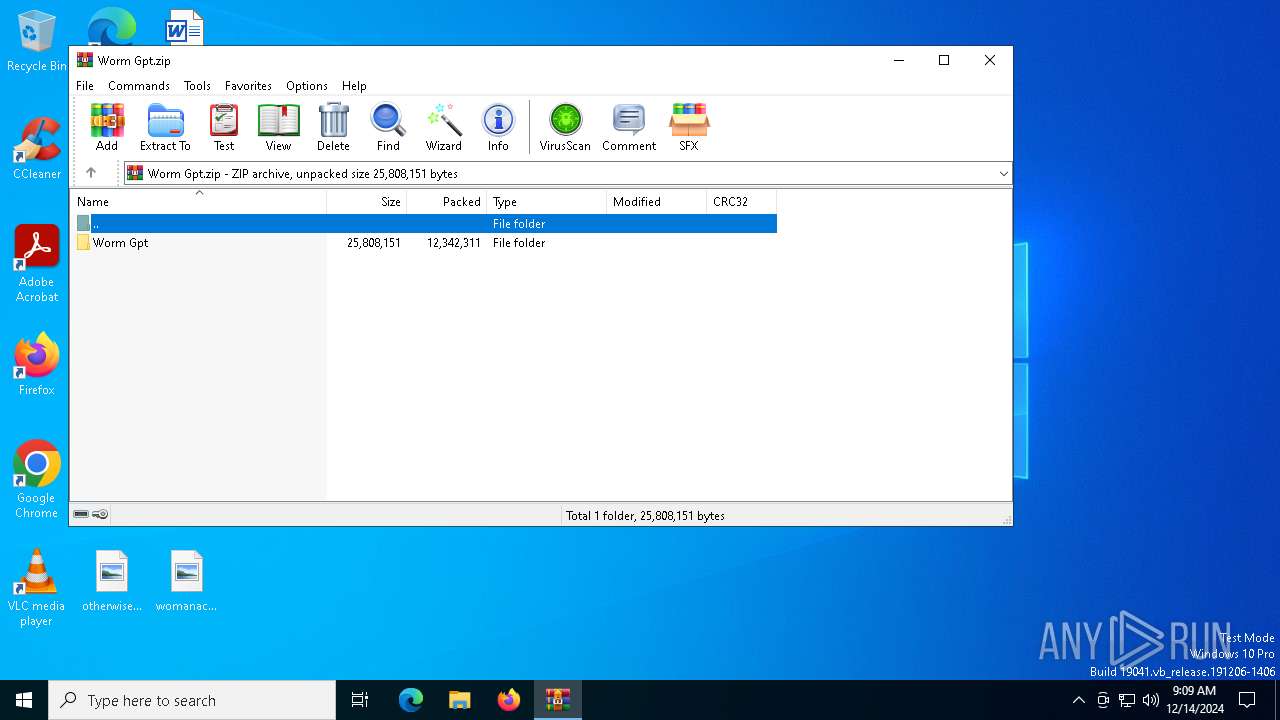
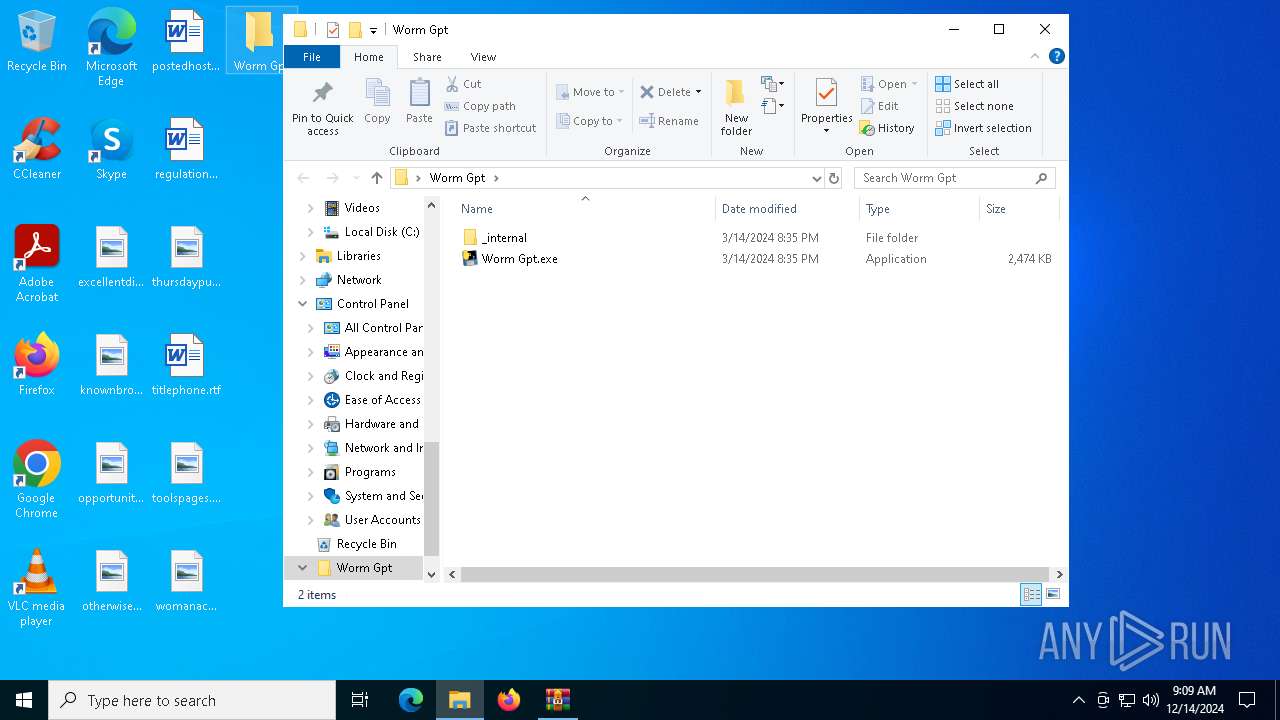
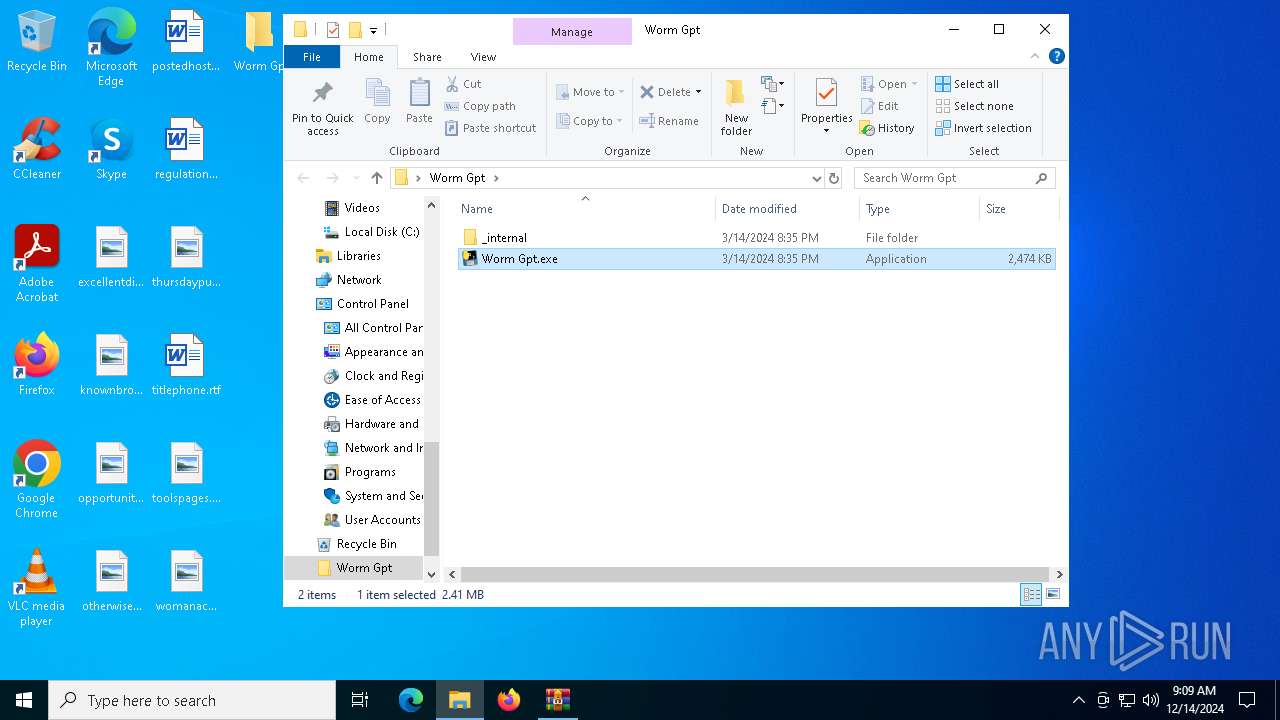
| File name: | Worm Gpt.zip |
| Full analysis: | https://app.any.run/tasks/69076256-caae-4df1-a017-ea4e53858f94 |
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2024, 09:09:37 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | A3309BA763E575F888678194BA20C7F7 |
| SHA1: | CF49753AED2CC38128F56C87B1EBA1737F14B521 |
| SHA256: | F637FE964D9EF183CB32C9F1749EFFA54BFCB5E7E029BA56FDA3BBFA406B5220 |
| SSDEEP: | 98304:ldd2PaORF9K9Zhoi/bWo1WNq7PZU2tmQyZFgrK3R1W2mNQ9hoSFogmXZM3VvyDtV:lyZ7L3K5/zrMF9lSyI |
MALICIOUS
No malicious indicators.SUSPICIOUS
Generic archive extractor
- WinRAR.exe (PID: 6792)
Starts CMD.EXE for commands execution
- Worm Gpt.exe (PID: 6452)
Process drops python dynamic module
- WinRAR.exe (PID: 6792)
Loads Python modules
- Worm Gpt.exe (PID: 6452)
Process drops legitimate windows executable
- WinRAR.exe (PID: 6792)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 6792)
The process uses the downloaded file
- WinRAR.exe (PID: 6792)
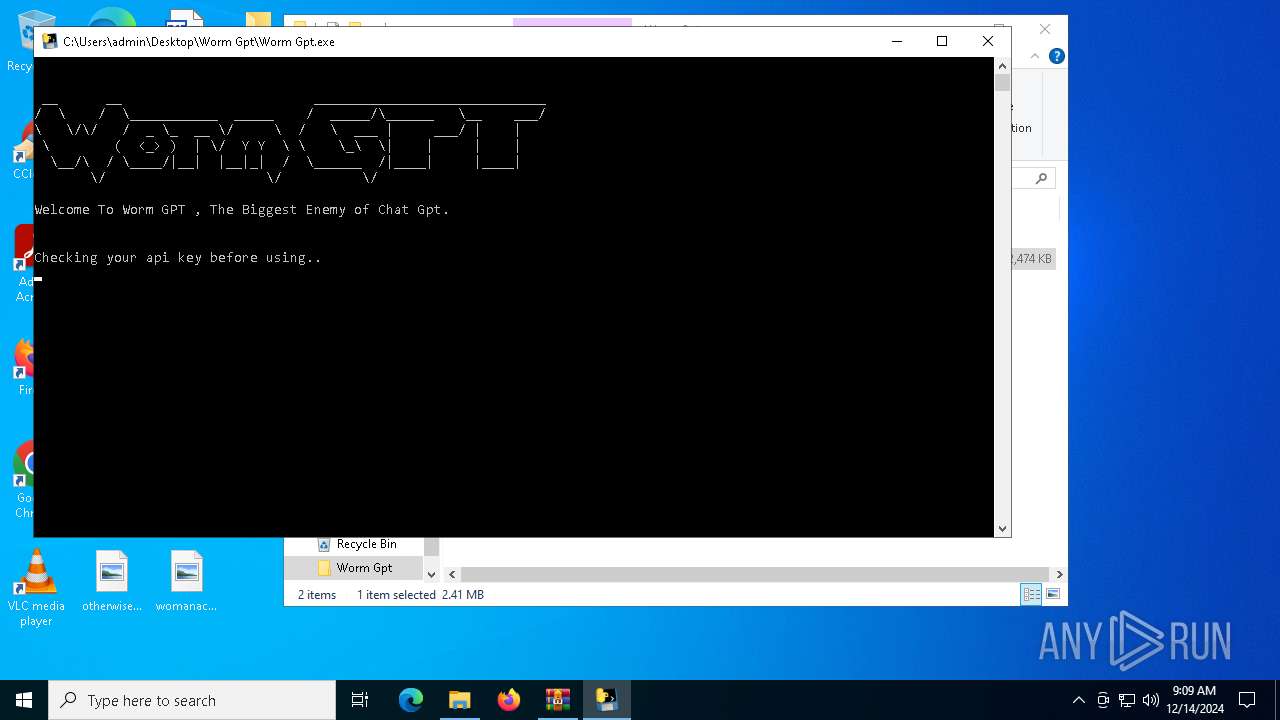
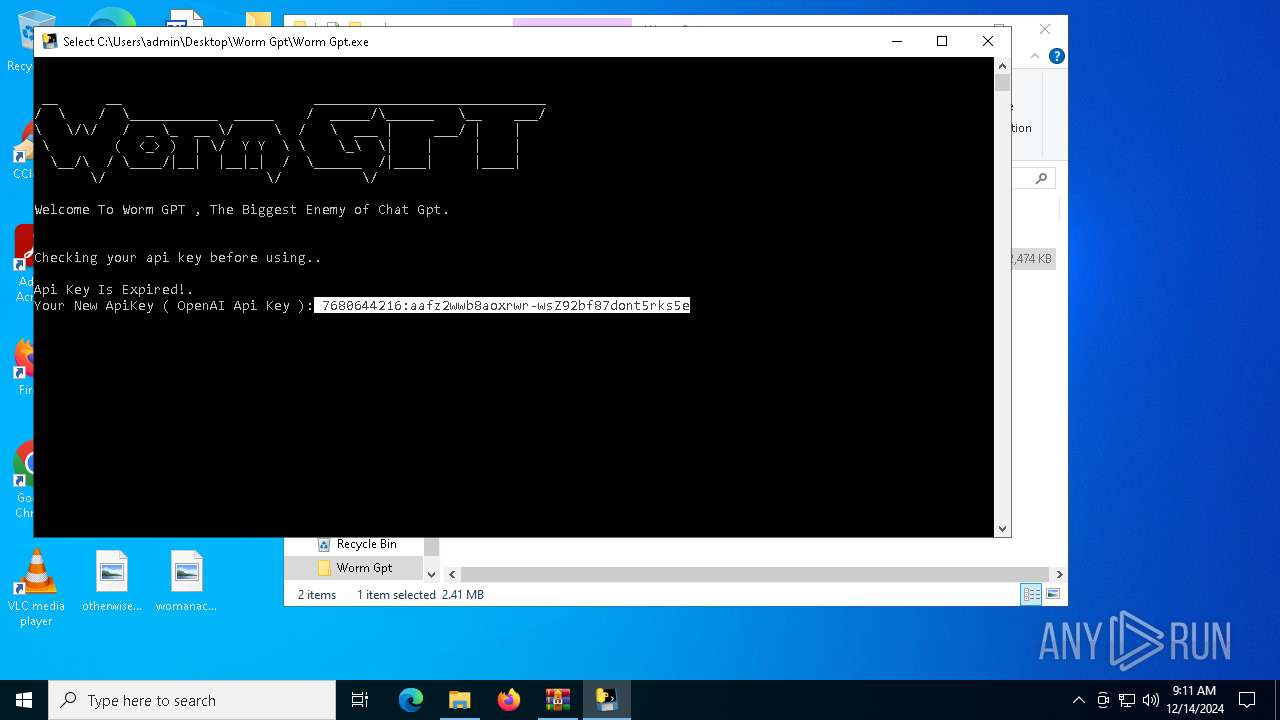
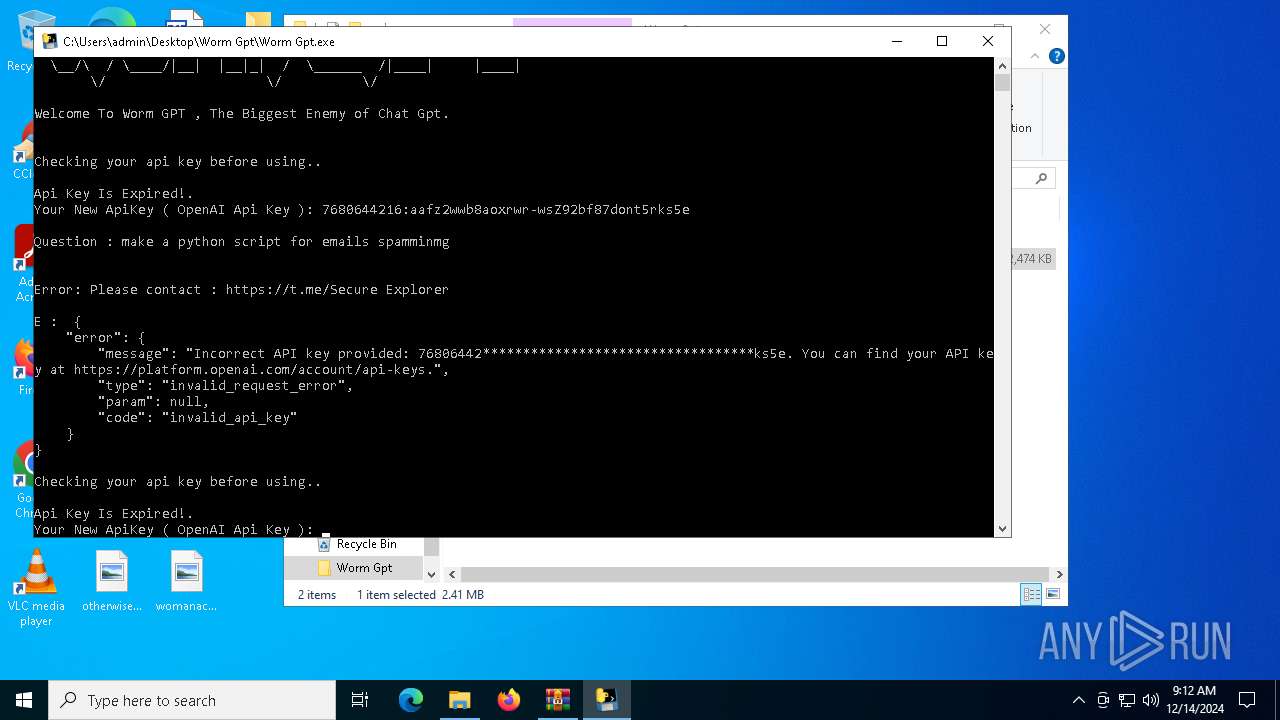
Manual execution by a user
- Worm Gpt.exe (PID: 6452)
Checks proxy server information
- Worm Gpt.exe (PID: 6452)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6792)
Reads the computer name
- Worm Gpt.exe (PID: 6452)
PyInstaller has been detected (YARA)
- Worm Gpt.exe (PID: 6452)
Checks supported languages
- Worm Gpt.exe (PID: 6452)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:03:14 20:35:08 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Worm Gpt/_internal/ |
Total processes
127
Monitored processes
6
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 556 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6364 | C:\WINDOWS\system32\cmd.exe /c cls | C:\Windows\System32\cmd.exe | — | Worm Gpt.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6452 | "C:\Users\admin\Desktop\Worm Gpt\Worm Gpt.exe" | C:\Users\admin\Desktop\Worm Gpt\Worm Gpt.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 6484 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Worm Gpt.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
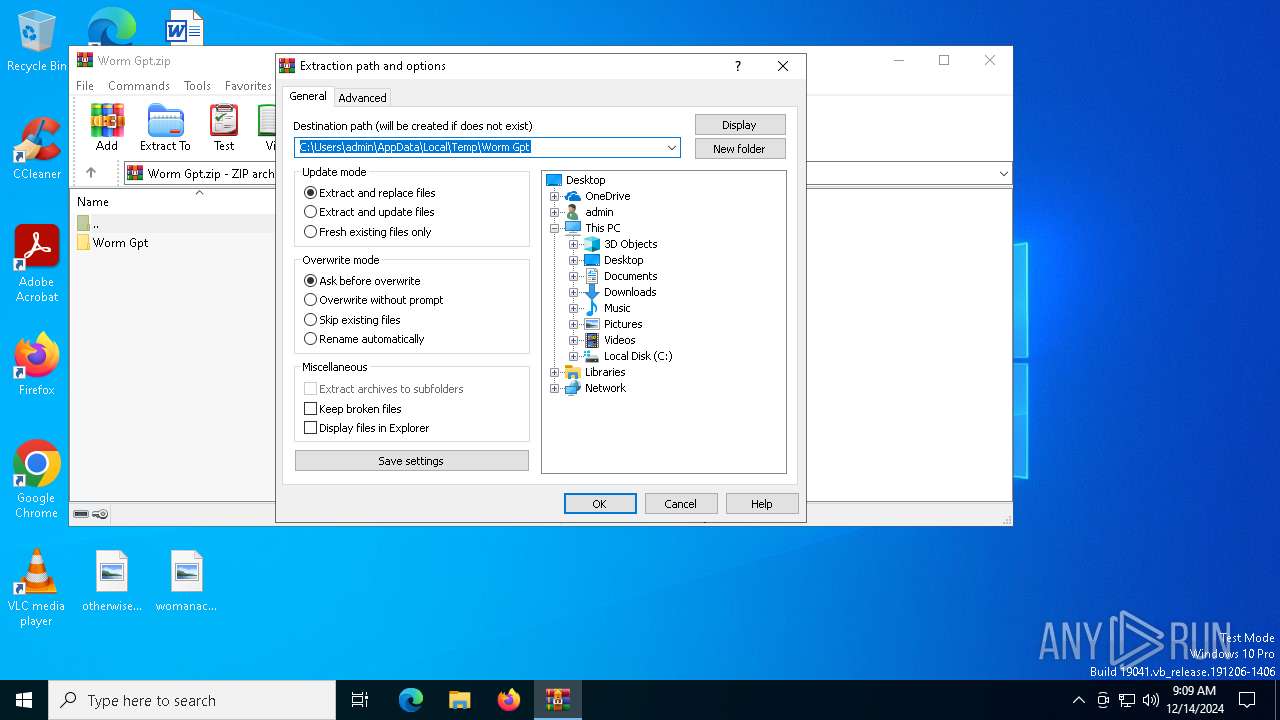
| 6792 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Worm Gpt.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
2 451
Read events
2 427
Write events
11
Delete events
13
Modification events
| (PID) Process: | (6792) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6792) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6792) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6792) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Worm Gpt.zip | |||
