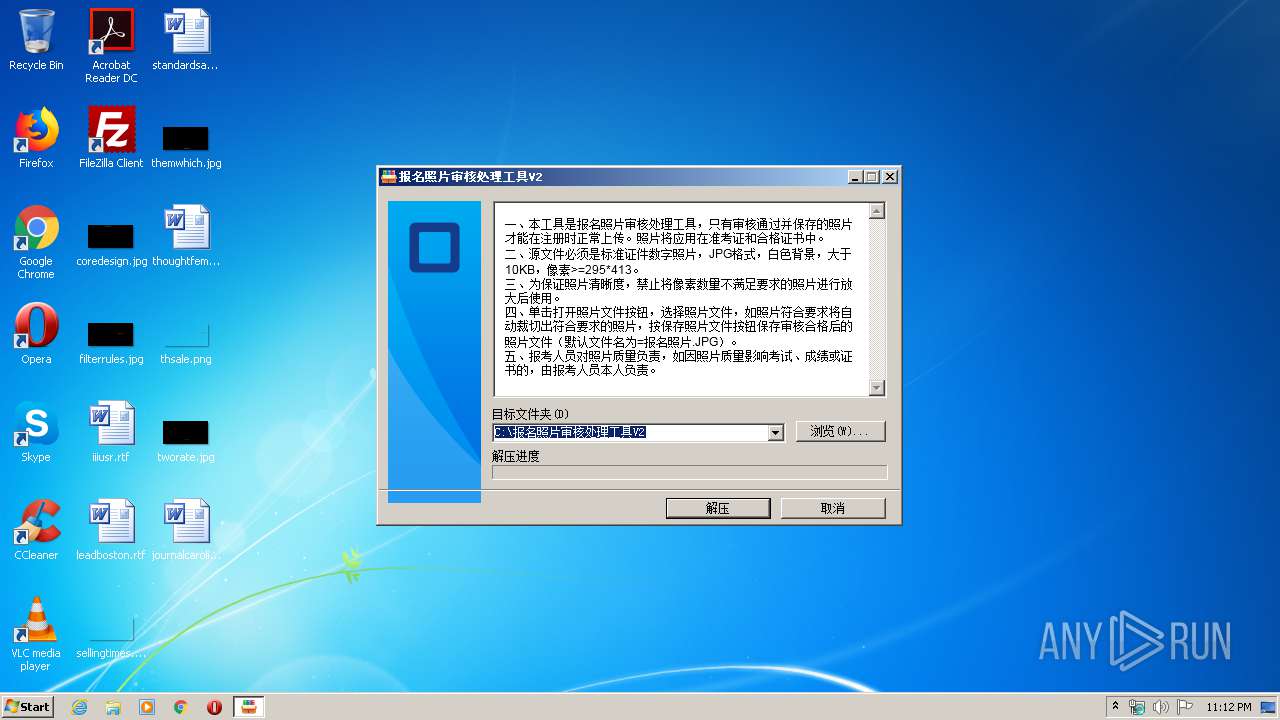
| File name: | photosetup.exe |
| Full analysis: | https://app.any.run/tasks/08ea3cd1-5eb3-4cf5-a2dd-eafbd2bc31de |
| Verdict: | Malicious activity |
| Analysis date: | April 05, 2020, 22:12:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 67996700D56E5422960006164B79C798 |
| SHA1: | 4E4DC88933B7C40A3A0375D2328913BDE485962D |
| SHA256: | F5EA4AC3995992118F346C74415E849410D090E576407F73861521986C3F846E |
| SSDEEP: | 98304:bI9QRVQB4QD9OMP1Zq3qbYLMKrFLoRXigQ+NMajupsj7s8XXhFo8vTUJ:bIwQB4QP1+qeMIqSgZup8VXDvTU |
MALICIOUS
Application was dropped or rewritten from another process
- OumaPictureCheck.exe (PID: 3848)
- OumaPictureCheck.exe (PID: 3436)
Loads dropped or rewritten executable
- OumaPictureCheck.exe (PID: 3848)
- OumaPictureCheck.exe (PID: 3436)
SUSPICIOUS
Reads Internet Cache Settings
- photosetup.exe (PID: 1844)
Executable content was dropped or overwritten
- photosetup.exe (PID: 1844)
Reads internet explorer settings
- photosetup.exe (PID: 1844)
INFO
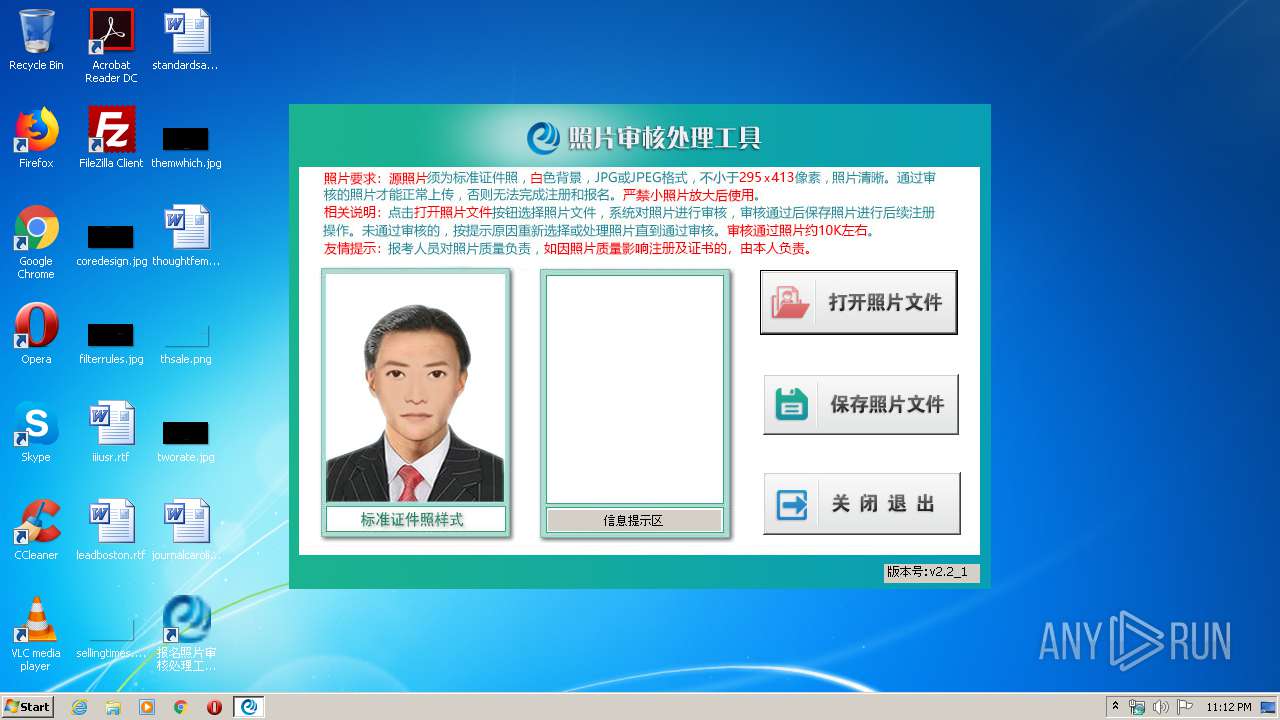
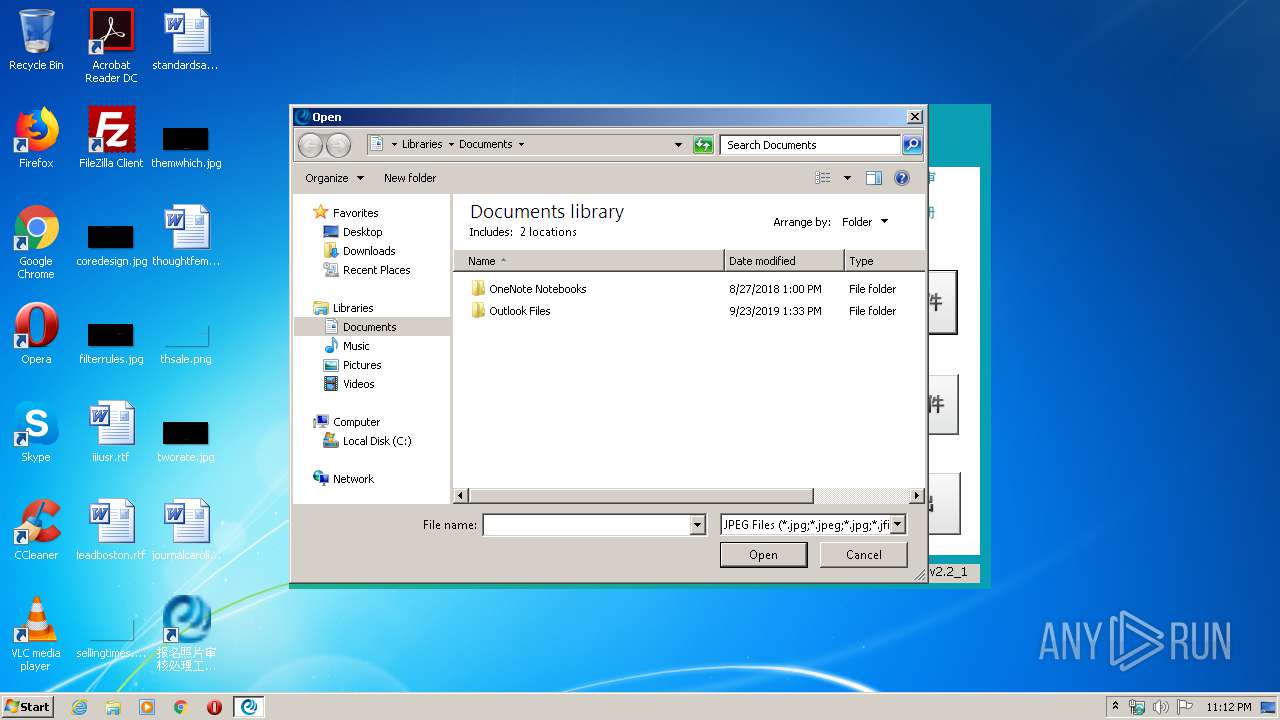
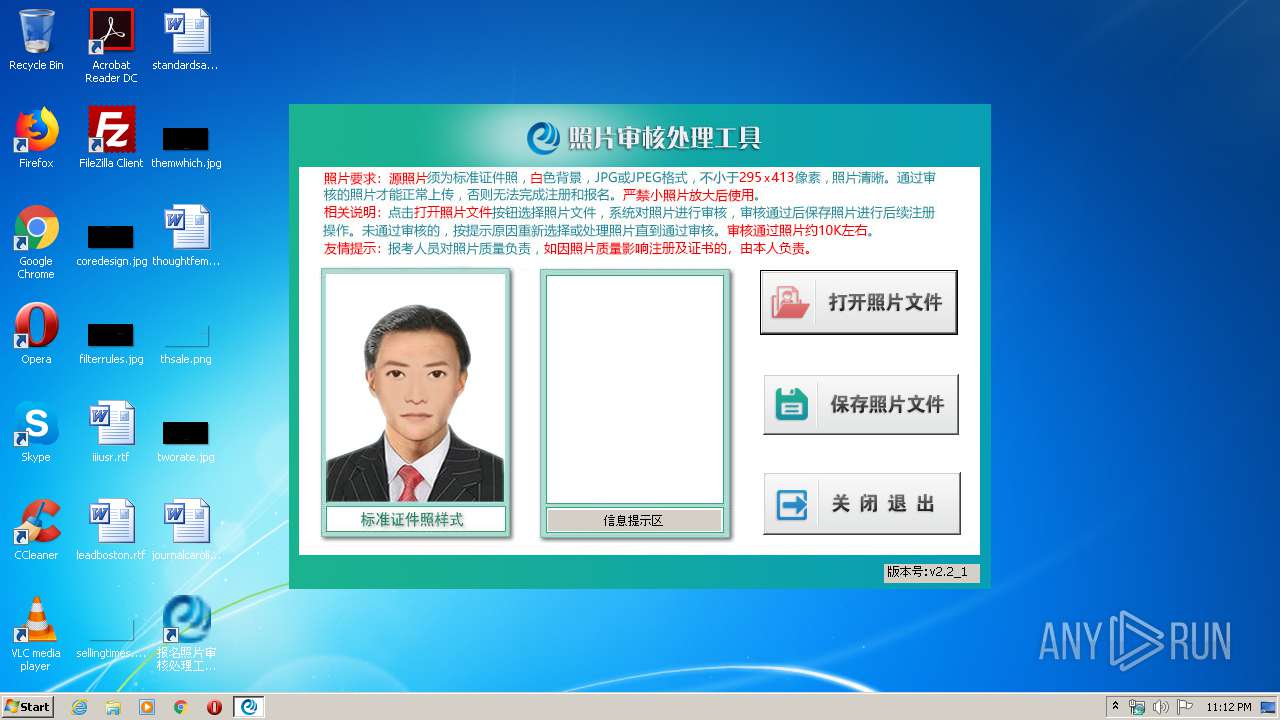
Manual execution by user
- OumaPictureCheck.exe (PID: 3848)
