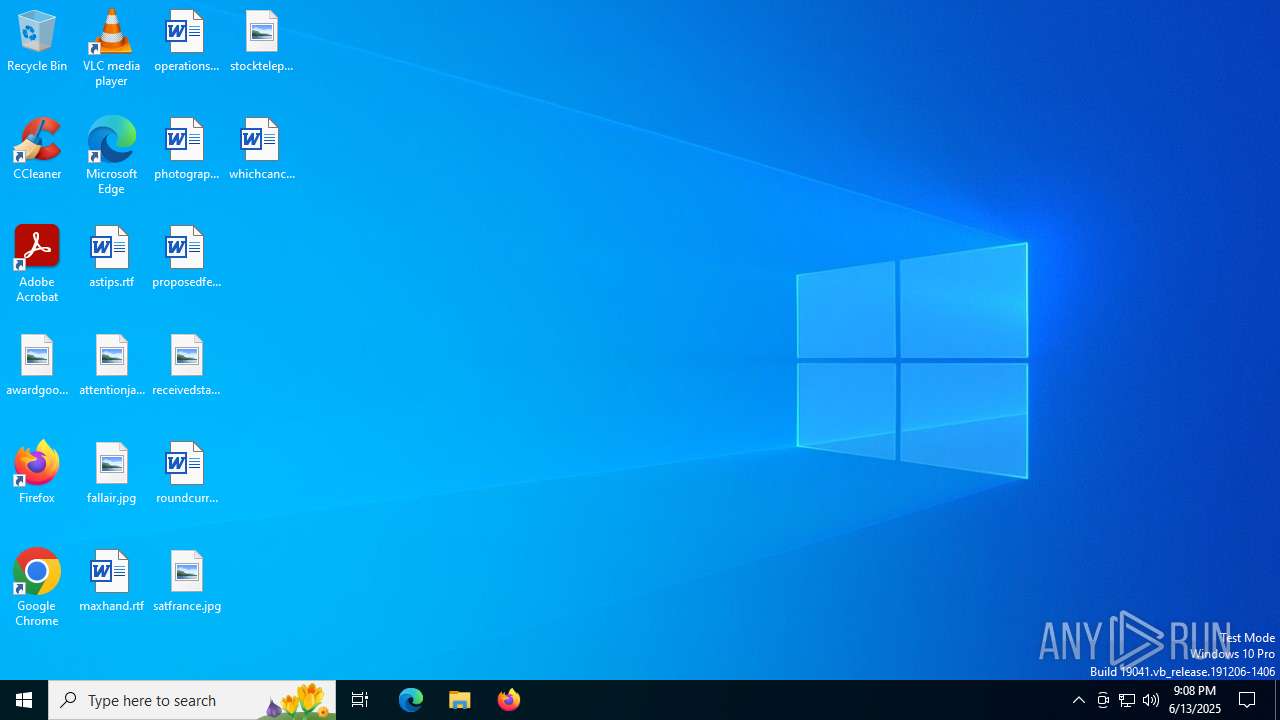
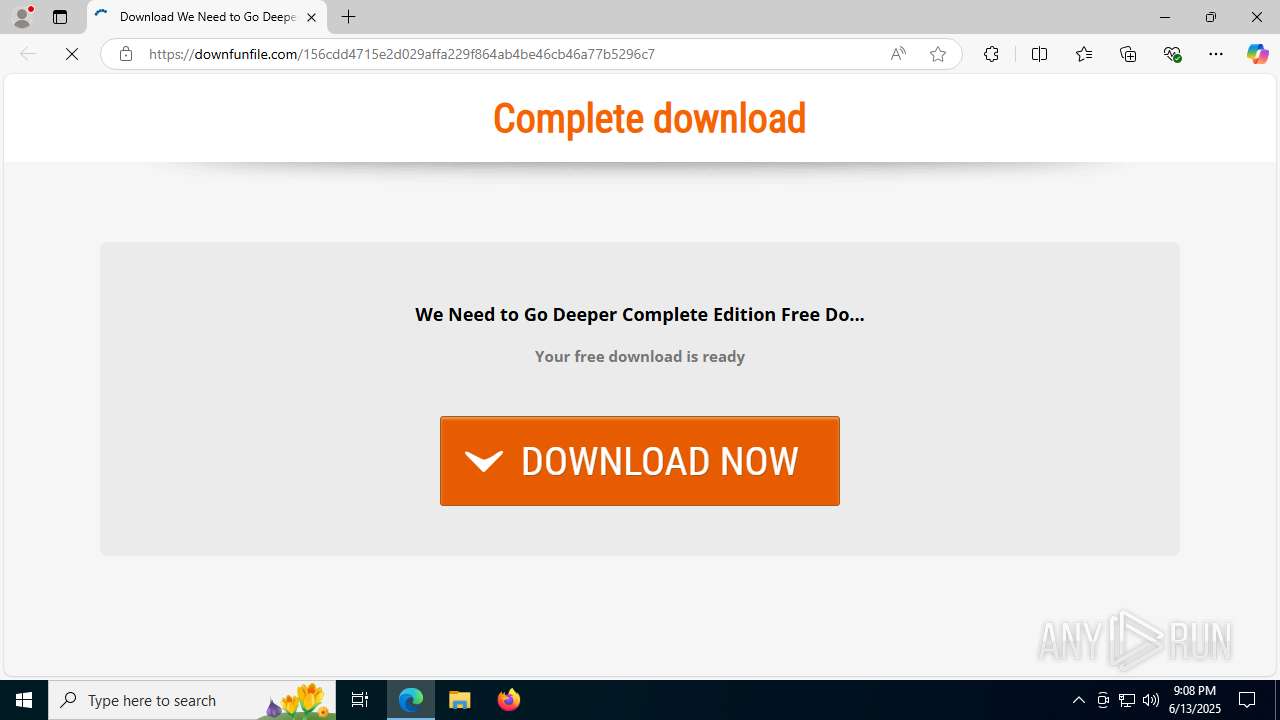
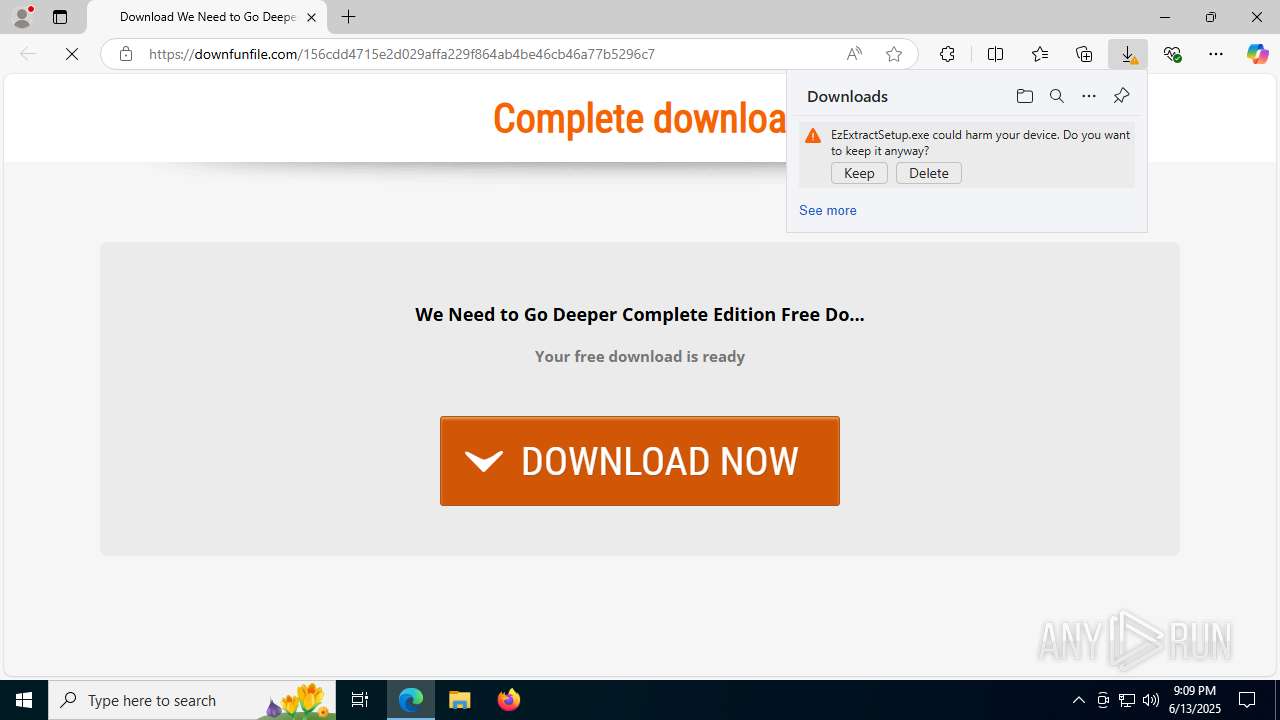
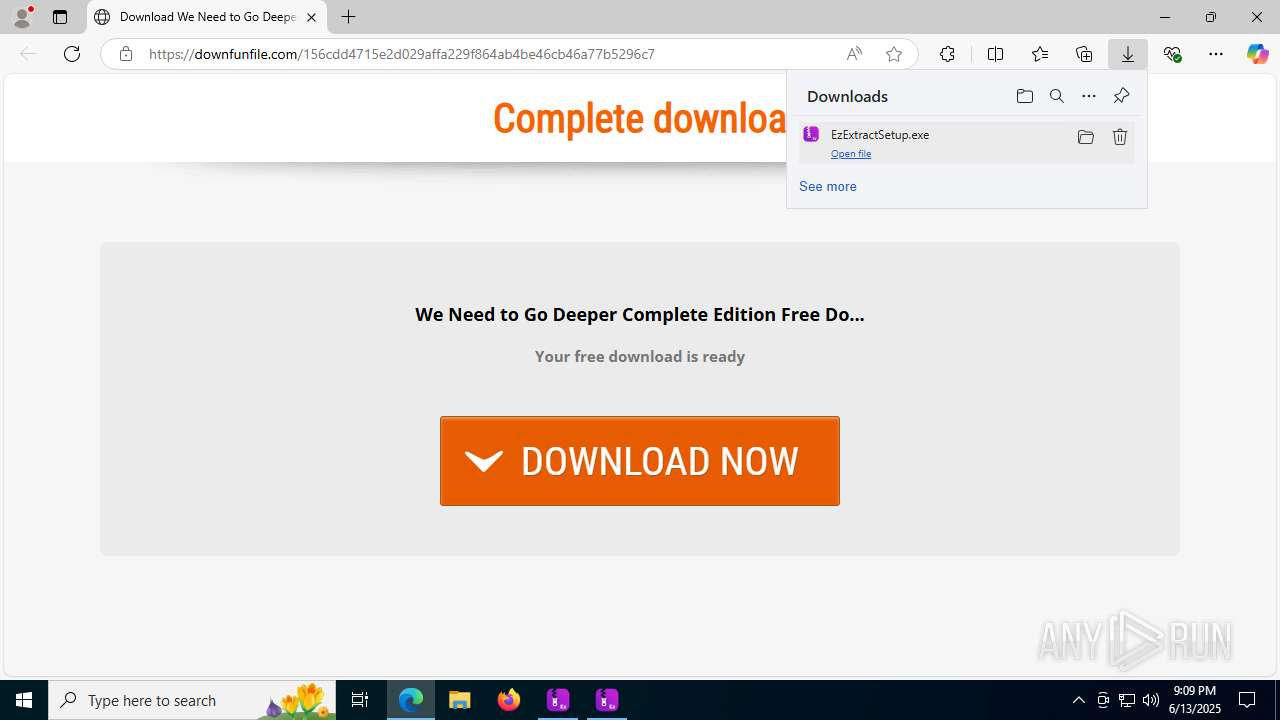
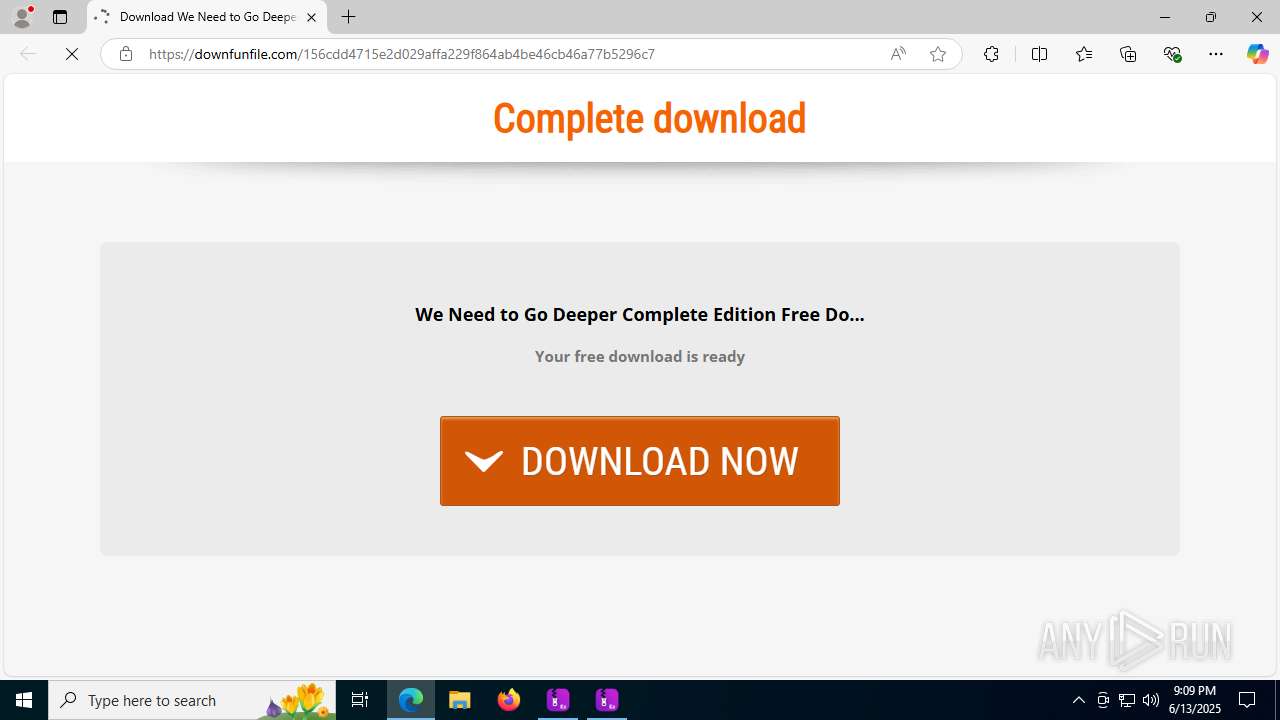
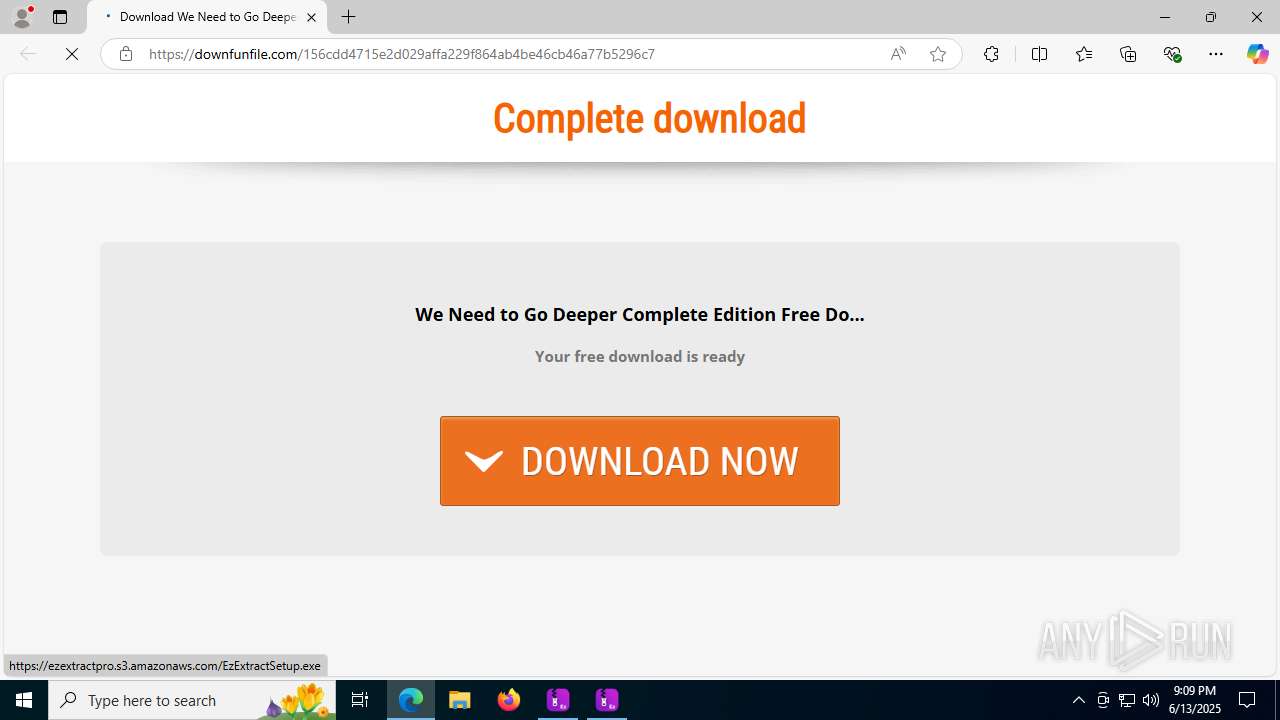
| URL: | https://downfunfile.com/156cdd4715e2d029affa229f864ab4be46cb46a77b5296c7 |
| Full analysis: | https://app.any.run/tasks/8f45cbaa-68af-4f66-98f0-99d014ae60fe |
| Verdict: | Malicious activity |
| Analysis date: | June 13, 2025, 21:08:49 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 19269793716F8BED6F350F89C5B0D533 |
| SHA1: | EB93F71D25FAEA15F41C176D235731052A32197E |
| SHA256: | F62E3D8A8F53BB4176DFBD2662E332D127825E7F89470857345430B095597541 |
| SSDEEP: | 3:N8SOrAyMTaVFfEHyRqARKxKbF:2SAJS2oyRqAGoF |
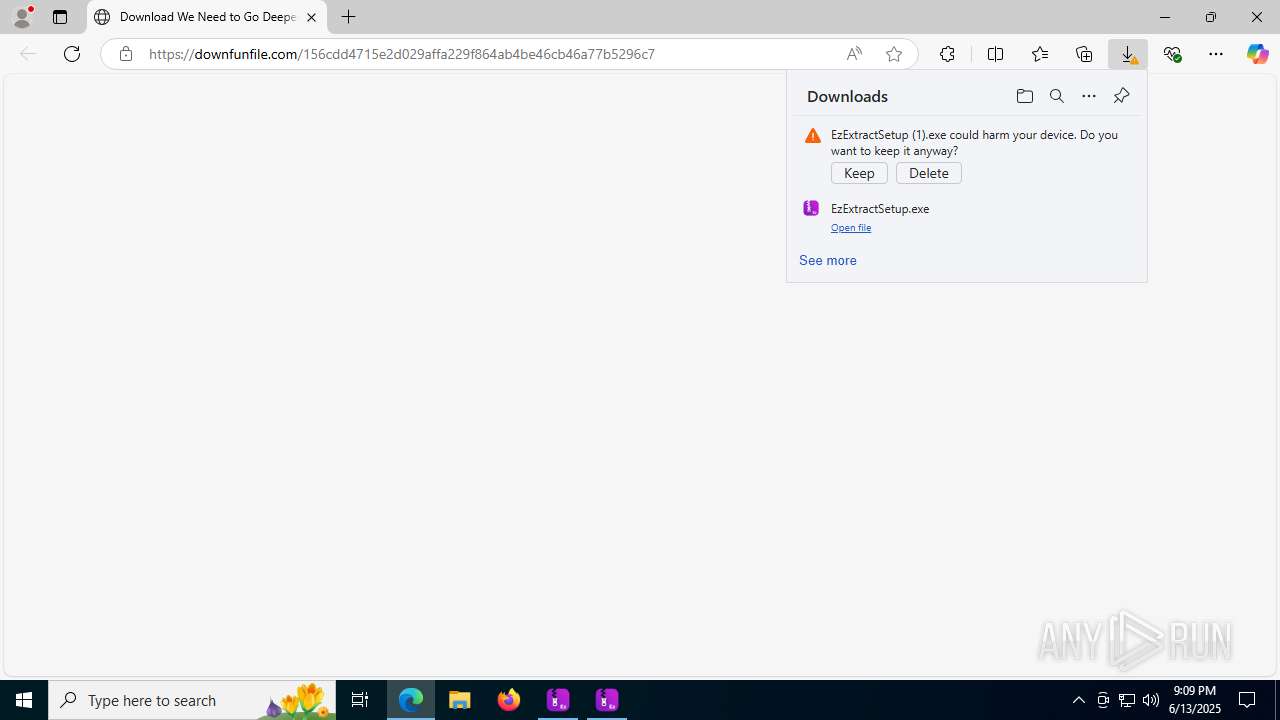
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- EzExtractSetup.exe (PID: 3948)
The DLL Hijacking
- regsvr32.exe (PID: 6876)
SUSPICIOUS
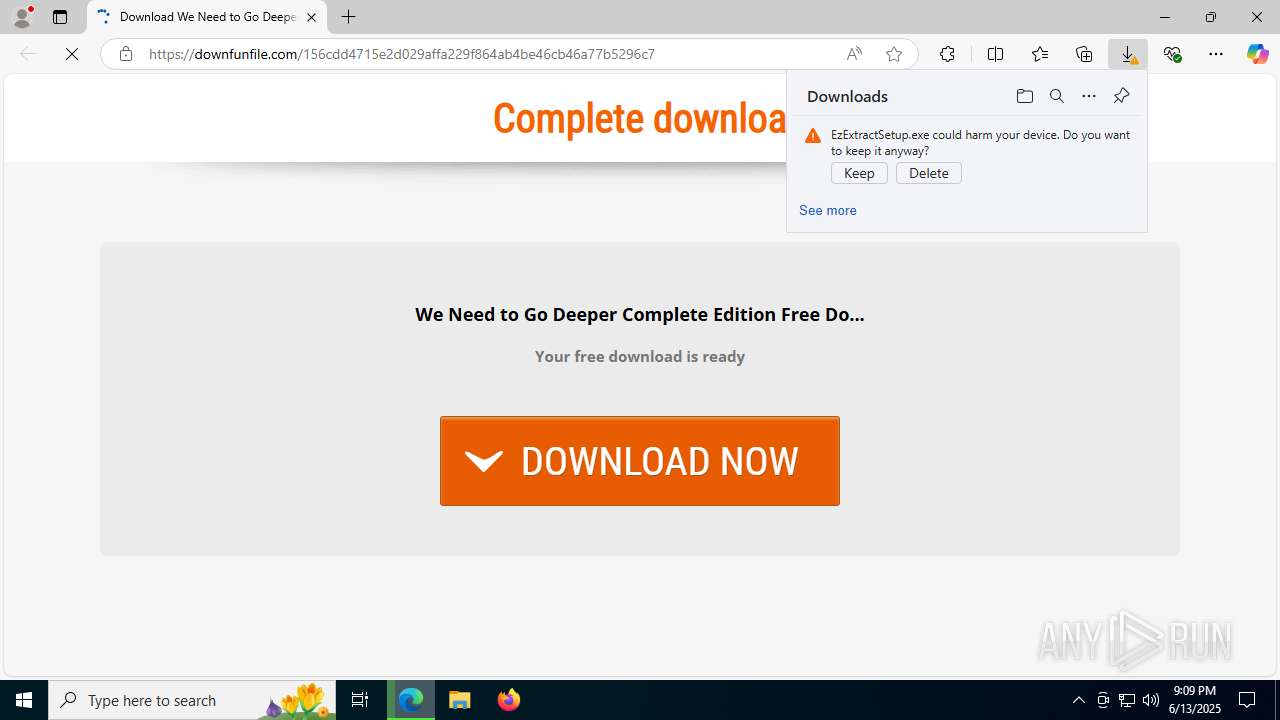
Executable content was dropped or overwritten
- EzExtractSetup.exe (PID: 5908)
- EzExtractSetup.exe (PID: 3948)
- EzExtractSetup.exe (PID: 1096)
- EzExtractSetup.exe (PID: 7236)
Reads security settings of Internet Explorer
- EzExtractSetup.exe (PID: 5908)
- EzExtractSetup.exe (PID: 3948)
- EzExtractSetup.exe (PID: 7236)
- EzExtractSetup.exe (PID: 1096)
- EzExtractProApp.exe (PID: 5232)
The process creates files with name similar to system file names
- EzExtractSetup.exe (PID: 3948)
- EzExtractSetup.exe (PID: 5908)
- EzExtractSetup.exe (PID: 1096)
- EzExtractSetup.exe (PID: 7236)
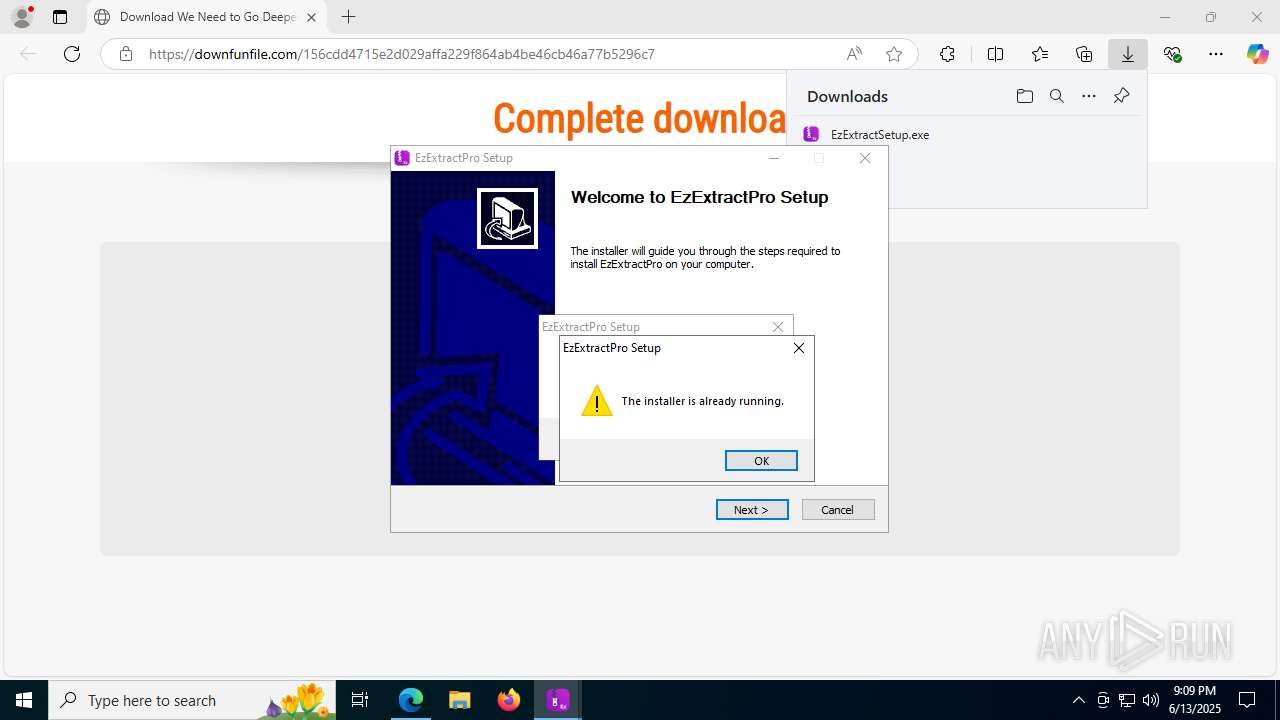
Malware-specific behavior (creating "System.dll" in Temp)
- EzExtractSetup.exe (PID: 3948)
- EzExtractSetup.exe (PID: 5908)
- EzExtractSetup.exe (PID: 1096)
- EzExtractSetup.exe (PID: 7236)
There is functionality for taking screenshot (YARA)
- EzExtractSetup.exe (PID: 5908)
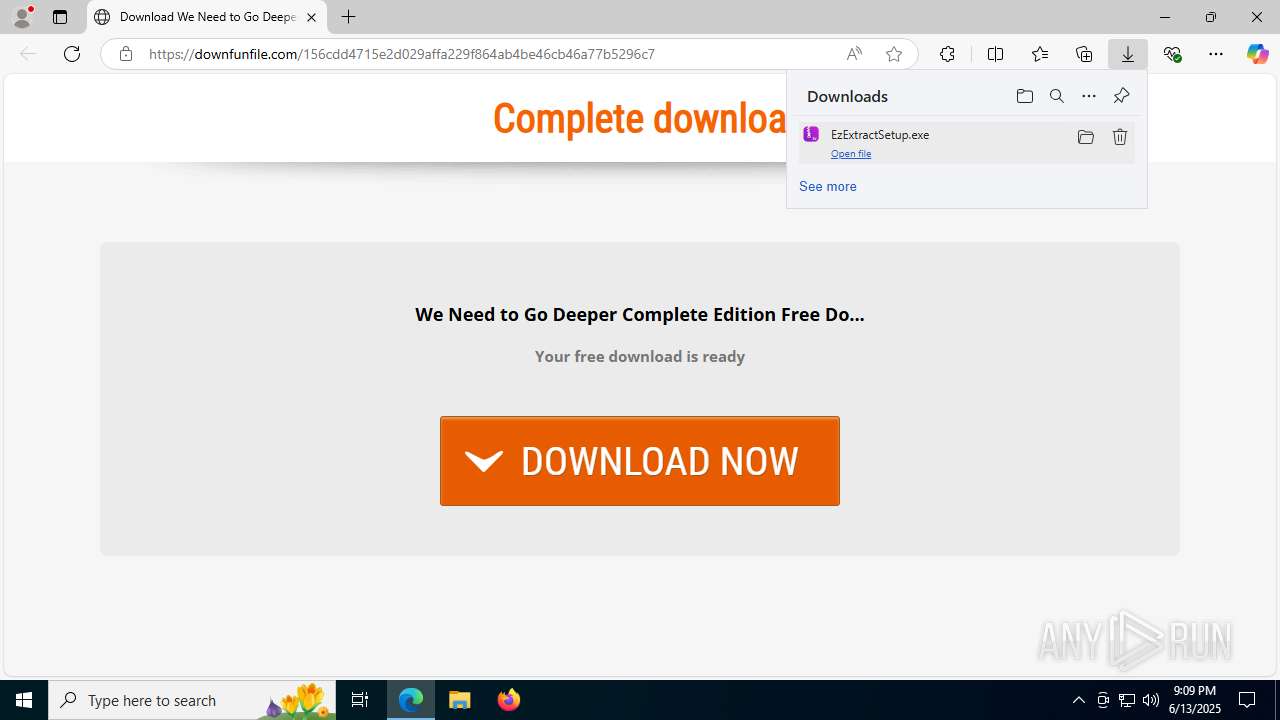
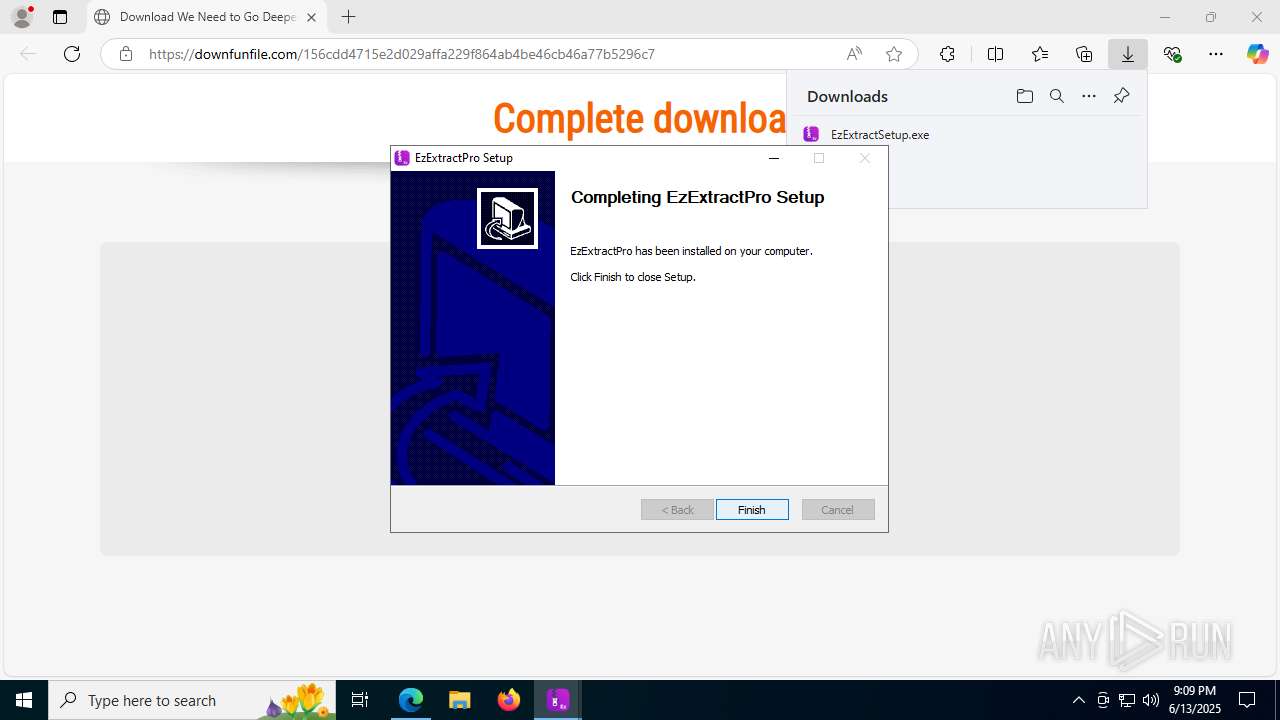
Creates a software uninstall entry
- EzExtractSetup.exe (PID: 3948)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 6876)
- regsvr32.exe (PID: 7020)
Explorer used for Indirect Command Execution
- explorer.exe (PID: 1512)
INFO
Executable content was dropped or overwritten
- msedge.exe (PID: 1068)
- msedge.exe (PID: 1712)
Application launched itself
- msedge.exe (PID: 1068)
Connects to unusual port
- msedge.exe (PID: 1712)
Reads the computer name
- identity_helper.exe (PID: 7788)
- EzExtractSetup.exe (PID: 3948)
- EzExtractSetup.exe (PID: 5908)
- EzExtractSetup.exe (PID: 1096)
- EzExtractSetup.exe (PID: 7236)
- EzExtractProApp.exe (PID: 5232)
Checks supported languages
- identity_helper.exe (PID: 7788)
- EzExtractSetup.exe (PID: 3948)
- EzExtractSetup.exe (PID: 5908)
- EzExtractSetup.exe (PID: 1096)
