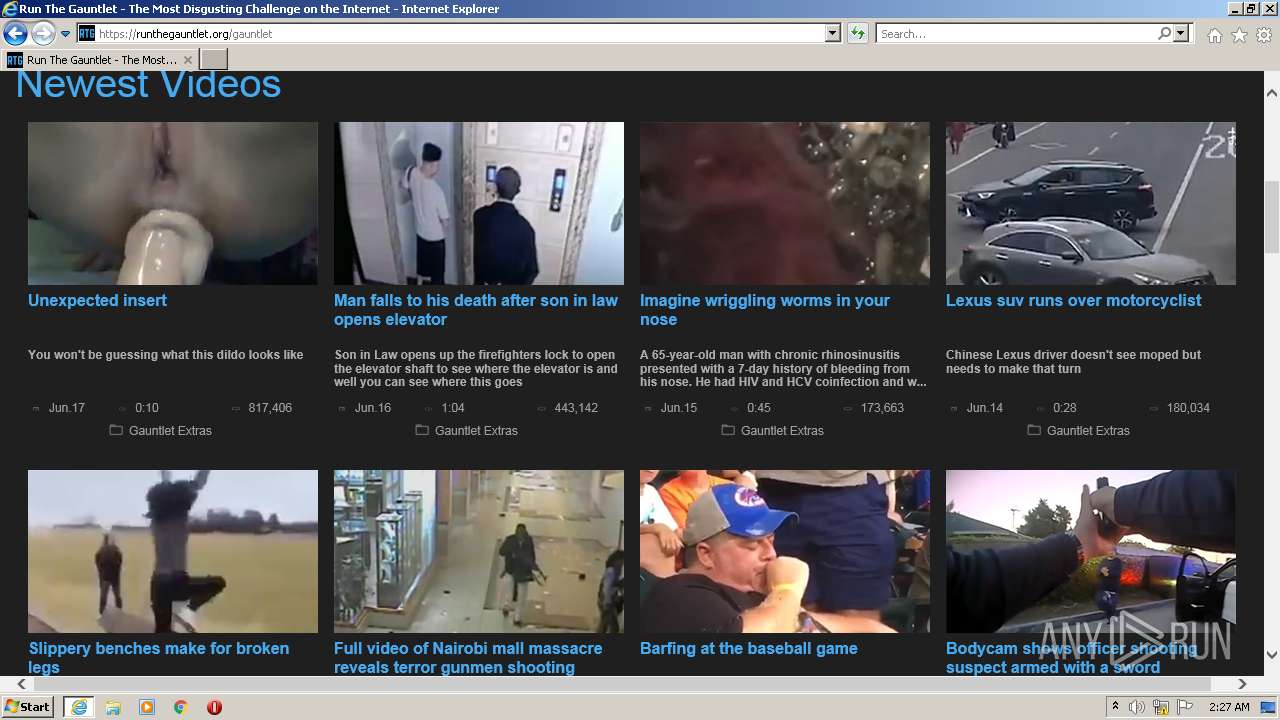
| URL: | https://runthegauntlet.org/ |
| Full analysis: | https://app.any.run/tasks/fbbf9adf-f3f2-4215-8743-00a3529fe7bd |
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2022, 02:26:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D59BA50DAAD26330B9FF06798EA94CC8 |
| SHA1: | 726659C6B7BC7B34C8ABC8F6468AD3054FD477AB |
| SHA256: | F67BAF20B7DD637E3F1924C6E7BDA116C257C0239204D96AF7C8C180F8B92FED |
| SSDEEP: | 3:N8YNAwlJyMJ:2YSw9J |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 4020)
- iexplore.exe (PID: 1212)
Checks supported languages
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2904)
Reads the computer name
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2904)
Executed via COM
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2904)
Creates files in the user directory
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2904)
INFO
Reads the computer name
- iexplore.exe (PID: 3672)
- iexplore.exe (PID: 4020)
- iexplore.exe (PID: 1212)
Checks supported languages
- iexplore.exe (PID: 3672)
- iexplore.exe (PID: 4020)
- iexplore.exe (PID: 1212)
Changes internet zones settings
- iexplore.exe (PID: 3672)
Reads settings of System Certificates
- iexplore.exe (PID: 4020)
- iexplore.exe (PID: 3672)
- iexplore.exe (PID: 1212)
Application launched itself
- iexplore.exe (PID: 3672)
Checks Windows Trust Settings
- iexplore.exe (PID: 4020)
- iexplore.exe (PID: 3672)
- iexplore.exe (PID: 1212)
Creates files in the user directory
- iexplore.exe (PID: 4020)
- iexplore.exe (PID: 1212)
- iexplore.exe (PID: 3672)
Drops Coronavirus (possible) decoy
- iexplore.exe (PID: 4020)
Reads internet explorer settings
- iexplore.exe (PID: 4020)
- iexplore.exe (PID: 1212)
Reads CPU info
- iexplore.exe (PID: 1212)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1212 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3672 CREDAT:4068636 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2904 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Integrity Level: MEDIUM Description: Adobe� Flash� Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
| 3672 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://runthegauntlet.org/" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 4020 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3672 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
25 976
Read events
25 813
Write events
163
Delete events
0
Modification events
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30949359 | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30949359 | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
28
Text files
265
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4020 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:95C2C7A7104019DE7DCB155E0836CD04 | SHA256:12F55F34DF65AD549C847B0FAC90966E769A15BA0882D5D9B6A15B6E3EC0BD0E | |||
| 4020 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\ULCAWSBV.htm | html | |
MD5:858EBDBD98017EAEA669CE1297662A54 | SHA256:88FD9191C880D56462712105CF27210A712937E6ADED010687AFBEB8C0729098 | |||
| 4020 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\unexpected_insert[1].jpg | image | |
MD5:5226E0D8E5ACC1692DBD2EEB03A0A193 | SHA256:EB46C13727377C52F93B6826410F4281981C2A62ED605BCBCC8786203FA7922A | |||
| 4020 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\ic_tv_darkgrey_24px[1].svg | image | |
MD5:1AB0E0AE4C4FDBD61731C90A3151802D | SHA256:713AE955F3122148FD01C3320330AE732A35BD6CB8086DB1DC6051B49C8F30B1 | |||
| 4020 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\ic_event_darkgrey_24px[1].svg | image | |
MD5:0B16E4052224336074227B0DFCD44D38 | SHA256:7C1BA276AA0C5A22CDE2CB2E4BF2DC2DDB29447ECC0B8F340FBD4DC372678F38 | |||
| 4020 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\ic_access_time_darkgrey_24px[1].svg | image | |
MD5:ECB61A6816DDFBAA249486375B95CAEA | SHA256:5E29E387772375CF641D37BA71C5898ECAD80E4ACE481435D2ECEC7E3E019FBF | |||
| 4020 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\ic_folder_open_darkgrey_24px[1].svg | image | |
MD5:CDDF2180AD29DC2D61E180BC8A296CCA | SHA256:A41B1B02443DFB4E7476916FF04294A3BC075E3B26A786615FF24B35BDD2E7F5 | |||
| 4020 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\logo[1].png | image | |
MD5:4AF61DFB9F5E1B0BF576EB4032052269 | SHA256:6ACDA3BE28D521FE32BA75334D00F9A44BCB44DB69A09DCB5FD1946EE2FDE917 | |||
| 4020 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:EFADD12EA6190354379F09F195FCD4FE | SHA256:8EE24253A730E08A963BD9F829AF98C30C177FE9B1236430221D3D17D3E34EB4 | |||
| 4020 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
58
TCP/UDP connections
180
DNS requests
37
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4020 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAZUH6%2Bn%2Bv2lkCqM24msk3Y%3D | US | der | 471 b | whitelisted |
4020 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
3672 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.68 Kb | whitelisted |
4020 | iexplore.exe | GET | 301 | 172.67.206.66:80 | http://tubefilter.net/i/5e8/5e8a0d1406dc2-0.jpg | US | html | 336 b | shared |
4020 | iexplore.exe | GET | 200 | 104.90.178.254:80 | http://x1.c.lencr.org/ | NL | der | 717 b | whitelisted |
4020 | iexplore.exe | GET | 200 | 92.123.195.57:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?fea34f61c9660f35 | unknown | compressed | 59.5 Kb | whitelisted |
4020 | iexplore.exe | GET | 301 | 172.67.206.66:80 | http://tubefilter.net/i/5e8/5e88b7e671a08-0.jpg | US | html | 336 b | shared |
4020 | iexplore.exe | GET | 301 | 172.67.206.66:80 | http://tubefilter.net/i/5e8/5e88d035b7bc0-0.jpg | US | html | 336 b | shared |
4020 | iexplore.exe | GET | 301 | 172.67.206.66:80 | http://tubefilter.net/i/623/623c5f7895213-0.jpg | US | html | 336 b | shared |
4020 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4020 | iexplore.exe | 92.123.195.57:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
4020 | iexplore.exe | 104.21.70.7:443 | runthegauntlet.org | Cloudflare Inc | US | unknown |
4020 | iexplore.exe | 142.250.181.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
4020 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4020 | iexplore.exe | 142.250.184.200:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
4020 | iexplore.exe | 142.250.184.227:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
4020 | iexplore.exe | 216.58.212.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3672 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3672 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
4020 | iexplore.exe | 142.250.185.110:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
runthegauntlet.org |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |