFF290ADB8963DC5E518B9B8 | SHA256:3D7EC761BEF1B1AF418B909F1C81CE577C769722957713FDAFBC8131B0A0C7D3 | |||
| 7696 | 2025-05-16_61c0cda2c9d7e328283895f9e9d65f04_amadey_black-basta_elex_hellokitty_luca-stealer_swisyn.exe | C:\Program Files (x86)\Microsoft\Temp\EUDAE1.tmp\msedgeupdateres_am.dll | executable | |
MD5:415B67A9697B1D527131B851A5A28CA3 | SHA256:BF3D60E65EF49404BB3B6EDD920D7C0E61E444BB7B014E5FBAB869DC02CD7E31 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
24
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4208 | RUXIMICS.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4208 | RUXIMICS.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4208 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4208 | RUXIMICS.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4208 | RUXIMICS.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
7824 | MicrosoftEdgeUpdate.exe | 13.107.43.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7448 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7204 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |