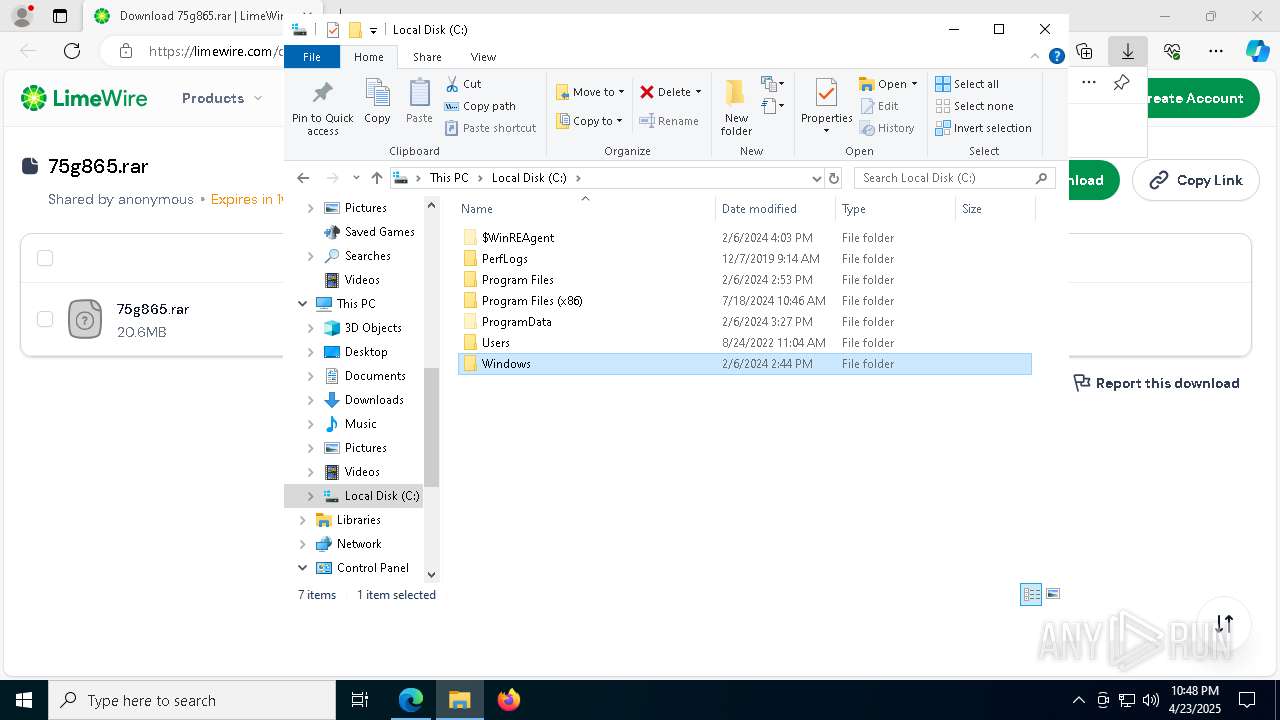
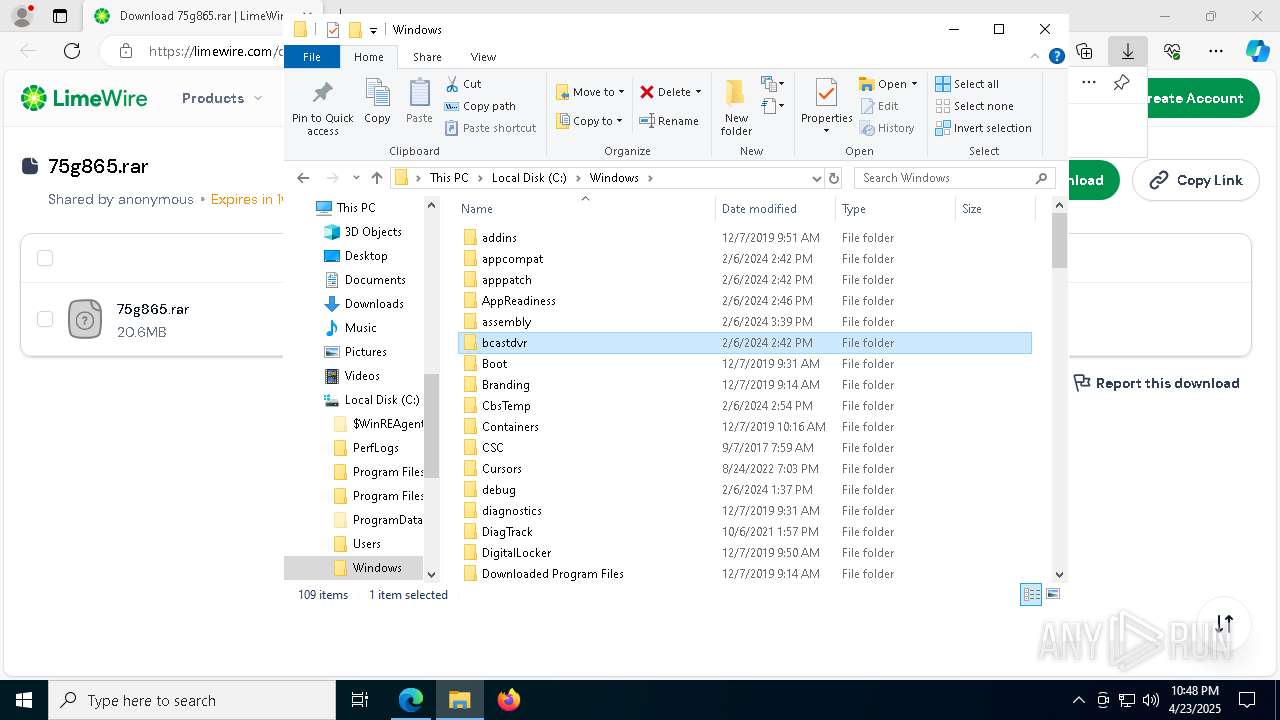
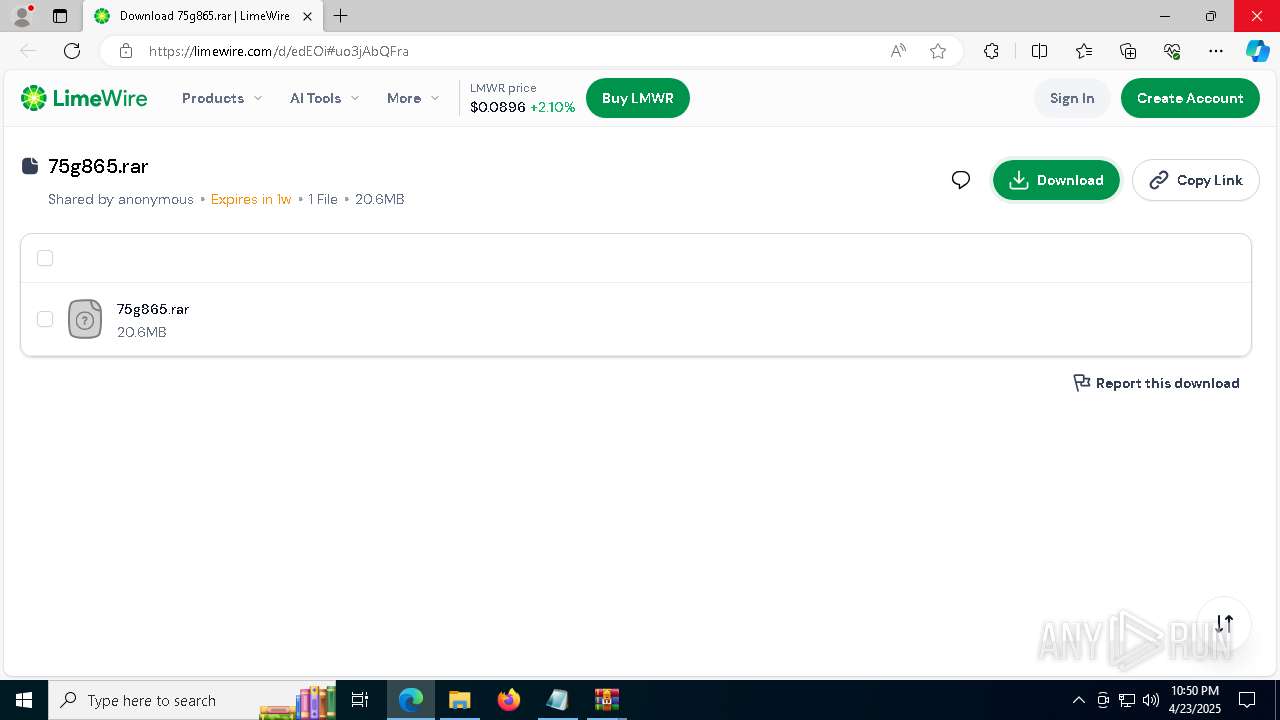
| URL: | https://limewire.com/d/edEOi#uo3jAbQFra |
| Full analysis: | https://app.any.run/tasks/11cbbdc2-18ca-4211-b816-25f4eac783c1 |
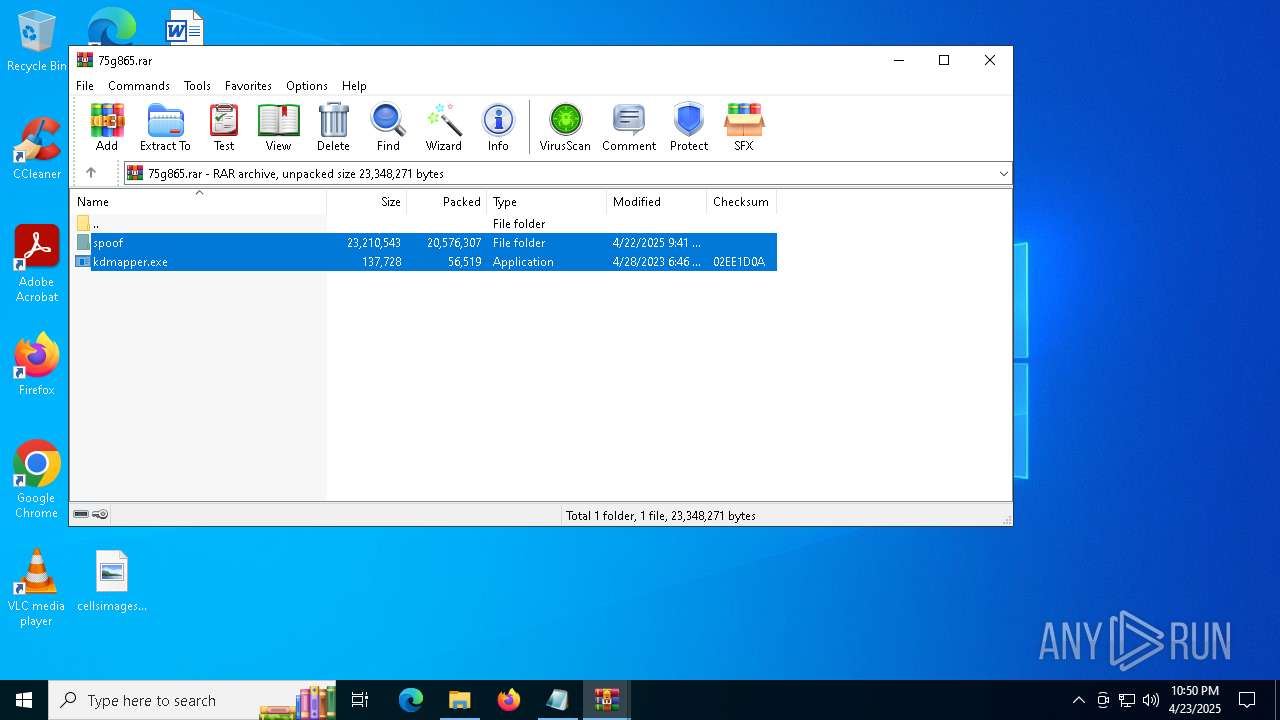
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2025, 22:47:39 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 94D11DD6454E65611D7F4BFDB6515DF8 |
| SHA1: | 77987908A4766CB6FE0F431715D76462F03F168D |
| SHA256: | F65A839A2A91CFD59F3B1CCF33290B3C5C475E0D6521EC345B6D233D91B7036D |
| SSDEEP: | 3:N8MIA/enKP0:2MIA/eKP0 |
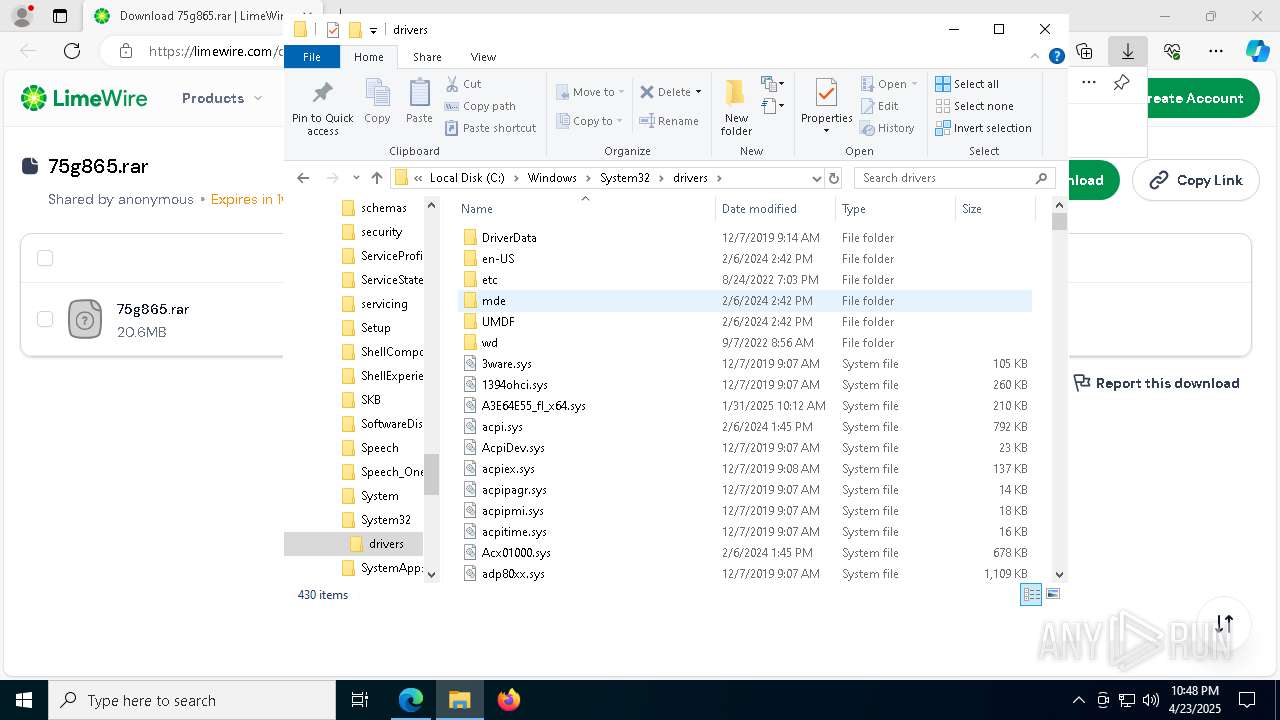
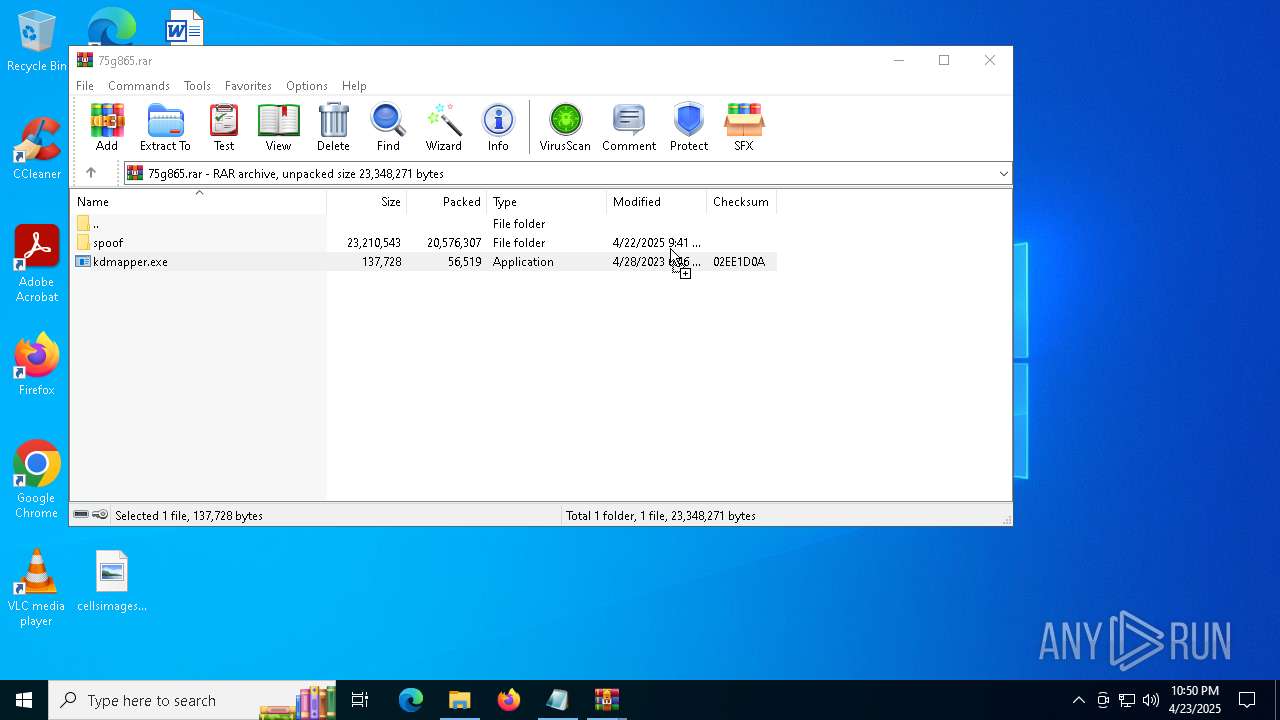
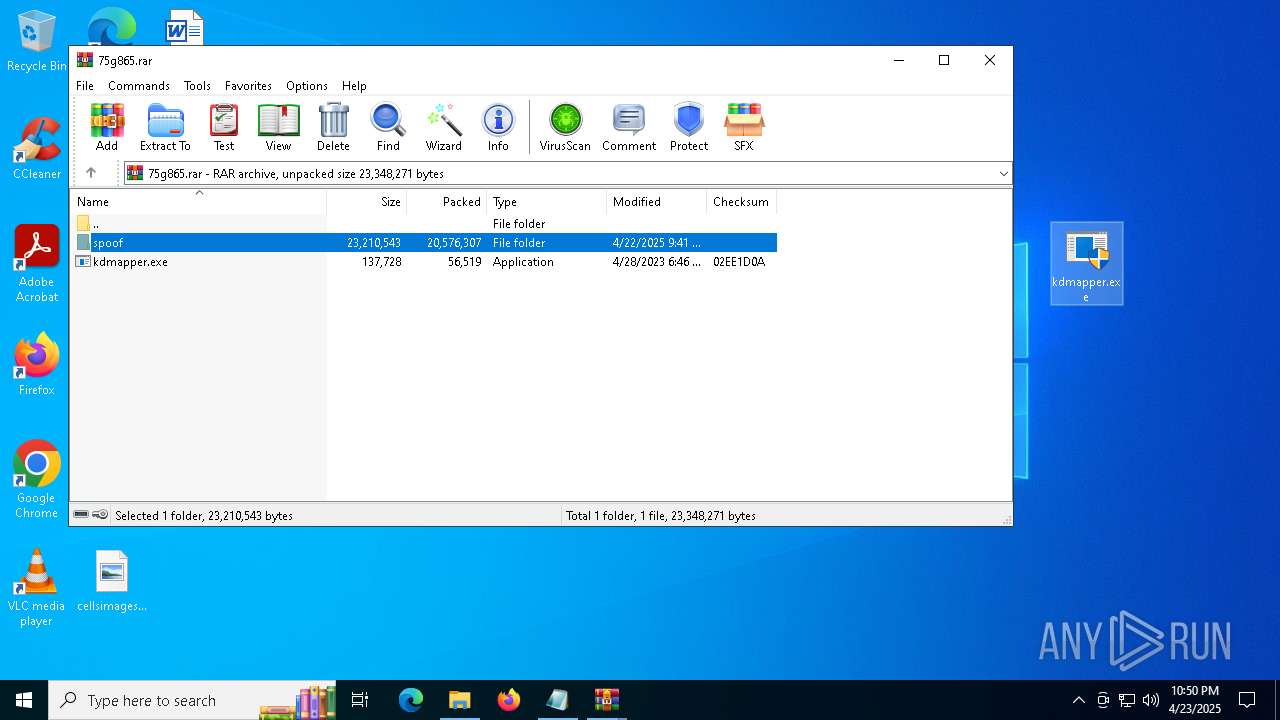
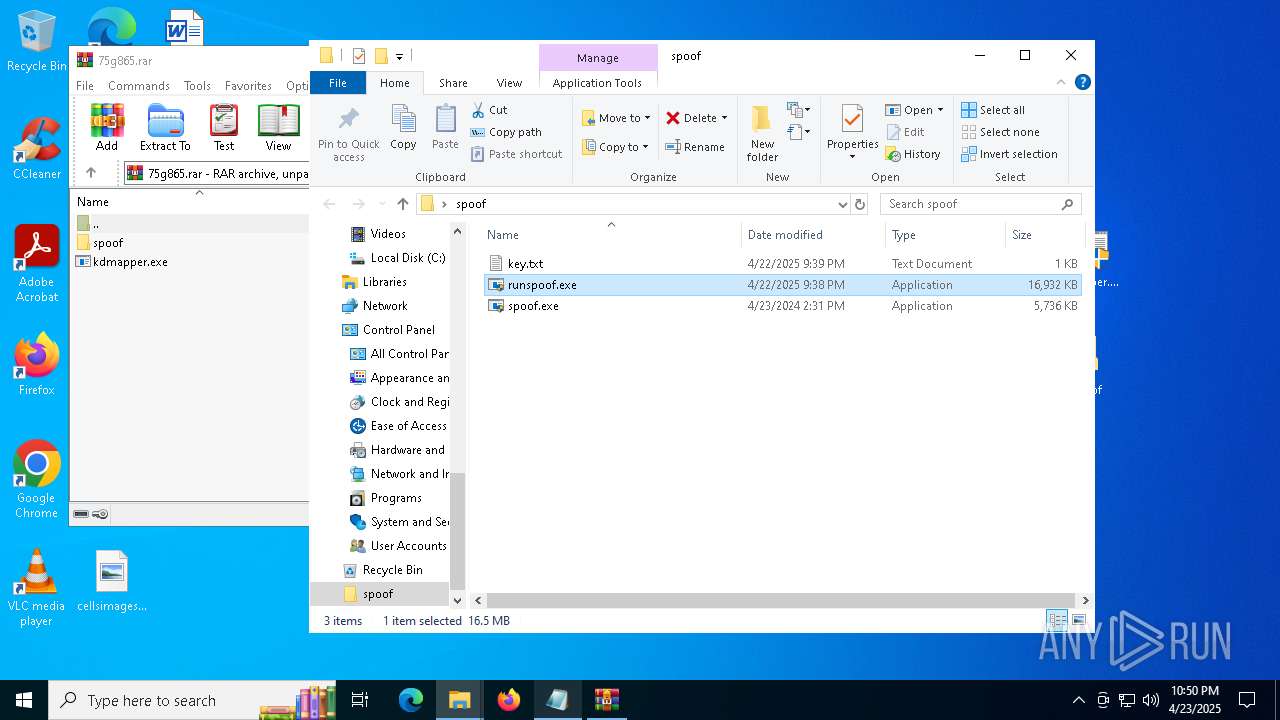
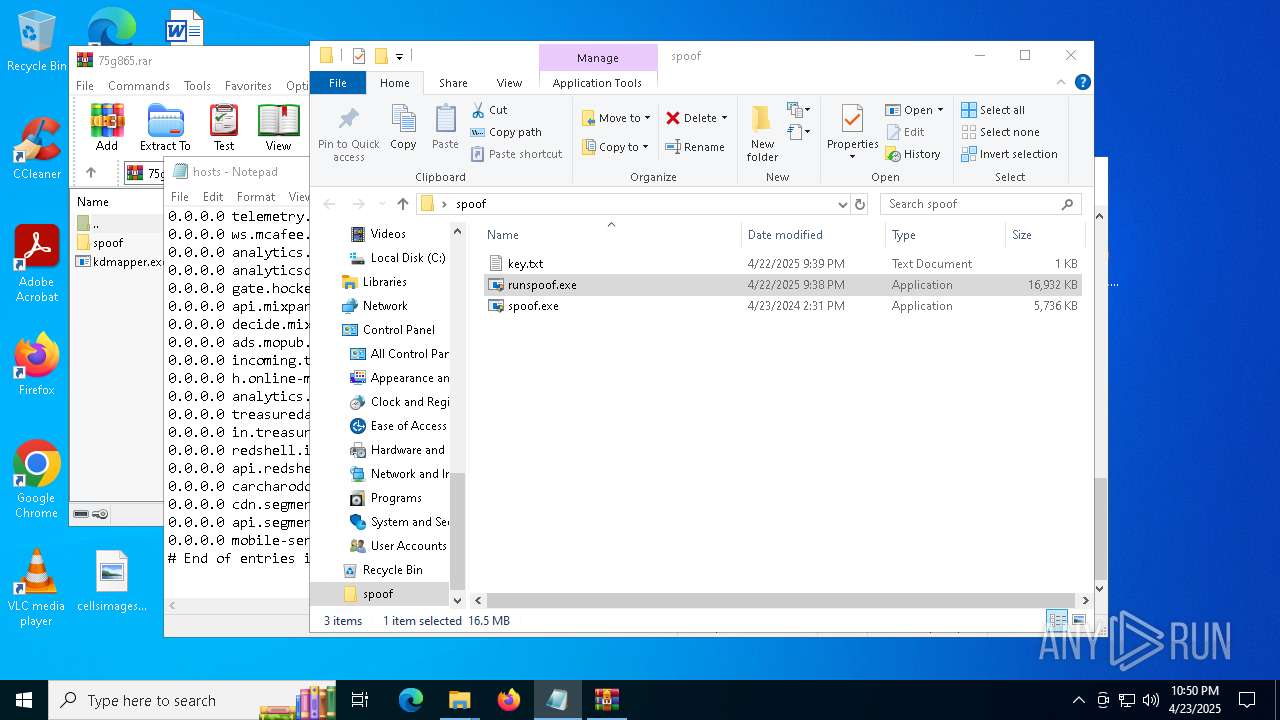
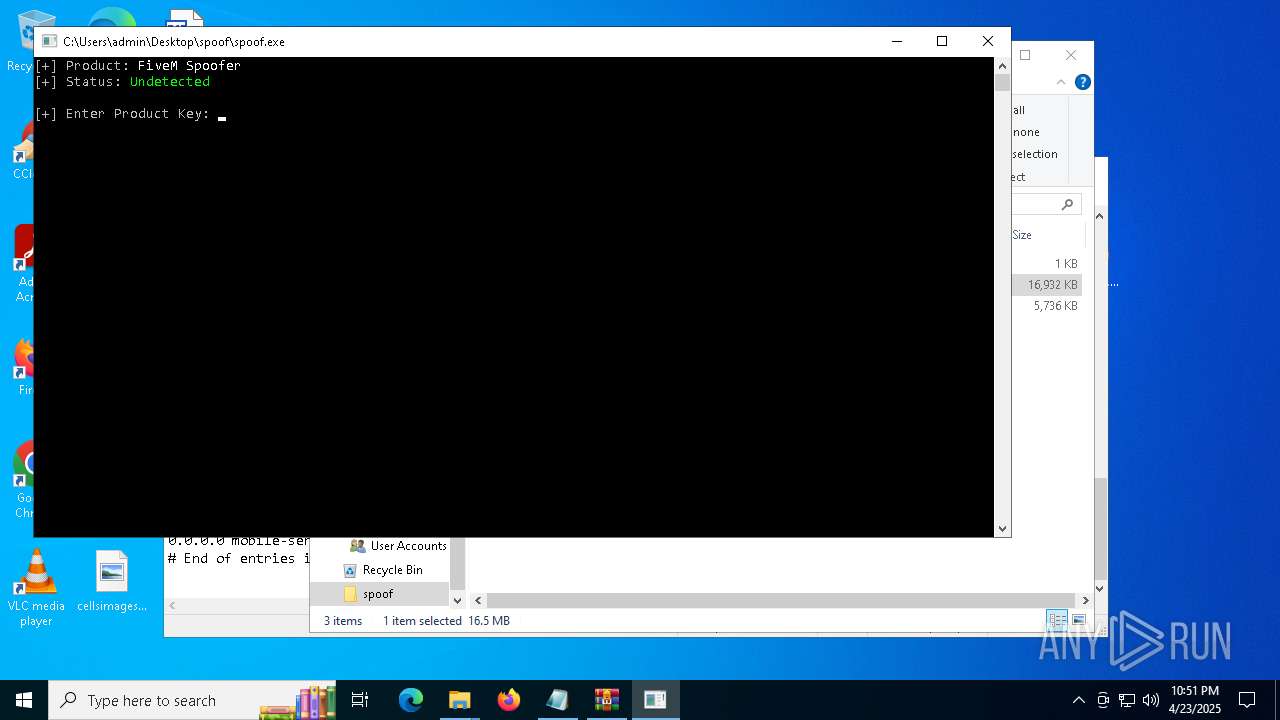
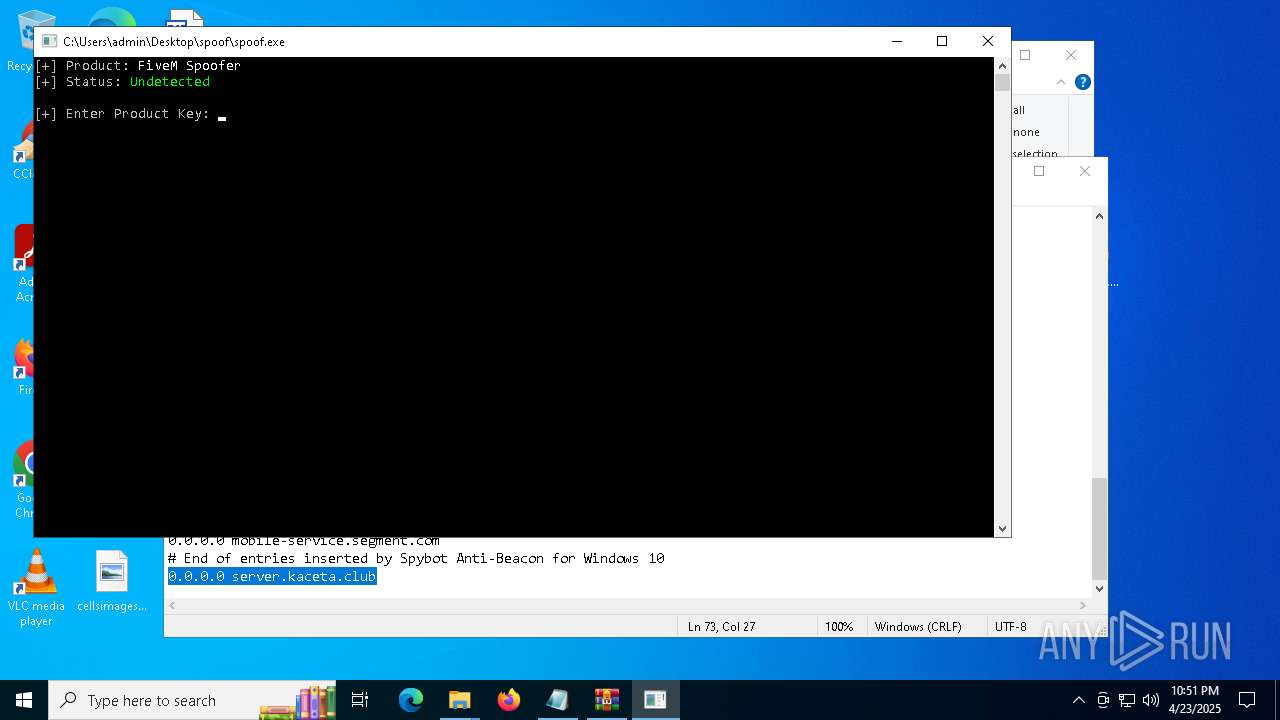
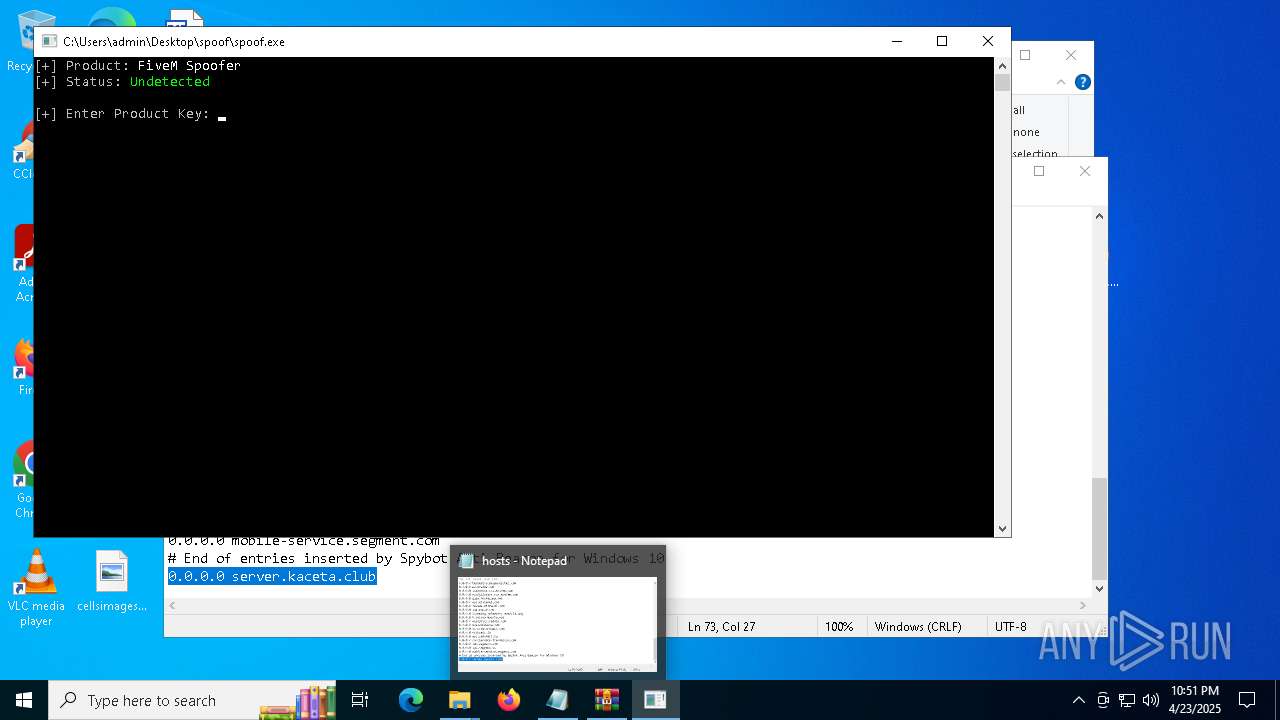
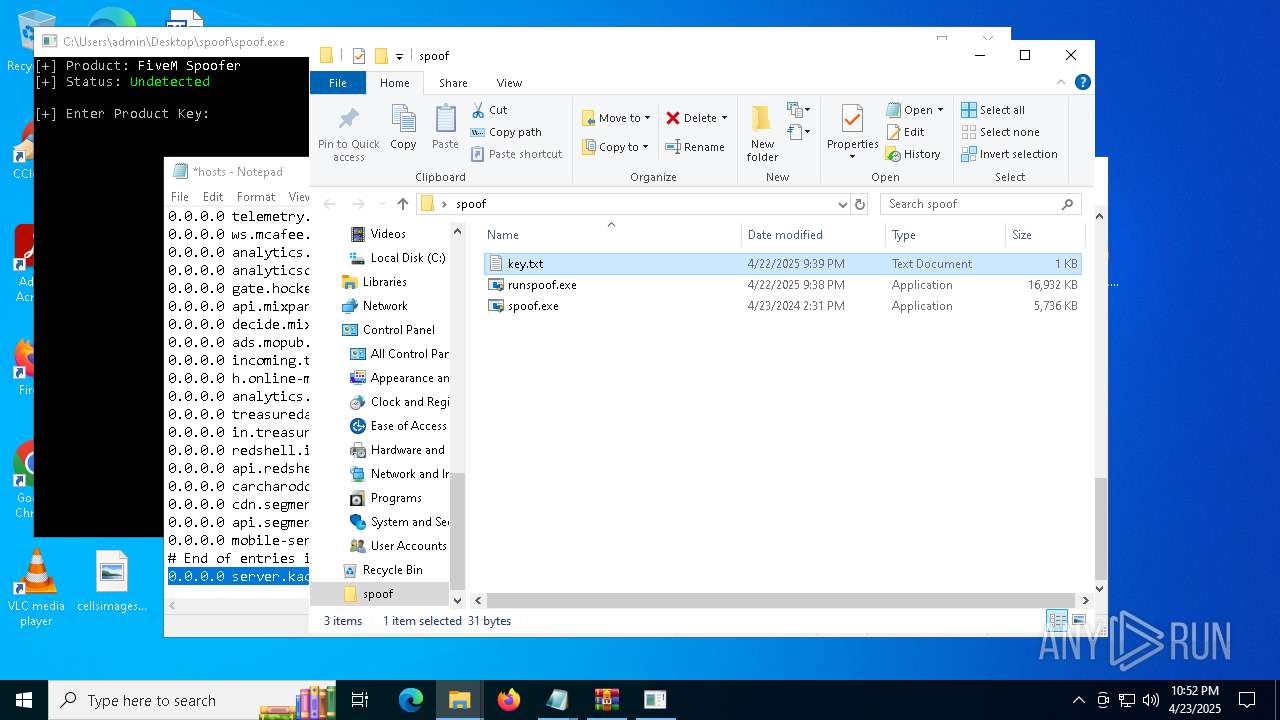
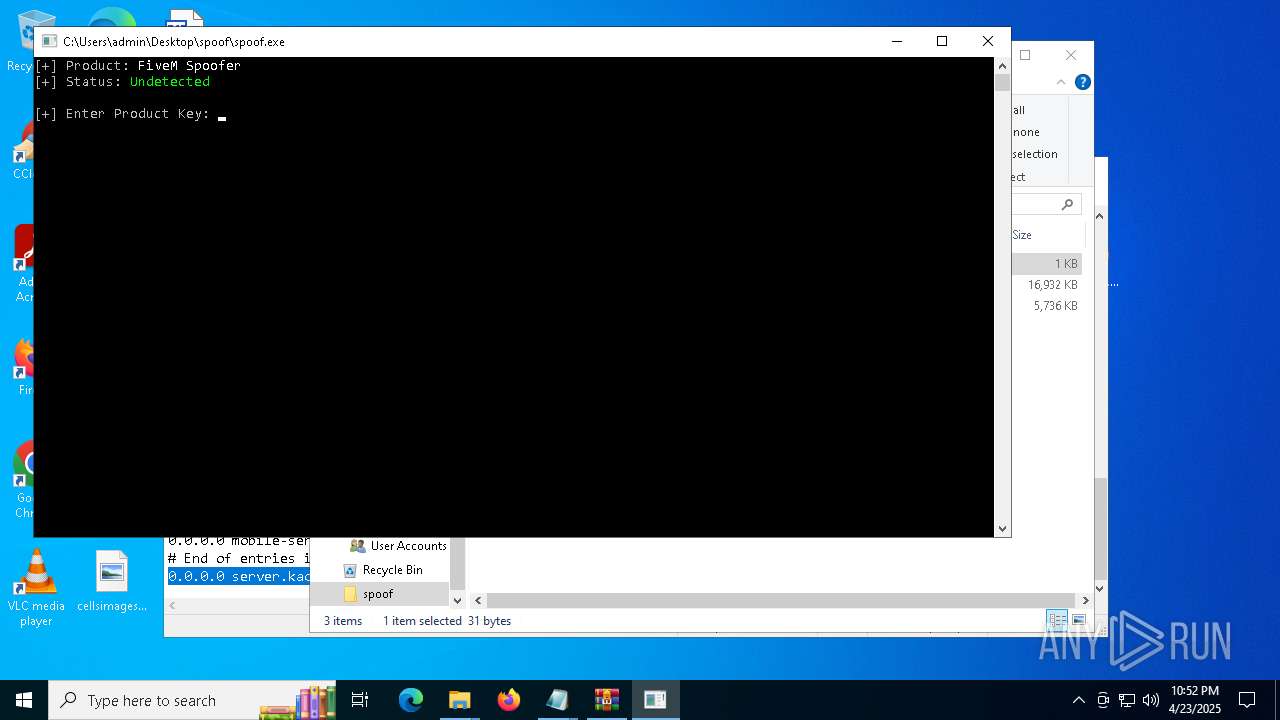
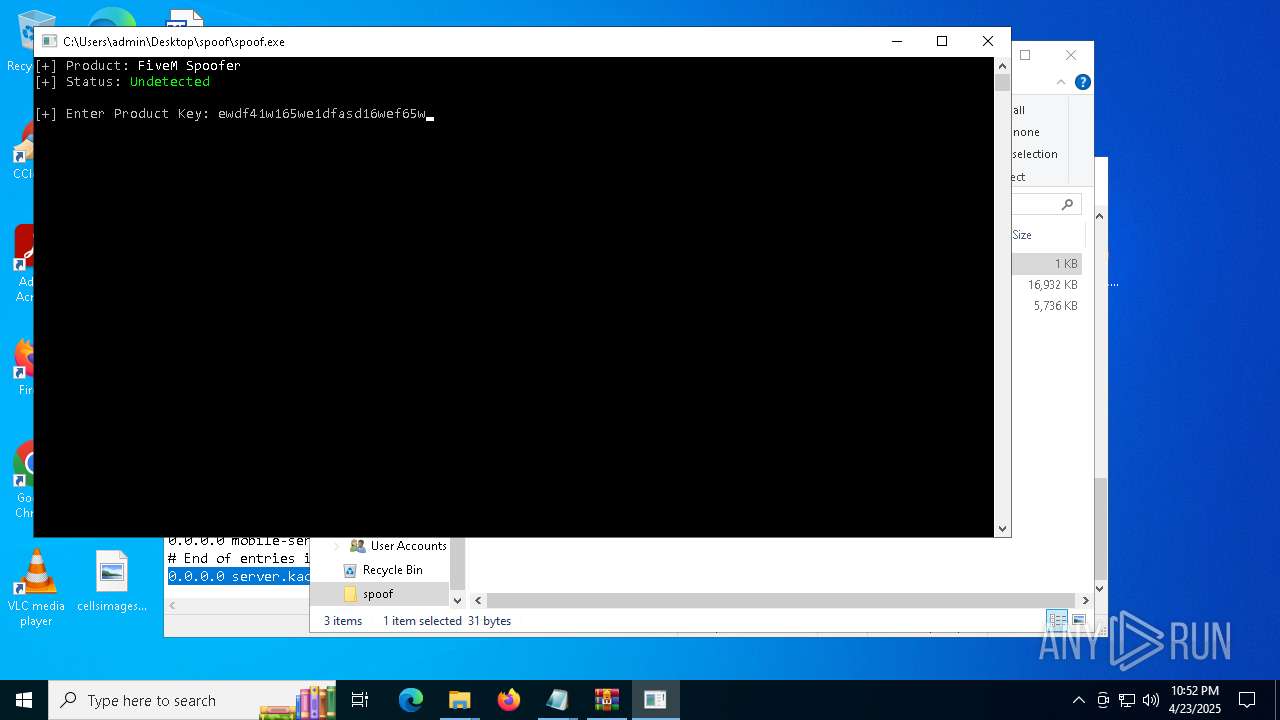
MALICIOUS
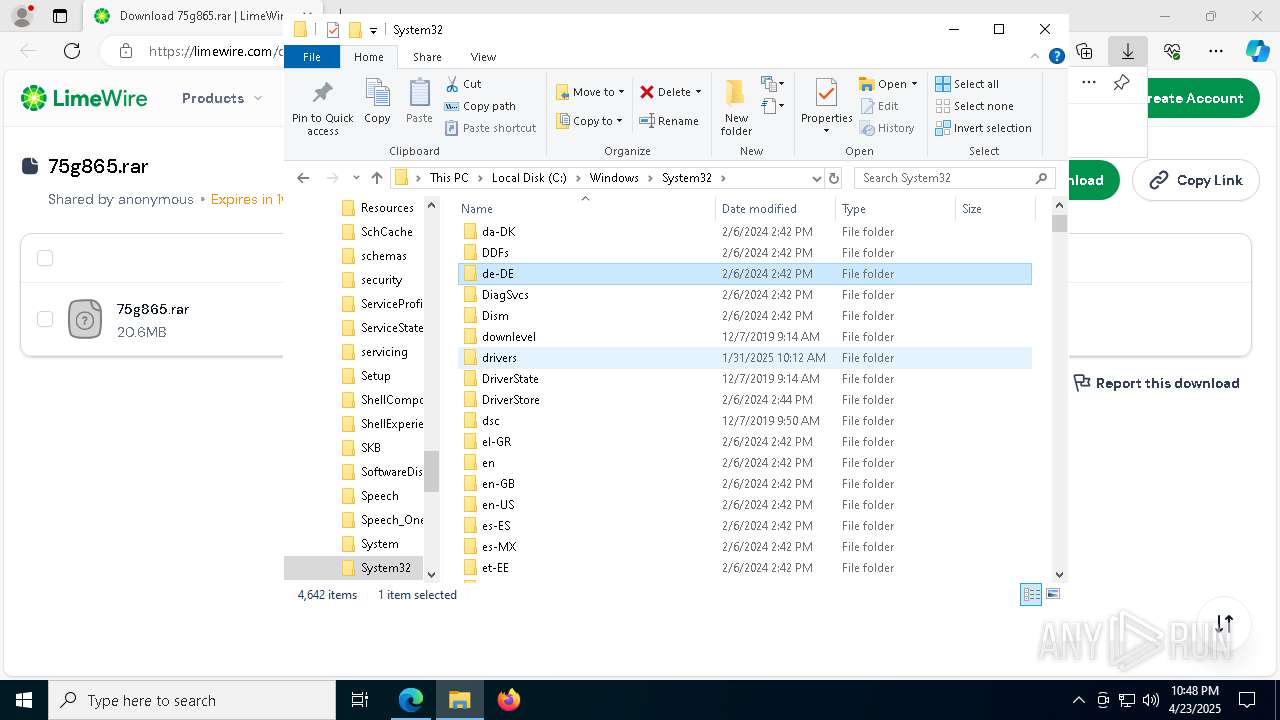
Vulnerable driver has been detected
- spoof.exe (PID: 3896)
SUSPICIOUS
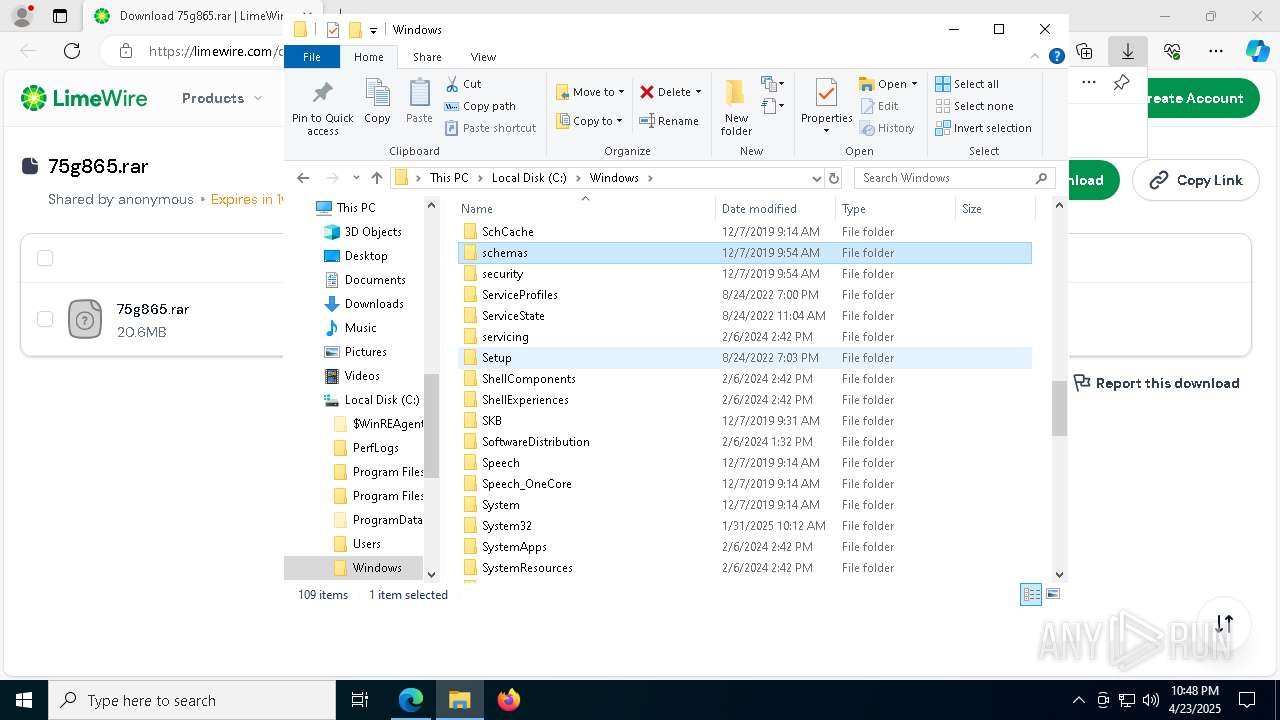
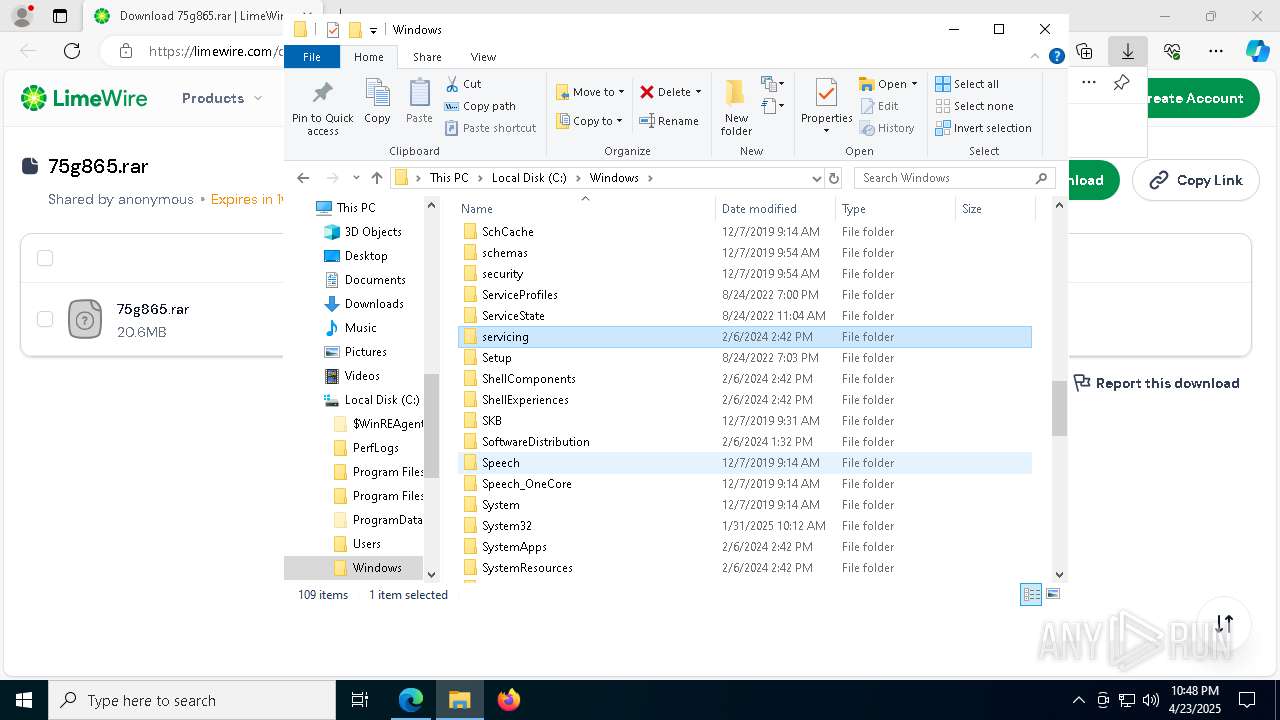
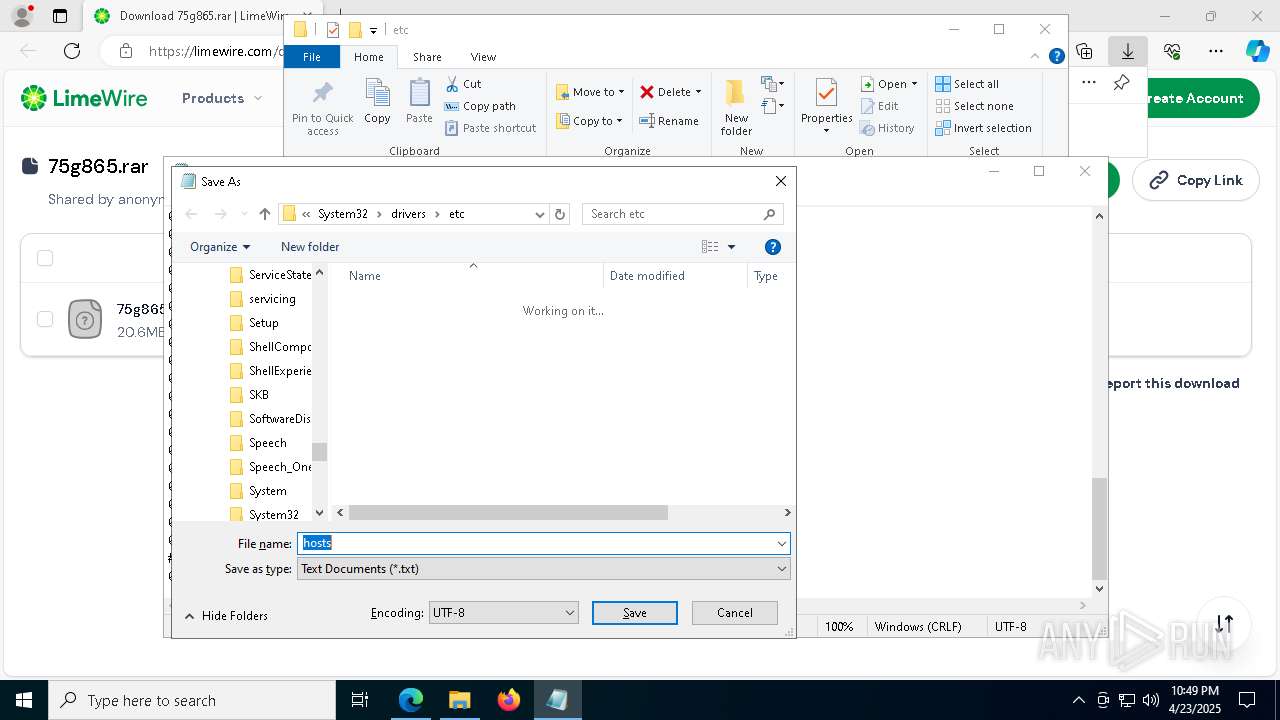
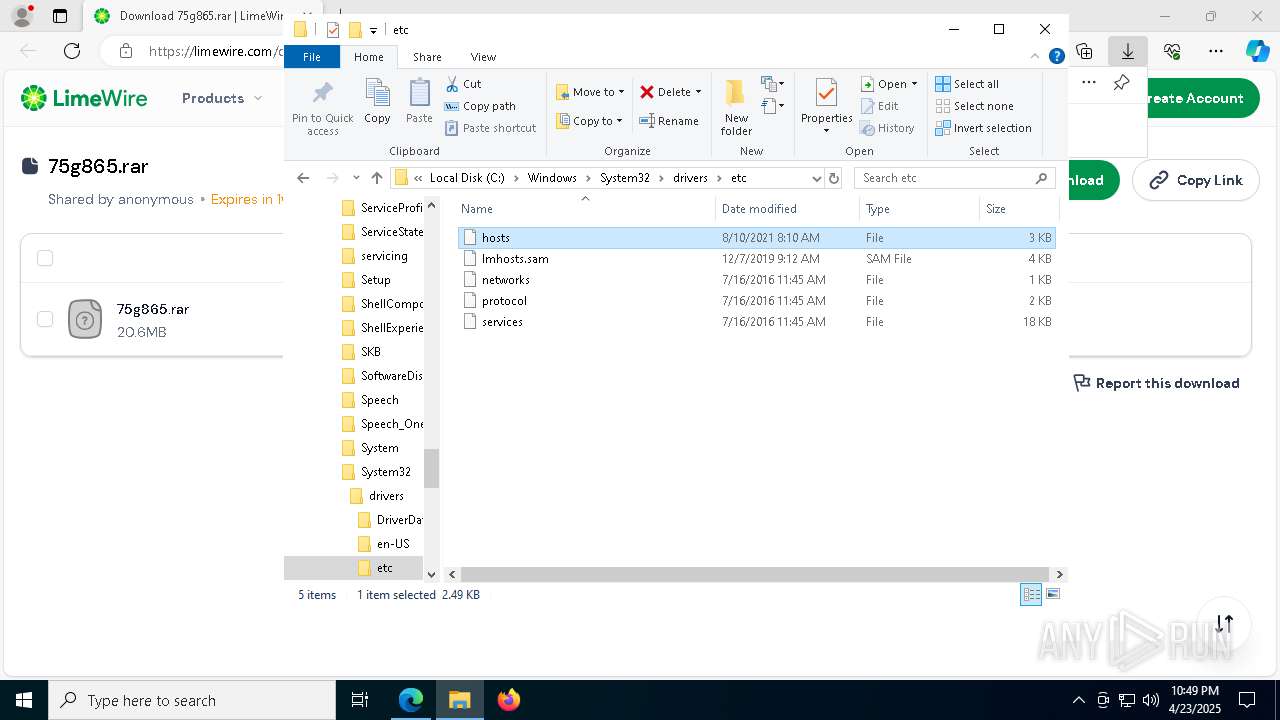
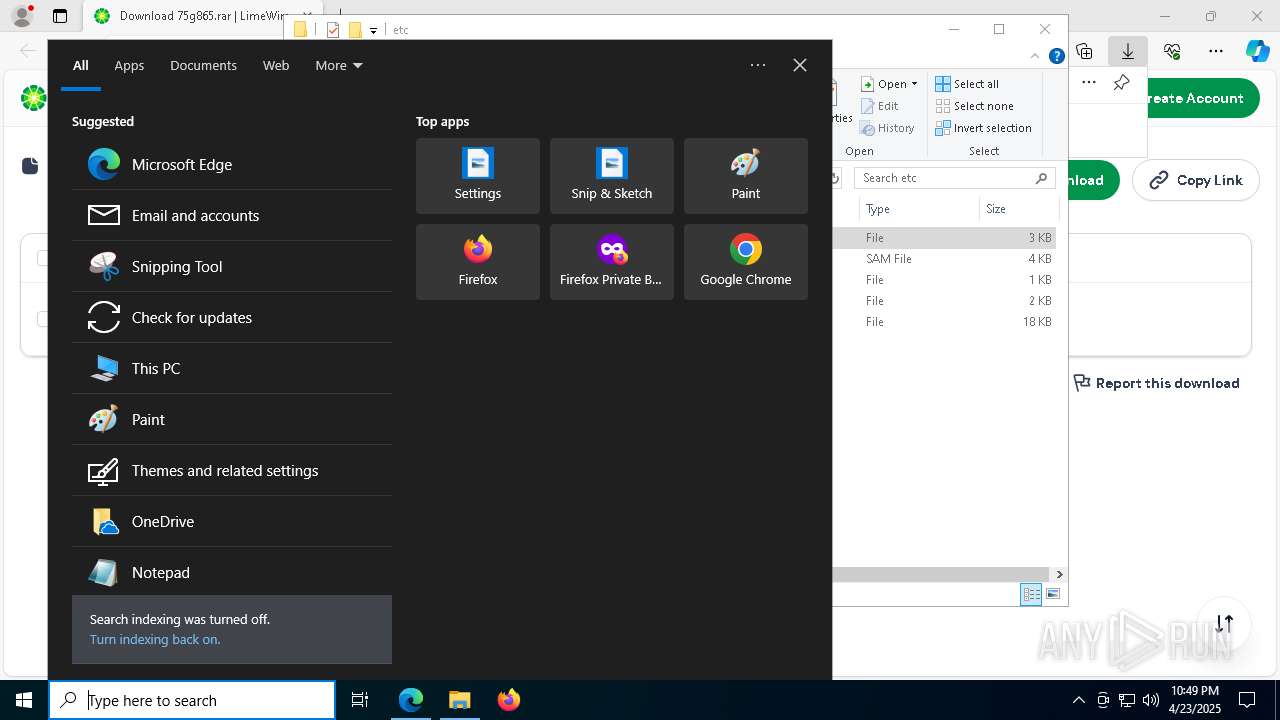
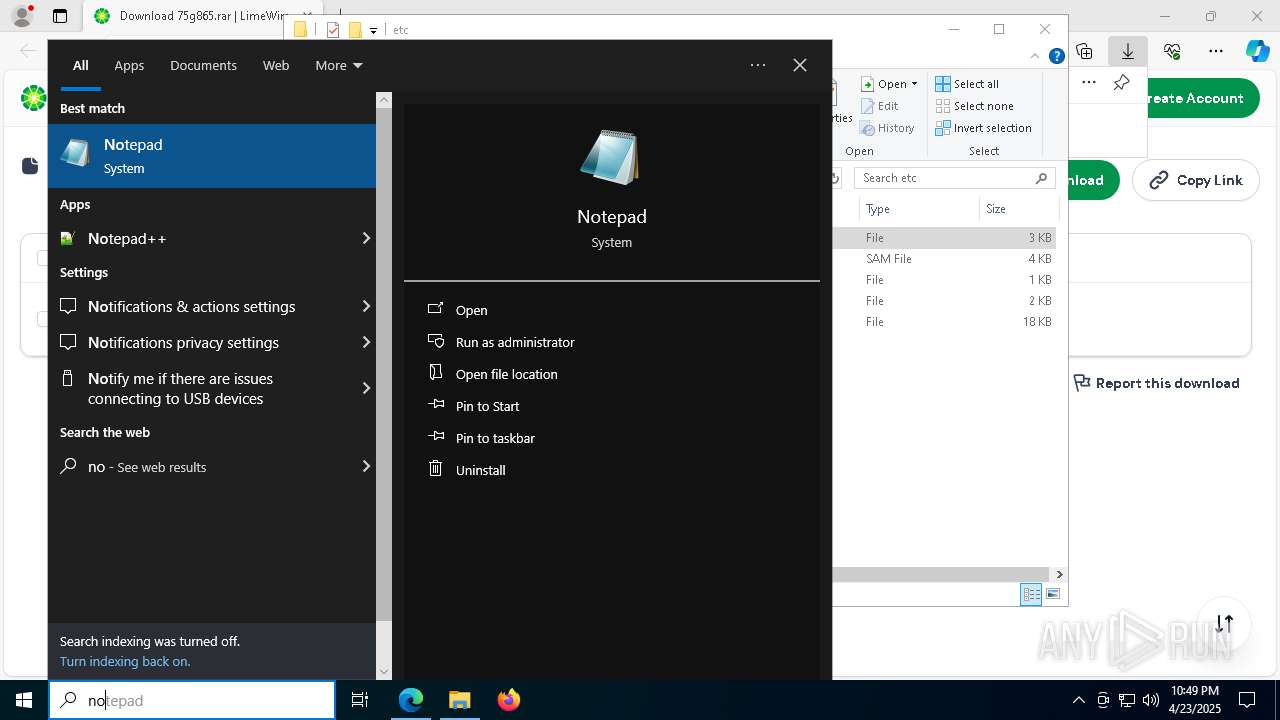
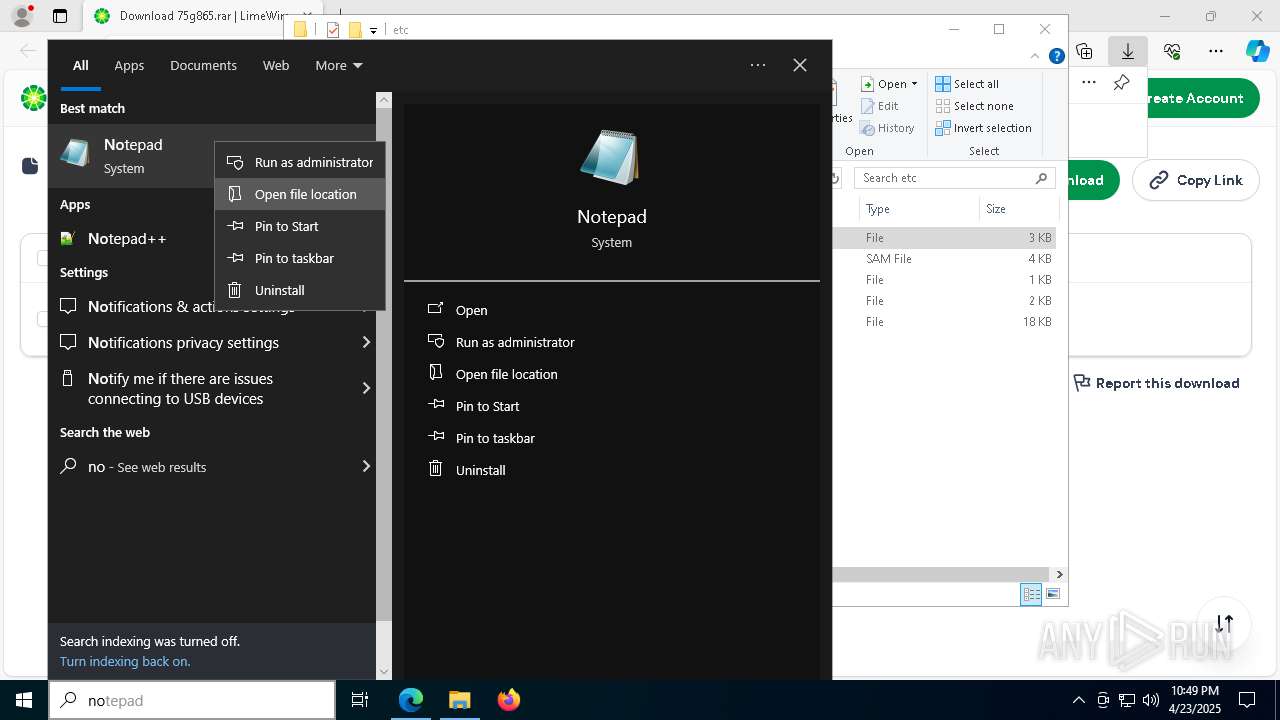
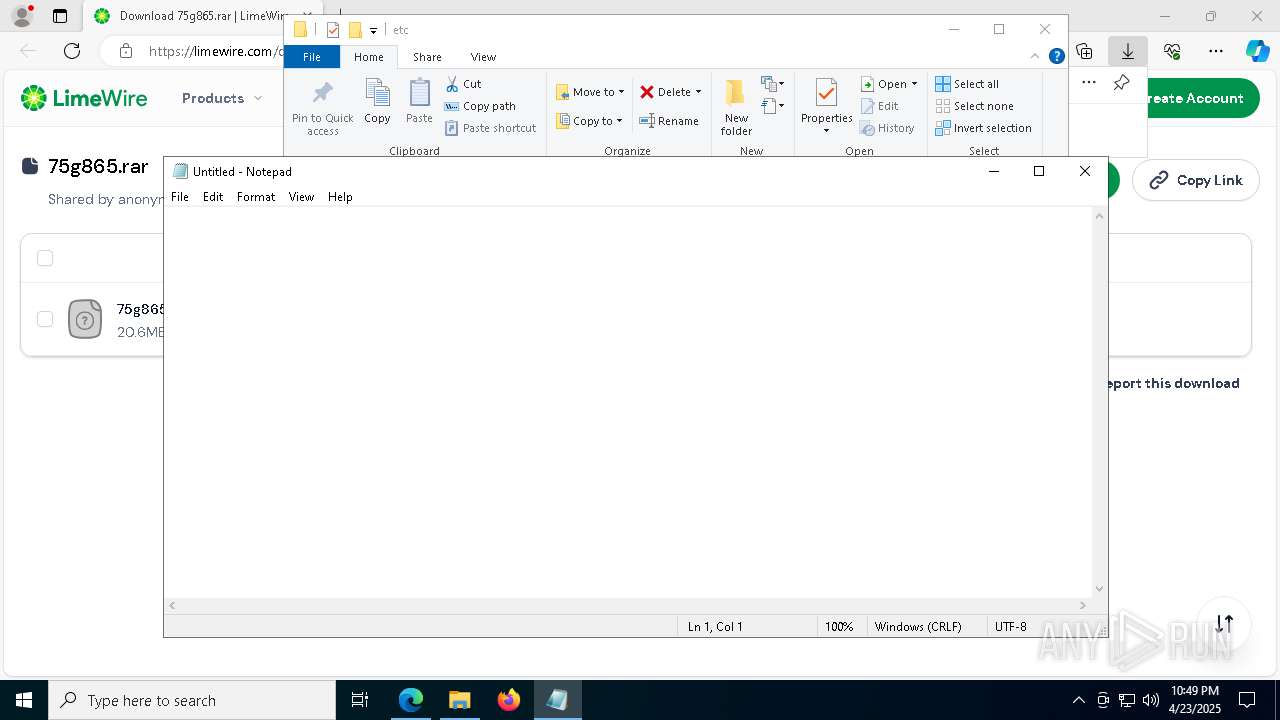
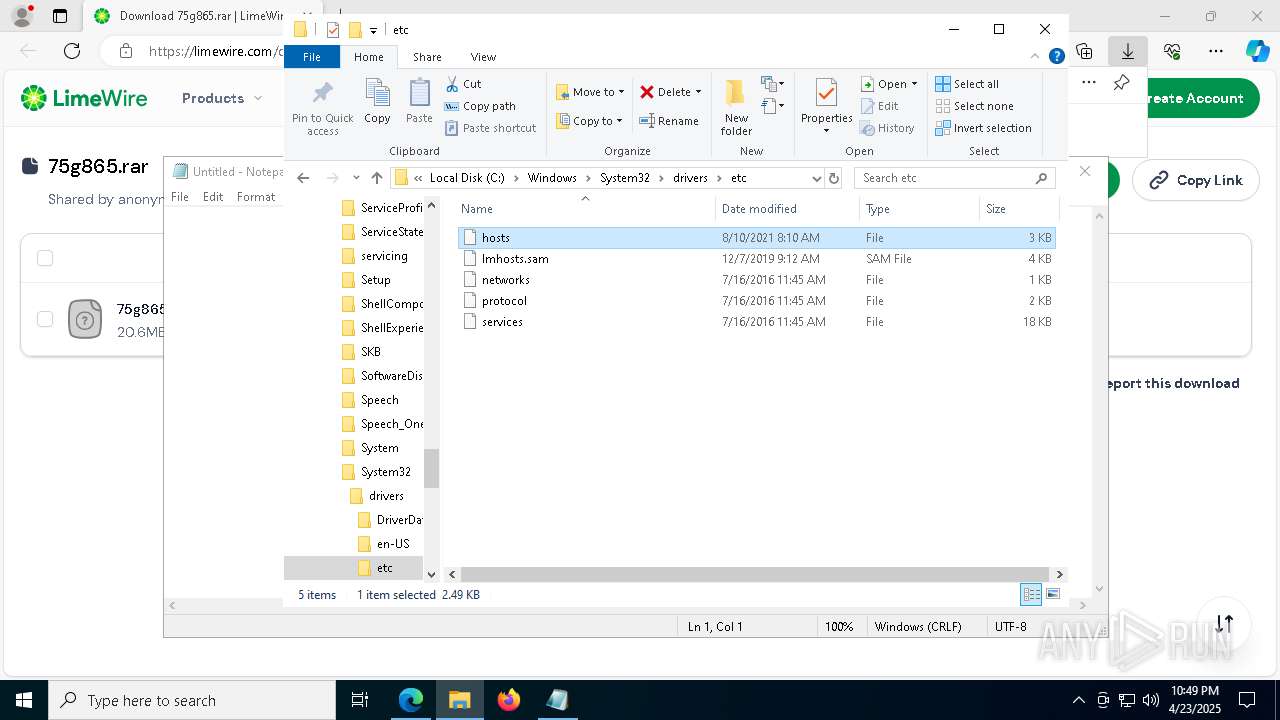
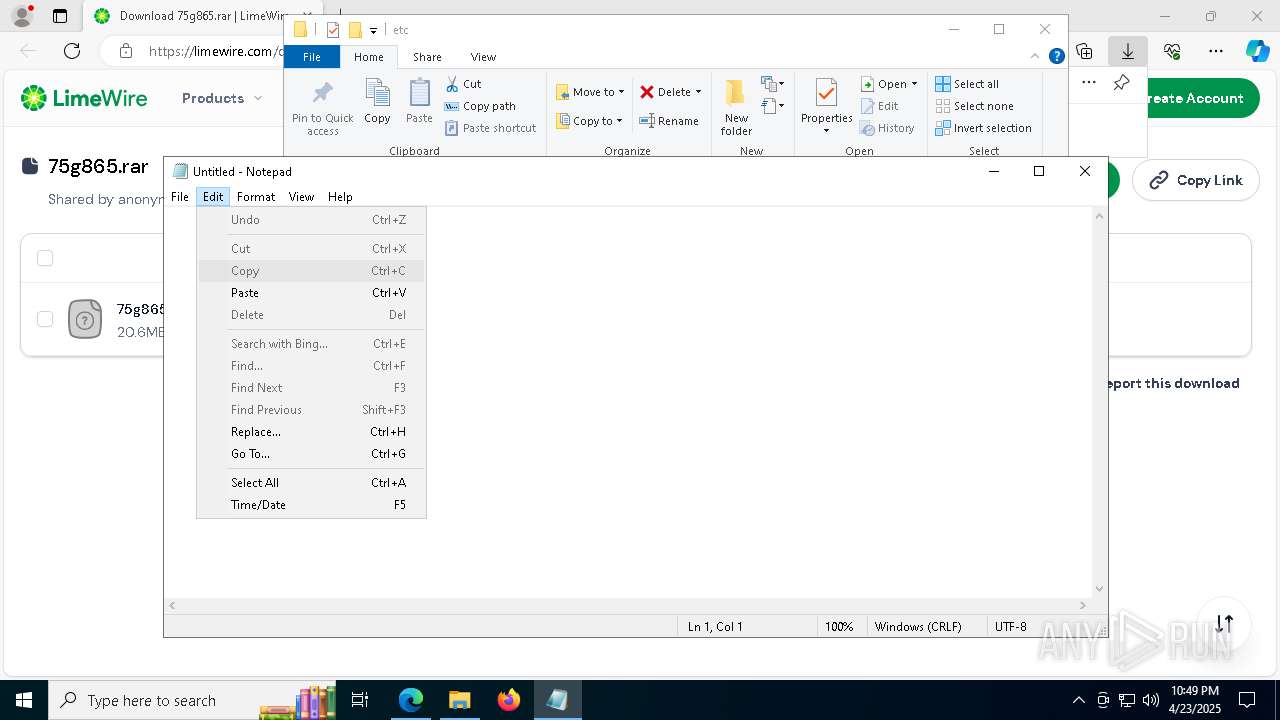
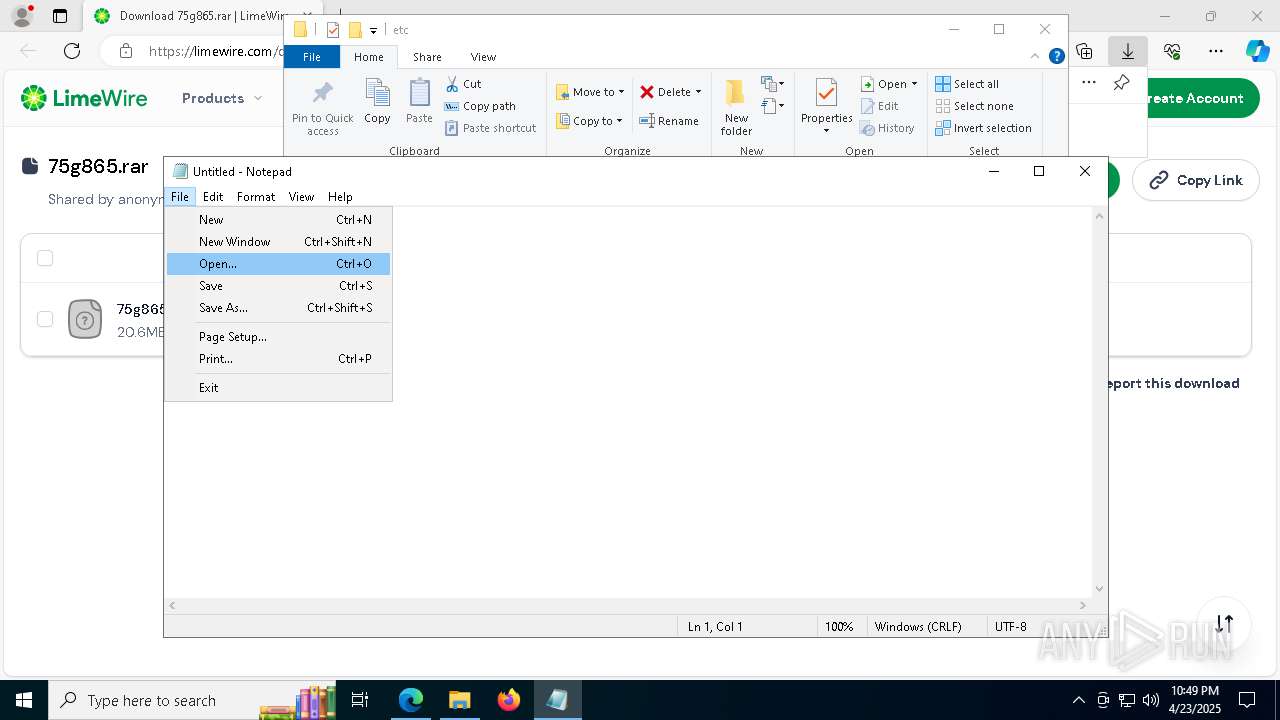
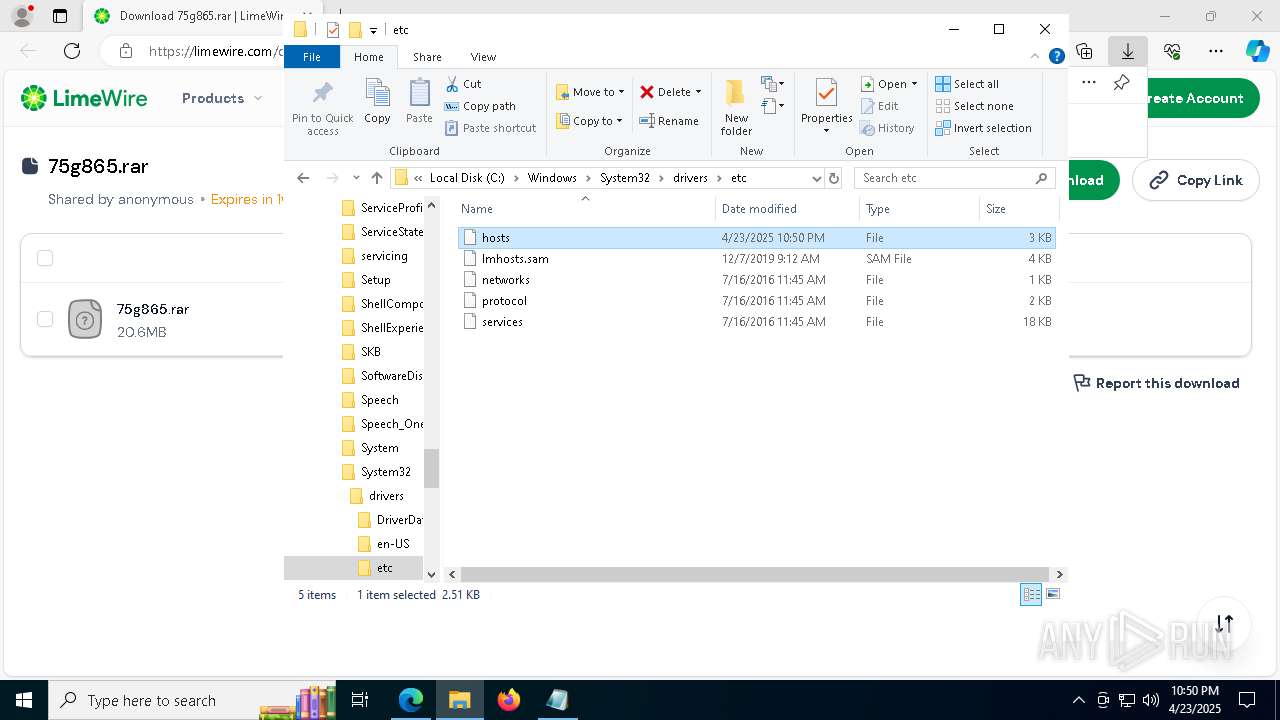
Creates file in the systems drive root
- notepad.exe (PID: 5188)
- notepad.exe (PID: 812)
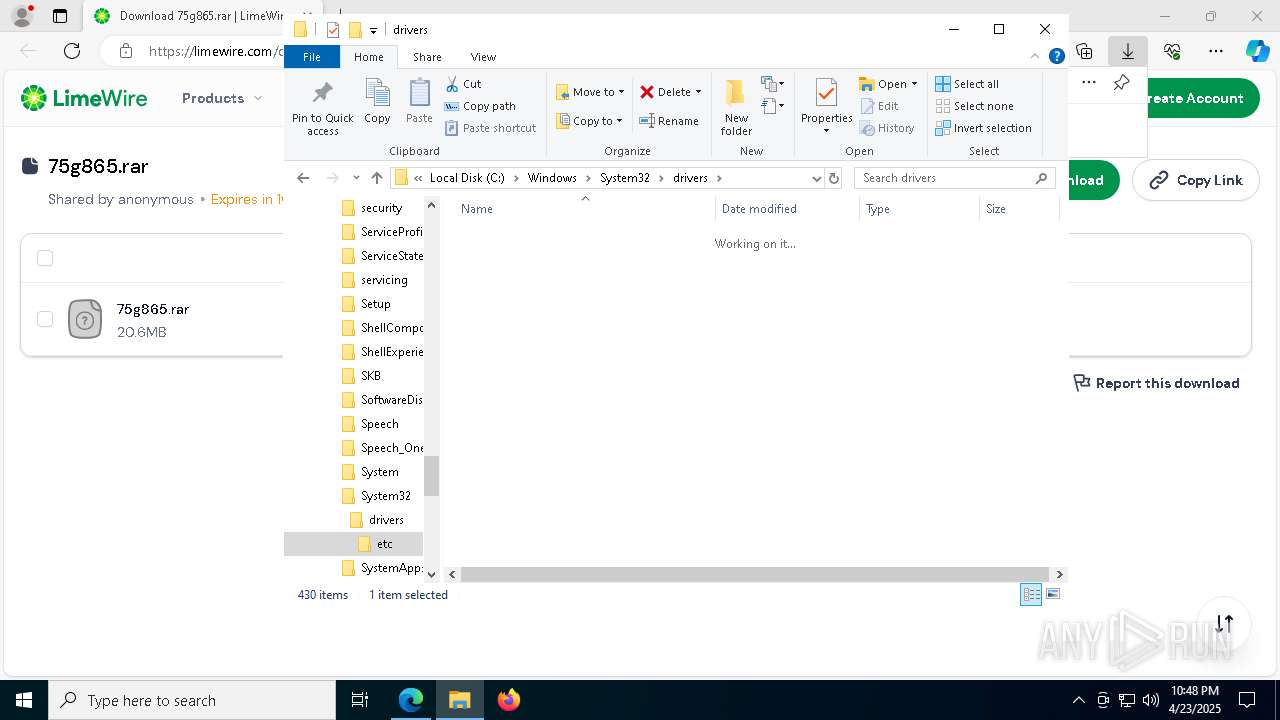
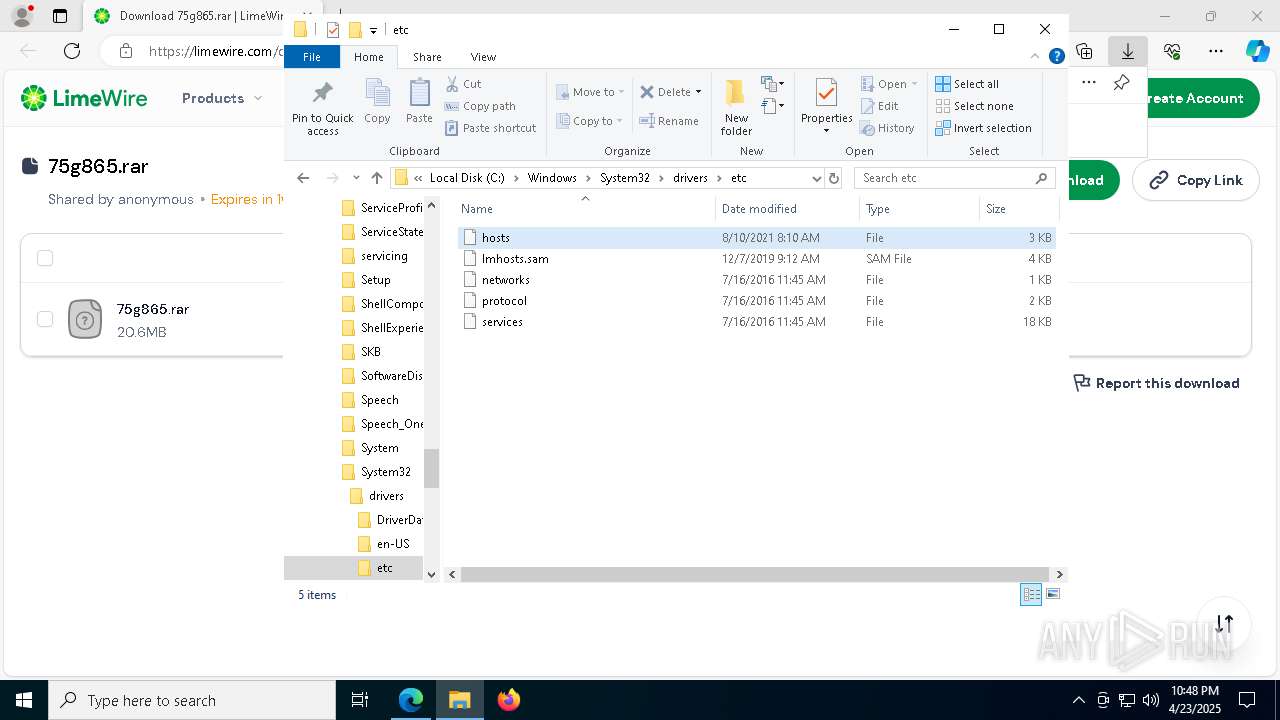
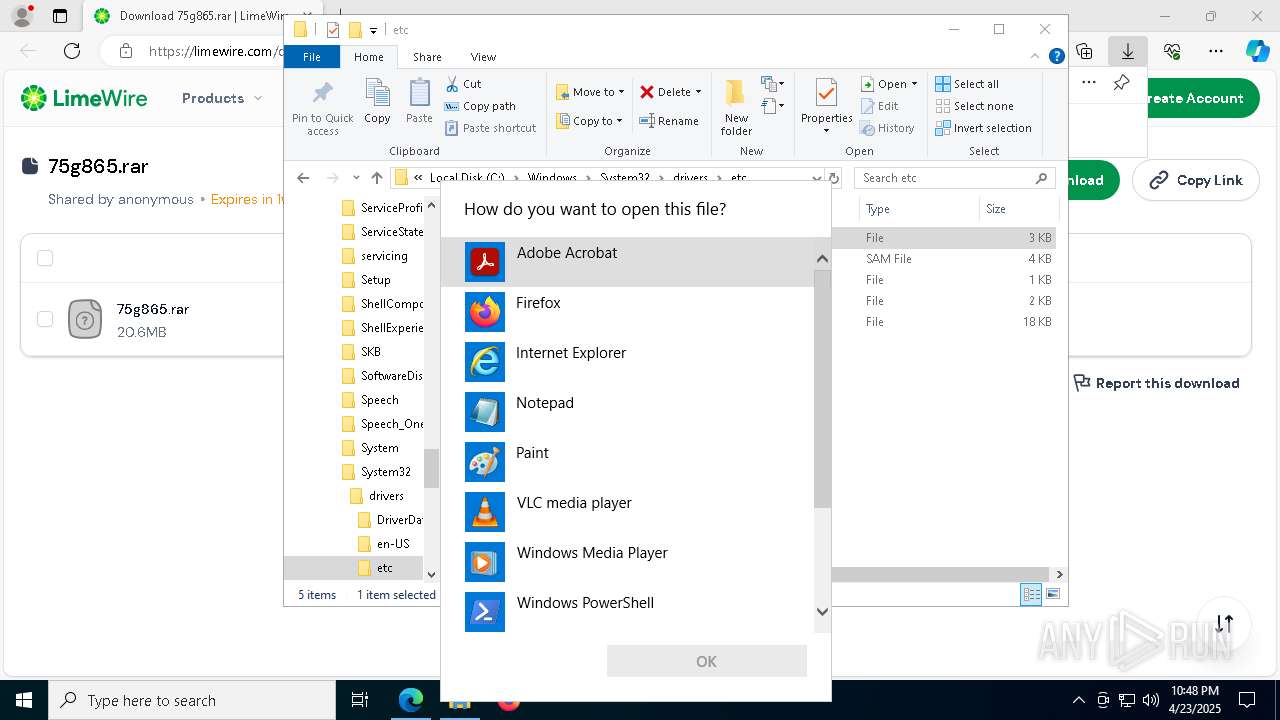
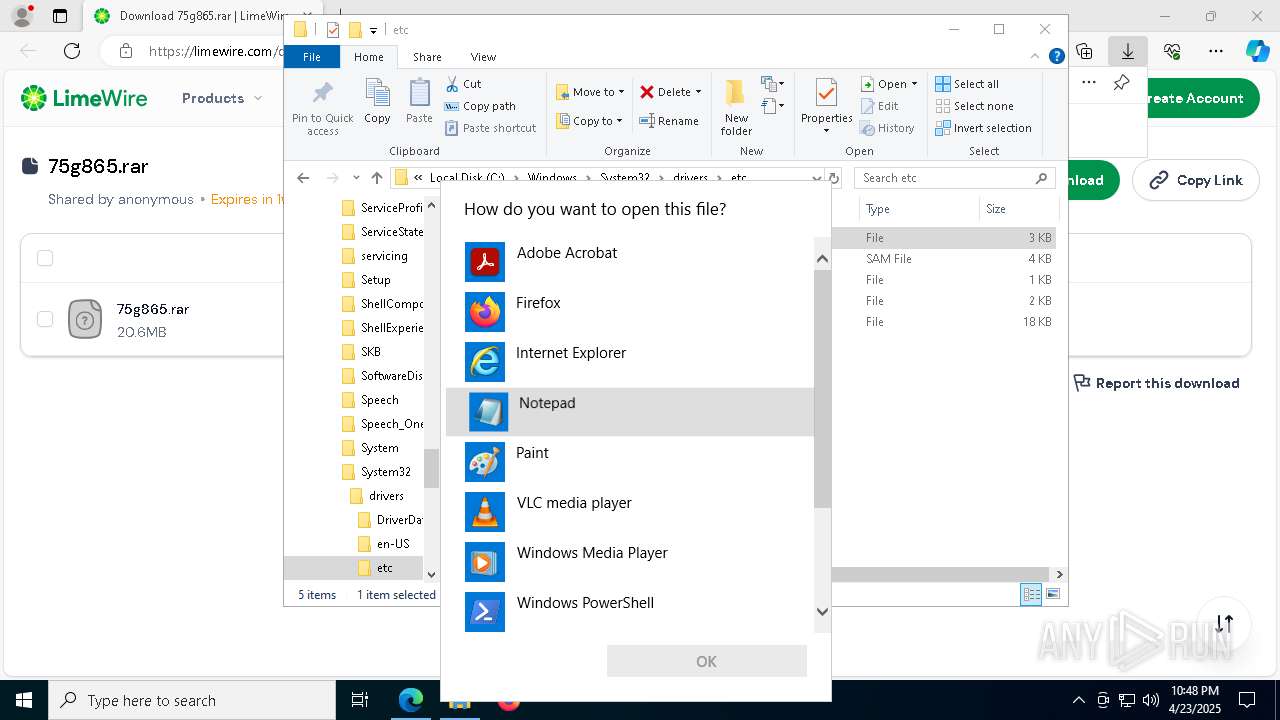
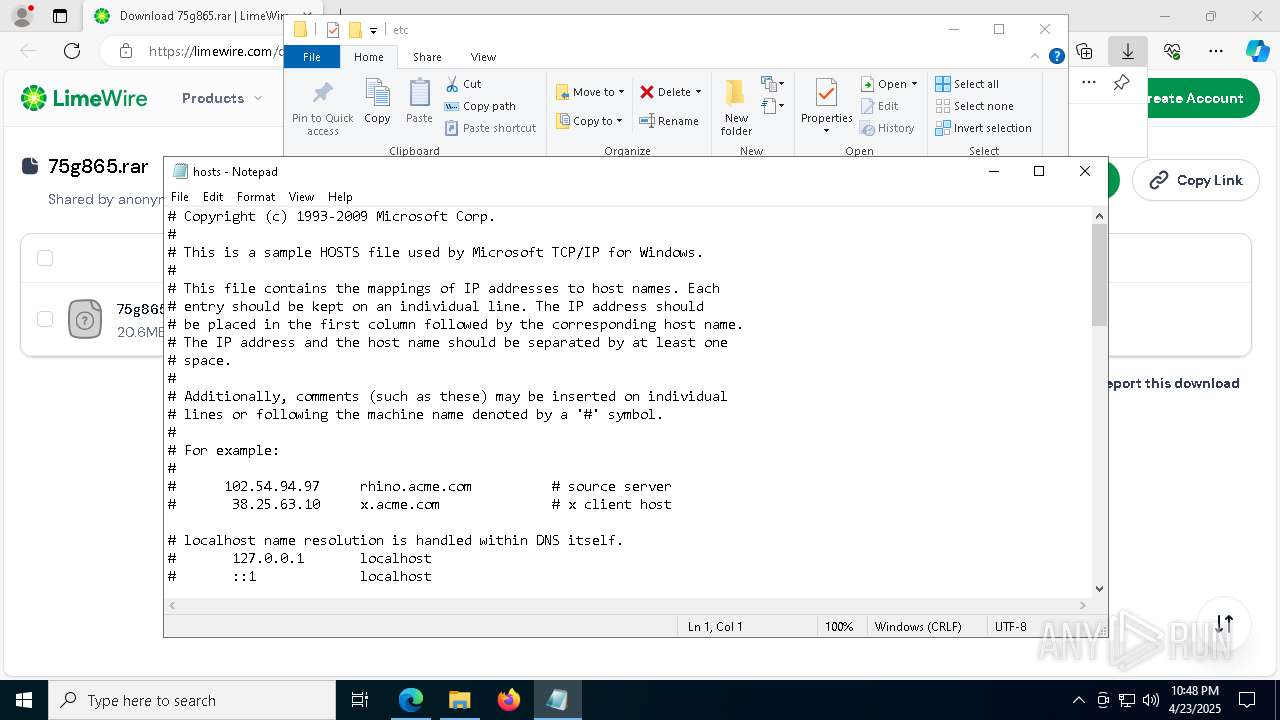
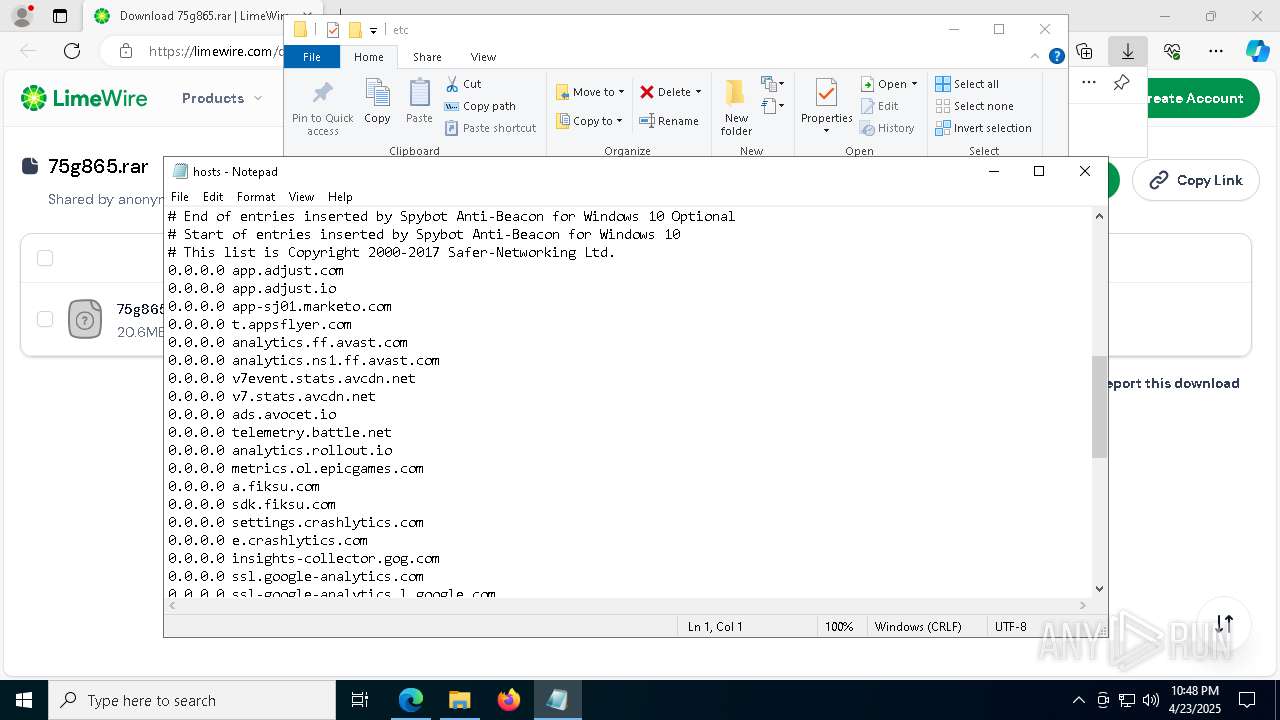
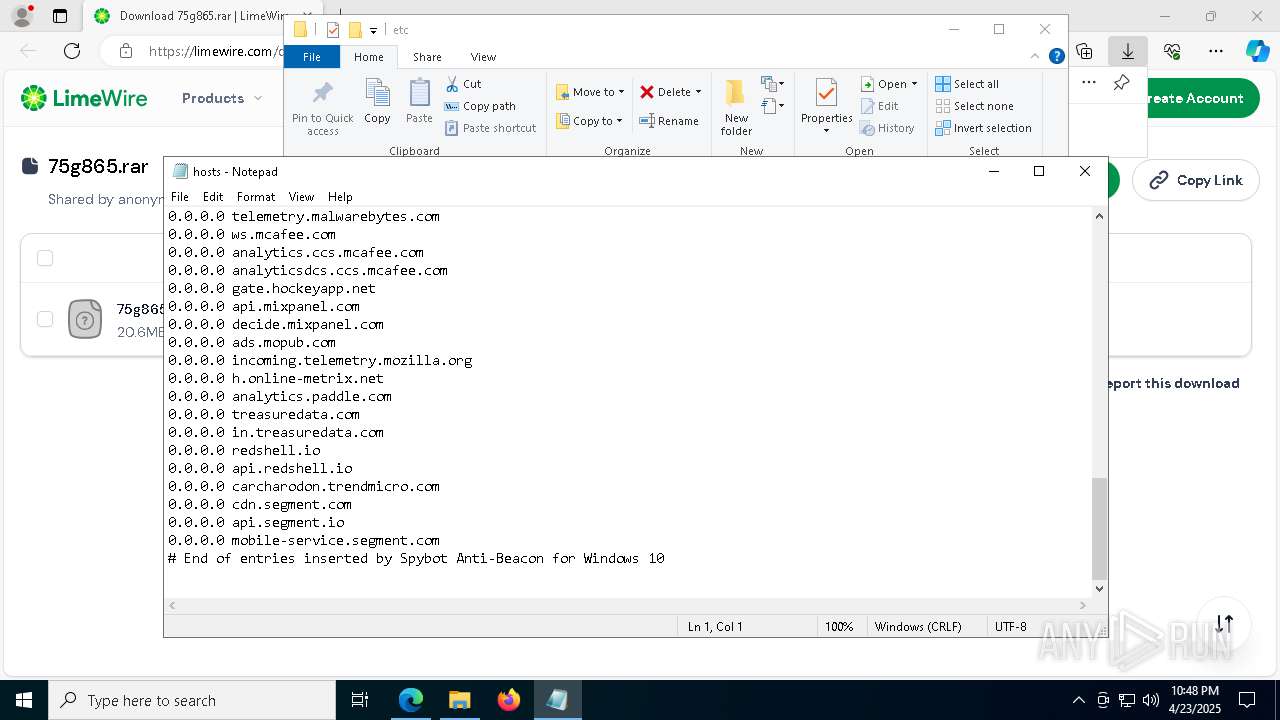
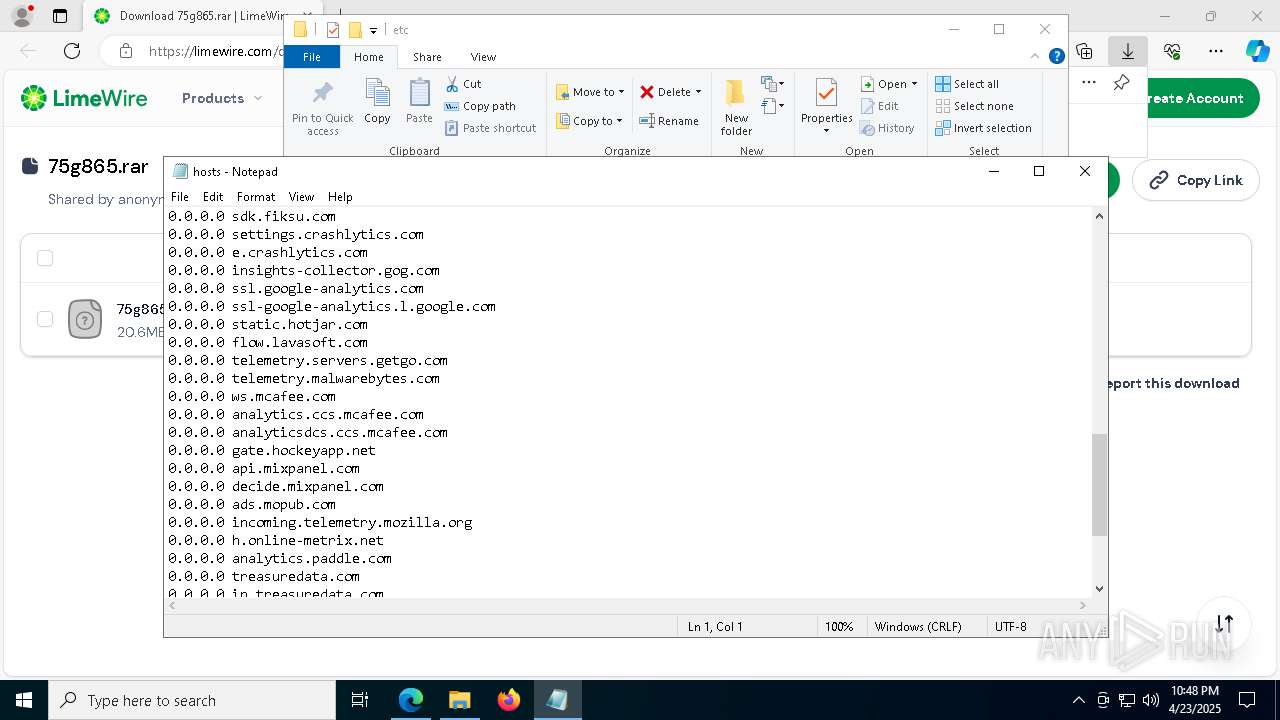
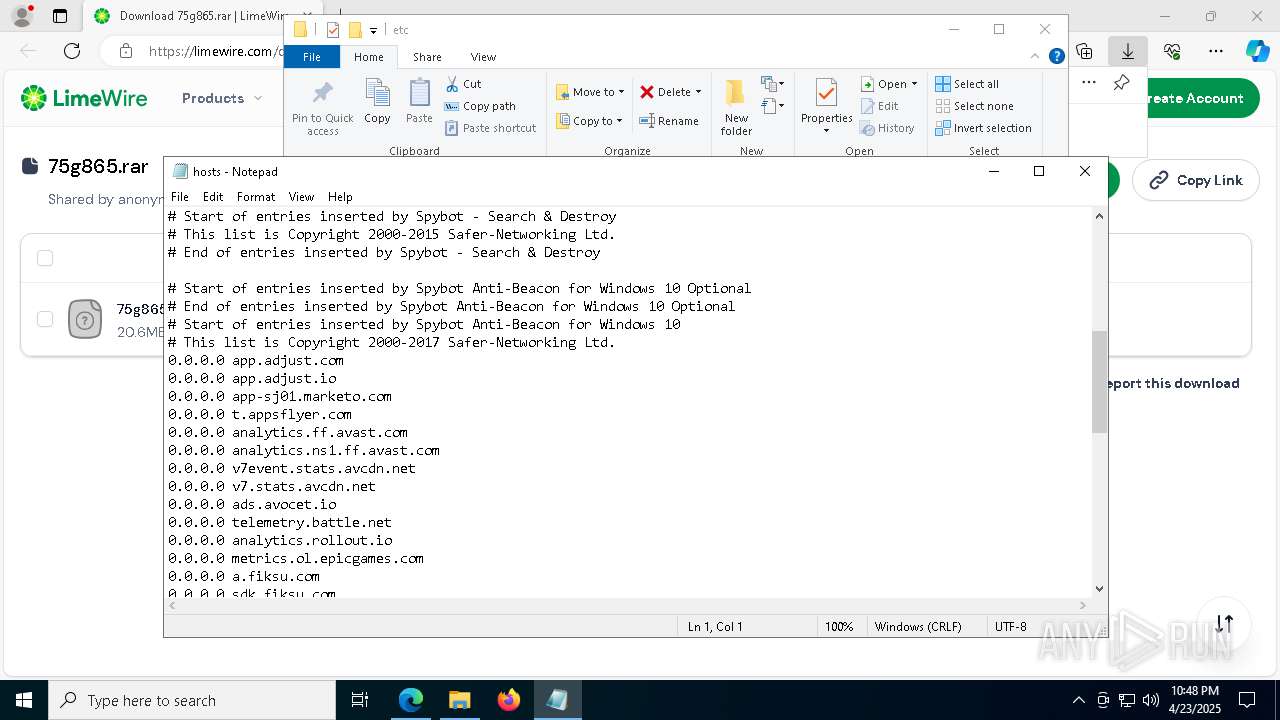
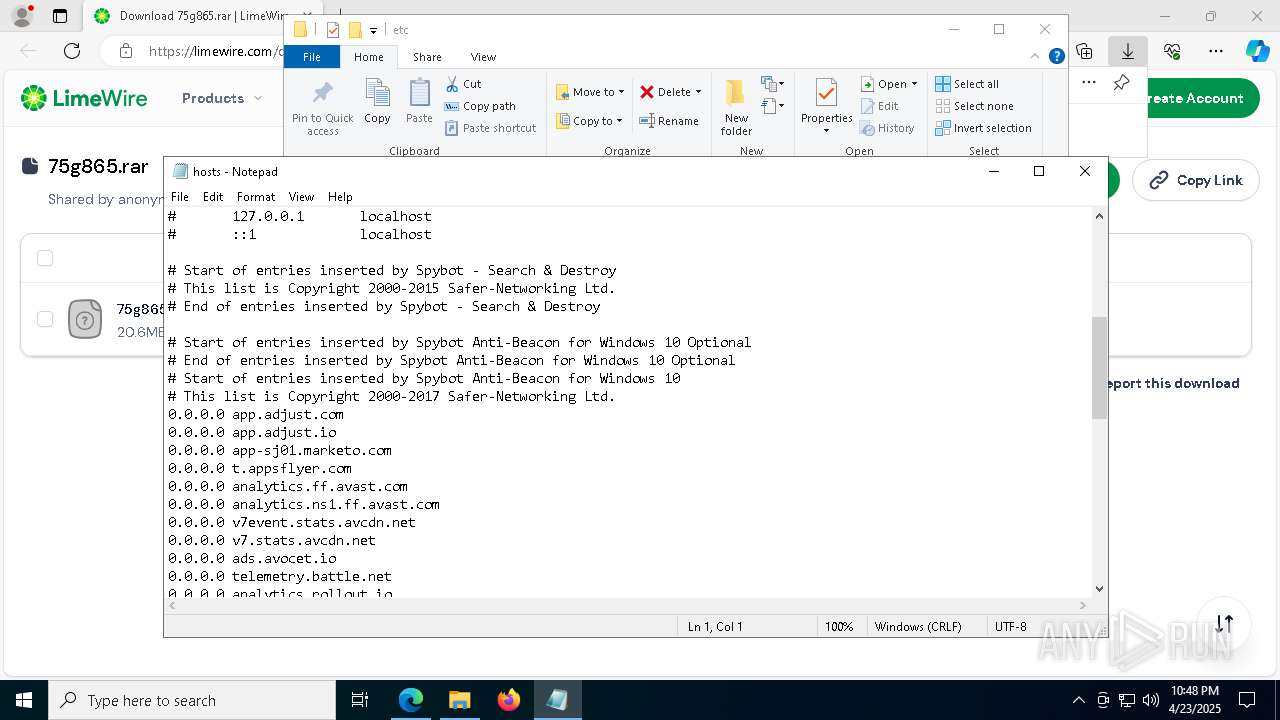
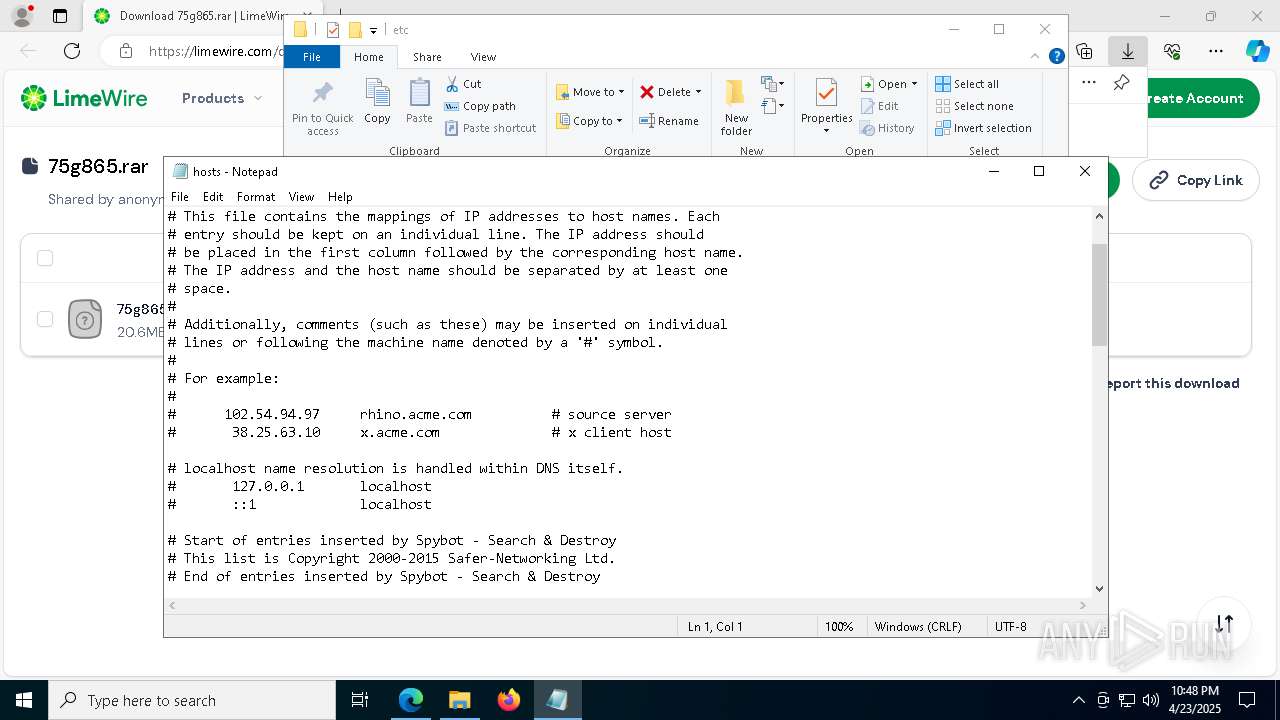
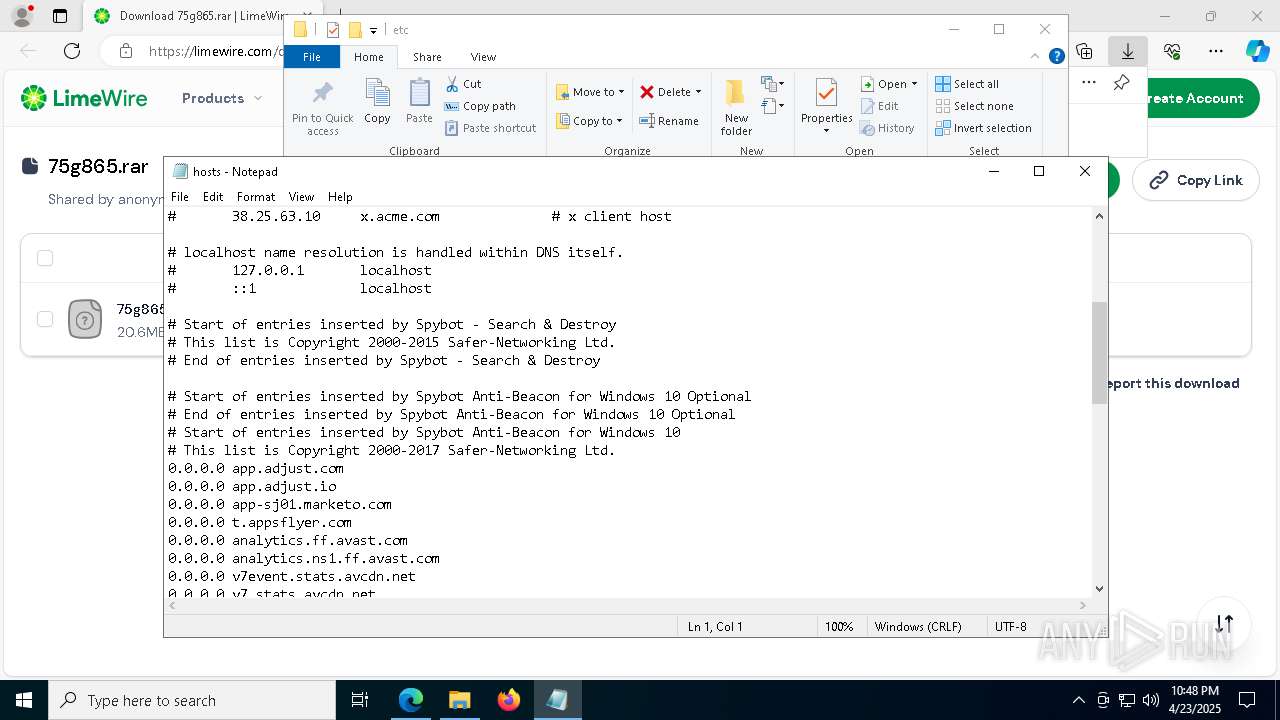
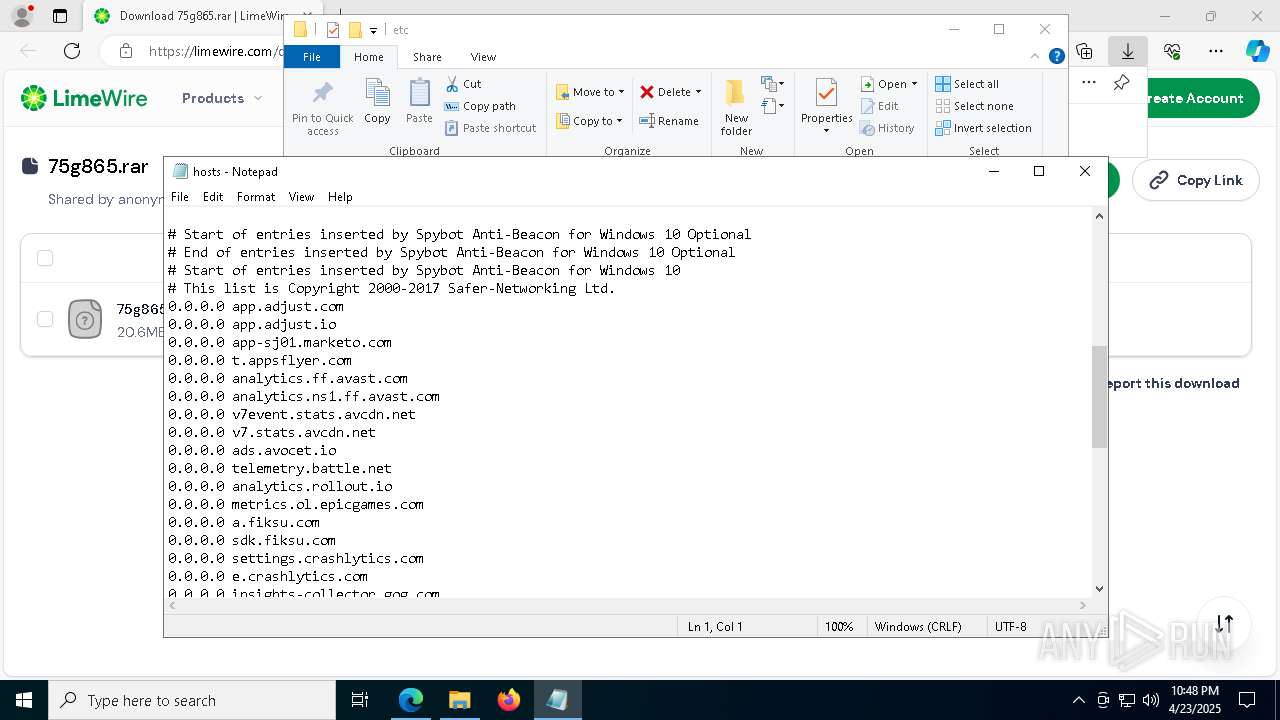
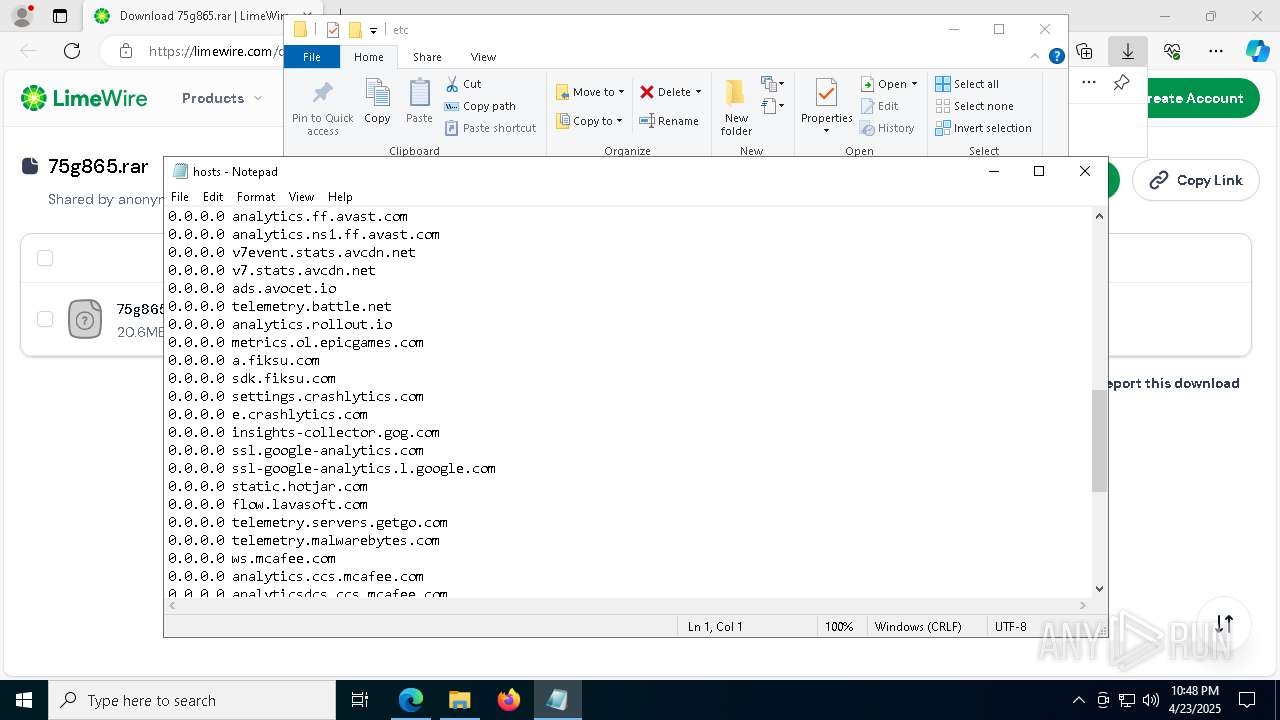
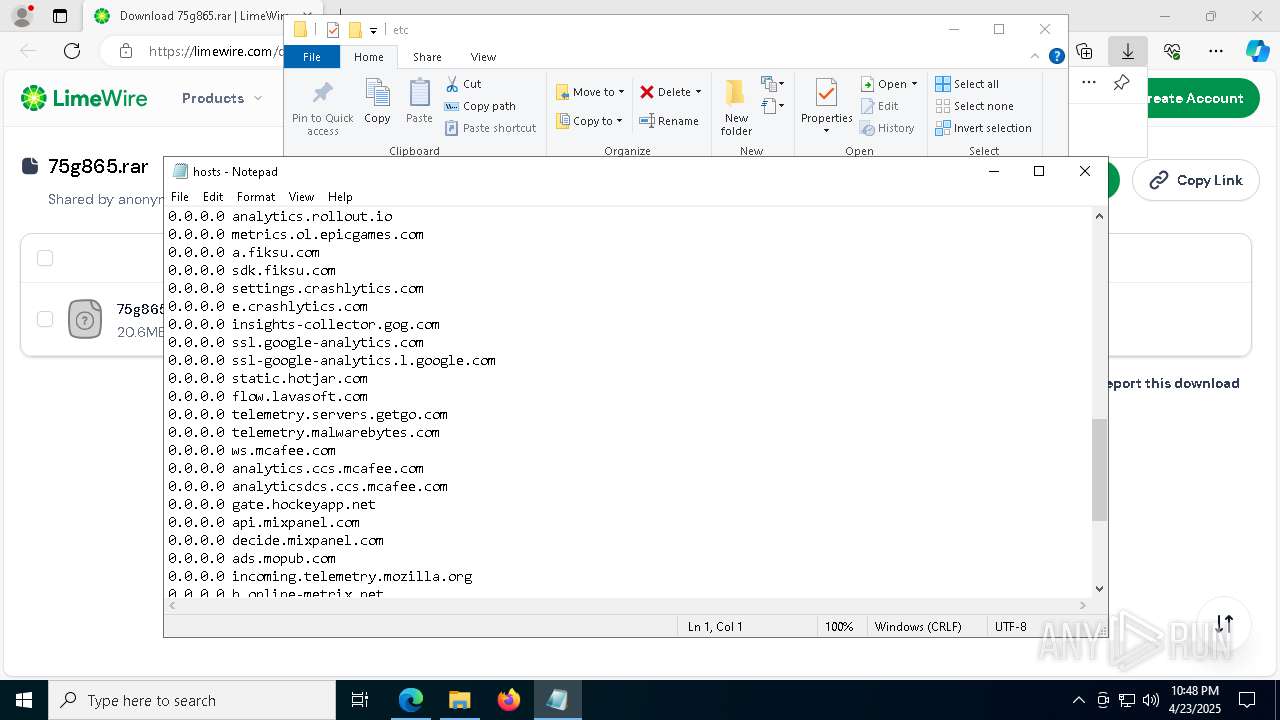
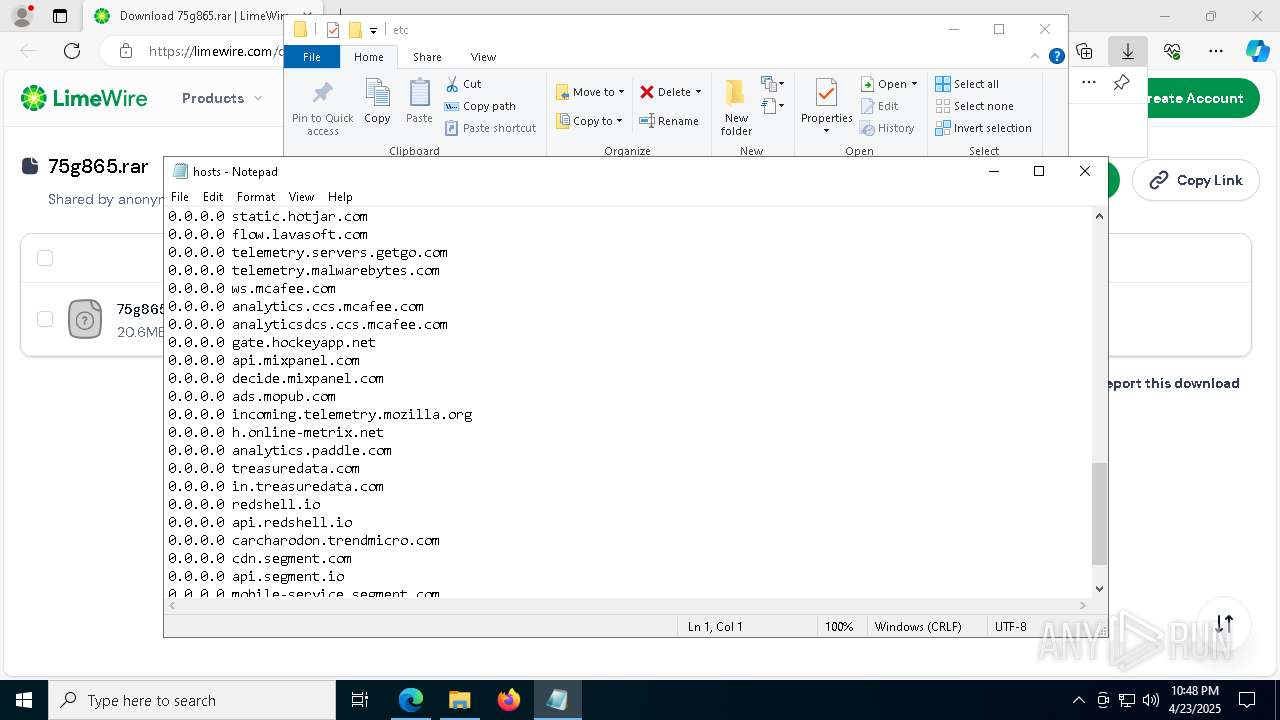
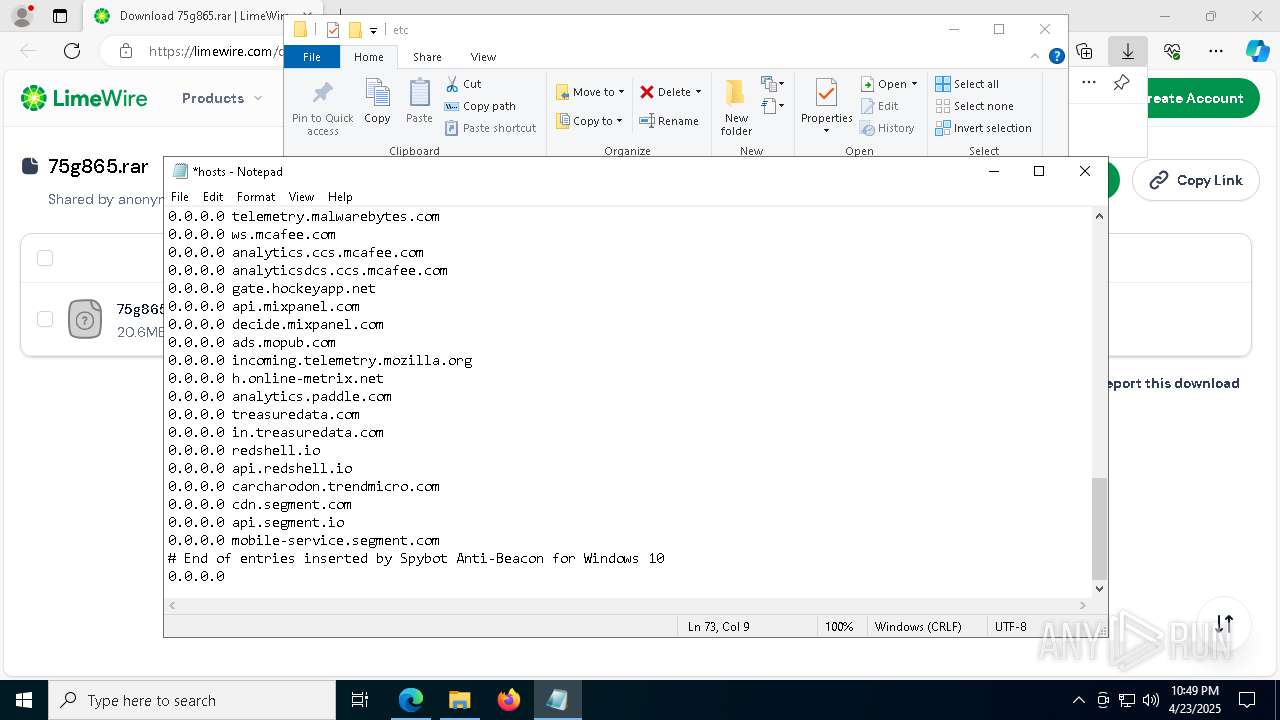
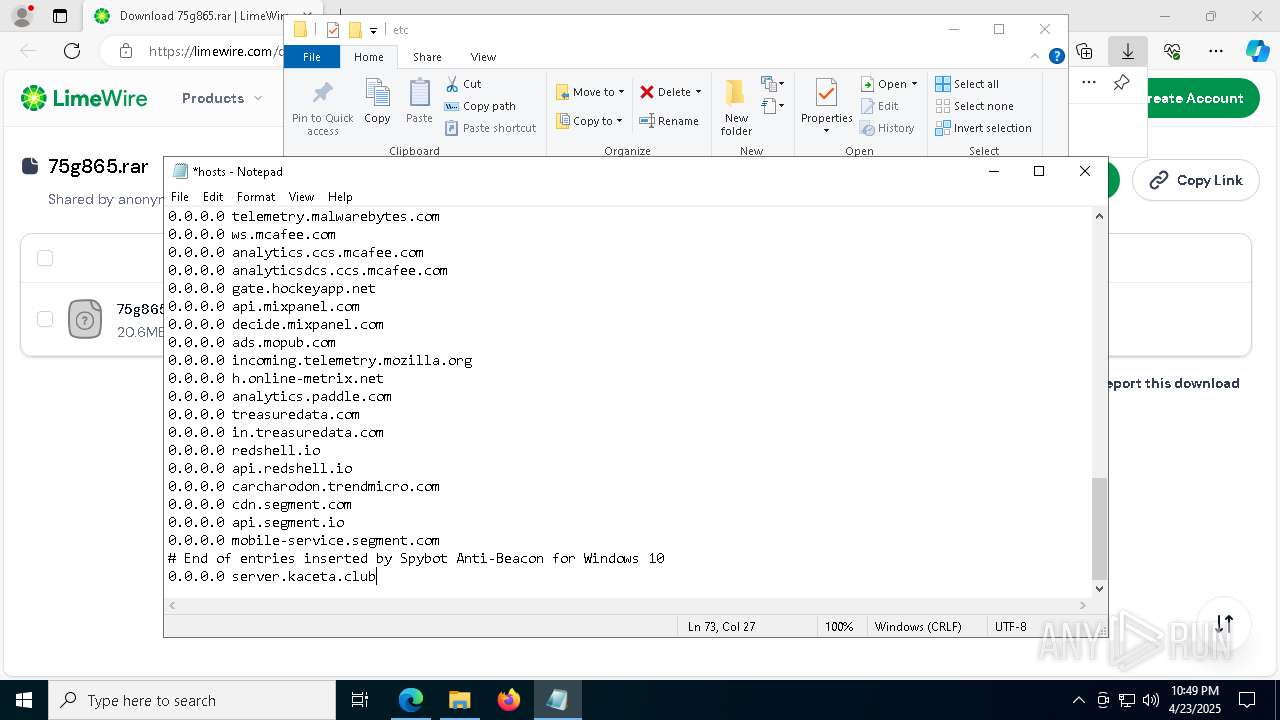
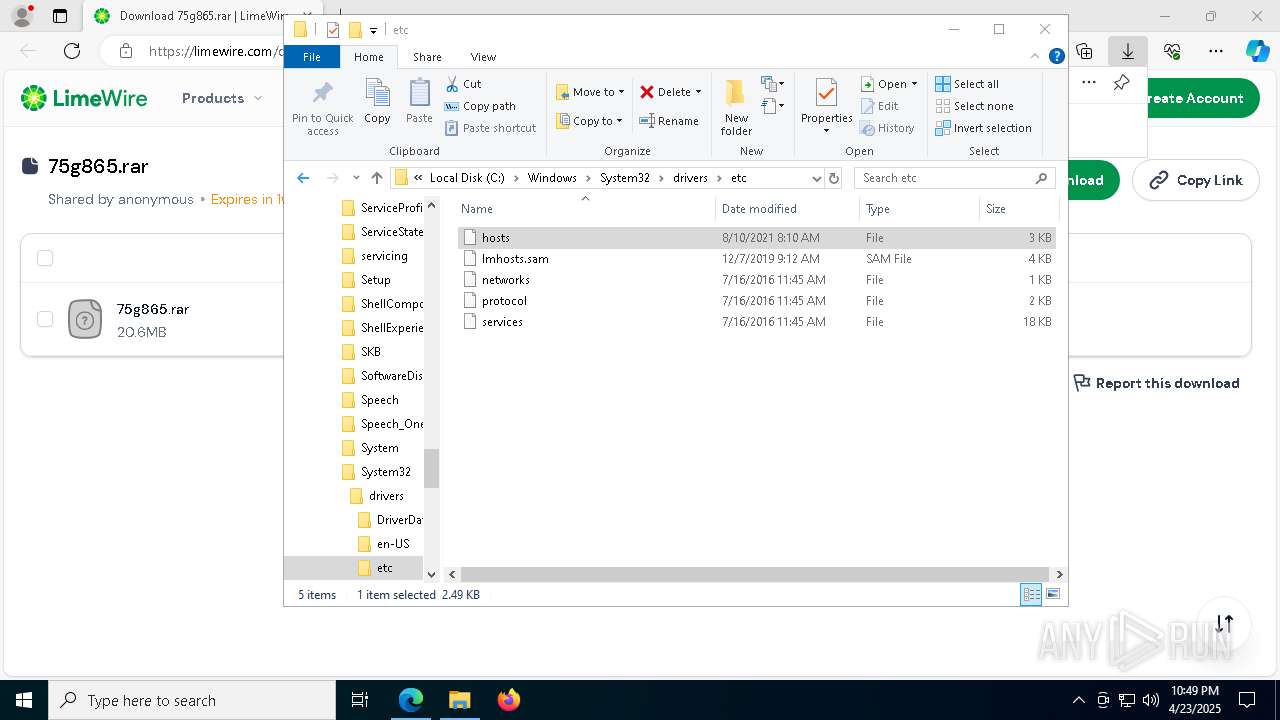
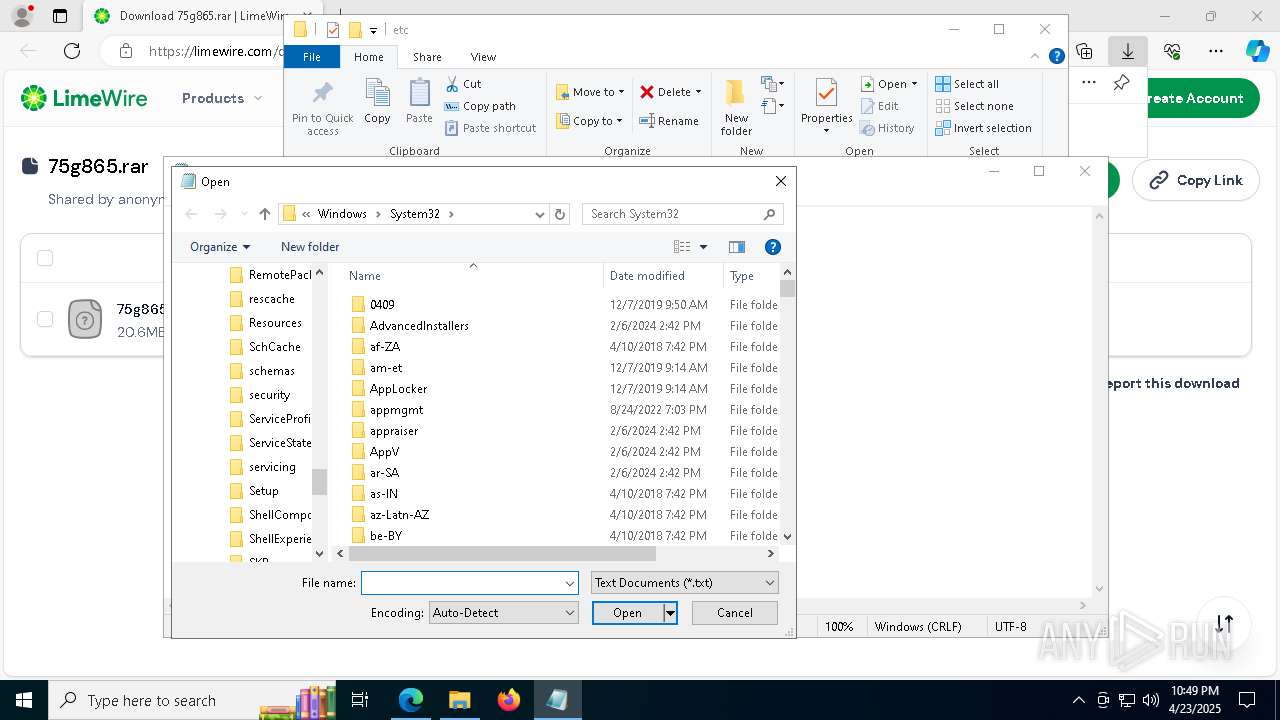
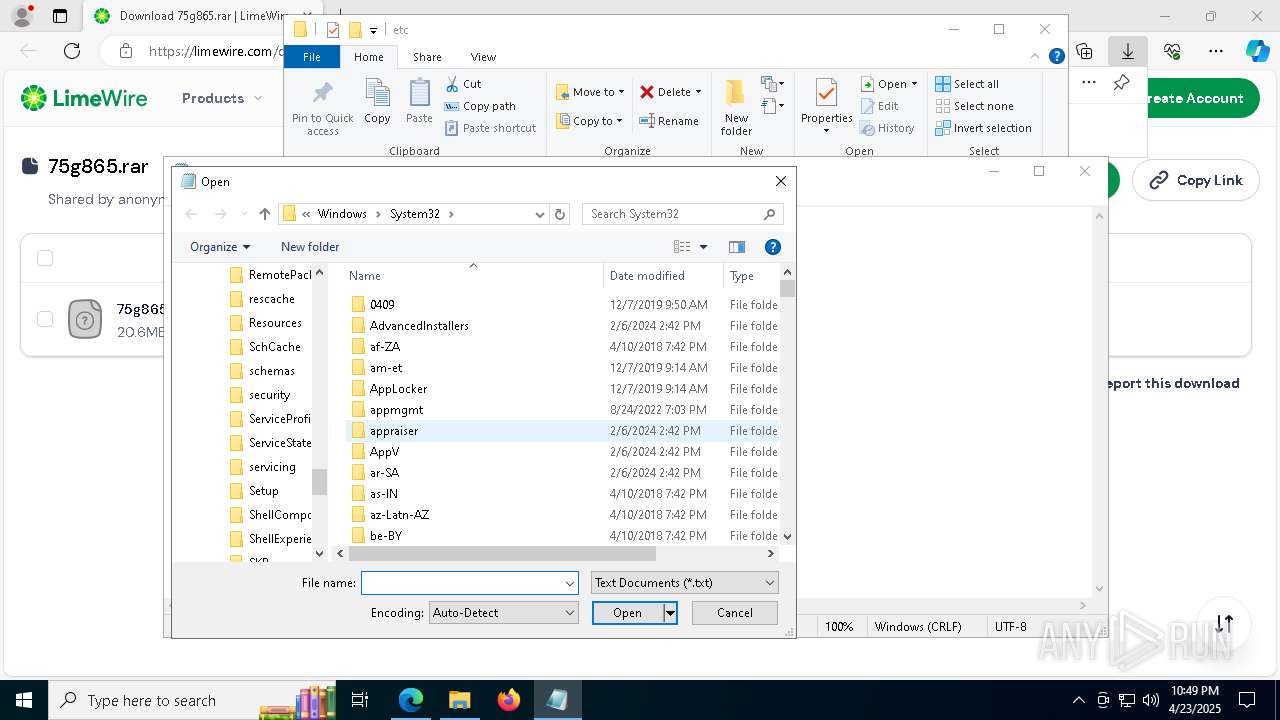
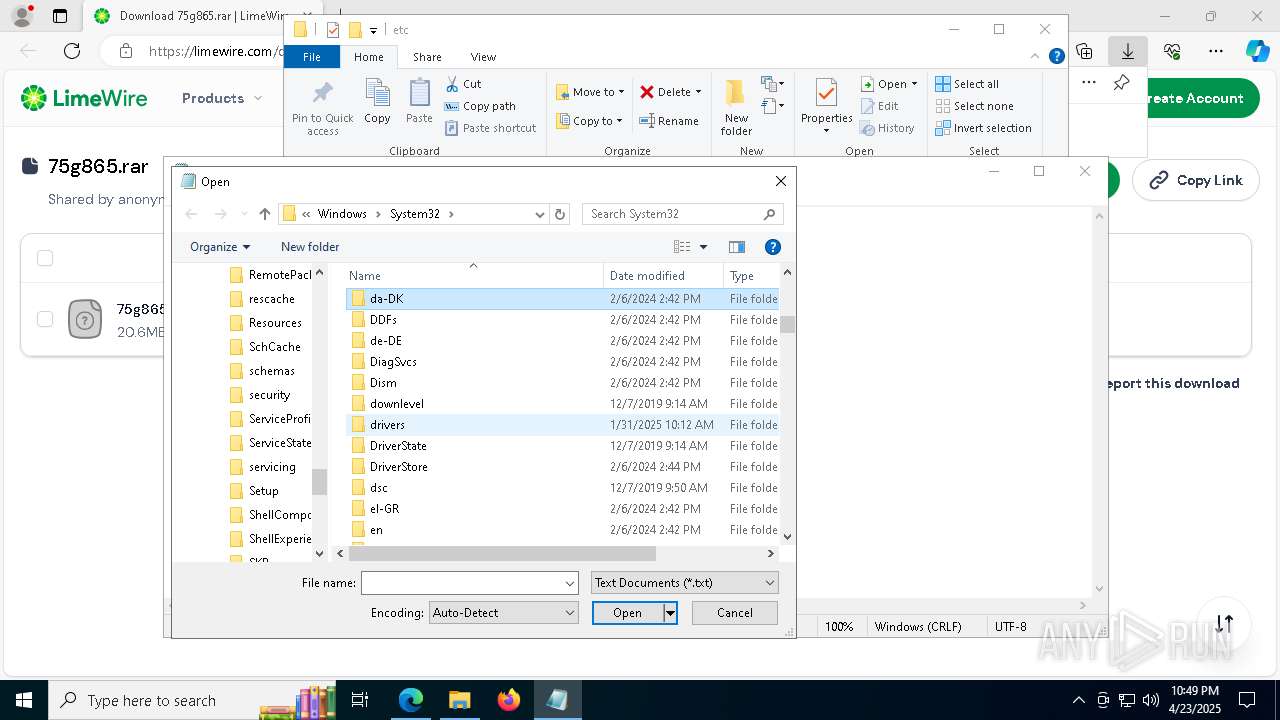
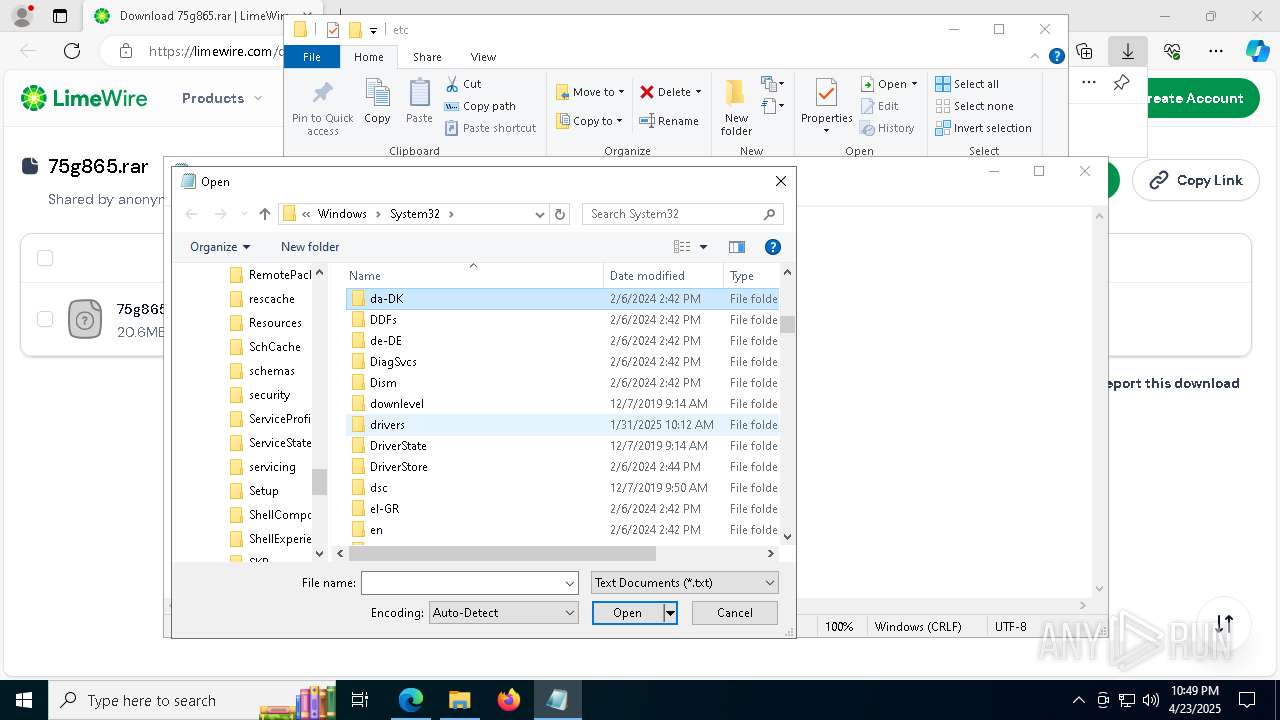
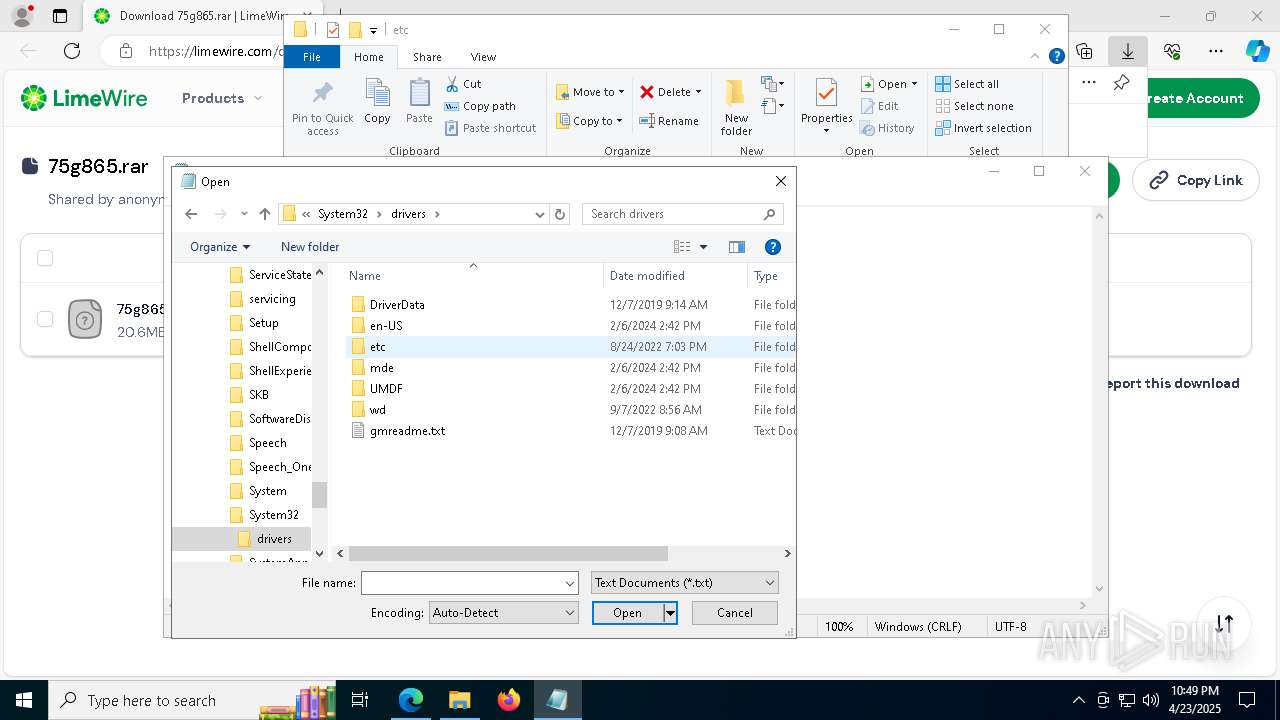
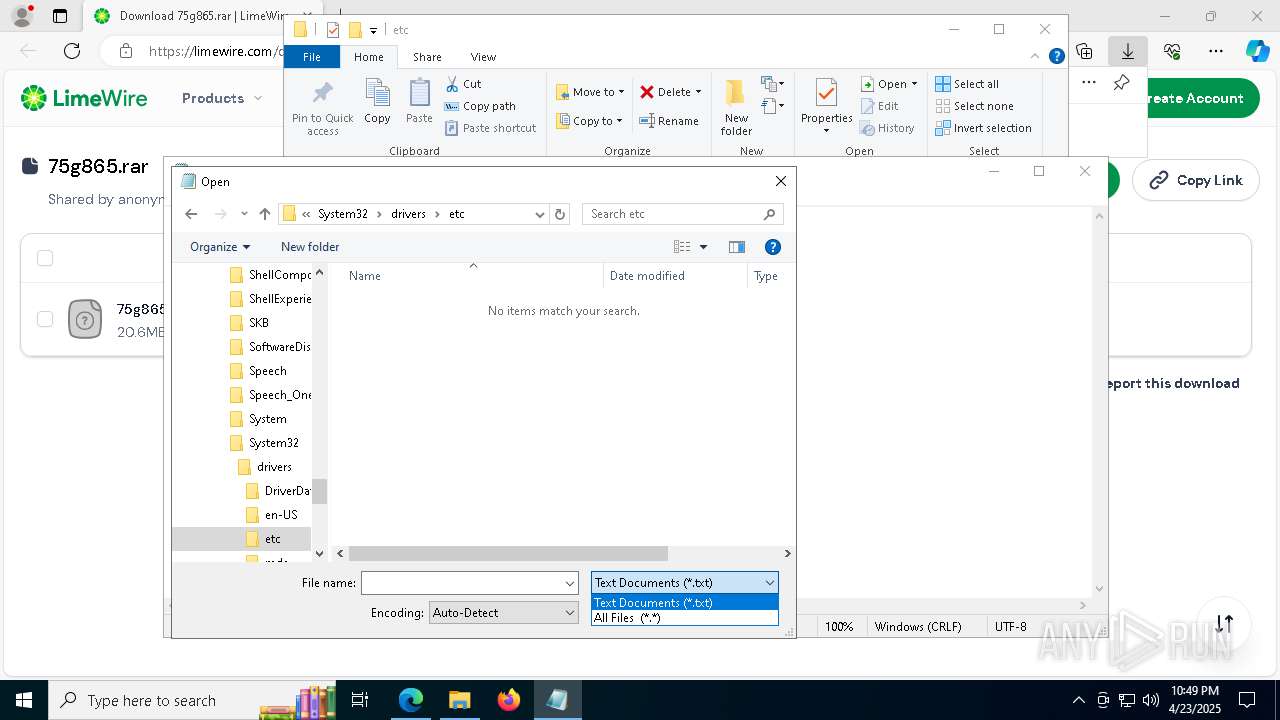
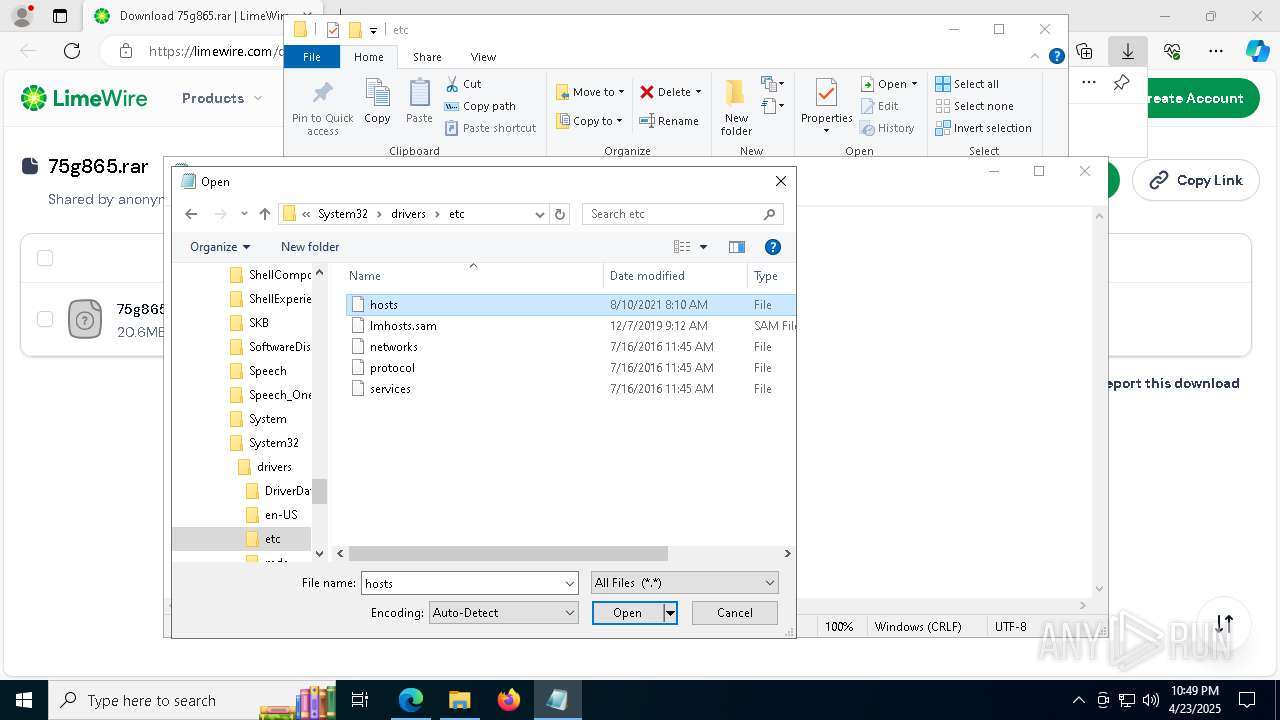
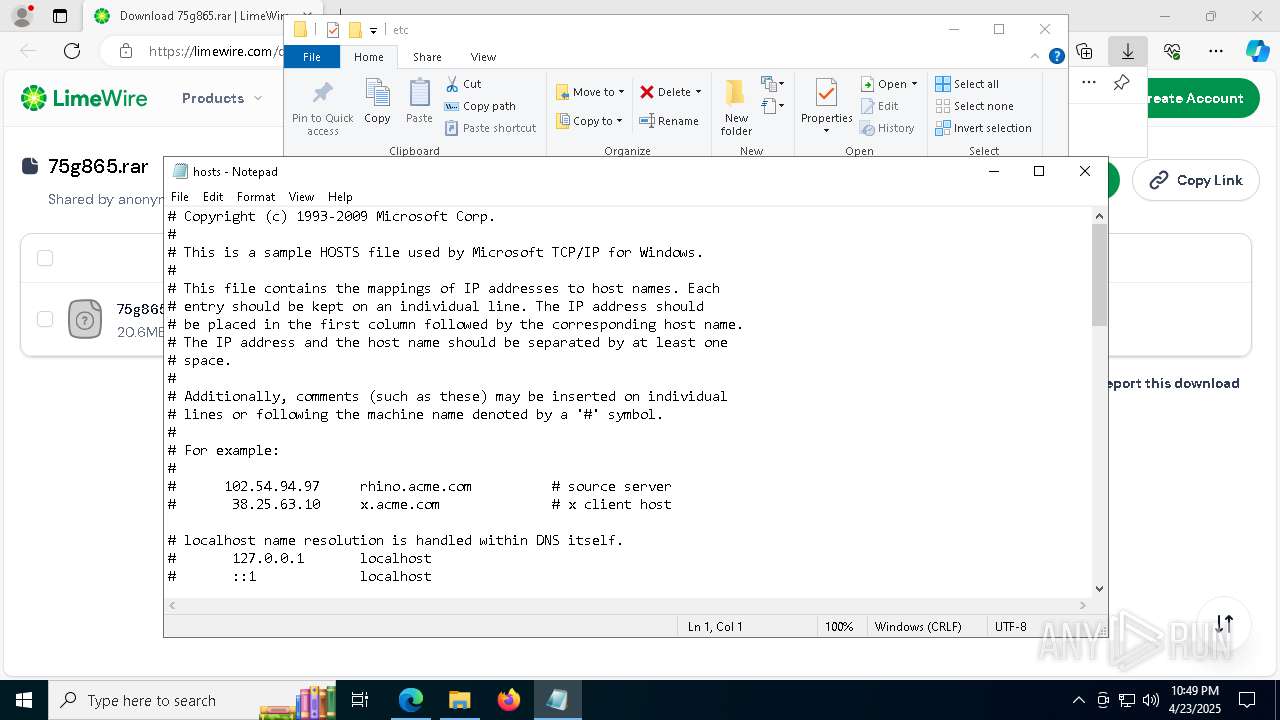
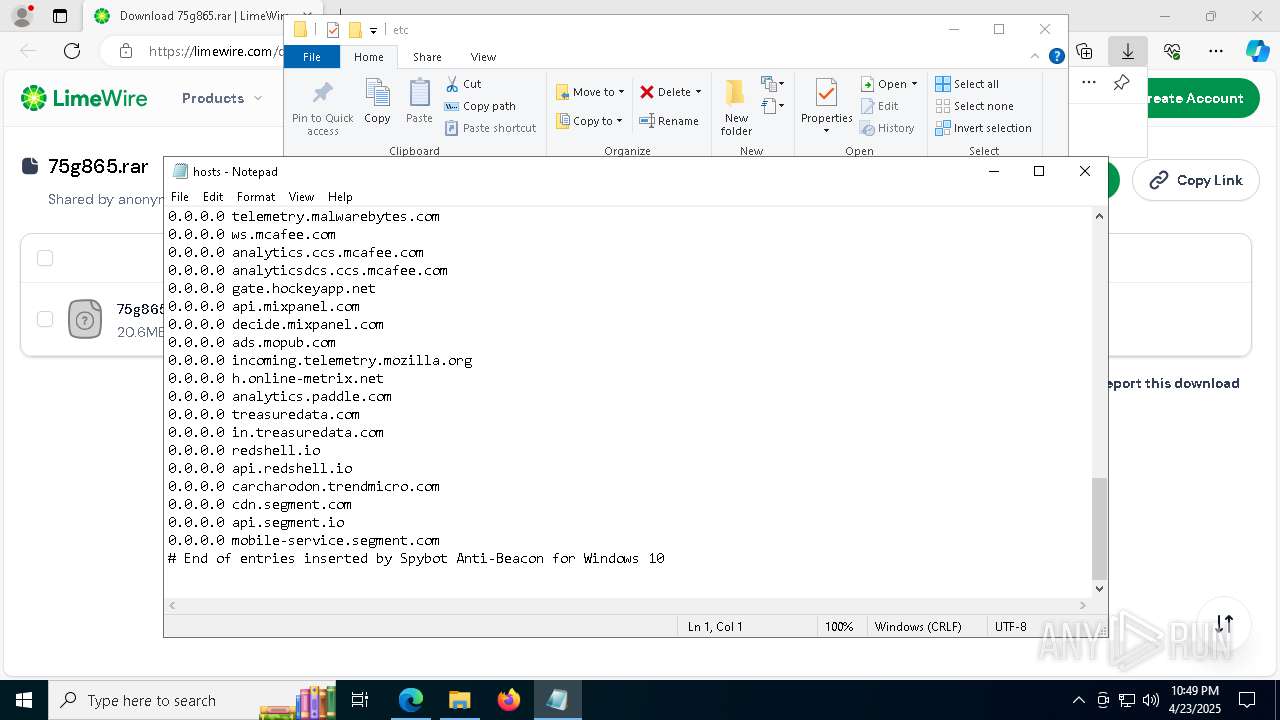
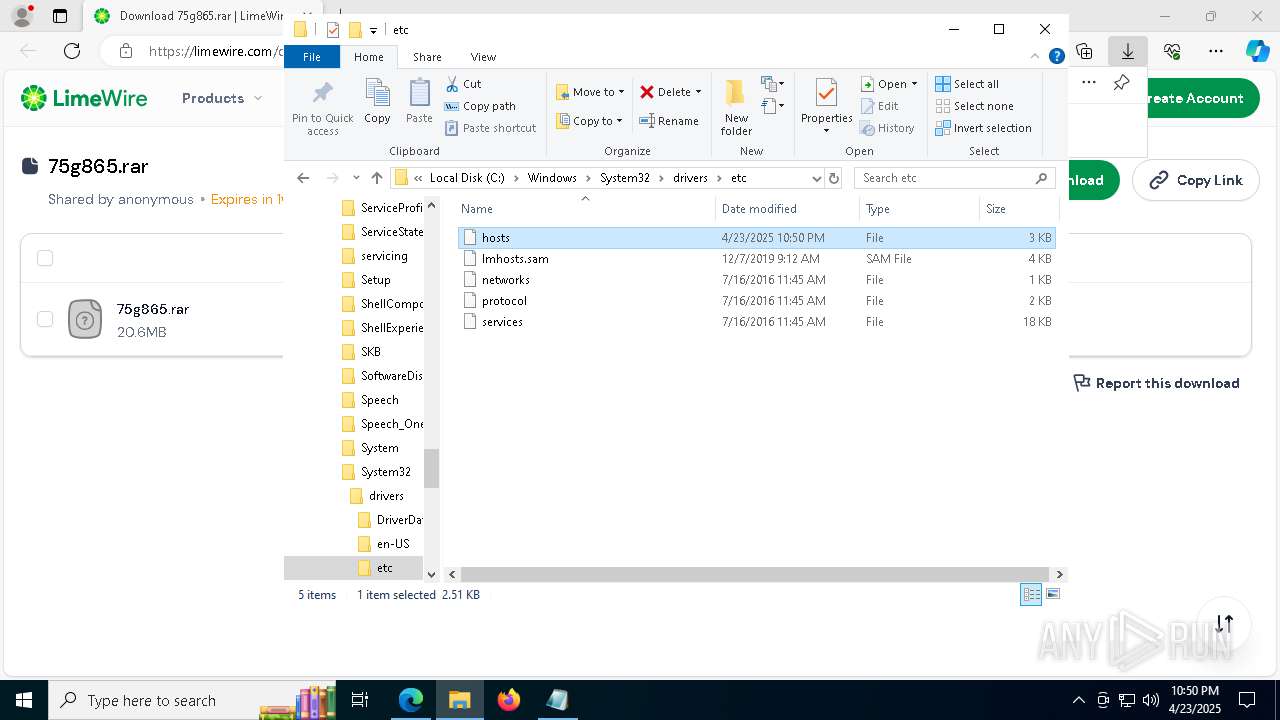
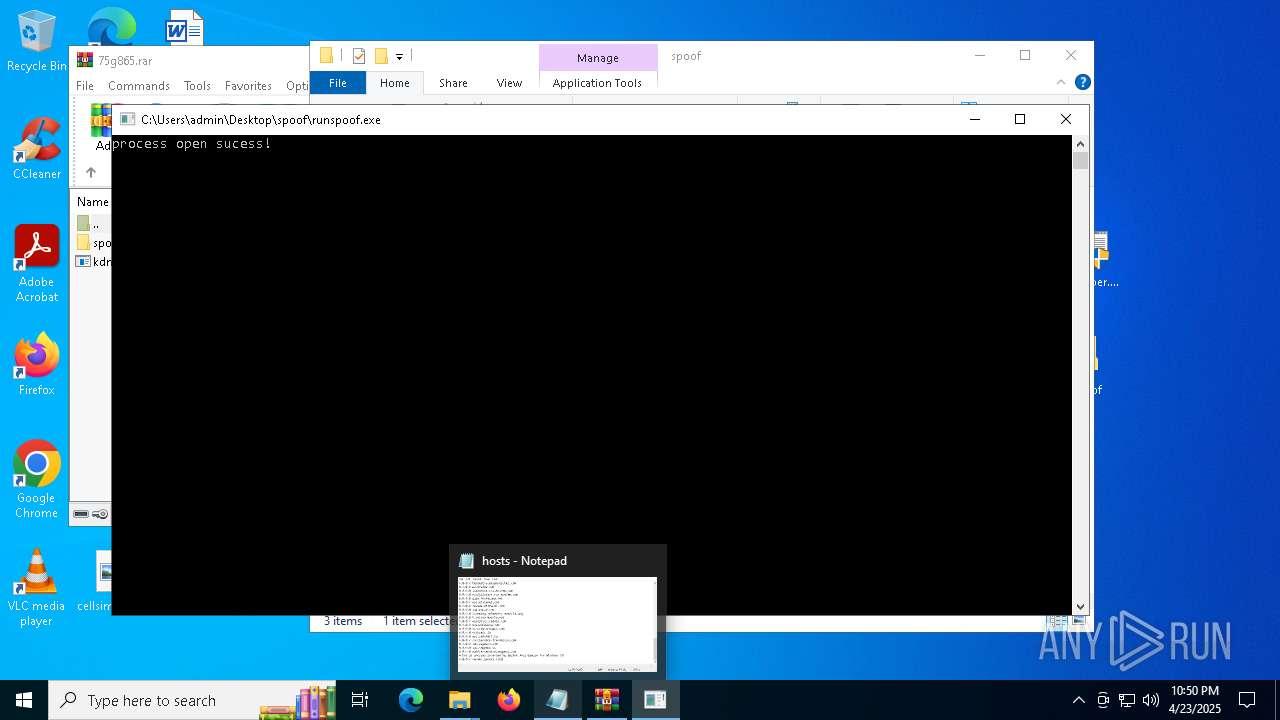
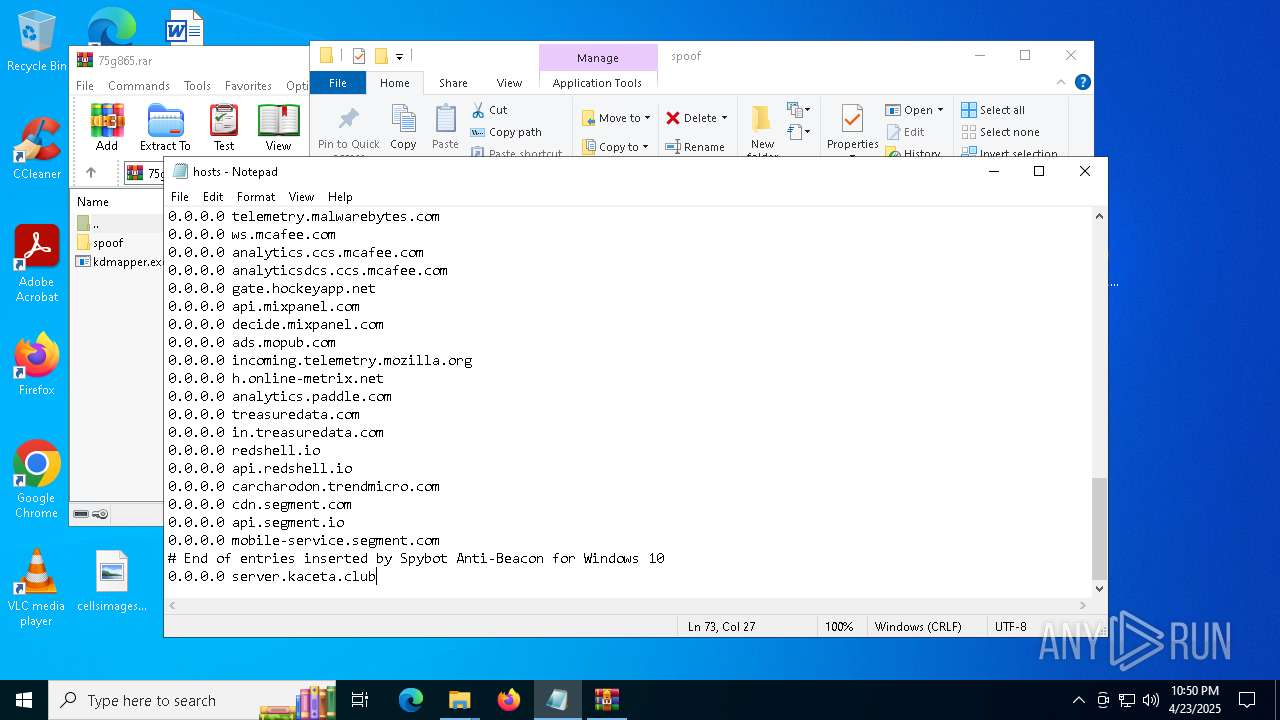
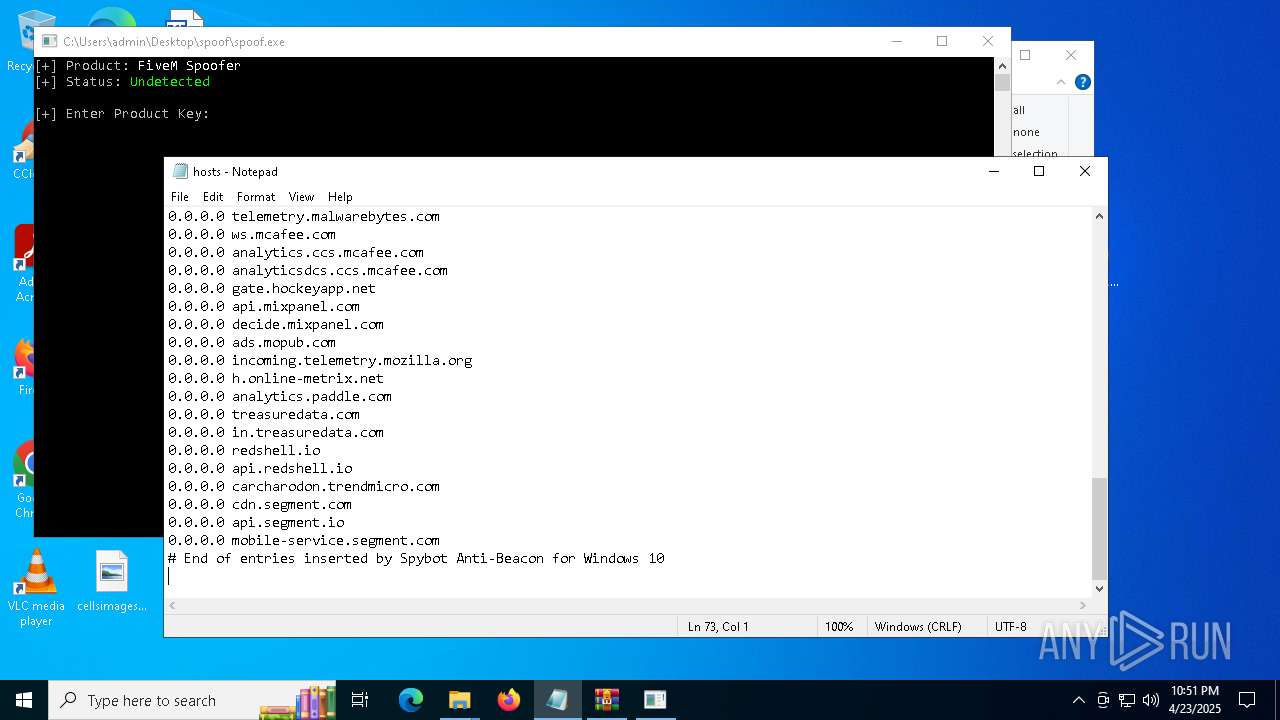
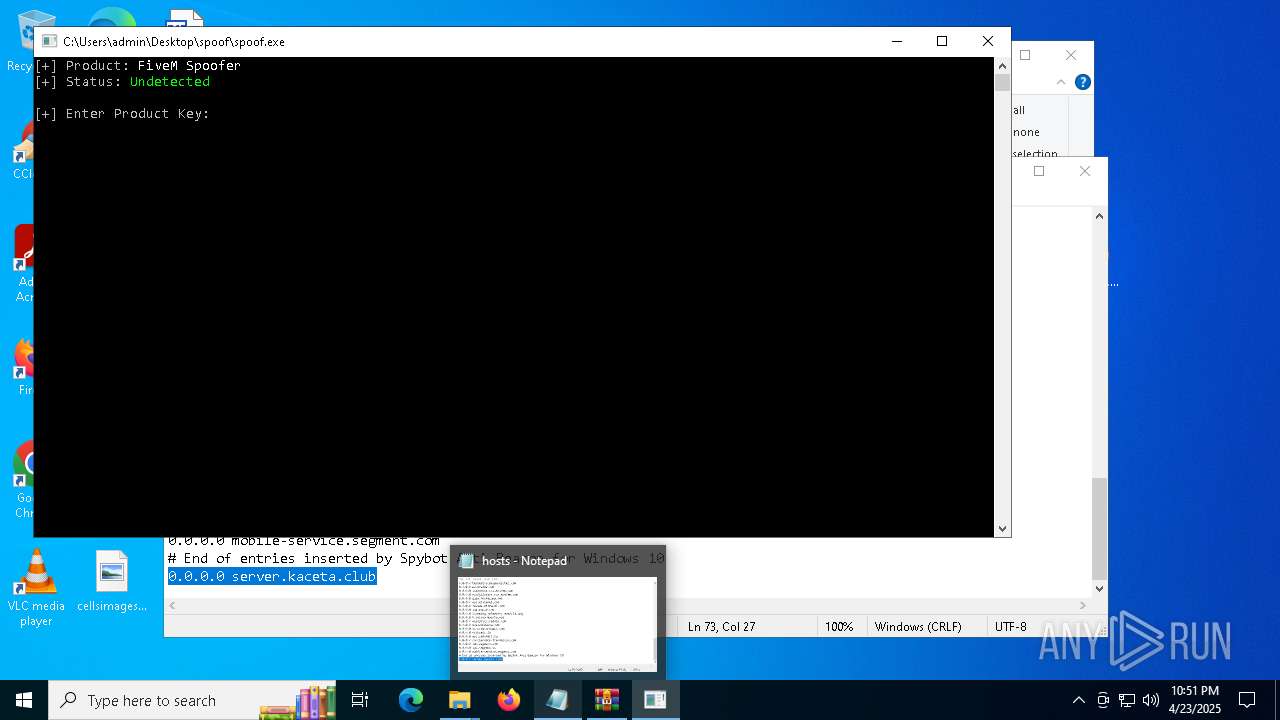
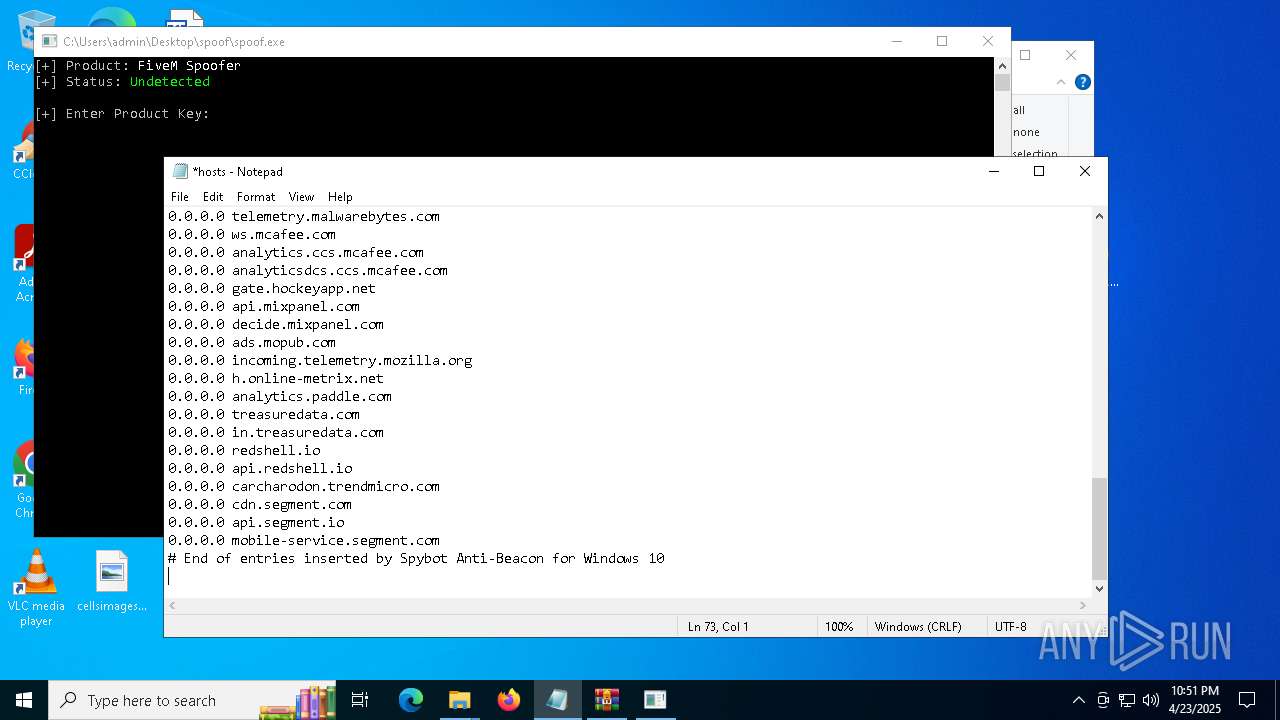
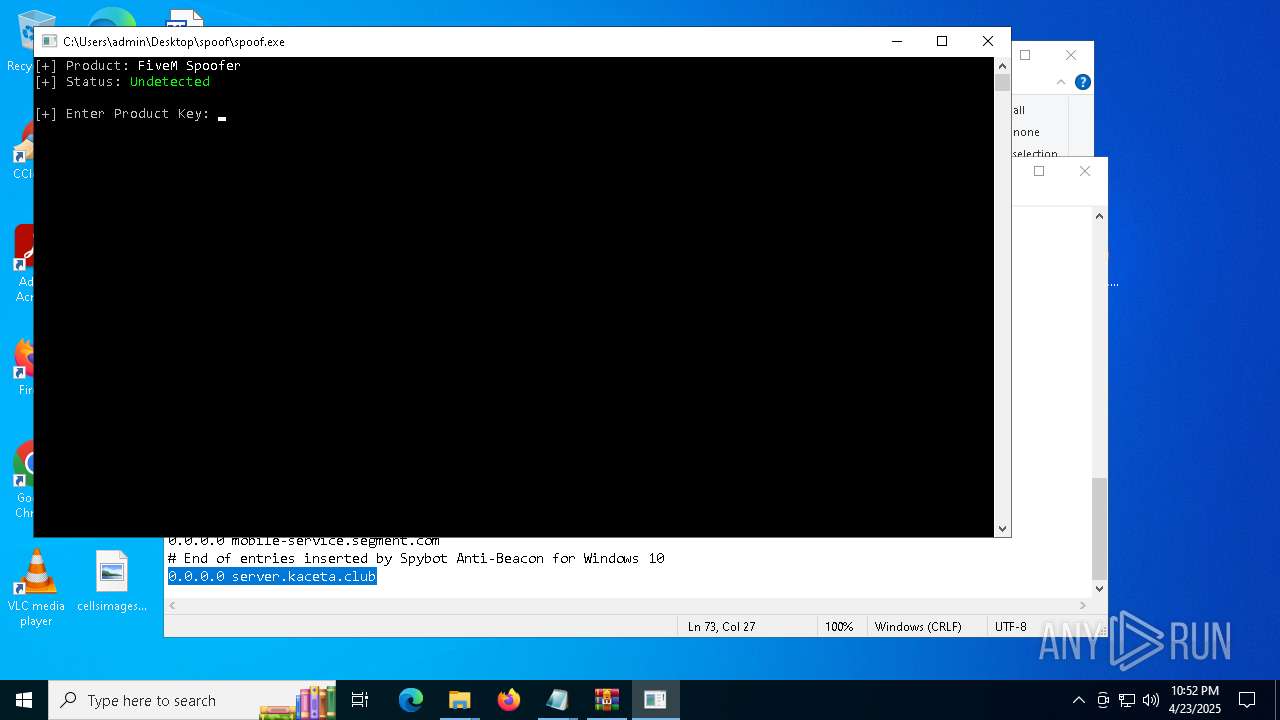
Modifies hosts file to alter network resolution
- notepad.exe (PID: 812)
- notepad.exe (PID: 5188)
Reads security settings of Internet Explorer
- runspoof.exe (PID: 7624)
- runspoof.exe (PID: 7932)
Reads the BIOS version
- spoof.exe (PID: 7588)
- spoof.exe (PID: 3896)
Reads the date of Windows installation
- spoof.exe (PID: 3896)
- spoof.exe (PID: 7588)
Hides command output
- cmd.exe (PID: 6540)
Starts CMD.EXE for commands execution
- spoof.exe (PID: 3896)
Starts application with an unusual extension
- cmd.exe (PID: 6540)
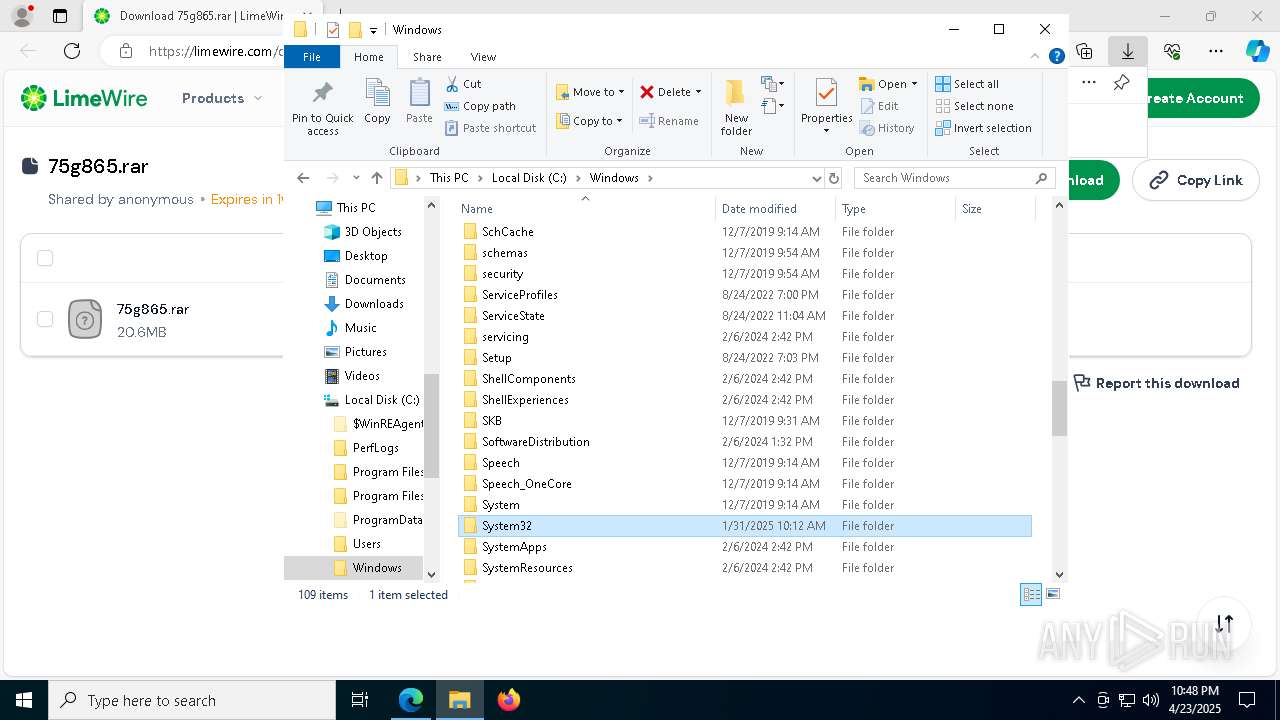
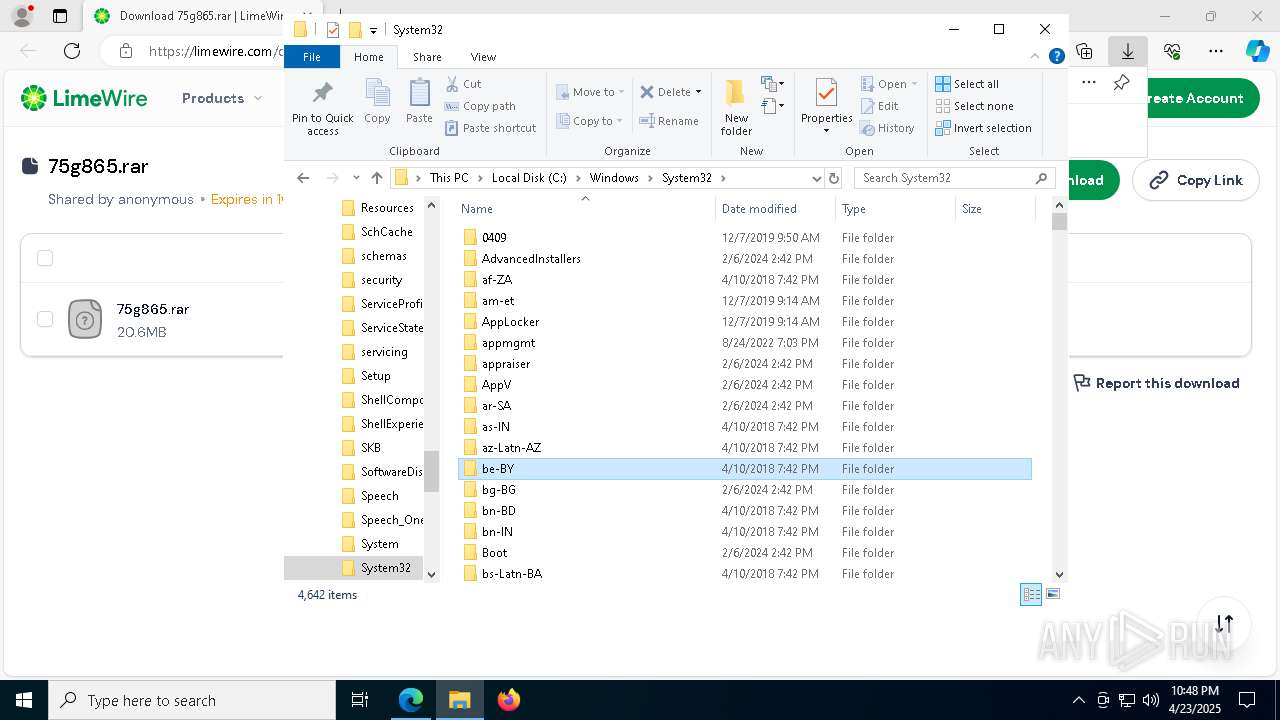
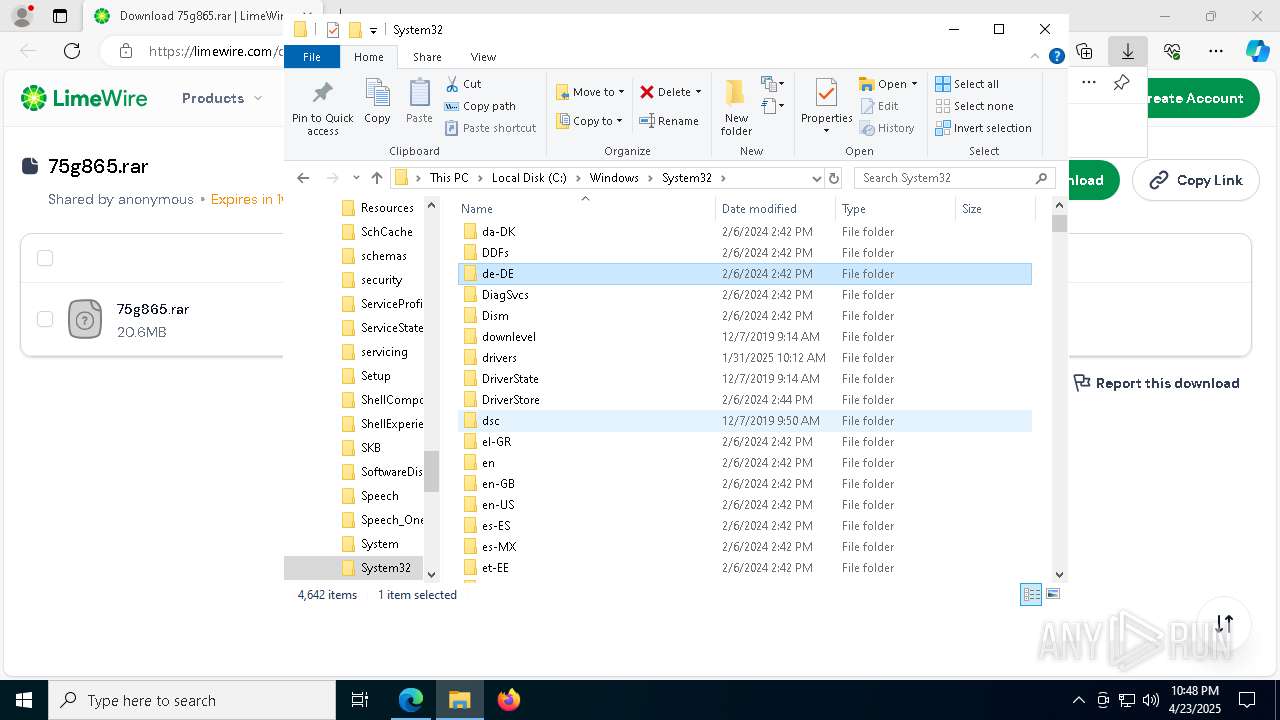
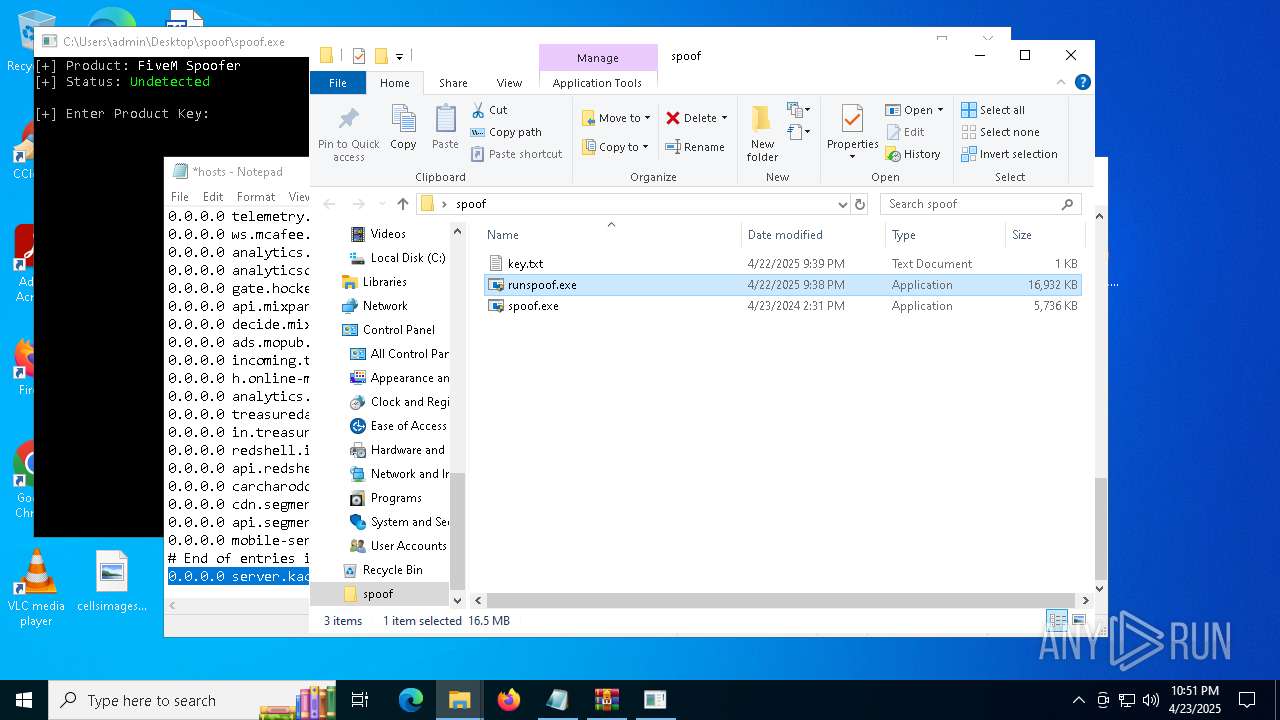
Executable content was dropped or overwritten
- spoof.exe (PID: 3896)
Creates or modifies Windows services
- spoof.exe (PID: 3896)
INFO
Application launched itself
- msedge.exe (PID: 7192)
- msedge.exe (PID: 1012)
Checks supported languages
- identity_helper.exe (PID: 1056)
- identity_helper.exe (PID: 496)
- identity_helper.exe (PID: 2236)
- runspoof.exe (PID: 7624)
- spoof.exe (PID: 7588)
- spoof.exe (PID: 3896)
- runspoof.exe (PID: 7932)
- chcp.com (PID: 5352)
