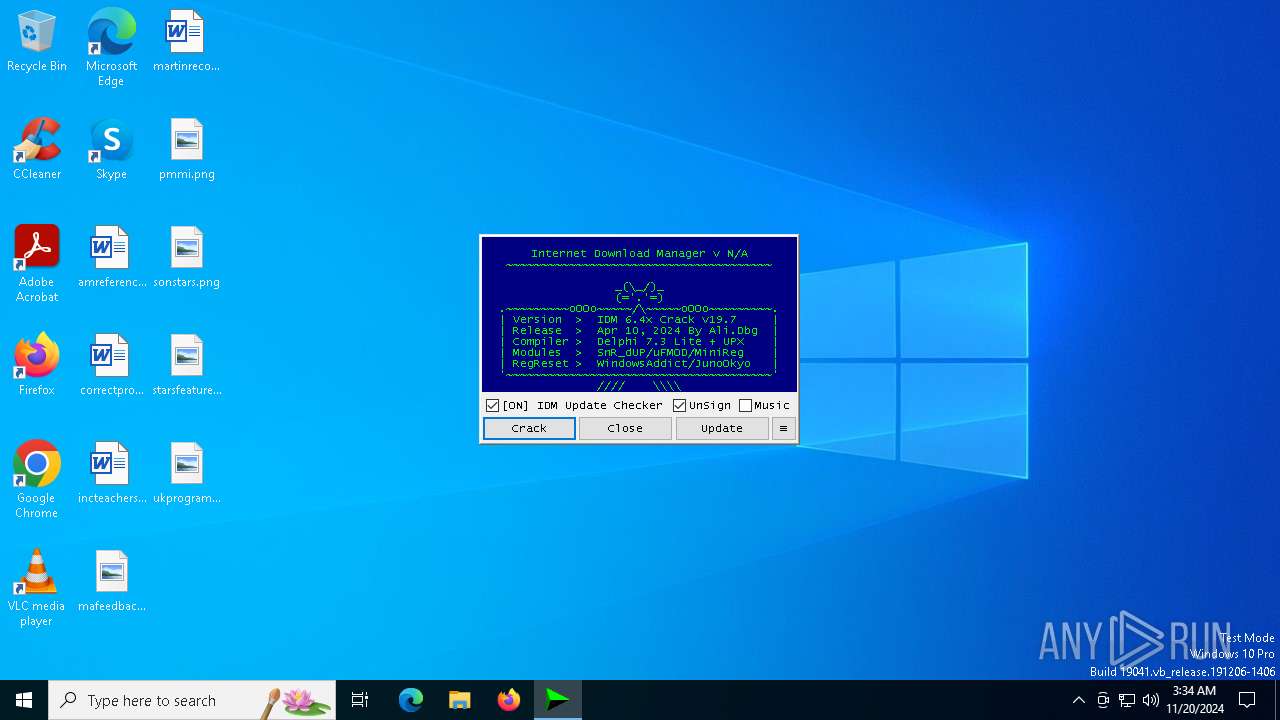
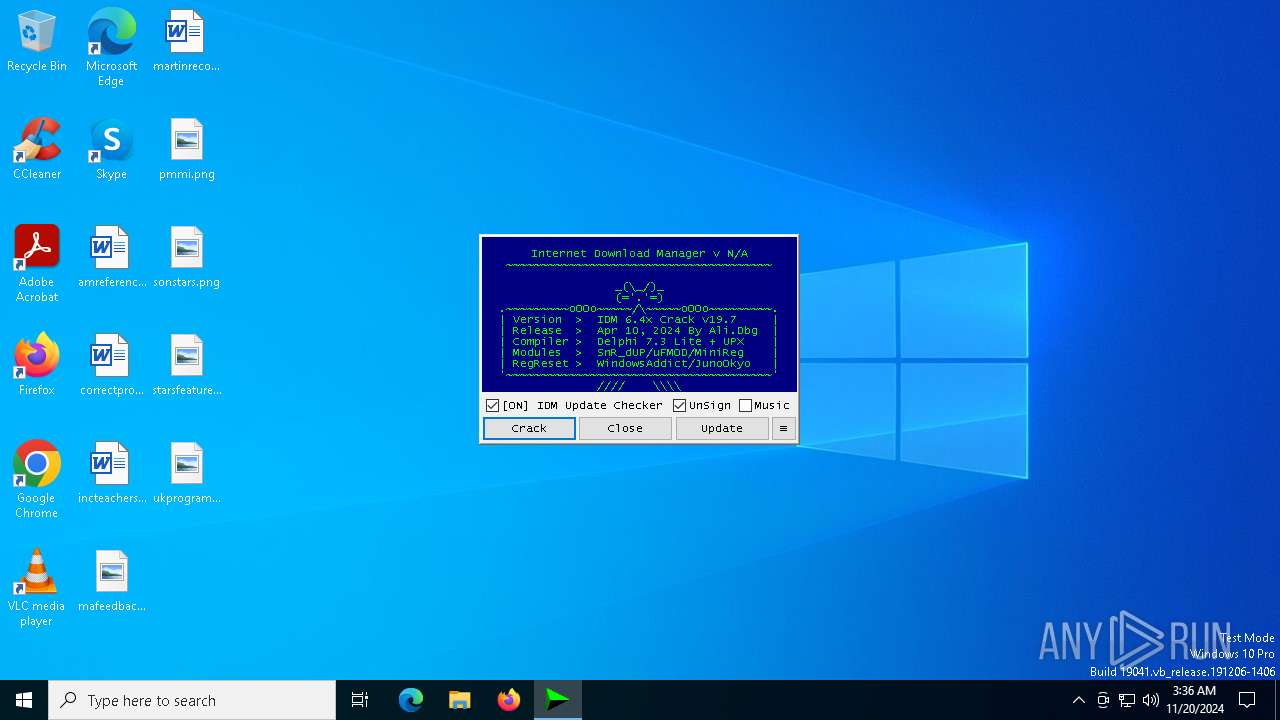
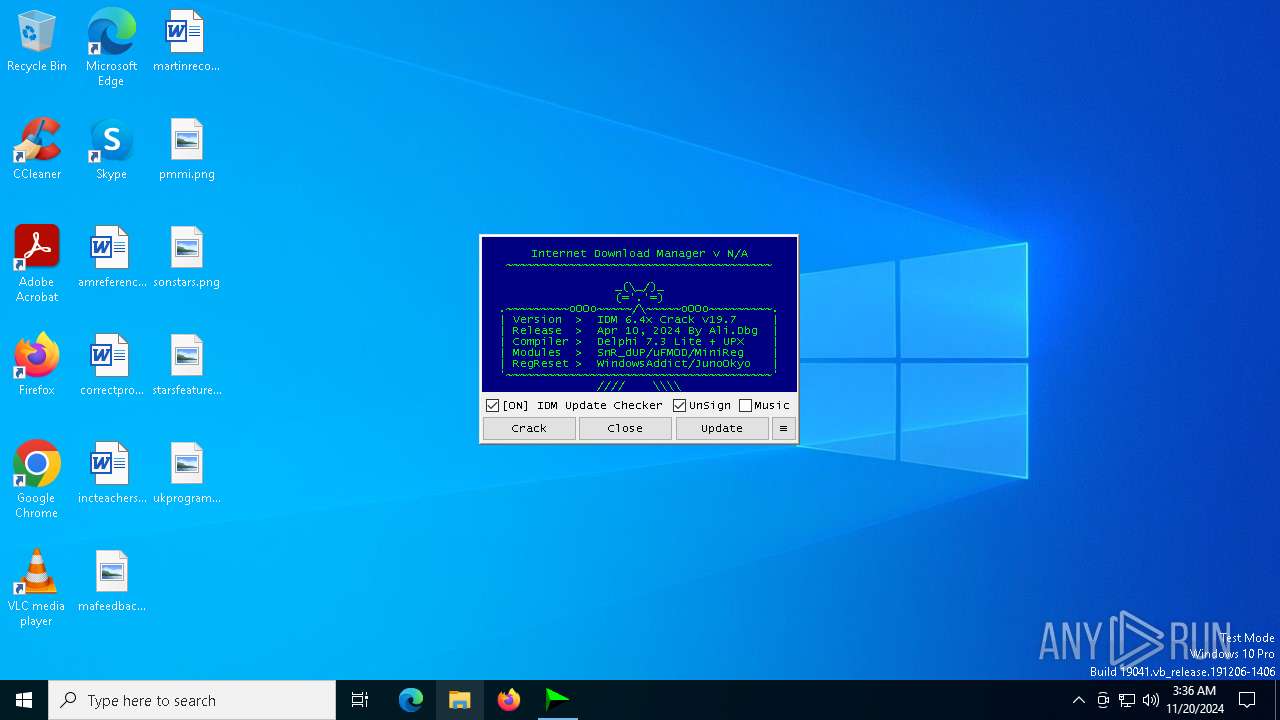
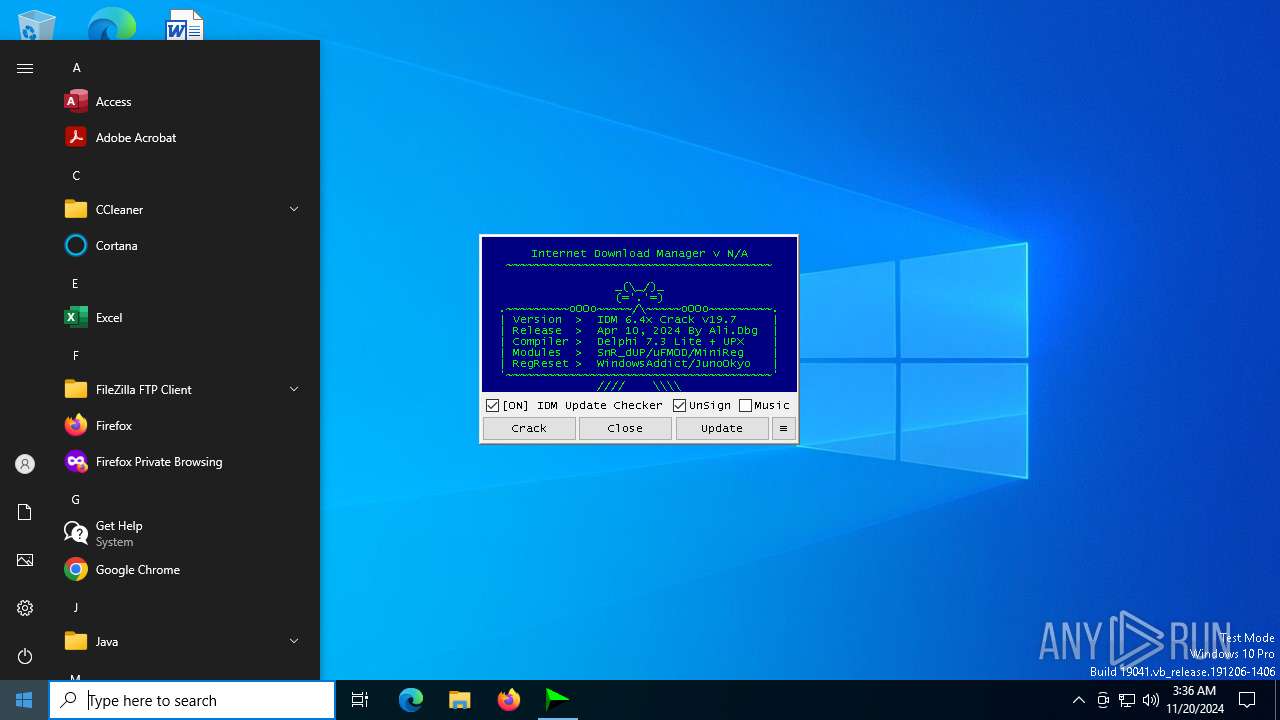
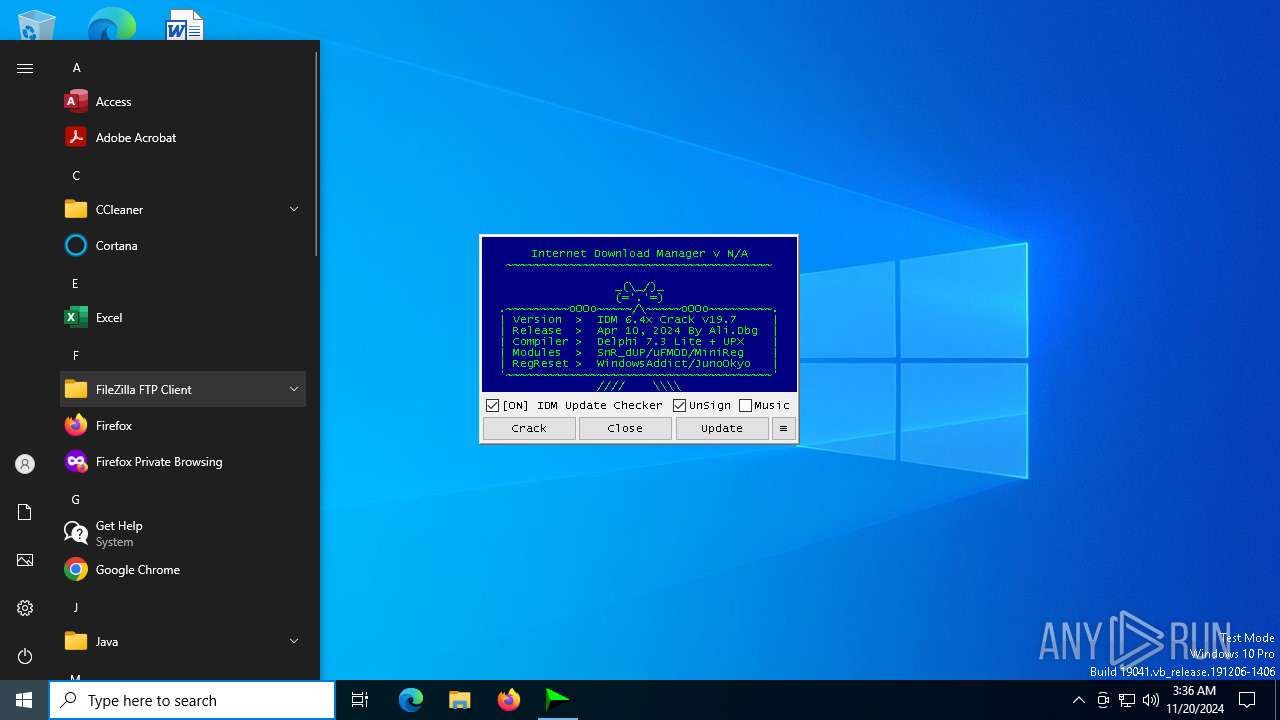
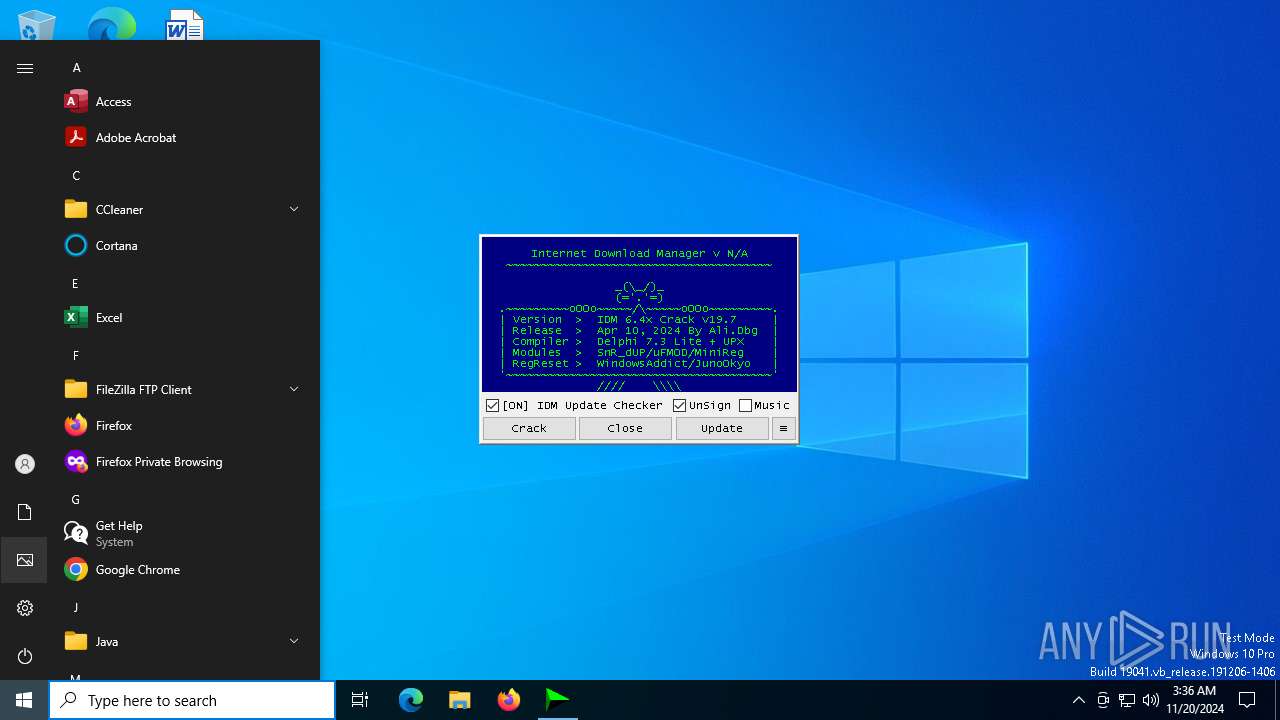
| File name: | IDM_6.4x_Crack_v19.7.exe |
| Full analysis: | https://app.any.run/tasks/6884f6ff-db80-4375-b35b-10a02e655b19 |
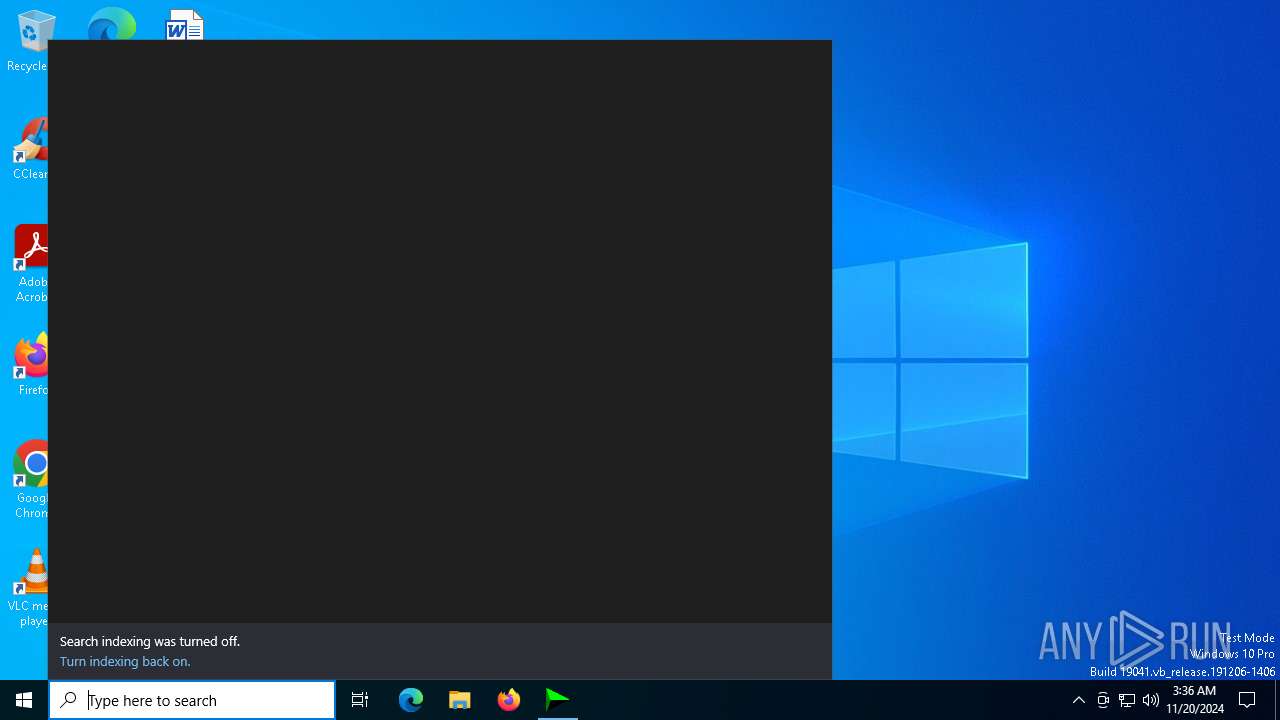
| Verdict: | Malicious activity |
| Analysis date: | November 20, 2024, 03:34:31 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | C9CC4256AA07471277C0750033EAA399 |
| SHA1: | 02BEC8ED28462CCF5FAEB7BAC50B11E7A80406A2 |
| SHA256: | F5DC5C81E4AED96EA17578C9564A9282EBF911F2B58DAB4EFFED538013919012 |
| SSDEEP: | 98304:yXACbWdI+BcG/iQLTl2yNIRVAajVo6QM1AW/jZm2SG/kDHIjGwC1R4yHJwDHf2kC:FSZx12 |
MALICIOUS
Executing a file with an untrusted certificate
- mdwslp.exe (PID: 6116)
- uptimecrx.exe (PID: 2000)
- 6gl7oc.exe (PID: 2940)
- J4KPYO.exe (PID: 6612)
- uptimecrx.exe (PID: 2332)
- mdwslp.exe (PID: 6636)
- mdwslp.exe (PID: 4968)
Application was injected by another process
- explorer.exe (PID: 4488)
Runs injected code in another process
- J4KPYO.exe (PID: 6612)
SUSPICIOUS
Reads security settings of Internet Explorer
- IDM_6.4x_Crack_v19.7.exe (PID: 2632)
- IDM_6.4x_Crack.exe (PID: 2396)
- mdwslp.exe (PID: 6116)
Checks Windows Trust Settings
- IDM_6.4x_Crack_v19.7.exe (PID: 2632)
- IDM_6.4x_Crack.exe (PID: 2396)
Reads the date of Windows installation
- IDM_6.4x_Crack_v19.7.exe (PID: 2632)
- IDM_6.4x_Crack.exe (PID: 2396)
- mdwslp.exe (PID: 6116)
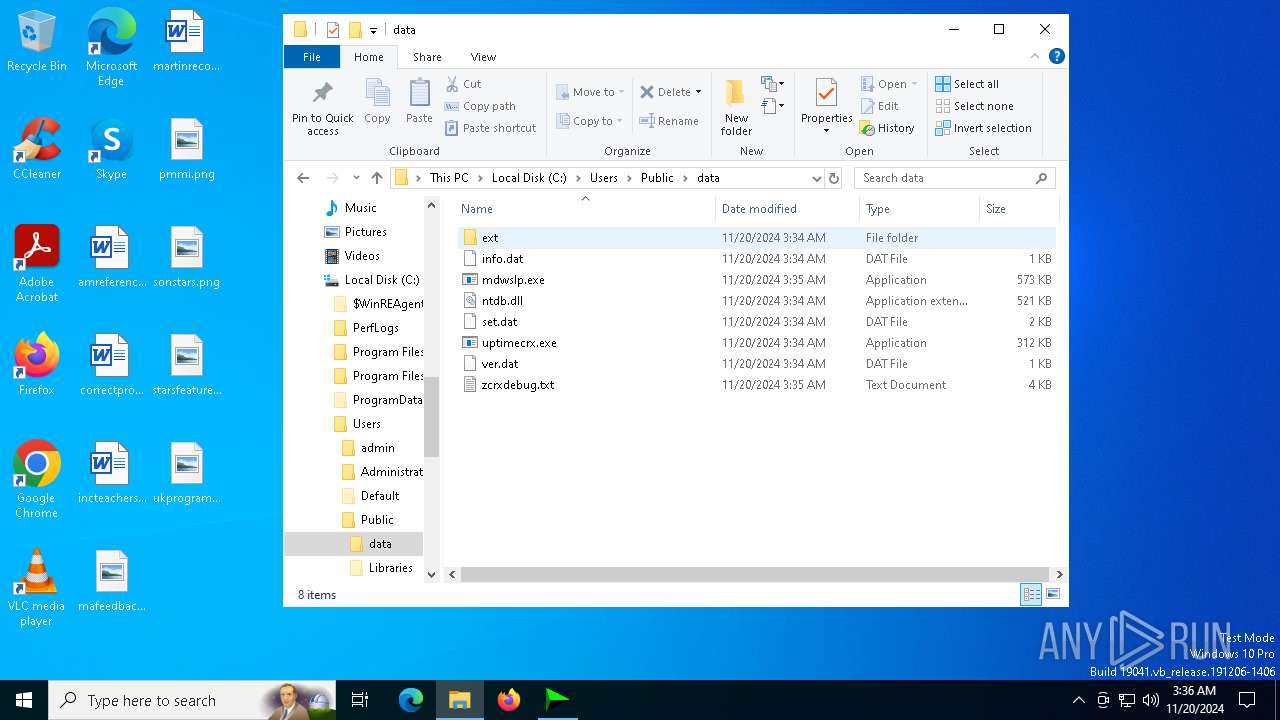
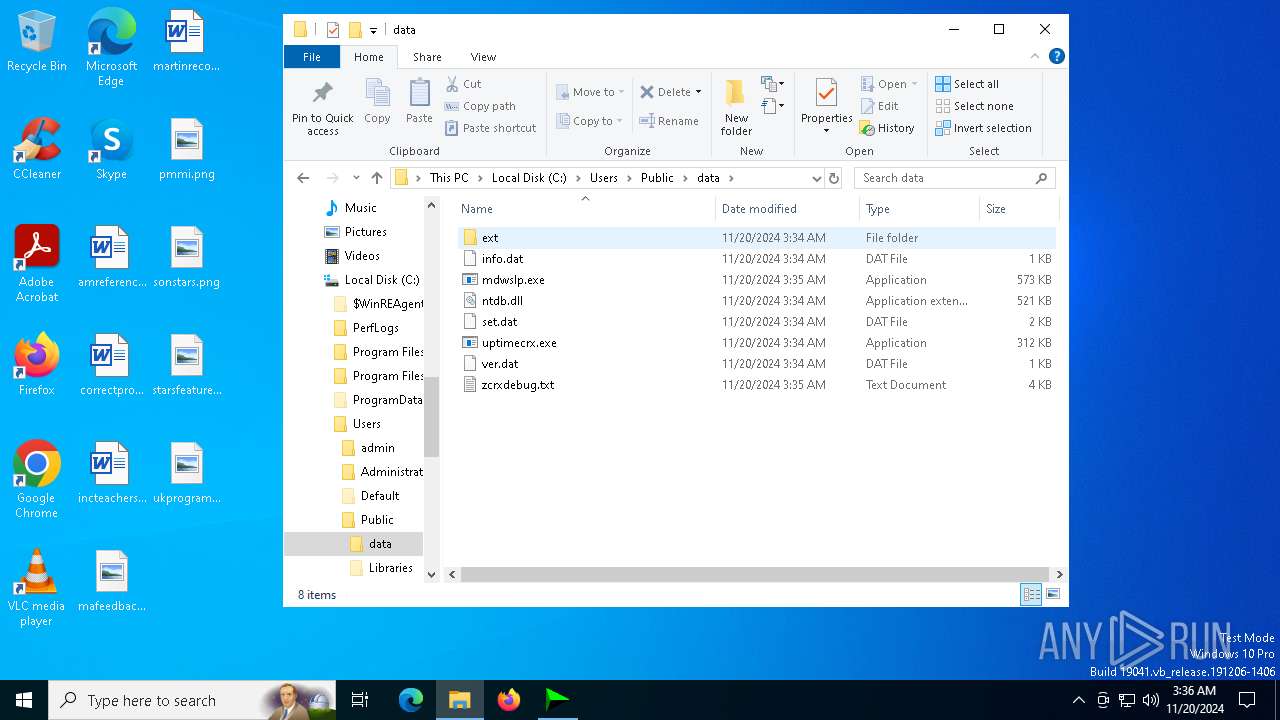
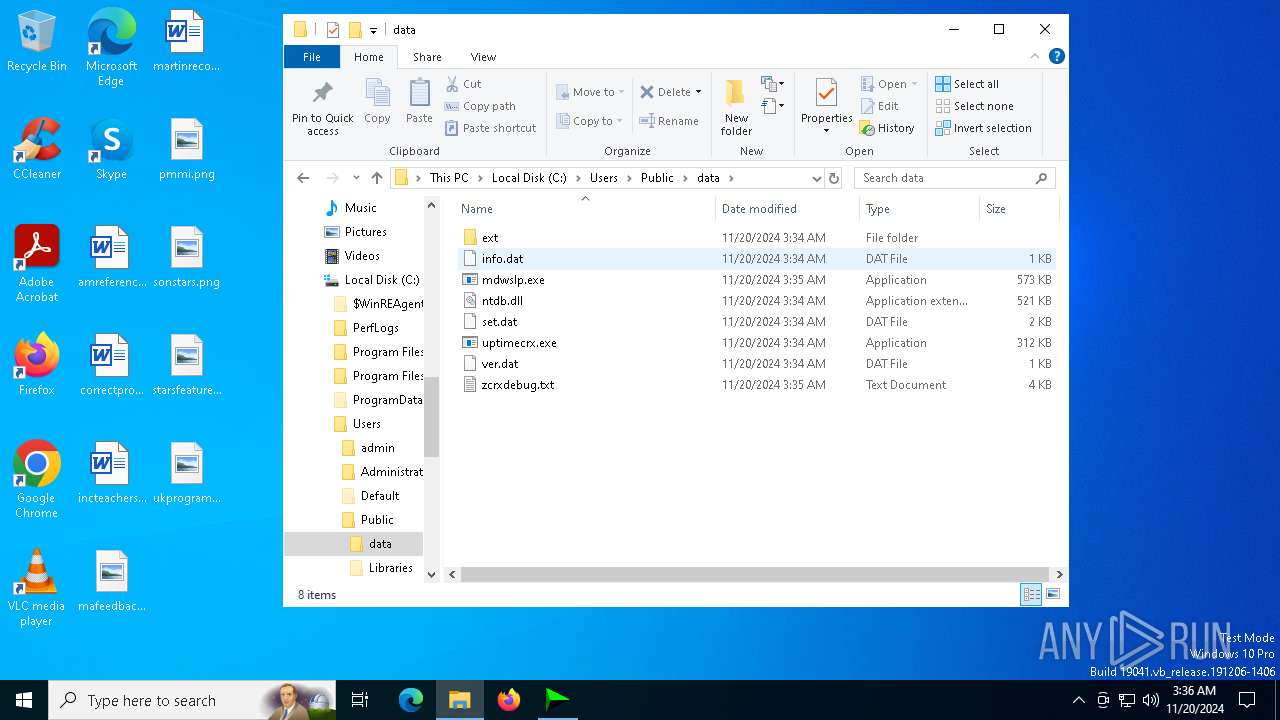
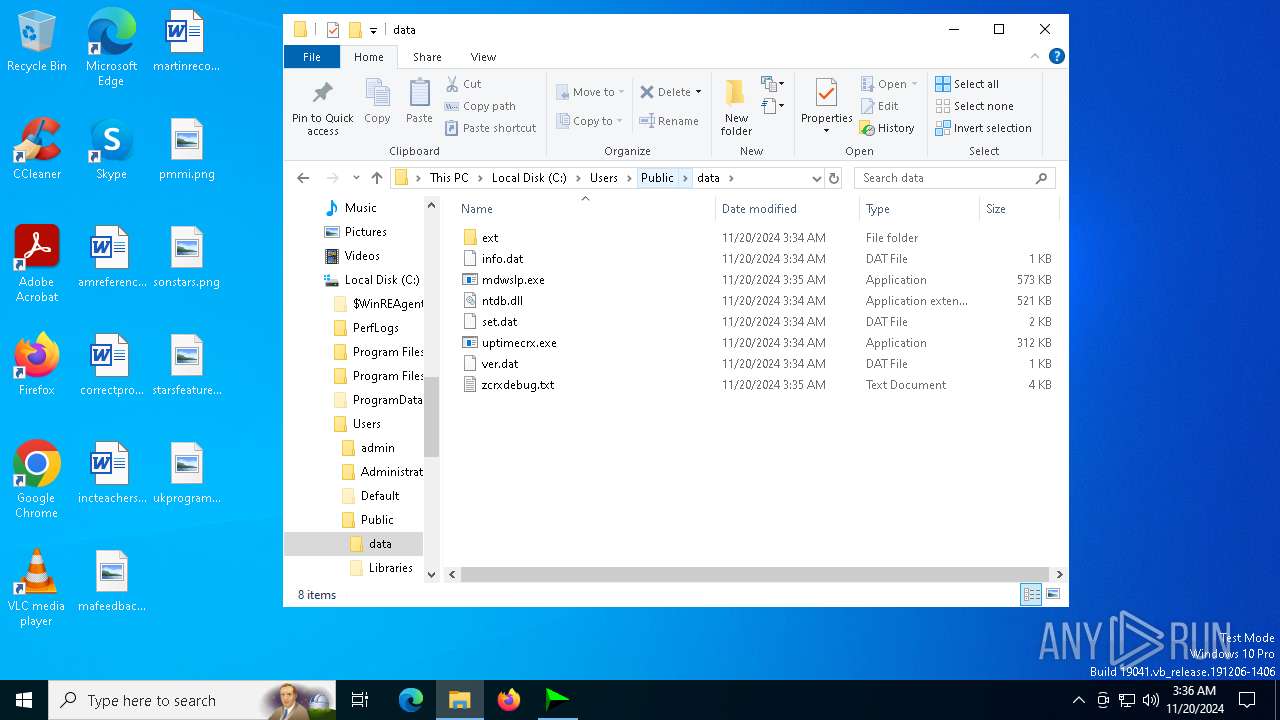
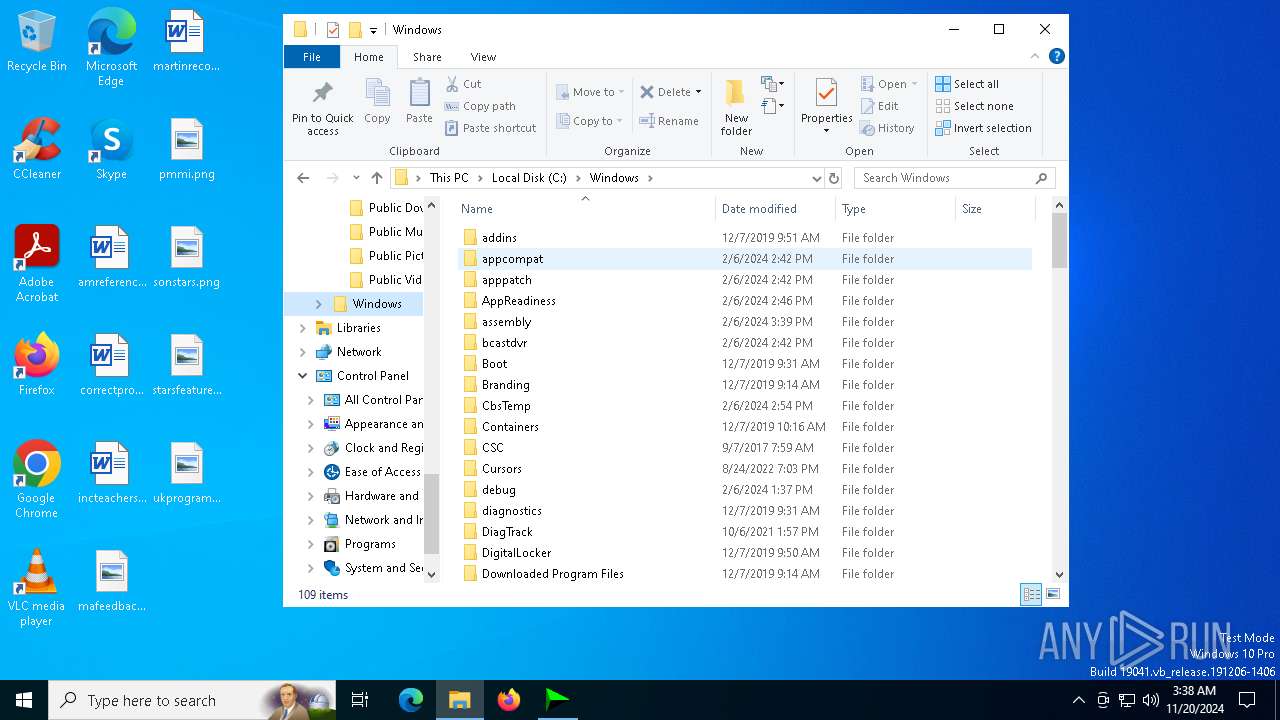
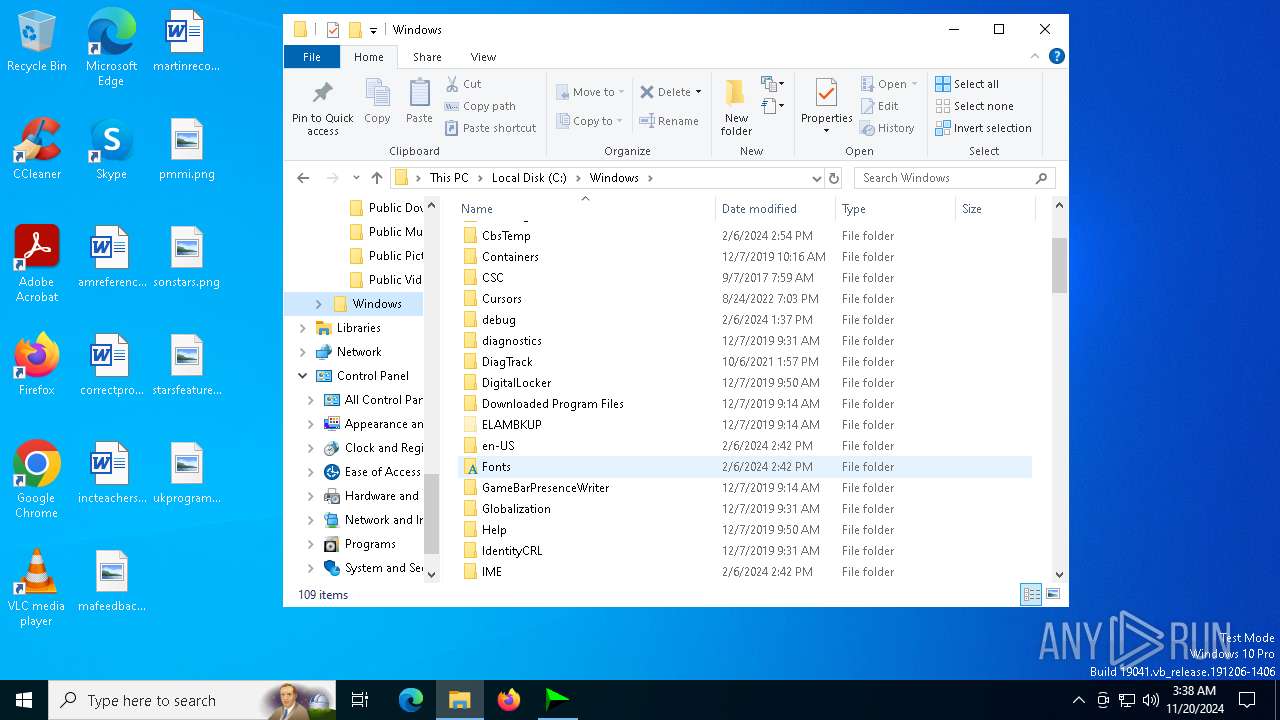
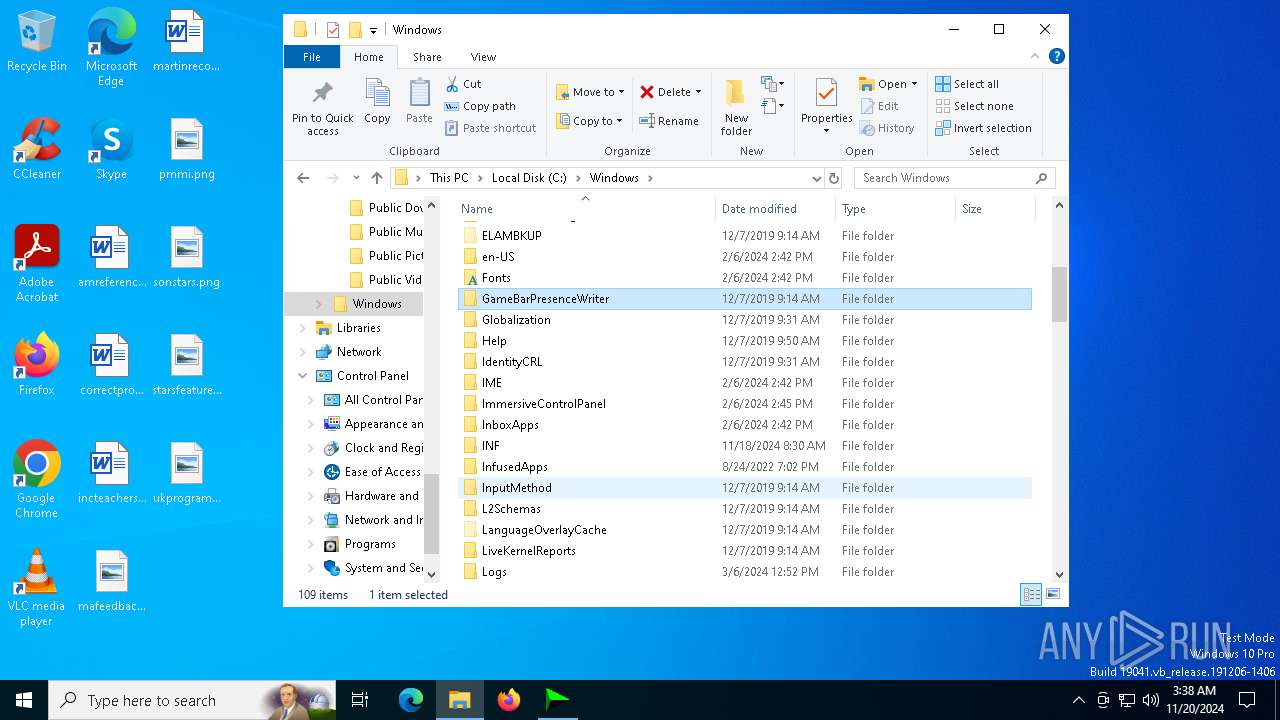
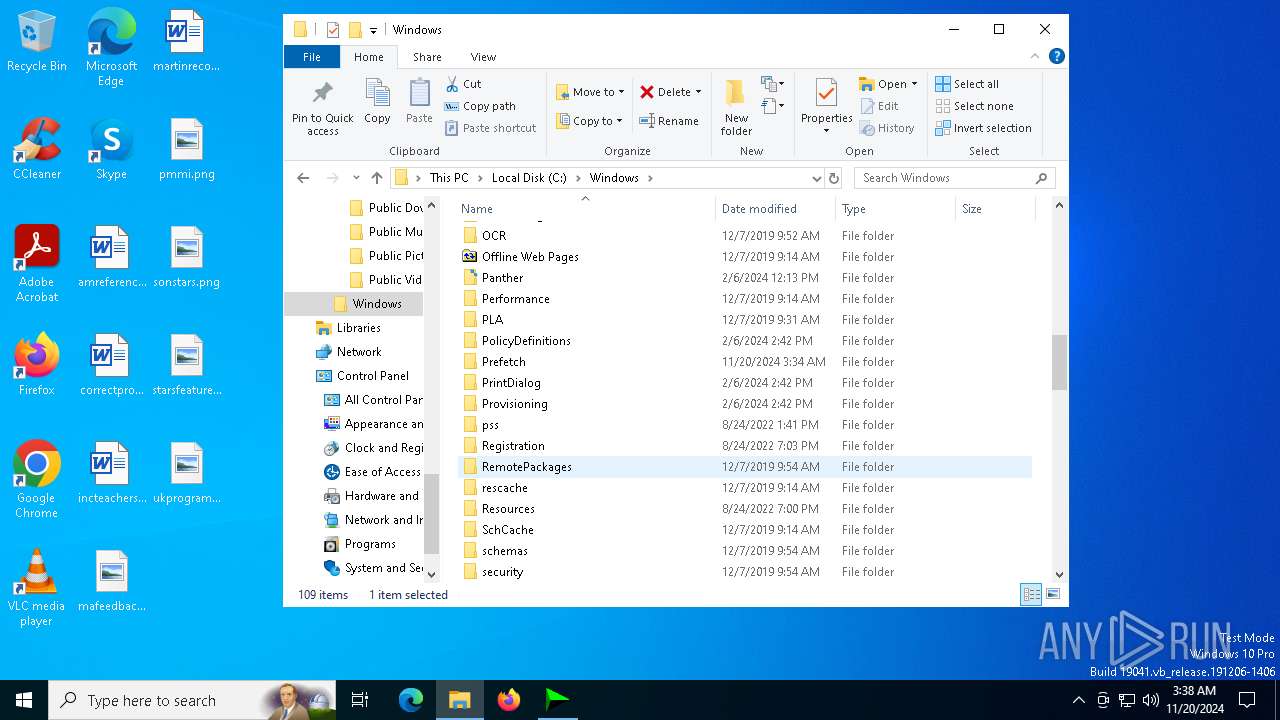
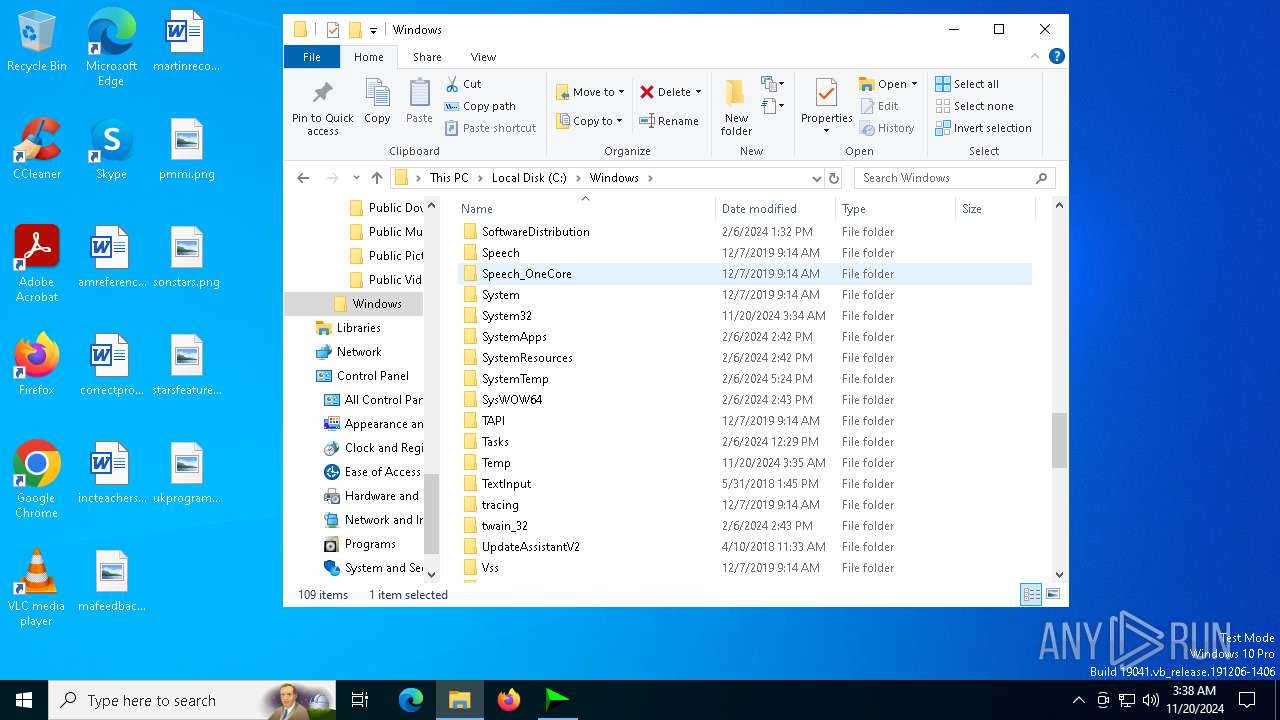
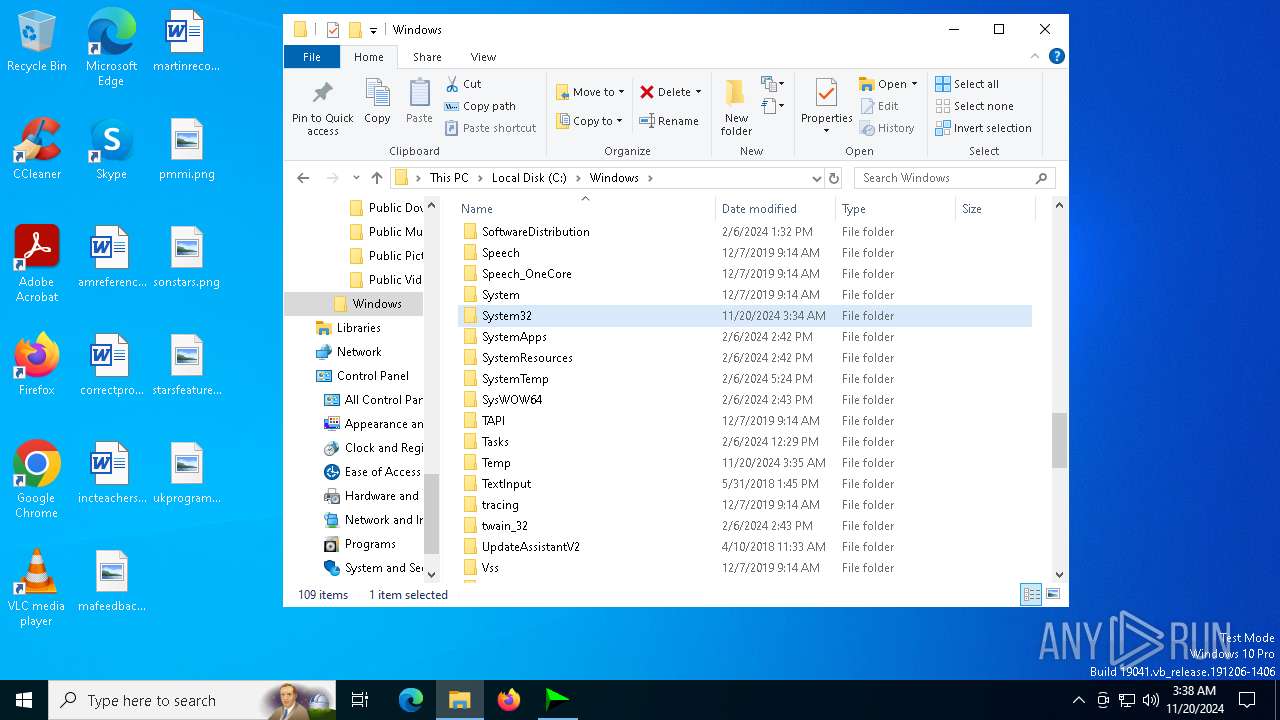
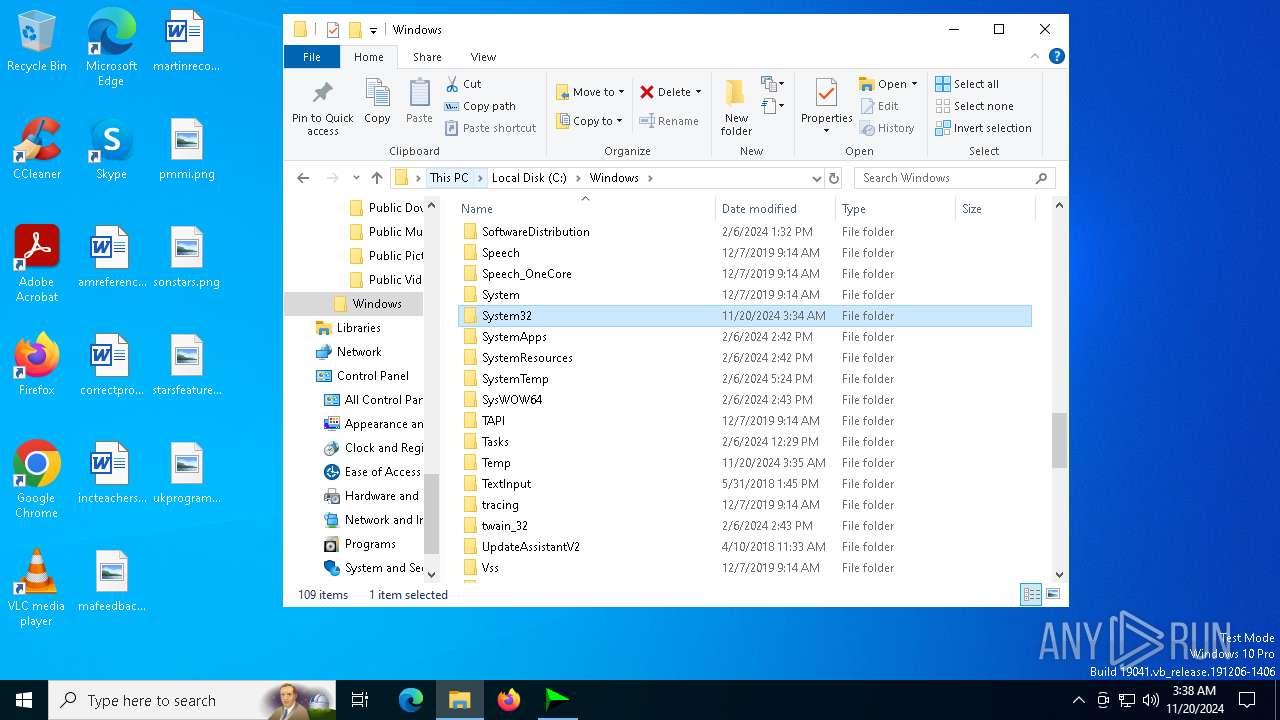
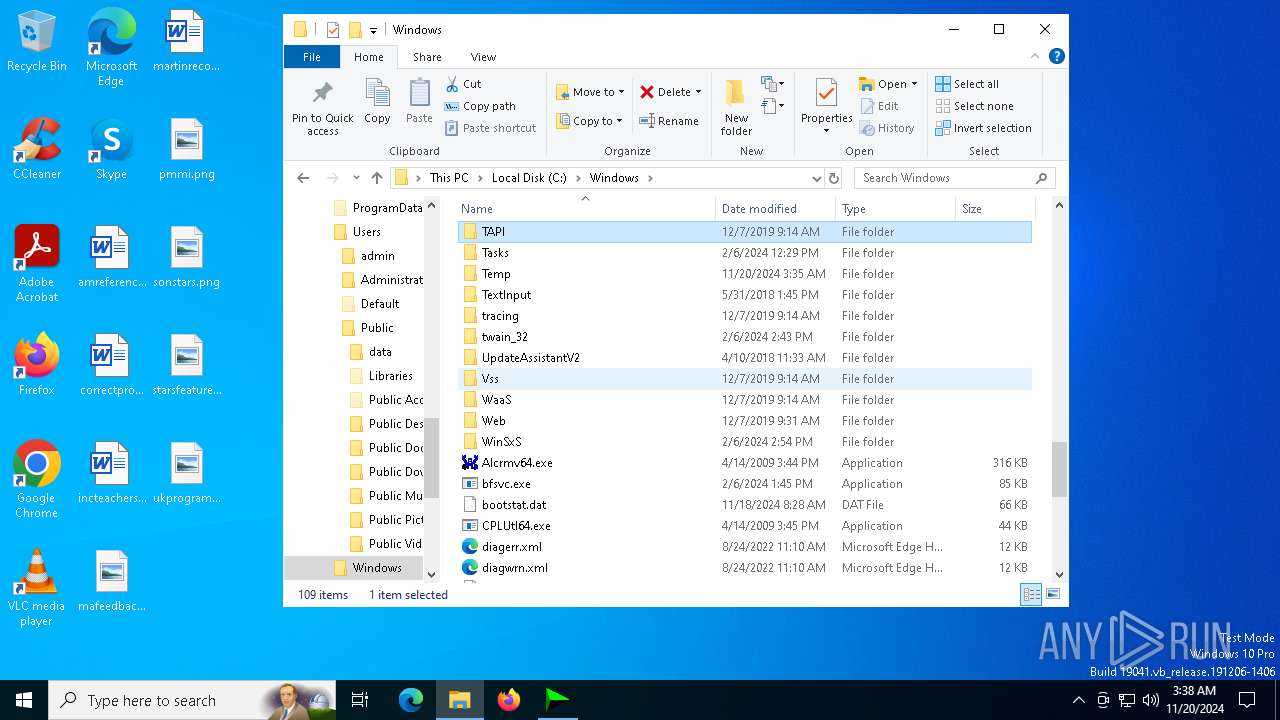
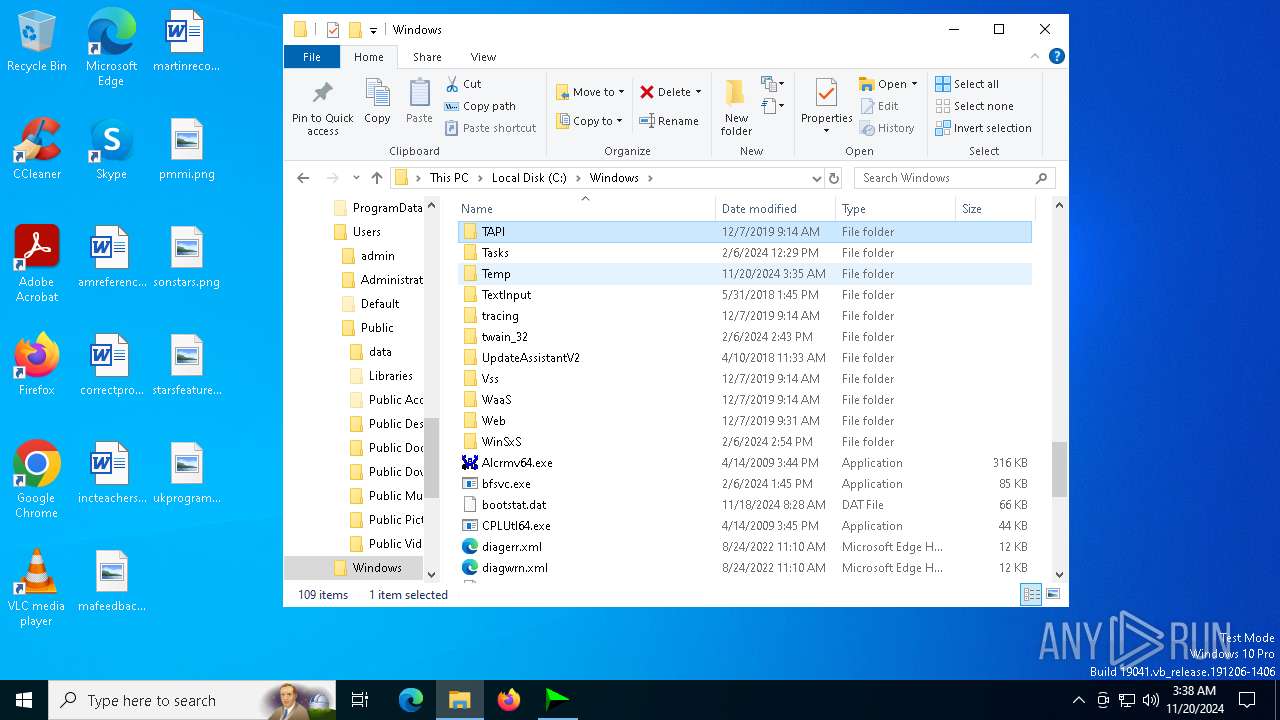
Process drops legitimate windows executable
- IDM_6.4x_Crack.exe (PID: 2396)
Executable content was dropped or overwritten
- IDM_6.4x_Crack_v19.7.exe (PID: 2632)
