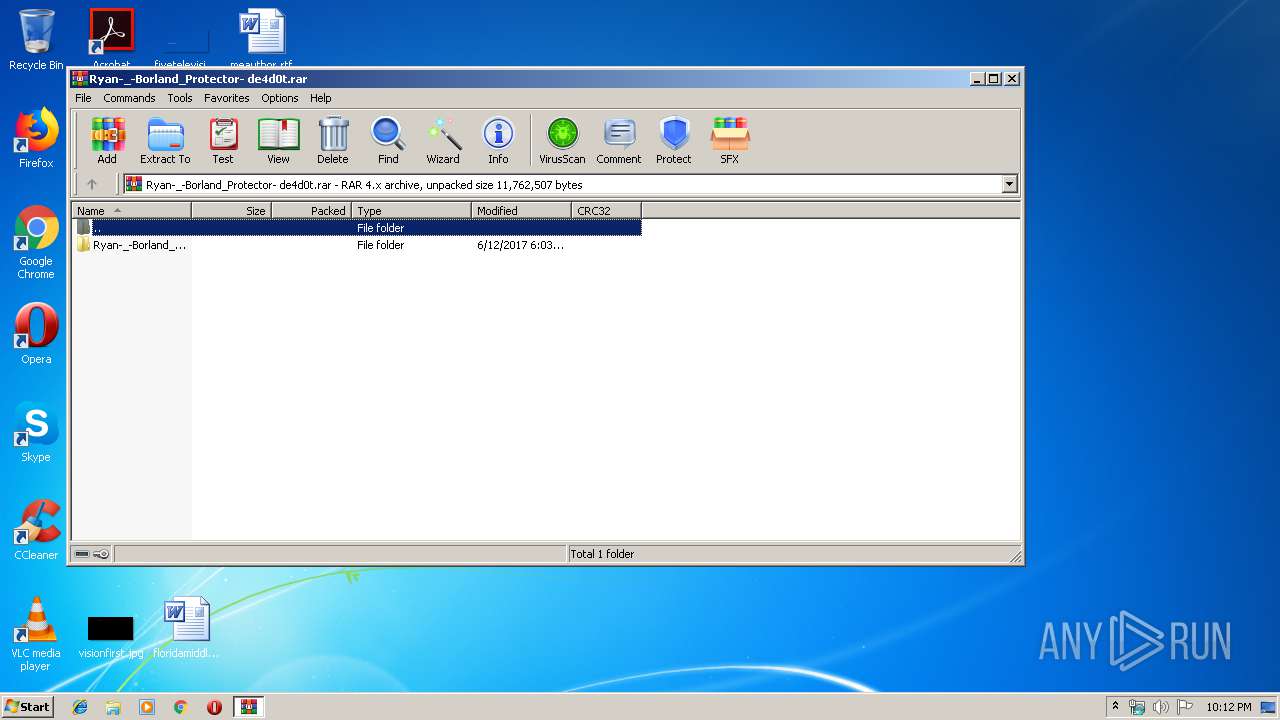
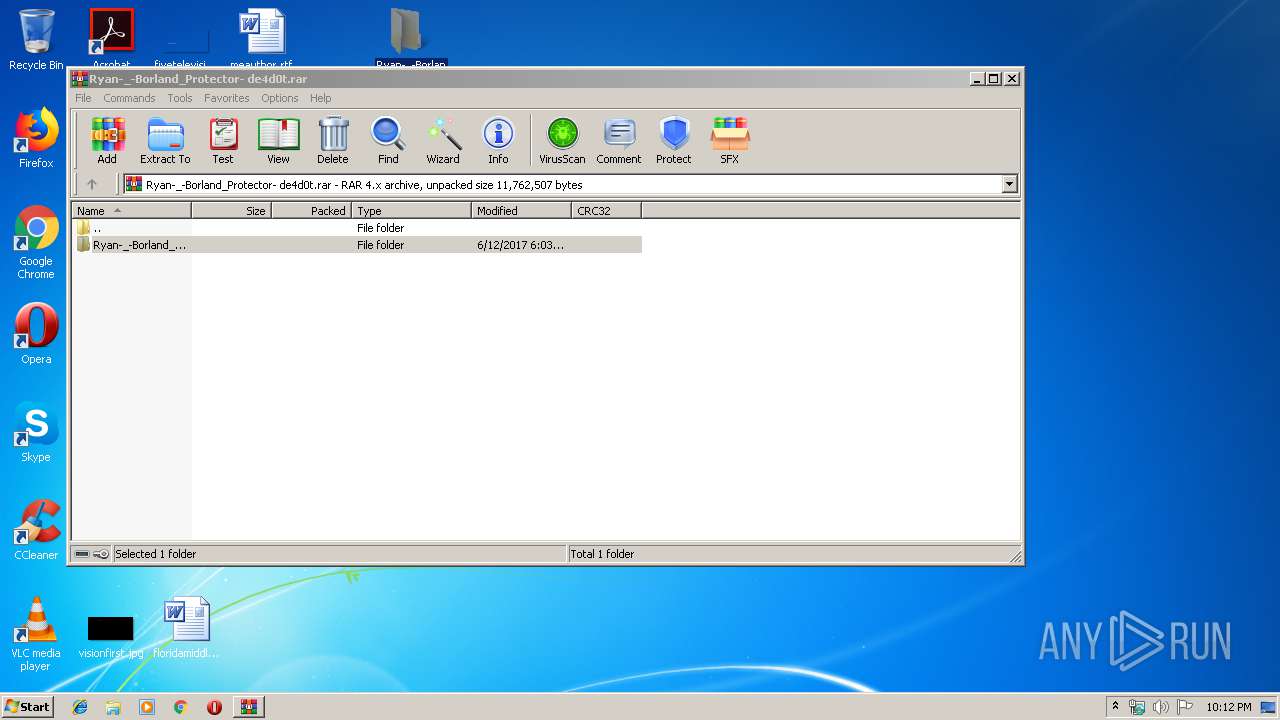
| File name: | Ryan-_-Borland_Protector- de4d0t.rar |
| Full analysis: | https://app.any.run/tasks/9d4c11b8-70a8-426e-a6fe-3e50e03bd13c |
| Verdict: | Malicious activity |
| Analysis date: | September 11, 2019, 21:11:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | ECE62E0F9A832F212DD0B294C0862B01 |
| SHA1: | 8E2593DC8588E105C9422807497FD550E8C20BD7 |
| SHA256: | F5E16EA3338E07A21829595FB254AC373912E42ADCCF249588C62857FF2824A8 |
| SSDEEP: | 49152:wKYIUo2ptKx/hQEiBIzJWm2glWmia6Bx76ldspUQJ9Z7x1VQApONv:YIwKGAcSWmF6busmQ5V/ONv |
MALICIOUS
Application was dropped or rewritten from another process
- ConfuserEx.exe (PID: 408)
Loads dropped or rewritten executable
- ConfuserEx.exe (PID: 408)
- SearchProtocolHost.exe (PID: 1728)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2892)
INFO
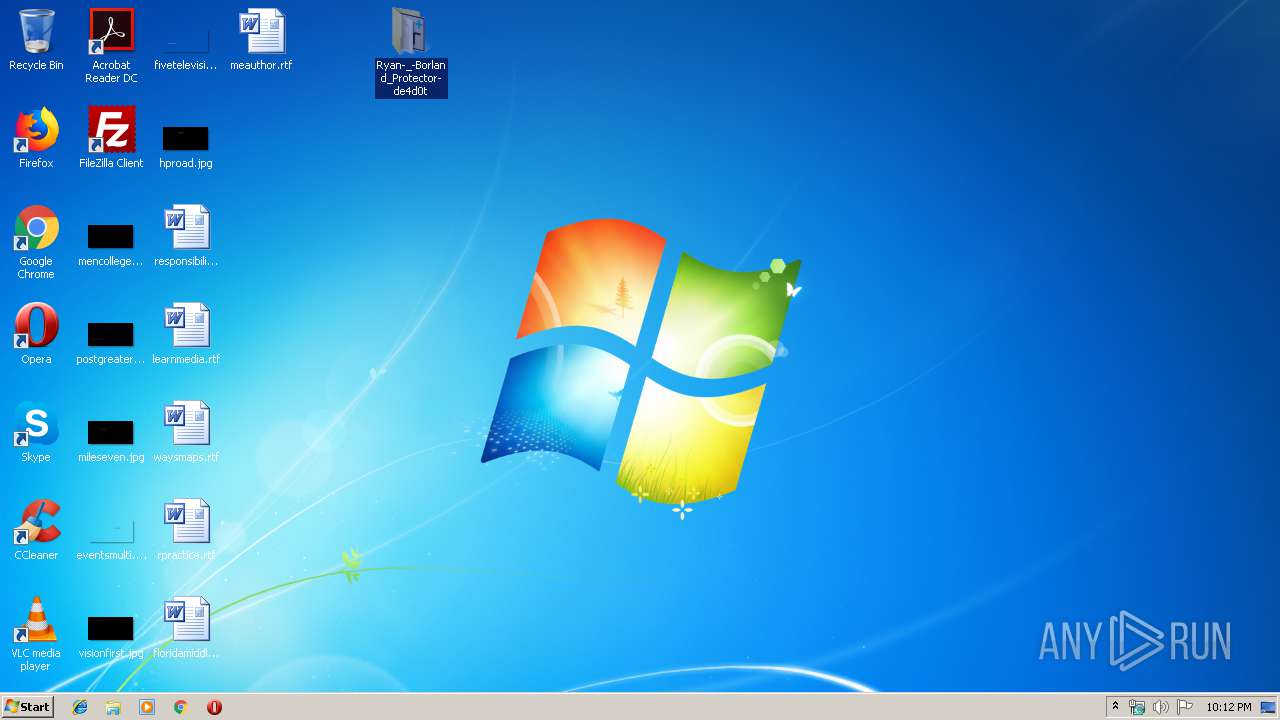
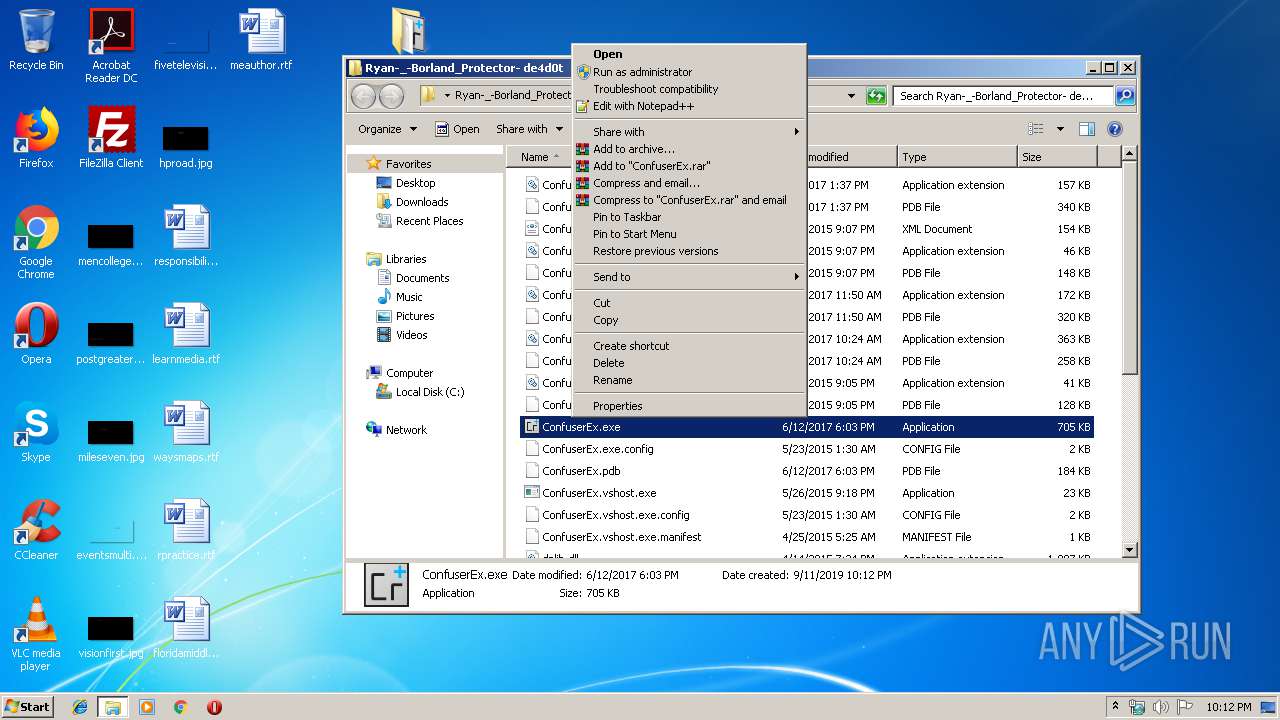
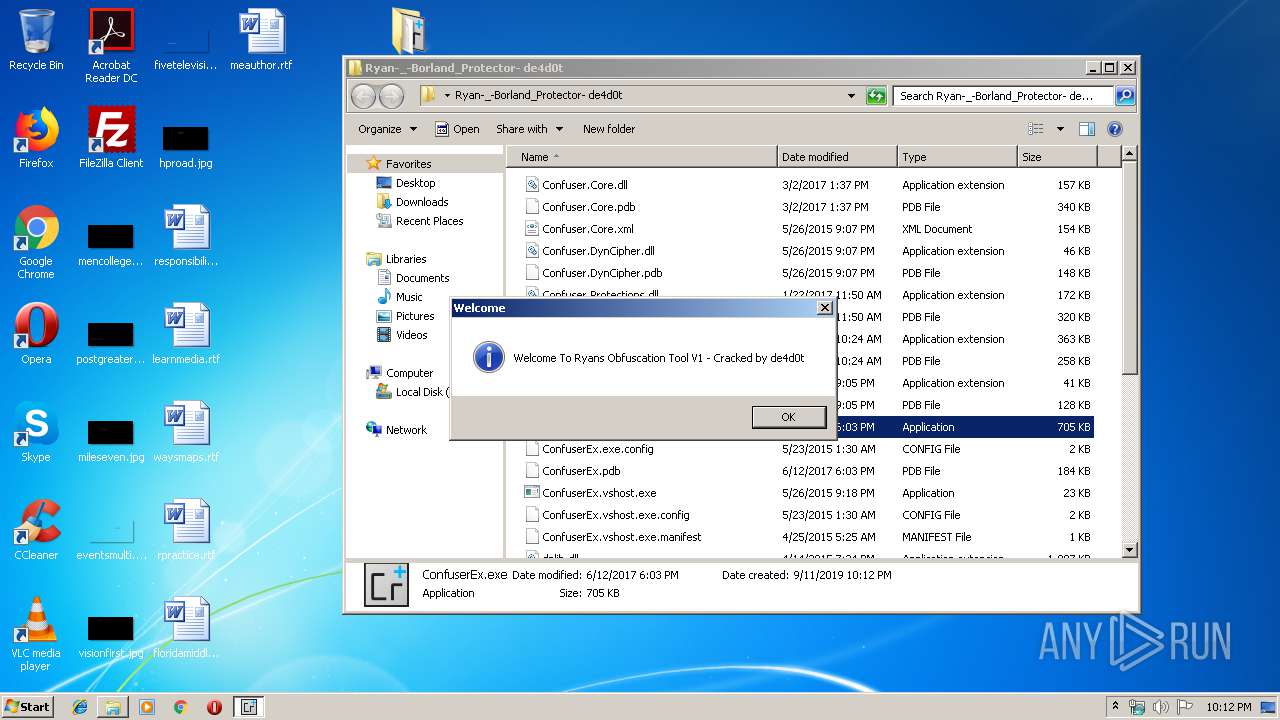