Reads the computer name
- identity_helper.exe (PID: 1056)
- identity_helper.exe (PID: 496)
- identity_helper.exe (PID: 2236)
- runspoof.exe (PID: 7624)
- spoof.exe (PID: 7588)
- spoof.exe (PID: 3896)
- runspoof.exe (PID: 7932)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 5508)
- msedge.exe (PID: 7192)
Reads the software policy settings
- slui.exe (PID: 8164)
- slui.exe (PID: 8144)
- runspoof.exe (PID: 7624)
- runspoof.exe (PID: 7932)
Reads security settings of Internet Explorer
- OpenWith.exe (PID: 5508)
- notepad.exe (PID: 5188)
- notepad.exe (PID: 812)
- notepad.exe (PID: 444)
The sample compiled with english language support
- msedge.exe (PID: 7908)
- spoof.exe (PID: 3896)
Reads Environment values
- identity_helper.exe (PID: 1056)
- identity_helper.exe (PID: 496)
- identity_helper.exe (PID: 2236)
- spoof.exe (PID: 7588)
- spoof.exe (PID: 3896)
Executable content was dropped or overwritten
- msedge.exe (PID: 7908)
- WinRAR.exe (PID: 7084)
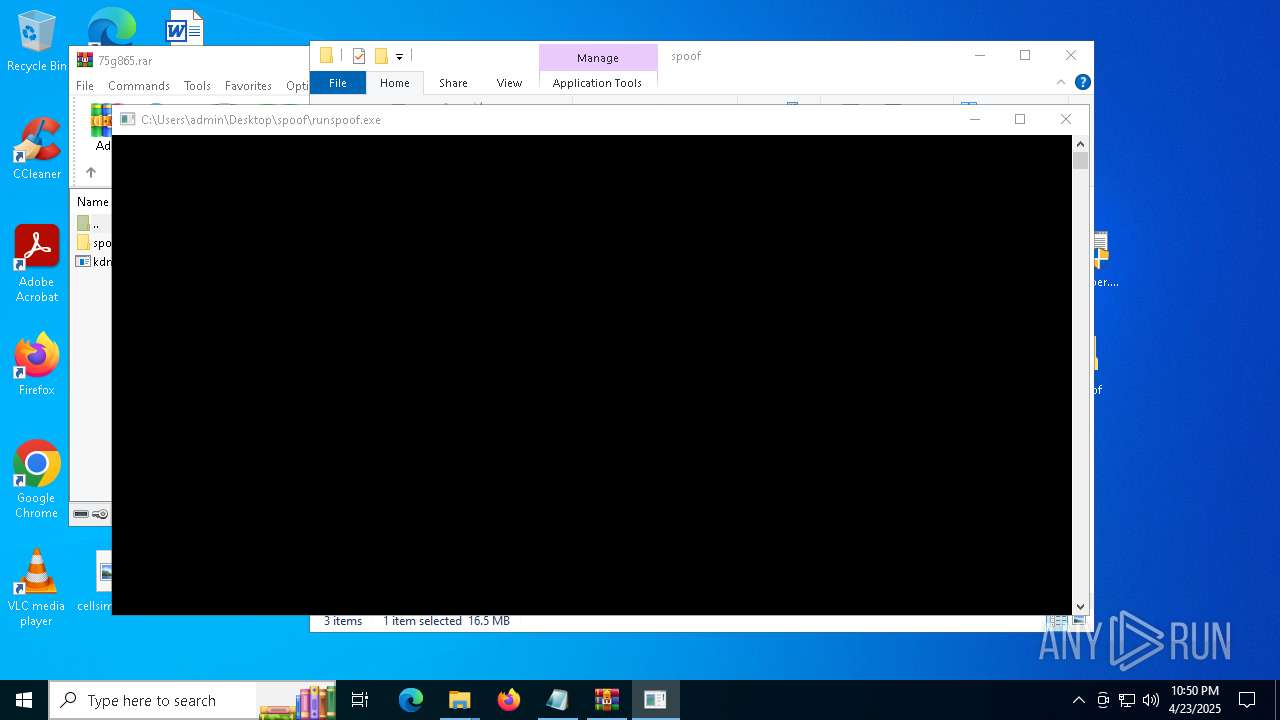
Manual execution by a user
- notepad.exe (PID: 5188)
- runspoof.exe (PID: 8188)
- runspoof.exe (PID: 7624)
- runspoof.exe (PID: 7932)
- runspoof.exe (PID: 7284)
- notepad.exe (PID: 444)
Checks proxy server information
- slui.exe (PID: 8144)
- runspoof.exe (PID: 7624)
- runspoof.exe (PID: 7932)
Reads the machine GUID from the registry
- runspoof.exe (PID: 7624)
- runspoof.exe (PID: 7932)
Creates files or folders in the user directory
