| File name: | runme.exe |
| Full analysis: | https://app.any.run/tasks/94e63cf1-ff04-4fed-bd4c-37c7ee461e53 |
| Verdict: | Malicious activity |
| Analysis date: | January 28, 2024, 18:11:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | EADE828AFE0CE5B7C0B3BCD5FB8086C2 |
| SHA1: | 63CFAF6A5BC232C0035C906CC944348458F69C98 |
| SHA256: | F61A6F9F28A97B3ACA7574878F9F15C3922642225C4E92F64236701E6FA16263 |
| SSDEEP: | 98304:FXDrQ3yErFq+CrrUyMzSvRRyOC2HpaxF3fycPfDmlH4ubCOMGRHgtEdmpVpFJlbP:Dzh4QHV7iZjupiUR |
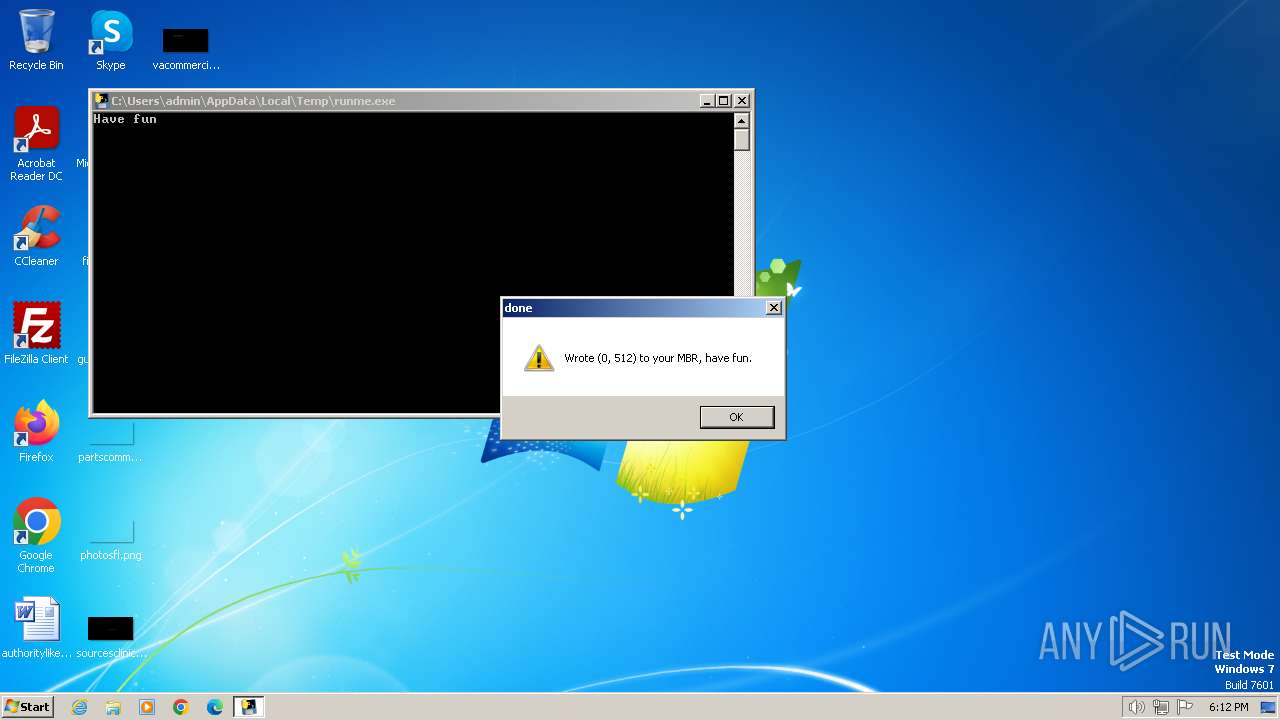
MALICIOUS
Drops the executable file immediately after the start
- runme.exe (PID: 2592)
SUSPICIOUS
Process drops legitimate windows executable
- runme.exe (PID: 2592)
Application launched itself
- runme.exe (PID: 2592)
Executable content was dropped or overwritten
- runme.exe (PID: 2592)
The process drops C-runtime libraries
- runme.exe (PID: 2592)
Loads Python modules
- runme.exe (PID: 2780)
INFO
Checks supported languages
- runme.exe (PID: 2592)
- runme.exe (PID: 2780)
Reads the computer name
- runme.exe (PID: 2592)
Create files in a temporary directory
- runme.exe (PID: 2592)
Reads the machine GUID from the registry
- runme.exe (PID: 2780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:01:28 19:11:06+01:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.37 |
| CodeSize: | 156672 |
| InitializedDataSize: | 128512 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xaa80 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows command line |
Total processes
45
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1036 | "C:\Users\admin\AppData\Local\Temp\runme.exe" | C:\Users\admin\AppData\Local\Temp\runme.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2592 | "C:\Users\admin\AppData\Local\Temp\runme.exe" | C:\Users\admin\AppData\Local\Temp\runme.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2780 | "C:\Users\admin\AppData\Local\Temp\runme.exe" | C:\Users\admin\AppData\Local\Temp\runme.exe | — | runme.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
40
Read events
40
Write events
0
Delete events
0
Modification events
