| File name: | OInstall.exe |
| Full analysis: | https://app.any.run/tasks/41266fb2-9d3e-49a2-96f6-853dc90b755a |
| Verdict: | Malicious activity |
| Analysis date: | December 31, 2020, 18:15:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | E4A514F71BC9E329C641BEB89343BCAC |
| SHA1: | 99DBB79944B2582E1D903ACF3499572B8E9A6B86 |
| SHA256: | F674489ACE458373C9C28B60A3AFD76F1C4176986D6FB3B51BF0832011C8AF4D |
| SSDEEP: | 196608:ZBBSl7E58Xoe7HJflWIMSNKLzP/qEOc9DDZs68lKDNCe0XilVfEVfP:nm3XX7pfEIZkLzPL9DydlKwXceVfP |
MALICIOUS
Drops executable file immediately after starts
- files.dat (PID: 3684)
- OInstall.exe (PID: 1592)
Application was dropped or rewritten from another process
- test.dat (PID: 2904)
- files.dat (PID: 3684)
- test.dat (PID: 3716)
- test.dat (PID: 924)
- test.dat (PID: 2940)
- test.dat (PID: 2236)
- test.dat (PID: 2616)
SUSPICIOUS
Starts application with an unusual extension
- cmd.exe (PID: 2980)
- cmd.exe (PID: 2328)
- cmd.exe (PID: 1196)
- cmd.exe (PID: 3712)
- cmd.exe (PID: 1680)
- cmd.exe (PID: 2764)
- cmd.exe (PID: 2064)
Executable content was dropped or overwritten
- files.dat (PID: 3684)
- OInstall.exe (PID: 1592)
Drops a file that was compiled in debug mode
- OInstall.exe (PID: 1592)
- files.dat (PID: 3684)
Starts CMD.EXE for commands execution
- OInstall.exe (PID: 1592)
Creates files in the Windows directory
- OInstall.exe (PID: 1592)
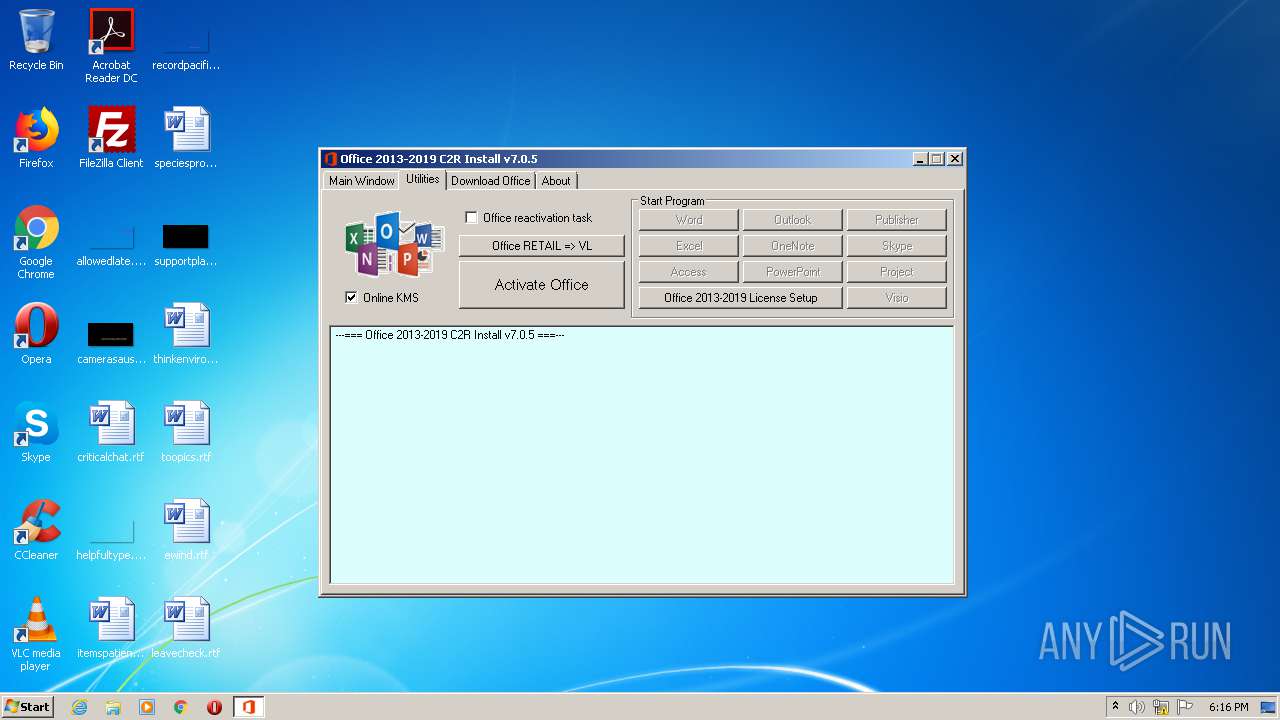
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3444)
- cmd.exe (PID: 3708)
Executes scripts
- cmd.exe (PID: 3288)
- cmd.exe (PID: 760)
- cmd.exe (PID: 3364)
- cmd.exe (PID: 3800)
INFO
Reads Microsoft Office registry keys
- reg.exe (PID: 1676)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (76) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.6) |
| .exe | | | Generic Win/DOS Executable (5.6) |
| .exe | | | DOS Executable Generic (5.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:04:30 13:19:21+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 9687040 |
| InitializedDataSize: | 90112 |
| UninitializedDataSize: | 10665984 |
| EntryPoint: | 0x1368e90 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
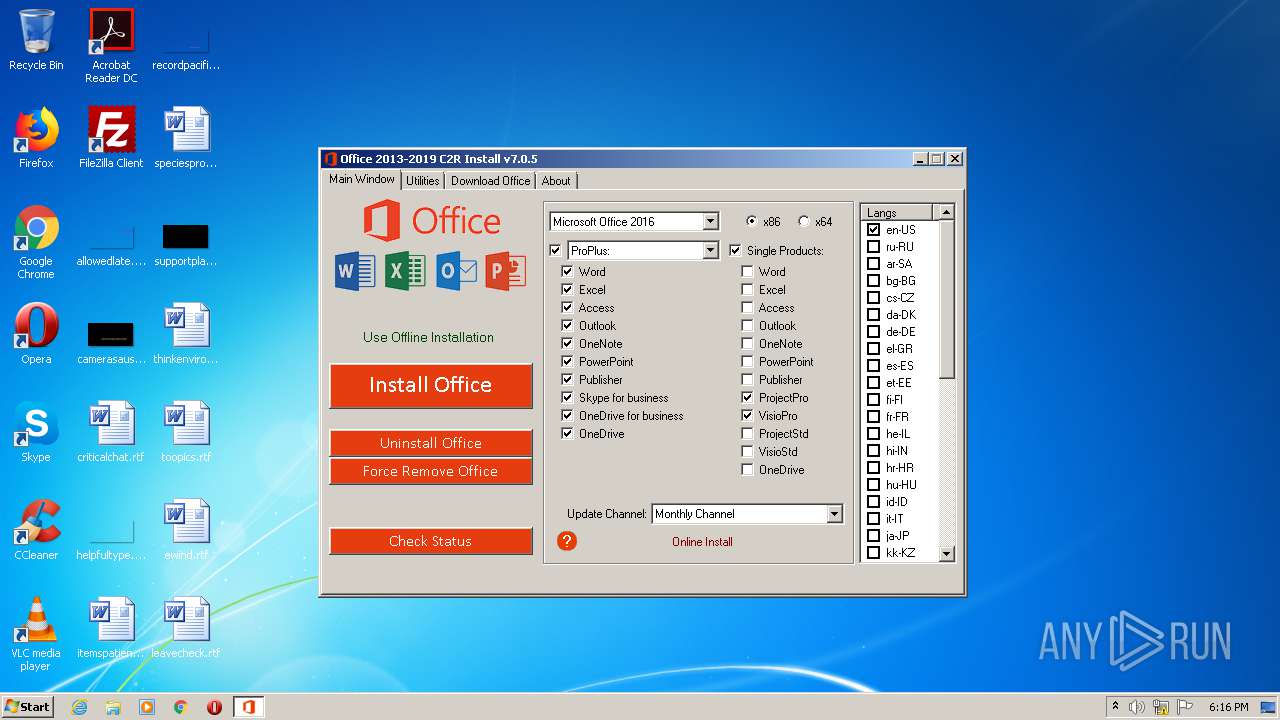
| FileVersionNumber: | 7.0.5.0 |
| ProductVersionNumber: | 7.0.5.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| ProductName: | Office 2013-2019 C2R Install |
| FileDescription: | Office 2013-2019 C2R Install |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Apr-2020 11:19:21 |
| Detected languages: |
|
| ProductName: | Office 2013-2019 C2R Install |
| FileDescription: | Office 2013-2019 C2R Install |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 30-Apr-2020 11:19:21 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00A2C000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00A2D000 | 0x0093D000 | 0x0093C200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.89735 |
.rsrc | 0x0136A000 | 0x00016000 | 0x00015200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.96929 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.94291 | 1117 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 1.96082 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 2.20562 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 2.87138 | 1128 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.DLL |
COMCTL32.DLL |
GDI32.DLL |
ICMP.DLL |
IMAGEHLP.DLL |
IPHLPAPI.DLL |
KERNEL32.DLL |
MSI.DLL |
MSVCRT.dll |
NETAPI32.DLL |
Total processes
77
Monitored processes
28
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 348 | cscript.exe "" //NoLogo /remhst | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 1 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 760 | "C:\Windows\System32\cmd.exe" /D /c cscript.exe "" //NoLogo /sethst:kms.srv.crsoo.com | C:\Windows\System32\cmd.exe | — | OInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 924 | C:\Windows\Temp\test.dat xykz.f3322.org:1688 -l Windows -6 | C:\Windows\Temp\test.dat | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1196 | "C:\Windows\System32\cmd.exe" /D /c C:\Windows\Temp\test.dat hq1.chinancce.com:1688 -l Windows -6 | C:\Windows\System32\cmd.exe | — | OInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1592 | "C:\Users\admin\AppData\Local\Temp\OInstall.exe" | C:\Users\admin\AppData\Local\Temp\OInstall.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Office 2013-2019 C2R Install Exit code: 0 Modules
| |||||||||||||||
| 1676 | REG QUERY HKLM\Software\Microsoft\Office /s /v Path /reg:64 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1680 | "C:\Windows\System32\cmd.exe" /D /c C:\Windows\Temp\test.dat kms.srv.crsoo.com:1688 -l Windows -6 | C:\Windows\System32\cmd.exe | — | OInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1832 | cscript.exe "" //NoLogo /setprt:1688 | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 1 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2064 | "C:\Windows\System32\cmd.exe" /D /c C:\Windows\Temp\test.dat kms789.com:1688 -l Windows -6 | C:\Windows\System32\cmd.exe | — | OInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2236 | C:\Windows\Temp\test.dat kms.srv.crsoo.com:1688 -l Windows -6 | C:\Windows\Temp\test.dat | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
136
Read events
136
Write events
0
Delete events
0
Modification events
Executable files
7
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3684 | files.dat | C:\Users\admin\AppData\Local\Temp\files\x64\cleanospp.exe | executable | |
MD5:162AB955CB2F002A73C1530AA796477F | SHA256:5CE462E5F34065FC878362BA58617FAB28C22D631B9D836DDDCF43FB1AD4DE6E | |||
| 3684 | files.dat | C:\Users\admin\AppData\Local\Temp\files\x86\cleanospp.exe | executable | |
MD5:5FD363D52D04AC200CD24F3BCC903200 | SHA256:3FDEFE2AD092A9A7FE0EDF0AC4DC2DE7E5B9CE6A0804F6511C06564194966CF9 | |||
| 1592 | OInstall.exe | C:\Users\admin\AppData\Local\Temp\files\Configure.xml | text | |
MD5:AC6BE84084E31DBB0E08D188B6C86EC8 | SHA256:1879F7DE537C2AA70292C61EBEF9C6477D36E25B2E6A639E318B159E0A22B0FC | |||
| 3684 | files.dat | C:\Users\admin\AppData\Local\Temp\files\Uninstall.xml | text | |
MD5:364F86F97324EA82FE0D142CD01CF6DD | SHA256:09D5B42140BAB13165BA97FBD0E77792304C3C93555BE02C3DCE21A7A69C66DD | |||
| 1592 | OInstall.exe | C:\Users\admin\AppData\Local\Temp\files\files.dat | executable | |
MD5:55D21B2C272A5D6B9F54FA9ED82BF9EB | SHA256:7A1C82E264258470D14CA345EA1A9B6FC34FA19B393A92077A01BE5F1AD08F47 | |||
| 1592 | OInstall.exe | C:\Windows\Temp\test.dat | executable | |
MD5:CC470D06E9AFC9A7C0B395274B02AC88 | SHA256:81F84A27C49DDD56C799D935787BECB989A6E5B8E000E76E21C82B6CDE4C42FF | |||
| 1592 | OInstall.exe | C:\Users\admin\AppData\Local\Temp\files\setup.exe | executable | |
MD5:9B31E72F0D80D638A8A44EE973103835 | SHA256:49D226E1863D8467437F20A60CB60746694AF08F28EEEAA83E7DB4C183C9C118 | |||
| 3684 | files.dat | C:\Users\admin\AppData\Local\Temp\files\x64\msvcr100.dll | executable | |
MD5:DF3CA8D16BDED6A54977B30E66864D33 | SHA256:1D1A1AE540BA132F998D60D3622F0297B6E86AE399332C3B47462D7C0F560A36 | |||
| 3684 | files.dat | C:\Users\admin\AppData\Local\Temp\files\x86\msvcr100.dll | executable | |
MD5:BF38660A9125935658CFA3E53FDC7D65 | SHA256:60C06E0FA4449314DA3A0A87C1A9D9577DF99226F943637E06F61188E5862EFA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
6
DNS requests
8
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2904 | test.dat | 185.86.180.36:1688 | kms.digiboy.ir | Sindad Netwok Technology Ltd. | IR | unknown |
2904 | test.dat | 162.223.90.90:1688 | kms.digiboy.ir | ColoUp | US | unknown |
924 | test.dat | 113.99.216.7:1688 | xykz.f3322.org | No.31,Jin-rong Street | CN | unknown |
2616 | test.dat | 121.196.29.254:1688 | kms.lotro.cc | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
2940 | test.dat | 162.255.119.150:1688 | kms789.com | Namecheap, Inc. | US | suspicious |
2236 | test.dat | 168.235.74.243:1688 | kms.srv.crsoo.com | RamNode LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
kms.digiboy.ir |
| unknown |
dns.msftncsi.com |
| shared |
hq1.chinancce.com |
| unknown |
xykz.f3322.org |
| unknown |
kms.lotro.cc |
| unknown |
kms789.com |
| suspicious |
kms.srv.crsoo.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |