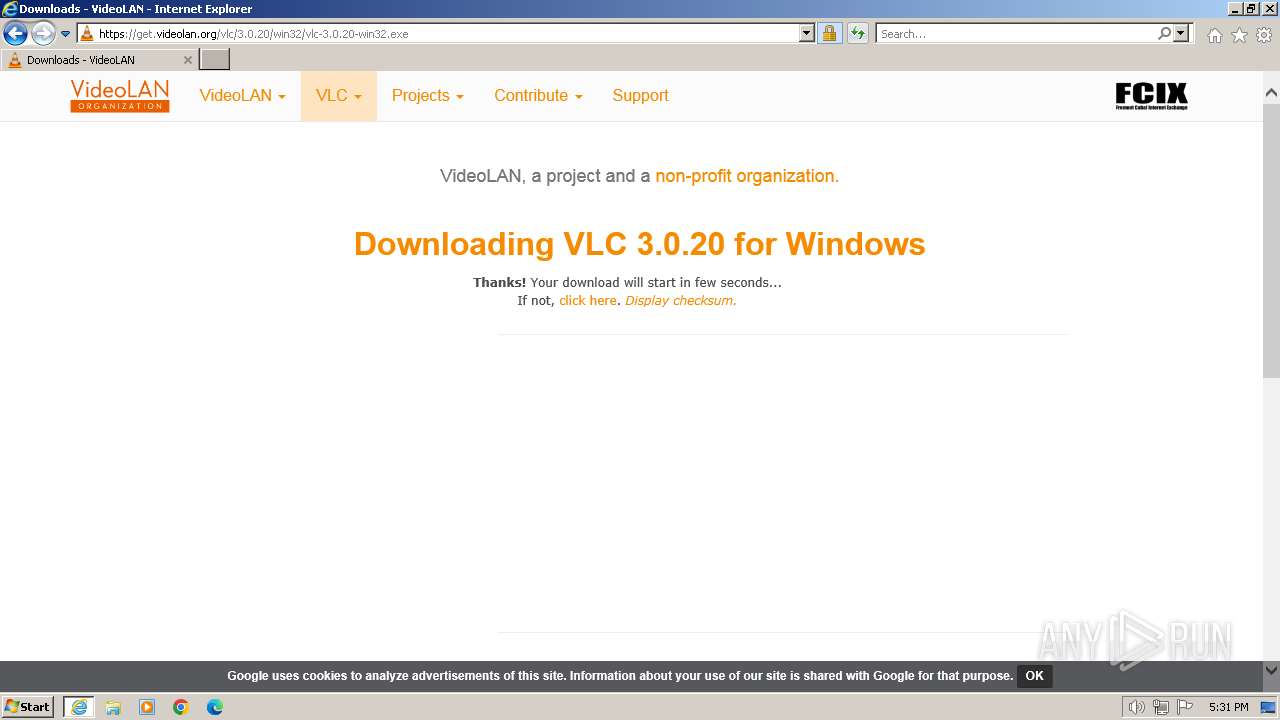
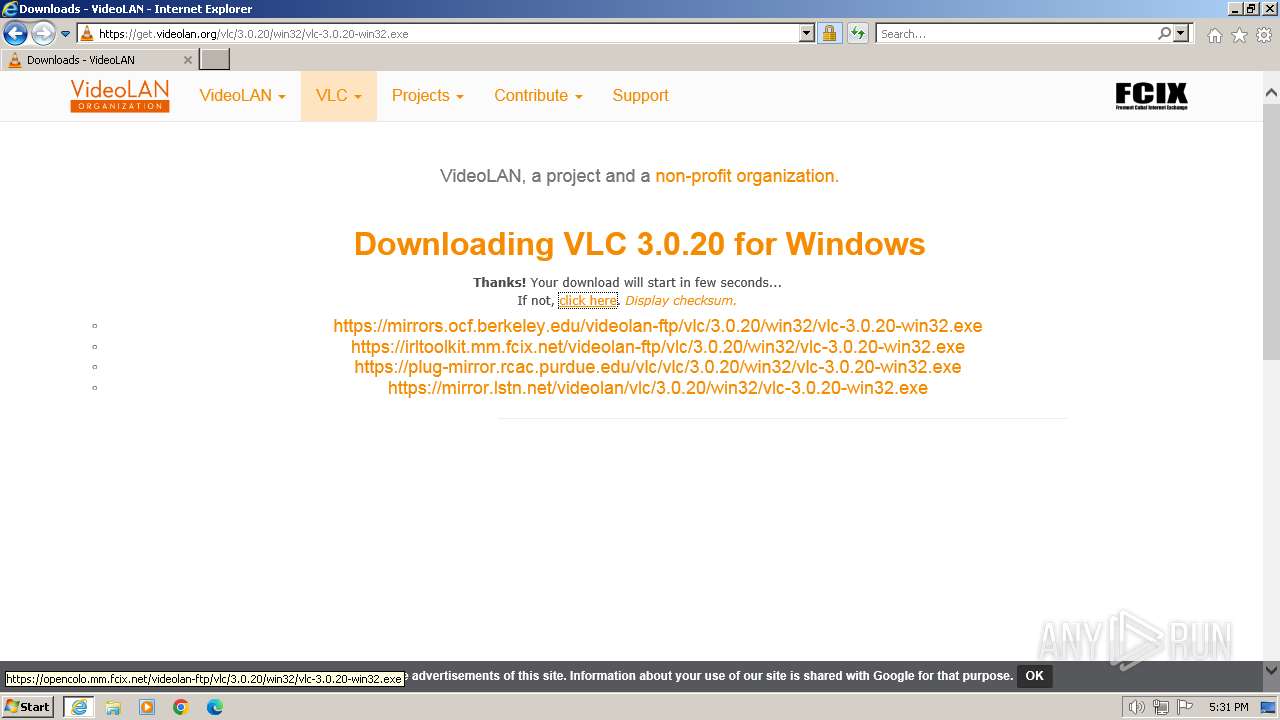
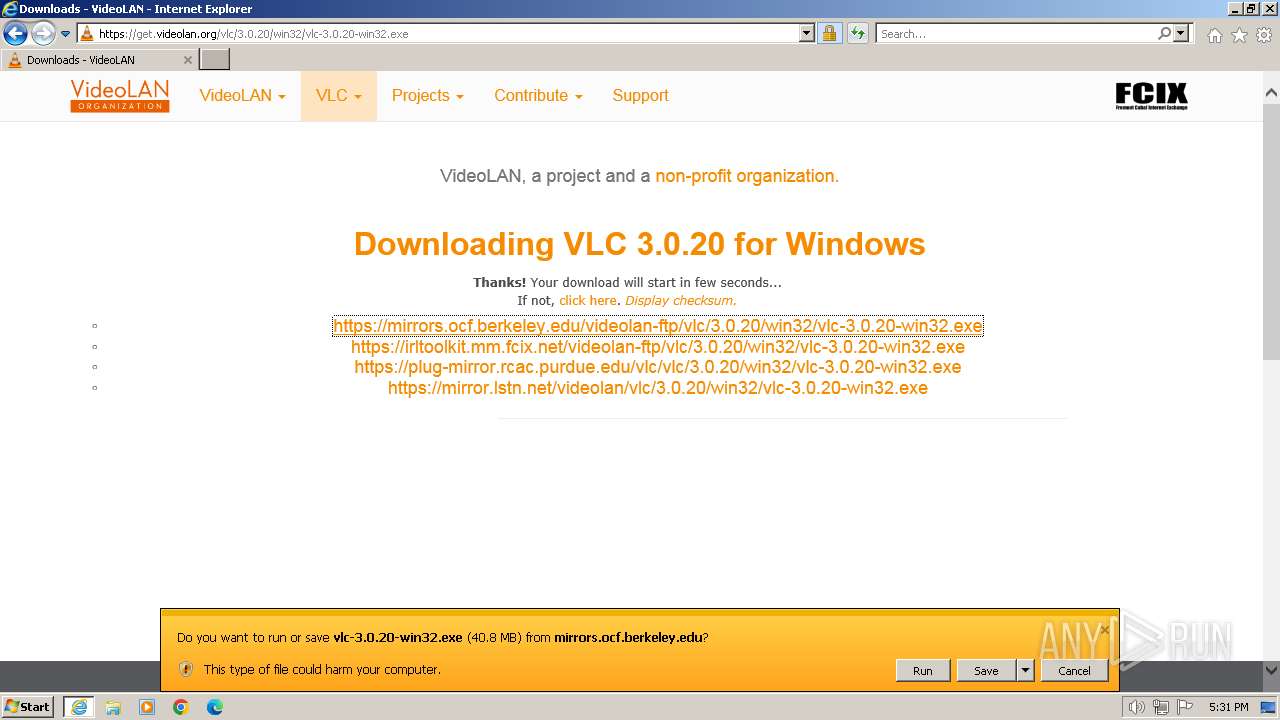
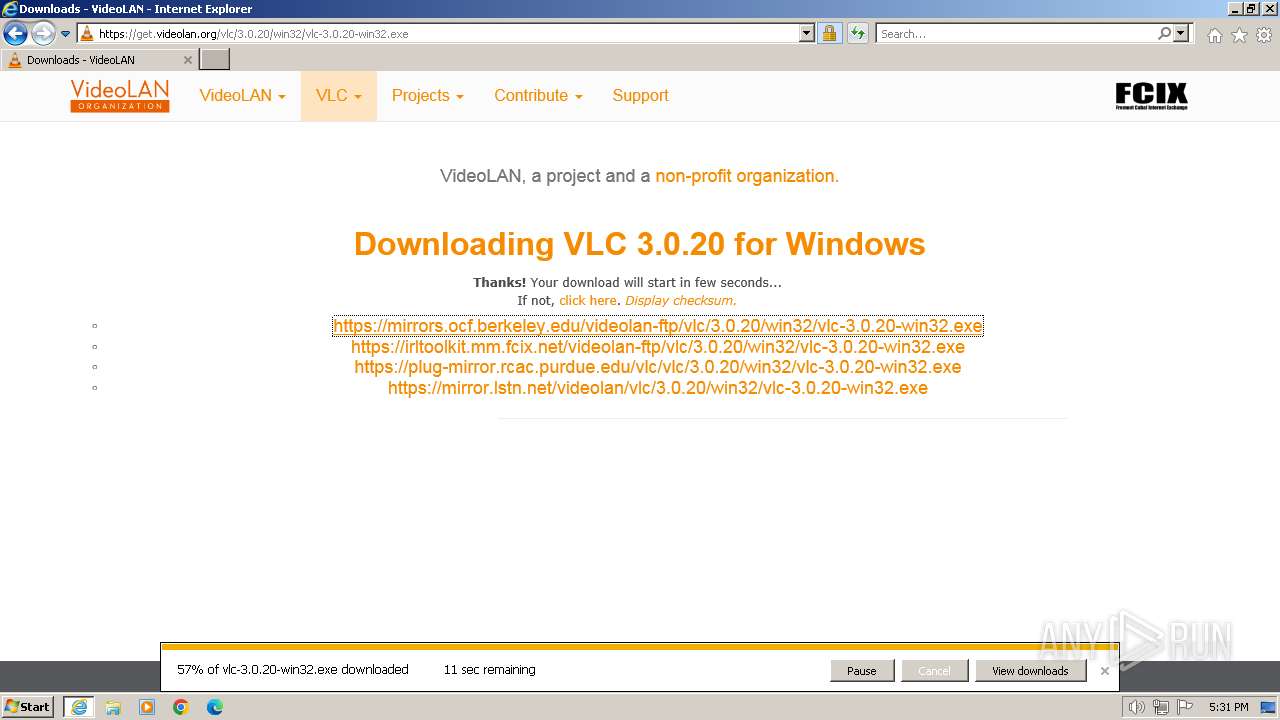
| URL: | https://www.videolan.org/vlc/download-windows.es.html |
| Full analysis: | https://app.any.run/tasks/83ba6aef-4866-48ad-a223-a0d5d3b1d7f7 |
| Verdict: | Malicious activity |
| Analysis date: | January 26, 2024, 17:30:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 89BE36263BB6AC3EFEDC0F855CD59ED4 |
| SHA1: | B849266C01F4C25C3482362FDE68E30CFE2FDB58 |
| SHA256: | F6626950F714A7E6FE041F40975AF11C32F8241B078A819CB6F2612A7205A036 |
| SSDEEP: | 3:N8DSLABAKJELoC0WJSM1KSgLD0n:2OLAtJEUxM1KSy0 |
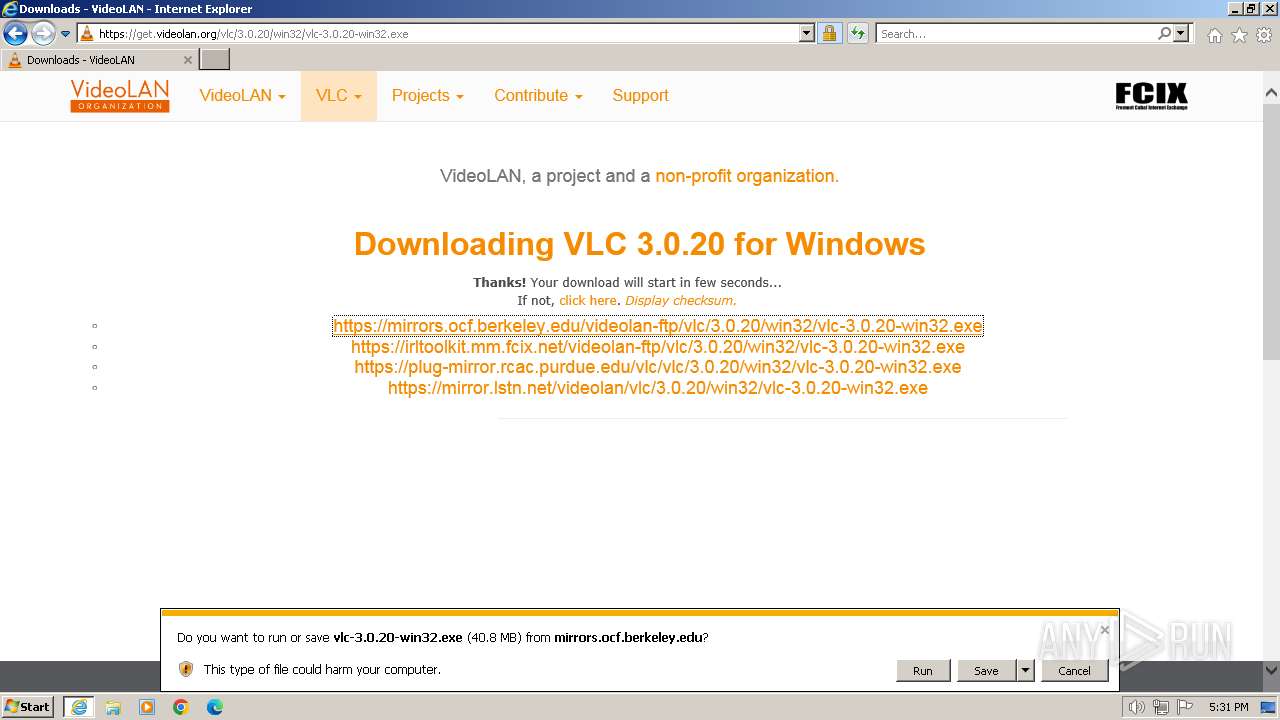
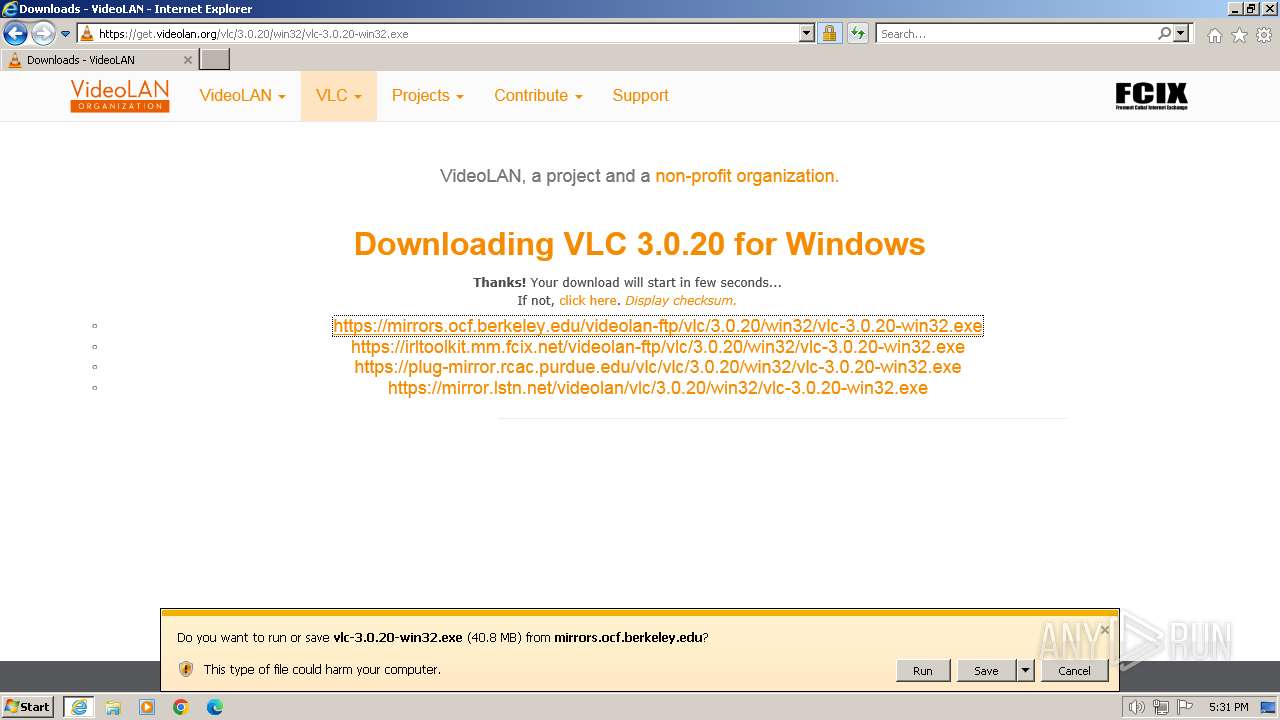
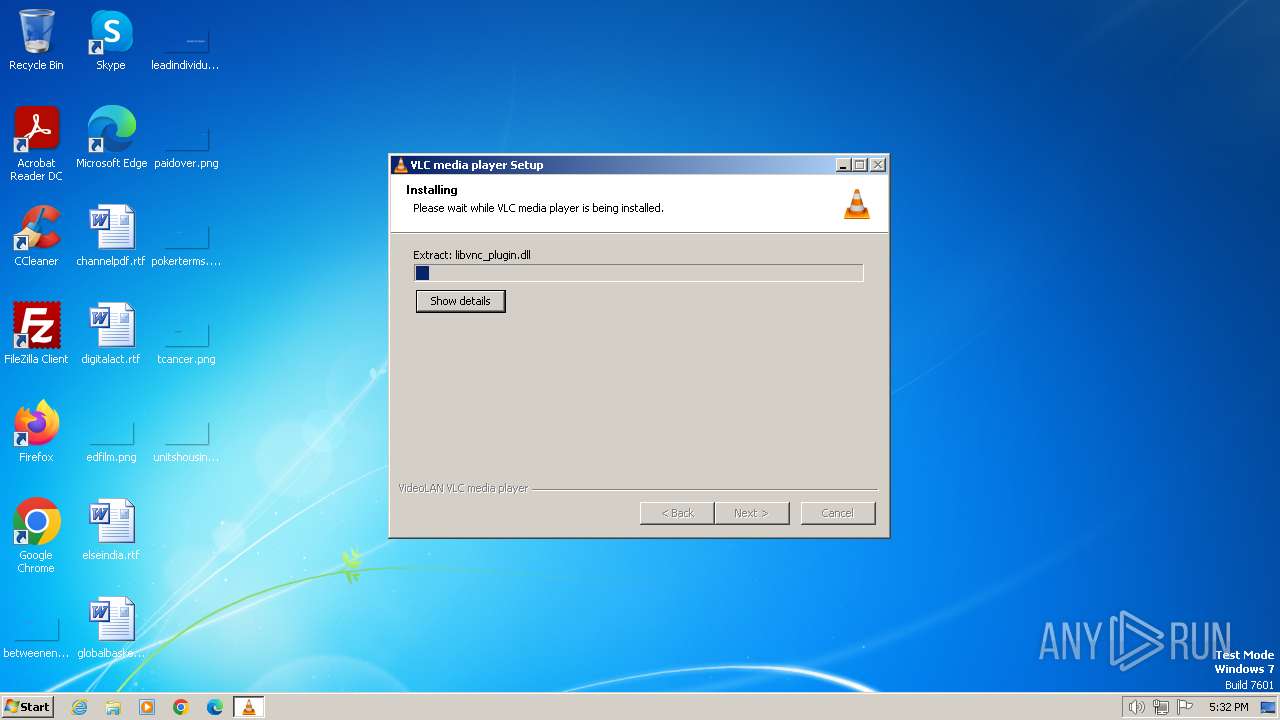
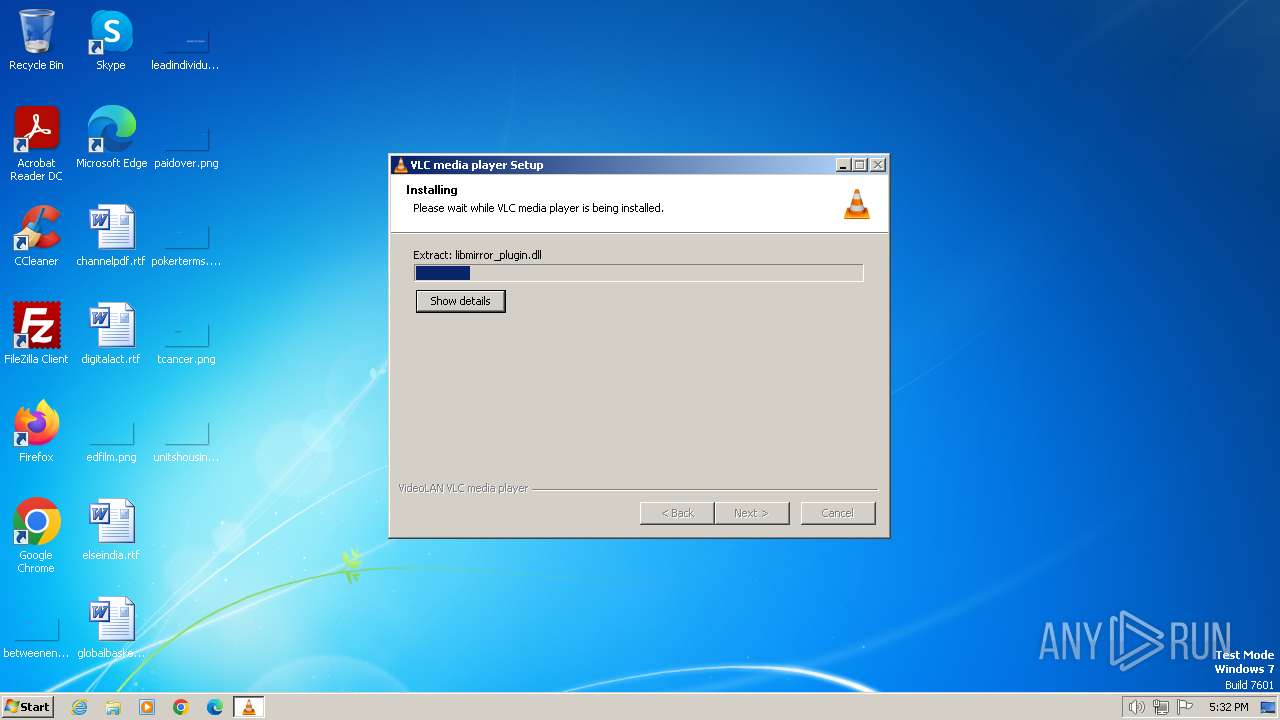
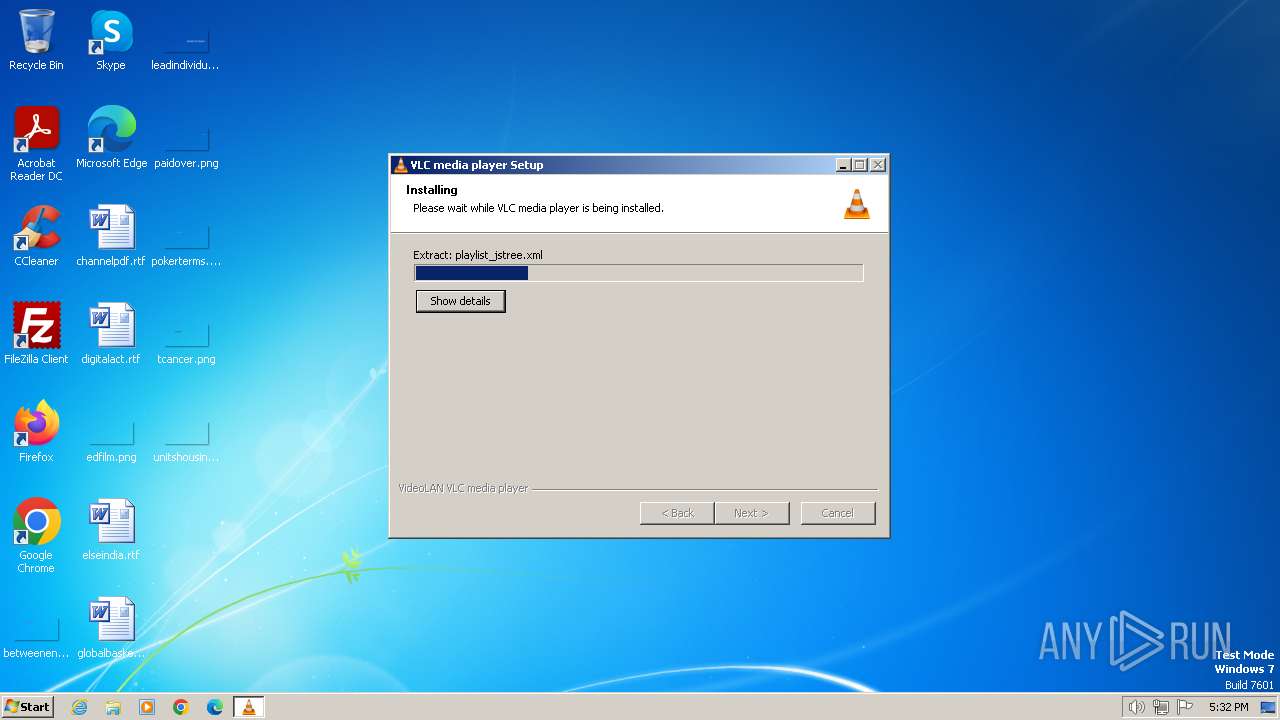
MALICIOUS
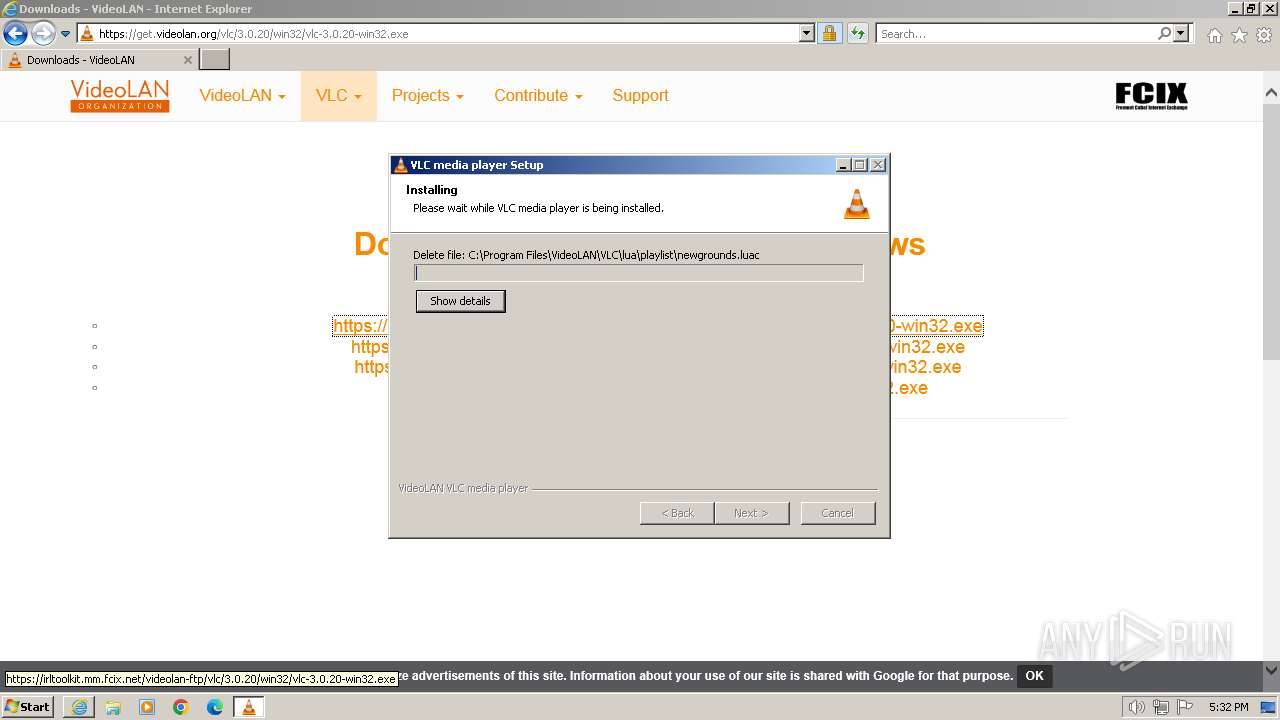
Drops the executable file immediately after the start
- vlc-3.0.20-win32.exe (PID: 3376)
SUSPICIOUS
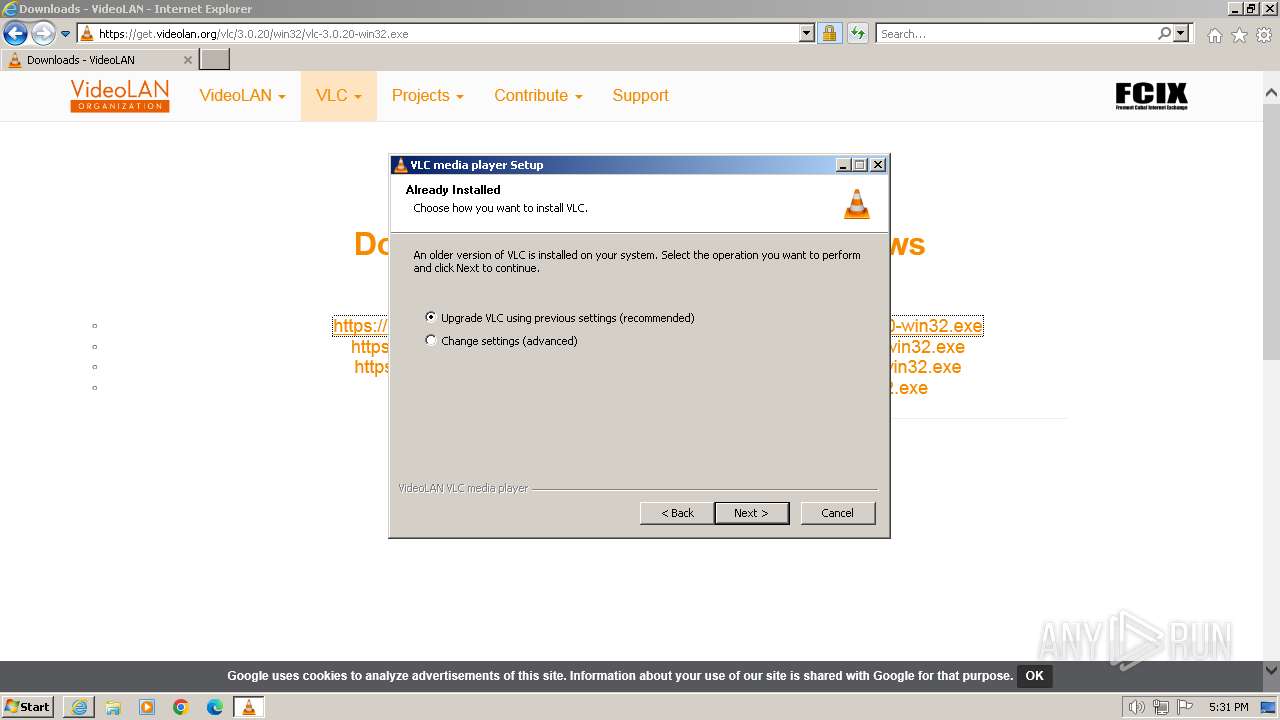
Searches for installed software
- vlc-3.0.20-win32.exe (PID: 3376)
Malware-specific behavior (creating "System.dll" in Temp)
- vlc-3.0.20-win32.exe (PID: 3376)
The process creates files with name similar to system file names
- vlc-3.0.20-win32.exe (PID: 3376)
Executable content was dropped or overwritten
- vlc-3.0.20-win32.exe (PID: 3376)
Starts application with an unusual extension
- vlc-3.0.20-win32.exe (PID: 3376)
Explorer used for Indirect Command Execution
- explorer.exe (PID: 3852)
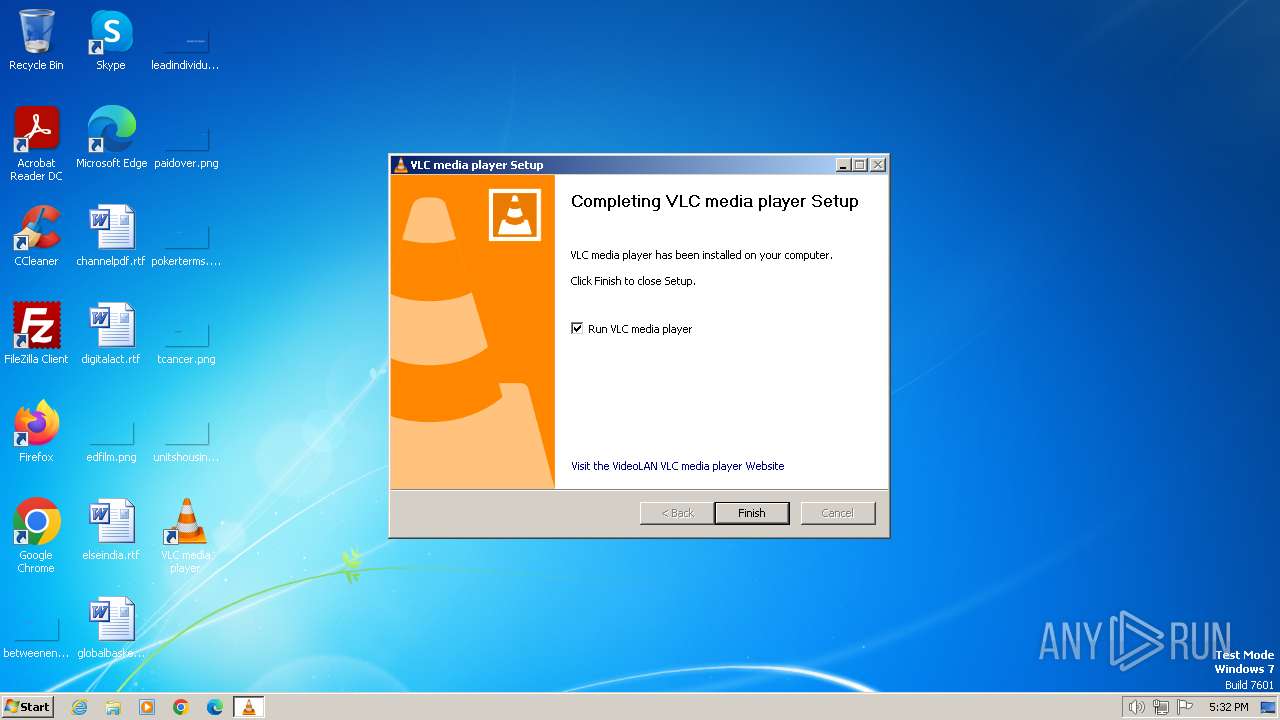
Creates a software uninstall entry
- vlc-3.0.20-win32.exe (PID: 3376)
INFO
Executable content was dropped or overwritten
- iexplore.exe (PID: 2560)
Checks supported languages
- vlc-3.0.20-win32.exe (PID: 3376)
- ns2AA2.tmp (PID: 3088)
- vlc.exe (PID: 3920)
- vlc-cache-gen.exe (PID: 3624)
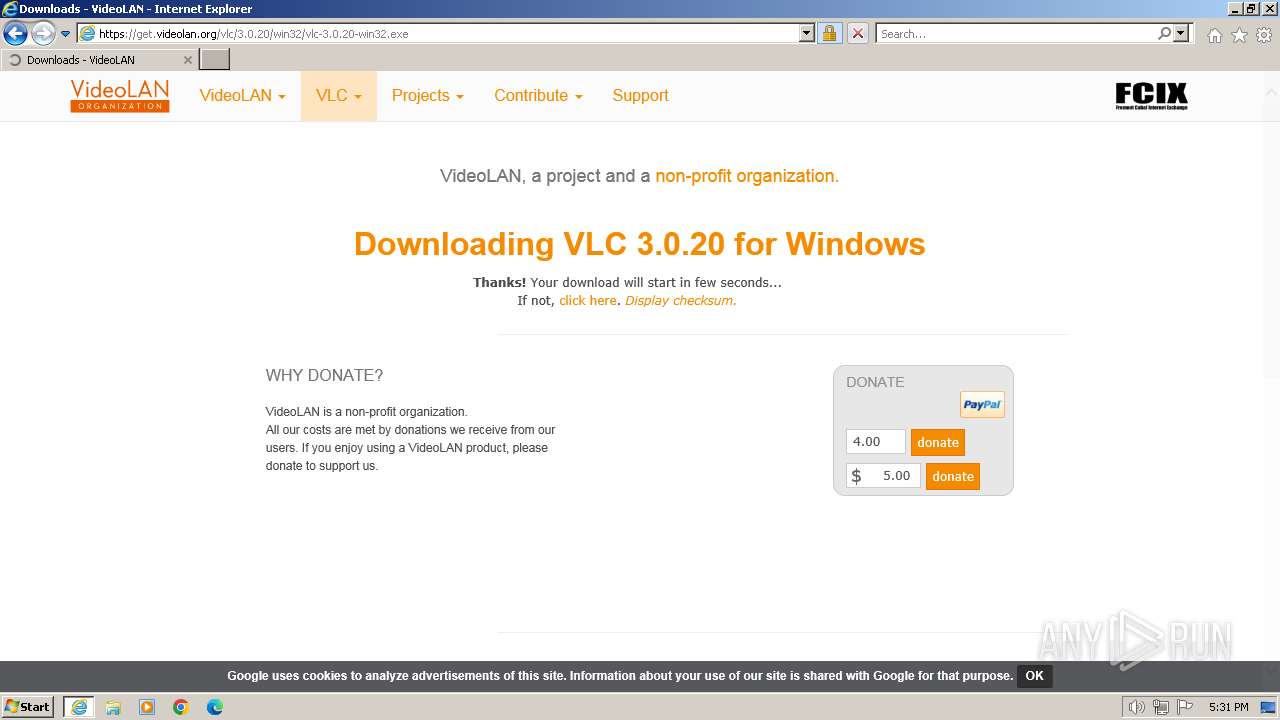
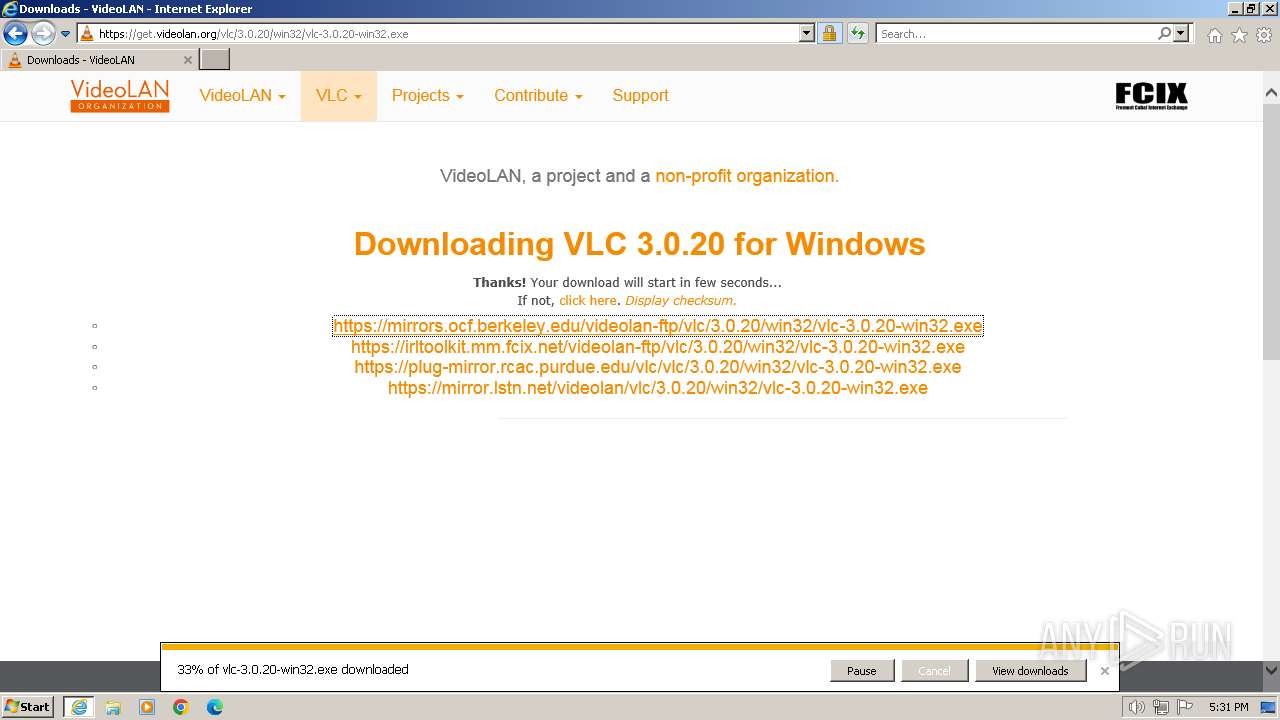
The process uses the downloaded file
- iexplore.exe (PID: 2640)
Reads the computer name
- vlc-3.0.20-win32.exe (PID: 3376)
- vlc.exe (PID: 3920)
Drops the executable file immediately after the start
- iexplore.exe (PID: 2560)
Application launched itself
- iexplore.exe (PID: 2640)
Create files in a temporary directory
- vlc-3.0.20-win32.exe (PID: 3376)
Creates files in the program directory
- vlc-3.0.20-win32.exe (PID: 3376)
- vlc-cache-gen.exe (PID: 3624)
Reads the machine GUID from the registry
- vlc-cache-gen.exe (PID: 3624)
- vlc-3.0.20-win32.exe (PID: 3376)
Reads the Internet Settings
- explorer.exe (PID: 3968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
54
Monitored processes
9