Executable files
14
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2780 | runme.exe | \Device\Harddisk0\DR0 | — | |
MD5:— | SHA256:— | |||
| 2592 | runme.exe | C:\Users\admin\AppData\Local\Temp\_MEI25922\Pythonwin\mfc140u.dll | executable | |
MD5:E76B52D11DB435D36453D26C8B446A8F | SHA256:E422C9366A53536A35E307EF301F08661C28C29B7FCDA1B454333C6A41C6BB21 | |||
| 2592 | runme.exe | C:\Users\admin\AppData\Local\Temp\_MEI25922\select.pyd | executable | |
MD5:25AE837BEC095038DB628878C3B12C6A | SHA256:6D5A3630570035555CEA342C3A8E2922CA23451113CB178CD7FEE07E59DA123C | |||
| 2592 | runme.exe | C:\Users\admin\AppData\Local\Temp\_MEI25922\_bz2.pyd | executable | |
MD5:18CD8755E6D4559840D07467DF26AF34 | SHA256:82A85187FAF8786216C82AC1C4CCF32C8839048E242025ED4E7A1E3AB870255F | |||
| 2592 | runme.exe | C:\Users\admin\AppData\Local\Temp\_MEI25922\_hashlib.pyd | executable | |
MD5:FE12F0301B1E8749108627F1085FD10C | SHA256:8929B5818AAA0F595B8CC3B6AADDC630F2B27BCDE3A29D44C13D95037596AA1B | |||
| 2592 | runme.exe | C:\Users\admin\AppData\Local\Temp\_MEI25922\Pythonwin\win32ui.pyd | executable | |
MD5:9A206178DC7E2A6CE185553245A3325D | SHA256:00EA5C2866A682627651B7883F80854748D7B7EE4F6C6B6D7B4ADF4D01DC4652 | |||
| 2592 | runme.exe | C:\Users\admin\AppData\Local\Temp\_MEI25922\_socket.pyd | executable | |
MD5:E7AD342AF27EF2B62C6FBA44A2456FBA | SHA256:48F1F1842E6845A197C9BE50027BB2A67A868E743BFA81B8D8753C24CDC08B7B | |||
| 2592 | runme.exe | C:\Users\admin\AppData\Local\Temp\_MEI25922\libcrypto-1_1.dll | executable | |
MD5:C7298CD5232CF8F6E34B3404FC276266 | SHA256:1E95A63B165672ACCDE92A9C9F8B9052C8F6357344F1376AF9F916AEEB306DA3 | |||
| 2592 | runme.exe | C:\Users\admin\AppData\Local\Temp\_MEI25922\_lzma.pyd | executable | |
MD5:B23D17B4B3B15DAB84E384B8DD1D8FC6 | SHA256:D3350AD957D6C37B2C75F56A5A149F0EEB58295227F78C15048669A2E816AE3A | |||
| 2592 | runme.exe | C:\Users\admin\AppData\Local\Temp\_MEI25922\VCRUNTIME140.dll | executable | |
MD5:5F9D90D666620944943B0D6D1CCA1945 | SHA256:9EC4AFAD505E0A3DAD760FA5B59C66606AE54DD043C16914CF56D7006E46D375 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |