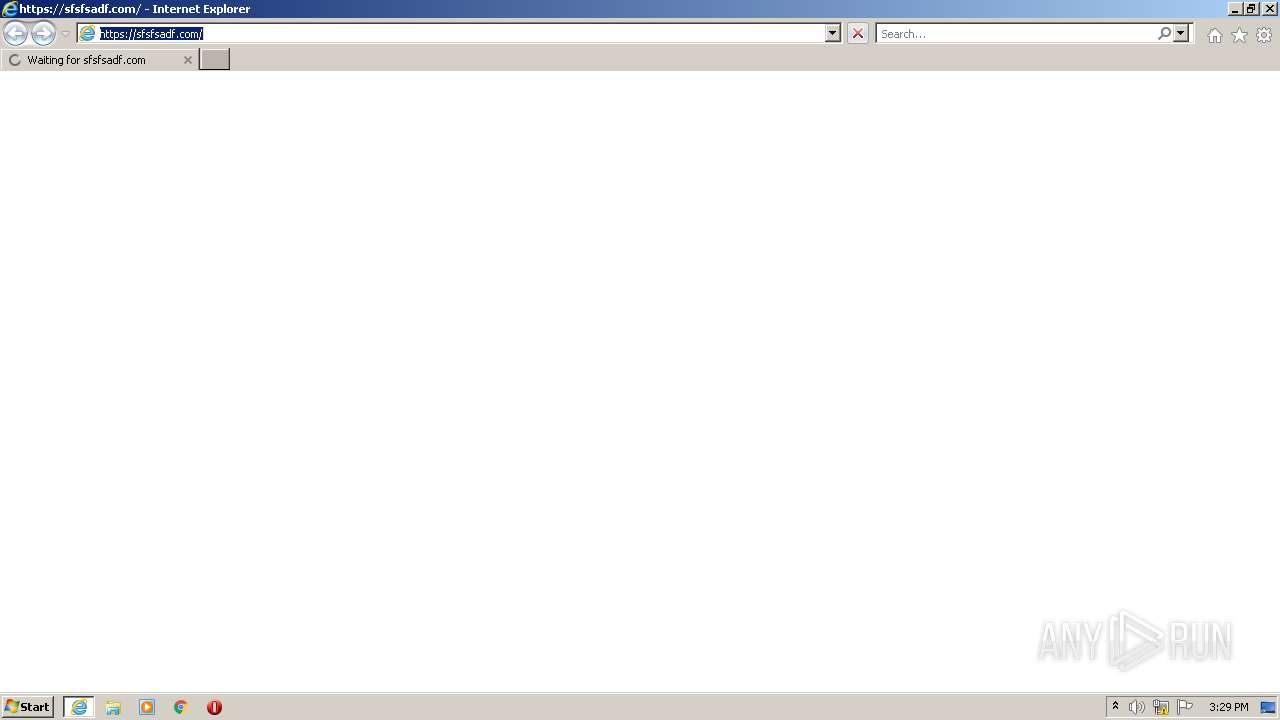
| URL: | https://sfsfsadf.com |
| Full analysis: | https://app.any.run/tasks/a7c4b861-ce53-40e6-a4a4-5e3a8efd46e6 |
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 15:29:44 |
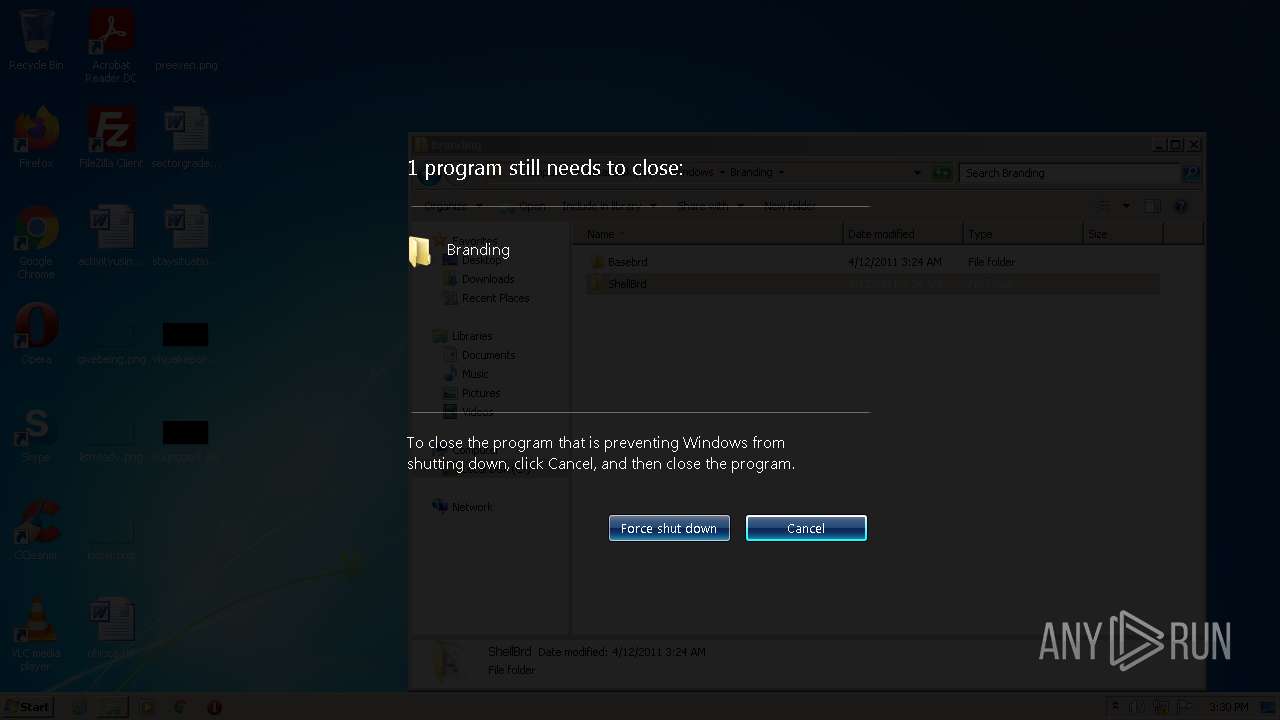
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5F539AB978A7FC9D3F82889873387922 |
| SHA1: | 290E80EB9B3A263CC2B88BA67CA80F1B5B9B0AEE |
| SHA256: | F633ABC890E3D2D0F0B1EA506190F11D3201946BDF37F828487177D9FA511C25 |
| SSDEEP: | 3:N8OWDWE1yKIn:2OEDI |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3728)
Executed via COM
- DllHost.exe (PID: 3416)
- DllHost.exe (PID: 3976)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3088)
Checks supported languages
- iexplore.exe (PID: 3088)
- iexplore.exe (PID: 3728)
- DllHost.exe (PID: 3416)
- DllHost.exe (PID: 3976)
Reads the computer name
- iexplore.exe (PID: 3088)
- iexplore.exe (PID: 3728)
- DllHost.exe (PID: 3416)
- DllHost.exe (PID: 3976)
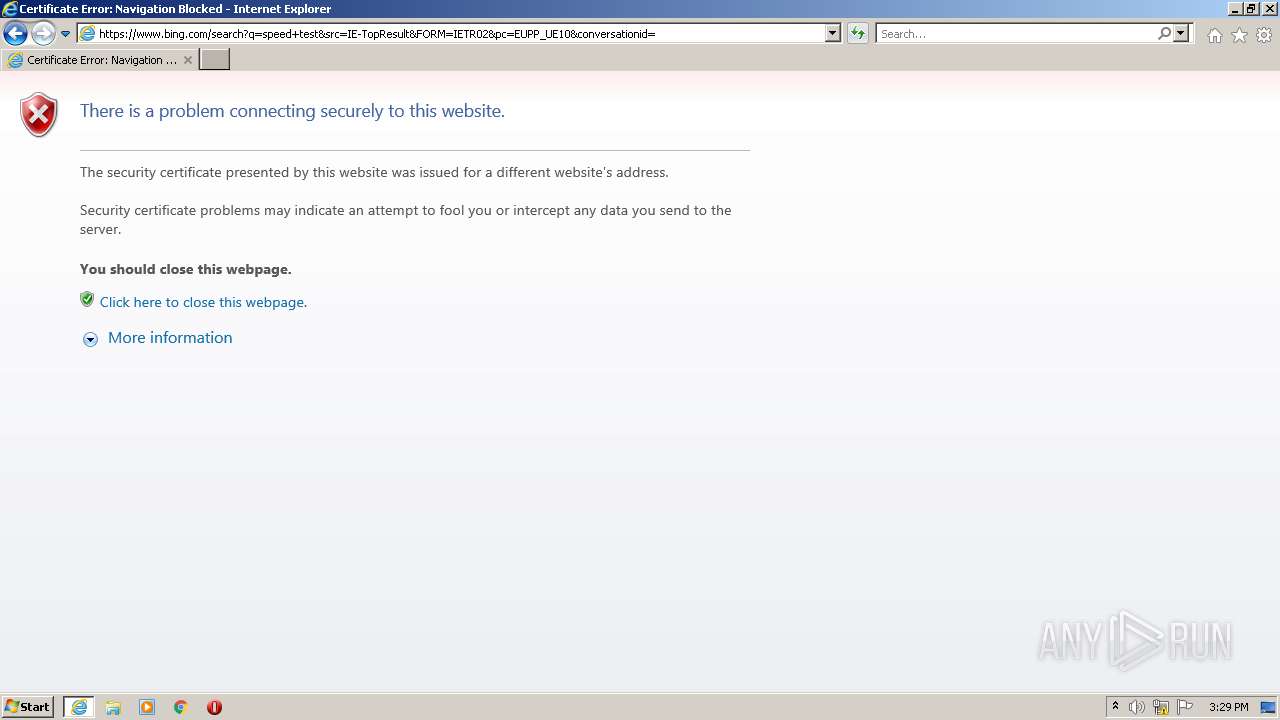
Checks Windows Trust Settings
- iexplore.exe (PID: 3728)
- iexplore.exe (PID: 3088)
Application launched itself
- iexplore.exe (PID: 3088)
Reads settings of System Certificates
- iexplore.exe (PID: 3728)
- iexplore.exe (PID: 3088)
Reads internet explorer settings
- iexplore.exe (PID: 3728)
Reads the date of Windows installation
- iexplore.exe (PID: 3088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
45
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3088 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://sfsfsadf.com" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1073807364 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3416 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3728 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3088 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3976 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 1073807364 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
14 229
Read events
14 129
Write events
98
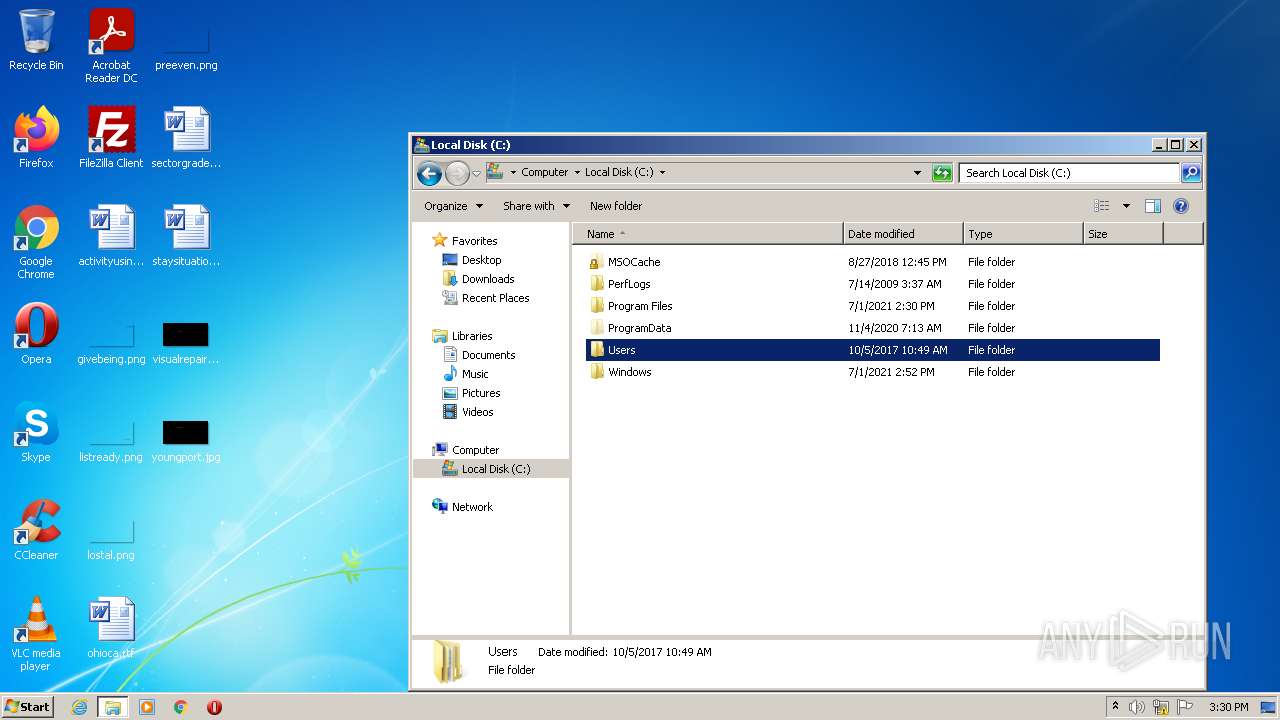
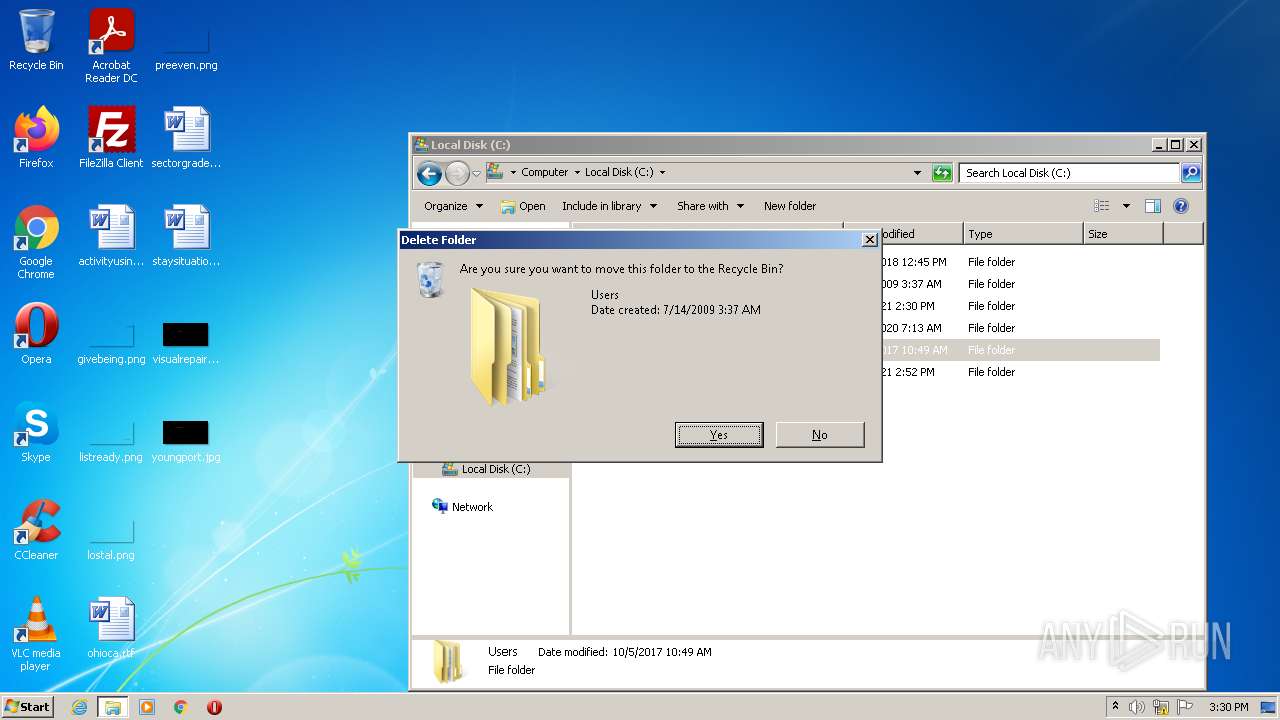
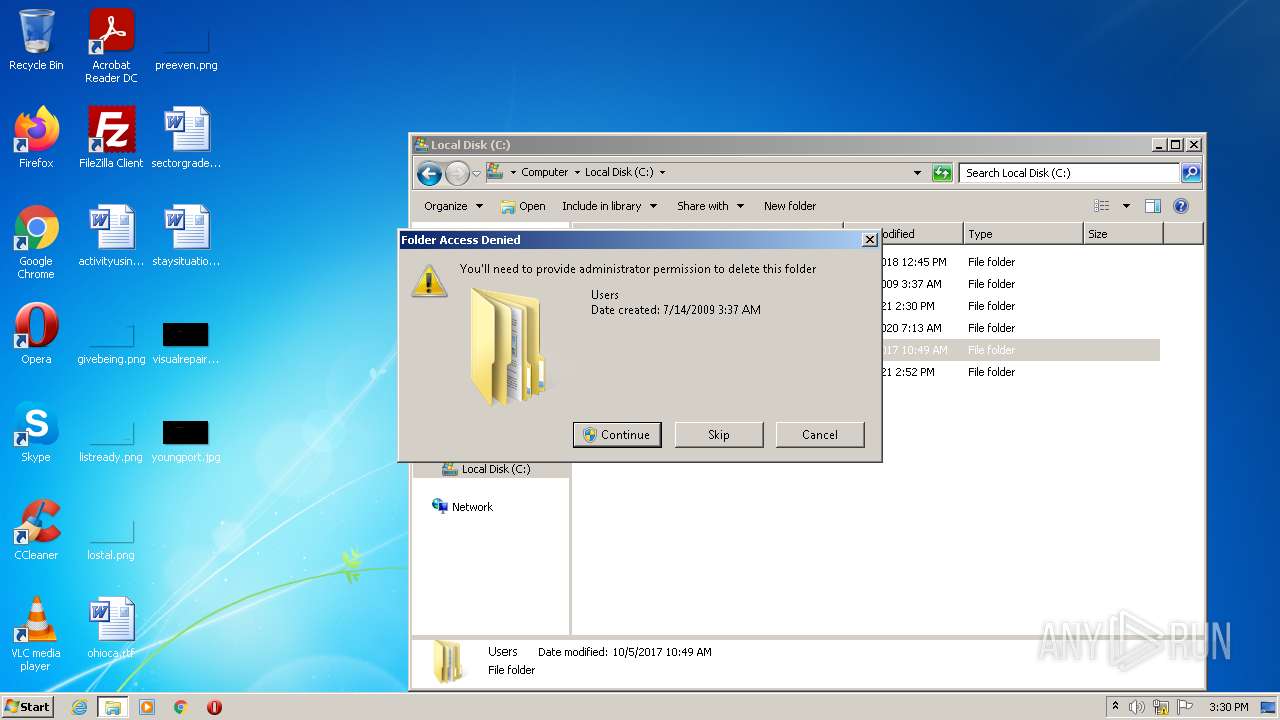
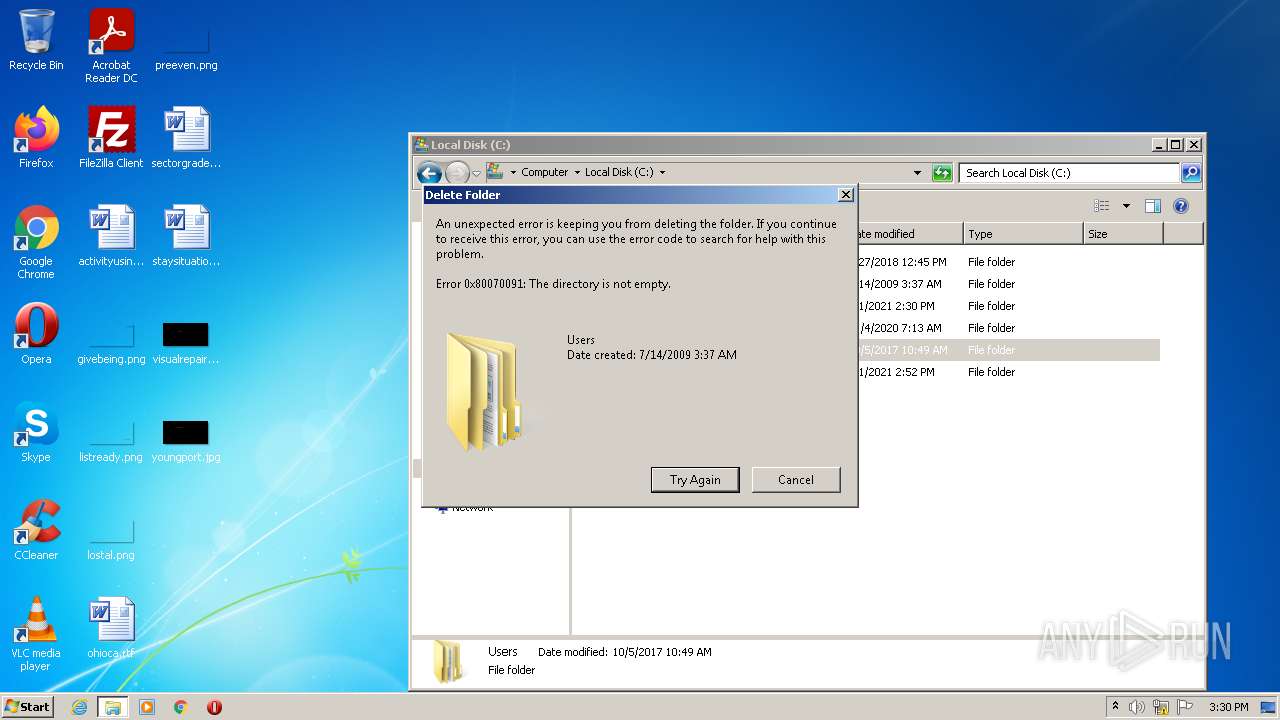
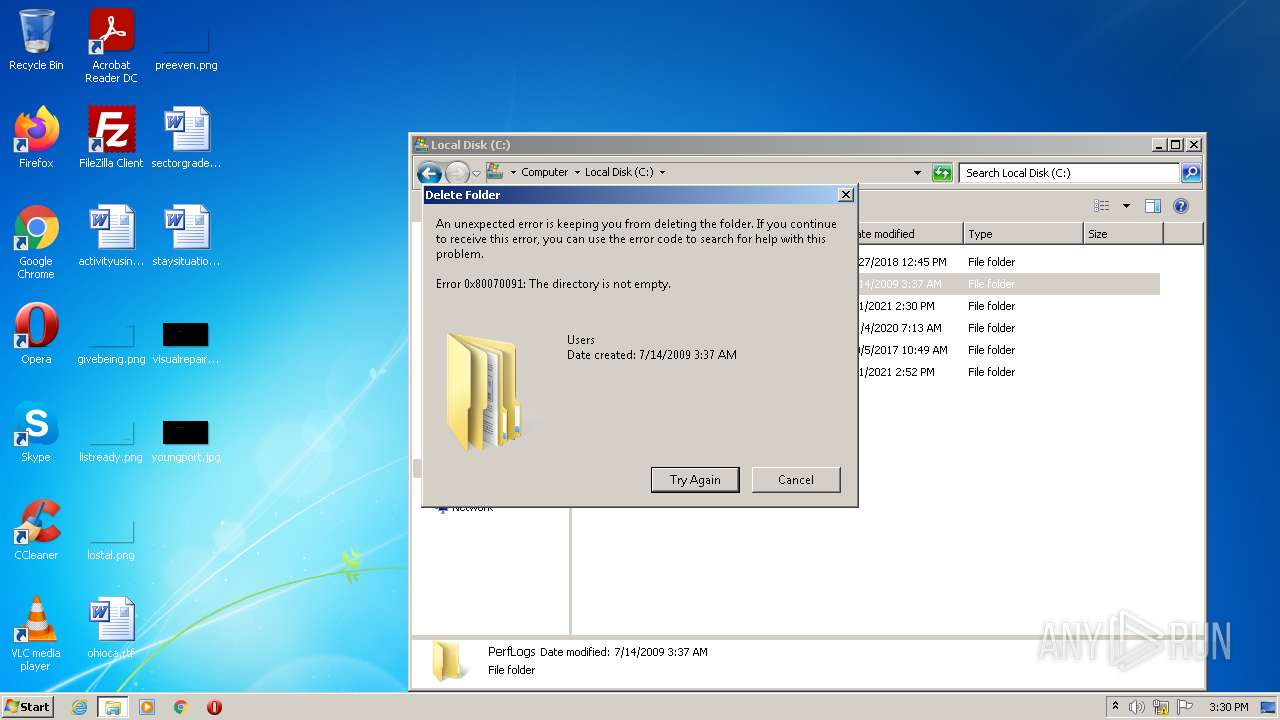
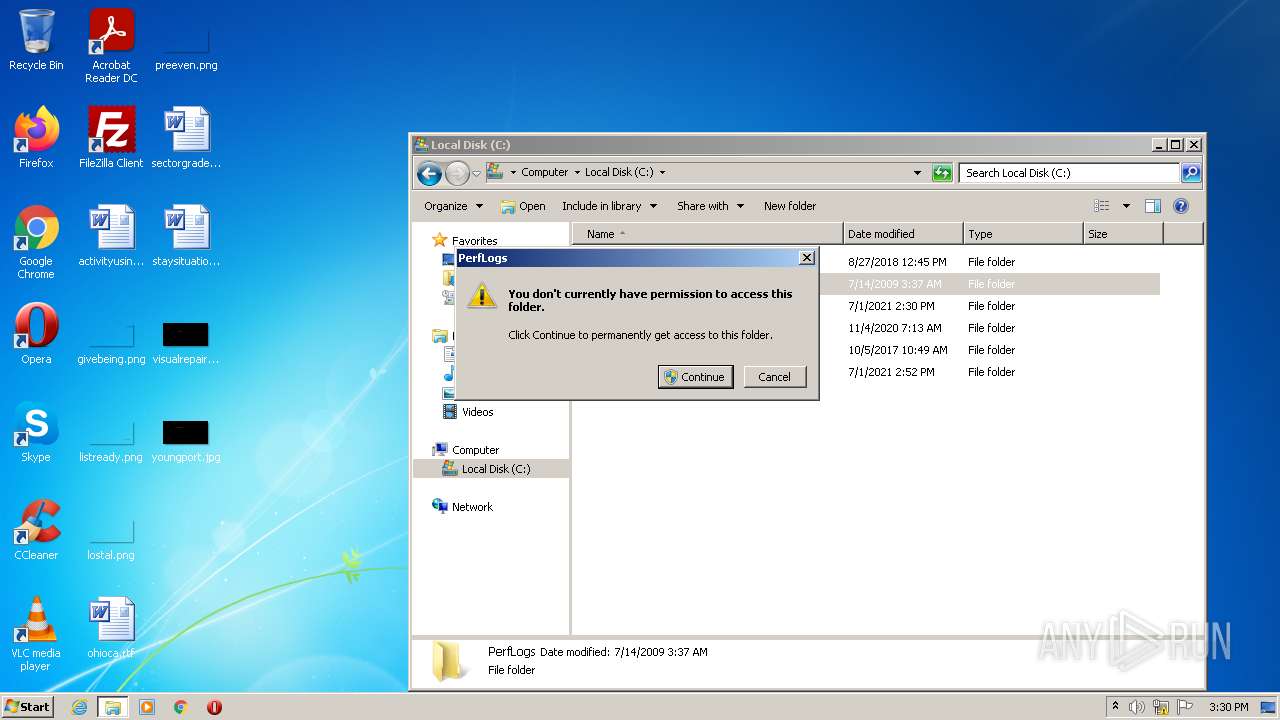
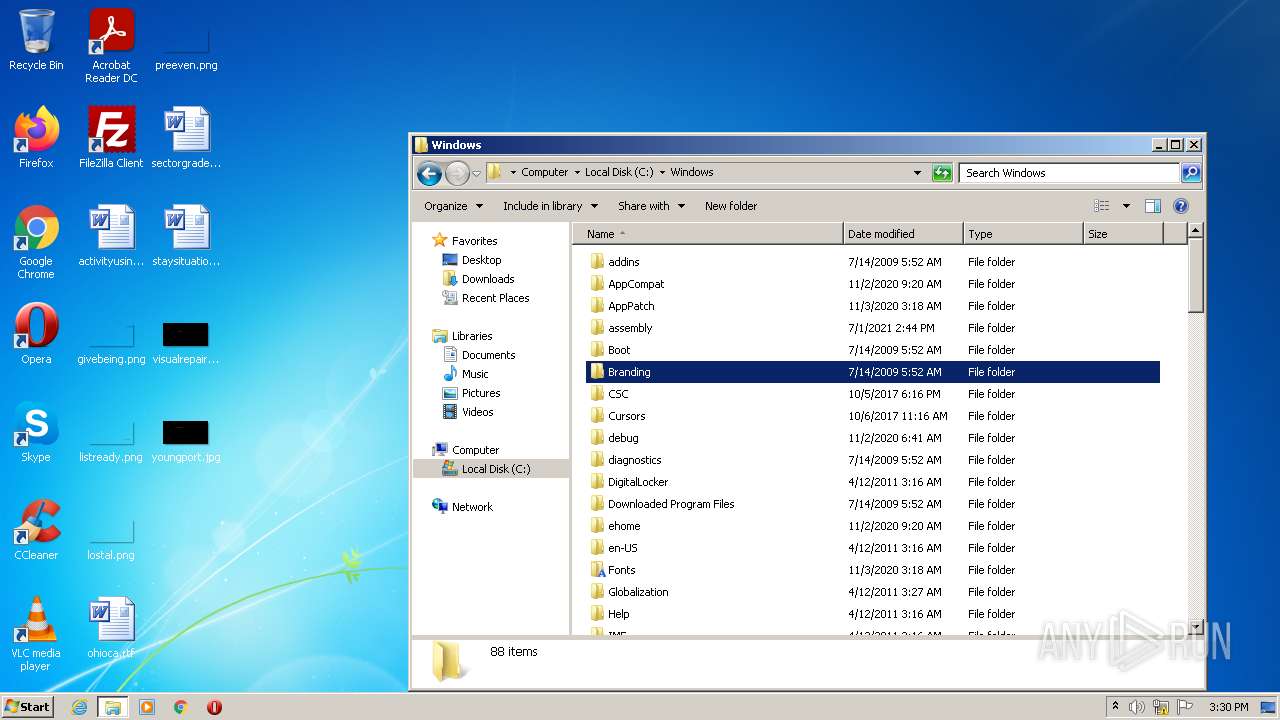
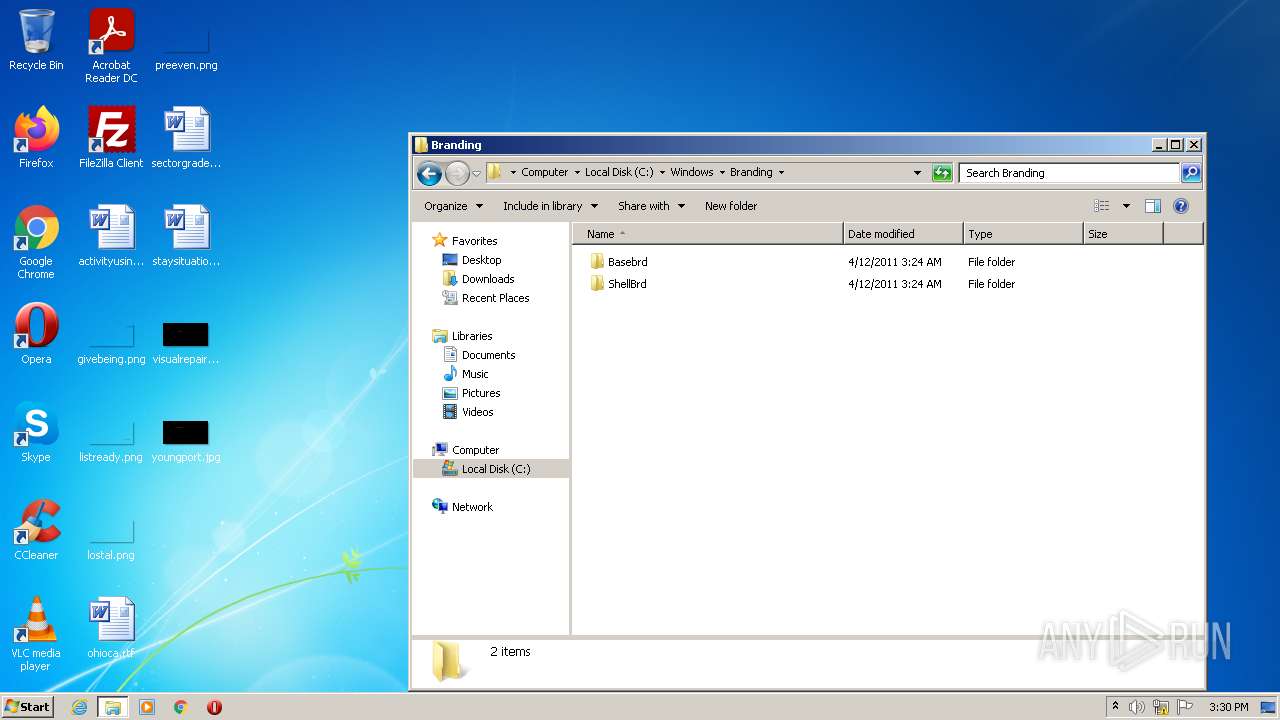
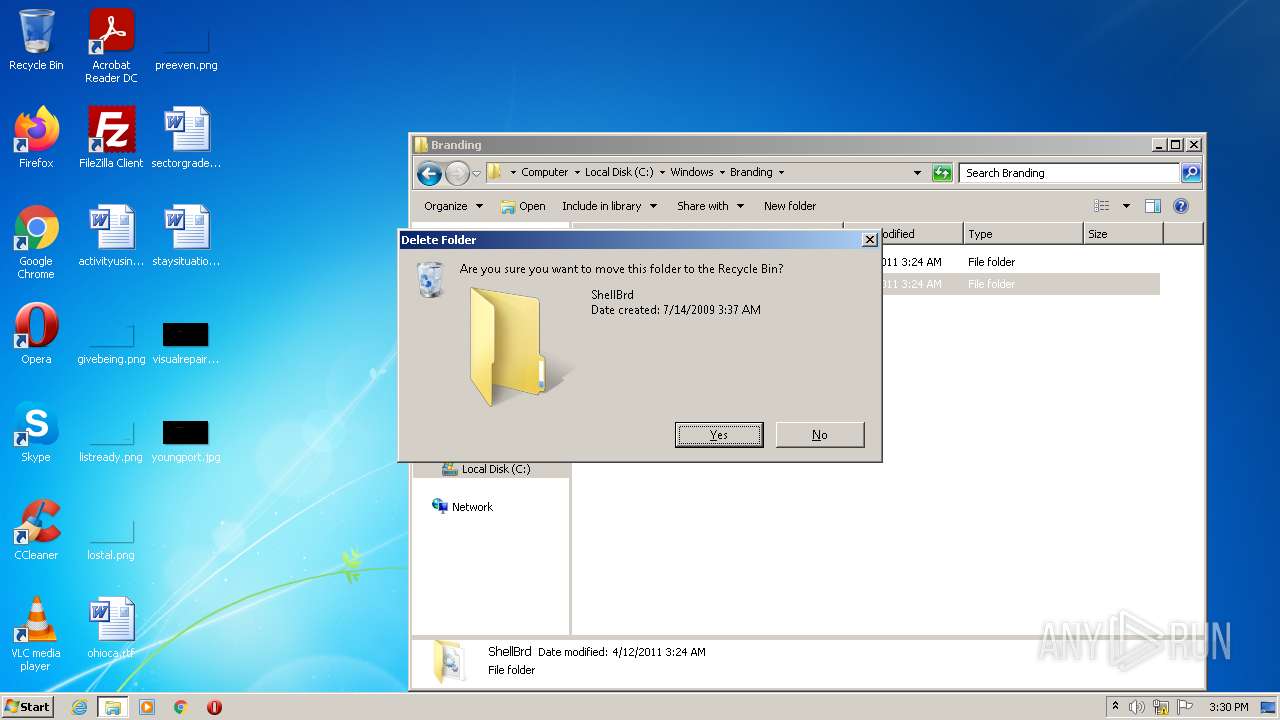
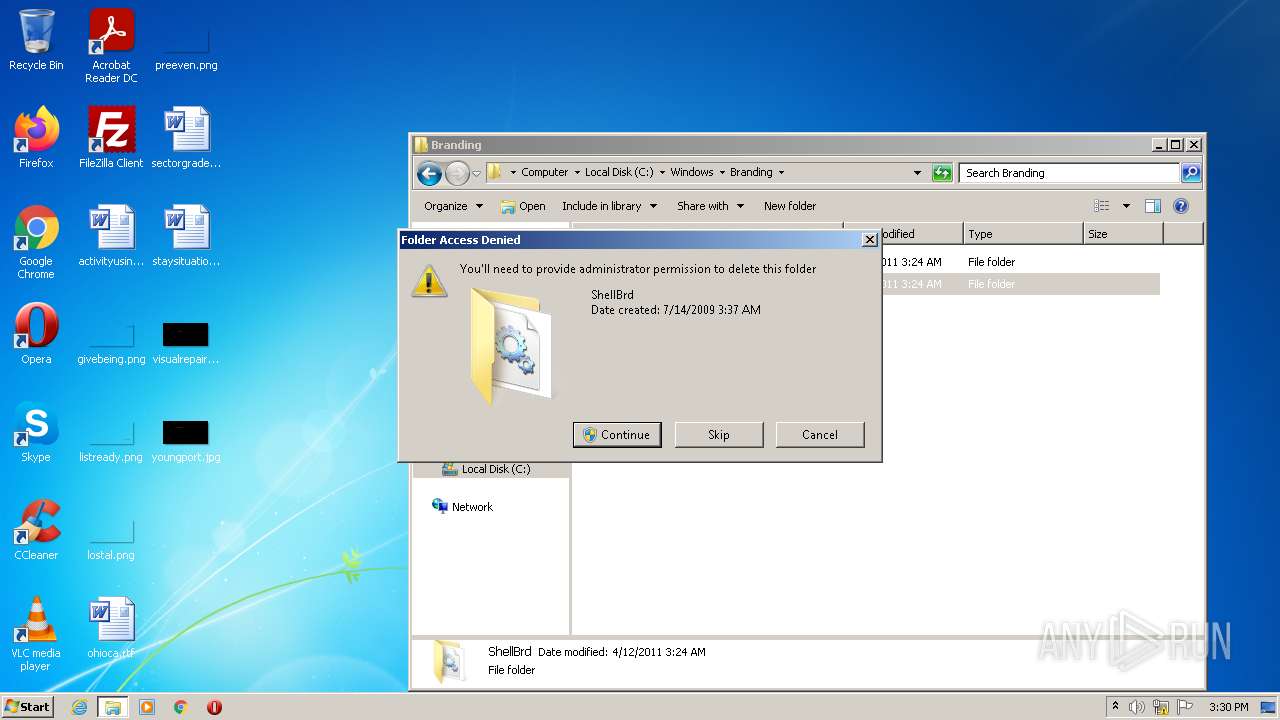
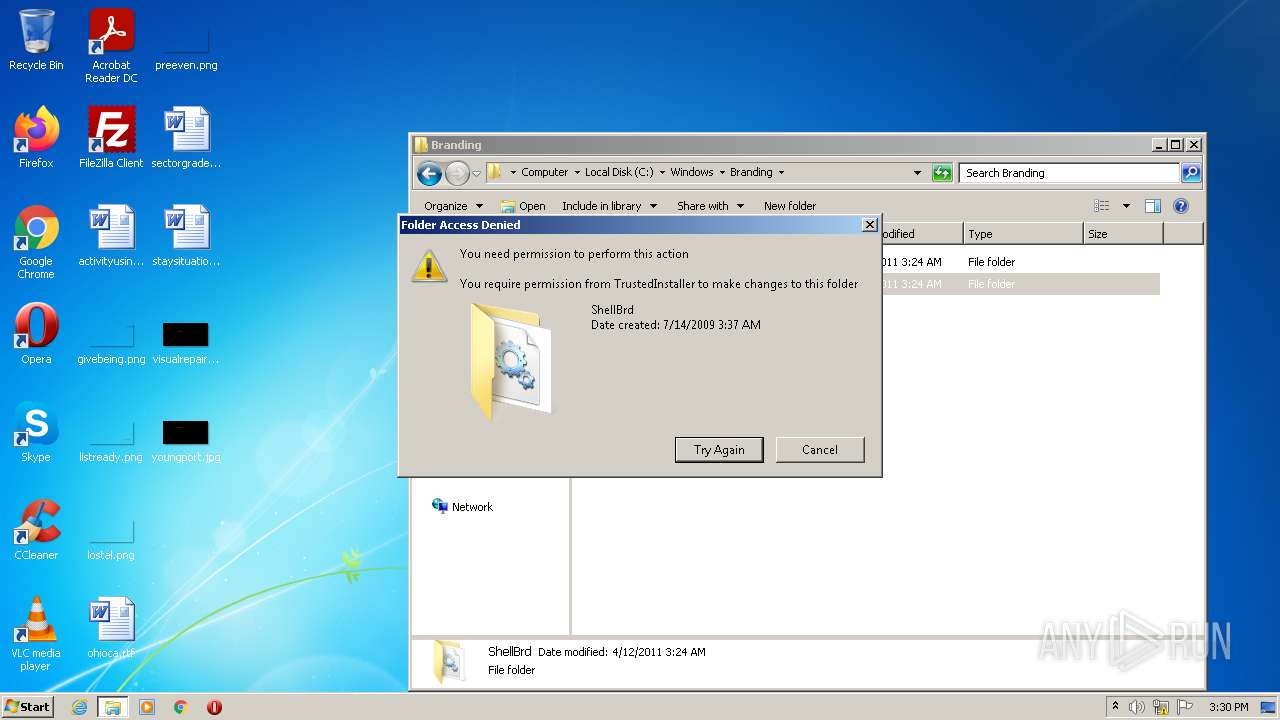
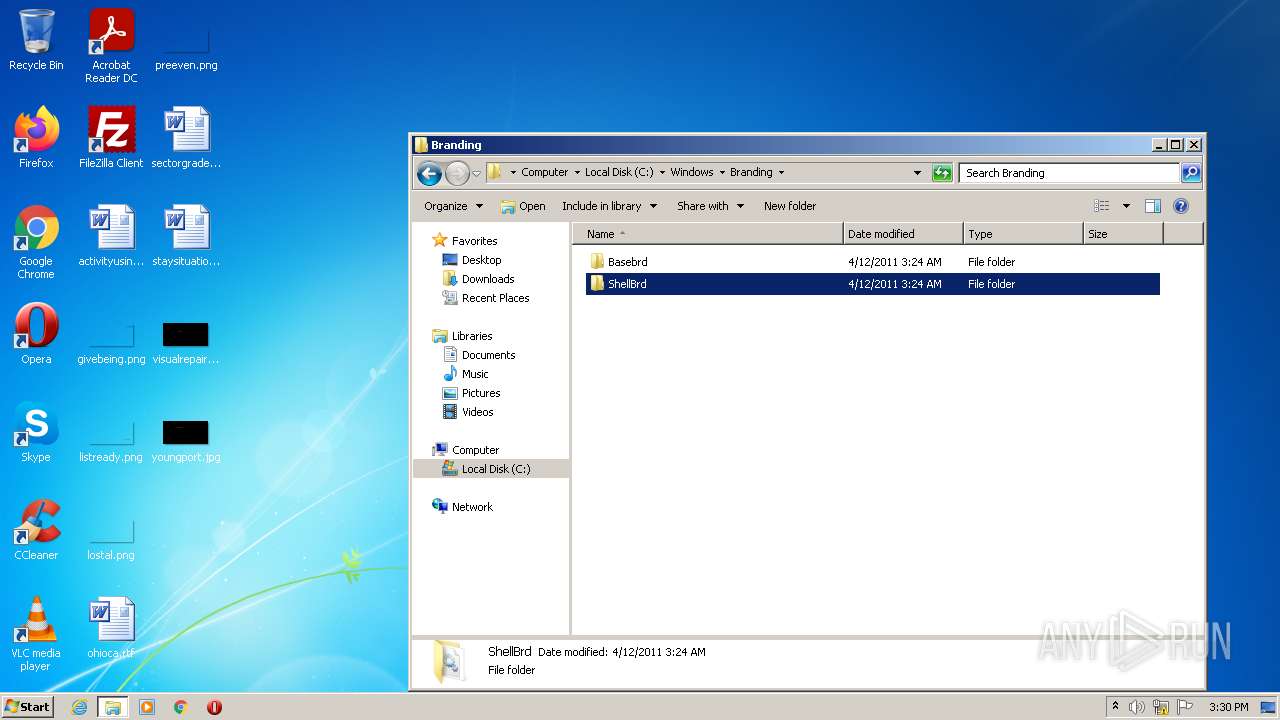
Delete events
2
Modification events
| (PID) Process: | (3088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 950446896 | |||
| (PID) Process: | (3088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30937399 | |||
| (PID) Process: | (3088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30937399 | |||
| (PID) Process: | (3088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
4
Text files
1
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3088 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{7649CFD1-7D2A-11EC-A45D-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3088 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFA04478D31E346618.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3088 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\{7649CFD4-7D2A-11EC-A45D-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3088 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{42C873D0-1D90-11EB-BA2C-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3088 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFA3C0C3F15A5AD0A0.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3088 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{7649CFD3-7D2A-11EC-A45D-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3088 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF50F8BC3849429380.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3088 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\StructuredQuery.log | text | |
MD5:1CDF4E86C1CDA95A0E6A6DC20A2712ED | SHA256:A4A9B991428C356A6CB95C1EA2EB47CE0573A22416B4371187F1AA7E1C24820C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
28
DNS requests
6
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
364 | svchost.exe | GET | 404 | 67.27.233.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?05ae3aeb768d9571 | US | xml | 341 b | whitelisted |
3728 | iexplore.exe | GET | 404 | 67.27.233.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?58ec6aeeafa85f96 | US | xml | 341 b | whitelisted |
3088 | iexplore.exe | GET | 404 | 67.27.233.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?15d924fd7b8b52ce | US | xml | 341 b | whitelisted |
3088 | iexplore.exe | GET | 404 | 67.27.233.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a53a6cc97fb8ab6b | US | xml | 341 b | whitelisted |
3088 | iexplore.exe | GET | 404 | 67.27.233.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?474448c0b713d8ba | US | xml | 341 b | whitelisted |
3728 | iexplore.exe | GET | 404 | 67.27.233.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d68f4ae558fb6517 | US | xml | 341 b | whitelisted |
3088 | iexplore.exe | GET | 404 | 67.27.233.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?81b7bc6a738bcca7 | US | xml | 341 b | whitelisted |
3728 | iexplore.exe | GET | 404 | 67.27.233.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?93a388791bae1293 | US | xml | 341 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
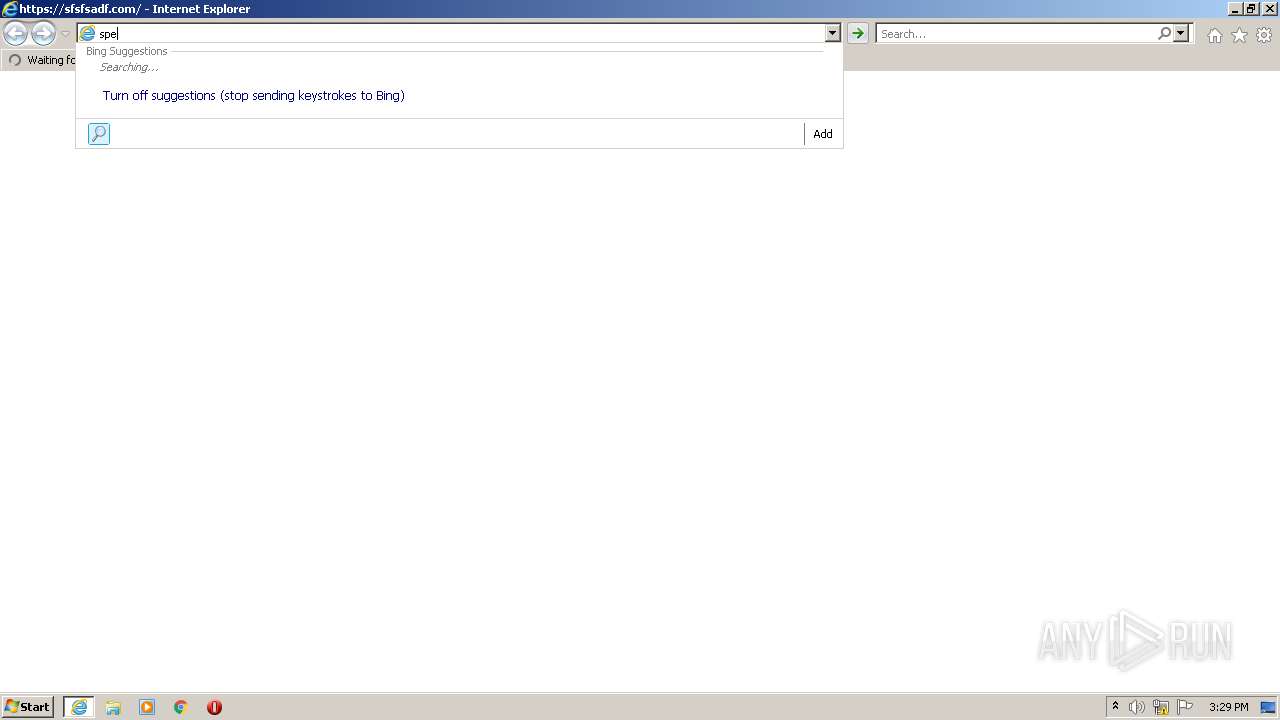
3728 | iexplore.exe | 13.107.5.80:443 | api.bing.com | Microsoft Corporation | US | whitelisted |
3728 | iexplore.exe | 67.27.233.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3728 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3088 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3088 | iexplore.exe | 67.27.233.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3088 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
364 | svchost.exe | 67.27.233.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sfsfsadf.com |
| unknown |
api.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
Threats
8 ETPRO signatures available at the full report