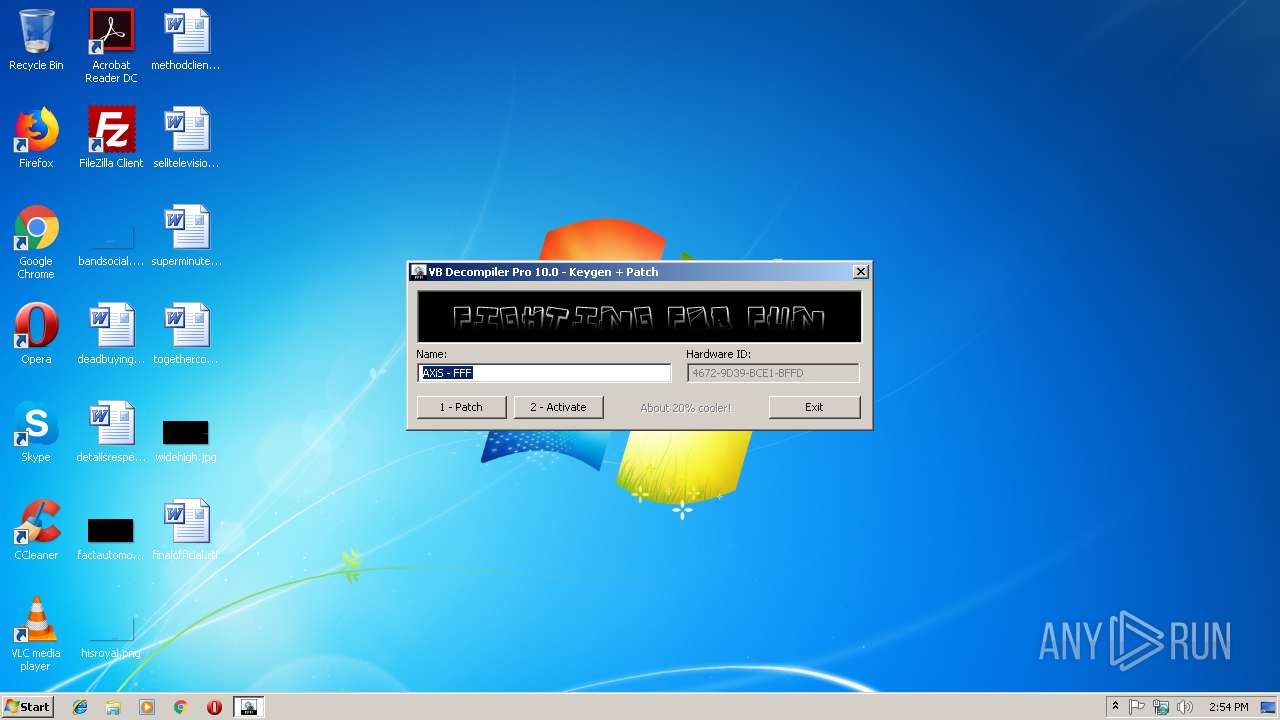
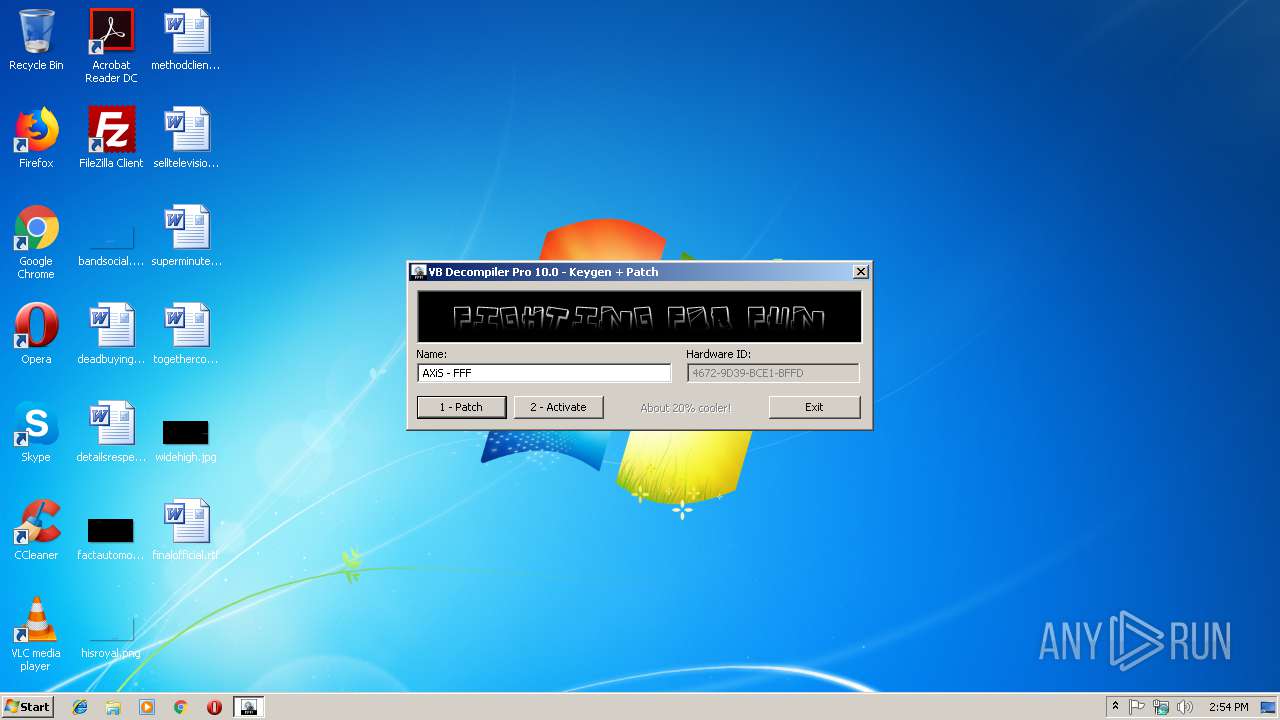
| File name: | VB.Decompiler.Pro.v10.0.KEYGEN-FFF.exe |
| Full analysis: | https://app.any.run/tasks/3b9fa18e-9ab2-4ad3-9da5-c36b6647623d |
| Verdict: | No threats detected |
| Analysis date: | February 09, 2019, 14:54:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 06D5AEDAA044EEB6E6D6580AEF52560A |
| SHA1: | F38CA3D7329048AEFA44902536ECDAD18117702B |
| SHA256: | F687763C98531CFD4DBAB38E810BE7B4519EADB014F60A8A13ADEA3CF5EF9768 |
| SSDEEP: | 24576:Qghz5KoxC1gA++/I65htN0VJK6dvbrZJLMW/d:QgXRC1++wVJ1xn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (61.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.6) |
| .exe | | | Win32 Executable (generic) (10) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
| .exe | | | Generic Win/DOS Executable (4.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:07:02 11:49:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.22 |
| CodeSize: | 63488 |
| InitializedDataSize: | 477696 |
| UninitializedDataSize: | 512 |
| EntryPoint: | 0x37a858 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Jul-2015 09:49:04 |
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 22 |
| Time date stamp: | 02-Jul-2015 09:49:04 |
| Pointer to Symbol Table: | 0x0007B000 |
| Number of symbols: | 1861 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
0x00088000 | 0x00274000 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 | |
.rsrc | 0x00087000 | 0x00001000 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.67169 |
.upx | 0x002FC000 | 0x00081000 | 0x00080800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.93627 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.79951 | 411 | UNKNOWN | UNKNOWN | RT_MANIFEST |
101 | 7.43082 | 474 | UNKNOWN | UNKNOWN | RT_DIALOG |
103 | 7.78217 | 22838 | UNKNOWN | UNKNOWN | RT_BITMAP |
104 | 1.81924 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
advapi32.dll |
comdlg32.dll |
gdi32.dll |
kernel32.dll |
msvcrt.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
version.dll |
Total processes
34
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3104 | "C:\Users\admin\AppData\Local\Temp\VB.Decompiler.Pro.v10.0.KEYGEN-FFF.exe" | C:\Users\admin\AppData\Local\Temp\VB.Decompiler.Pro.v10.0.KEYGEN-FFF.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
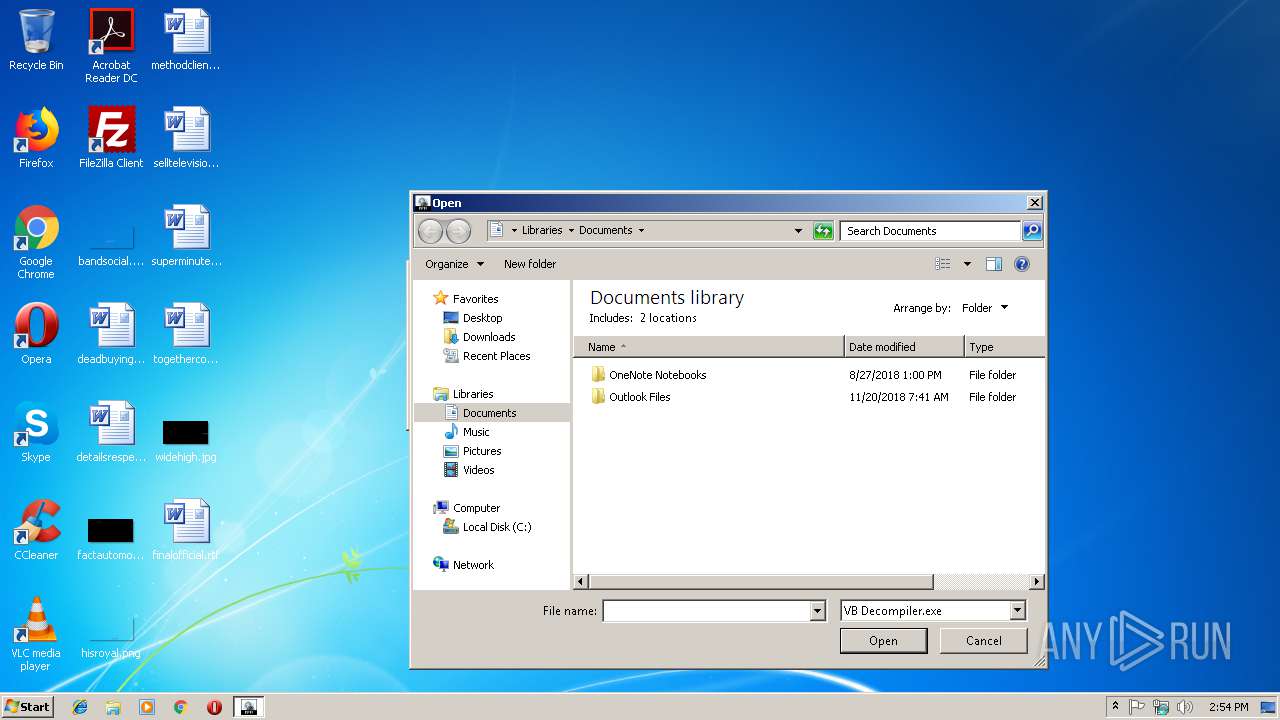
| 3320 | "C:\Users\admin\AppData\Local\Temp\VB.Decompiler.Pro.v10.0.KEYGEN-FFF.exe" | C:\Users\admin\AppData\Local\Temp\VB.Decompiler.Pro.v10.0.KEYGEN-FFF.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
492
Read events
462
Write events
29
Delete events
1
Modification events
| (PID) Process: | (3320) VB.Decompiler.Pro.v10.0.KEYGEN-FFF.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (3320) VB.Decompiler.Pro.v10.0.KEYGEN-FFF.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0200000000000000010000000700000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (3320) VB.Decompiler.Pro.v10.0.KEYGEN-FFF.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (3320) VB.Decompiler.Pro.v10.0.KEYGEN-FFF.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (3320) VB.Decompiler.Pro.v10.0.KEYGEN-FFF.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
| (PID) Process: | (3320) VB.Decompiler.Pro.v10.0.KEYGEN-FFF.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3320) VB.Decompiler.Pro.v10.0.KEYGEN-FFF.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | 2 |
Value: 560042002E004400650063006F006D00700069006C00650072002E00500072006F002E007600310030002E0030002E004B0045005900470045004E002D004600460046002E00650078006500000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000099010000BE000000190400009E020000000000000000000000000000000000000100000000000000 | |||
| (PID) Process: | (3320) VB.Decompiler.Pro.v10.0.KEYGEN-FFF.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | delete value | Name: | 2 |
Value: 560042002E004400650063006F006D00700069006C00650072002E00500072006F002E007600310030002E0030002E004B0045005900470045004E002D004600460046002E00650078006500000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000099010000BE000000190400009E020000000000000000000000000000000000000100000000000000 | |||
| (PID) Process: | (3320) VB.Decompiler.Pro.v10.0.KEYGEN-FFF.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | 2 |
Value: 560042002E004400650063006F006D00700069006C00650072002E00500072006F002E007600310030002E0030002E004B0045005900470045004E002D004600460046002E0065007800650000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000096010000040100006A030000AF0100000000000000000000000000000000000099010000BE000000190400009E020000000000000000000000000000000000000100000000000000 | |||
| (PID) Process: | (3320) VB.Decompiler.Pro.v10.0.KEYGEN-FFF.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | MRUListEx |
Value: 020000000100000000000000FFFFFFFF | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report