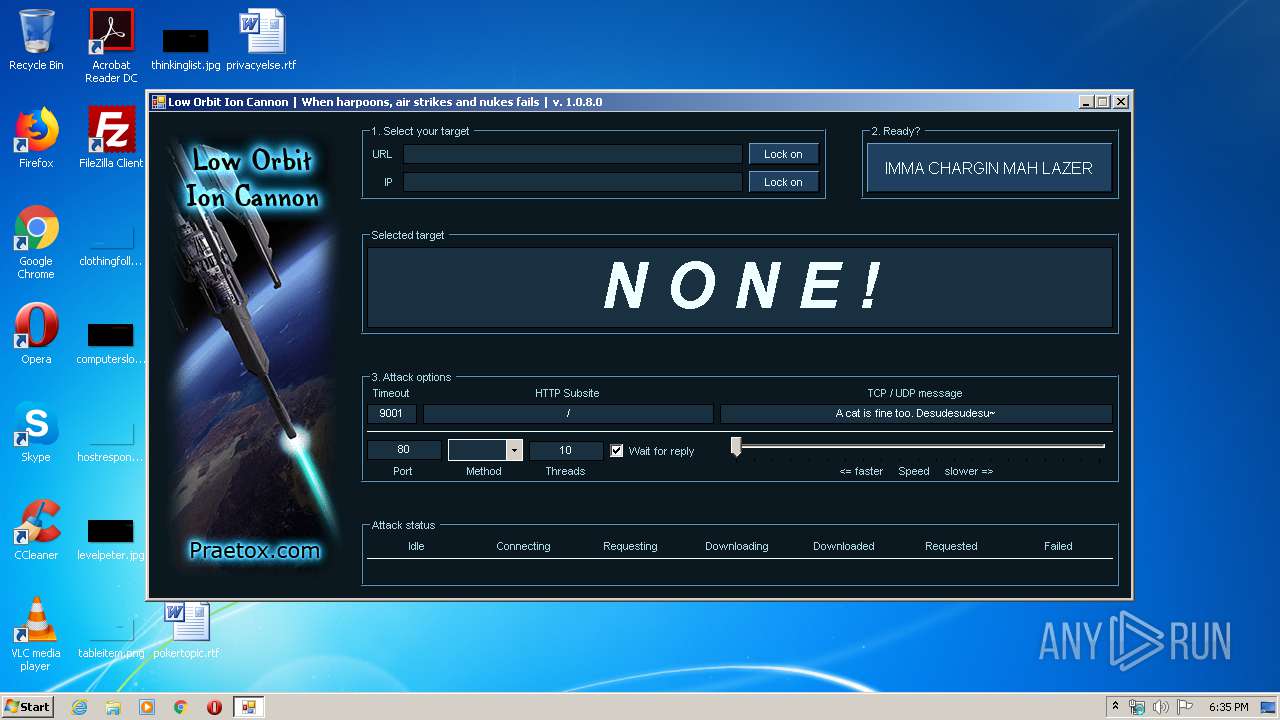
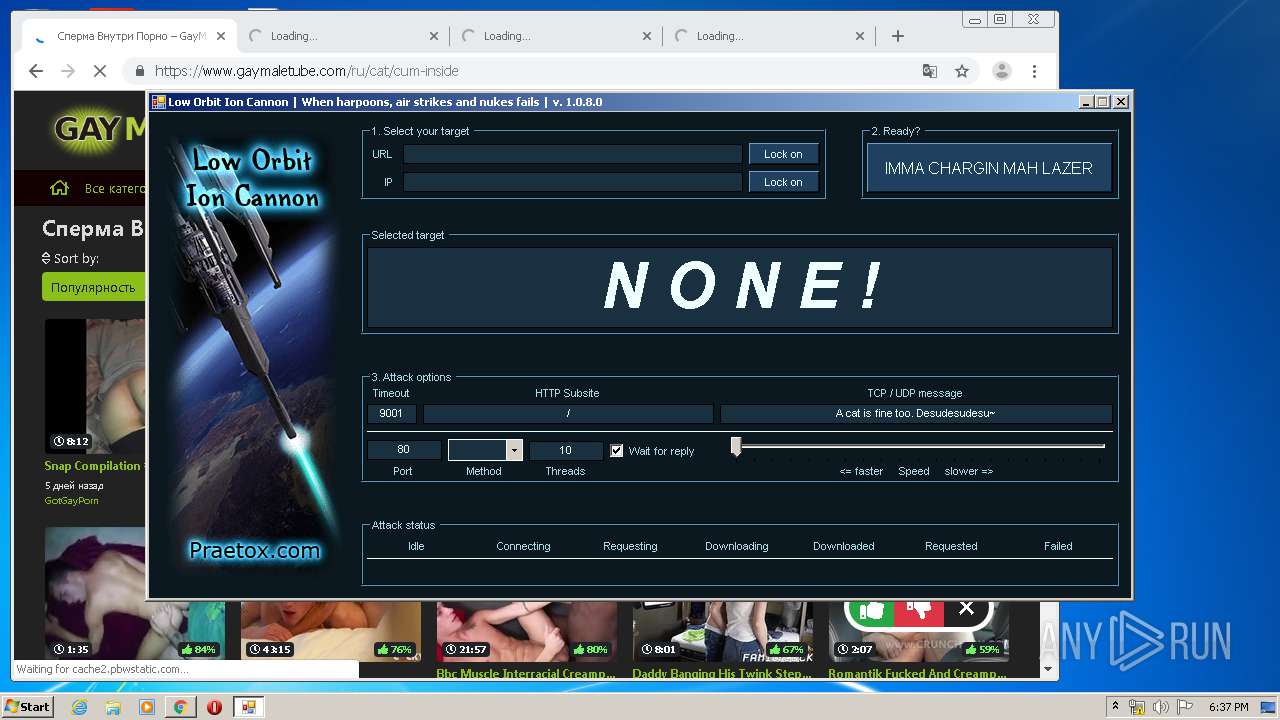
| File name: | LOIC.exe |
| Full analysis: | https://app.any.run/tasks/f9c4f5cd-3750-410b-a7b7-db223631a681 |
| Verdict: | Malicious activity |
| Analysis date: | April 06, 2020, 17:35:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | E6FA3028CD03318496852718143D256F |
| SHA1: | 4C85973D612CD1955163C244C9C334D3A0C507CB |
| SHA256: | F60A52512773B52DEF9BA9CE8AAD61144D2CF351F6BC04D1C5A13ABEF8F3B89B |
| SSDEEP: | 3072:aMGPLnkqtBoZ9B8ocW48kLcOpd29oRFdf:aZP7dXoZ9B8GJkVrd |
MALICIOUS
No malicious indicators.SUSPICIOUS
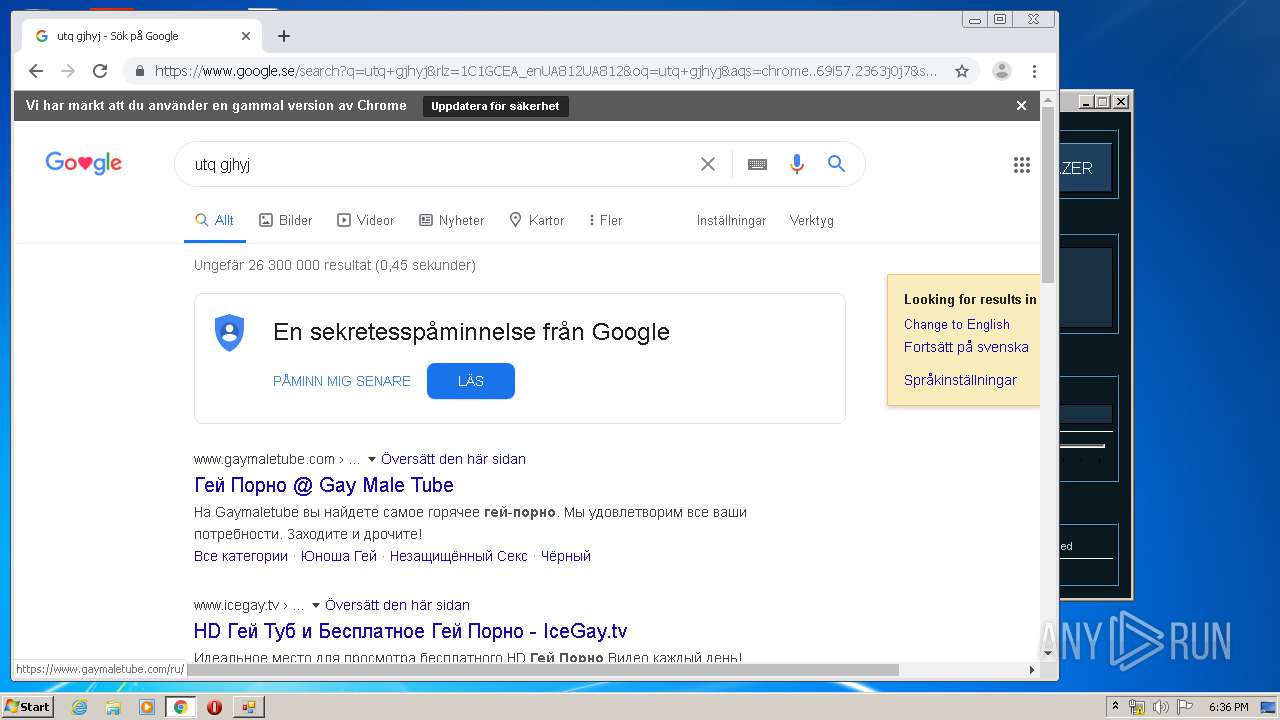
Modifies files in Chrome extension folder
- chrome.exe (PID: 880)
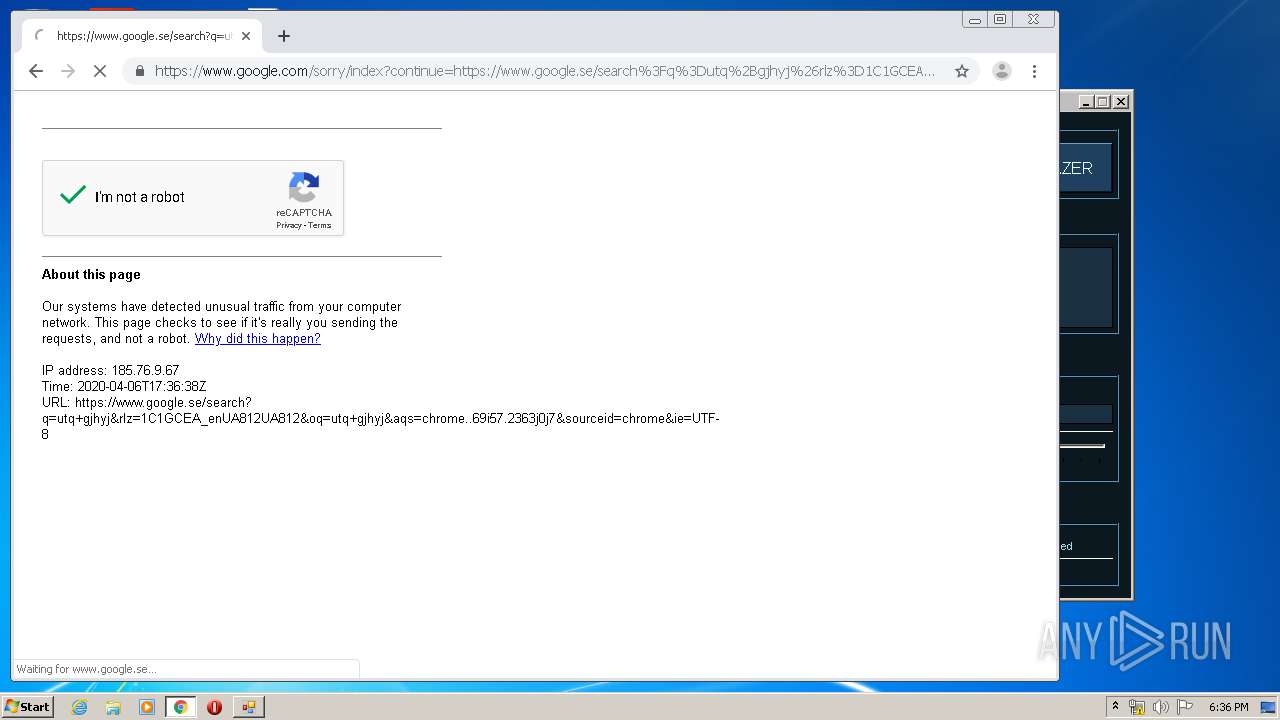
Reads Internet Cache Settings
- LOIC.exe (PID: 3004)
INFO
Creates files in the user directory
- opera.exe (PID: 3176)
Manual execution by user
- opera.exe (PID: 3176)
- chrome.exe (PID: 880)
Reads the hosts file
- chrome.exe (PID: 880)
- chrome.exe (PID: 3980)
Application launched itself
- chrome.exe (PID: 880)
Reads settings of System Certificates
- chrome.exe (PID: 3980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2014:12:13 06:09:01+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 115712 |
| InitializedDataSize: | 19968 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1e22e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.8.0 |
| ProductVersionNumber: | 1.0.8.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | TCP/IP stress-test tool |
| FileDescription: | Low Orbit Ion Cannon |
| FileVersion: | 1.0.8.0 |
| InternalName: | LOIC.exe |
| LegalCopyright: | Public domain |
| OriginalFileName: | LOIC.exe |
| ProductName: | Low Orbit Ion Cannon |
| ProductVersion: | 1.0.8.0 |
| AssemblyVersion: | 1.0.8.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Dec-2014 05:09:01 |
| Debug artifacts: |
|
| Comments: | TCP/IP stress-test tool |
| FileDescription: | Low Orbit Ion Cannon |
| FileVersion: | 1.0.8.0 |
| InternalName: | LOIC.exe |
| LegalCopyright: | Public domain |
| OriginalFilename: | LOIC.exe |
| ProductName: | Low Orbit Ion Cannon |
| ProductVersion: | 1.0.8.0 |
| Assembly Version: | 1.0.8.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 13-Dec-2014 05:09:01 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0001C234 | 0x0001C400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.57679 |
.rsrc | 0x00020000 | 0x00004B40 | 0x00004C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.52139 |
.reloc | 0x00026000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 6.3006 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 6.12381 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 6.30411 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 5.97706 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.68598 | 62 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
84
Monitored processes
48
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,6990541844280801657,5110852181289768632,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4125048657713644672 --mojo-platform-channel-handle=3888 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,6990541844280801657,5110852181289768632,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6211416307047514009 --mojo-platform-channel-handle=4156 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,6990541844280801657,5110852181289768632,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6254796083179504391 --mojo-platform-channel-handle=4376 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,6990541844280801657,5110852181289768632,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10503602710626587508 --renderer-client-id=40 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4608 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,6990541844280801657,5110852181289768632,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7452327867587046088 --mojo-platform-channel-handle=3828 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,6990541844280801657,5110852181289768632,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8471127463621103691 --renderer-client-id=44 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3336 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,6990541844280801657,5110852181289768632,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16031176051083143369 --mojo-platform-channel-handle=3904 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,6990541844280801657,5110852181289768632,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3289381189872379118 --mojo-platform-channel-handle=3988 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x671ea9d0,0x671ea9e0,0x671ea9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 046
Read events
837
Write events
204
Delete events
5
Modification events
| (PID) Process: | (3176) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe | |||
| (PID) Process: | (3176) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 880-13230668189219375 |
Value: 259 | |||
| (PID) Process: | (880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
Executable files
0
Suspicious files
263
Text files
375
Unknown types
95
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3176 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr37DC.tmp | — | |
MD5:— | SHA256:— | |||
| 3176 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr382B.tmp | — | |
MD5:— | SHA256:— | |||
| 3176 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00001.tmp | — | |
MD5:— | SHA256:— | |||
| 3176 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\R7QLZ7LASN5FNXA9OKES.temp | — | |
MD5:— | SHA256:— | |||
| 3176 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\oprAB68.tmp | — | |
MD5:— | SHA256:— | |||
| 3176 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\oprB731.tmp | — | |
MD5:— | SHA256:— | |||
| 3176 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\015ELIQO17AHSHC1KOZH.temp | — | |
MD5:— | SHA256:— | |||
| 3176 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\oprBB97.tmp | — | |
MD5:— | SHA256:— | |||
| 3176 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\tasks.xml | xml | |
MD5:FA8F90CCE1DD65539E5860535CE88562 | SHA256:3F6B98852F1A276D582B9F1AD0DE4CBDF7A71B6BCEDB91BBCF69EB32D0A51F37 | |||
| 3176 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\16ec093b8f51508f.customDestinations-ms~RFa74394.TMP | binary | |
MD5:214B1AF678519D9437606E566F2A809F | SHA256:86EFF0172D0DDD27AD4068777C9CFCF2803DB634E380C5F79EDADD82542972FE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
228
DNS requests
172
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
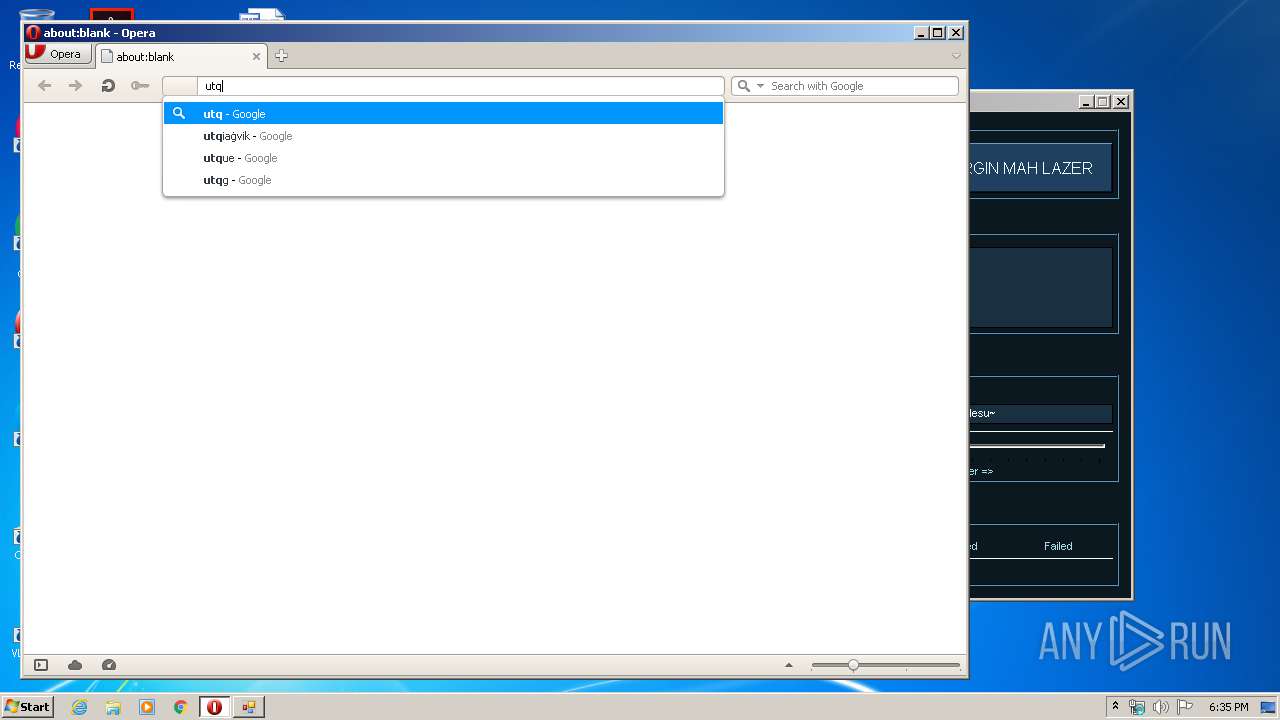
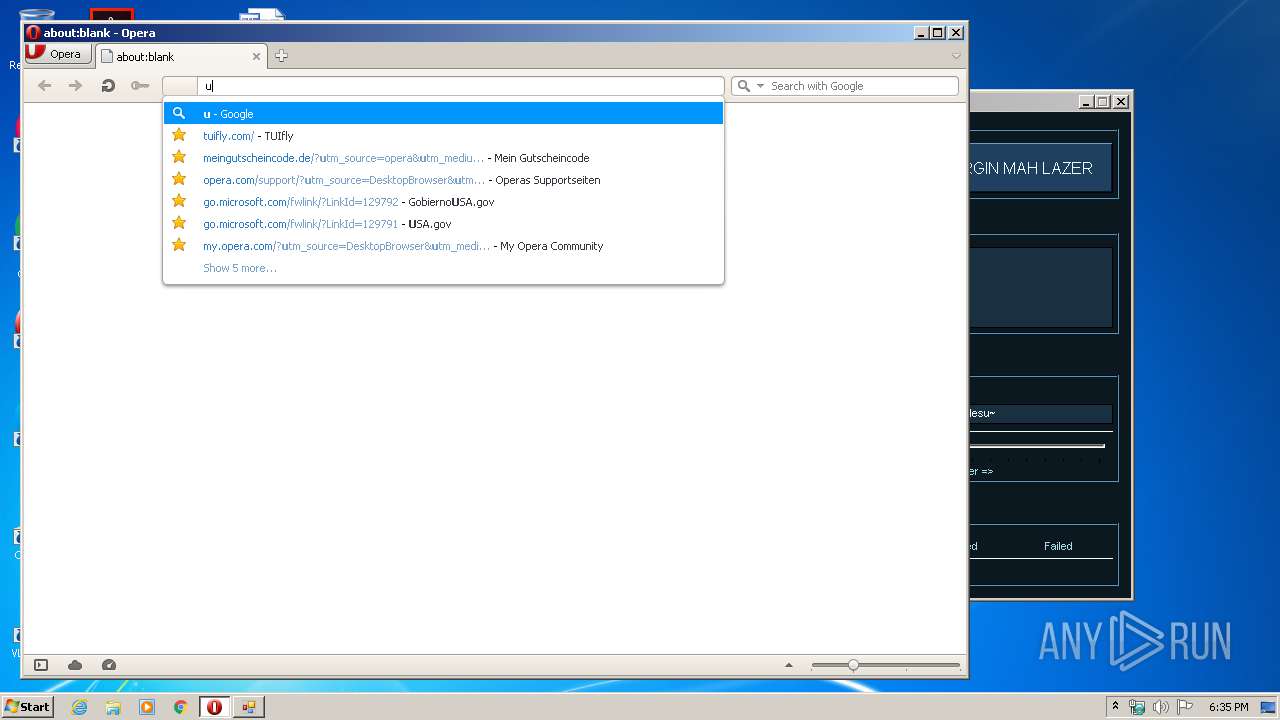
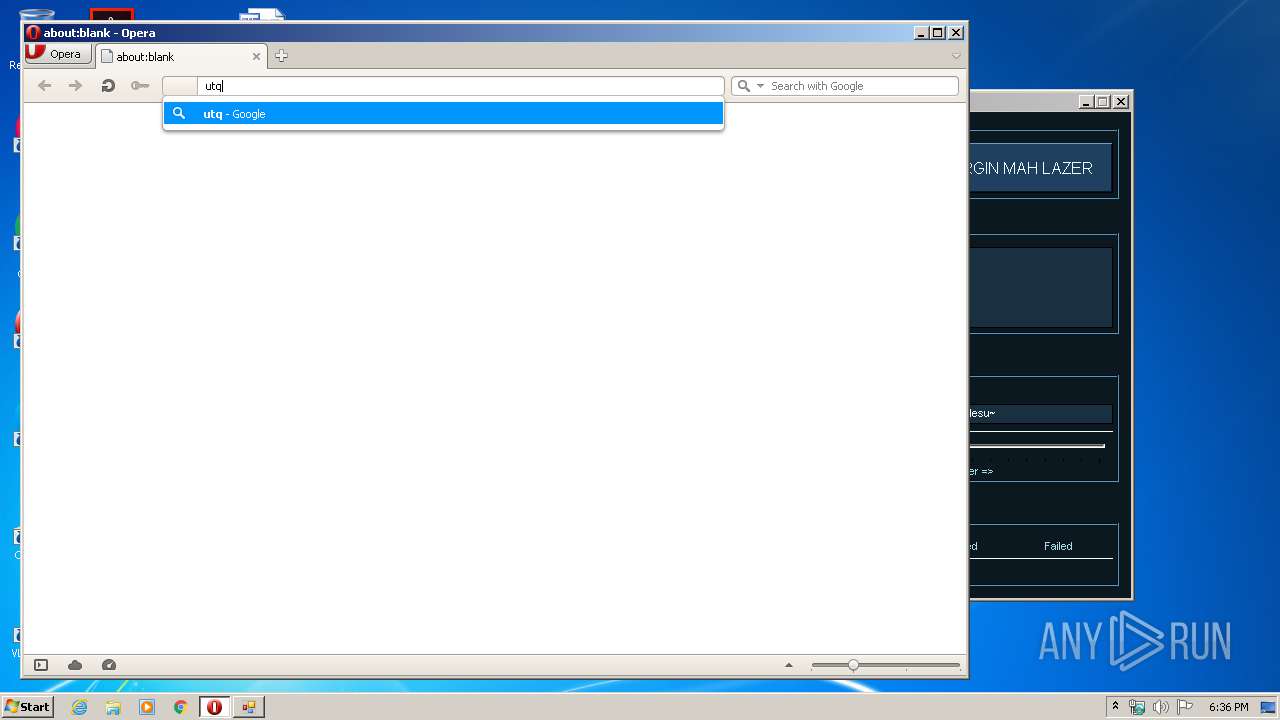
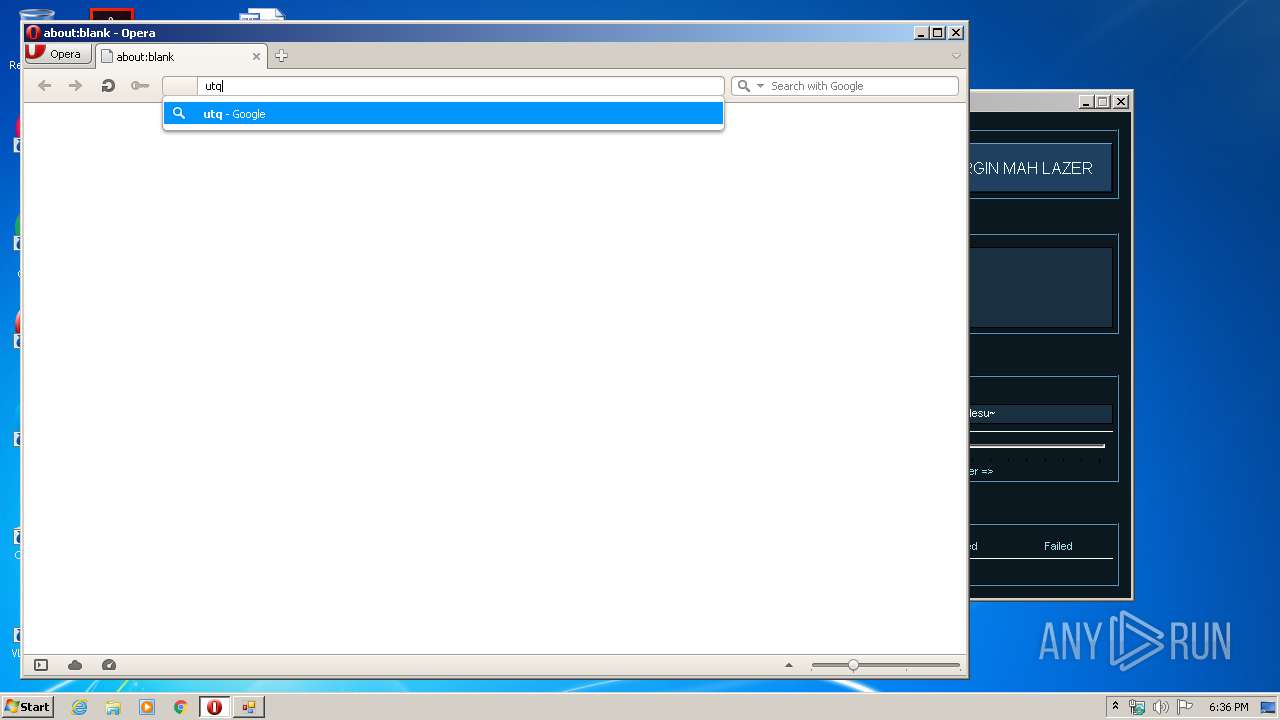
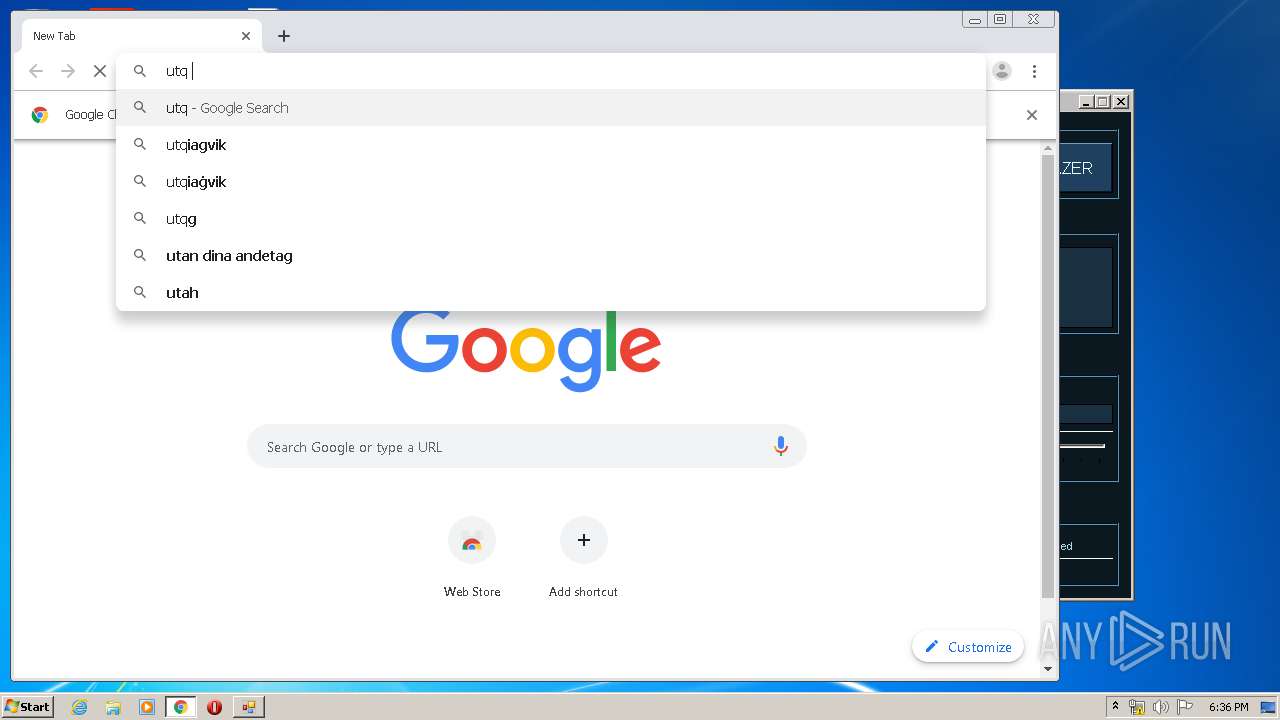
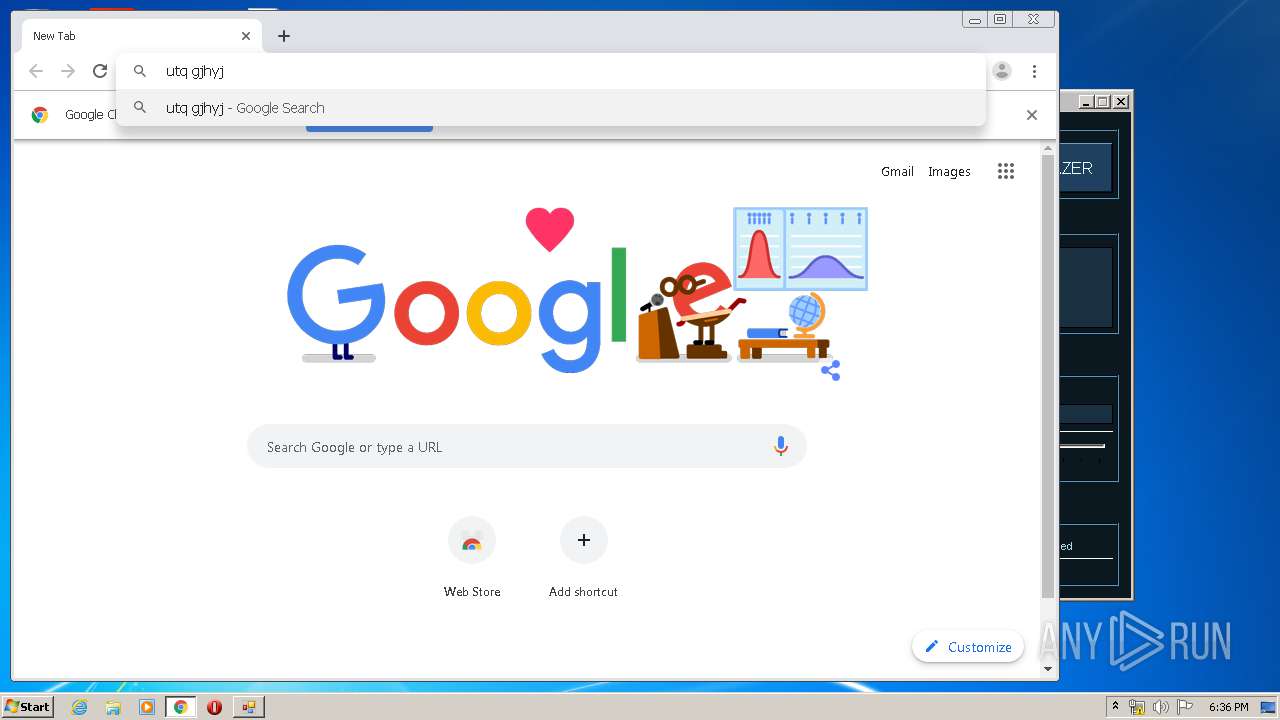
3176 | opera.exe | GET | 200 | 172.217.22.14:80 | http://clients1.google.com/complete/search?q=utq&client=opera-suggest-omnibox&hl=de | US | text | 136 b | whitelisted |
3176 | opera.exe | GET | 200 | 172.217.22.14:80 | http://clients1.google.com/complete/search?q=utq&client=opera-suggest-omnibox&hl=de | US | text | 136 b | whitelisted |
3176 | opera.exe | GET | 200 | 172.217.22.14:80 | http://clients1.google.com/complete/search?q=utq&client=opera-suggest-omnibox&hl=de | US | text | 136 b | whitelisted |
3176 | opera.exe | GET | 200 | 172.217.22.14:80 | http://clients1.google.com/complete/search?q=utq&client=opera-suggest-omnibox&hl=de | US | text | 136 b | whitelisted |
3176 | opera.exe | GET | 200 | 172.217.22.14:80 | http://clients1.google.com/complete/search?q=utq&client=opera-suggest-omnibox&hl=de | US | text | 136 b | whitelisted |
3176 | opera.exe | GET | 200 | 172.217.22.14:80 | http://clients1.google.com/complete/search?q=utq&client=opera-suggest-omnibox&hl=de | US | text | 136 b | whitelisted |
3176 | opera.exe | GET | 400 | 107.167.110.211:80 | http://sitecheck2.opera.com/?host=www.google.com.ua&hdn=Nxr6KEmdGjdmqcWka8dkkA== | US | html | 150 b | whitelisted |
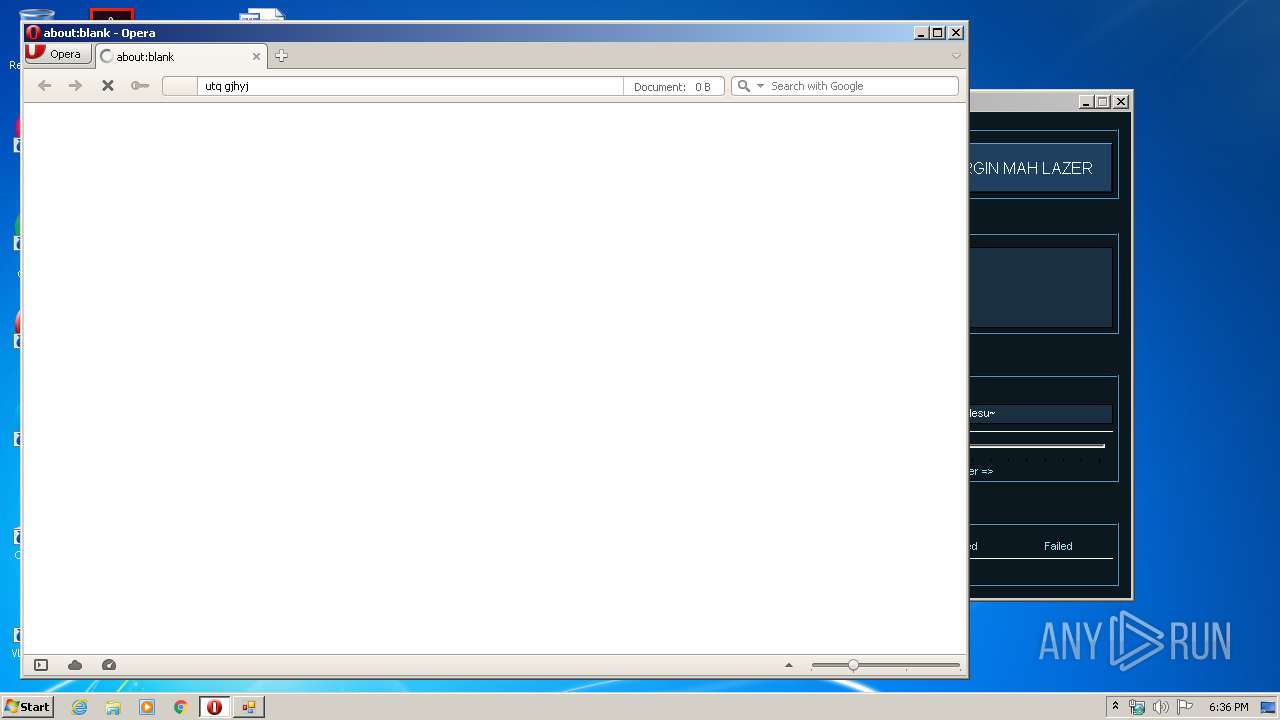
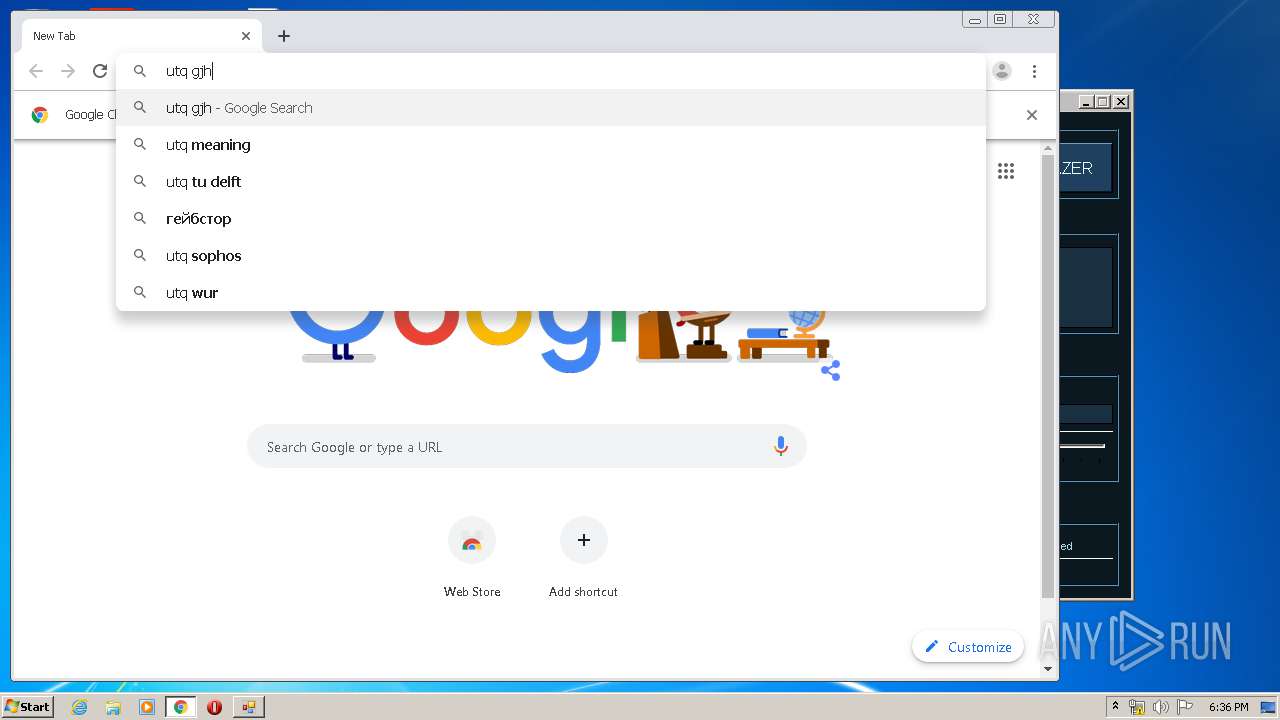
3176 | opera.exe | GET | 200 | 172.217.22.14:80 | http://clients1.google.com/complete/search?q=utq+gjhy&client=opera-suggest-omnibox&hl=de | US | text | 35 b | whitelisted |
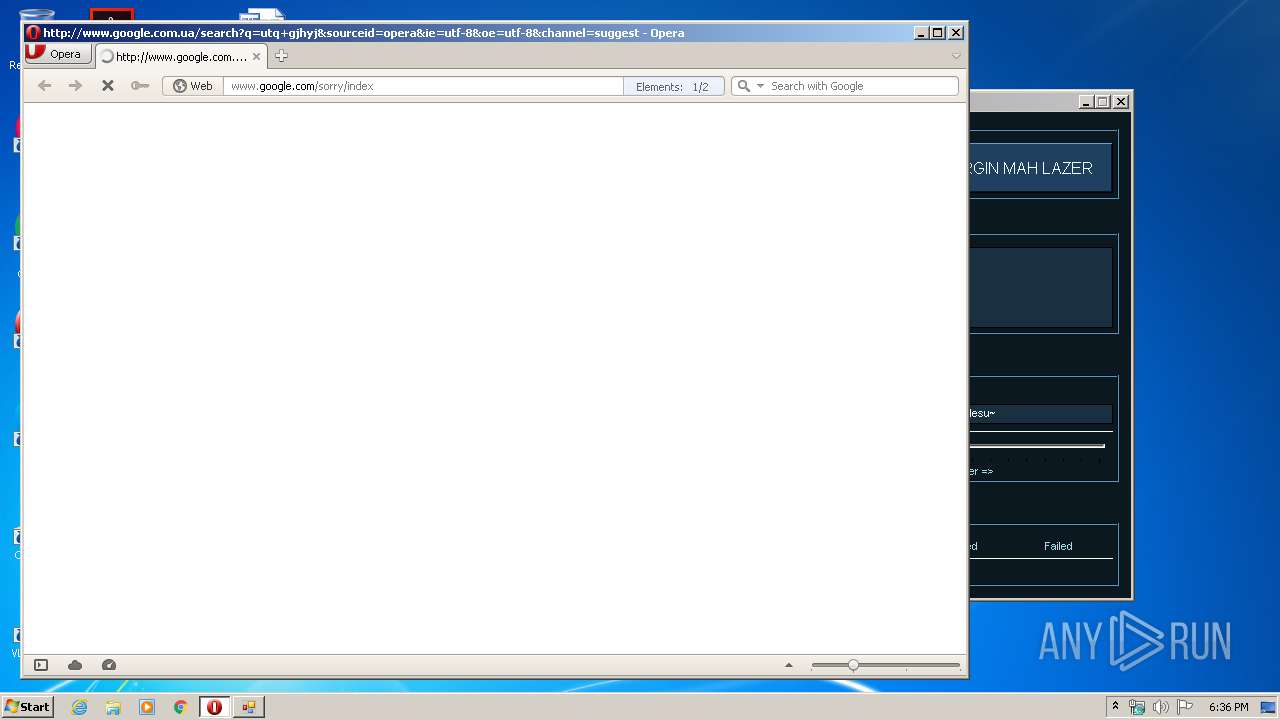
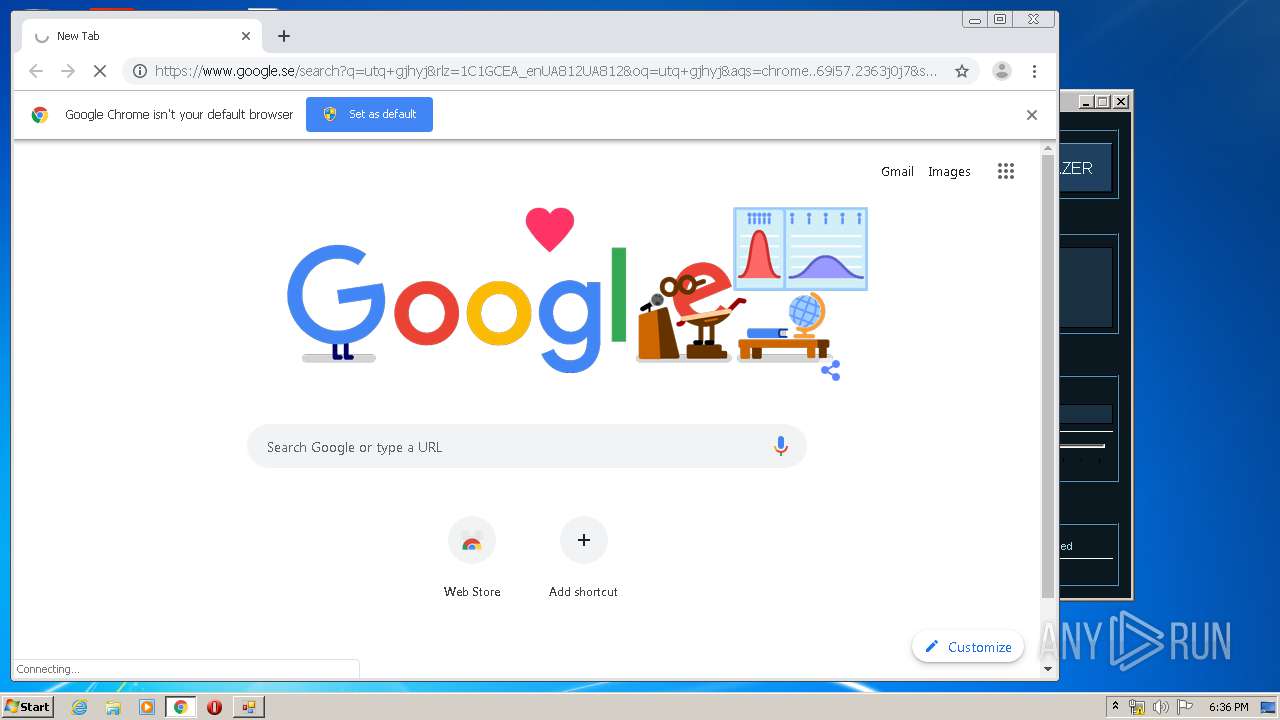
3176 | opera.exe | GET | 302 | 216.58.206.3:80 | http://www.google.com.ua/search?q=utq+gjhyj&sourceid=opera&ie=utf-8&oe=utf-8&channel=suggest | US | html | 417 b | whitelisted |
3176 | opera.exe | GET | 200 | 172.217.22.67:80 | http://crl.pki.goog/gsr2/gsr2.crl | US | der | 950 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3176 | opera.exe | 172.217.22.14:80 | clients1.google.com | Google Inc. | US | whitelisted |
3176 | opera.exe | 216.58.206.3:80 | www.google.com.ua | Google Inc. | US | whitelisted |
3176 | opera.exe | 107.167.110.211:80 | sitecheck2.opera.com | Opera Software Americas LLC | US | suspicious |
3176 | opera.exe | 172.217.16.196:80 | www.google.com | Google Inc. | US | whitelisted |
3176 | opera.exe | 172.217.16.196:443 | www.google.com | Google Inc. | US | whitelisted |
3176 | opera.exe | 172.217.22.67:80 | crl.pki.goog | Google Inc. | US | whitelisted |
3176 | opera.exe | 172.217.16.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3176 | opera.exe | 172.217.18.3:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3980 | chrome.exe | 172.217.16.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3980 | chrome.exe | 216.58.210.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
clients1.google.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
sitecheck2.opera.com |
| whitelisted |
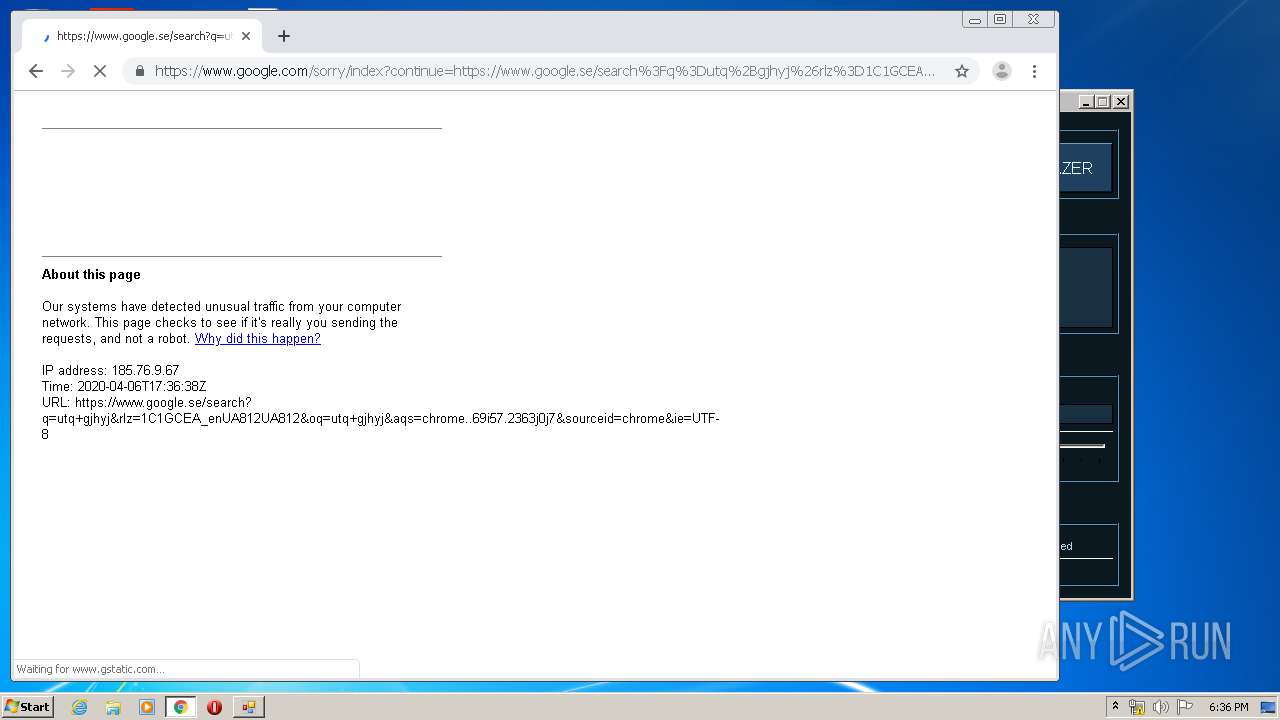
www.google.com |
| malicious |
crl.pki.goog |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
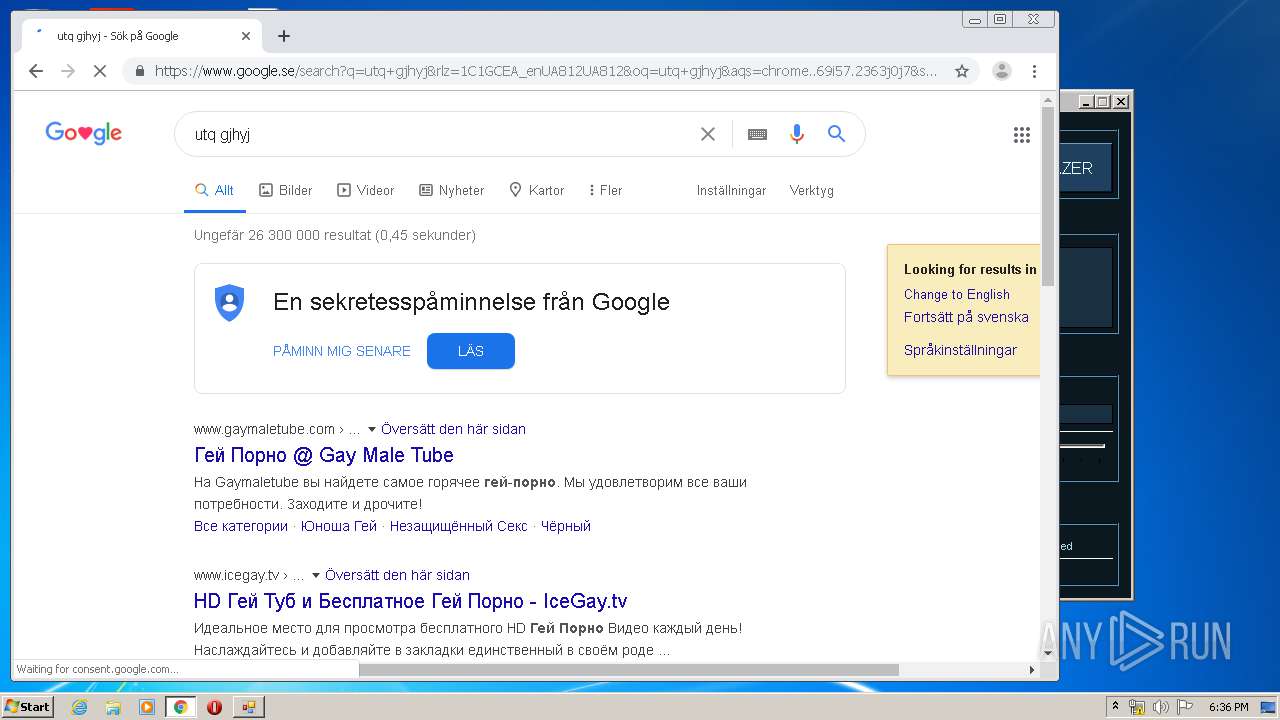
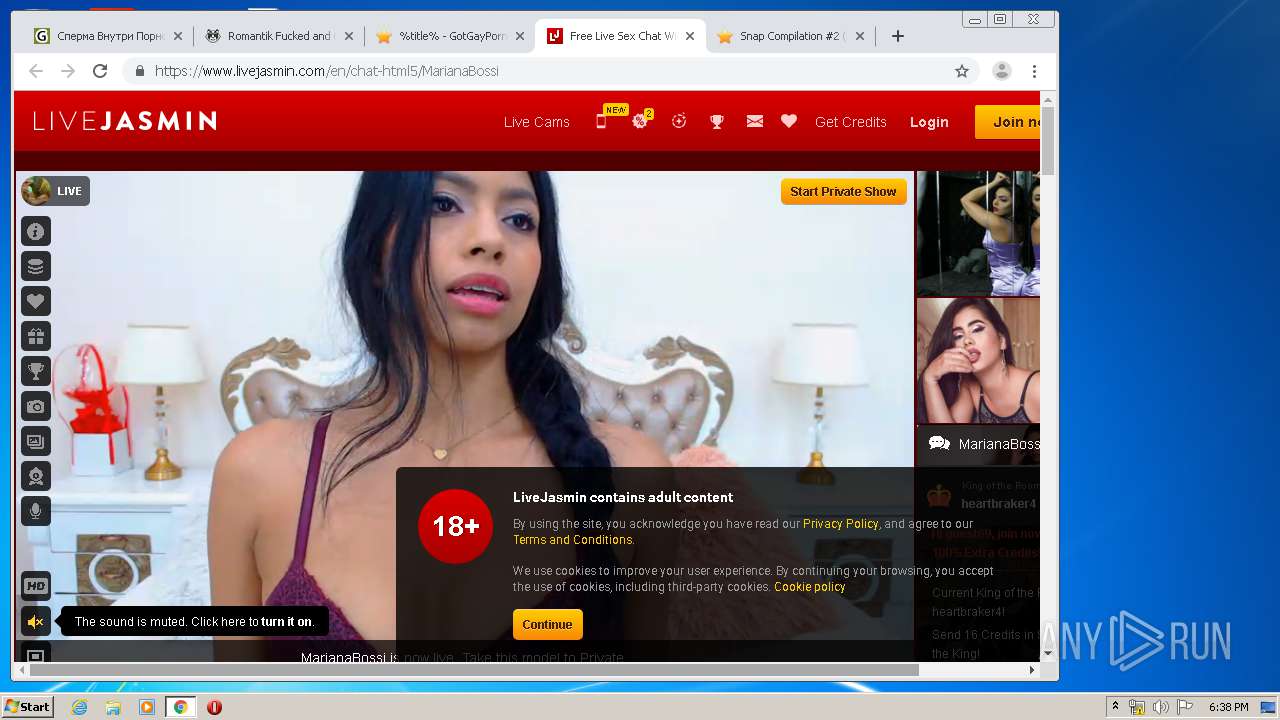
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .desi TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .desi TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .desi TLD |
1052 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query For XXX Adult Site Top Level Domain |