- EzExtractSetup.exe (PID: 7236)
- EzExtractProApp.exe (PID: 5232)
Reads Environment values
- identity_helper.exe (PID: 7788)
The sample compiled with english language support
- msedge.exe (PID: 1712)
- msedge.exe (PID: 1068)
- EzExtractSetup.exe (PID: 5908)
- EzExtractSetup.exe (PID: 1096)
- EzExtractSetup.exe (PID: 7236)
- EzExtractSetup.exe (PID: 3948)
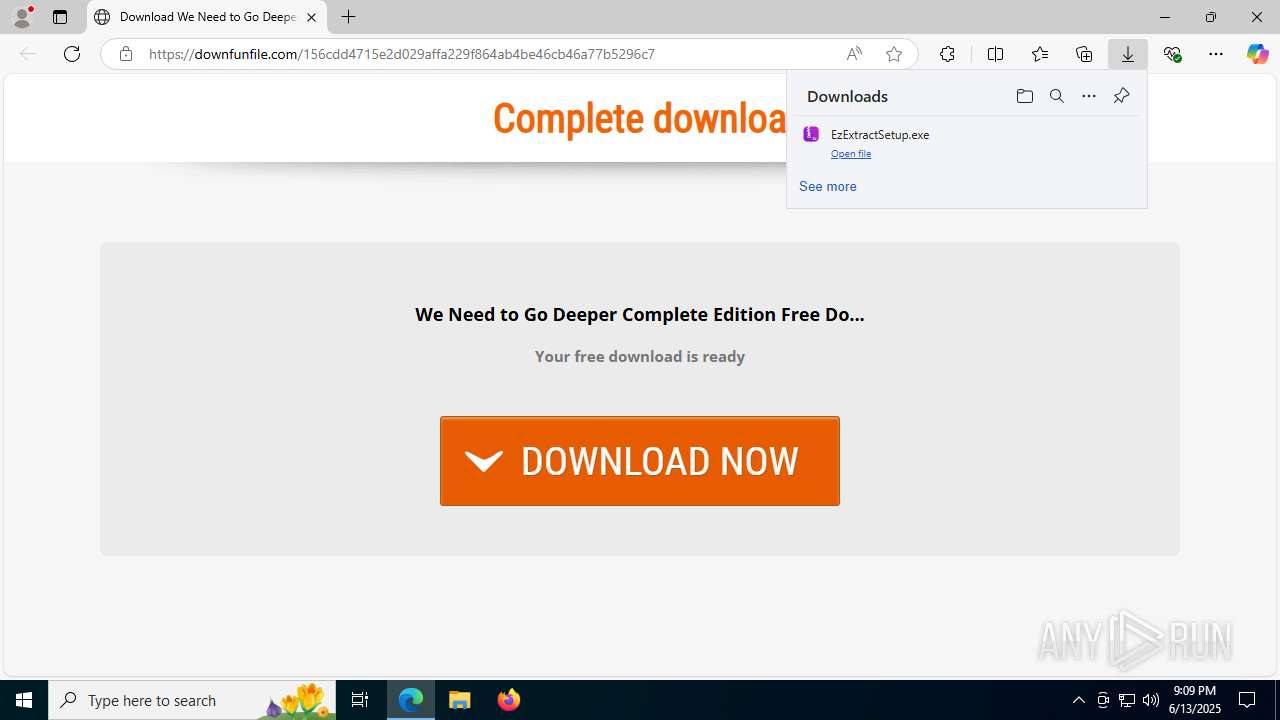
Launching a file from the Downloads directory
- msedge.exe (PID: 1068)
Create files in a temporary directory
- EzExtractSetup.exe (PID: 5908)
- EzExtractSetup.exe (PID: 3948)
- EzExtractSetup.exe (PID: 1096)
- EzExtractSetup.exe (PID: 7236)
Reads the machine GUID from the registry
- EzExtractSetup.exe (PID: 3948)
- EzExtractSetup.exe (PID: 1096)
- EzExtractSetup.exe (PID: 5908)
- EzExtractSetup.exe (PID: 7236)
- EzExtractProApp.exe (PID: 5232)
Checks proxy server information
- EzExtractSetup.exe (PID: 5908)
- EzExtractSetup.exe (PID: 3948)
- EzExtractSetup.exe (PID: 1096)
- EzExtractSetup.exe (PID: 7236)
Reads the software policy settings
- EzExtractSetup.exe (PID: 3948)
- EzExtractSetup.exe (PID: 1096)
- EzExtractSetup.exe (PID: 5908)
- EzExtractSetup.exe (PID: 7236)
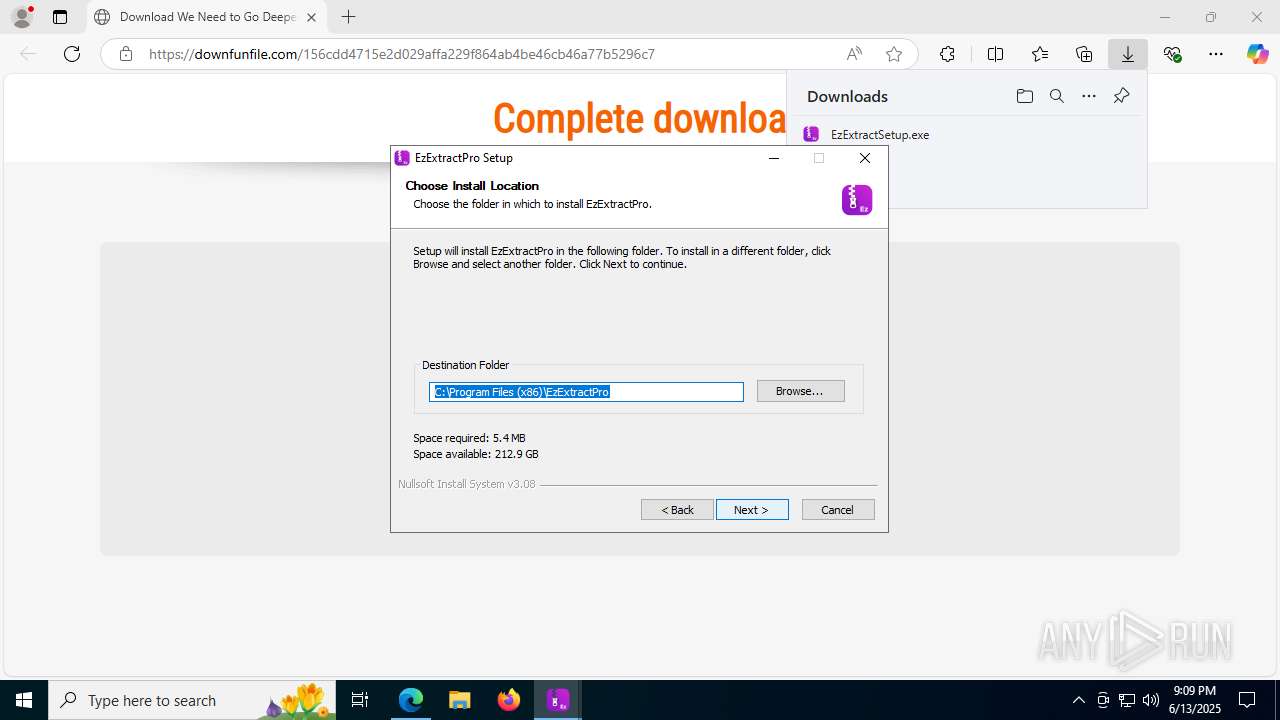
Creates files or folders in the user directory
- EzExtractSetup.exe (PID: 3948)
Creates files in the program directory
- EzExtractSetup.exe (PID: 3948)
Confuser has been detected (YARA)
- EzExtractProApp.exe (PID: 5232)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
186
Monitored processes
43
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=2792,i,17755063225990979730,2884593006550874364,262144 --variations-seed-version --mojo-platform-channel-handle=3684 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1068 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://downfunfile.com/156cdd4715e2d029affa229f864ab4be46cb46a77b5296c7" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
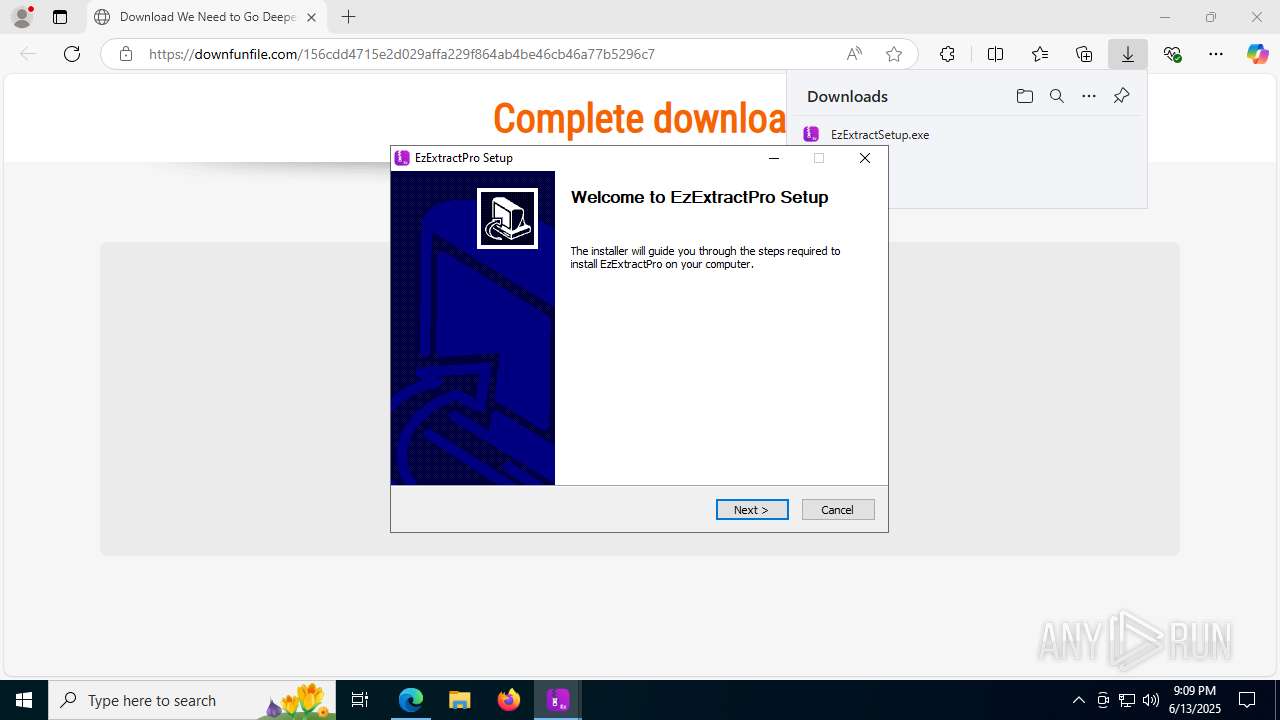
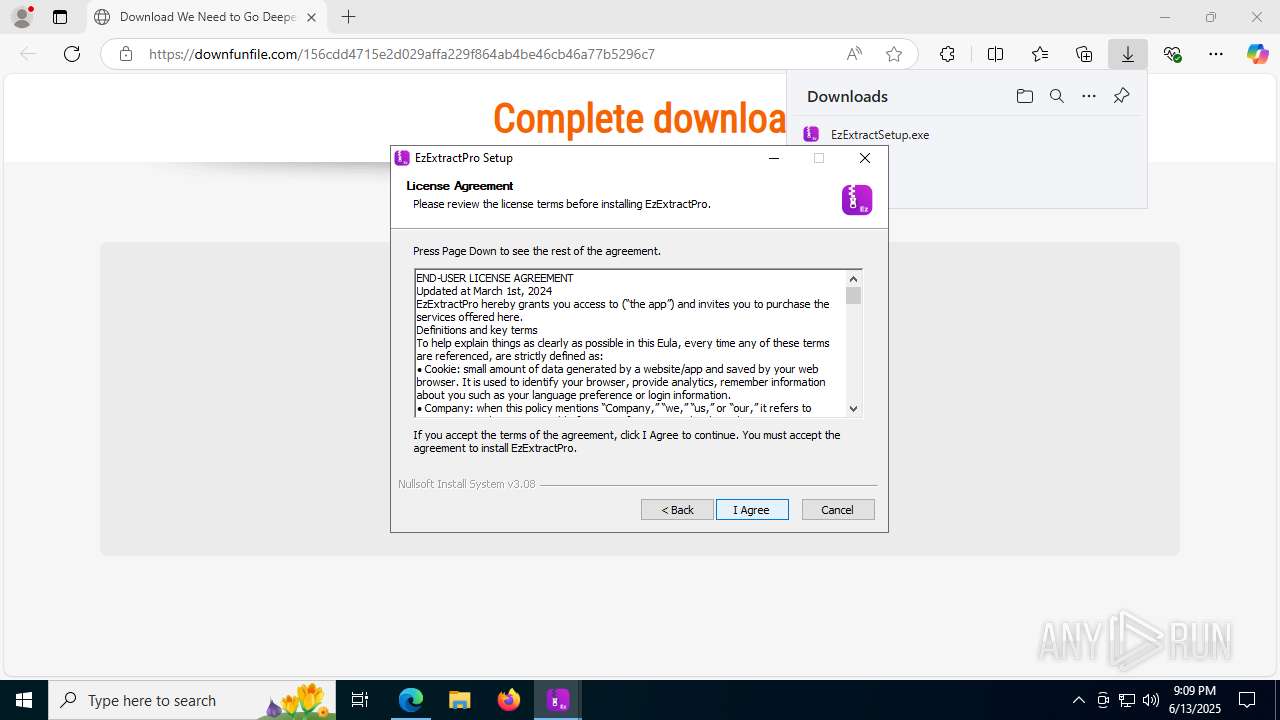
| 1096 | "C:\Users\admin\Downloads\EzExtractSetup.exe" | C:\Users\admin\Downloads\EzExtractSetup.exe | msedge.exe | ||||||||||||
User: admin Company: Empire Security Services Inc Integrity Level: HIGH Description: EzExtractPro Exit code: 2 Version: 1.0.0.1 Modules
| |||||||||||||||
| 1512 | "C:\WINDOWS\explorer.exe" "C:\Program Files (x86)\EzExtractPro\EzExtractProApp.exe" | C:\Windows\explorer.exe | — | EzExtractSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1636 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=2296,i,17755063225990979730,2884593006550874364,262144 --variations-seed-version --mojo-platform-channel-handle=4308 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1712 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2488,i,17755063225990979730,2884593006550874364,262144 --variations-seed-version --mojo-platform-channel-handle=2484 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1896 | "C:\Users\admin\Downloads\EzExtractSetup.exe" | C:\Users\admin\Downloads\EzExtractSetup.exe | — | msedge.exe | |||||||||||
User: admin Company: Empire Security Services Inc Integrity Level: MEDIUM Description: EzExtractPro Exit code: 3221226540 Version: 1.0.0.1 Modules
| |||||||||||||||
| 2620 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7676,i,17755063225990979730,2884593006550874364,262144 --variations-seed-version --mojo-platform-channel-handle=8016 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3948 | "C:\Users\admin\Downloads\EzExtractSetup.exe" | C:\Users\admin\Downloads\EzExtractSetup.exe | msedge.exe | ||||||||||||
User: admin Company: Empire Security Services Inc Integrity Level: HIGH Description: EzExtractPro Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 3964 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2780,i,17755063225990979730,2884593006550874364,262144 --variations-seed-version --mojo-platform-channel-handle=2804 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
9 226
Read events
9 172
Write events
54
Delete events
0
Modification events
| (PID) Process: | (1068) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1068) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1068) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1068) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1068) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1068) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1068) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 1F44CEBC10962F00 | |||
| (PID) Process: | (1068) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\787138 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {23DAAEFA-E867-4AFC-B3FC-955BC2D0C64F} | |||
| (PID) Process: | (1068) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\787138 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {BA7A1505-161B-44C8-89E8-1DAB600E4649} | |||
| (PID) Process: | (1068) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\787138 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F69949C9-F74B-431E-A0F7-1B8056D99E32} | |||
Executable files
31
Suspicious files
209
Text files
43
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1068 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF17660d.TMP | — | |
MD5:— | SHA256:— | |||
| 1068 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1068 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF17660d.TMP | — | |
MD5:— | SHA256:— | |||
| 1068 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1068 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF17661c.TMP | — | |
