| File name: | P72.exe |
| Full analysis: | https://app.any.run/tasks/7fec229e-34e7-42dc-b701-30a9cbb0fb61 |
| Verdict: | Malicious activity |
| Analysis date: | July 31, 2022, 17:54:48 |
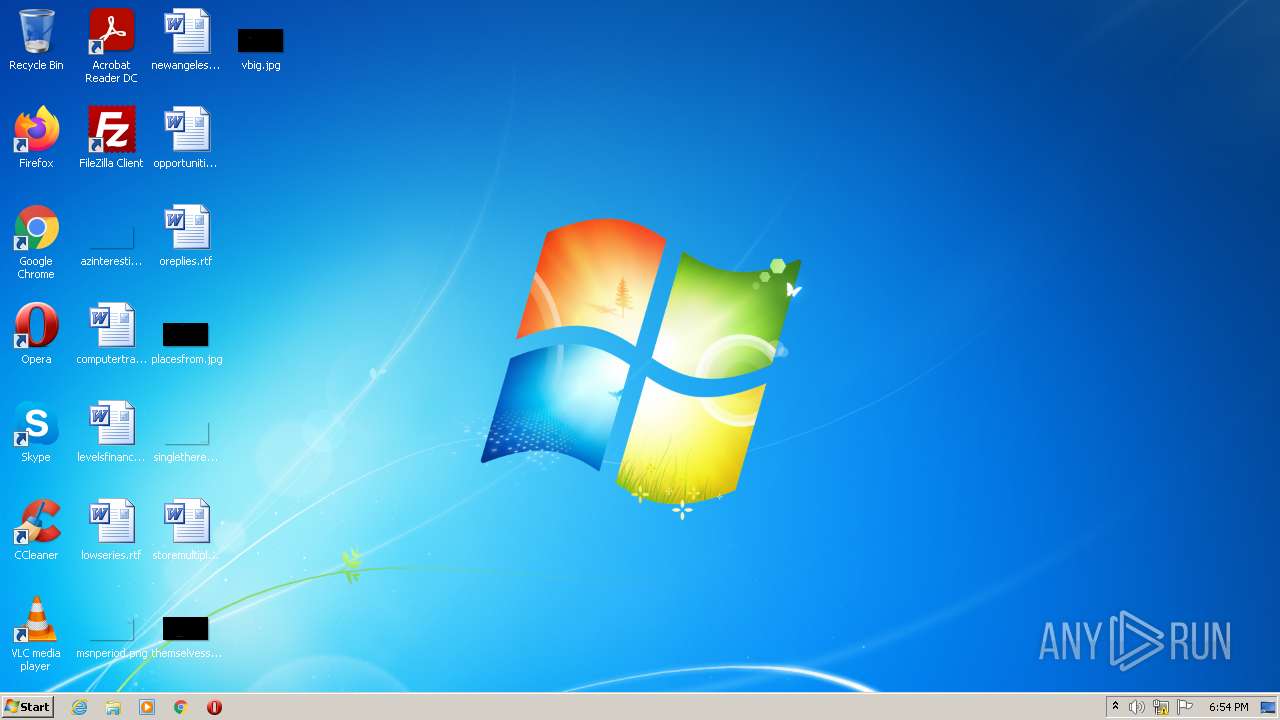
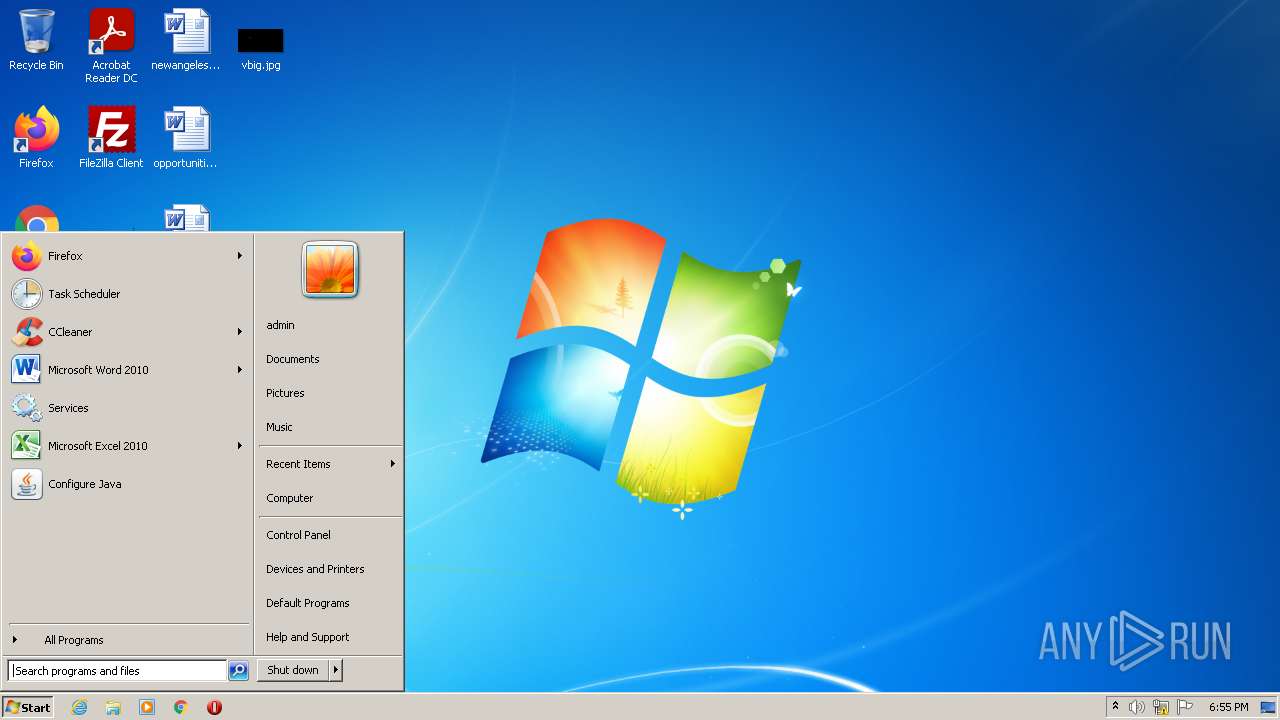
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 20963A476928F3AAD040AFFC4980E5F5 |
| SHA1: | B1254D5069B4A38608D0724E2485701DD8BF0DC2 |
| SHA256: | F6072FF57C1CFE74B88F521D70C524BCBBB60C561705E9FEBE033F51131BE408 |
| SSDEEP: | 3072:4SNTPzB1fdiGuNbvAzJ7ZGNWmhOgLe4+zOWeIclqi+vUAzZhkj:7Vv/dcN3OaWFlzw |
MALICIOUS
Drops executable file immediately after starts
- P72.exe (PID: 2972)
SUSPICIOUS
Checks supported languages
- P72.exe (PID: 2972)
Reads the computer name
- P72.exe (PID: 2972)
Writes to a desktop.ini file (may be used to cloak folders)
- P72.exe (PID: 2972)
Drops a file with a compile date too recent
- P72.exe (PID: 2972)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x8910 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 38400 |
| CodeSize: | 76800 |
| LinkerVersion: | 14.16 |
| PEType: | PE32 |
| TimeStamp: | 2022:07:25 02:55:15+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Jul-2022 00:55:15 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 25-Jul-2022 00:55:15 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00012B45 | 0x00012C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60429 |
.rdata | 0x00014000 | 0x00005AFE | 0x00005C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.00687 |
.data | 0x0001A000 | 0x00002750 | 0x00001C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.40723 |
.reloc | 0x0001D000 | 0x000011BC | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.58792 |
Imports
KERNEL32.dll |
Total processes
33
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2972 | "C:\Users\admin\AppData\Local\Temp\P72.exe" | C:\Users\admin\AppData\Local\Temp\P72.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
285
Read events
285
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
300
Text files
1
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2972 | P72.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\AccLR.cab | — | |
MD5:— | SHA256:— | |||
| 2972 | P72.exe | C:\MSOCache\All Users\{90140000-0015-040C-0000-0000000FF1CE}-C\AccLR.cab | — | |
MD5:— | SHA256:— | |||
| 2972 | P72.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\AccessMUI.xml | binary | |
MD5:— | SHA256:— | |||
| 2972 | P72.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\desktop.ini | binary | |
MD5:— | SHA256:— | |||
| 2972 | P72.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\Setup.xml | binary | |
MD5:— | SHA256:— | |||
| 2972 | P72.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\desktop.ini.PLAY | binary | |
MD5:— | SHA256:— | |||
| 2972 | P72.exe | C:\MSOCache\All Users\{90140000-0015-0410-0000-0000000FF1CE}-C\AccLR.cab | — | |
MD5:— | SHA256:— | |||
| 2972 | P72.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\AccessMUI.xml.PLAY | binary | |
MD5:— | SHA256:— | |||
| 2972 | P72.exe | C:\MSOCache\All Users\{90140000-0015-0411-0000-0000000FF1CE}-C\AccLR.cab | — | |
MD5:— | SHA256:— | |||
| 2972 | P72.exe | C:\Users\admin\AppData\Local\VirtualStore\ReadMe.txt | text | |
MD5:DD5FAE9E93C3B4718C7D42CC2869154A | SHA256:99D73E7322DE2BAE90801E86FA241ED831EB3520935CA7C8C581AD90AD961309 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
6
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.2:445 | — | — | — | whitelisted |