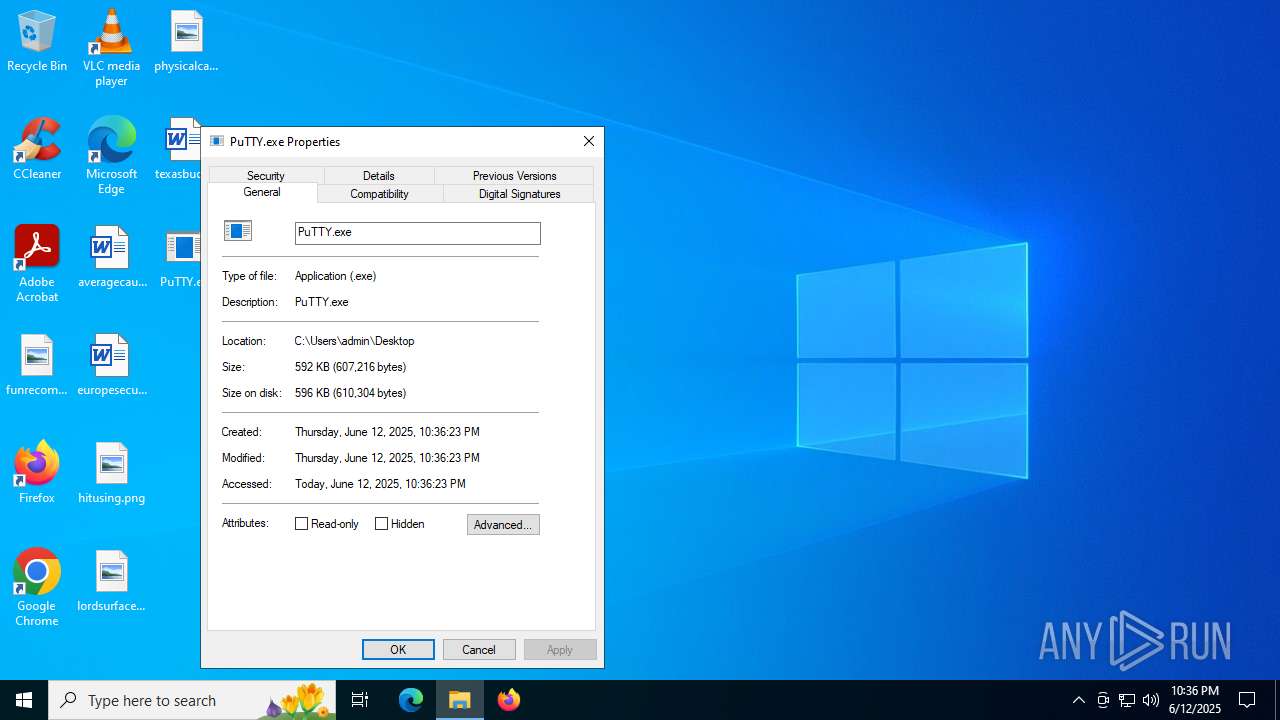
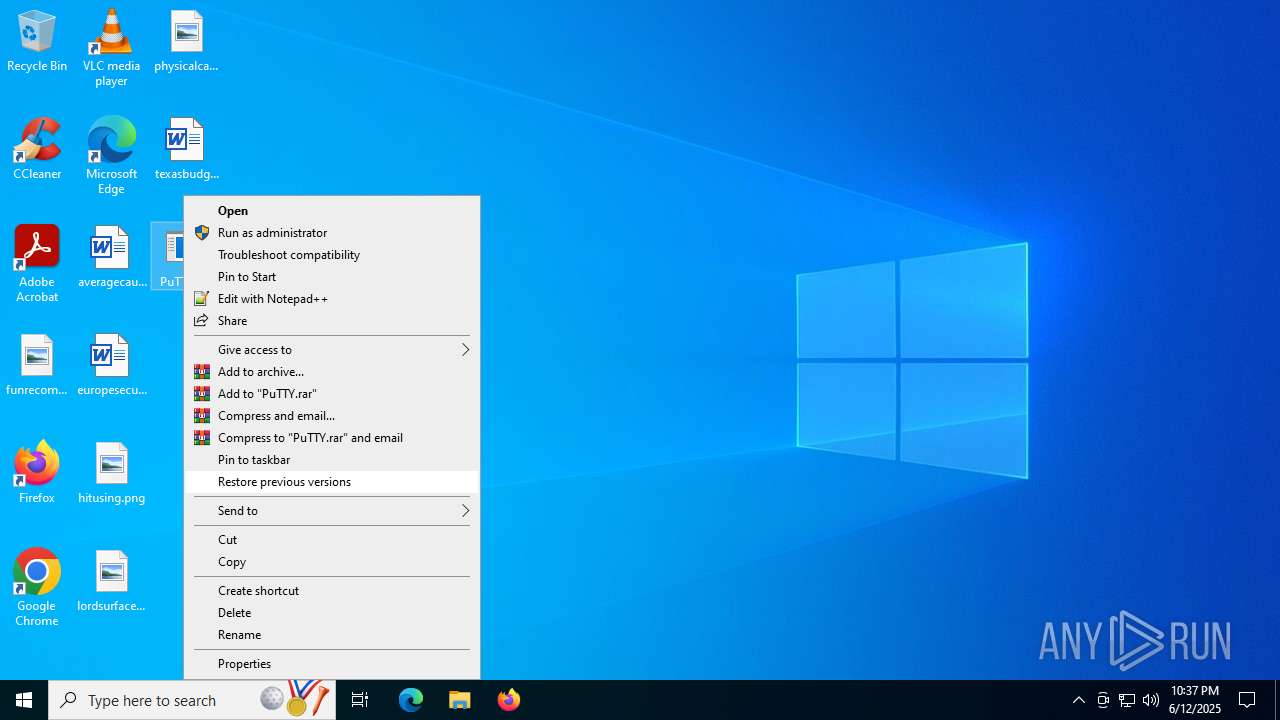
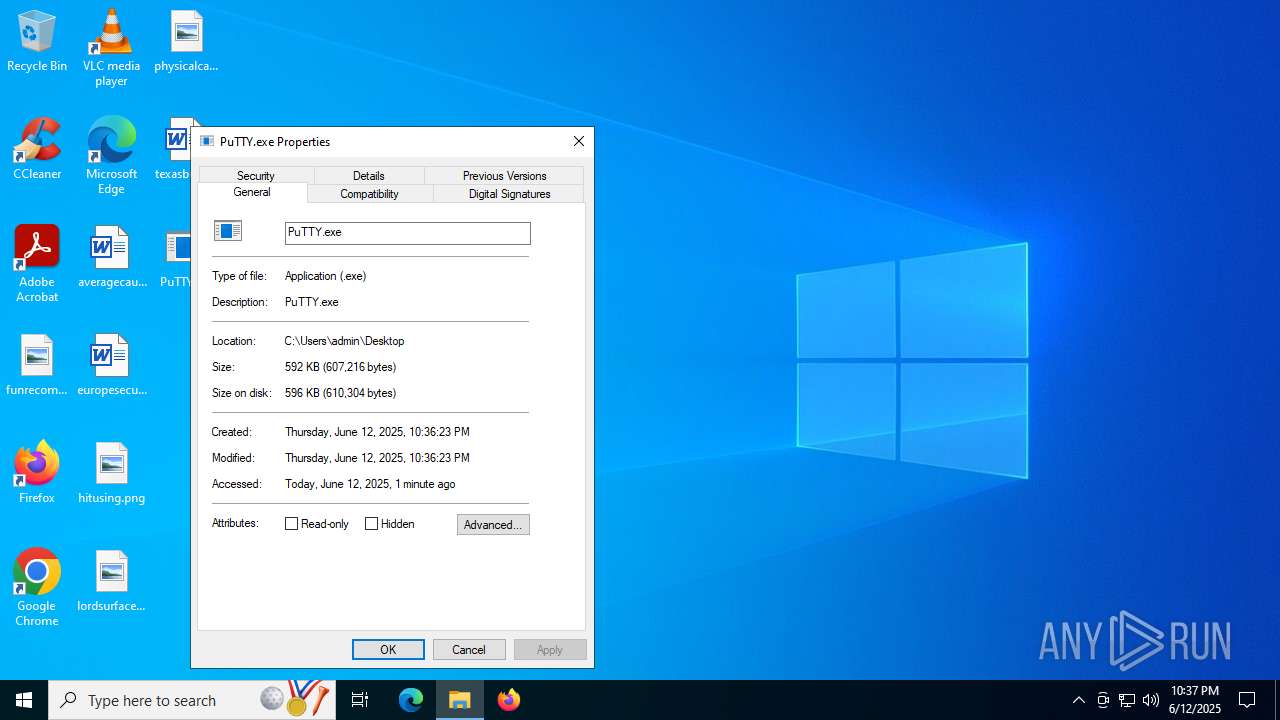
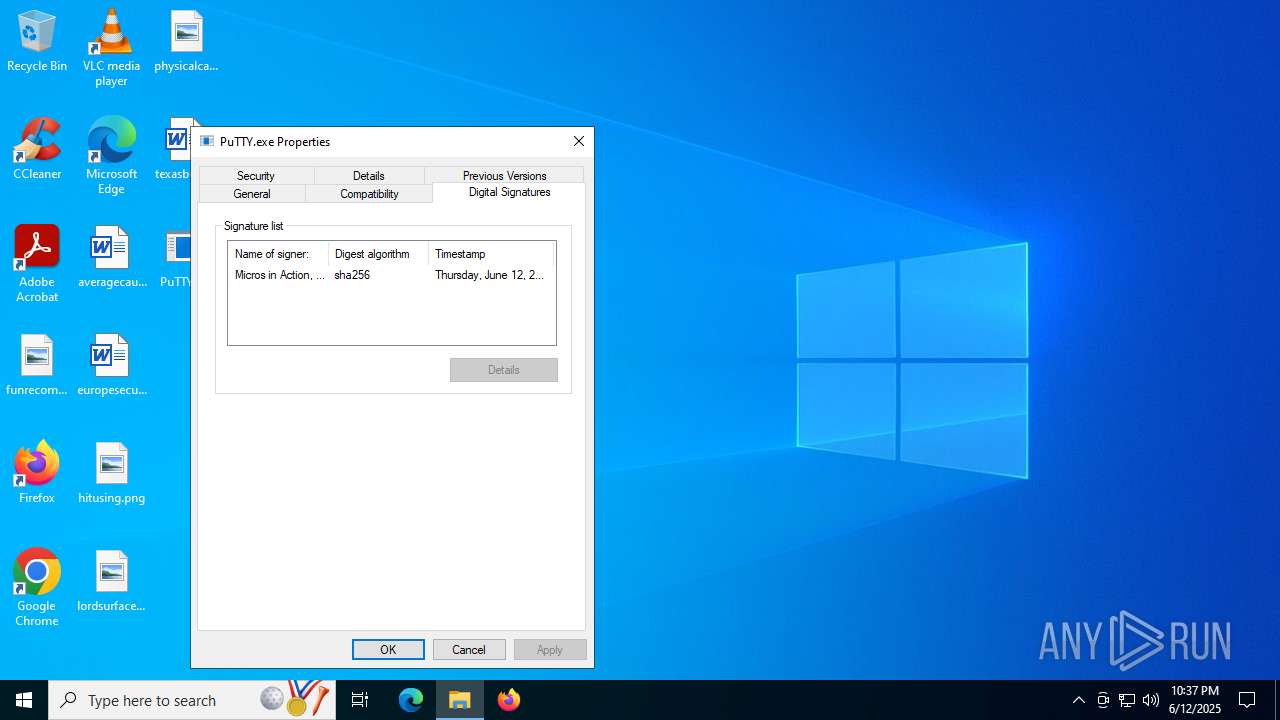
| File name: | PuTTY.exe |
| Full analysis: | https://app.any.run/tasks/67235c96-d66b-4e8f-a4a4-4cd6dfc2edee |
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2025, 22:36:19 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 6 sections |
| MD5: | 47D8FA90485FA8E4DF338FB8858E4742 |
| SHA1: | 9133A1E657857379AF2BE805510E5E2A387D5813 |
| SHA256: | F60B2C3EC0C0C79AD5E9EF3E6CAE702585780F9A33AD21B7E0324E1EFFF2878C |
| SSDEEP: | 12288:z5ybjxXBT6Flu1IJiCCm9PZcUFlaBs7qiGqpeON:zYb2uGJXCo5k2gON |
MALICIOUS
Uses Task Scheduler to run other applications
- PuTTY.exe (PID: 5616)
- PuTTY.exe (PID: 420)
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- PuTTY.exe (PID: 5616)
- PuTTY.exe (PID: 5716)
- PuTTY.exe (PID: 420)
- rundll32.exe (PID: 6684)
Uses RUNDLL32.EXE to load library
- PuTTY.exe (PID: 5616)
- PuTTY.exe (PID: 420)
Reads security settings of Internet Explorer
- PuTTY.exe (PID: 5616)
- PuTTY.exe (PID: 5716)
- PuTTY.exe (PID: 420)
The process executes via Task Scheduler
- rundll32.exe (PID: 2876)
- rundll32.exe (PID: 1100)
- rundll32.exe (PID: 4168)
Executable content was dropped or overwritten
- PuTTY.exe (PID: 420)
- PuTTY.exe (PID: 5616)
Connects to the server without a host name
- rundll32.exe (PID: 6684)
INFO
Checks supported languages
- PuTTY.exe (PID: 5716)
- PuTTY.exe (PID: 420)
- PuTTY.exe (PID: 5616)
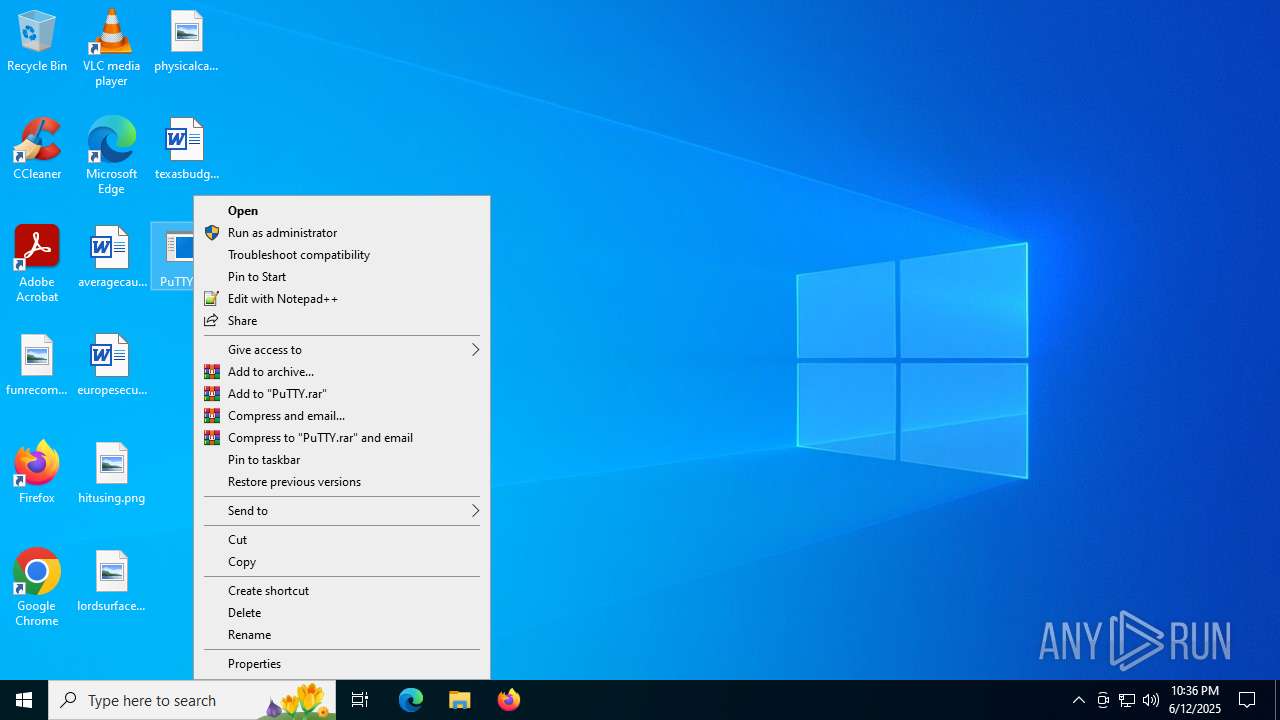
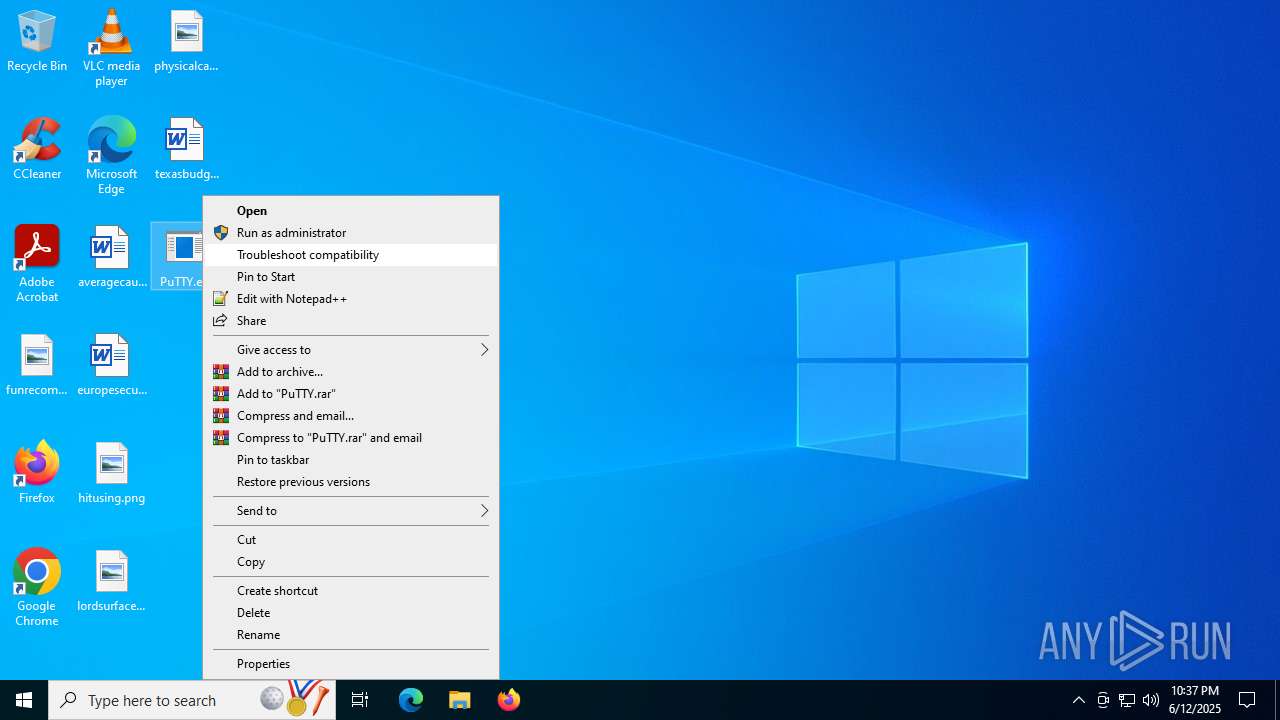
Manual execution by a user
- PuTTY.exe (PID: 420)
- PuTTY.exe (PID: 5716)
Reads the computer name
- PuTTY.exe (PID: 5616)
- PuTTY.exe (PID: 5716)
- PuTTY.exe (PID: 420)
Creates files or folders in the user directory
- PuTTY.exe (PID: 5616)
- rundll32.exe (PID: 6684)
- PuTTY.exe (PID: 420)
Checks proxy server information
- PuTTY.exe (PID: 5616)
- rundll32.exe (PID: 6684)
- PuTTY.exe (PID: 5716)
- PuTTY.exe (PID: 420)
- slui.exe (PID: 4216)
Launching a file from Task Scheduler
- PuTTY.exe (PID: 5616)
- PuTTY.exe (PID: 420)
Reads the software policy settings
- slui.exe (PID: 4216)
Reads security settings of Internet Explorer
- rundll32.exe (PID: 6684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:06:13 02:12:10+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.43 |
| CodeSize: | 542720 |
| InitializedDataSize: | 56320 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x770ec |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
162
Monitored processes
16
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 420 | "C:\Users\admin\Desktop\PuTTY.exe" | C:\Users\admin\Desktop\PuTTY.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1100 | "C:\WINDOWS\System32\rundll32.exe" C:\Users\admin\AppData\Roaming\H41jwdp0Zv6y¿\twain_96.dll DllRegisterServer | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | PuTTY.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1880 | C:\WINDOWS\System32\schtasks.exe /Create /SC MINUTE /MO 3 /TN "Security Updater" /TR "C:\WINDOWS\System32\rundll32.exe C:\Users\admin\AppData\Roaming\H41jwdp0Zv6y¿\twain_96.dll DllRegisterServer" | C:\Windows\System32\schtasks.exe | — | PuTTY.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2348 | C:\WINDOWS\System32\schtasks.exe /Create /SC MINUTE /MO 3 /TN "Security Updater" /TR "C:\WINDOWS\System32\rundll32.exe C:\Users\admin\AppData\Roaming\ueosSEgc9wRHF\twain_96.dll DllRegisterServer" | C:\Windows\System32\schtasks.exe | — | PuTTY.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2876 | "C:\WINDOWS\System32\rundll32.exe" C:\Users\admin\AppData\Roaming\H41jwdp0Zv6y¿\twain_96.dll DllRegisterServer | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3092 | C:\WINDOWS\System32\schtasks.exe /run /tn "Security Updater" | C:\Windows\System32\schtasks.exe | — | PuTTY.