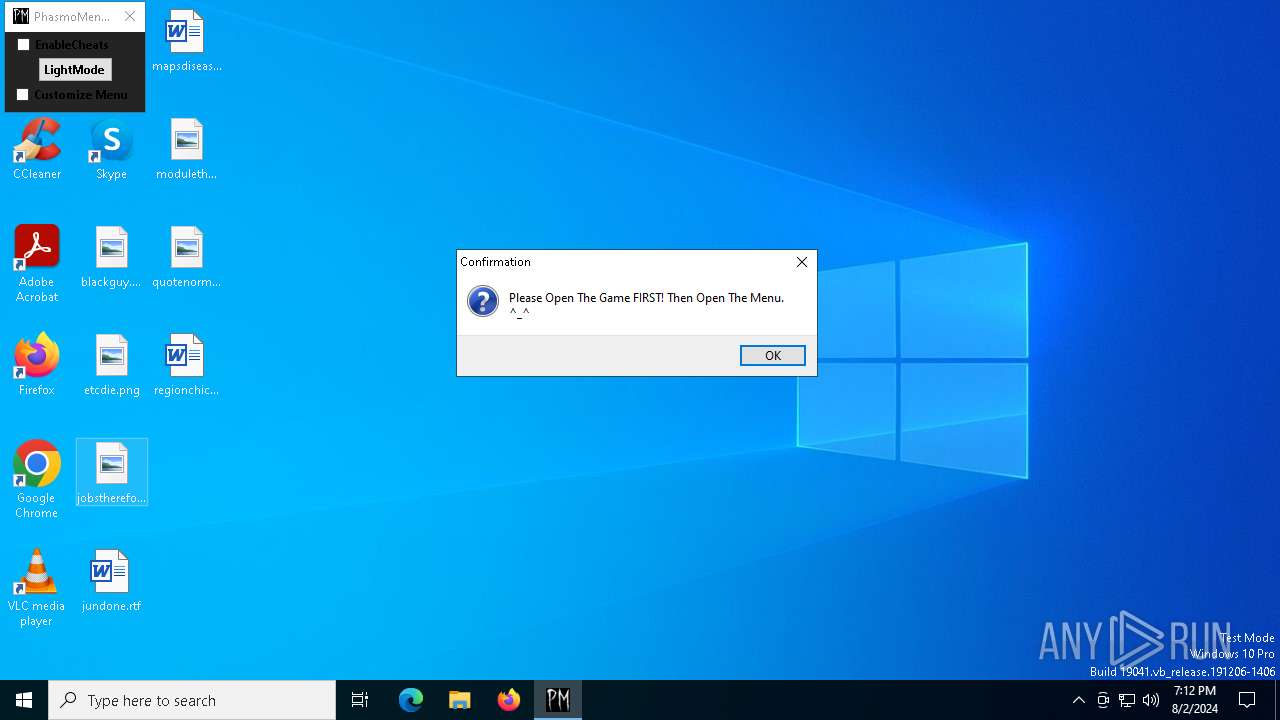
| File name: | PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe |
| Full analysis: | https://app.any.run/tasks/03304a51-0f23-459d-8425-78d86441771e |
| Verdict: | Malicious activity |
| Analysis date: | August 02, 2024, 19:12:37 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 547707B98636F7F46477517C148B348E |
| SHA1: | F77289E3A8D7193E70AFF99678E3FD5AAC5B2D59 |
| SHA256: | F6136577076A86A427E5738152AF5BC62CE6B32D1B43092A9259B45971EE1281 |
| SSDEEP: | 98304:NiAAJ/weKsf0EIqZmgCBVwKWBIVQuqGTqn2R8IlzHNY3ZalbKOXGs7oia6kZNLk9:MndanTvRjZNM |
MALICIOUS
Drops the executable file immediately after the start
- PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe (PID: 6428)
- PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe (PID: 7160)
SUSPICIOUS
Executable content was dropped or overwritten
- PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe (PID: 7160)
- PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe (PID: 6428)
INFO
Checks supported languages
- PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe (PID: 7160)
- PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe (PID: 6240)
- PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe (PID: 6428)
Create files in a temporary directory
- PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe (PID: 6428)
- PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe (PID: 7160)
Reads the computer name
- PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe (PID: 7160)
- PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe (PID: 6240)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:06:28 14:45:44+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 36352 |
| InitializedDataSize: | 7475712 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x15eb |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Total processes
141
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6240 | "C:\Users\admin\AppData\Local\Temp\cetrainers\CET55EC.tmp\extracted\PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe" "C:\Users\admin\AppData\Local\Temp\cetrainers\CET55EC.tmp\extracted\CET_TRAINER.CETRAINER" "-ORIGIN:C:\Users\admin\AppData\Local\Temp\" | C:\Users\admin\AppData\Local\Temp\cetrainers\CET55EC.tmp\extracted\PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe | — | PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe | |||||||||||
User: admin Company: Cheat Engine Integrity Level: HIGH Description: Cheat Engine Exit code: 0 Version: 7.5.0.7431 Modules
| |||||||||||||||
| 6428 | "C:\Users\admin\AppData\Local\Temp\cetrainers\CET55EC.tmp\PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe" -ORIGIN:"C:\Users\admin\AppData\Local\Temp\" | C:\Users\admin\AppData\Local\Temp\cetrainers\CET55EC.tmp\PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe | PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 7016 | "C:\Users\admin\AppData\Local\Temp\PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe" | C:\Users\admin\AppData\Local\Temp\PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 7160 | "C:\Users\admin\AppData\Local\Temp\PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe" | C:\Users\admin\AppData\Local\Temp\PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
413
Read events
412
Write events
1
Delete events
0
Modification events
| (PID) Process: | (6240) PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Cheat Engine |
| Operation: | write | Name: | DPI Aware |
Value: 1 | |||
Executable files
5
Suspicious files
2
