| File name: | IDM_6.4x software2u.exe |
| Full analysis: | https://app.any.run/tasks/c7ac33cc-e47a-4f1e-83a6-01ed946940cf |
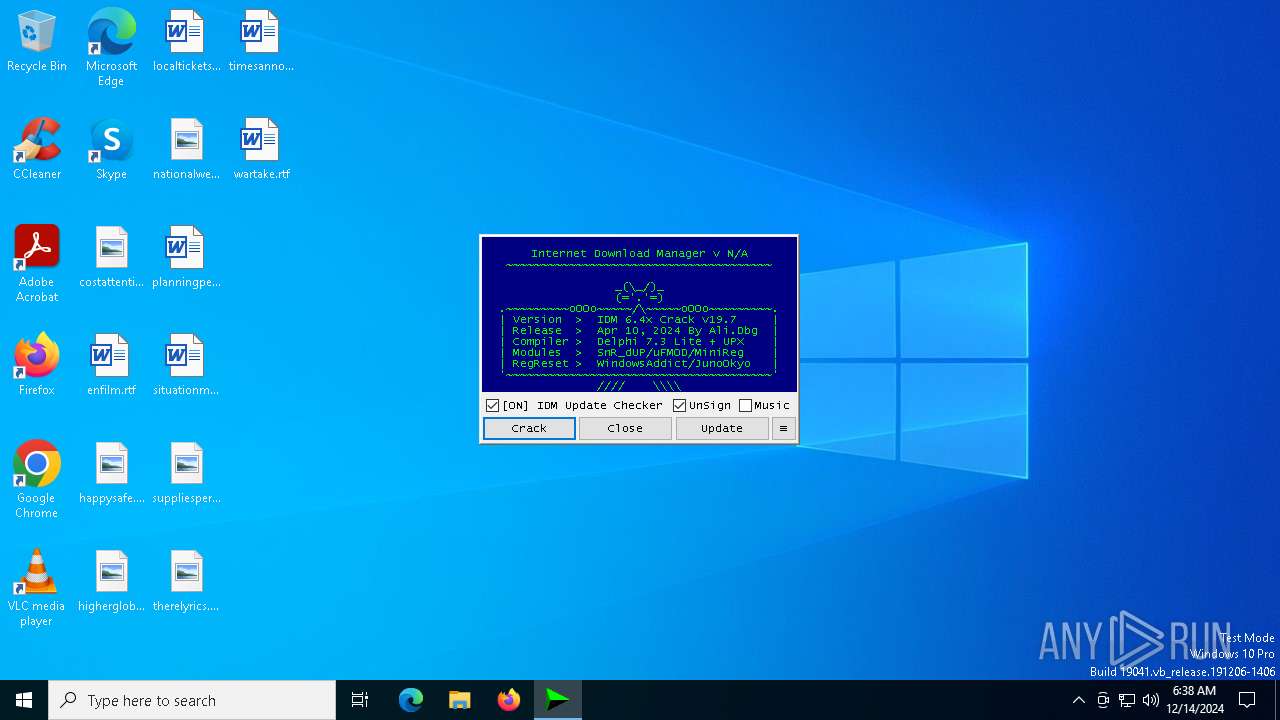
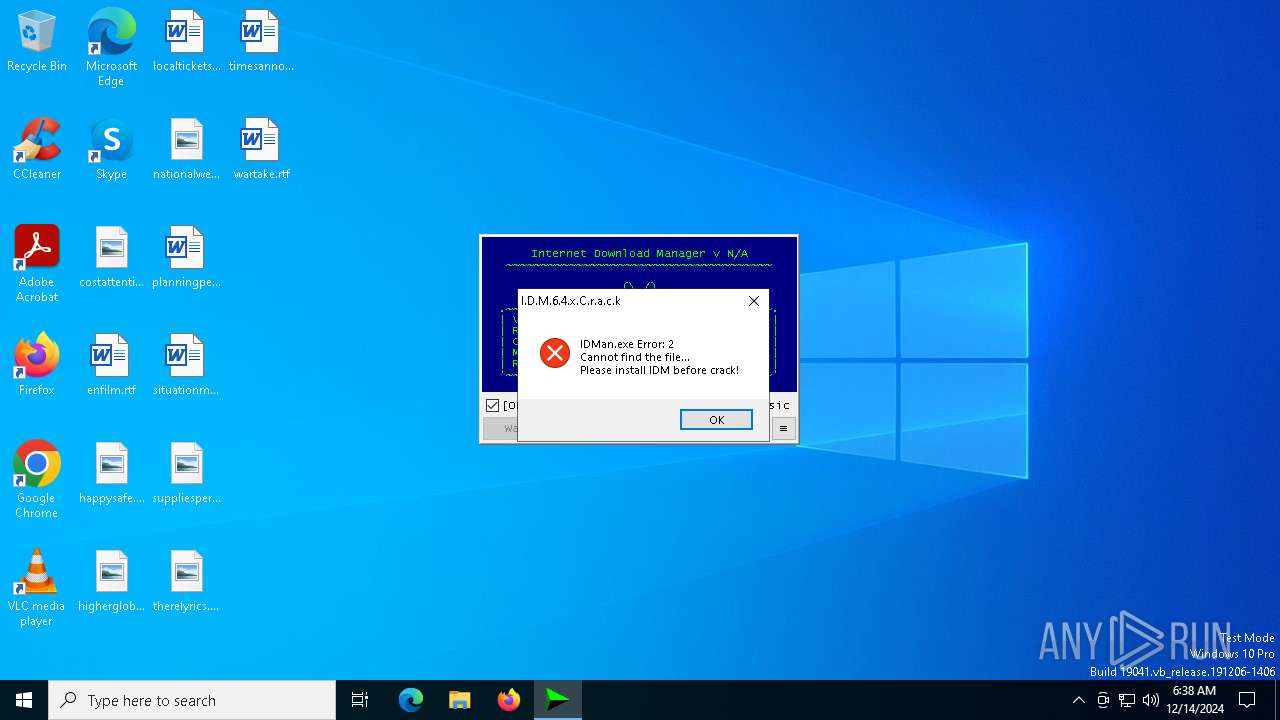
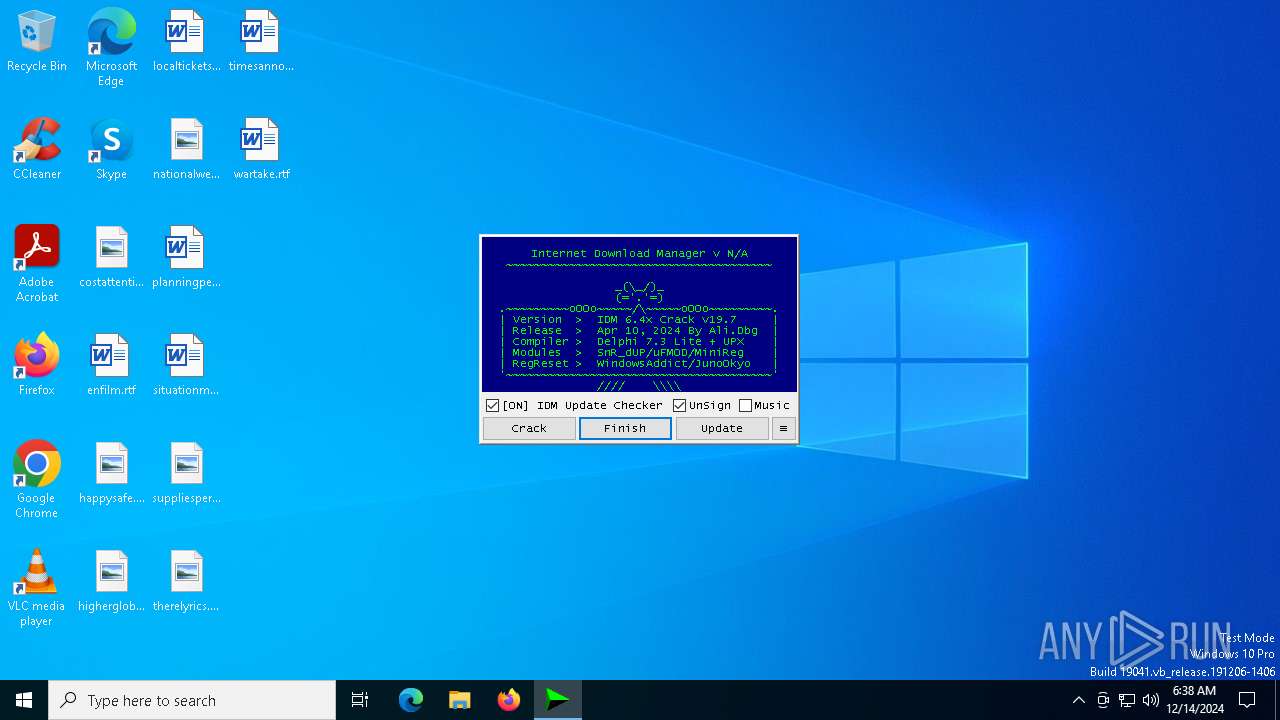
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2024, 06:38:20 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | C9CC4256AA07471277C0750033EAA399 |
| SHA1: | 02BEC8ED28462CCF5FAEB7BAC50B11E7A80406A2 |
| SHA256: | F5DC5C81E4AED96EA17578C9564A9282EBF911F2B58DAB4EFFED538013919012 |
| SSDEEP: | 98304:yXACbWdI+BcG/iQLTl2yNIRVAajVo6QM1AW/jZm2SG/kDHIjGwC1R4yHJwDHf2kC:FSZx12 |
MALICIOUS
Executing a file with an untrusted certificate
- mdwslp.exe (PID: 6988)
- uptimecrx.exe (PID: 2828)
- l5VS6Z.exe (PID: 3820)
- kQycVz.exe (PID: 6264)
- uptimecrx.exe (PID: 6888)
- mdwslp.exe (PID: 2744)
- mdwslp.exe (PID: 7300)
Runs injected code in another process
- kQycVz.exe (PID: 6264)
Application was injected by another process
- explorer.exe (PID: 4488)
SUSPICIOUS
Executable content was dropped or overwritten
- IDM_6.4x software2u.exe (PID: 6528)
- IDM_6.4x_Crack.exe (PID: 6760)
- mdwslp.exe (PID: 6988)
- l5VS6Z.exe (PID: 3820)
Reads security settings of Internet Explorer
- IDM_6.4x_Crack.exe (PID: 6760)
- IDM_6.4x software2u.exe (PID: 6528)
- mdwslp.exe (PID: 6988)
- uptimecrx.exe (PID: 6888)
Reads the date of Windows installation
- IDM_6.4x software2u.exe (PID: 6528)
- IDM_6.4x_Crack.exe (PID: 6760)
- mdwslp.exe (PID: 6988)
- uptimecrx.exe (PID: 6888)
Checks Windows Trust Settings
- IDM_6.4x software2u.exe (PID: 6528)
- IDM_6.4x_Crack.exe (PID: 6760)
Likely accesses (executes) a file from the Public directory
- cmd.exe (PID: 6832)
- mdwslp.exe (PID: 6988)
- cmd.exe (PID: 7032)
- sc.exe (PID: 7088)
- sc.exe (PID: 6884)
- uptimecrx.exe (PID: 2828)
- cmd.exe (PID: 4876)
- signtool.exe (PID: 6284)
- cmd.exe (PID: 4596)
- sc.exe (PID: 6860)
- msedge.exe (PID: 7084)
- mdwslp.exe (PID: 2744)
- uptimecrx.exe (PID: 6888)
- signtool.exe (PID: 4164)
- cmd.exe (PID: 8136)
- cmd.exe (PID: 7072)
- sc.exe (PID: 6900)
- mdwslp.exe (PID: 7300)
- cmd.exe (PID: 7588)
- signtool.exe (PID: 7776)
- sc.exe (PID: 8020)
- cmd.exe (PID: 8060)
- signtool.exe (PID: 5640)
- cmd.exe (PID: 6444)
Process drops legitimate windows executable
- IDM_6.4x_Crack.exe (PID: 6760)
Starts CMD.EXE for commands execution
- IDM_6.4x_Crack.exe (PID: 6760)
- l5VS6Z.exe (PID: 3820)
- cmd.exe (PID: 6752)
- IDM_6.4x_Crack_v19.7.exe (PID: 5752)
- cmd.exe (PID: 6868)
- mdwslp.exe (PID: 6988)
- uptimecrx.exe (PID: 6888)
Starts SC.EXE for service management
- cmd.exe (PID: 6832)
- cmd.exe (PID: 6916)
- cmd.exe (PID: 7032)
- cmd.exe (PID: 7136)
- cmd.exe (PID: 4912)
- cmd.exe (PID: 6896)
- cmd.exe (PID: 4596)
- cmd.exe (PID: 7072)
- cmd.exe (PID: 7248)
- cmd.exe (PID: 8060)
- cmd.exe (PID: 8072)
Executes as Windows Service
- mdwslp.exe (PID: 6988)
- uptimecrx.exe (PID: 2828)
- uptimecrx.exe (PID: 6888)
- mdwslp.exe (PID: 7300)
- mdwslp.exe (PID: 2744)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3436)
- cmd.exe (PID: 6752)
- cmd.exe (PID: 6212)
- cmd.exe (PID: 628)
- cmd.exe (PID: 6504)
- cmd.exe (PID: 7388)
- cmd.exe (PID: 7360)
Uses REG/REGEDIT.EXE to modify registry
- IDM_6.4x_Crack_v19.7.exe (PID: 5752)
- cmd.exe (PID: 6752)
- cmd.exe (PID: 624)
Executing commands from a ".bat" file
- IDM_6.4x_Crack_v19.7.exe (PID: 5752)
- cmd.exe (PID: 6752)
Application launched itself
- cmd.exe (PID: 6752)
- cmd.exe (PID: 6868)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 6752)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 6752)
Hides command output
- cmd.exe (PID: 628)
- cmd.exe (PID: 624)
Starts application with an unusual extension
- cmd.exe (PID: 6752)
INFO
Reads the machine GUID from the registry
- IDM_6.4x software2u.exe (PID: 6528)
- signtool.exe (PID: 6284)
- mdwslp.exe (PID: 6988)
- signtool.exe (PID: 5640)
- IDM_6.4x_Crack.exe (PID: 6760)
- mdwslp.exe (PID: 2744)
- signtool.exe (PID: 4164)
- mdwslp.exe (PID: 7300)
- signtool.exe (PID: 7776)
Creates files or folders in the user directory
- IDM_6.4x software2u.exe (PID: 6528)
Checks supported languages
- IDM_6.4x_Crack.exe (PID: 6760)
- IDM_6.4x software2u.exe (PID: 6528)
- mdwslp.exe (PID: 6988)
- uptimecrx.exe (PID: 2828)
- l5VS6Z.exe (PID: 3820)
- signtool.exe (PID: 6284)
- IDM_6.4x_Crack_v19.7.exe (PID: 5752)
- kQycVz.exe (PID: 6264)
- signtool.exe (PID: 5640)
- mdwslp.exe (PID: 2744)
- chcp.com (PID: 7032)
- identity_helper.exe (PID: 7812)
- signtool.exe (PID: 4164)
- uptimecrx.exe (PID: 6888)
- mdwslp.exe (PID: 7300)
- signtool.exe (PID: 7776)
Reads the software policy settings
- IDM_6.4x software2u.exe (PID: 6528)
- IDM_6.4x_Crack.exe (PID: 6760)
- signtool.exe (PID: 6284)
- signtool.exe (PID: 5640)
- signtool.exe (PID: 4164)
- signtool.exe (PID: 7776)
The process uses the downloaded file
- IDM_6.4x_Crack.exe (PID: 6760)
- IDM_6.4x software2u.exe (PID: 6528)
- powershell.exe (PID: 5588)
- mdwslp.exe (PID: 6988)
- powershell.exe (PID: 3780)
- explorer.exe (PID: 4488)
- powershell.exe (PID: 7448)
- uptimecrx.exe (PID: 6888)
- powershell.exe (PID: 1356)
The sample compiled with english language support
- IDM_6.4x software2u.exe (PID: 6528)
- IDM_6.4x_Crack.exe (PID: 6760)
Reads the computer name
- IDM_6.4x software2u.exe (PID: 6528)
- IDM_6.4x_Crack.exe (PID: 6760)
- mdwslp.exe (PID: 6988)
- uptimecrx.exe (PID: 2828)
- IDM_6.4x_Crack_v19.7.exe (PID: 5752)
- signtool.exe (PID: 6284)
- signtool.exe (PID: 5640)
- uptimecrx.exe (PID: 6888)
- mdwslp.exe (PID: 2744)
- identity_helper.exe (PID: 7812)
- signtool.exe (PID: 4164)
- mdwslp.exe (PID: 7300)
- signtool.exe (PID: 7776)
Checks proxy server information
- IDM_6.4x software2u.exe (PID: 6528)
- IDM_6.4x_Crack.exe (PID: 6760)
Process checks computer location settings
- IDM_6.4x software2u.exe (PID: 6528)
- IDM_6.4x_Crack.exe (PID: 6760)
Create files in a temporary directory
- IDM_6.4x software2u.exe (PID: 6528)
- IDM_6.4x_Crack_v19.7.exe (PID: 5752)
- reg.exe (PID: 6072)
Checks operating system version
- cmd.exe (PID: 6752)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7052)
- powershell.exe (PID: 7092)
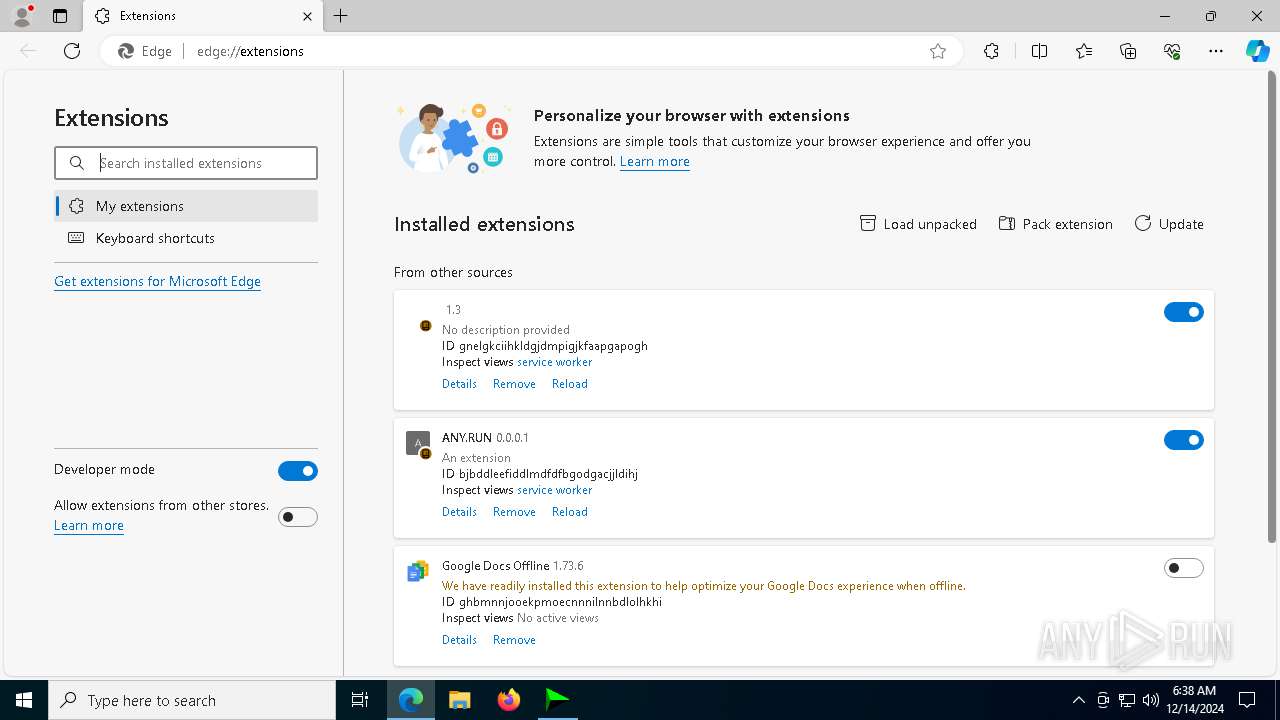
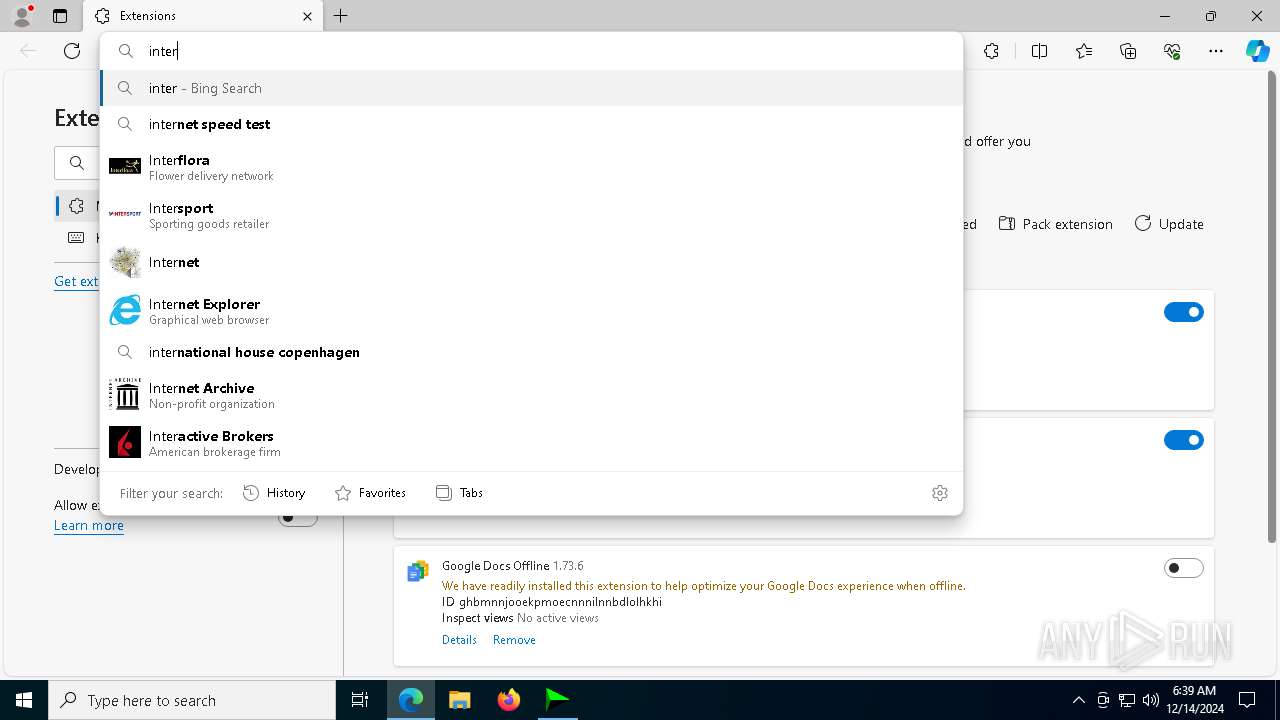
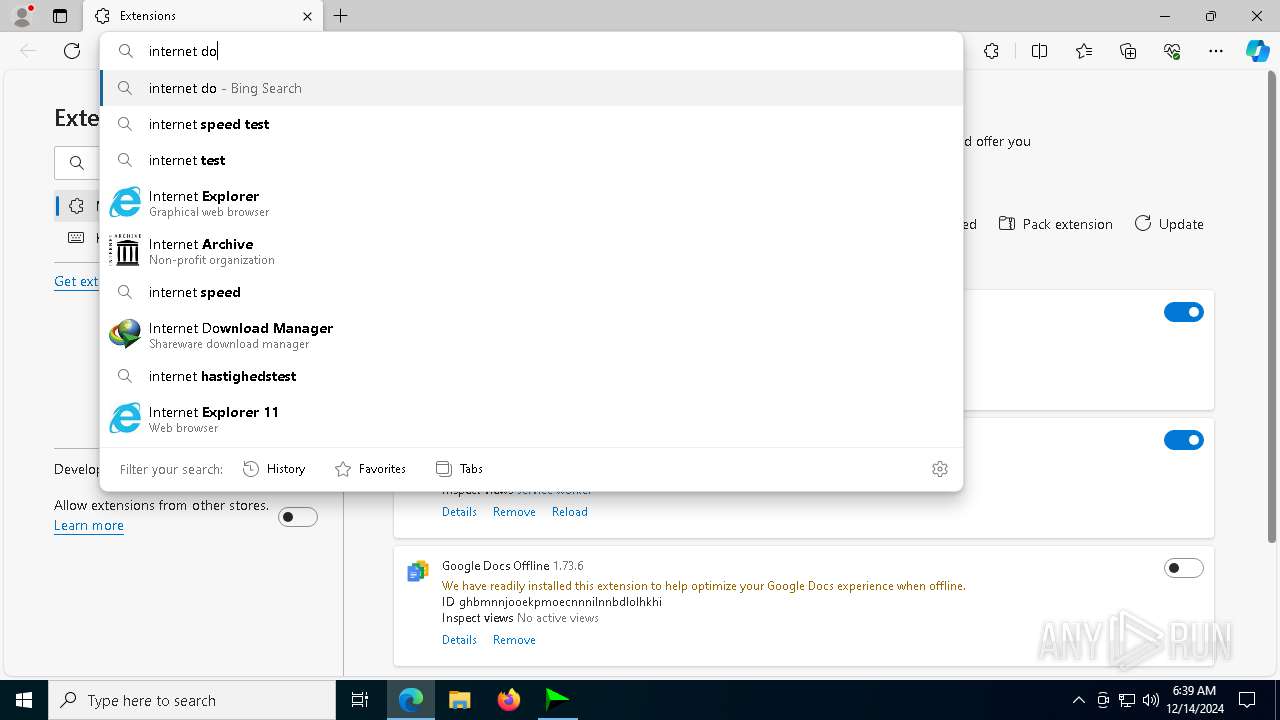
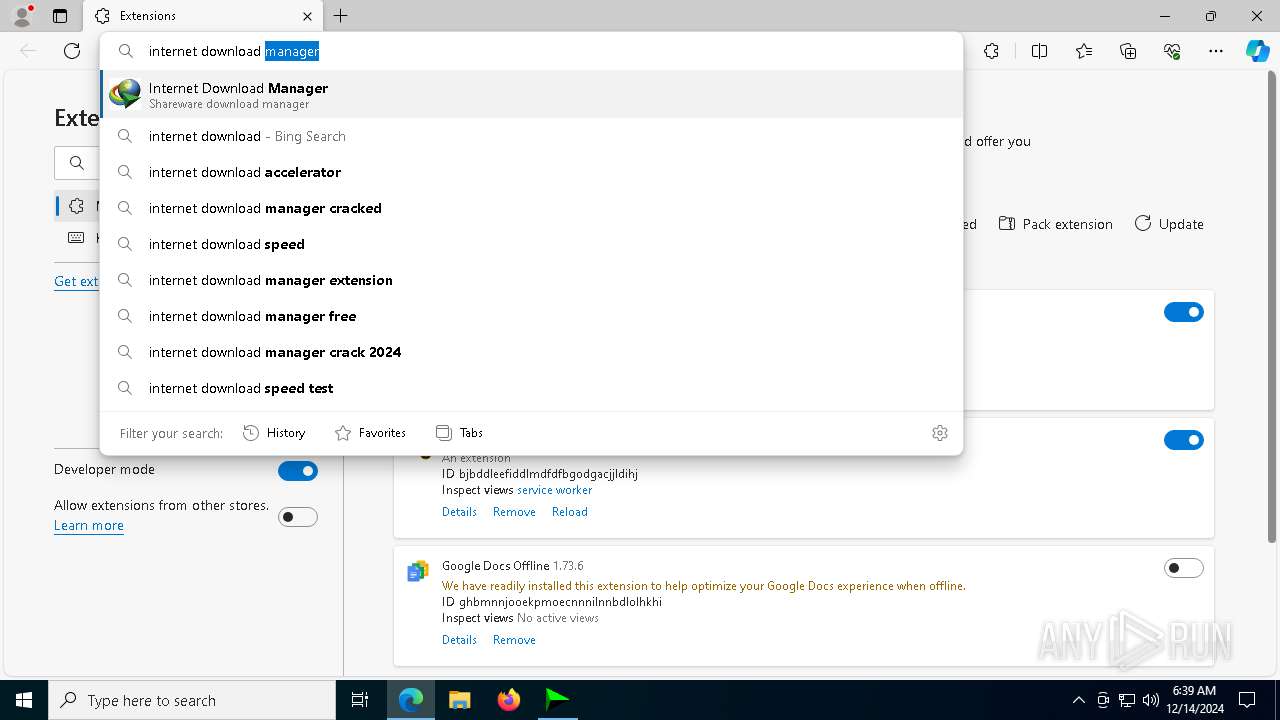
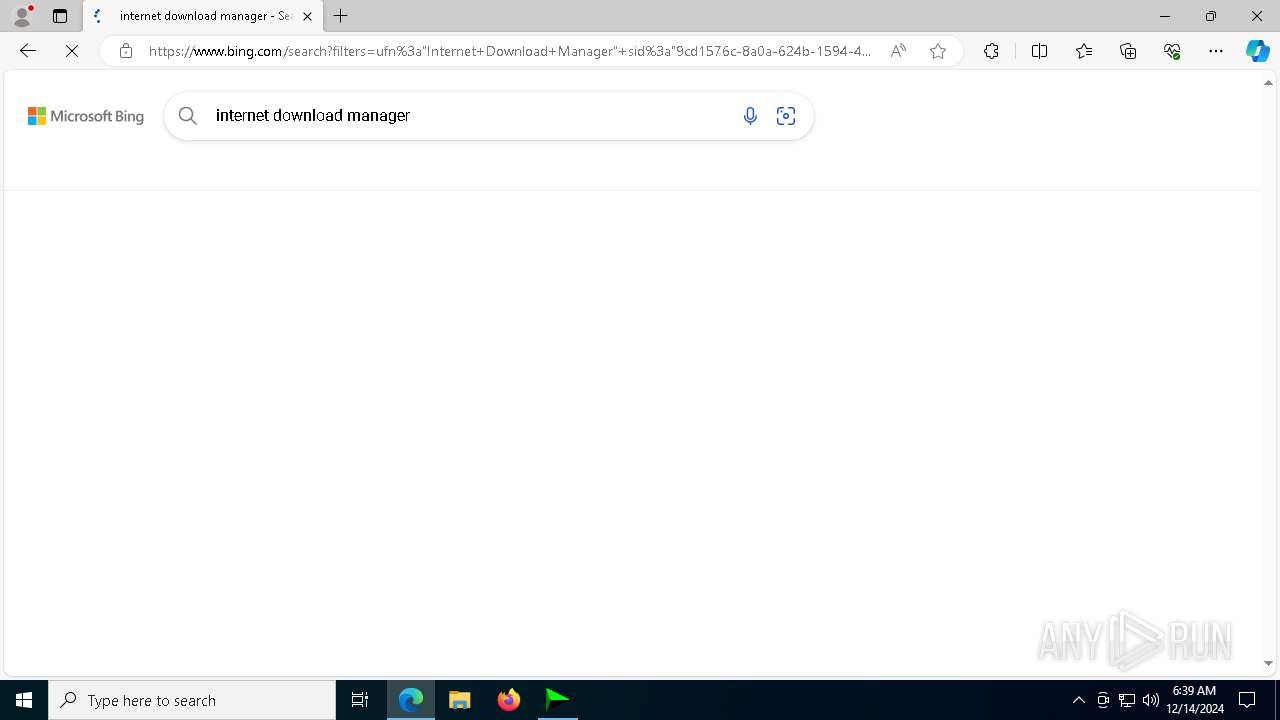
Manual execution by a user
- msedge.exe (PID: 7084)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4488)
Changes the display of characters in the console
- cmd.exe (PID: 6752)
Reads Environment values
- identity_helper.exe (PID: 7812)
Application launched itself
- msedge.exe (PID: 7084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:09:13 05:23:52+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.41 |
| CodeSize: | 296960 |
| InitializedDataSize: | 7142912 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x208a8 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
293
Monitored processes
161
Malicious processes
12
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 624 | C:\WINDOWS\system32\cmd.exe /c reg query "HKU\S-1-5-21-1693682860-607145093-2874071422-1001\Software\DownloadManager" /v ExePath 2>nul | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 628 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 628 | C:\WINDOWS\system32\cmd.exe /c powershell.exe "([System.Security.Principal.NTAccount](Get-WmiObject -Class Win32_ComputerSystem).UserName).Translate([System.Security.Principal.SecurityIdentifier]).Value" 2>nul | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1356 | powershell -Command "New-SelfSignedCertificate -Type CodeSigning -Subject 'CN=GEYgkO.projects.google.com' -KeyUsage DigitalSignature -FriendlyName 'GEYgkO.projects.google.com' -DnsName 'GEYgkO.projects.google.com' -CertStoreLocation 'Cert:\CurrentUser\My'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2092 | reg query "HKCU\Software\DownloadManager" "/v" "tvfrdt" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2148 | reg delete HKCU\IAS_TEST /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2148 | reg query "HKLM\SOFTWARE\Wow6432Node\Internet Download Manager" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2216 | reg delete HKU\S-1-5-21-1693682860-607145093-2874071422-1001\Software\Classes\Wow6432Node\CLSID\IAS_TEST /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2412 | reg add HKU\S-1-5-21-1693682860-607145093-2874071422-1001\Software\Classes\Wow6432Node\CLSID\IAS_TEST | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2412 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=4468 --field-trial-handle=2404,i,6082032750526550205,12569932222061276178,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
67 698
Read events
67 612
Write events
67
Delete events
19
Modification events
| (PID) Process: | (6528) IDM_6.4x software2u.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6528) IDM_6.4x software2u.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6528) IDM_6.4x software2u.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6760) IDM_6.4x_Crack.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6760) IDM_6.4x_Crack.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6760) IDM_6.4x_Crack.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5752) IDM_6.4x_Crack_v19.7.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (5752) IDM_6.4x_Crack_v19.7.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Wow6432Node\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (5752) IDM_6.4x_Crack_v19.7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (5752) IDM_6.4x_Crack_v19.7.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableRegistryTools |
Value: 0 | |||
Executable files
15
Suspicious files
169
Text files
107
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6760 | IDM_6.4x_Crack.exe | C:\Windows\System32\mi_nt_svc.dat | executable | |
MD5:D9AA5776CF71EFD408C4B48B1587B80D | SHA256:B460B3E8C0795B5BC2E9F2406E0A66AB2FF13B1A3D7CEF0C92B9D28B240A7EAF | |||
| 6528 | IDM_6.4x software2u.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B46811C17859FFB409CF0E904A4AA8F8 | der | |
MD5:971C514F84BBA0785F80AA1C23EDFD79 | SHA256:F157ED17FCAF8837FA82F8B69973848C9B10A02636848F995698212A08F31895 | |||
| 6760 | IDM_6.4x_Crack.exe | C:\Windows\System32\data1.zip | compressed | |
MD5:30CBD0B69D80C6F6752182E953D6560E | SHA256:D55723A534DAF669AE2AB5345B65ECDF0CD4AE0B6F864076E59191347CBE9A7A | |||
| 6528 | IDM_6.4x software2u.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B46811C17859FFB409CF0E904A4AA8F8 | binary | |
MD5:51766751E29079767080306D1BD46FAC | SHA256:D70AA95EC2EA85F90D6085DFE3B0D770C041ADC3826B97B9CD97EC1E40A3B6B8 | |||
| 6760 | IDM_6.4x_Crack.exe | C:\Windows\System32\ntdb.dat | executable | |
MD5:817AC44171AAA80E179B45B91E61E9F9 | SHA256:FEEF3273EE5064828553078E7001B488C05DB8BE7A2114BB02D5801ADF8E904F | |||
| 6760 | IDM_6.4x_Crack.exe | C:\Windows\System32\datax.dat | executable | |
MD5:EBEE140BDB9F1F80597CDEA66860E1B6 | SHA256:0A4CFB029A4E52521D60D5A65C0FC0AABBB59E5F68568DE6DF964F209E72108B | |||
| 6988 | mdwslp.exe | C:\Users\Public\data\ext\disabled-trusted-types.js | binary | |
MD5:7DE5BBCE72F622D991D5B232517F3D00 | SHA256:A5FA85CFAB45C7577877D7D7FAE2BA3A70B583F3B259EEF8A09C5EA071282D40 | |||
| 6760 | IDM_6.4x_Crack.exe | C:\Users\Public\data\ver.dat | binary | |
MD5:C2846DD09C460773E434A46376F3A878 | SHA256:B2E9457022303C98FFEAE3B020062870426DAD2FE4D3887B2BD938F3BCC177D3 | |||
| 6988 | mdwslp.exe | C:\Users\Public\data\ext\.DS_Store | ds_store | |
MD5:1BF5B6BCC8A8B8F3330BC18BED1BA1A7 | SHA256:DD8E3EFC5D651F36FFF858E20A4CAC5F275FBDC52EAF744F6FA8A3FC672F11CF | |||
| 6760 | IDM_6.4x_Crack.exe | C:\Users\Public\data\set.dat | binary | |
MD5:337126DAD75533D3F123A8F55A5394E3 | SHA256:A064DBBF3FC8479A3601AB2CDBB1FAA943761592A37A525313FA7552F6318C8B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
84
DNS requests
79
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6528 | IDM_6.4x software2u.exe | GET | 200 | 142.250.181.227:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.20.245.138:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5888 | SIHClient.exe | GET | 200 | 23.38.73.129:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5888 | SIHClient.exe | GET | 200 | 23.38.73.129:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4164 | signtool.exe | POST | 200 | 91.199.212.79:80 | http://timestamp.sectigo.com/ | unknown | — | — | whitelisted |
6284 | signtool.exe | POST | 200 | 91.199.212.79:80 | http://timestamp.sectigo.com/ | unknown | — | — | whitelisted |
5640 | signtool.exe | POST | 200 | 91.199.212.79:80 | http://timestamp.sectigo.com/ | unknown | — | — | whitelisted |
6528 | IDM_6.4x software2u.exe | GET | 200 | 142.250.181.227:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
3628 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.20.245.138:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
— | — | 23.38.73.129:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 2.19.80.27:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 40.126.32.72:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
dash.zintrack.com |
| unknown |
c.pki.goog |
| whitelisted |
go.microsoft.com |
| whitelisted |