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3936 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | PuTTY.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4168 | "C:\WINDOWS\System32\rundll32.exe" C:\Users\admin\AppData\Roaming\H41jwdp0Zv6y¿\twain_96.dll DllRegisterServer | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4216 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 306
Read events
2 294
Write events
12
Delete events
0
Modification events
| (PID) Process: | (5616) PuTTY.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5616) PuTTY.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5616) PuTTY.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6684) rundll32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6684) rundll32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6684) rundll32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5716) PuTTY.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5716) PuTTY.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5716) PuTTY.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (420) PuTTY.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
2
Suspicious files
0
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5616 | PuTTY.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\login[1].ico | image | |
MD5:BB134CA5E61D43BBD203C377B434C541 | SHA256:645486E9F8694B8CDA84B6B66F748814E8A1B4A0FE8128B30459AEE008DB85D3 | |||
| 6684 | rundll32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\secure[1].ico | image | |
MD5:E131DAA9710A51BCC8EF4490AB99F420 | SHA256:25599852B17539E6A23D2E4F64EB734D0C260E5284E191BCC77EC78B827BBE00 | |||
| 5616 | PuTTY.exe | C:\Users\admin\AppData\Roaming\H41jwdp0Zv6y¿\twain_96.dll | executable | |
MD5:F3B42AF1DEA239BEFD2CCE9AC953865A | SHA256:E9E5311FBF76EEA22C42DAA381074FEECB745020DB473184E6236F9A08816925 | |||
| 420 | PuTTY.exe | C:\Users\admin\AppData\Roaming\ueosSEgc9wRHF\twain_96.dll | executable | |
MD5:F3B42AF1DEA239BEFD2CCE9AC953865A | SHA256:E9E5311FBF76EEA22C42DAA381074FEECB745020DB473184E6236F9A08816925 | |||
| 420 | PuTTY.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\login[2].ico | image | |
MD5:BB134CA5E61D43BBD203C377B434C541 | SHA256:645486E9F8694B8CDA84B6B66F748814E8A1B4A0FE8128B30459AEE008DB85D3 | |||
| 420 | PuTTY.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\E4DJRUXW\reg[1].txt | text | |
MD5:260CA9DD8A4577FC00B7BD5810298076 | SHA256:AEE408847D35E44E99430F0979C3357B85FE8DBB4535A494301198ADBEE85F27 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
51
DNS requests
24
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6800 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6800 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5848 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6684 | rundll32.exe | GET | 200 | 185.196.8.217:80 | http://185.196.8.217/api/kcehc | unknown | — | — | unknown |
5328 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6684 | rundll32.exe | POST | 200 | 185.196.8.217:80 | http://185.196.8.217/api/kcehc | unknown | — | — | unknown |
2940 | svchost.exe | GET | 200 | 2.16.252.233:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
6684 | rundll32.exe | POST | 200 | 185.196.8.217:80 | http://185.196.8.217/api/jgfnsfnuefcnegfnehjbfncejfh | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2792 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
1268 | svchost.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6800 | SIHClient.exe | 20.12.23.50:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5616 | PuTTY.exe | Potentially Bad Traffic | ET INFO HTTP traffic on port 443 (POST) |