- OumaPictureCheck.exe (PID: 3436)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:02:21 11:16:42+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 190976 |
| InitializedDataSize: | 105984 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d779 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Feb-2019 10:16:42 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 21-Feb-2019 10:16:42 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002E864 | 0x0002EA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.69348 |
.rdata | 0x00030000 | 0x00009AAC | 0x00009C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.13386 |
.data | 0x0003A000 | 0x000213D0 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.24289 |
.gfids | 0x0005C000 | 0x000000E8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.09592 |
.rsrc | 0x0005D000 | 0x0000D2C8 | 0x0000D400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.85319 |
.reloc | 0x0006B000 | 0x00001FD0 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.68736 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.22792 | 1600 | Latin 1 / Western European | Chinese - PRC | RT_MANIFEST |
2 | 5.10026 | 2216 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 5.25868 | 3752 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
4 | 5.02609 | 1128 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
5 | 5.18109 | 4264 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
6 | 5.04307 | 9640 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
7 | 5.24197 | 182 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
8 | 5.27357 | 214 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
9 | 5.38938 | 202 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
10 | 5.08077 | 118 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
38
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1844 | "C:\Users\admin\AppData\Local\Temp\photosetup.exe" | C:\Users\admin\AppData\Local\Temp\photosetup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3436 | "C:\报名照片审核处理工具V2\OumaPictureCheck.exe" | C:\报名照片审核处理工具V2\OumaPictureCheck.exe | — | explorer.exe | |||||||||||
User: admin Company: TODO: <公司名> Integrity Level: MEDIUM Description: OumaPictureCheck Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 3848 | "C:\报名照片审核处理工具V2\OumaPictureCheck.exe" | C:\报名照片审核处理工具V2\OumaPictureCheck.exe | — | explorer.exe | |||||||||||
User: admin Company: TODO: <公司名> Integrity Level: MEDIUM Description: OumaPictureCheck Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
Total events
737
Read events
696
Write events
40
Delete events
1
Modification events
| (PID) Process: | (1844) photosetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1844) photosetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1844) photosetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1844) photosetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1844) photosetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1844) photosetup.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR SFX |
| Operation: | write | Name: | C%%报名照片审核处理工具V2 |
Value: C:\报名照片审核处理工具V2 | |||
| (PID) Process: | (3848) OumaPictureCheck.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (3848) OumaPictureCheck.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 02000000010000000A0000000700000009000000080000000000000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (3848) OumaPictureCheck.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\2 |
| Operation: | write | Name: | MRUListEx |
Value: 0000000001000000FFFFFFFF | |||
| (PID) Process: | (3848) OumaPictureCheck.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
Executable files
8
Suspicious files
1
Text files
8
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1844 | photosetup.exe | C:\报名照片审核处理工具V2\OumaPictureCheck.exe | executable | |
MD5:— | SHA256:— | |||
| 1844 | photosetup.exe | C:\报名照片审核处理工具V2\README.doc | document | |
MD5:— | SHA256:— | |||
| 1844 | photosetup.exe | C:\Users\admin\Desktop\报名照片审核处理工具V2.lnk | lnk | |
MD5:— | SHA256:— | |||
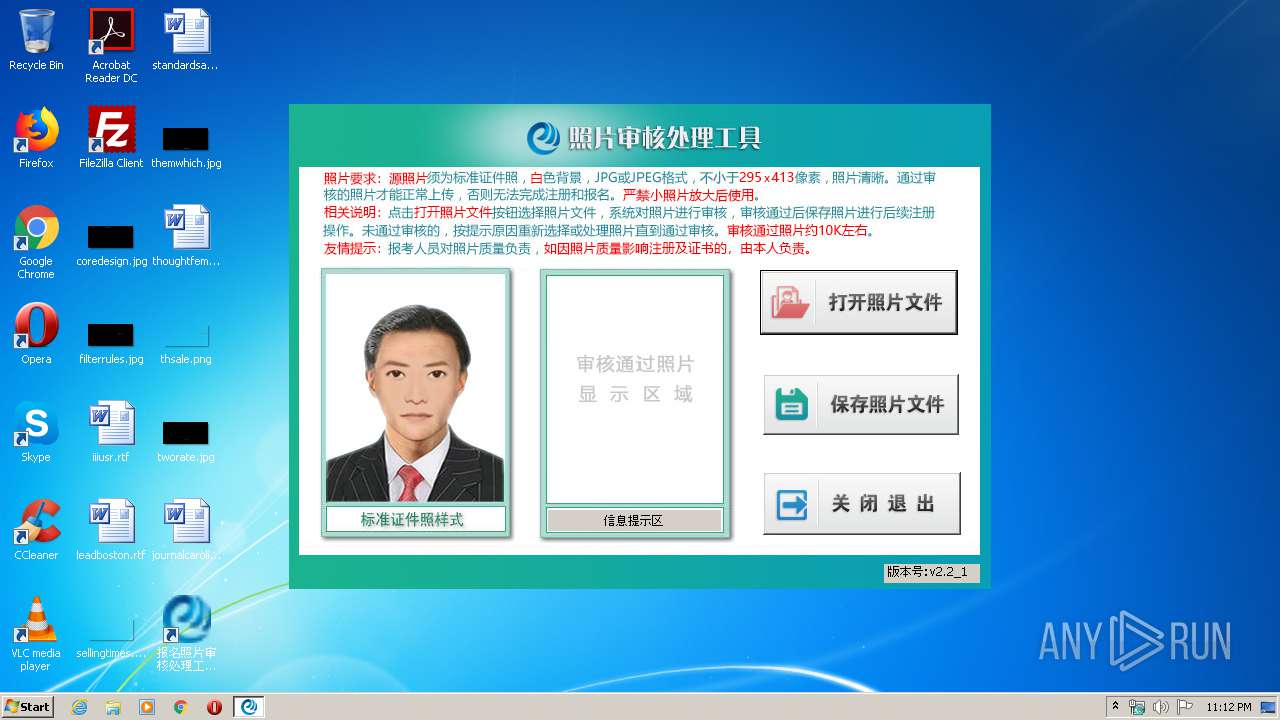
| 1844 | photosetup.exe | C:\报名照片审核处理工具V2\tips\state8.jpg | image | |
MD5:— | SHA256:— | |||
| 1844 | photosetup.exe | C:\报名照片审核处理工具V2\tips\state1.jpg | image | |
MD5:DB3927D52EA711C59EBBB771B7653855 | SHA256:9BCB477E88572F36FA4152E75D5AC0B2326E4CE25CC6C9AA03D90B99AA0402F5 | |||
| 1844 | photosetup.exe | C:\报名照片审核处理工具V2\tips\state6.jpg | image | |
MD5:— | SHA256:— | |||
| 1844 | photosetup.exe | C:\报名照片审核处理工具V2\setting.ini | text | |
MD5:— | SHA256:— | |||
| 1844 | photosetup.exe | C:\报名照片审核处理工具V2\tips\state3.jpg | image | |
MD5:D1BEF2B28A8F6A5C618FD74BDF75DE85 | SHA256:E9EB533770C2FB0BBA1B403538FCEB5664CD2DCADF8E9F0517DADBF7B6C44642 | |||
| 1844 | photosetup.exe | C:\报名照片审核处理工具V2\opencv_highgui249.dll | executable | |
MD5:5FB3A7D35187C7BC04144C934DC3336C | SHA256:B32FCF0A82F42B80FE13B7EE7B27280FA02BB4039A035BD3BAB9B5BF61087FCA | |||
| 1844 | photosetup.exe | C:\报名照片审核处理工具V2\tips\state4.jpg | image | |
MD5:E219979FAFAA6D8845CE93988BBD1F89 | SHA256:DE1F700B4B14949891C3C243CEC8AD08703EBF0F784787147C42DE3B4D62F863 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report