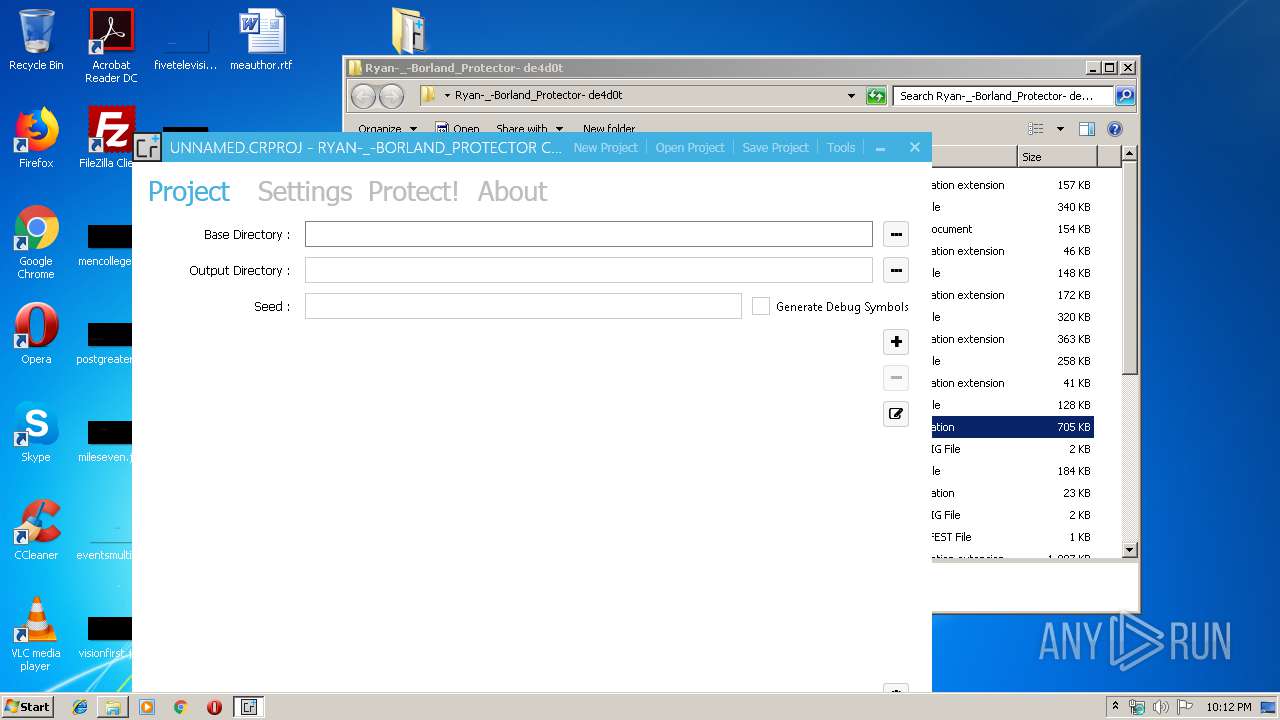
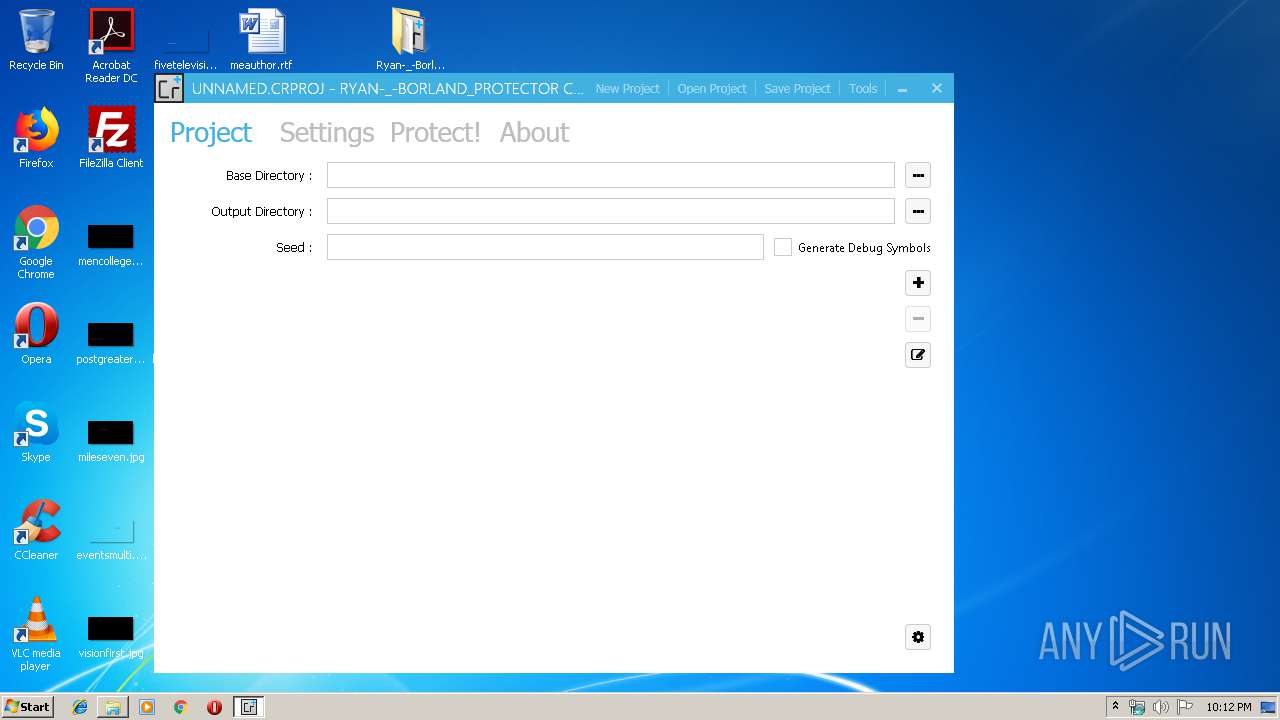
Manual execution by user
- ConfuserEx.exe (PID: 408)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 65165 |
|---|---|
| UncompressedSize: | 160256 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2017:03:02 13:37:02 |
| PackingMethod: | Normal |
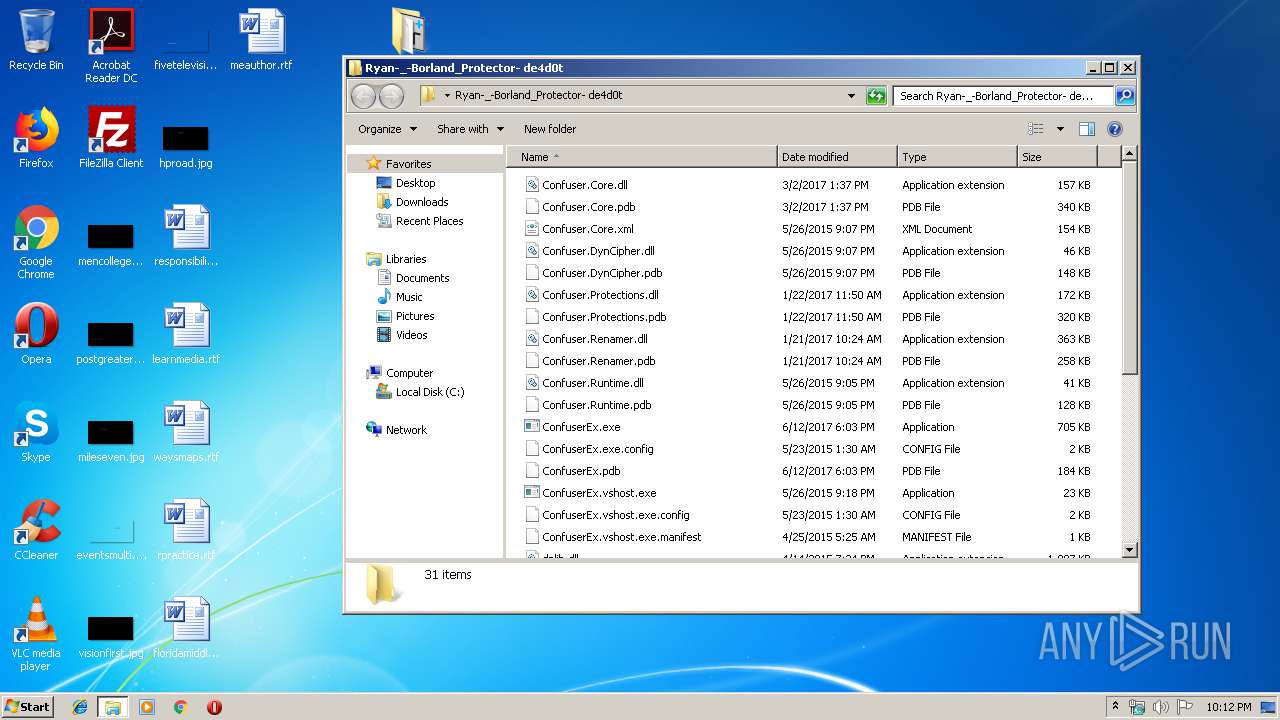
| ArchivedFileName: | Ryan-_-Borland_Protector- de4d0t\Confuser.Core.dll |
Total processes
36
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