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7160 | PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe | C:\Users\admin\AppData\Local\Temp\cetrainers\CET55EC.tmp\CET_Archive.dat | — | |
MD5:— | SHA256:— | |||
| 6428 | PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe | C:\Users\admin\AppData\Local\Temp\cetrainers\CET55EC.tmp\extracted\CET_TRAINER.CETRAINER | binary | |
MD5:4FC9002E0DF427F662E55533598BF6FC | SHA256:9EDCA8CECC59A23993A4561932CD851936682F4894F81737FAC74C951D850461 | |||
| 6428 | PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe | C:\Users\admin\AppData\Local\Temp\cetrainers\CET55EC.tmp\extracted\PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe | executable | |
MD5:EDEEF697CBF212B5ECFCD9C1D9A8803D | SHA256:AC9BCC7813C0063BDCD36D8E4E79A59B22F6E95C2D74C65A4249C7D5319AE3F6 | |||
| 6428 | PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe | C:\Users\admin\AppData\Local\Temp\cetrainers\CET55EC.tmp\extracted\autorun\dlls\MonoDataCollector32.dll | executable | |
MD5:C5B870CE07DA5206D8A81E139920B7DC | SHA256:EB26B38A604CF98B95A39FD249C0771E351061A9894D22284CDFE984E8FC7A6C | |||
| 6428 | PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe | C:\Users\admin\AppData\Local\Temp\cetrainers\CET55EC.tmp\extracted\autorun\monoscript.lua | text | |
MD5:76168CA68F3ED8ADE110B140244EFBAF | SHA256:5832B5AB00E84690AC1E780E8B1C4ABD9649465234C9FFA2CECB410BE66A6B8A | |||
| 6428 | PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe | C:\Users\admin\AppData\Local\Temp\cetrainers\CET55EC.tmp\extracted\autorun\forms\MonoDataCollector.frm | xml | |
MD5:03D4DD46084BCBE16A39D72BA22E5446 | SHA256:4F254BBC897AD0E165986D18577E0A04FD31C93CCA542A0999FA0093EDC5BC61 | |||
| 6428 | PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe | C:\Users\admin\AppData\Local\Temp\cetrainers\CET55EC.tmp\extracted\autorun\luasymbols.lua | binary | |
MD5:DF4D243AB0407A1F03CCF448232FCF62 | SHA256:C5A35380AF8BEBE96B85377F5F41F8C068CB857C74B9CB85B7467B35C1DE10C4 | |||
| 7160 | PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe | C:\Users\admin\AppData\Local\Temp\cetrainers\CET55EC.tmp\PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe | executable | |
MD5:971B37CEDF686E0AC8CA0297A953AAD9 | SHA256:1965546A19990B4523A1588EB0D7FDD42BD443E2BCC632DAE04343D358394AE7 | |||
| 6428 | PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe | C:\Users\admin\AppData\Local\Temp\cetrainers\CET55EC.tmp\extracted\defines.lua | text | |
MD5:62E1FA241D417668F7C5DA6E4009A5A6 | SHA256:82E8EF7DF20A86791CEF062F2DCACB1D91B4ADC9F5DEA2FD274886BE8365B2F8 | |||
| 6428 | PhasmoMenu v0.5.3.4 By PappyG_[unknowncheats.me]_.exe | C:\Users\admin\AppData\Local\Temp\cetrainers\CET55EC.tmp\extracted\lua53-64.dll | executable | |
MD5:B7C9F1E7E640F1A034BE84AF86970D45 | SHA256:6D0A06B90213F082CB98950890518C0F08B9FC16DBFAB34D400267CB6CDADEFF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
56
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4248 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4248 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6532 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6560 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6600 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4708 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2768 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5336 | SearchApp.exe | 23.37.226.106:443 | www.bing.com | Akamai International B.V. | DE | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4248 | svchost.exe | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4248 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |
arc.msn.com |
| whitelisted |
r.bing.com |
| whitelisted |