- IDM_6.4x_Crack.exe (PID: 2396)
- mdwslp.exe (PID: 6116)
- 6gl7oc.exe (PID: 2940)
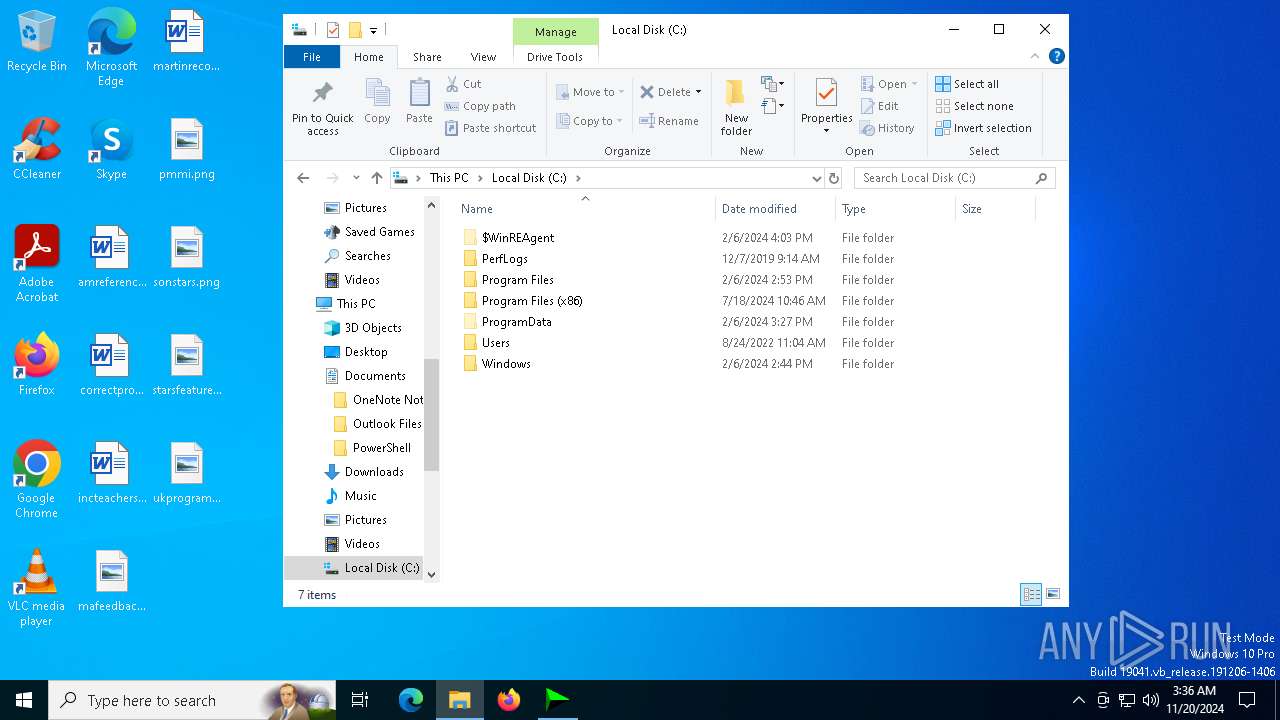
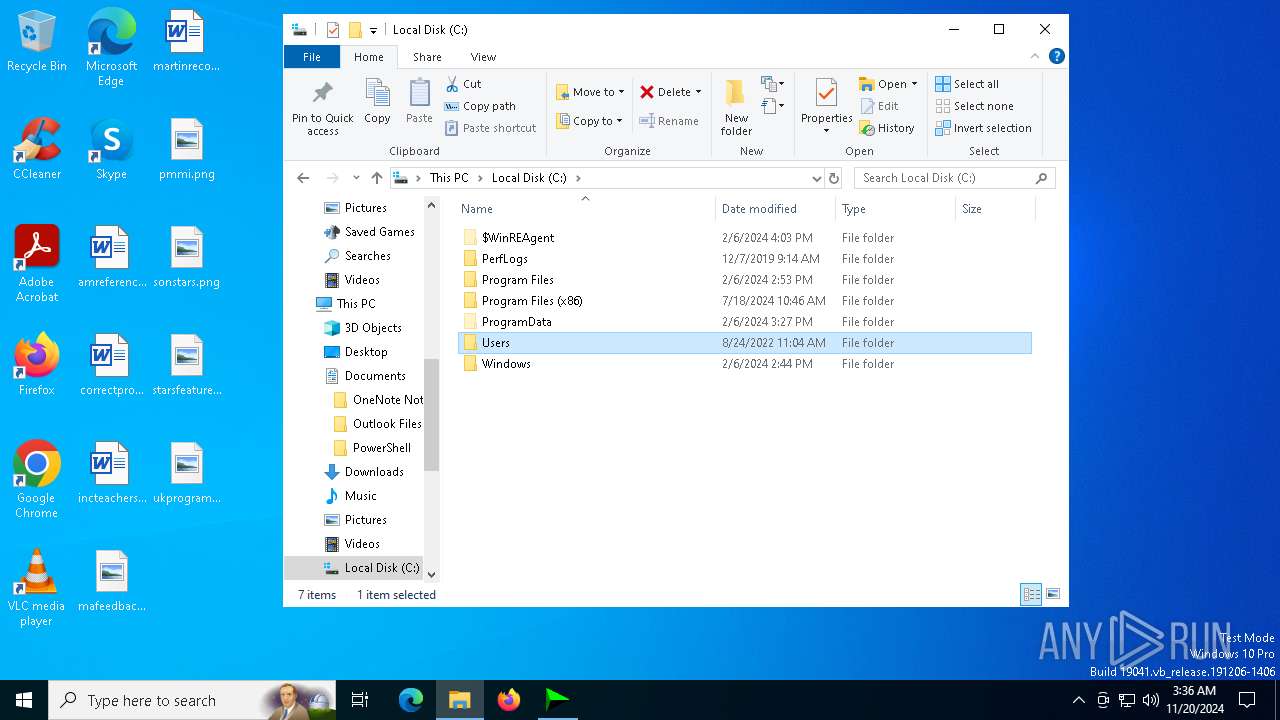
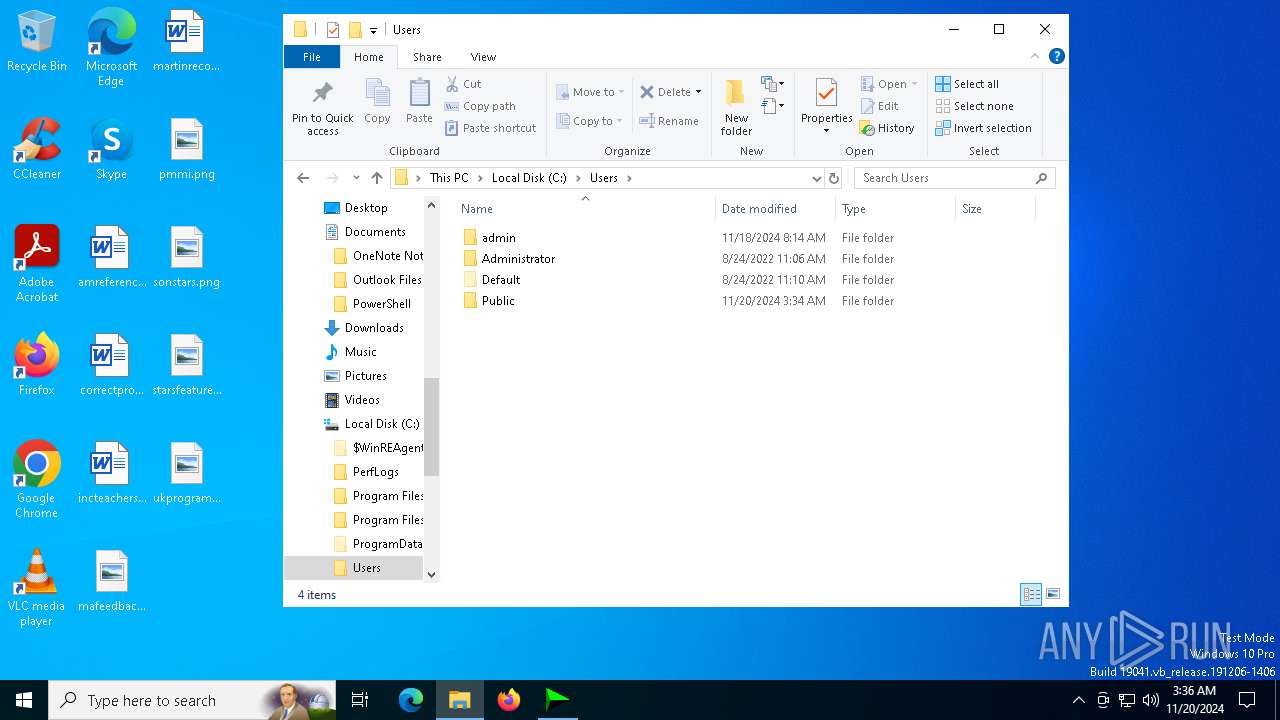
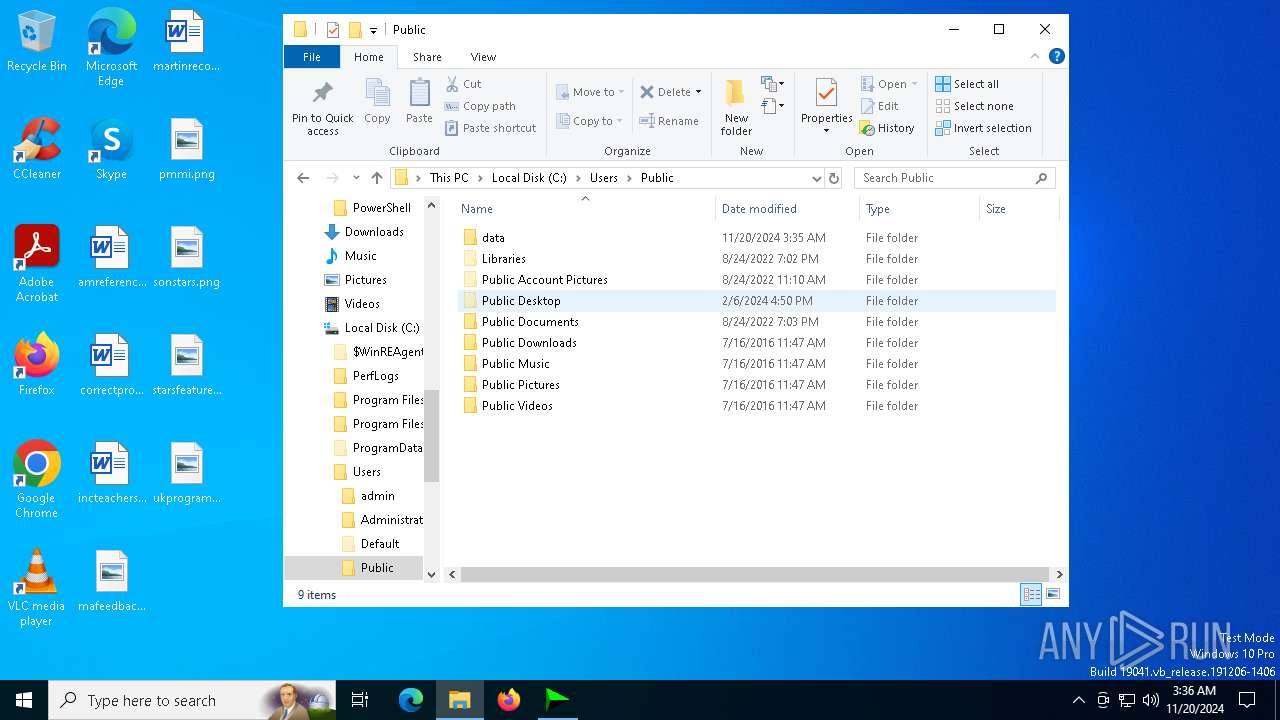
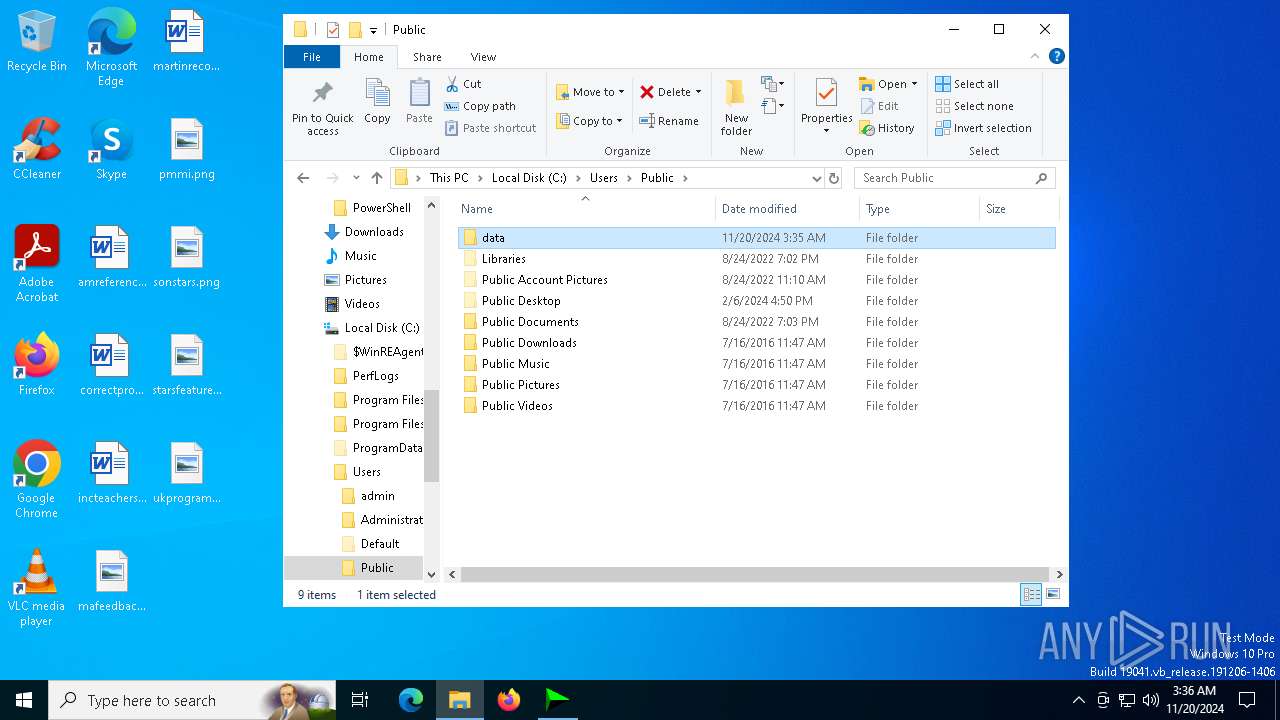
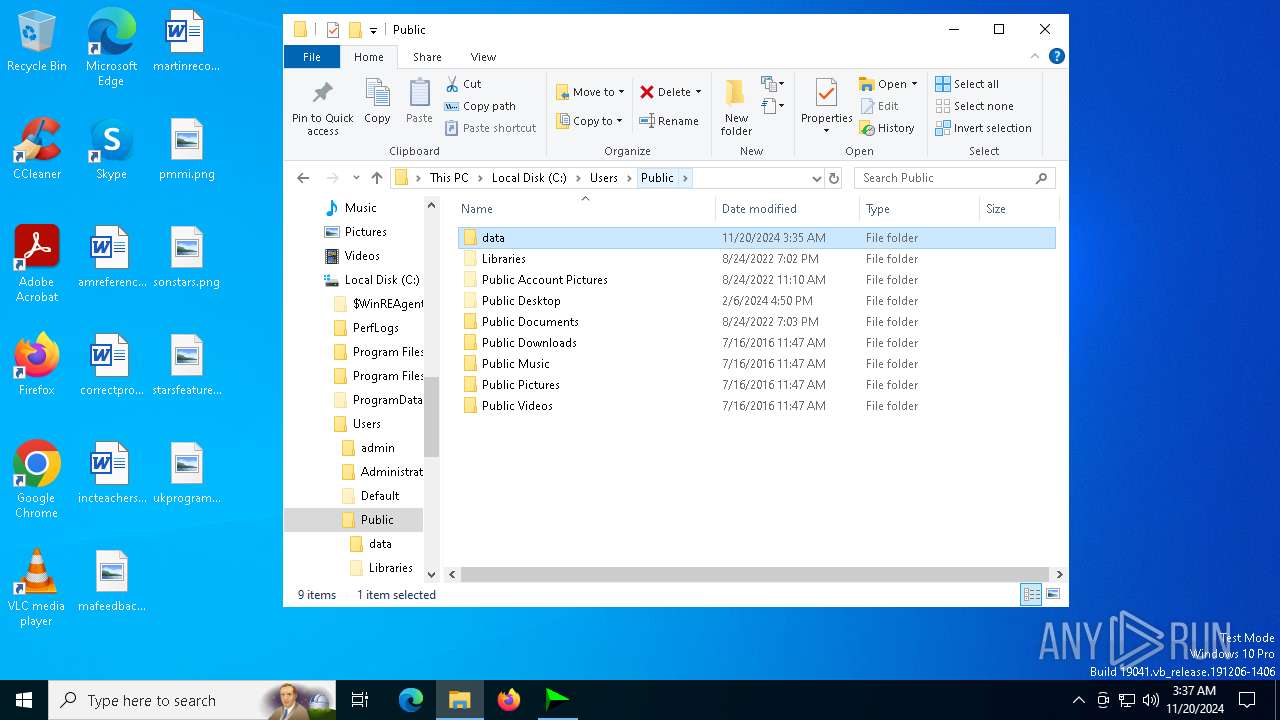
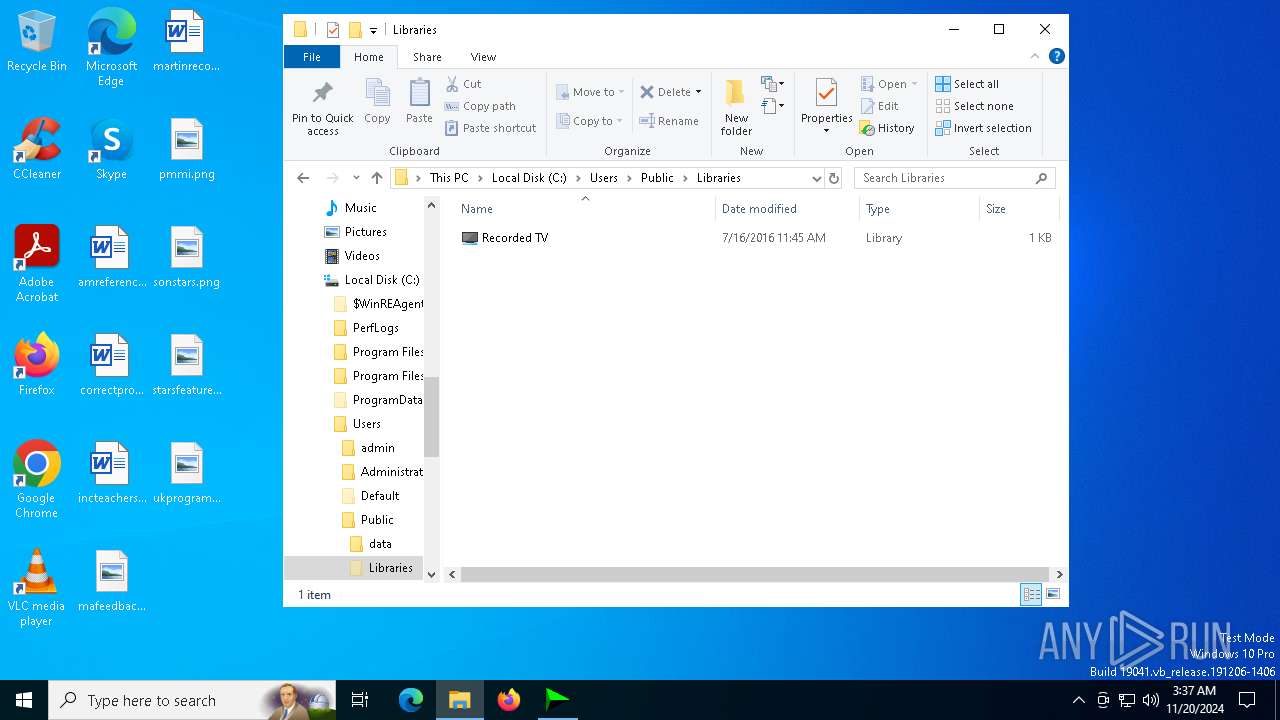