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2560 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2640 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2640 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.videolan.org/vlc/download-windows.es.html" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
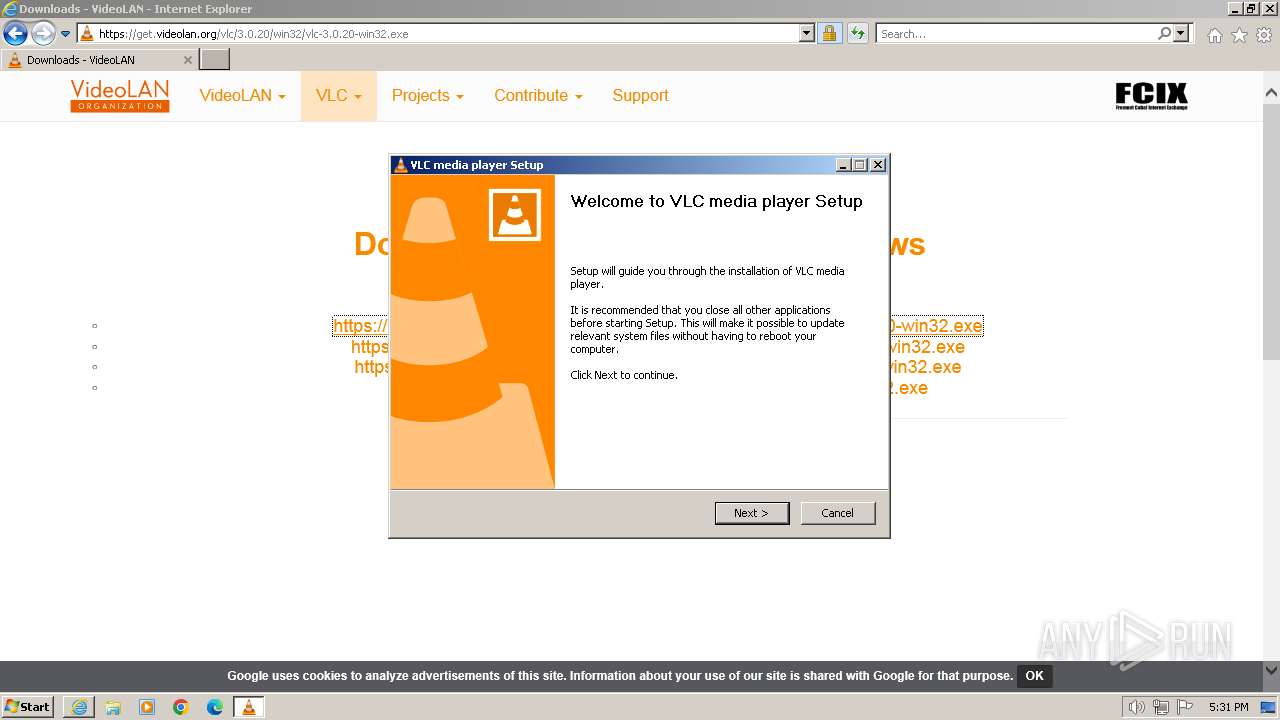
| 3012 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\vlc-3.0.20-win32.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\vlc-3.0.20-win32.exe | — | iexplore.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3088 | "C:\Users\admin\AppData\Local\Temp\nsxBDED.tmp\ns2AA2.tmp" "C:\Program Files\VideoLAN\VLC\vlc-cache-gen.exe" C:\Program Files\VideoLAN\VLC\plugins | C:\Users\admin\AppData\Local\Temp\nsxBDED.tmp\ns2AA2.tmp | — | vlc-3.0.20-win32.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3376 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\vlc-3.0.20-win32.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\vlc-3.0.20-win32.exe | iexplore.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3624 | "C:\Program Files\VideoLAN\VLC\vlc-cache-gen.exe" C:\Program Files\VideoLAN\VLC\plugins | C:\Program Files\VideoLAN\VLC\vlc-cache-gen.exe | ns2AA2.tmp | ||||||||||||
User: admin Company: VideoLAN Integrity Level: HIGH Description: VLC media player Exit code: 0 Version: 3.0.20 Modules
| |||||||||||||||
| 3852 | "C:\Windows\explorer.exe" "C:\Program Files\VideoLAN\VLC\vlc.exe" | C:\Windows\explorer.exe | — | vlc-3.0.20-win32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3920 | "C:\Program Files\VideoLAN\VLC\vlc.exe" | C:\Program Files\VideoLAN\VLC\vlc.exe | explorer.exe | ||||||||||||
User: admin Company: VideoLAN Integrity Level: MEDIUM Description: VLC media player Exit code: 0 Version: 3.0.20 Modules
| |||||||||||||||
| 3968 | C:\Windows\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
34 150
Read events
33 003
Write events
1 055
Delete events
92
Modification events
| (PID) Process: | (2640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2640) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
380
Suspicious files
208
Text files
147
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2560 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\download-windows.es[1].htm | html | |
MD5:AF1B059051B9BEB9E08CAFED886865E0 | SHA256:F5352D722853B982F57C38BCBF6A0FC644D56F62E506017659920F0DB7BB9250 | |||
| 2560 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:BF7706472D02CAF3DDB5984820002EDE | SHA256:6152B19C03D9AE57A5D8CC79BFAC9B2297B2C688351497F0304892CD2C7406F2 | |||
| 2560 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\slick.min[1].css | text | |
MD5:5068CEFA5422D93D178FE1EB11B12F07 | SHA256:392312E066C737ED7E5E050AE32EA7A23CE558E0A74464E6EABFCC2DA70DEF67 | |||
| 2560 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 2560 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar96A2.tmp | cat | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
| 2560 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\slimbox2[1].css | text | |
MD5:D01B890D26B1C593A8C9A71CC0789857 | SHA256:AD845491516A444170E1DB5FA298BECB6A665E26BB17CDB991772DCDF092EBE1 | |||
| 2560 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\bootstrap.min[1].js | text | |
MD5:08727E57EFBDAC291AEE21A4F2CD66E4 | SHA256:261E9641B228870B00CBC0C9A7692D6165E48E5427B7A6947E8218DA93BE0AAD | |||
| 2560 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar96A4.tmp | binary | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
| 2560 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:60FE01DF86BE2E5331B0CDBE86165686 | SHA256:C08CCBC876CD5A7CDFA9670F9637DA57F6A1282198A9BC71FC7D7247A6E5B7A8 | |||
| 2560 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\slimbox2[1].js | text | |
MD5:85C51C7F4732B219213191E253515672 | SHA256:AC6A14DD559F18840C74256210AF040D9CBE6734E61CAD6406F272D7DDB96913 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
59
DNS requests
26
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2560 | iexplore.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
2560 | iexplore.exe | GET | 304 | 184.24.77.187:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a0aa2a2858c872c9 | unknown | — | — | unknown |
2560 | iexplore.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | unknown | binary | 724 b | unknown |
2560 | iexplore.exe | GET | 200 | 184.24.77.187:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?d66bcfdf10b71413 | unknown | compressed | 65.2 Kb | unknown |
2560 | iexplore.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDE6XWylEpsdhIHrOIVW5lM | unknown | binary | 472 b | unknown |
2640 | iexplore.exe | GET | 304 | 184.24.77.187:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?1012f9097c4a32e9 | unknown | — | — | unknown |
2560 | iexplore.exe | GET | 200 | 184.24.77.82:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgTb%2BvOgEqJJwOXEUmdXM0NhVA%3D%3D | unknown | binary | 503 b | unknown |
2560 | iexplore.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
2560 | iexplore.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCECTIWCtOriVGCn%2FSzrsWgJo%3D | unknown | binary | 471 b | unknown |
2560 | iexplore.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEGvAvXmprKMFCmCe7TxUGUo%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2560 | iexplore.exe | 213.36.253.2:443 | www.videolan.org | Free SAS | FR | unknown |
2560 | iexplore.exe | 184.24.77.187:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2560 | iexplore.exe | 69.192.161.44:80 | x1.c.lencr.org | AKAMAI-AS | DE | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2560 | iexplore.exe | 142.250.74.200:443 | www.googletagmanager.com | GOOGLE | US | unknown |
2560 | iexplore.exe | 142.250.185.67:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
2560 | iexplore.exe | 195.154.241.219:443 | get.videolan.org | Online S.a.s. | FR | unknown |
2560 | iexplore.exe | 142.250.185.78:443 | www.google-analytics.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.videolan.org |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
images.videolan.org |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
get.videolan.org |
| unknown |
www.google-analytics.com |
| whitelisted |
region1.google-analytics.com |
| whitelisted |
r3.o.lencr.org |
| shared |
Threats
Process | Message |
|---|---|
vlc-cache-gen.exe | main libvlc debug: min period: 1 ms, max period: 1000000 ms
|
vlc-cache-gen.exe | main libvlc debug: ignoring plugins cache file
|
vlc-cache-gen.exe | main libvlc debug: VLC media player - 3.0.20 Vetinari
|
vlc-cache-gen.exe | main libvlc debug: Copyright © 1996-2023 the VideoLAN team
|
vlc-cache-gen.exe | main libvlc debug: recursively browsing `C:\Program Files\VideoLAN\VLC\plugins'
|
vlc-cache-gen.exe | main libvlc debug: revision 3.0.20-0-g6f0d0ab126
|
vlc-cache-gen.exe | main libvlc debug: searching plug-in modules
|
vlc-cache-gen.exe | main libvlc debug: configured with /builds/videolan/vlc/extras/package/win32/../../../configure '--enable-update-check' '--enable-lua' '--enable-faad' '--enable-flac' '--enable-theora' '--enable-avcodec' '--enable-merge-ffmpeg' '--enable-dca' '--enable-mpc' '--enable-libass' '--enable-schroedinger' '--enable-realrtsp' '--enable-live555' '--enable-shout' '--enable-goom' '--enable-sse' '--enable-mmx' '--enable-libcddb' '--enable-zvbi' '--disable-telx' '--enable-nls' '--host=i686-w64-mingw32' '--with-contrib=../contrib/i686-w64-mingw32' '--with-breakpad=https://win.crashes.videolan.org' '--enable-qt' '--enable-skins2' '--enable-dvdread' '--enable-caca' 'host_alias=i686-w64-mingw32' 'CFLAGS= -D_WIN32_WINNT=0x0502 -DWINVER=0x502 -D__MSVCRT_VERSION__=0x700 ' 'CXXFLAGS= -D_WIN32_WINNT=0x0502 -DWINVER=0x502 -D__MSVCRT_VERSION__=0x700 ' 'PKG_CONFIG=pkg-config' 'PKG_CONFIG_LIBDIR=/usr/i686-w64-mingw32/lib/pkgconfig:/usr/lib/i686-w64-mingw32/pkgconfig'
|
vlc-cache-gen.exe | main libvlc debug: using multimedia timers as clock source
|
vlc-cache-gen.exe | main libvlc debug: saving plugins cache C:\Program Files\VideoLAN\VLC\plugins\plugins.dat
|