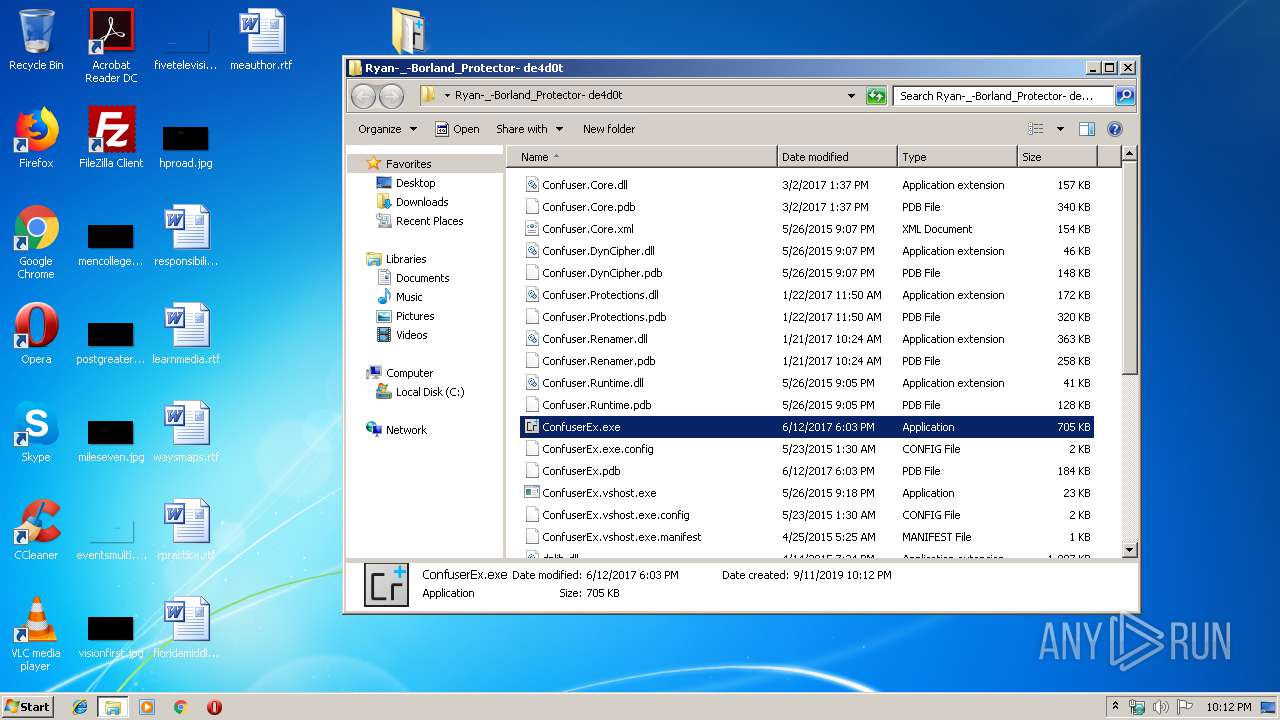
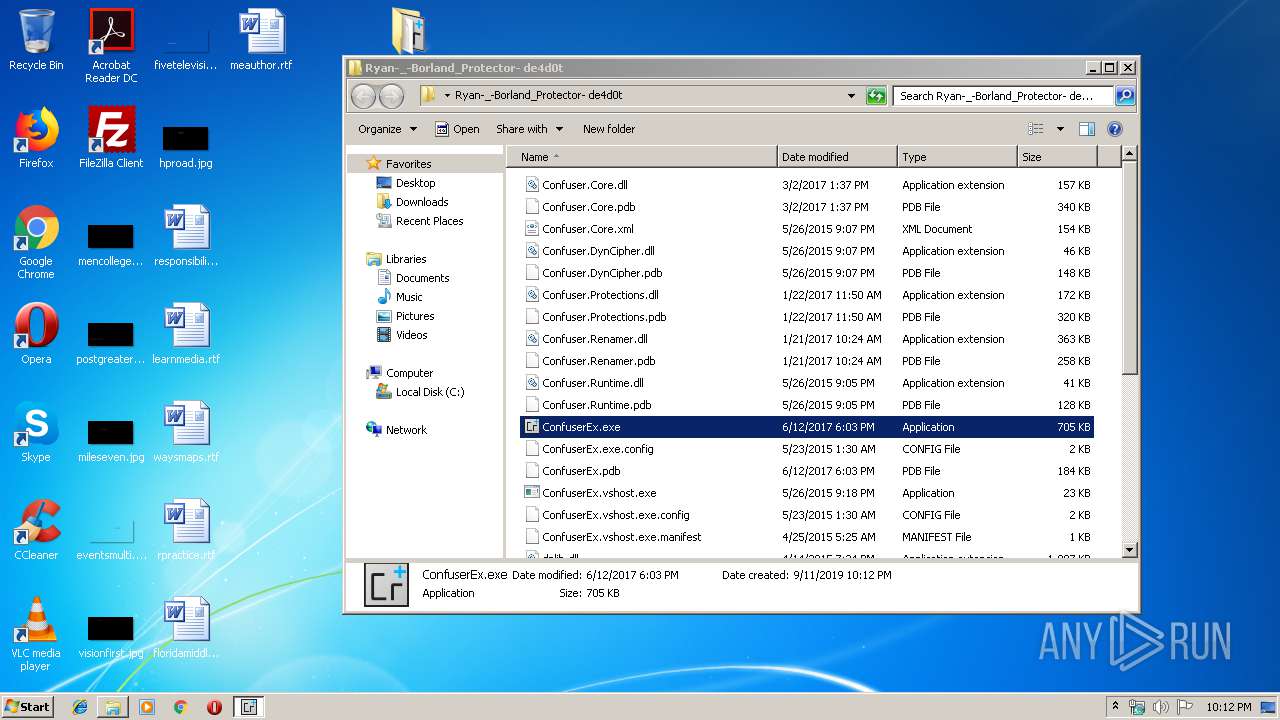
| 408 | "C:\Users\admin\Desktop\Ryan-_-Borland_Protector- de4d0t\ConfuserEx.exe" | C:\Users\admin\Desktop\Ryan-_-Borland_Protector- de4d0t\ConfuserEx.exe | explorer.exe | ||||||||||||
User: admin Company: Xenocode Integrity Level: HIGH Description: ConfuserEx Exit code: 0 Version: 4.5.0 Modules
| |||||||||||||||
| 1728 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2892 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Ryan-_-Borland_Protector- de4d0t.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
795
Read events
771
Write events
24
Delete events
0
Modification events
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Ryan-_-Borland_Protector- de4d0t.rar | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
8
Suspicious files
0
Text files
4
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2892 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2892.34596\Ryan-_-Borland_Protector- de4d0t\dnlib.pdb | — | |
MD5:— | SHA256:— | |||
| 2892 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2892.34596\Ryan-_-Borland_Protector- de4d0t\dnlib.xml | — | |
MD5:— | SHA256:— | |||
| 2892 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2892.34596\Ryan-_-Borland_Protector- de4d0t\GalaSoft.MvvmLight.Extras.WPF4.dll | — | |
MD5:— | SHA256:— | |||
| 2892 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2892.34596\Ryan-_-Borland_Protector- de4d0t\GalaSoft.MvvmLight.WPF4.dll | — | |
MD5:— | SHA256:— | |||
| 2892 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2892.34596\Ryan-_-Borland_Protector- de4d0t\MahApps.Metro.dll | — | |
MD5:— | SHA256:— | |||
| 2892 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2892.34596\Ryan-_-Borland_Protector- de4d0t\MahApps.Metro.xml | — | |
MD5:— | SHA256:— | |||
| 2892 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2892.34596\Ryan-_-Borland_Protector- de4d0t\MetroFramework.Design.dll | — | |
MD5:— | SHA256:— | |||
| 2892 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2892.34596\Ryan-_-Borland_Protector- de4d0t\MetroFramework.dll | — | |
MD5:— | SHA256:— | |||
| 2892 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2892.34596\Ryan-_-Borland_Protector- de4d0t\MetroFramework.Fonts.dll | — | |
MD5:— | SHA256:— | |||
| 2892 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2892.34596\Ryan-_-Borland_Protector- de4d0t\Microsoft.Practices.ServiceLocation.dll | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report