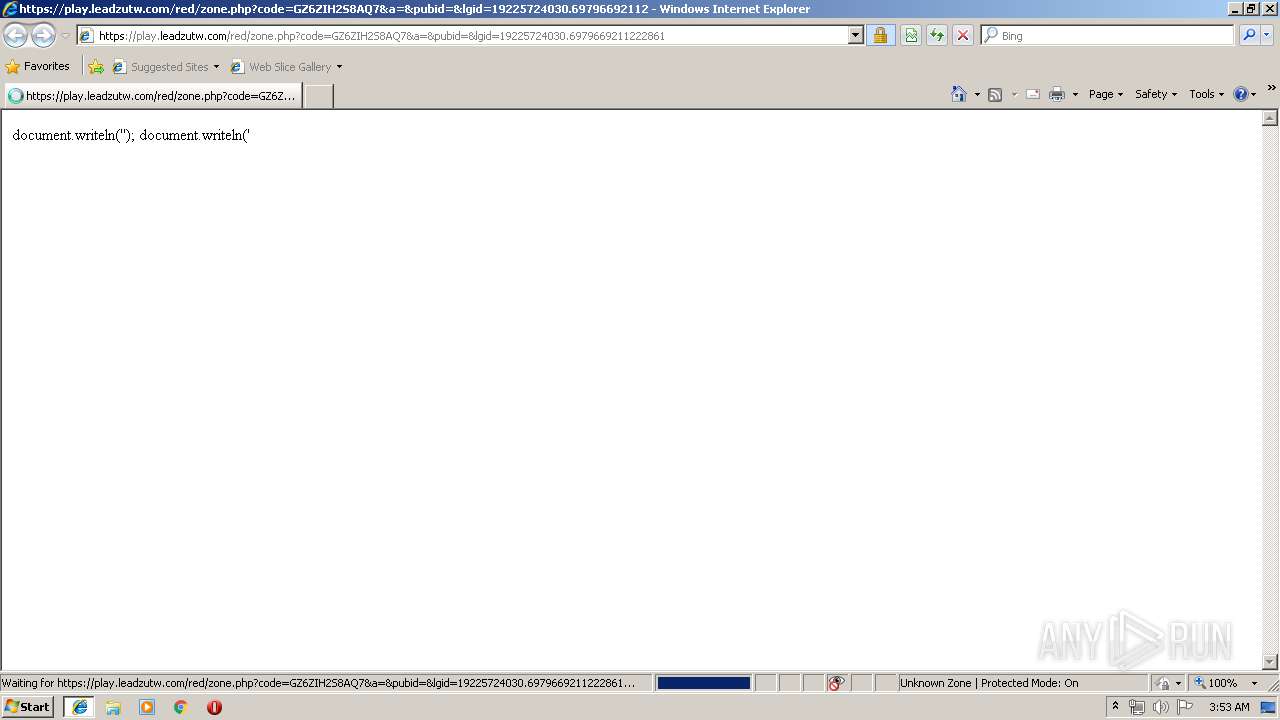
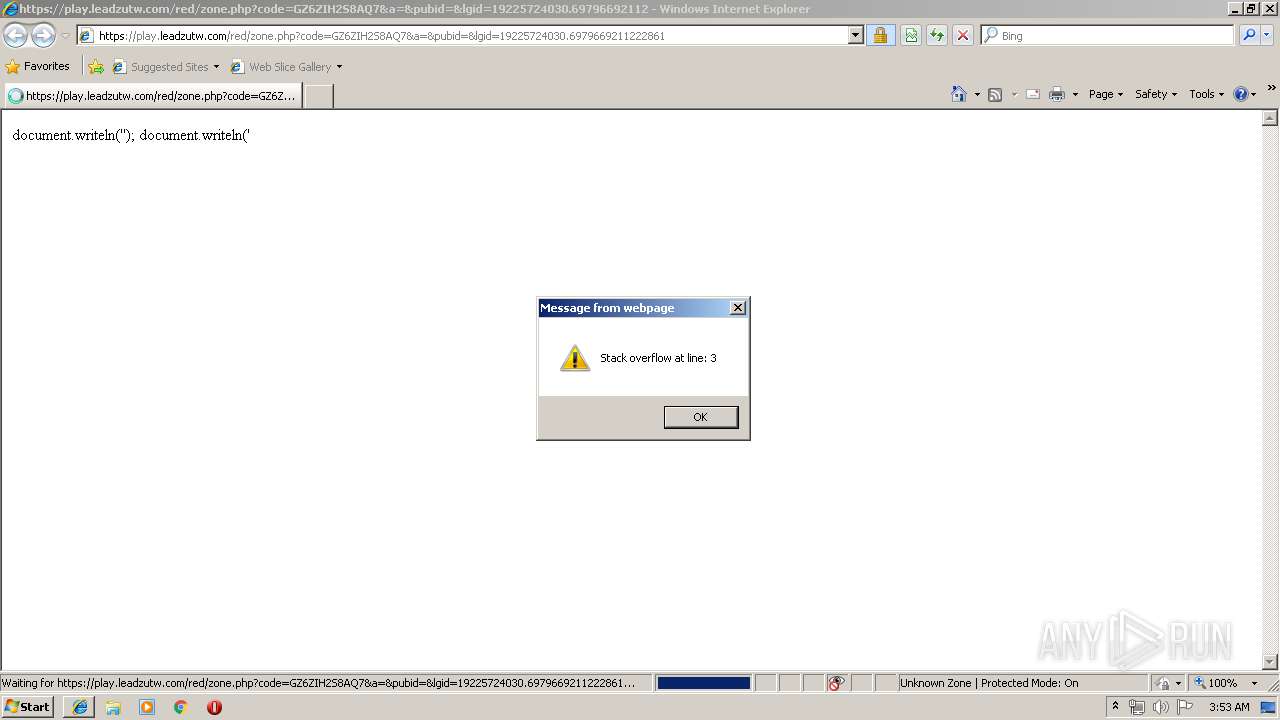
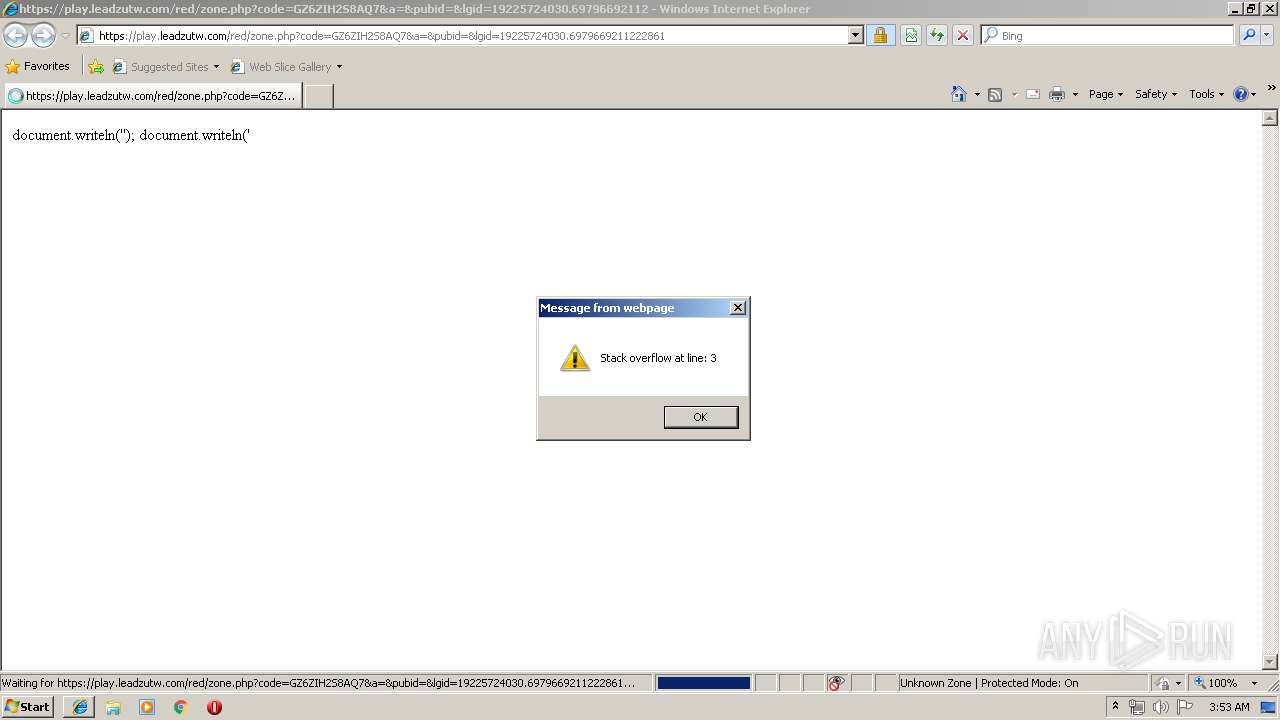
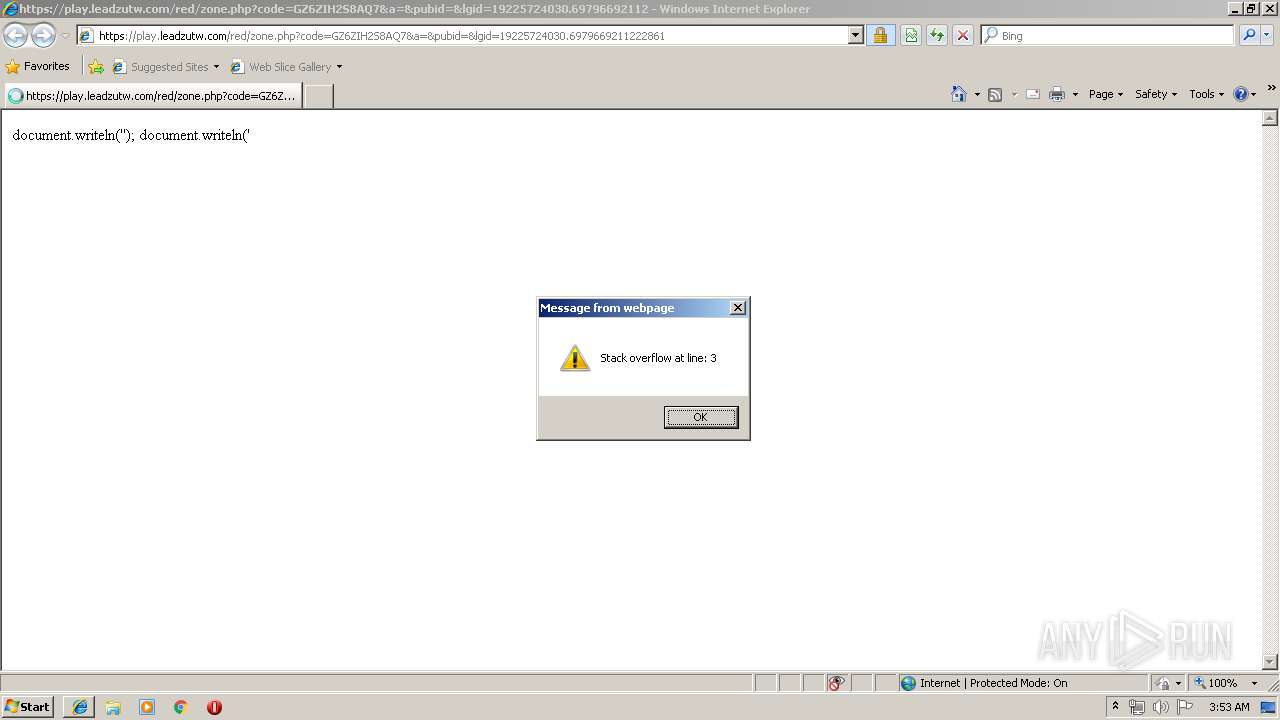
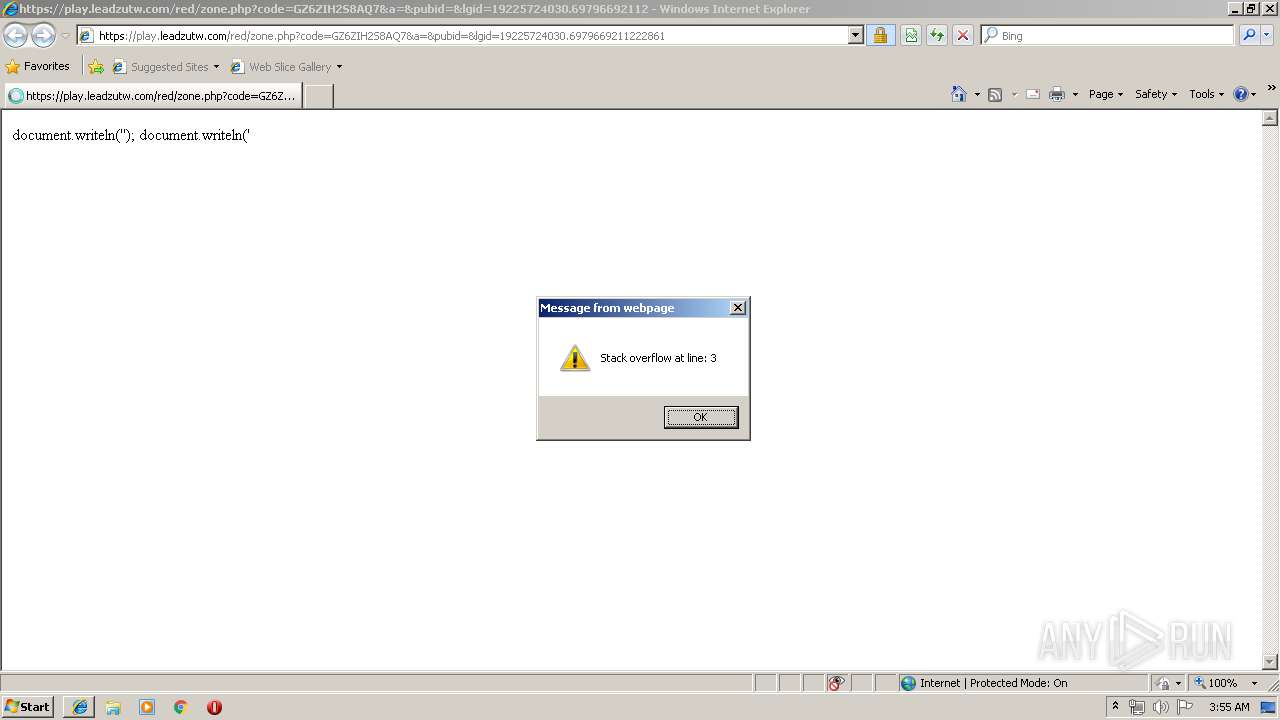
| URL: | https://play.leadzutw.com/red/zone.php?code=GZ6ZIH2S8AQ7&a=&pubid=&lgid=19225724030.6979669211222861 |
| Full analysis: | https://app.any.run/tasks/542cf1e9-7156-4c4d-9eed-ed63141cf96a |
| Verdict: | No threats detected |
| Analysis date: | August 09, 2019, 02:52:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | AE66BE523EDBE9AC4936E599D61B8D77 |
| SHA1: | 93FDA3E13070BB29B63D36F6971597FED376E4FE |
| SHA256: | F635654319E608A7108E1F483AF41258CB6C5A3B44AC9BB90F9090FC049A4D50 |
| SSDEEP: | 3:N8N1iEB2f8a9czst/FtFFH3zSjiE3dY:2bnIfweTHDOP3dY |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads internet explorer settings
- iexplore.exe (PID: 1496)
Reads Internet Cache Settings
- iexplore.exe (PID: 1496)
Creates files in the user directory
- iexplore.exe (PID: 1496)
Reads settings of System Certificates
- iexplore.exe (PID: 2160)
Changes internet zones settings
- iexplore.exe (PID: 2160)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1496 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2160 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2160 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
422
Read events
340
Write events
80
Delete events
2
Modification events
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {D4A16DD3-BA50-11E9-9885-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307080005000900020035000F00B600 | |||
Executable files
0
Suspicious files
0
Text files
10
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2160 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2160 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1496 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\M25CPTSL\zone[1].php | — | |
MD5:— | SHA256:— | |||
| 1496 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\1Q8MX3WG\25619[1] | text | |
MD5:96CCB7C7DE12E3DD7C567608D126CB57 | SHA256:1676DD6CD23592352935314357B7E6FBA66903C868CE9E20137992B77DD2CCDB | |||
| 1496 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\M25CPTSL\96acb355-693e-4a5c-b863-6480bd39fdc4[1].js | text | |
MD5:0AC34A1E9DD8E53E6A690FAB29C0534F | SHA256:8331943DEFE83C344BABB2116E9C64B88B682725693A9B0698D254638A8863D0 | |||
| 1496 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@leadzutw[1].txt | text | |
MD5:7ECB56BF81AE7BC8935AD19EA839EA82 | SHA256:CFF8522903D42CFE43CCC7AD9E550E92B3F9F2FF6E8CCB53B7660929F5675588 | |||
| 1496 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\index.dat | dat | |
MD5:E96ACAF221831E59B9782B1AAC8A3C84 | SHA256:560550FFE3E407CE6476641A328A55BB921806BBC0D4210C758B366E23C69925 | |||
| 1496 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:9614E4858C74494B1499AD83DB931AE9 | SHA256:6FD609A3A43CA0A52429C03833EE8951BBD736D8EA50047A83A9A4D3A4F19485 | |||
| 1496 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\U9NXVGJJ\632ac0b5-e0b8-49b8-8092-b4853a94fe8f[1].js | text | |
MD5:6EA51FBBB458C4BAD3E3907A10DB522C | SHA256:D9A45DAF53334E9109ADD1B8901009AF7513CB1C1B2418B60A6CD2DA72BEB6DA | |||
| 2160 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019080920190810\index.dat | dat | |
MD5:B8A67251BB3CEDA3CF3FA092681559B9 | SHA256:C25706CF317BC83B11318E2267B44CA07677F3BD495606296AFDF0B3A0CDEDFF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
7
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2160 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2160 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1496 | iexplore.exe | 104.20.10.37:443 | ads.ayads.co | Cloudflare Inc | US | shared |
1496 | iexplore.exe | 51.68.180.203:443 | static.addevweb.com | — | GB | unknown |
1496 | iexplore.exe | 104.20.11.37:443 | ads.ayads.co | Cloudflare Inc | US | shared |
2160 | iexplore.exe | 217.13.124.95:443 | play.leadzutw.com | Com 2002, S.l. | ES | unknown |
1496 | iexplore.exe | 217.13.124.95:443 | play.leadzutw.com | Com 2002, S.l. | ES | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
play.leadzutw.com |
| suspicious |
static.addevweb.com |
| unknown |
ads.ayads.co |
| suspicious |
sac.ayads.co |
| suspicious |
static.sunmedia.tv |
| unknown |