| (PID) Process: | (6792) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6792) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6792) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6792) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6792) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (6792) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
19
Suspicious files
1
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6792 | WinRAR.exe | C:\Users\admin\Desktop\Worm Gpt\_internal\_bz2.pyd | executable | |
MD5:37EACE4B806B32F829DE08DB3803B707 | SHA256:1BE51EF2B5ACBE490217AA1FF12618D24B95DF6136C6844714B9CA997B4C7F9B | |||
| 6792 | WinRAR.exe | C:\Users\admin\Desktop\Worm Gpt\_internal\_hashlib.pyd | executable | |
MD5:BA682DFCDD600A4BB43A51A0D696A64C | SHA256:2AD55E11BDDB5B65CDF6E9E126D82A3B64551F7AD9D4CBF74A1058FD7E5993BD | |||
| 6792 | WinRAR.exe | C:\Users\admin\Desktop\Worm Gpt\_internal\cryptography-42.0.5.dist-info\LICENSE.APACHE | text | |
MD5:4E168CCE331E5C827D4C2B68A6200E1B | SHA256:AAC73B3148F6D1D7111DBCA32099F68D26C644C6813AE1E4F05F6579AA2663FE | |||
| 6792 | WinRAR.exe | C:\Users\admin\Desktop\Worm Gpt\_internal\cryptography-42.0.5.dist-info\INSTALLER | text | |
MD5:365C9BFEB7D89244F2CE01C1DE44CB85 | SHA256:CEEBAE7B8927A3227E5303CF5E0F1F7B34BB542AD7250AC03FBCDE36EC2F1508 | |||
| 6792 | WinRAR.exe | C:\Users\admin\Desktop\Worm Gpt\_internal\cryptography\hazmat\bindings\_rust.pyd | executable | |
MD5:12A7C0D35CCBD002150BB29DDD7E8440 | SHA256:7E22D579AC503B959268964102C03D4E96C8A9B74186158B8C82FDC8CF9D9522 | |||
| 6792 | WinRAR.exe | C:\Users\admin\Desktop\Worm Gpt\_internal\cryptography-42.0.5.dist-info\RECORD | csv | |
MD5:B8A20E6112E320D4C671BDBD4A62211E | SHA256:05E89D7DD1F7E50697843E4803E9A864CD5540E06E831BEE264D1308354FBF0F | |||
| 6792 | WinRAR.exe | C:\Users\admin\Desktop\Worm Gpt\_internal\cryptography-42.0.5.dist-info\LICENSE.BSD | text | |
MD5:5AE30BA4123BC4F2FA49AA0B0DCE887B | SHA256:602C4C7482DE6479DD2E9793CDA275E5E63D773DACD1ECA689232AB7008FB4FB | |||
| 6792 | WinRAR.exe | C:\Users\admin\Desktop\Worm Gpt\_internal\cryptography-42.0.5.dist-info\METADATA | text | |
MD5:AD313397AABF8AF5D234DF73C901CB4D | SHA256:65479522961A5B9B1C4811232C4133DDC8BDA9BBBC7562B81EF76857A2A2475A | |||
| 6792 | WinRAR.exe | C:\Users\admin\Desktop\Worm Gpt\_internal\charset_normalizer\md.cp311-win_amd64.pyd | executable | |
MD5:723EC2E1404AE1047C3EF860B9840C29 | SHA256:790A11AA270523C2EFA6021CE4F994C3C5A67E8EAAAF02074D5308420B68BD94 | |||
| 6792 | WinRAR.exe | C:\Users\admin\Desktop\Worm Gpt\_internal\charset_normalizer\md__mypyc.cp311-win_amd64.pyd | executable | |
MD5:9EA8098D31ADB0F9D928759BDCA39819 | SHA256:3D9893AA79EFD13D81FCD614E9EF5FB6AAD90569BEEDED5112DE5ED5AC3CF753 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
35
DNS requests
20
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
732 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
732 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6656 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6372 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6372 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
732 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
732 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 104.126.37.145:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 20.190.159.23:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
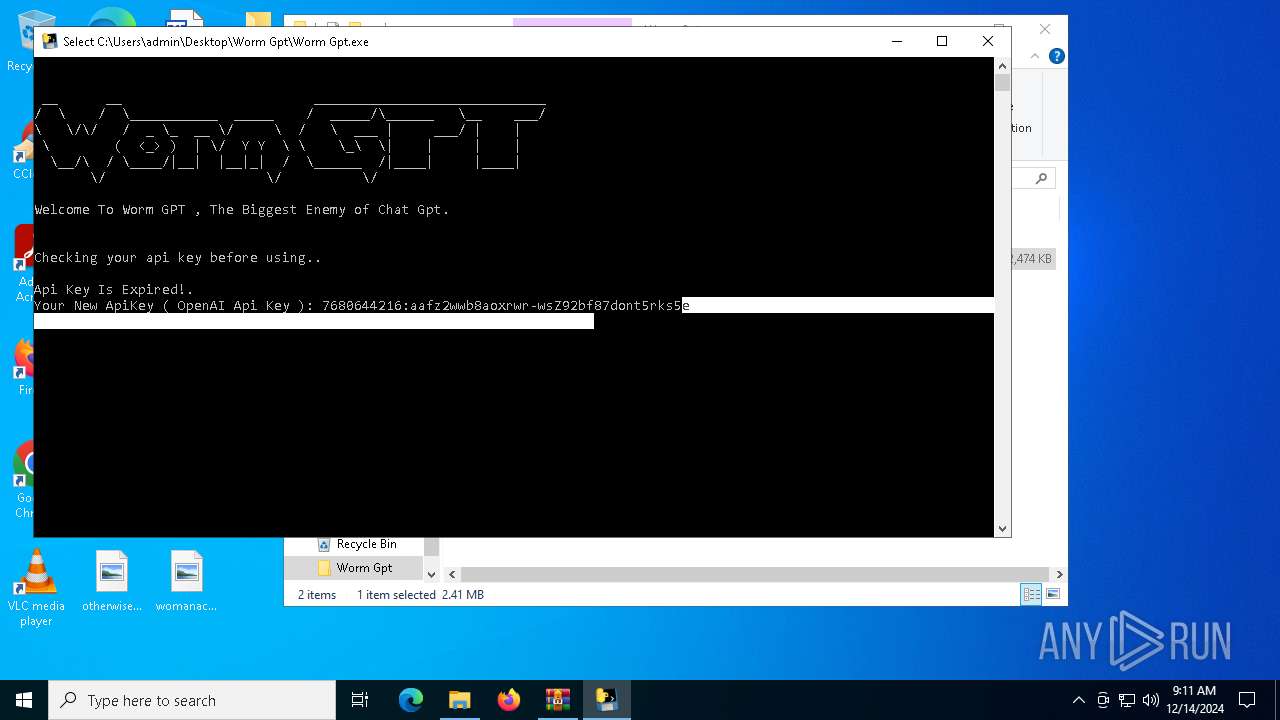
api.openai.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Potentially Bad Traffic | ET INFO OpenAI API Domain in DNS Lookup (api .openai .com) |
2192 | svchost.exe | Potentially Bad Traffic | ET INFO OpenAI API Domain in DNS Lookup (api .openai .com) |