| File name: | RServer.exe |
| Full analysis: | https://app.any.run/tasks/1ea1a190-4bb5-41ae-ab2d-db86b4fc9fa3 |
| Verdict: | Malicious activity |
| Analysis date: | May 12, 2025, 14:48:21 |
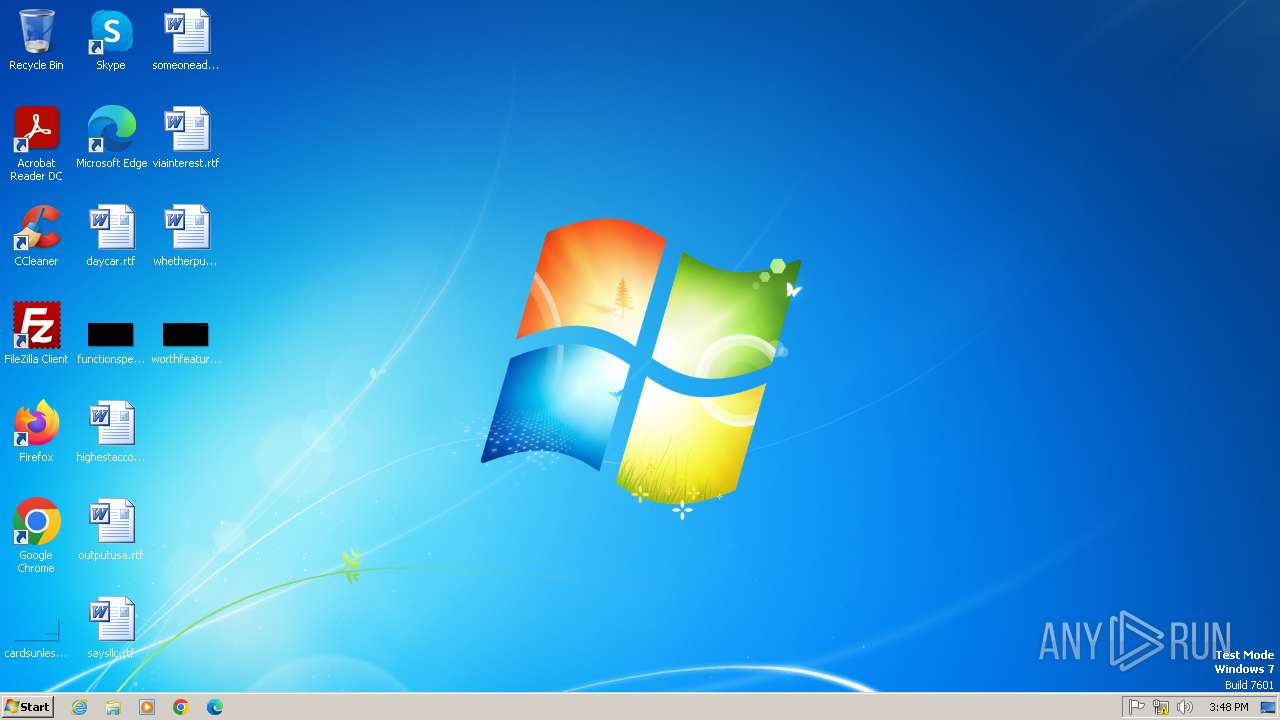
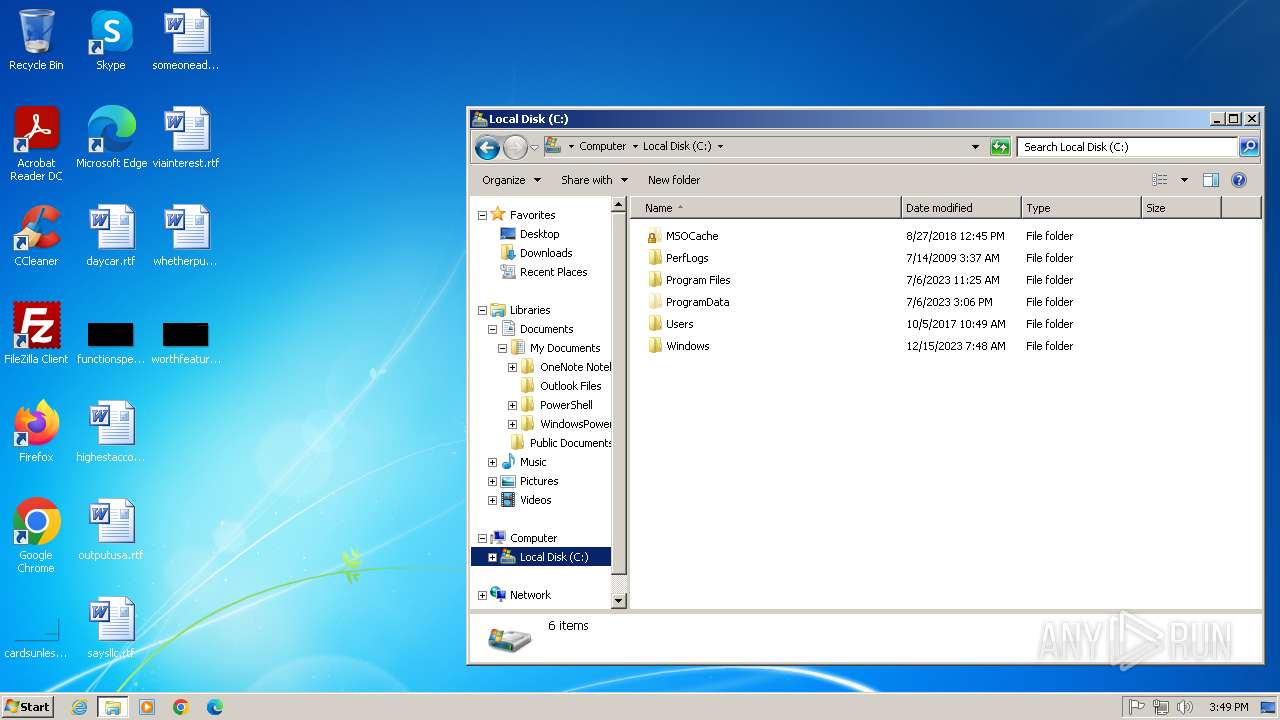
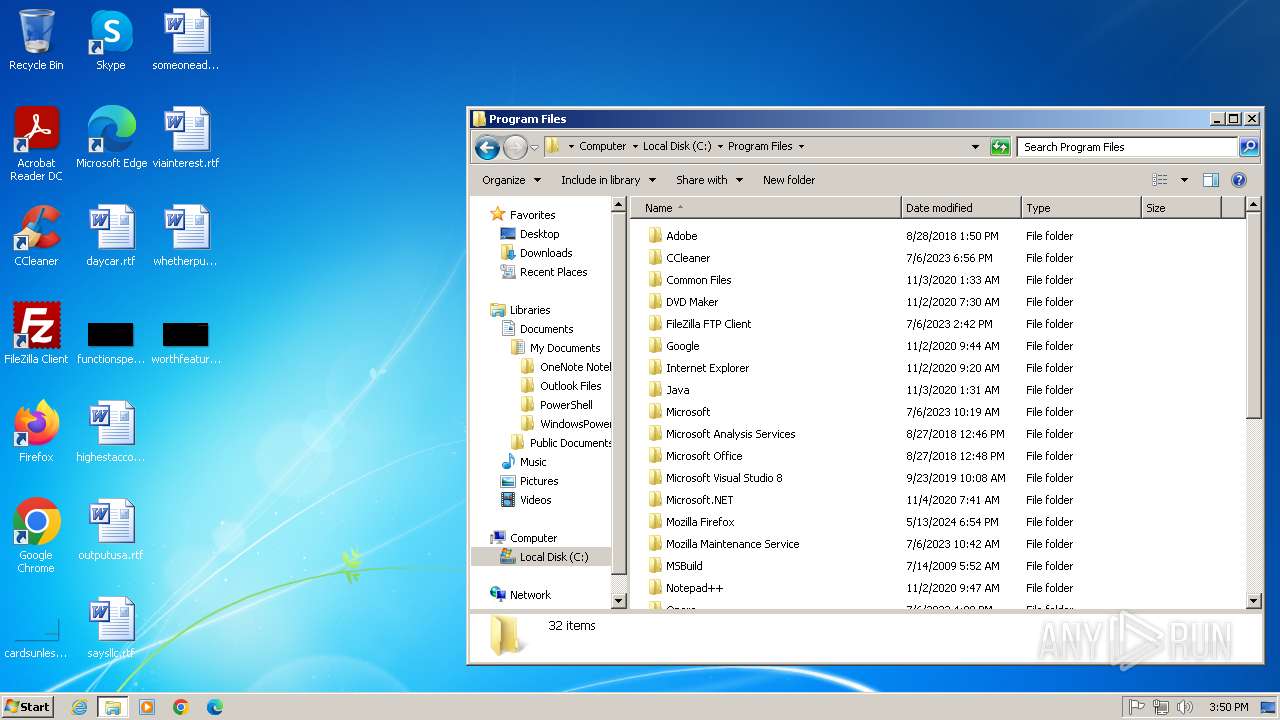
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | 94DF301A9842D3E1A42B6FAE69359B70 |
| SHA1: | 2139D1924EE9F5362727A7F18275FF2A9A01C4A1 |
| SHA256: | F5F2B3FFFFD401895B66C2254703425A800B4E288FFCDF9A3C34A9E953621696 |
| SSDEEP: | 98304:MfeGPE+mYjHS9dry54DP9+gAQdaCnnLt2kC0FiOwYQ7U0D6w7edEDaF0o5+ZVvhj:wKAS |
MALICIOUS
Executing a file with an untrusted certificate
- rsetup.exe (PID: 3124)
- rsetup.exe (PID: 1980)
- rserver3.exe (PID: 2872)
- FamItrfc.Exe (PID: 3300)
- FamItrf2.Exe (PID: 3256)
- FamItrfc.Exe (PID: 3684)
SUSPICIOUS
Executable content was dropped or overwritten
- RServer.exe (PID: 1336)
- cmd.exe (PID: 672)
- drvinst.exe (PID: 3376)
- rsetup.exe (PID: 3124)
- drvinst.exe (PID: 2528)
Drops a system driver (possible attempt to evade defenses)
- RServer.exe (PID: 1336)
- cmd.exe (PID: 672)
- rsetup.exe (PID: 3124)
- drvinst.exe (PID: 3376)
- drvinst.exe (PID: 2528)
Executing commands from a ".bat" file
- Radmin Server install.exe (PID: 2588)
Reads the Internet Settings
- Radmin Server install.exe (PID: 2588)
- RServer.exe (PID: 1336)
Reads security settings of Internet Explorer
- RServer.exe (PID: 1336)
- Radmin Server install.exe (PID: 2588)
- rsetup.exe (PID: 3124)
Process drops legitimate windows executable
- RServer.exe (PID: 1336)
- cmd.exe (PID: 672)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 672)
Starts CMD.EXE for commands execution
- Radmin Server install.exe (PID: 2588)
- cmd.exe (PID: 672)
Application launched itself
- cmd.exe (PID: 672)
- FamItrfc.Exe (PID: 3300)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 672)
Reads settings of System Certificates
- rsetup.exe (PID: 3124)
Creates files in the driver directory
- drvinst.exe (PID: 3376)
- drvinst.exe (PID: 2528)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 672)
Executes as Windows Service
- rserver3.exe (PID: 2872)
There is functionality for communication over UDP network (YARA)
- rserver3.exe (PID: 2872)
- FamItrfc.Exe (PID: 3300)
- FamItrfc.Exe (PID: 3684)
INFO
The sample compiled with chinese language support
- RServer.exe (PID: 1336)
Checks supported languages
- Radmin Server install.exe (PID: 2588)
- RServer.exe (PID: 1336)
- rsetup.exe (PID: 3124)
- drvinst.exe (PID: 3376)
- drvinst.exe (PID: 2528)
- rsetup.exe (PID: 1980)
- rserver3.exe (PID: 2872)
- FamItrfc.Exe (PID: 3300)
- FamItrf2.Exe (PID: 3256)
- FamItrfc.Exe (PID: 3684)
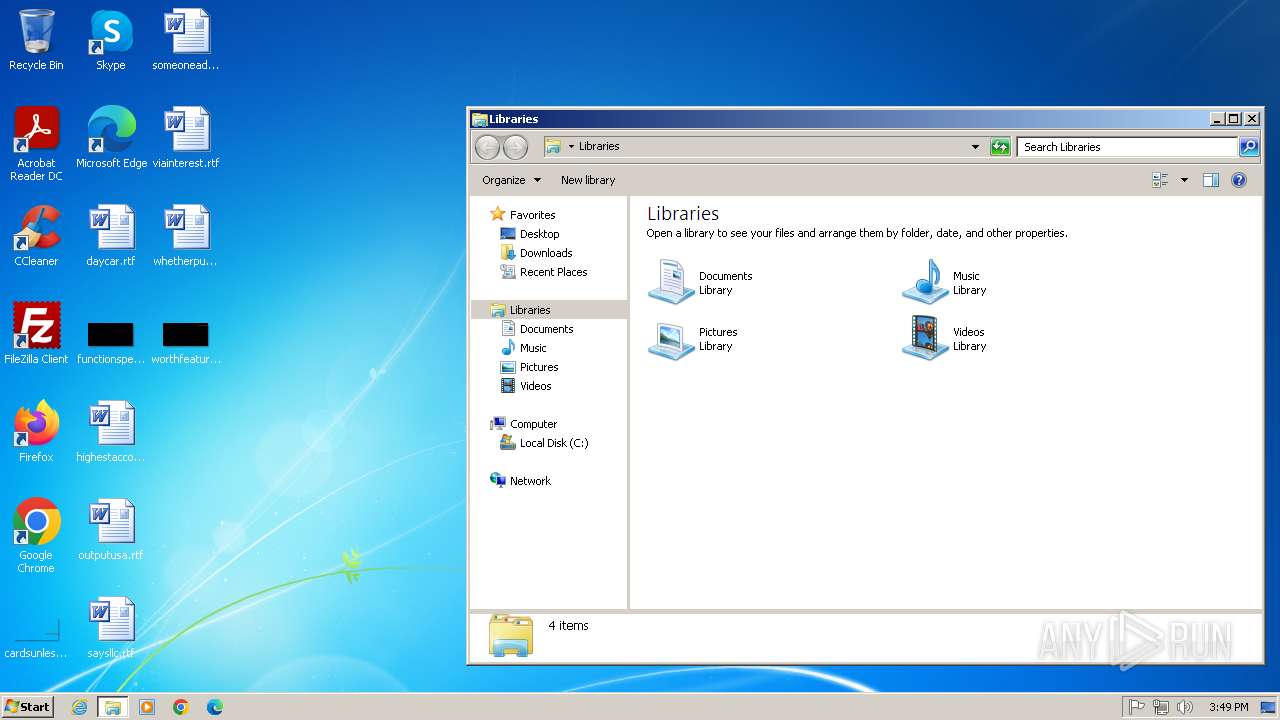
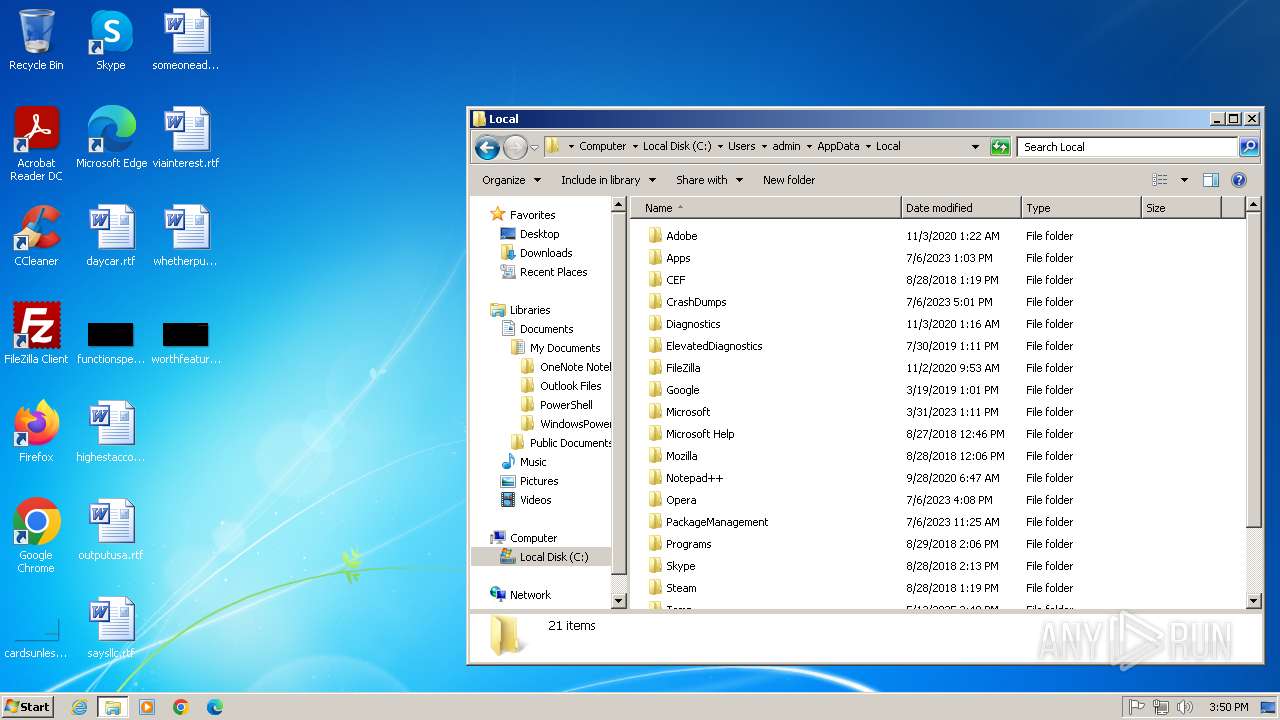
Create files in a temporary directory
- RServer.exe (PID: 1336)
- rsetup.exe (PID: 3124)
Reads the computer name
- Radmin Server install.exe (PID: 2588)
- RServer.exe (PID: 1336)
- rsetup.exe (PID: 3124)
- drvinst.exe (PID: 2528)
- drvinst.exe (PID: 3376)
- rsetup.exe (PID: 1980)
- rserver3.exe (PID: 2872)
- FamItrfc.Exe (PID: 3300)
- FamItrfc.Exe (PID: 3684)
The sample compiled with english language support
- RServer.exe (PID: 1336)
- cmd.exe (PID: 672)
- drvinst.exe (PID: 3376)
- rsetup.exe (PID: 3124)
- drvinst.exe (PID: 2528)
RADMIN has been detected
- RServer.exe (PID: 1336)
- cmd.exe (PID: 672)
- rsetup.exe (PID: 3124)
- reg.exe (PID: 676)
- rserver3.exe (PID: 2872)
- reg.exe (PID: 676)
- rsetup.exe (PID: 1980)
- FamItrfc.Exe (PID: 3300)
- FamItrf2.Exe (PID: 3256)
- FamItrfc.Exe (PID: 3684)
Reads the software policy settings
- rsetup.exe (PID: 3124)
- drvinst.exe (PID: 2528)
- drvinst.exe (PID: 3376)
Checks operating system version
- cmd.exe (PID: 672)
Reads the machine GUID from the registry
- rsetup.exe (PID: 3124)
- drvinst.exe (PID: 2528)
- drvinst.exe (PID: 3376)
- rserver3.exe (PID: 2872)
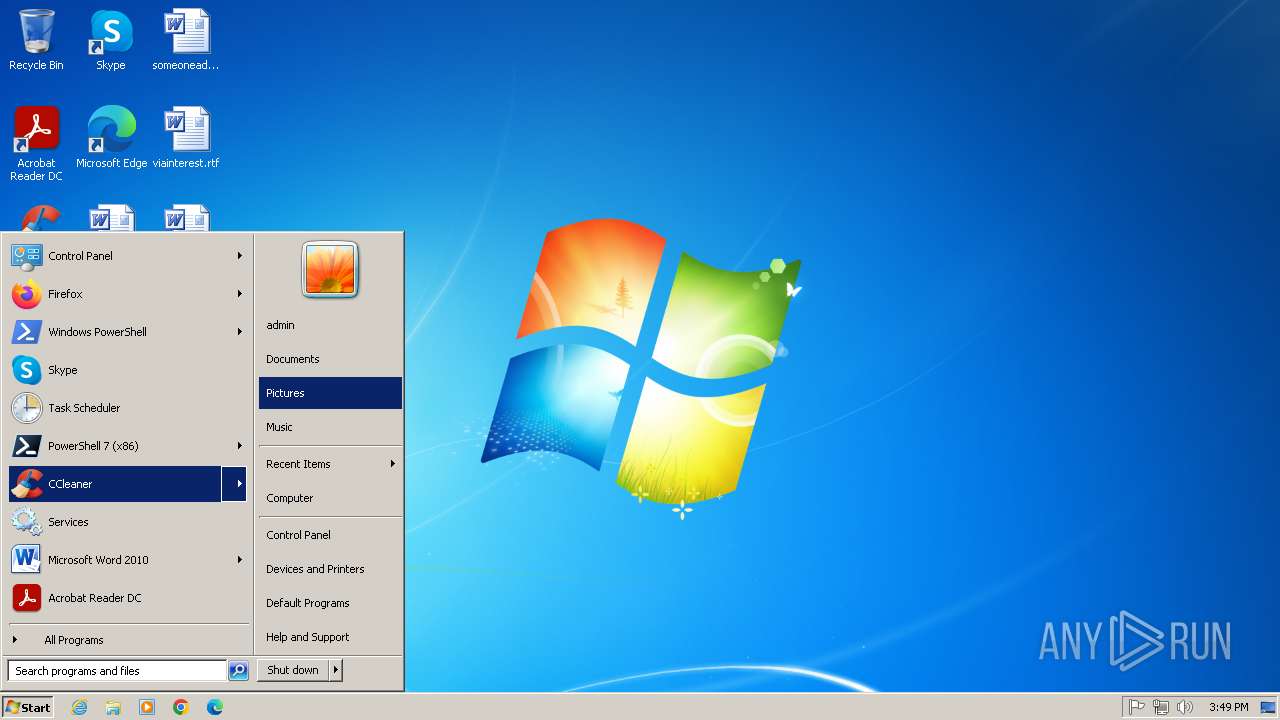
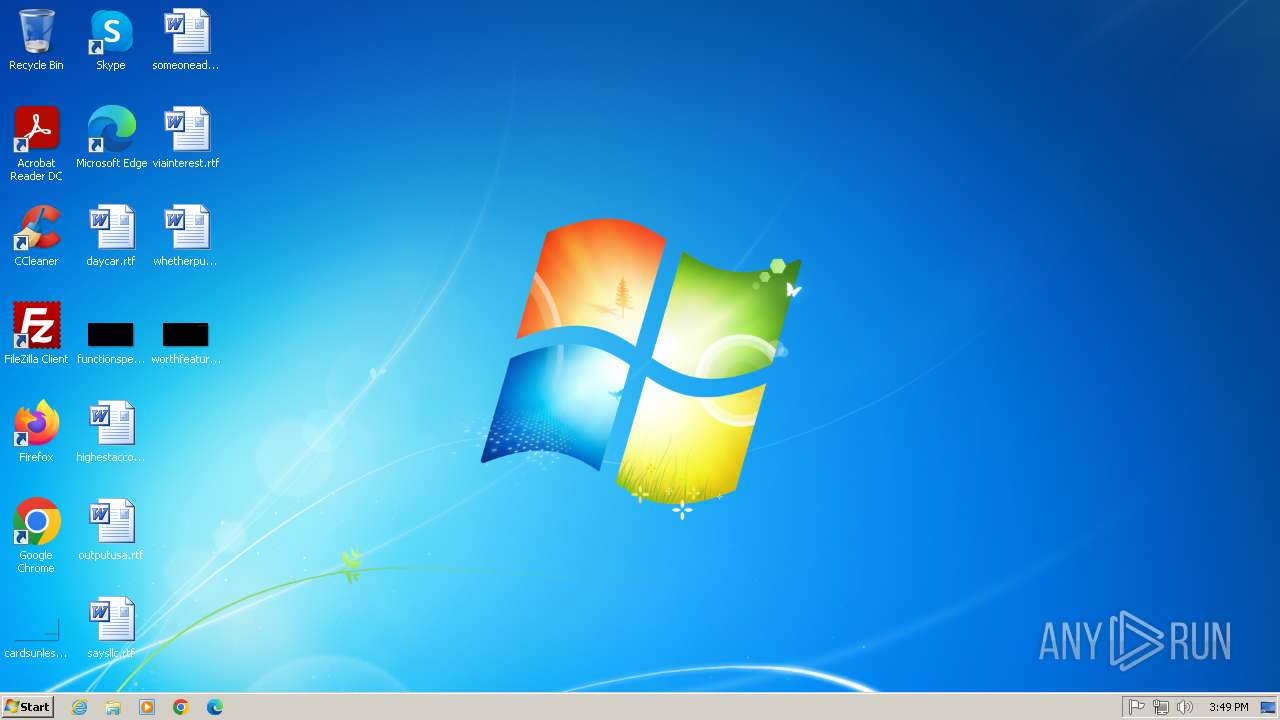
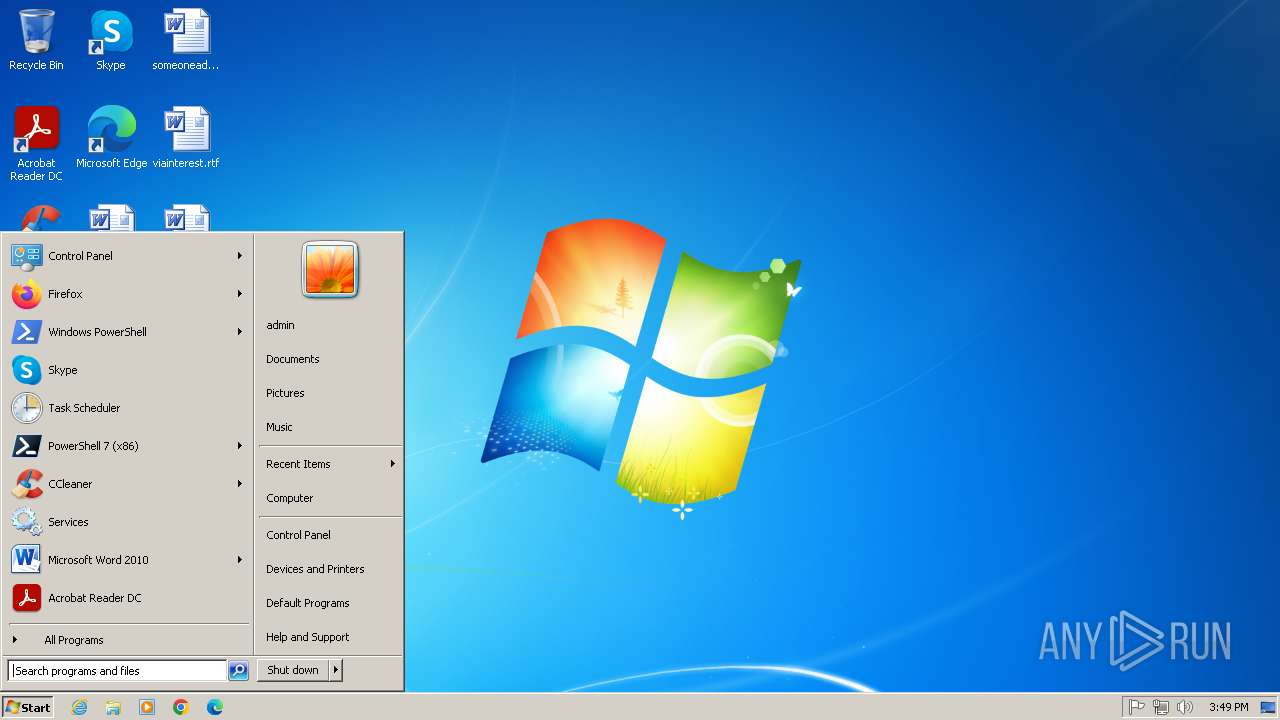
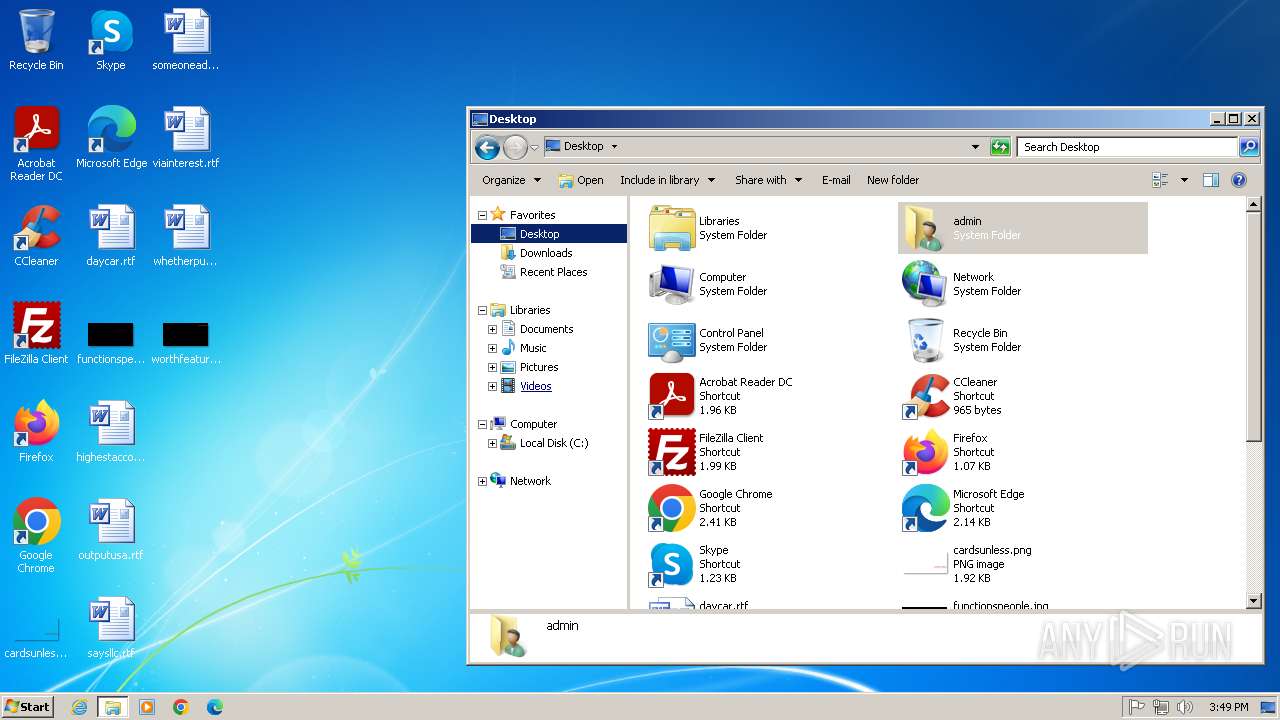
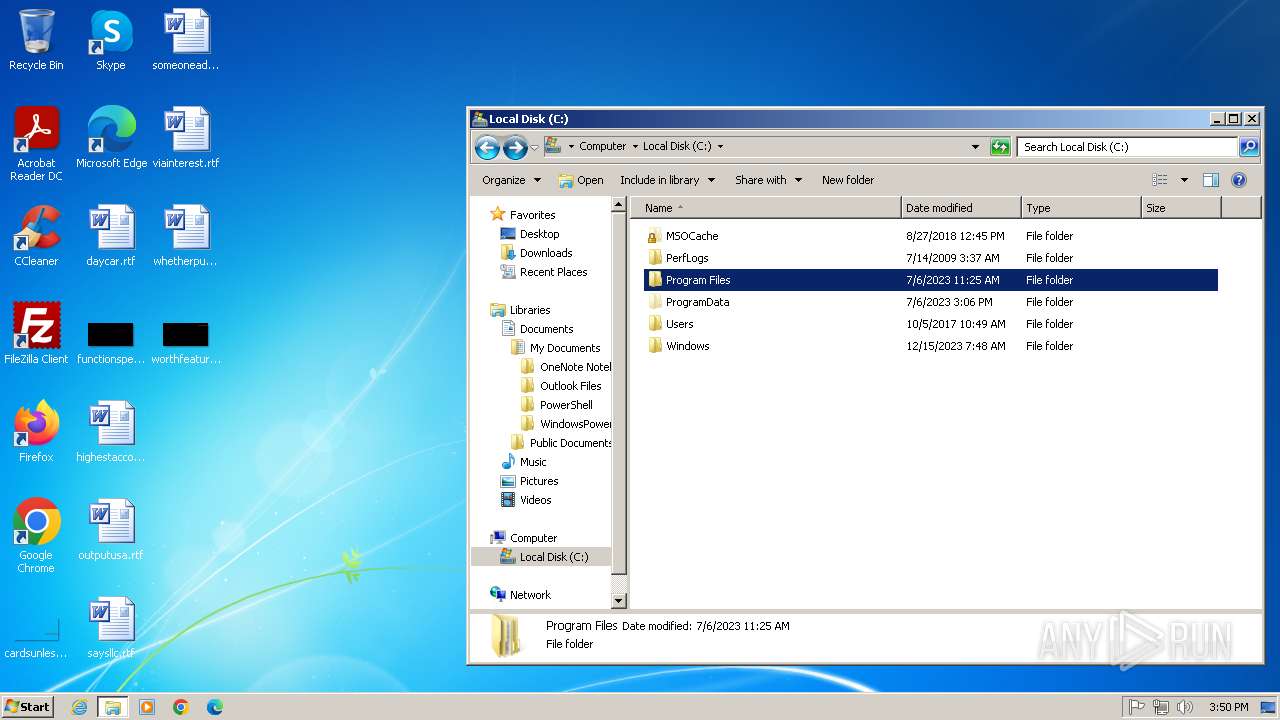
Manual execution by a user
- explorer.exe (PID: 3144)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (45.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (20.9) |
| .exe | | | Win32 Executable (generic) (14.3) |
| .exe | | | Win16/32 Executable Delphi generic (6.6) |
| .exe | | | Generic Win/DOS Executable (6.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 107520 |
| InitializedDataSize: | 45056 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1a238 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 1.0.0.0 |
| FileDescription: | Radmin Server install |
| ProductName: | Radmin Server install |
| ProductVersion: | 1.0.0.0 |
| CompanyName: | Bluefish |
| LegalCopyright: | Bluefish QQ10531348 |
| Comments: | Radmin服务端静默安装器 |
Total processes
58
Monitored processes
19
Malicious processes
8
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 672 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\~sfx004CB0CB55\@°²×°.bat" " | C:\Windows\System32\cmd.exe | Radmin Server install.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 676 | reg import C:\Windows\System32\rserver30\install.reg /reg:32 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
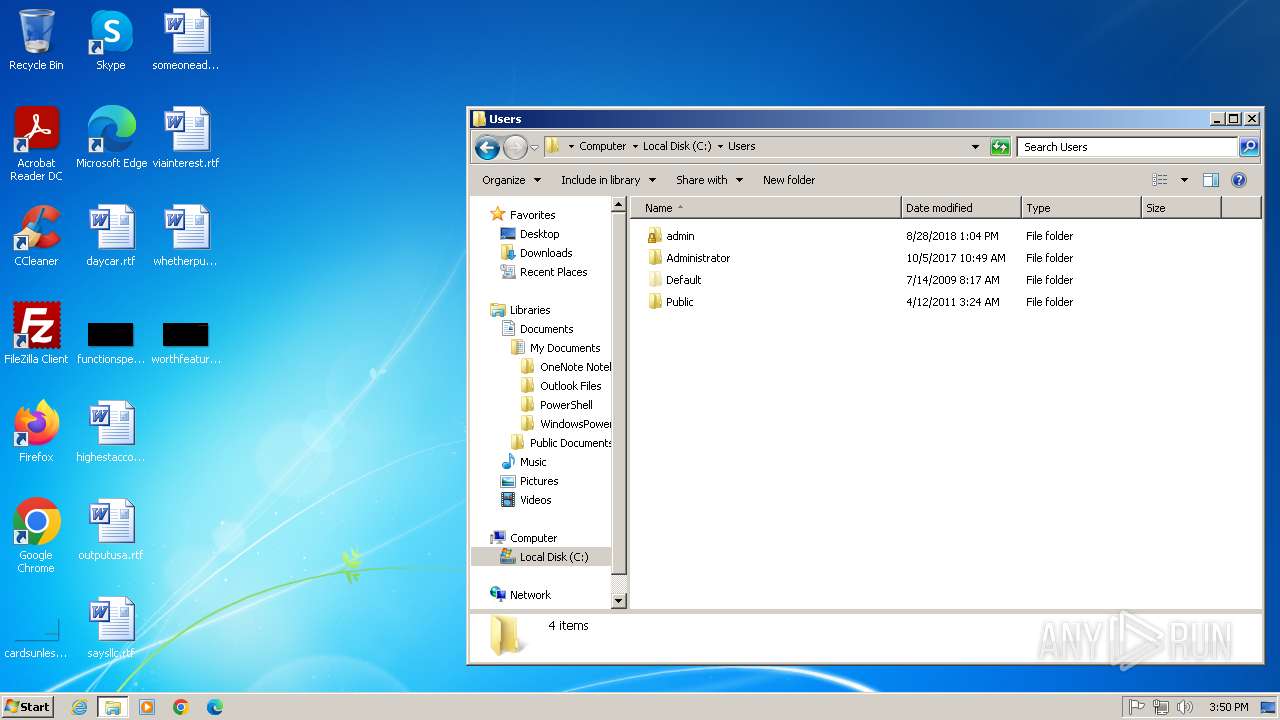
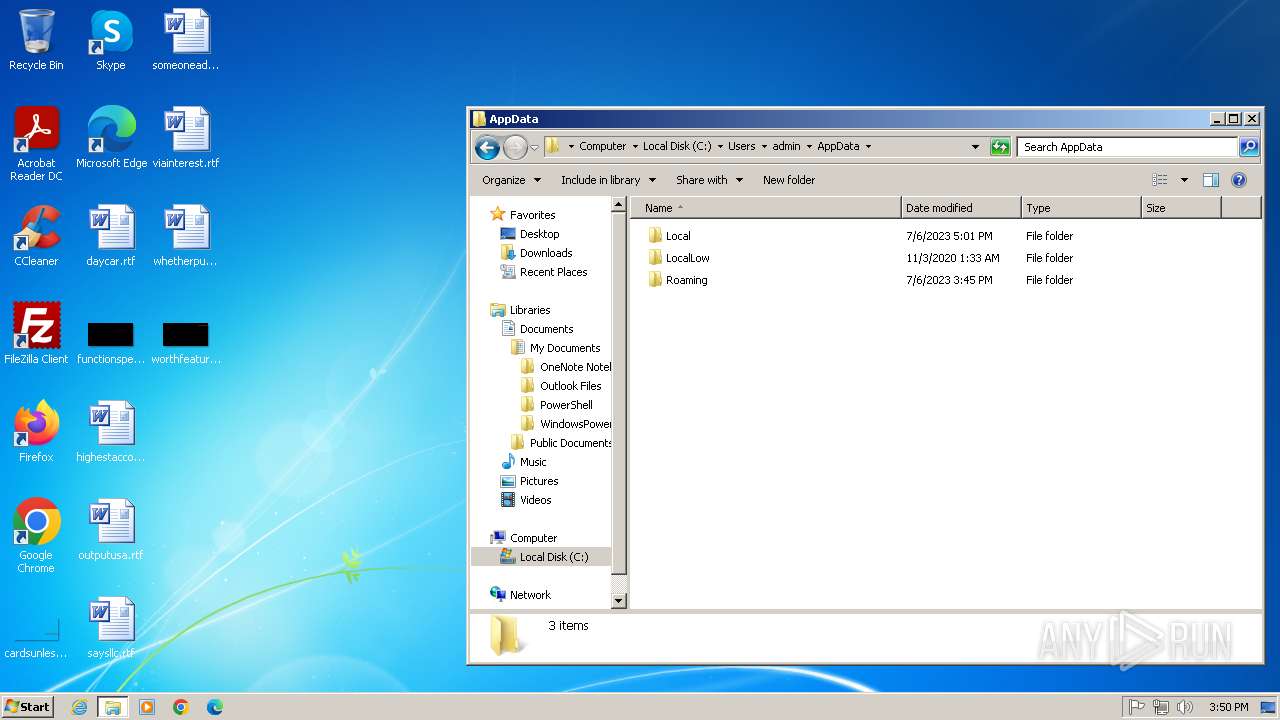
| 1336 | "C:\Users\admin\AppData\Local\Temp\RServer.exe" | C:\Users\admin\AppData\Local\Temp\RServer.exe | explorer.exe | ||||||||||||
User: admin Company: Bluefish Integrity Level: HIGH Description: Radmin Server install Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1964 | "C:\Users\admin\AppData\Local\Temp\RServer.exe" | C:\Users\admin\AppData\Local\Temp\RServer.exe | — | explorer.exe | |||||||||||
User: admin Company: Bluefish Integrity Level: MEDIUM Description: Radmin Server install Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1980 | C:\Windows\System32\rserver30\rsetup.exe /start | C:\Windows\System32\rserver30\rsetup.exe | — | cmd.exe | |||||||||||
User: admin Company: Famatech Corp. Integrity Level: HIGH Description: Radmin Setup Helper Exit code: 1 Version: 3, 5, 0, 0 Modules
| |||||||||||||||
| 2528 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{3b126f26-d831-678a-a1e9-e12f38b96a1d}\mirrorv3.inf" "0" "60bbf019f" "00000404" "WinSta0\Default" "00000560" "208" "c:\windows\system32\rserver30" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2588 | "C:\Users\admin\AppData\Local\Temp\~sfx004CB0CB55\Radmin Server install.exe" | C:\Users\admin\AppData\Local\Temp\~sfx004CB0CB55\Radmin Server install.exe | — | RServer.exe | |||||||||||
User: admin Company: Bluefish Integrity Level: HIGH Description: Radmin Server install Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2832 | C:\Windows\system32\cmd.exe /S /D /c" ver" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2872 | "C:\Windows\System32\rserver30\RServer3.exe" /service | C:\Windows\System32\rserver30\rserver3.exe | services.exe | ||||||||||||
User: SYSTEM Company: Famatech Corp. Integrity Level: SYSTEM Description: Radmin Server Version: 3, 5, 0, 0 Modules
| |||||||||||||||
| 2944 | findstr "6\.[0-9]\.[0-9][0-9]*" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
15 094
Read events
14 902
Write events
184
Delete events
8
Modification events
| (PID) Process: | (2588) Radmin Server install.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2588) Radmin Server install.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2588) Radmin Server install.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2588) Radmin Server install.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1336) RServer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1336) RServer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1336) RServer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1336) RServer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1336) RServer.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager |
| Operation: | write | Name: | PendingFileRenameOperations |
Value: \??\C:\Users\admin\AppData\Local\Temp\~sfx004CB0CB55\@жÔØ.bat | |||
| (PID) Process: | (3116) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
66
Suspicious files
27
Text files
8
Unknown types
0
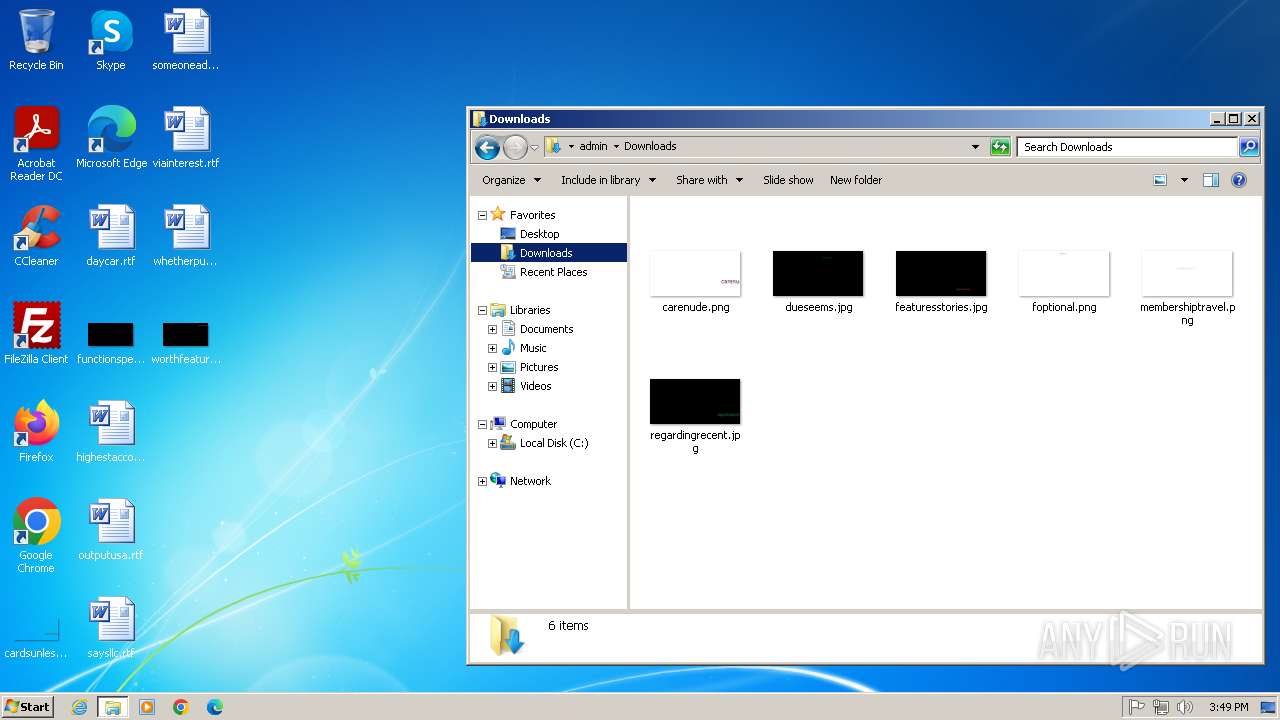
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1336 | RServer.exe | C:\Users\admin\AppData\Local\Temp\~sfx004CB0CB55\rserver30\2052.lng_rad | executable | |
MD5:1DACE6EB4596D6D17B011755F6F07253 | SHA256:6D2325F96294A38F3CF1F17925F6CAD42DF3A3765305FC869B7F111E21EEA697 | |||
| 1336 | RServer.exe | C:\Users\admin\AppData\Local\Temp\~sfx004CB0CB55\rserver30\ChatLPCx.dll | executable | |
MD5:56F925FB4C91A2F88B63E5DB095EC251 | SHA256:E0DF0A7AE8A84F14CF2D05239E64C30557B92A6E74A2F19DEA31342B3A8581A2 | |||
| 1336 | RServer.exe | C:\Users\admin\AppData\Local\Temp\~sfx004CB0CB55\rserver30\raudiox.dll | executable | |
MD5:E4B19ABF75D0ED279AB4D8856109B169 | SHA256:80CCD620D5C46797078DB9AB2E8DD94CB03324C42D34E811C1203729D6B6FDB6 | |||
| 1336 | RServer.exe | C:\Users\admin\AppData\Local\Temp\~sfx004CB0CB55\rserver30\FirewallInstallHelper.dll | executable | |
MD5:FB1B13C20766630A858591C00FFA3DE2 | SHA256:3928266D66790991D2DDBB31A955AC503254413EBC82D29439E0ADA95F45BBBF | |||
| 1336 | RServer.exe | C:\Users\admin\AppData\Local\Temp\~sfx004CB0CB55\rserver30\install.reg | text | |