MD5:— | SHA256:— | |||
| 1068 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1068 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF17665b.TMP | — | |
MD5:— | SHA256:— | |||
| 1068 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1068 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF17666a.TMP | — | |
MD5:— | SHA256:— | |||
| 1068 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
95
DNS requests
84
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1712 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:X38WsX-7xjQpsbFYE9RFYPJ2rXeUfrTtIW61evpZqyk&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 97 b | whitelisted |
4944 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | CL | binary | 868 b | whitelisted |
5908 | EzExtractSetup.exe | GET | 200 | 142.250.186.67:80 | http://c.pki.goog/r/gsr1.crl | US | binary | 1.70 Kb | whitelisted |
3948 | EzExtractSetup.exe | GET | 200 | 142.250.186.67:80 | http://c.pki.goog/r/r4.crl | US | binary | 530 b | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | RU | binary | 825 b | whitelisted |
3948 | EzExtractSetup.exe | GET | 200 | 142.250.186.67:80 | http://c.pki.goog/r/gsr1.crl | US | binary | 1.70 Kb | whitelisted |
5908 | EzExtractSetup.exe | GET | 200 | 142.250.186.67:80 | http://c.pki.goog/r/r4.crl | US | binary | 530 b | whitelisted |
1132 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | CL | binary | 420 b | whitelisted |
1132 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | CL | binary | 408 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1512 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1712 | msedge.exe | 188.114.97.3:443 | downfunfile.com | CLOUDFLARENET | NL | unknown |
1712 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1712 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1712 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1712 | msedge.exe | 2.16.241.224:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
downfunfile.com |
| unknown |
config.edge.skype.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
yourjsdelivery.com |
| unknown |
ajax.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1712 | msedge.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected Domain Associated with Malware Distribution (downfunfile .com) |
1712 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
1712 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
1712 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
1712 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
1712 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
1712 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
1712 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
1712 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |