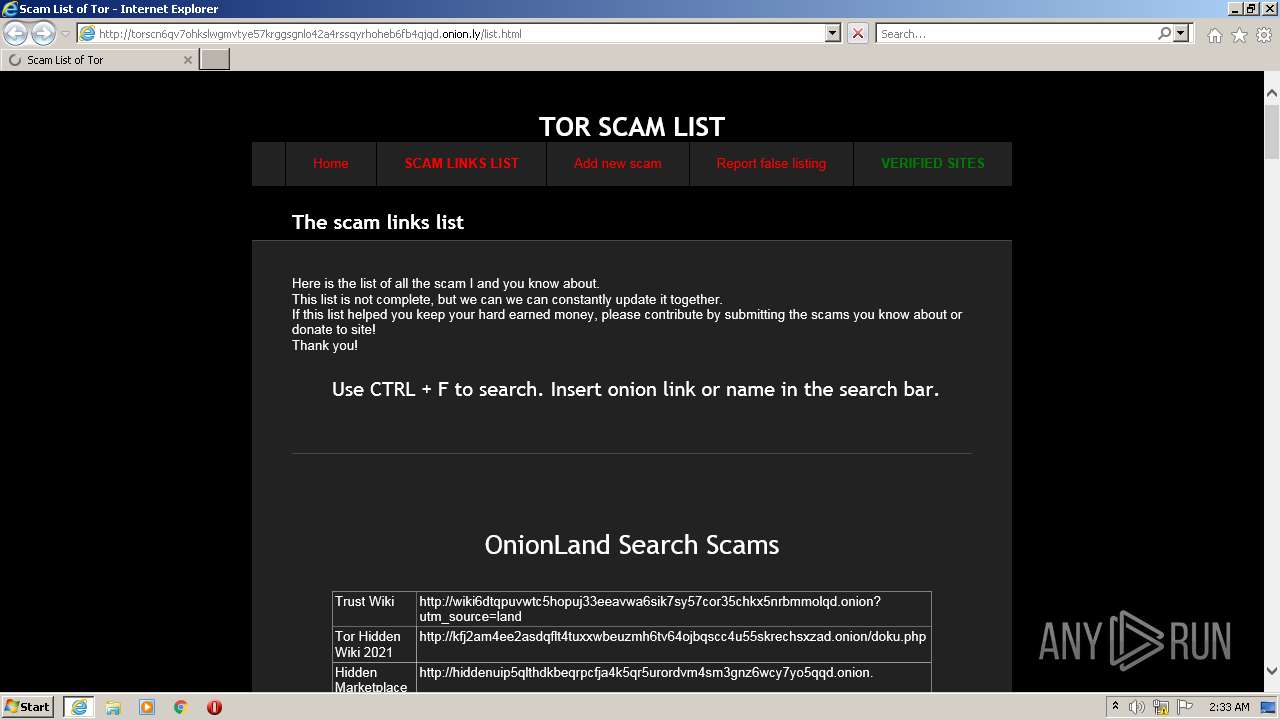
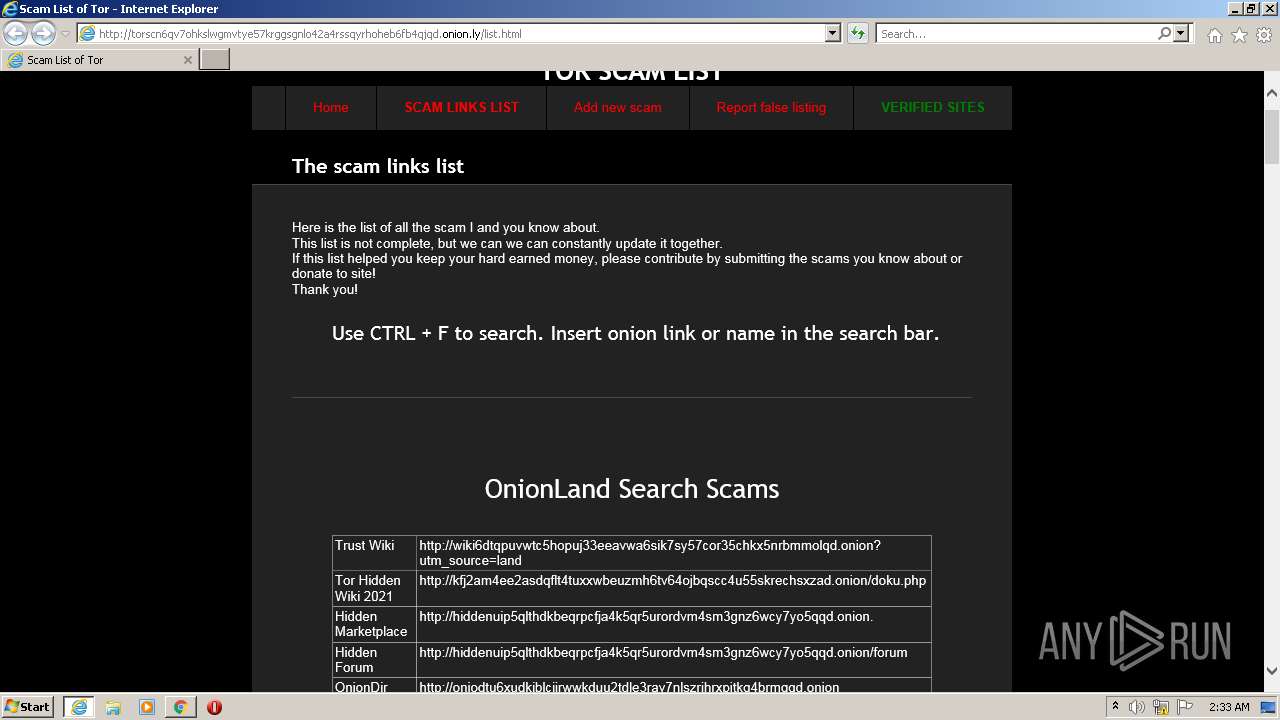
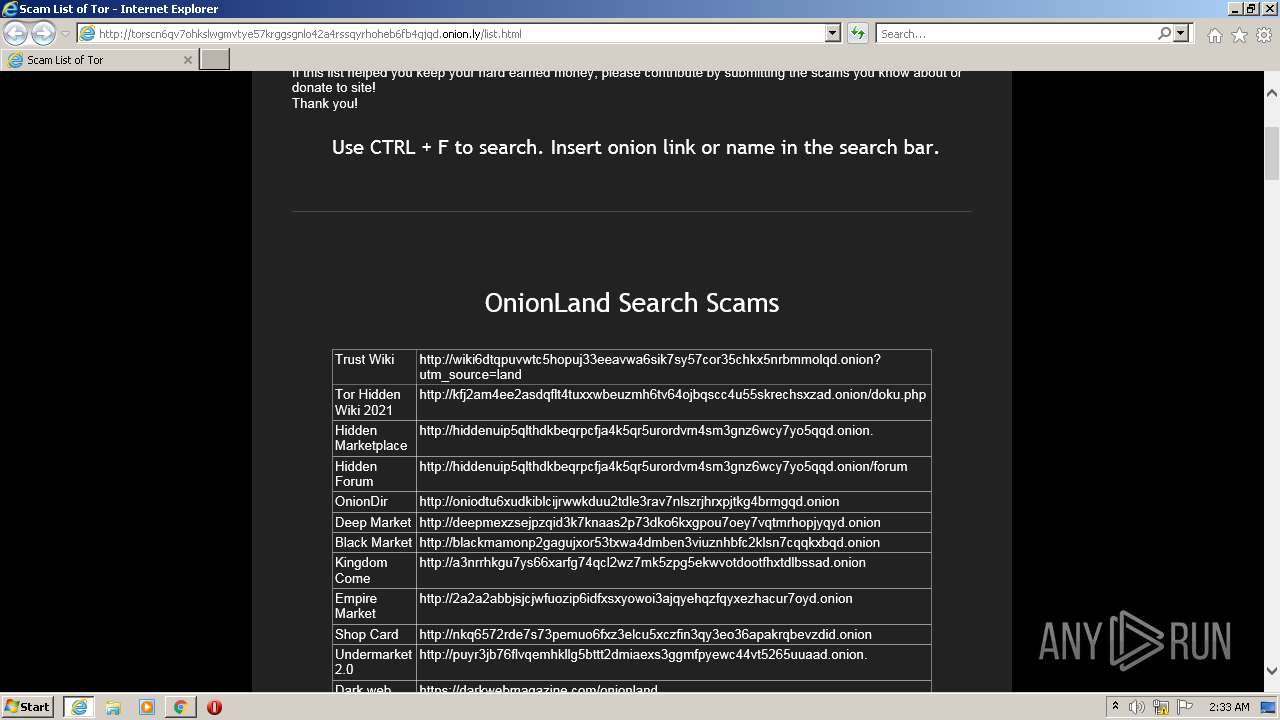
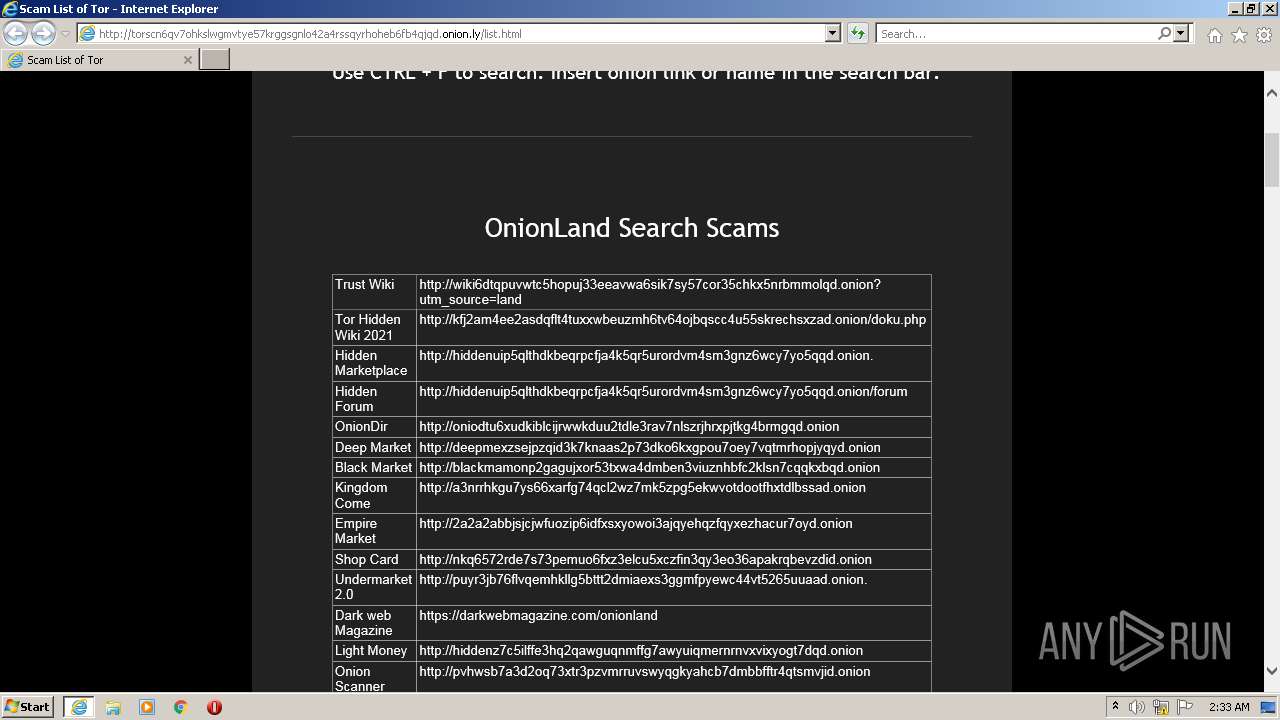
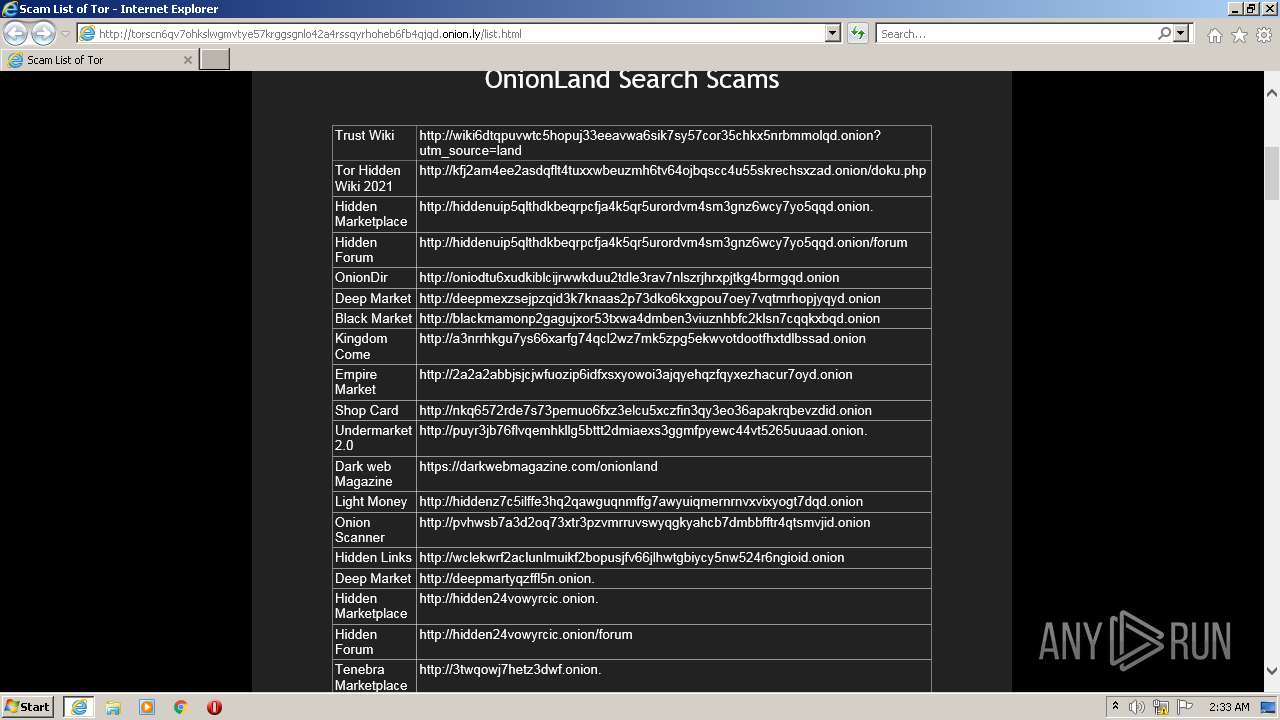
| URL: | http://torscn6qv7ohkslwgmvtye57krggsgnlo42a4rssqyrhoheb6fb4qjqd.onion.ly/list.html |
| Full analysis: | https://app.any.run/tasks/dac783dd-9a73-4a60-926c-79f57993f25c |
| Verdict: | Malicious activity |
| Analysis date: | January 15, 2022, 02:33:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 15DAE60861D0B9C4F849CD10E6FB93E9 |
| SHA1: | A0EB474CA80B772160EC0ED7A38B6B22B7917992 |
| SHA256: | F603BB24DDF3E8002CA7588E6D809EA2C6EB8BE171D84EFB05B983B929C40B90 |
| SSDEEP: | 3:N1KKKGFNsKQ0KRXEQCYNAfRWULecMQ:CKVNsKQzxvKWUD |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1708)
INFO
Checks supported languages
- iexplore.exe (PID: 3204)
- iexplore.exe (PID: 1708)
Reads the computer name
- iexplore.exe (PID: 1708)
- iexplore.exe (PID: 3204)
Application launched itself
- iexplore.exe (PID: 3204)
Reads internet explorer settings
- iexplore.exe (PID: 1708)
Changes internet zones settings
- iexplore.exe (PID: 3204)
Reads settings of System Certificates
- iexplore.exe (PID: 1708)
- iexplore.exe (PID: 3204)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 1708)
Checks Windows Trust Settings
- iexplore.exe (PID: 1708)
- iexplore.exe (PID: 3204)
Creates files in the user directory
- iexplore.exe (PID: 1708)
Dropped object may contain URL to Tor Browser
- iexplore.exe (PID: 3204)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1708 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3204 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3204 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://torscn6qv7ohkslwgmvtye57krggsgnlo42a4rssqyrhoheb6fb4qjqd.onion.ly/list.html" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
13 162
Read events
13 047
Write events
115
Delete events
0
Modification events
| (PID) Process: | (3204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30935480 | |||
| (PID) Process: | (3204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30935480 | |||
| (PID) Process: | (3204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
8
Text files
10
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3204 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:7AE581655E90CE9CD48FA48A1D9FD7E9 | SHA256:92C8D2F9993EAB8A3CBD47963A67CD002AFECBD7C3473CD33C804ED9927327D3 | |||
| 1708 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\list[1].html | html | |
MD5:A4A0F5E2E607A2331322305271866914 | SHA256:E2991222A836944D3E173B6215A25872D922A4C2306730CF5A4D12871F8961A8 | |||
| 3204 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:AC68ACF50745357D4EA92B214D9E7132 | SHA256:AE3F7FDE380D2D90571A61378E52B1BC284B4C4C6A1E099F6F022395EBED6154 | |||
| 3204 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:7DA1BCD167CC222293DE24155C34DD99 | SHA256:FB67CD1ED680A768577340777946F4C49D7072D61FF1A86FC5D236D58ADAC5EA | |||
| 1708 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:396CD69662FC1EE91DEC0FBE75F6B932 | SHA256:3FA83246A192B81A9A5C4DBDF59E4B15178DCBAB95D98F6139C625548F027E42 | |||
| 1708 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | binary | |
MD5:D95A7EEC256BC45121E49F102C77681F | SHA256:EE5FDB835429B6CD38E3736A9E36D26947DB18E92ADBFE293FA90870DD3B022A | |||
| 1708 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\C1DV34MI.txt | text | |
MD5:72B049AB6209910741DF7812C09956F9 | SHA256:D06B426FA643E06A03884CA0974AB58EDC747D356FB4571AB05869F315EDC870 | |||
| 1708 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:2663BED1F902BED00647B84FABBF8DEA | SHA256:7A3C6A8BE401F6DE91999C00919EA0F3BDCF80D06EB0E8A15D801F8F9A465DE9 | |||
| 1708 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | der | |
MD5:64E9B8BB98E2303717538CE259BEC57D | SHA256:76BD459EC8E467EFC3E3FB94CB21B9C77A2AA73C9D4C0F3FAF823677BE756331 | |||
| 1708 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\OTXM1EPW.txt | text | |
MD5:A7CBC64BE9EC8A3BAAEA7DA3300EFD53 | SHA256:2E4606BC7C9135C6D9681F36B91044011B673CECD2D68D4C10DF4847B3E5A8C5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
24
DNS requests
13
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1708 | iexplore.exe | GET | 200 | 203.28.246.190:80 | http://torscn6qv7ohkslwgmvtye57krggsgnlo42a4rssqyrhoheb6fb4qjqd.onion.ly/css/main.css | AU | text | 1.87 Kb | malicious |
1708 | iexplore.exe | GET | 200 | 203.28.246.190:80 | http://torscn6qv7ohkslwgmvtye57krggsgnlo42a4rssqyrhoheb6fb4qjqd.onion.ly/list.html | AU | html | 8.26 Kb | malicious |
3204 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
1708 | iexplore.exe | GET | 200 | 178.79.242.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?cf95c5ff4f4a00f9 | DE | compressed | 4.70 Kb | whitelisted |
3204 | iexplore.exe | GET | 200 | 178.79.242.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?827d66014578e129 | DE | compressed | 4.70 Kb | whitelisted |
1708 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3204 | iexplore.exe | GET | 200 | 203.28.246.190:80 | http://torscn6qv7ohkslwgmvtye57krggsgnlo42a4rssqyrhoheb6fb4qjqd.onion.ly/favicon.ico | AU | html | 15.0 Kb | malicious |
1708 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCAnDacZA1UWwoAAAABJ9nq | US | der | 472 b | whitelisted |
1708 | iexplore.exe | GET | 200 | 178.79.242.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a6efc47fc83b78c4 | DE | compressed | 4.70 Kb | whitelisted |
1708 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1708 | iexplore.exe | 142.250.185.200:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
1708 | iexplore.exe | 203.28.246.190:80 | torscn6qv7ohkslwgmvtye57krggsgnlo42a4rssqyrhoheb6fb4qjqd.onion.ly | The University of Melbourne, Melbourne, Victoria | AU | malicious |
1708 | iexplore.exe | 178.79.242.0:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | DE | whitelisted |
3204 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3204 | iexplore.exe | 178.79.242.0:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | DE | whitelisted |
3204 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1708 | iexplore.exe | 142.250.185.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3204 | iexplore.exe | 203.28.246.190:80 | torscn6qv7ohkslwgmvtye57krggsgnlo42a4rssqyrhoheb6fb4qjqd.onion.ly | The University of Melbourne, Melbourne, Victoria | AU | malicious |
1708 | iexplore.exe | 142.250.186.174:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3204 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
torscn6qv7ohkslwgmvtye57krggsgnlo42a4rssqyrhoheb6fb4qjqd.onion.ly |
| malicious |
www.googletagmanager.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.google-analytics.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query to .onion proxy Domain (onion . ly) |