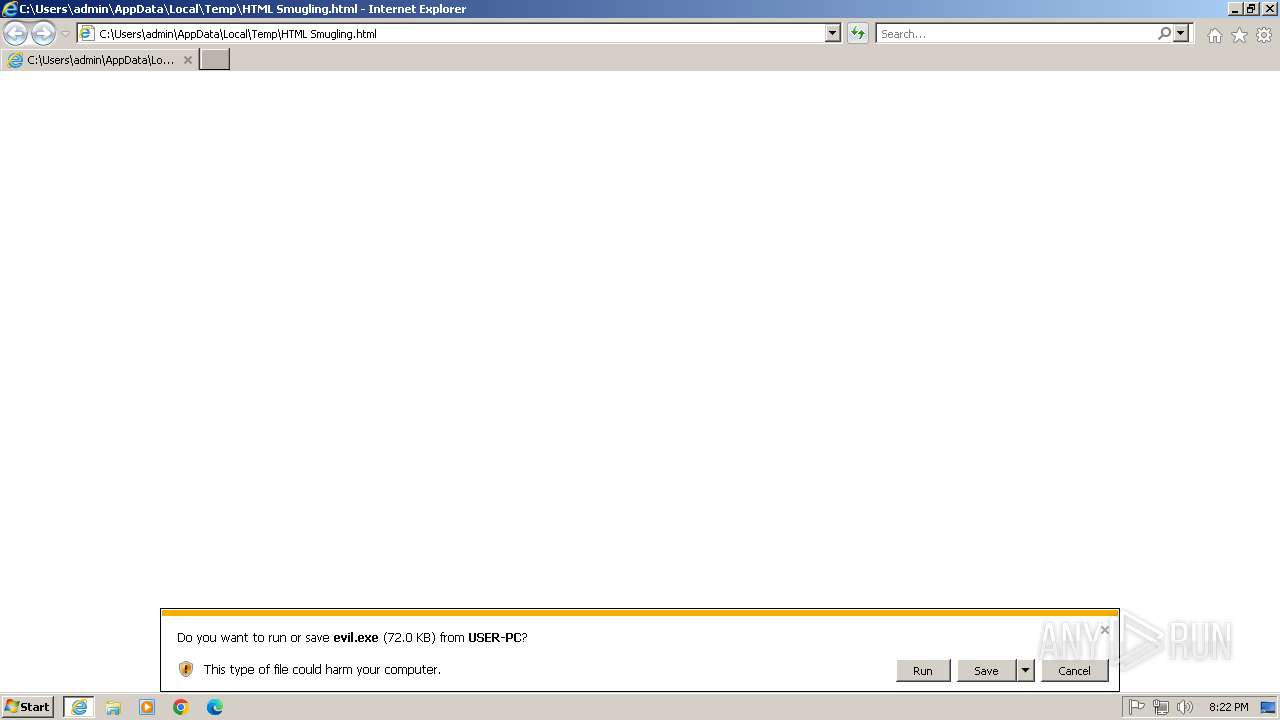
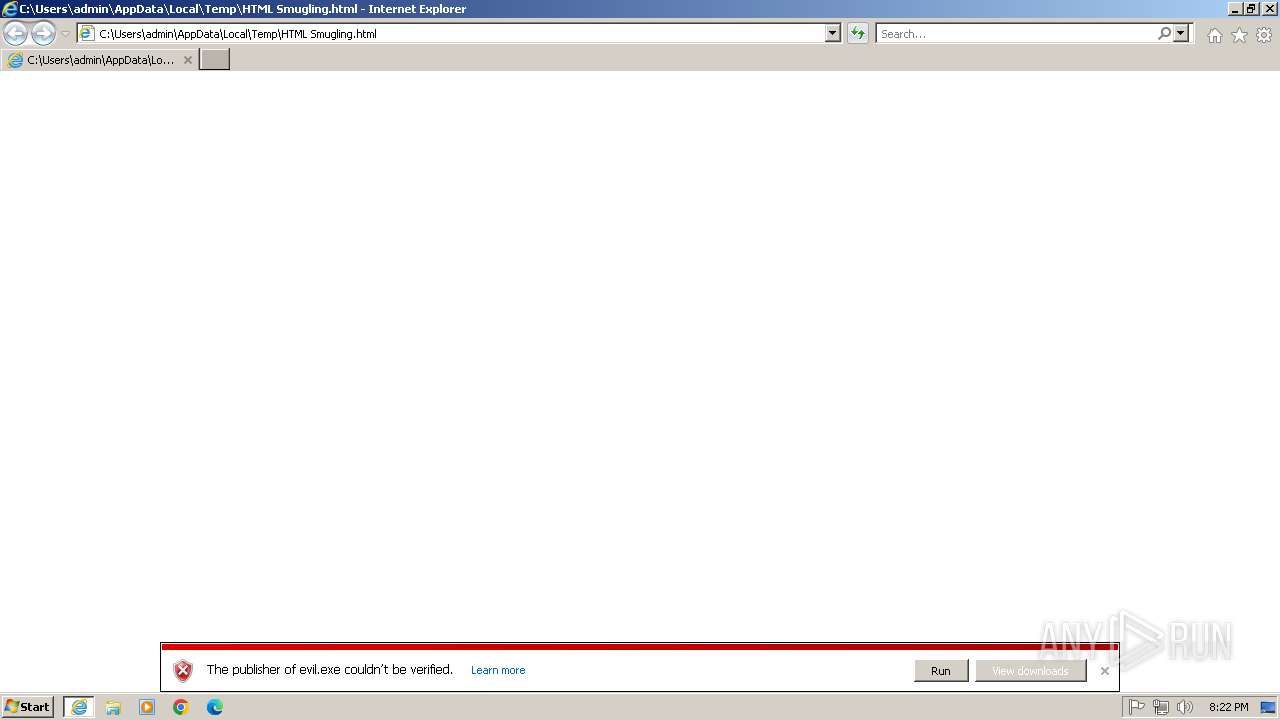
| File name: | HTML Smugling.html |
| Full analysis: | https://app.any.run/tasks/bbf6f4aa-2cb6-468e-a6bd-c0ac5a262594 |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2025, 20:22:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines (65014), with CRLF line terminators |
| MD5: | AF6AE319759BAA30C7E8E80EE098E2A6 |
| SHA1: | 5D2DD2E84E93D004EE2F2189BD5301D3C5BCA04C |
| SHA256: | F69304D58EF5FF7FF58CD71FA6BE2A44584062C103F3BEB74DF480E596DA8606 |
| SSDEEP: | 1536:DdTWLP/2gjd1M58b0X47swsD7Qo48ErGeaOgdJT3Zazwz6bK3hxnU4YNHmKNBKMR:D4qcvpbA4A74mOMJVz6ChnYkKN1 |
MALICIOUS
METASPLOIT has been detected (YARA)
- evil.exe (PID: 1472)
SUSPICIOUS
No suspicious indicators.INFO
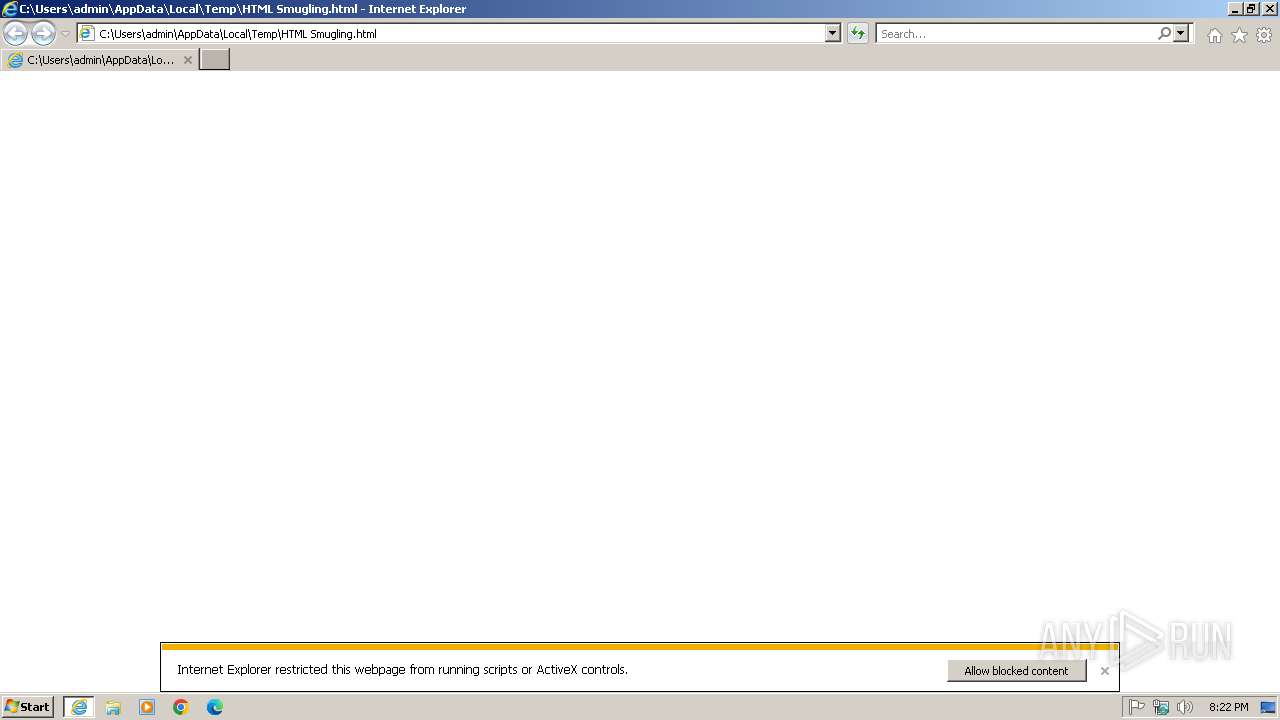
Executable content was dropped or overwritten
- iexplore.exe (PID: 492)
- iexplore.exe (PID: 2840)
Application launched itself
- iexplore.exe (PID: 2840)
- iexplore.exe (PID: 492)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2840)
Autorun file from Downloads
- iexplore.exe (PID: 2840)
- iexplore.exe (PID: 492)
The sample compiled with english language support
- iexplore.exe (PID: 492)
- iexplore.exe (PID: 2840)
Checks supported languages
- evil.exe (PID: 1472)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
Total processes
38
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 492 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2840 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1472 | "C:\Users\admin\Downloads\evil.exe" | C:\Users\admin\Downloads\evil.exe | iexplore.exe | ||||||||||||
User: admin Company: Apache Software Foundation Integrity Level: MEDIUM Description: ApacheBench command line utility Version: 2.2.14 Modules
| |||||||||||||||
| 2656 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2840 CREDAT:333057 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2840 | "C:\Program Files\Internet Explorer\iexplore.exe" "C:\Users\admin\AppData\Local\Temp\HTML Smugling.html" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
13 910
Read events
13 760
Write events
121
Delete events
29
Modification events
| (PID) Process: | (492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {BB8C8429-08ED-11F0-B32B-12A9866C77DE} |
Value: 0 | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\WindowsSearch |
| Operation: | write | Name: | UpgradeTime |
Value: 4208317EFA9CDB01 | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | FullScreen |
Value: no | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | Window_Placement |
Value: 2C0000000200000003000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF20000000200000004003000078020000 | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\PendingRecovery |
| Operation: | write | Name: | Active |
Value: 0 | |||
| (PID) Process: | (492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
3
Suspicious files
6
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2840 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:016F2A3C6AFF71714F62B4018E18C840 | SHA256:916A0D09D74E1D9E8763D7A23F9A17188D8DDF40E62731303F35240D8E17151C | |||
| 2840 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:77B20B5CD41BC6BB475CCA3F91AE6E3C | SHA256:5511A9B9F9144ED7BDE4CCB074733B7C564D918D2A8B10D391AFC6BE5B3B1509 | |||
| 2840 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:4F787A21AF2DB0723F03A13CA1033C8A | SHA256:2A2C3273C982922C5833ABFCBDB64EFB6C93AF38BCB53307523DAB7EB192F9DF | |||
| 2840 | iexplore.exe | C:\Users\admin\Downloads\evil.exe | executable | |
MD5:31FB677C19FAEACD03C482BA2F99EEBB | SHA256:AD0459F46AC4339C676A6E0BBCF180E608C083DC91236471F5501A7E7FF961C5 | |||
| 2840 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 2840 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 492 | iexplore.exe | C:\Users\admin\Downloads\evil.exe.iy7yes5.partial | executable | |
MD5:31FB677C19FAEACD03C482BA2F99EEBB | SHA256:AD0459F46AC4339C676A6E0BBCF180E608C083DC91236471F5501A7E7FF961C5 | |||
| 2840 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:4872BABAF39AA62B8D32695EBB7E9173 | SHA256:2EE85DF86EE29BBEB3DCA81AA29B6DE204F605A2769B84C728A329178A2D0999 | |||
| 492 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\evil[1].exe | executable | |
MD5:7268AAE6B831570442DB347899C1C658 | SHA256:8B2E324E461D69AA40D9A8597D3B75B965806E71CF4A52F32026D76784110161 | |||
| 2840 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
13
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2840 | iexplore.exe | GET | 200 | 23.50.131.202:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?9727dbddfc8fc6cf | unknown | — | — | whitelisted |
2840 | iexplore.exe | GET | 200 | 23.50.131.202:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?794700bfc654c75d | unknown | — | — | whitelisted |
2840 | iexplore.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2840 | iexplore.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2840 | iexplore.exe | 2.16.204.135:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
2840 | iexplore.exe | 23.50.131.202:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | whitelisted |
2840 | iexplore.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1472 | evil.exe | 10.0.0.5:443 | — | — | — | unknown |
2840 | iexplore.exe | 52.239.160.33:443 | iecvlist.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |