| File name: | Profwiz.exe |
| Full analysis: | https://app.any.run/tasks/e9d8fc3c-ad7a-4342-b027-a5d8673fac93 |
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2020, 21:14:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FF56422C98F458B3E73DF93FD0AE0F4D |
| SHA1: | 279DA39A7E88DF337E03B43B6AC255400FB4DCB7 |
| SHA256: | F67ADC935C9209250923E3A16B9983795FAAC4DD2689BAADD389AD53CF734330 |
| SSDEEP: | 49152:q3tKCuoqgxBqVPs5gvbVWypfeTrJsIUy:q3tKC7BqvwsIU |
MALICIOUS
Application was dropped or rewritten from another process
- profhlp.exe (PID: 1752)
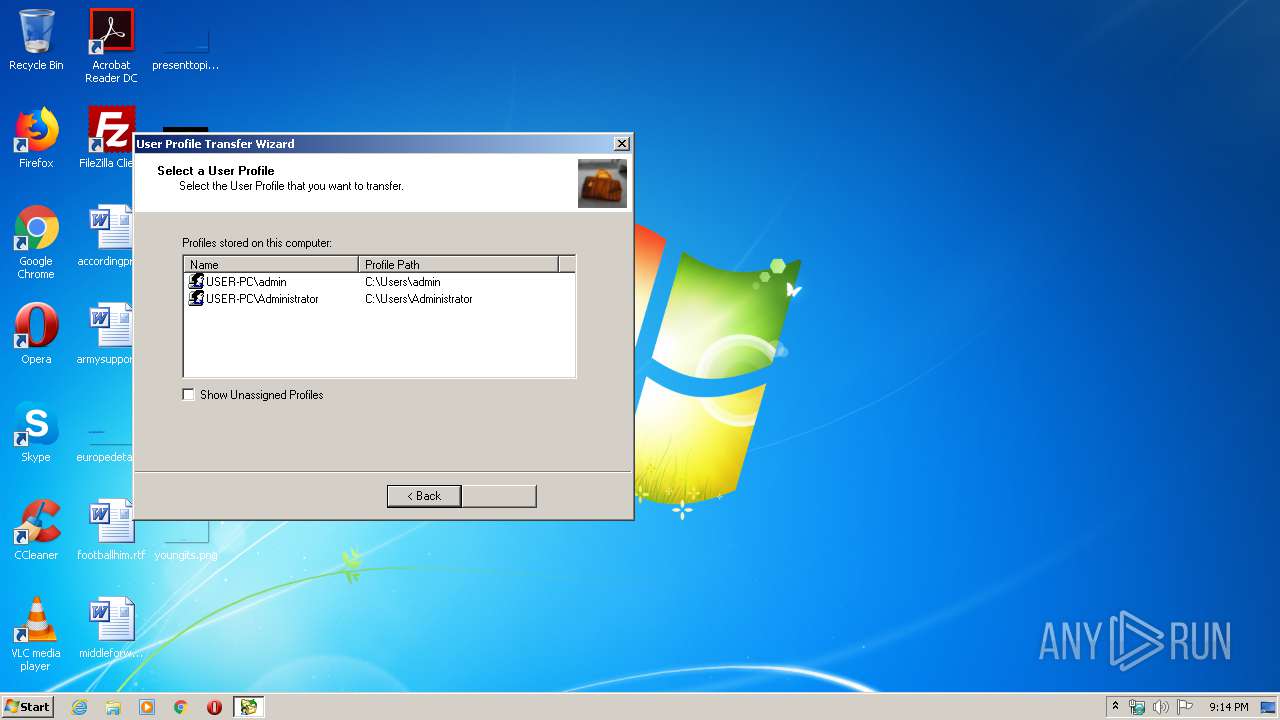
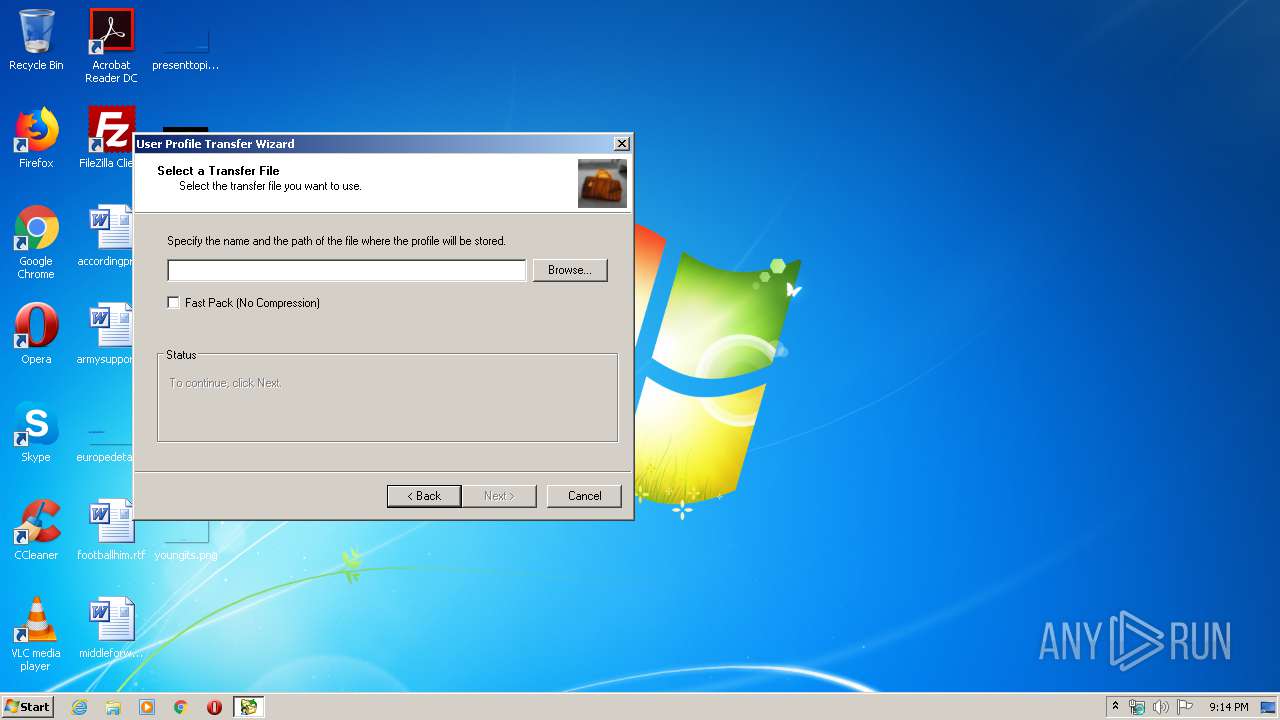
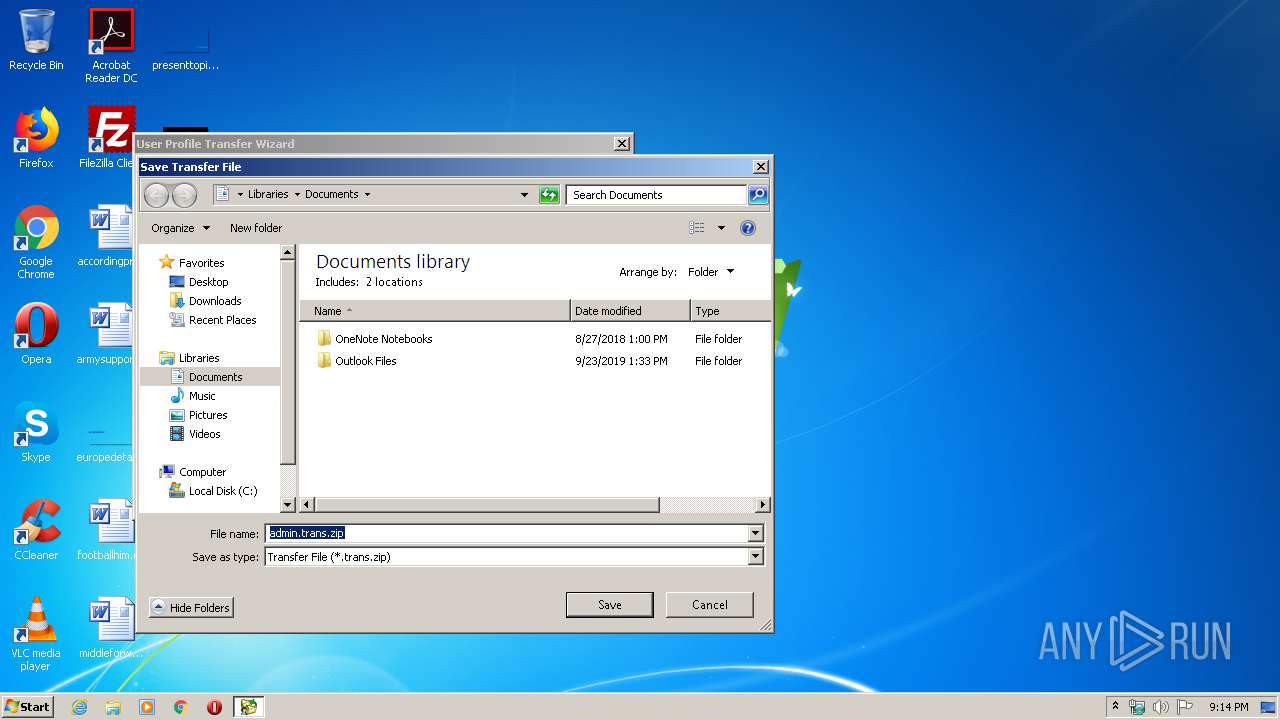
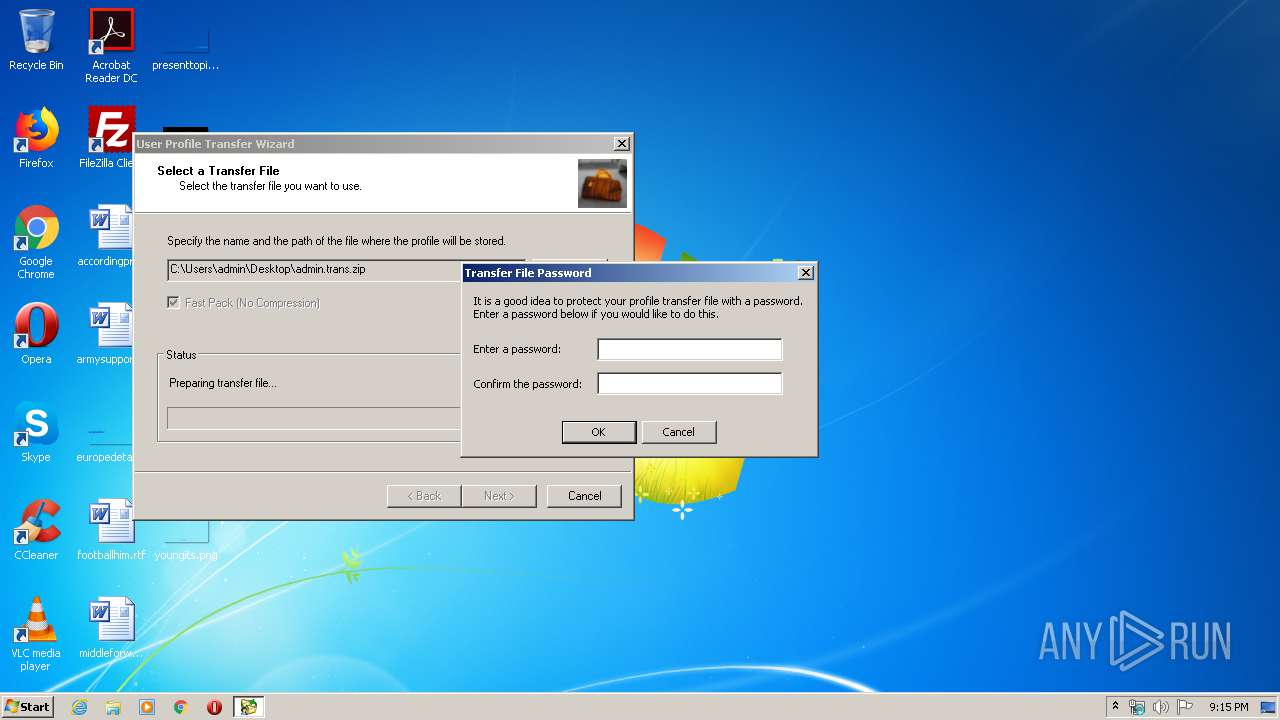
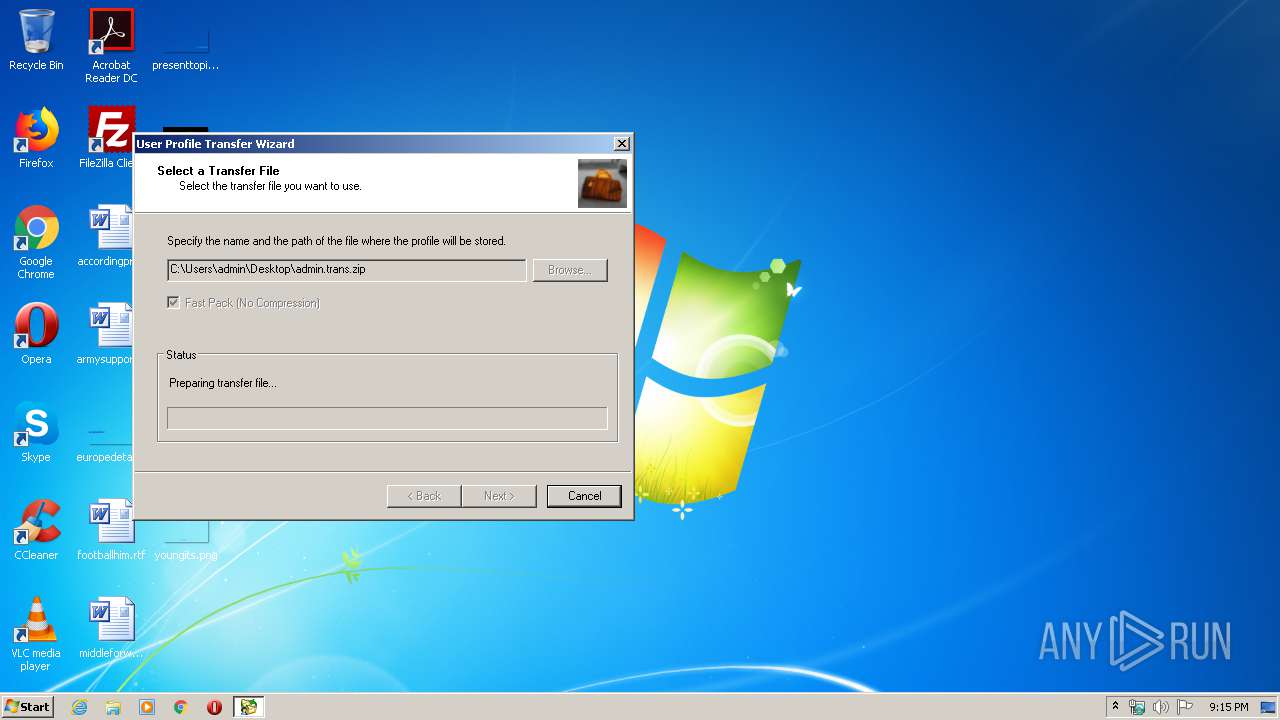
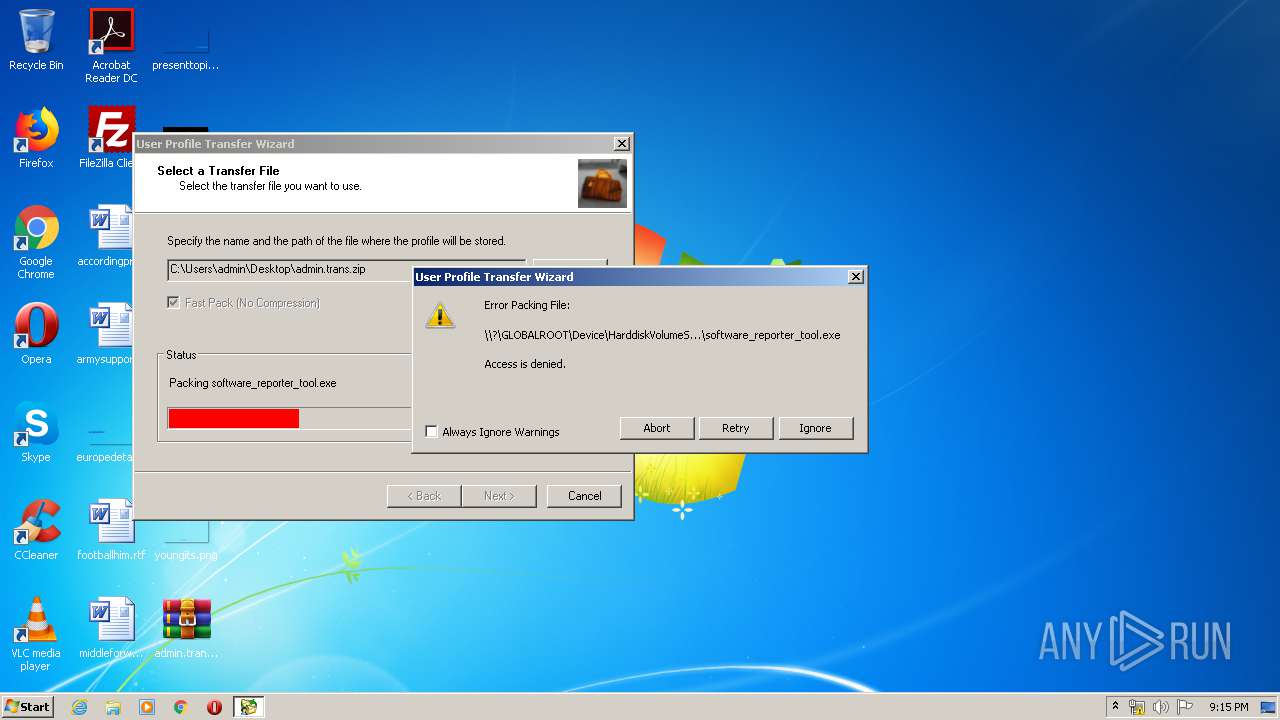
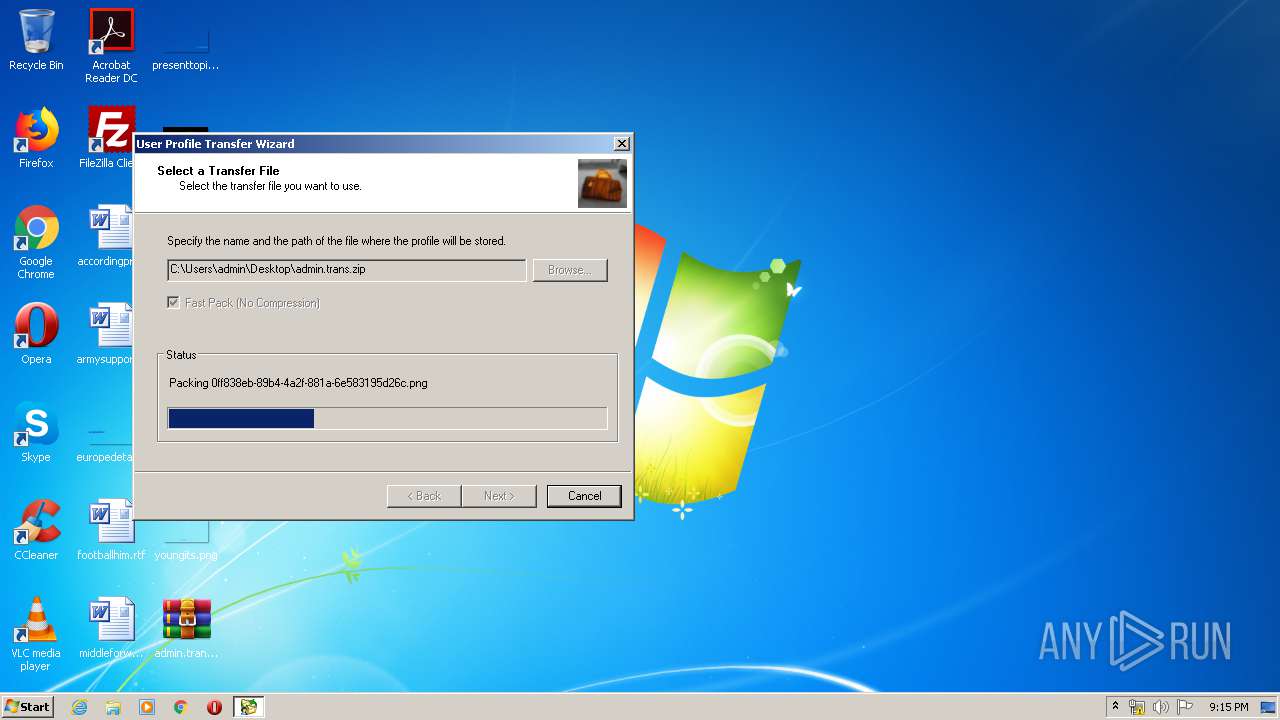
Actions looks like stealing of personal data
- Profwiz.exe (PID: 2844)
SUSPICIOUS
Creates files in the Windows directory
- Profwiz.exe (PID: 2844)
Executed as Windows Service
- vssvc.exe (PID: 2184)
Executable content was dropped or overwritten
- Profwiz.exe (PID: 2844)
INFO
Low-level read access rights to disk partition
- vssvc.exe (PID: 2184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:12:23 16:10:16+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.23 |
| CodeSize: | 1051648 |
| InitializedDataSize: | 896512 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8f581 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.17.1094.0 |
| ProductVersionNumber: | 1.17.1094.0 |
| FileFlagsMask: | 0x001f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
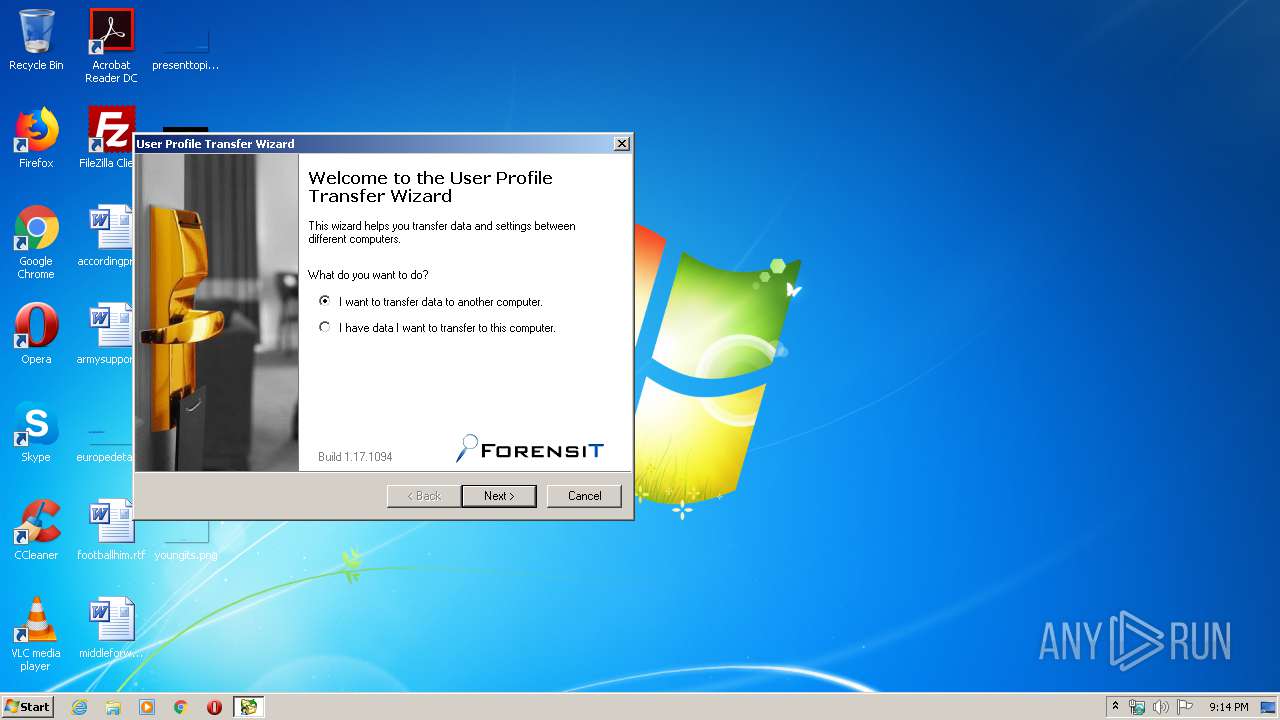
| Build: | 1.17.1094 |
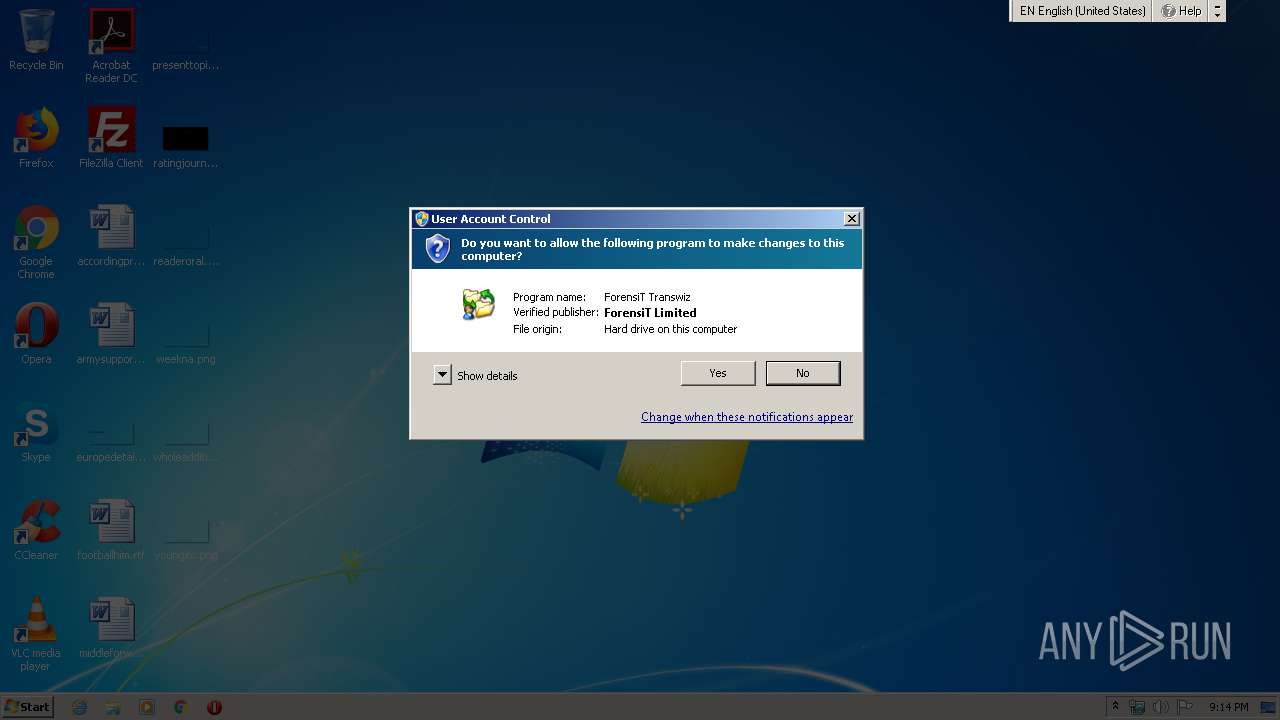
| CompanyName: | ForensiT Limited |
| FileDescription: | ForensiT Transwiz |
| FileVersion: | 1.17.1094.0 |
| InternalName: | Transwiz |
| LegalCopyright: | Copyright © ForensiT 2006-2020 |
| ProductName: | Transwiz |
| ProductVersion: | 1.17.1094.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Dec-2019 15:10:16 |
| Detected languages: |
|
| Debug artifacts: |
|
| Build: | 1.17.1094 |
| CompanyName: | ForensiT Limited |
| FileDescription: | ForensiT Transwiz |
| FileVersion: | 1.17.1094.0 |
| InternalName: | Transwiz |
| LegalCopyright: | Copyright © ForensiT 2006-2020 |
| ProductName: | Transwiz |
| ProductVersion: | 1.17.1094.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000130 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 23-Dec-2019 15:10:16 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00100BDE | 0x00100C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56 |
.rdata | 0x00102000 | 0x00040182 | 0x00040200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.54067 |
.data | 0x00143000 | 0x00019A84 | 0x00002E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.66511 |
.rsrc | 0x0015D000 | 0x00080F88 | 0x00081000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.83408 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.1894 | 1468 | UNKNOWN | English - United Kingdom | RT_MANIFEST |
2 | 6.4726 | 2216 | UNKNOWN | English - United Kingdom | RT_ICON |
3 | 6.36938 | 3752 | UNKNOWN | English - United Kingdom | RT_ICON |
4 | 6.15622 | 1128 | UNKNOWN | English - United Kingdom | RT_ICON |
5 | 5.6552 | 4264 | UNKNOWN | English - United Kingdom | RT_ICON |
6 | 5.28657 | 9640 | UNKNOWN | English - United Kingdom | RT_ICON |
7 | 2.02383 | 296 | UNKNOWN | English - United Kingdom | RT_ICON |
8 | 2.93612 | 296 | UNKNOWN | English - United Kingdom | RT_ICON |
9 | 2.82022 | 296 | UNKNOWN | English - United Kingdom | RT_ICON |
10 | 2.29052 | 296 | UNKNOWN | English - United Kingdom | RT_ICON |
Imports
ACTIVEDS.dll |
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
MPR.dll |
NETAPI32.dll |
NTDSAPI.dll |
OLEAUT32.dll |
RPCRT4.dll |
RstrtMgr.DLL |
Total processes
44
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1752 | C:\Windows\system32\profhlp.exe /1 | C:\Windows\system32\profhlp.exe | Profwiz.exe | ||||||||||||
User: admin Company: ForensiT Integrity Level: HIGH Description: User Profile Migration Helper Exit code: 0 Version: 3.0.0.1 Modules
| |||||||||||||||
| 2184 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2584 | "C:\Users\admin\AppData\Local\Temp\Profwiz.exe" -silent | C:\Users\admin\AppData\Local\Temp\Profwiz.exe | — | explorer.exe | |||||||||||
User: admin Company: ForensiT Limited Integrity Level: MEDIUM Description: ForensiT Transwiz Exit code: 3221226540 Version: 1.17.1094.0 Modules
| |||||||||||||||
| 2844 | "C:\Users\admin\AppData\Local\Temp\Profwiz.exe" -silent | C:\Users\admin\AppData\Local\Temp\Profwiz.exe | explorer.exe | ||||||||||||
User: admin Company: ForensiT Limited Integrity Level: HIGH Description: ForensiT Transwiz Exit code: 0 Version: 1.17.1094.0 Modules
| |||||||||||||||
Total events
812
Read events
589
Write events
218
Delete events
5
Modification events
| (PID) Process: | (2844) Profwiz.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Windows Error Reporting\LocalDumps\Transwiz.exe |
| Operation: | write | Name: | DumpCount |
Value: 16 | |||
| (PID) Process: | (2844) Profwiz.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Windows Error Reporting\LocalDumps\Transwiz.exe |
| Operation: | write | Name: | DumpFolder |
Value: %ALLUSERSPROFILE%\ForensiT\Error Reporting | |||
| (PID) Process: | (2844) Profwiz.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Windows Error Reporting\LocalDumps\Transwiz.exe |
| Operation: | write | Name: | DumpType |
Value: 1 | |||
| (PID) Process: | (2844) Profwiz.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2844) Profwiz.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 02000000010000000700000009000000080000000000000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (2844) Profwiz.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (2844) Profwiz.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (2844) Profwiz.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
| (PID) Process: | (2844) Profwiz.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2844) Profwiz.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | 1 |
Value: 500072006F006600770069007A002E00650078006500000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000100000000000000 | |||
Executable files
1
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2184 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 2844 | Profwiz.exe | C:\Users\admin\AppData\Local\Temp\19f5d17c-2c07-4490-aba0-32cd971a4f29 | — | |
MD5:— | SHA256:— | |||
| 2844 | Profwiz.exe | C:\Windows\system32\profhlp.exe | executable | |
MD5:E2AF49D657FAC39F6B9ABBFA01737578 | SHA256:6DF3B3328714E29356D6251411B2CA96E332DFC9D015D63054FC4AF4CA504B19 | |||
| 2844 | Profwiz.exe | C:\Users\admin\AppData\Local\Temp\transfer.transfer.xml | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
profhlp.exe | VSS: Waiting on Backup Complete |