- runspoof.exe (PID: 7624)
Process checks whether UAC notifications are on
- spoof.exe (PID: 7588)
- spoof.exe (PID: 3896)
Reads product name
- spoof.exe (PID: 7588)
- spoof.exe (PID: 3896)
Reads Windows Product ID
- spoof.exe (PID: 7588)
- spoof.exe (PID: 3896)
Changes the display of characters in the console
- cmd.exe (PID: 6540)
Themida protector has been detected
- spoof.exe (PID: 3896)
Create files in a temporary directory
- spoof.exe (PID: 3896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
248
Monitored processes
105
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
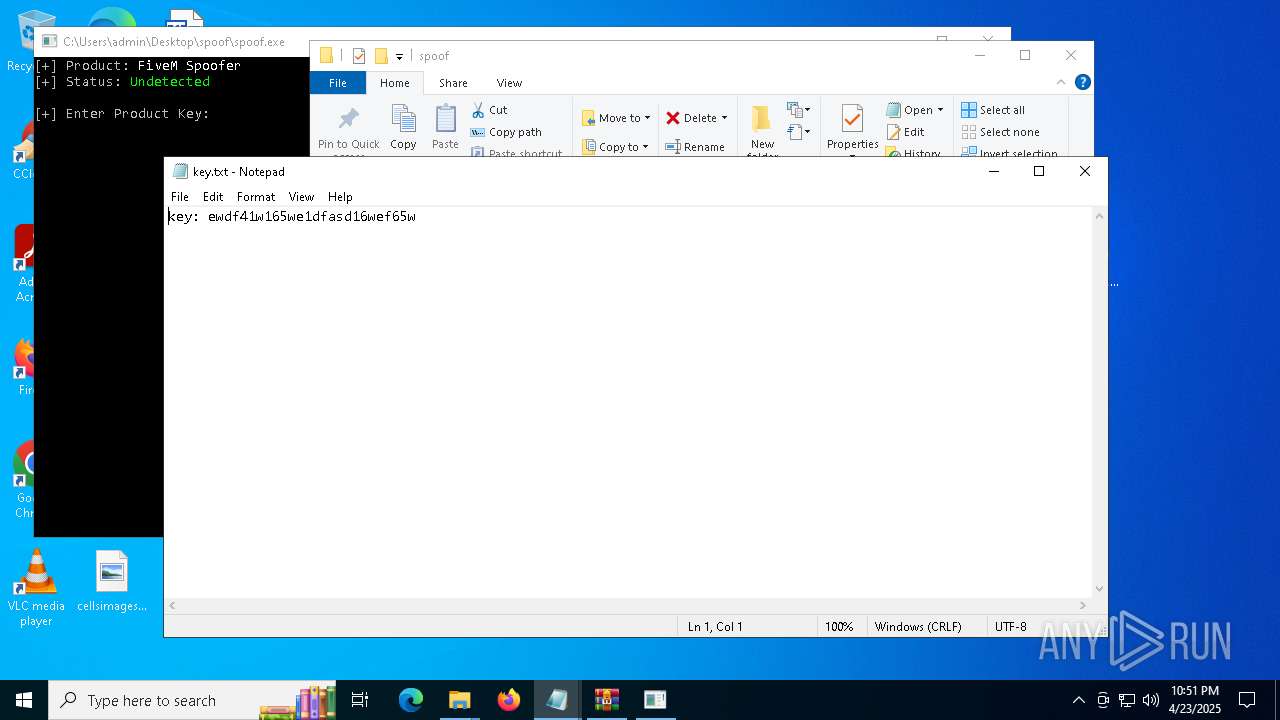
| 444 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\spoof\key.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 472 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2368 --field-trial-handle=2372,i,18103882457104365453,5736215415635034968,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 496 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7916 --field-trial-handle=2316,i,17344414822414908268,17240118334325763988,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 736 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x290,0x294,0x298,0x288,0x2a0,0x7ffc88105fd8,0x7ffc88105fe4,0x7ffc88105ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 812 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Windows\System32\drivers\etc\hosts | C:\Windows\System32\notepad.exe | — | OpenWith.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 904 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6908 --field-trial-handle=2316,i,17344414822414908268,17240118334325763988,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 976 | C:\WINDOWS\system32\cmd.exe /c echo %user_id% | C:\Windows\System32\cmd.exe | — | spoof.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1012 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5220 --field-trial-handle=2372,i,18103882457104365453,5736215415635034968,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1056 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6580 --field-trial-handle=2316,i,17344414822414908268,17240118334325763988,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
24 753
Read events
24 570
Write events
178
Delete events
5
Modification events
| (PID) Process: | (7192) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7192) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7192) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7192) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7192) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: ABF34E2C10922F00 | |||
| (PID) Process: | (7192) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 6E61552C10922F00 | |||
| (PID) Process: | (7192) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328518 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4615EA1A-F7EB-404F-94E9-FF10632A5D2A} | |||
| (PID) Process: | (4996) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4996) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4996) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
28
Suspicious files
574
Text files
126
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b855.TMP | — | |
MD5:— | SHA256:— | |||
| 7192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b865.TMP | — | |
MD5:— | SHA256:— | |||
| 7192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b865.TMP | — | |
MD5:— | SHA256:— | |||
| 7192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b865.TMP | — | |
MD5:— | SHA256:— | |||
| 7192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b874.TMP | — | |
MD5:— | SHA256:— | |||
| 7192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
65
TCP/UDP connections
117
DNS requests
126
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.20.245.137:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7332 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1746053246&P2=404&P3=2&P4=Q5DZ61cyku6Qq1kb0hNGw5VzcoBr64xIajBZSmEoog8lINaRPe5BulVg%2bURWlCOH80DwGET%2fESFs0yIogaSRzw%3d%3d | unknown | — | — | whitelisted |
7332 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1746053246&P2=404&P3=2&P4=Q5DZ61cyku6Qq1kb0hNGw5VzcoBr64xIajBZSmEoog8lINaRPe5BulVg%2bURWlCOH80DwGET%2fESFs0yIogaSRzw%3d%3d | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1096 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1096 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7332 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1746053246&P2=404&P3=2&P4=Q5DZ61cyku6Qq1kb0hNGw5VzcoBr64xIajBZSmEoog8lINaRPe5BulVg%2bURWlCOH80DwGET%2fESFs0yIogaSRzw%3d%3d | unknown | — | — | whitelisted |
7332 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1746053246&P2=404&P3=2&P4=YNQ5dzAgORaw20AT82U0WErOjIdGvtgDkkdU6hojf3Jpl5ClbykgW1eE%2bKQEQXP7Wv2T2OPY736kf9nMBDfBzA%3d%3d | unknown | — | — | whitelisted |
7332 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1746053246&P2=404&P3=2&P4=Q5DZ61cyku6Qq1kb0hNGw5VzcoBr64xIajBZSmEoog8lINaRPe5BulVg%2bURWlCOH80DwGET%2fESFs0yIogaSRzw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.20.245.137:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7192 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7432 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7432 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7432 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7432 | msedge.exe | 172.67.26.165:443 | limewire.com | CLOUDFLARENET | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
limewire.com |
| unknown |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7432 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare R2 Storage (r2 .cloudflarestorage .com) |
7432 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare R2 Storage (r2 .cloudflarestorage .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |