| File name: | COVID-19.exe |
| Full analysis: | https://app.any.run/tasks/31756dda-5dc8-41b6-a279-f6954d40c956 |
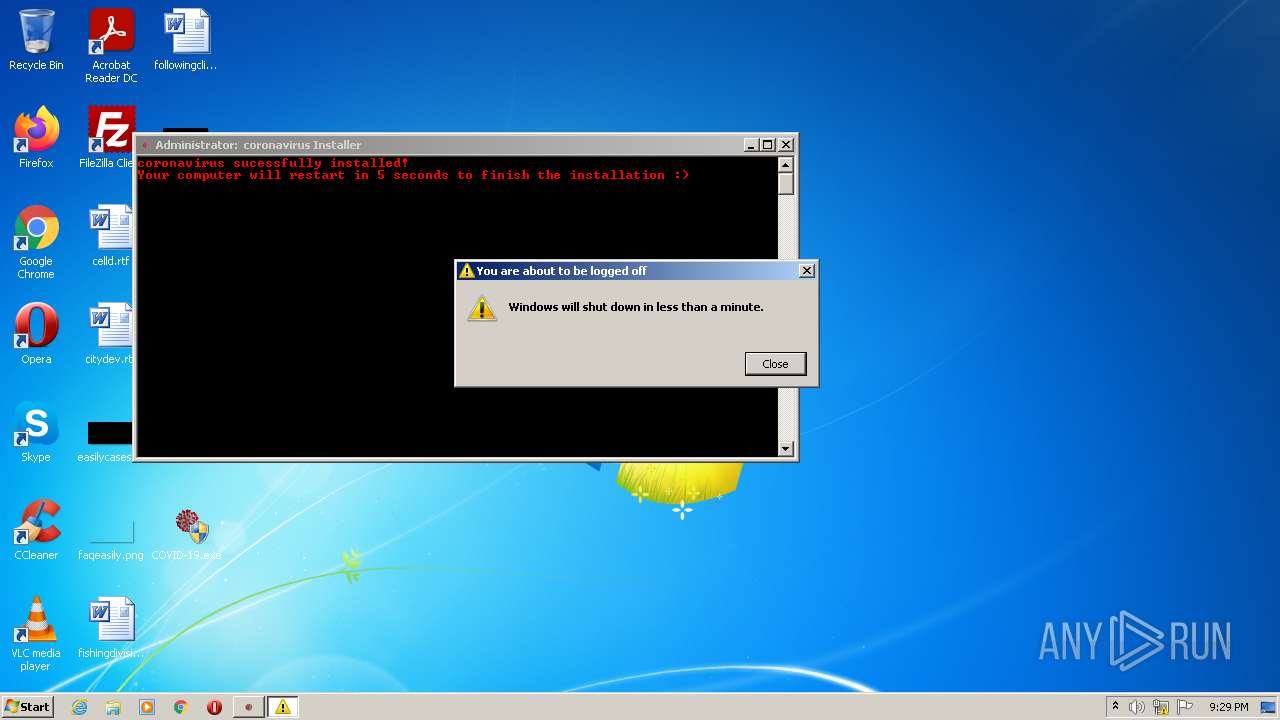
| Verdict: | Malicious activity |
| Analysis date: | July 05, 2022, 20:29:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows, UPX compressed |
| MD5: | E20EE9BBBD1EBE131F973FE3706CA799 |
| SHA1: | 4E92E5CBE9092F94B4F4951893B5D9CA304D292C |
| SHA256: | F632B6E822D69FB54B41F83A357FF65D8BFC67BC3E304E88BF4D9F0C4AEDC224 |
| SSDEEP: | 6144:egtJZ0NSt7Jb/Is8vIfYg6KcZQV7GdRMrKUIvcgfoS3Qz89r:egWNStd7R8cYgsZK7qCrqfoS3Mcr |
MALICIOUS
Drops executable file immediately after starts
- cmd.exe (PID: 1448)
- COVID-19.exe (PID: 3368)
UAC/LUA settings modification
- reg.exe (PID: 1004)
Task Manager has been disabled (taskmgr)
- reg.exe (PID: 3616)
Changes the autorun value in the registry
- reg.exe (PID: 776)
- reg.exe (PID: 2312)
- reg.exe (PID: 3808)
SUSPICIOUS
Starts CMD.EXE for commands execution
- COVID-19.exe (PID: 3368)
Checks supported languages
- COVID-19.exe (PID: 3368)
- cmd.exe (PID: 1448)
Executable content was dropped or overwritten
- COVID-19.exe (PID: 3368)
- cmd.exe (PID: 1448)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 1448)
Drops a file with a compile date too recent
- COVID-19.exe (PID: 3368)
- cmd.exe (PID: 1448)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 1448)
INFO
Drops Coronavirus (possible) decoy
- COVID-19.exe (PID: 3368)
Checks supported languages
- attrib.exe (PID: 3312)
- reg.exe (PID: 3832)
- reg.exe (PID: 3940)
- reg.exe (PID: 3616)
- reg.exe (PID: 1004)
- reg.exe (PID: 4040)
- reg.exe (PID: 2092)
- reg.exe (PID: 1252)
- reg.exe (PID: 776)
- reg.exe (PID: 3808)
- shutdown.exe (PID: 2432)
- reg.exe (PID: 2312)
Reads the computer name
- shutdown.exe (PID: 2432)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| ProductVersion: | 1,0,0,0 |
|---|---|
| InternalName: | COVID-19.exe |
| FileVersion: | 1,0,0,0 |
| FileDescription: | coronavirus Installer |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows 16-bit |
| FileFlags: | Debug, Pre-release, Private build |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows command line |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x5c7b0 |
| UninitializedDataSize: | 167936 |
| InitializedDataSize: | 86016 |
| CodeSize: | 212992 |
| LinkerVersion: | 2.5 |
| PEType: | PE32 |
| TimeStamp: | 2009:02:07 07:33:02+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 07-Feb-2009 06:33:02 |
| Detected languages: |
|
| FileDescription: | coronavirus Installer |
| FileVersion: | 1,0,0,0 |
| InternalName: | COVID-19.exe |
| ProductVersion: | 1,0,0,0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 07-Feb-2009 06:33:02 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00029000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x0002A000 | 0x00034000 | 0x00033400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.9977 |
.rsrc | 0x0005E000 | 0x00015000 | 0x00014400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.98509 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.09999 | 668 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 7.96409 | 12966 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 7.97927 | 36624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 3.18049 | 296 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 2.9769 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 2.61669 | 1640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 2.10093 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 4.19124 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 3.76716 | 3752 | Latin 1 / Western European | UNKNOWN | RT_ICON |
10 | 2.93898 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
COMCTL32.dll |
GDI32.dll |
KERNEL32.DLL |
MSVCRT.dll |
OLE32.dll |
SHELL32.dll |
USER32.dll |
Total processes
54
Monitored processes
15
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 776 | reg.exe ADD HKLM\Software\Microsoft\Windows\CurrentVersion\Run /v CheckForUpdates /t REG_SZ /d C:\COVID-19\Update.vbs /f | C:\Windows\system32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1004 | reg.exe ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System /v EnableLUA /t REG_DWORD /d 0 /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1252 | reg.exe ADD HKCU\Control Panel\Cursors /v Hand /t REG_SZ /d C:\COVID-19\cursor.cur /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1448 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\5F3D.tmp\coronavirus.bat"" | C:\Windows\system32\cmd.exe | COVID-19.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2092 | reg.exe ADD HKCU\Control Panel\Cursors /v AppStarting /t REG_SZ /d C:\COVID-19\cursor.cur /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2312 | reg.exe ADD HKLM\Software\Microsoft\Windows\CurrentVersion\Run /v explorer.exe /t REG_SZ /d C:\COVID-19\run.exe /f | C:\Windows\system32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2432 | shutdown -r -t 5 | C:\Windows\system32\shutdown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2624 | "C:\Users\admin\Desktop\COVID-19.exe" | C:\Users\admin\Desktop\COVID-19.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3312 | attrib +H C:\COVID-19 | C:\Windows\system32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3368 | "C:\Users\admin\Desktop\COVID-19.exe" | C:\Users\admin\Desktop\COVID-19.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
111
Read events
104
Write events
7
Delete events
0
Modification events
| (PID) Process: | (3616) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | disabletaskmgr |
Value: 1 | |||
| (PID) Process: | (1004) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 0 | |||
| (PID) Process: | (3832) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | wallpaper |
Value: C:\COVID-19\wallpaper.jpg | |||
| (PID) Process: | (3940) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\ActiveDesktop |
| Operation: | write | Name: | NoChangingWallPaper |
Value: 1 | |||
| (PID) Process: | (776) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | CheckForUpdates |
Value: C:\COVID-19\Update.vbs | |||
| (PID) Process: | (2312) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | explorer.exe |
Value: C:\COVID-19\run.exe | |||
| (PID) Process: | (3808) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | GoodbyePC! |
Value: C:\COVID-19\end.exe | |||
Executable files
6
Suspicious files
0
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3368 | COVID-19.exe | C:\Users\admin\Desktop\cursor.cur | image | |
MD5:21F48A9E113317B8E2B3CE5366621AA1 | SHA256:13C4423ED872E71990E703A21174847AB58DEC49501B186709B77B772CEEAB52 | |||
| 3368 | COVID-19.exe | C:\Users\admin\Desktop\run.exe | executable | |
MD5:B1349CA048B6B09F2B8224367FDA4950 | SHA256:C46C3D2BEA1E42B628D6988063D247918F3F8B69B5A1C376028A2A0CADD53986 | |||
| 1448 | cmd.exe | C:\COVID-19\mainWindow.exe | executable | |
MD5:E6CCC960AE38768664E8CF40C74A9902 | SHA256:B780E24E14885C6AB836AAE84747AA0D975017F5FC5B7F031D51C7469793EABE | |||
| 1448 | cmd.exe | C:\COVID-19\run.exe | executable | |
MD5:B1349CA048B6B09F2B8224367FDA4950 | SHA256:C46C3D2BEA1E42B628D6988063D247918F3F8B69B5A1C376028A2A0CADD53986 | |||
| 1448 | cmd.exe | C:\COVID-19\cursor.cur | image | |
MD5:21F48A9E113317B8E2B3CE5366621AA1 | SHA256:13C4423ED872E71990E703A21174847AB58DEC49501B186709B77B772CEEAB52 | |||
| 3368 | COVID-19.exe | C:\Users\admin\Desktop\wallpaper.jpg | image | |
MD5:087F4545E13BD7B8E1F36C941A62F8A4 | SHA256:4A17F58A8BF2B26ECE23B4D553D46B72E0CDA5E8668458A80CE8FE4E6D90C42D | |||
| 3368 | COVID-19.exe | C:\Users\admin\Desktop\Update.vbs | text | |
MD5:BFBAFDF20DADF4E83476228F2F86E80C | SHA256:A1A8D79508173CF16353E31A236D4A211BDCEDEF53791ACCE3CFBA600B51AAEC | |||
| 1448 | cmd.exe | C:\COVID-19\wallpaper.jpg | image | |
MD5:087F4545E13BD7B8E1F36C941A62F8A4 | SHA256:4A17F58A8BF2B26ECE23B4D553D46B72E0CDA5E8668458A80CE8FE4E6D90C42D | |||
| 3368 | COVID-19.exe | C:\Users\admin\Desktop\end.exe | executable | |
MD5:7DEF1C942EEA4C2024164CD5B7970EC8 | SHA256:C3F11936FE43D62982160A876CC000F906CB34BB589F4E76E54D0A5589B2FDB9 | |||
| 3368 | COVID-19.exe | C:\Users\admin\AppData\Local\Temp\5F3D.tmp\coronavirus.bat | text | |
MD5:E9B2F5E9305DC2A39258D69264647C53 | SHA256:4FD9B85EEC0B49548C462ACB9EC831A0728C0EF9E3DE70E772755834E38AA3B3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report