MD5:1A4FAF0CF38750C9B38EA8D2959379A8 | SHA256:CC364495CDD75E2C4DE86A0F45E2BF9DCAD1753AD1C18FF7E8BE99133D05F096 | |||
| 1336 | RServer.exe | C:\Users\admin\AppData\Local\Temp\~sfx004CB0CB55\@°²×°.bat | text | |
MD5:B709C4F23FD2F4412C1B3E5EBA9A39B3 | SHA256:5A1180327773D8FDED8E1AFF50CCDB7F0D1C2DB2A2D820C20FEAE5E6D813947A | |||
| 1336 | RServer.exe | C:\Users\admin\AppData\Local\Temp\~sfx004CB0CB55\rserver30\FamItrfc.Exe | executable | |
MD5:D97153B43EA9E9C3F5D9FB467E6B101D | SHA256:54F7CE751B2B4BEA492076F7B8E3172A14A343F8CDD59E3BAB1981D5FE04F0F6 | |||
| 1336 | RServer.exe | C:\Users\admin\AppData\Local\Temp\~sfx004CB0CB55\rserver30\rchatx.dll | executable | |
MD5:4BD29908E0CA2831CB74D5128F29F59A | SHA256:C4AA2789BE22FB8F49D63126169070072ED46D88A628E745AE2CA7A6E21FEAC8 | |||
| 1336 | RServer.exe | C:\Users\admin\AppData\Local\Temp\~sfx004CB0CB55\@жÔØ.bat | text | |
MD5:358E854E2C5A9A8F0CDF40B4C21EB525 | SHA256:FCB91E8B635B1954F8C9713E7F7F866468FA05C91E91922AA93402283572EABA | |||
| 1336 | RServer.exe | C:\Users\admin\AppData\Local\Temp\~sfx004CB0CB55\@ÉèÖÃ.bat | text | |
MD5:CB435A7161C2EEDB385B4E9B1FEA4500 | SHA256:1942D203F80CBBCB56E0FB14AEDB6E9C83EC6358987F48AB83EC1DE883F9EF3E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
DNS requests
Threats
Process | Message |
|---|---|
rserver3.exe | %n%n%n%n%n%n%n%n%n |