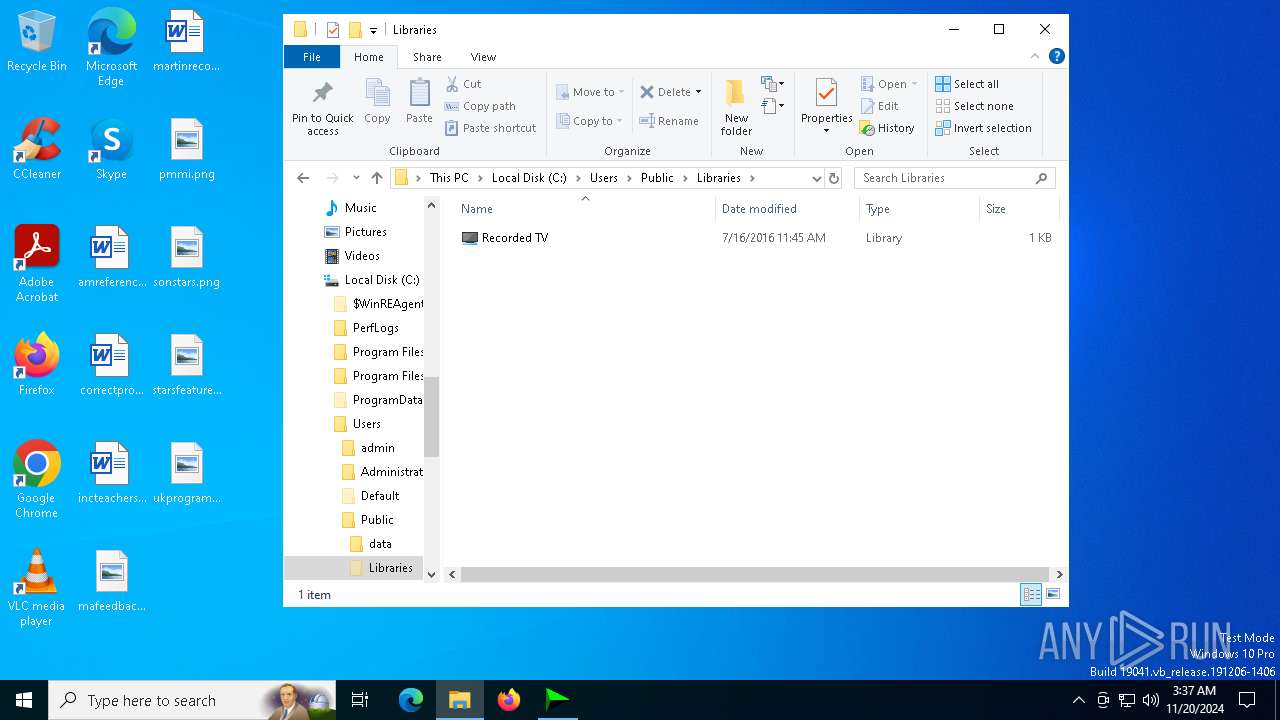
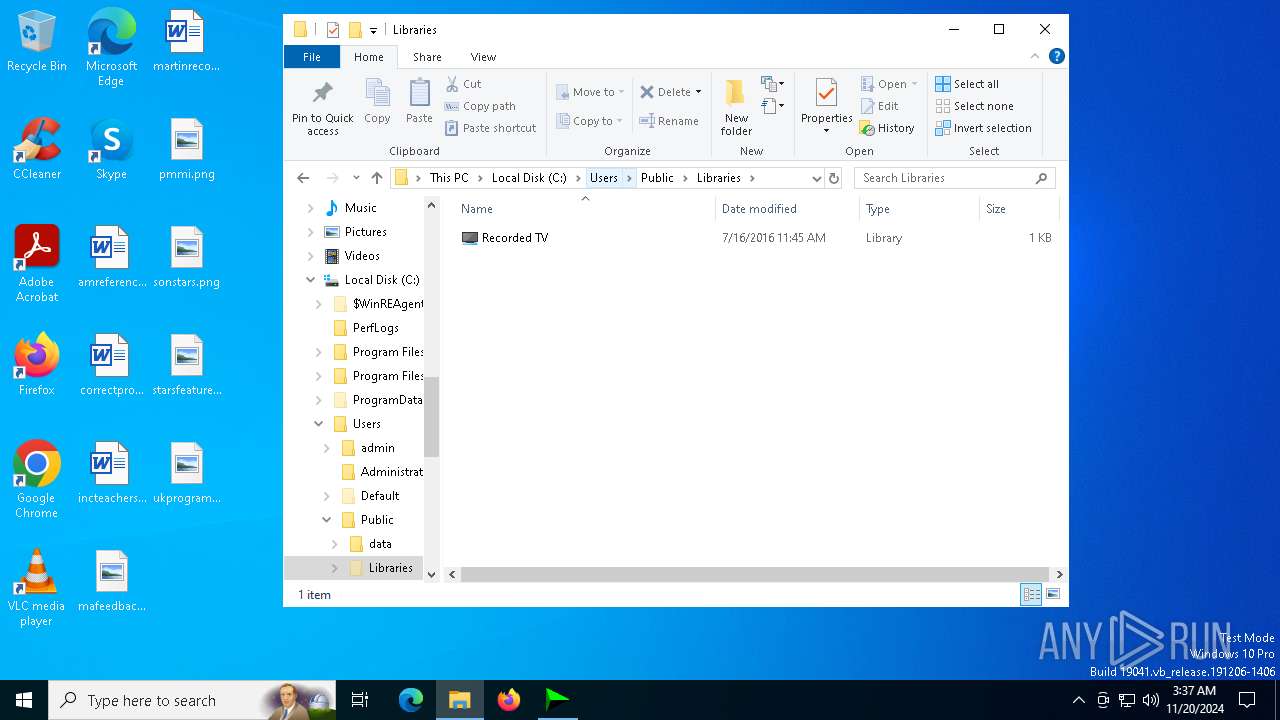
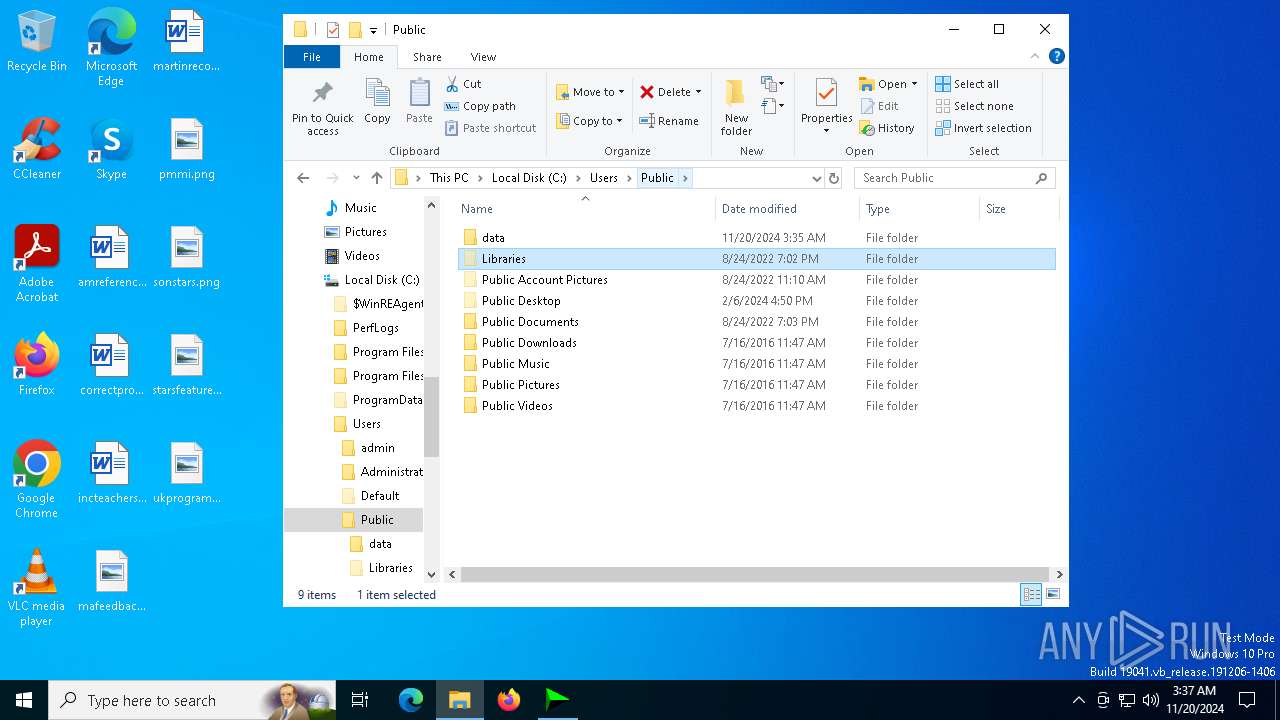
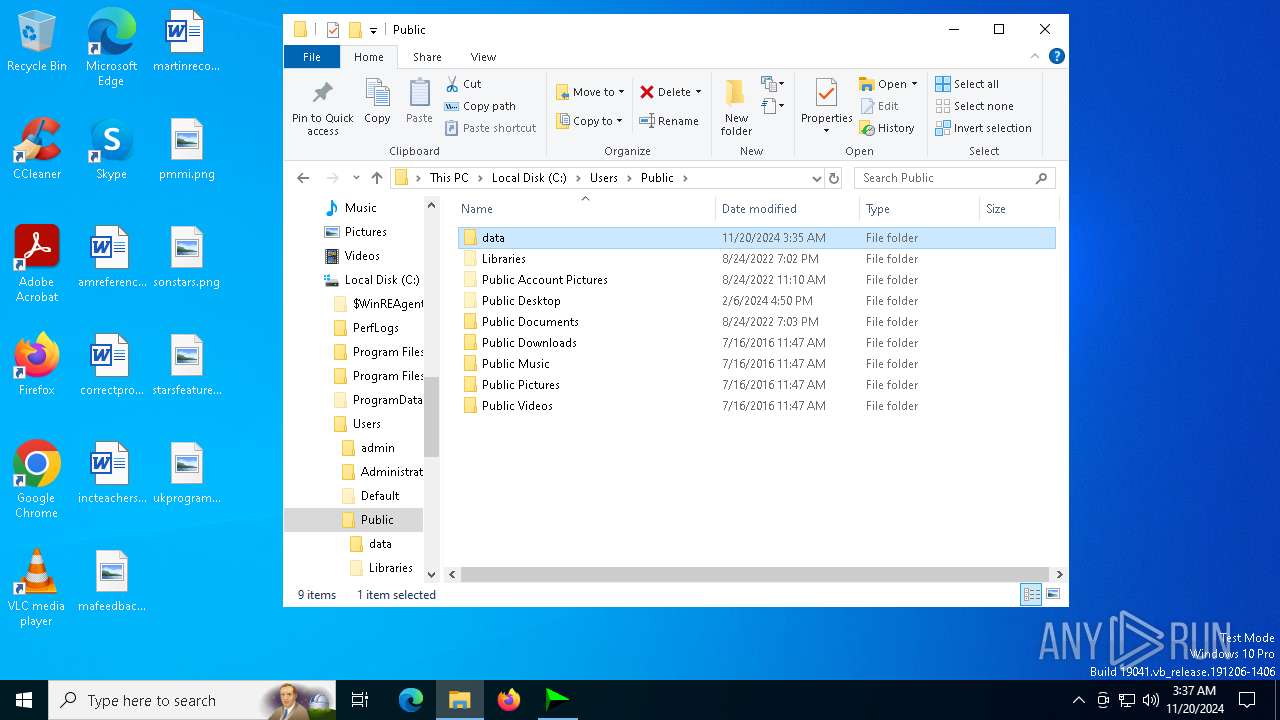
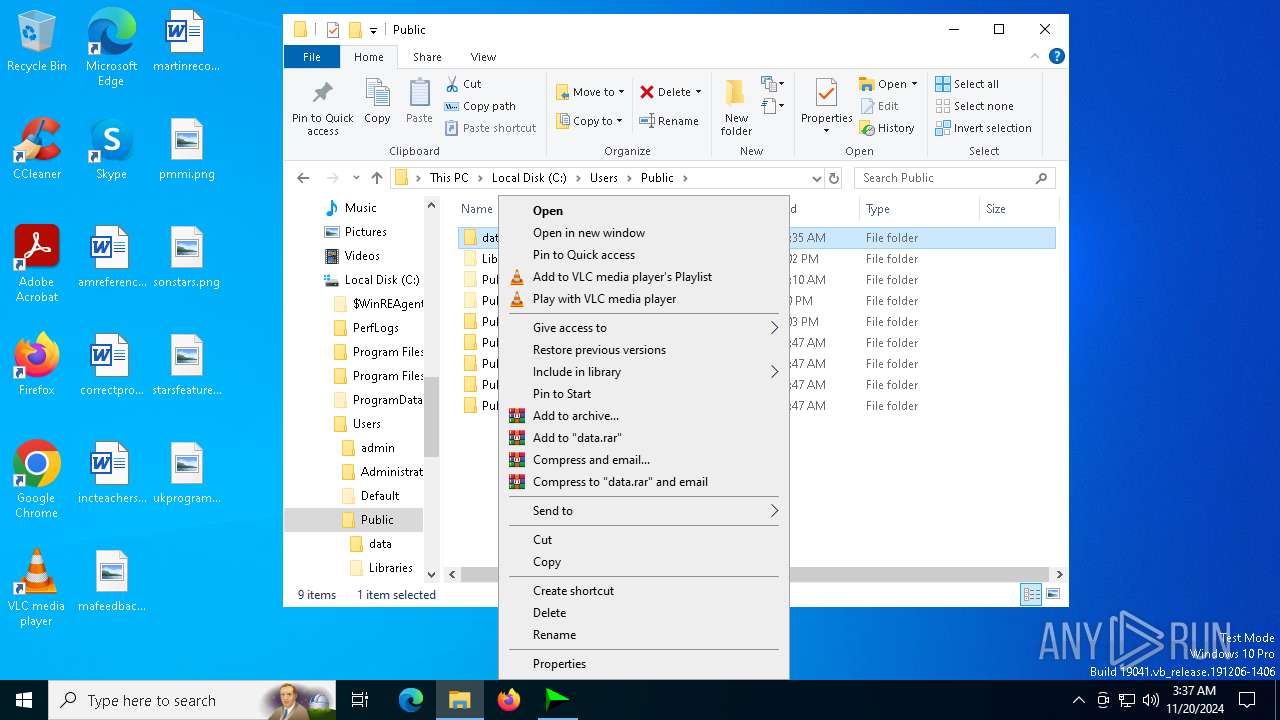
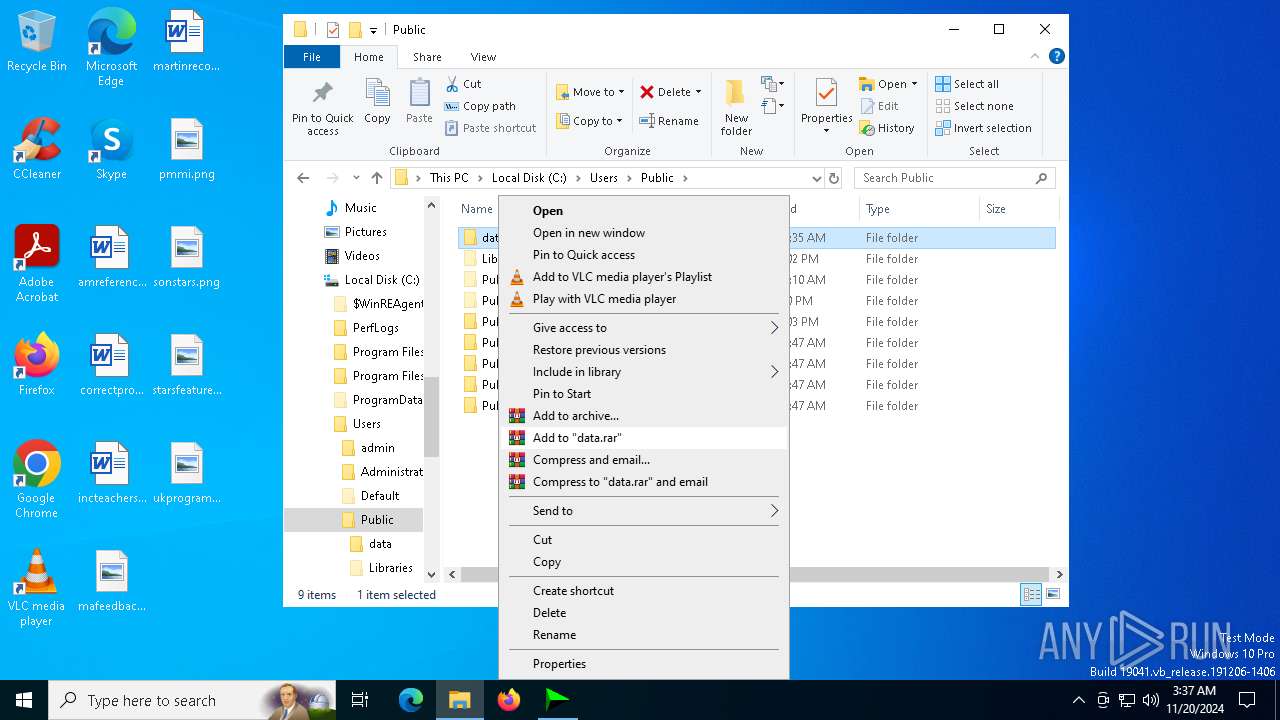
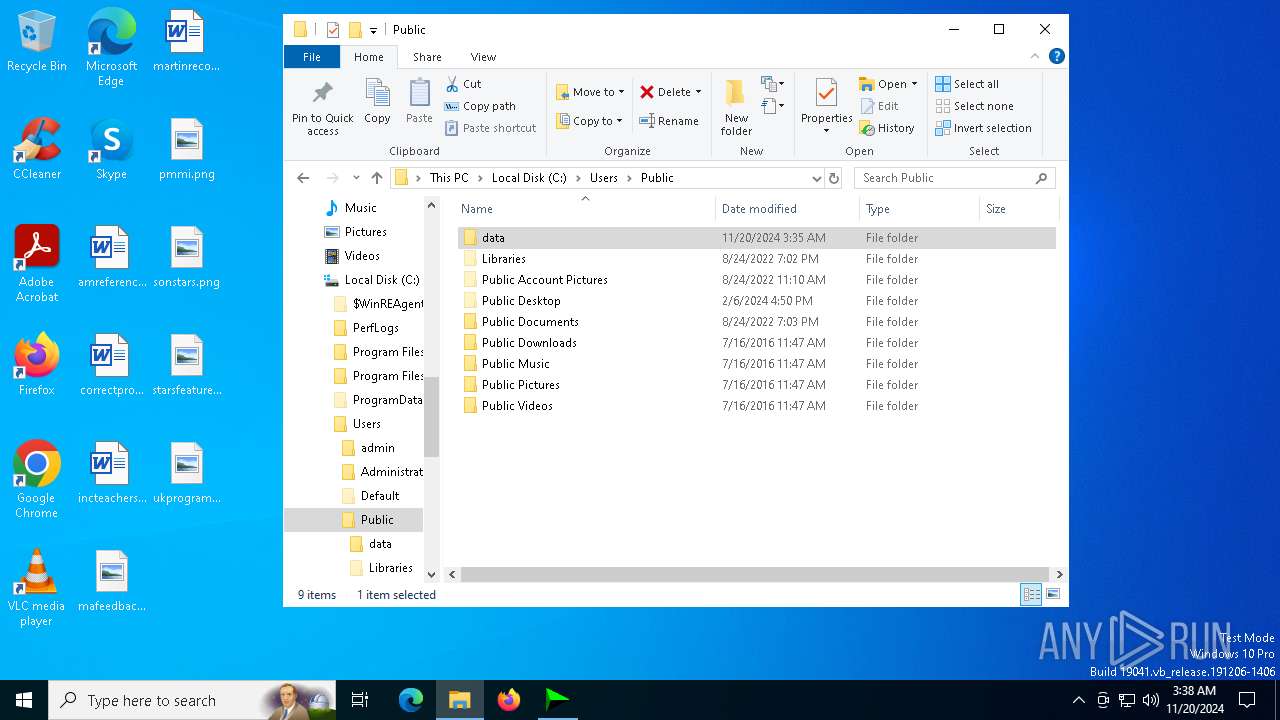
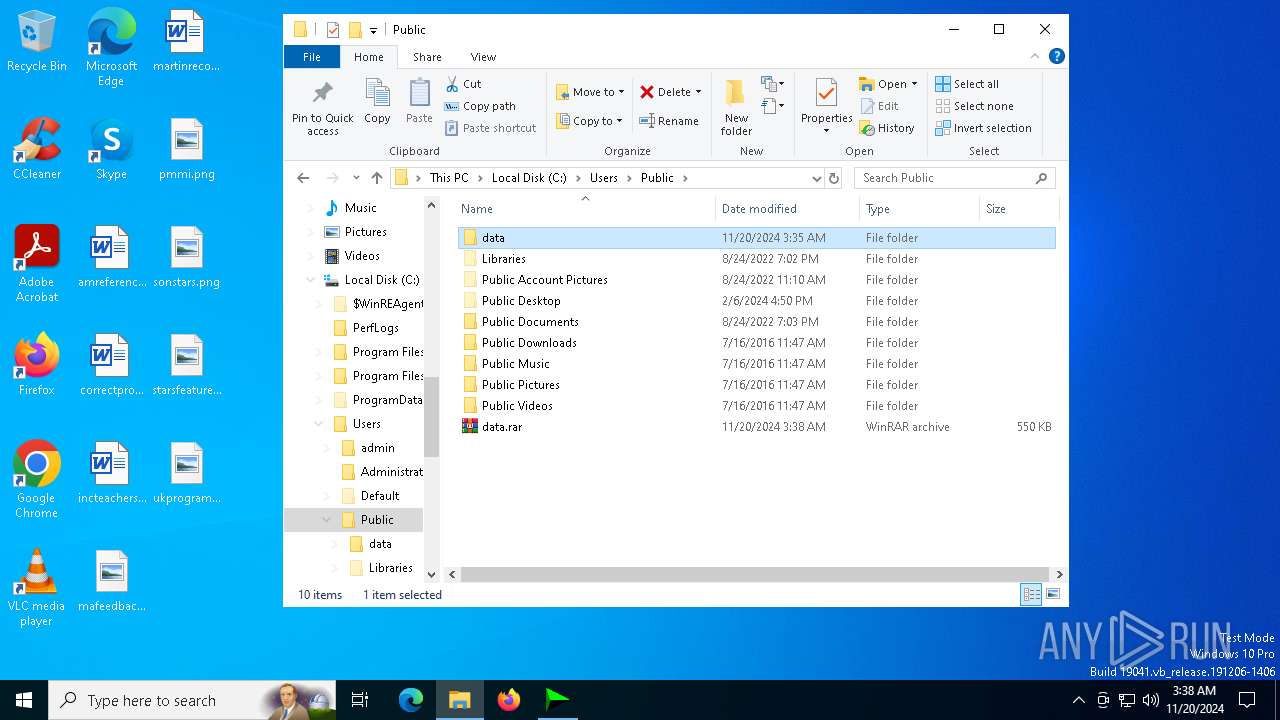
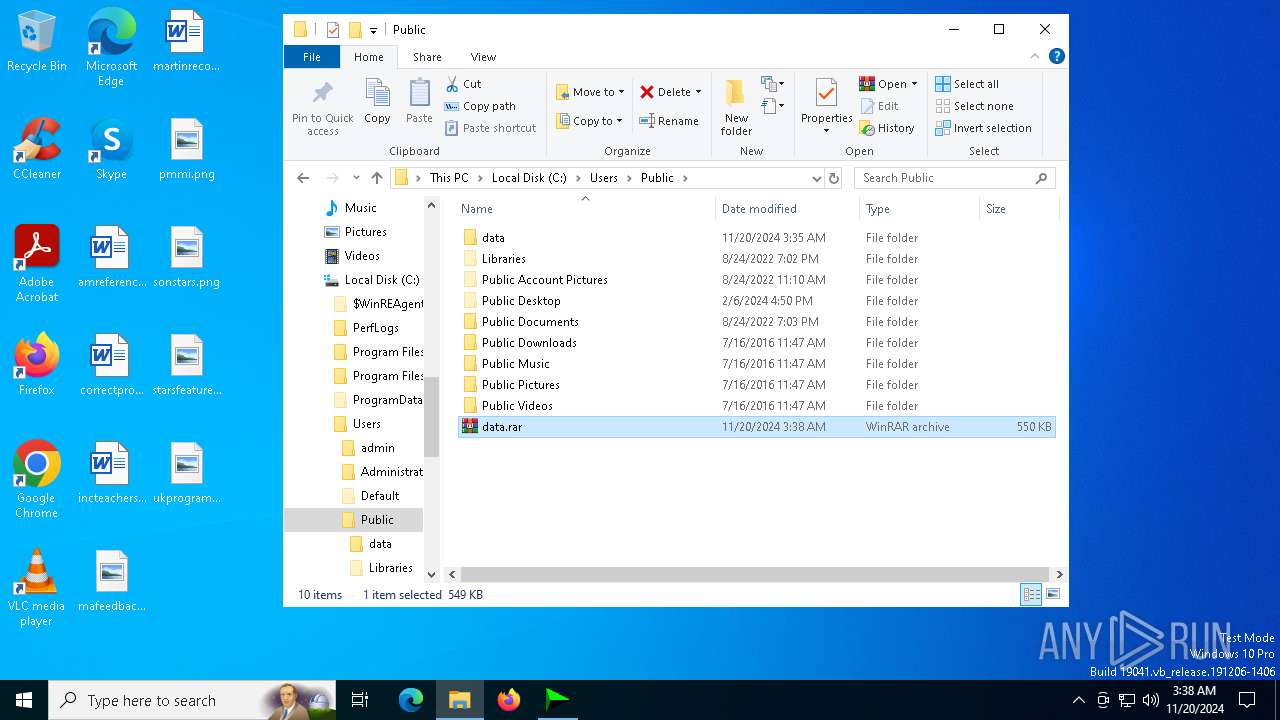
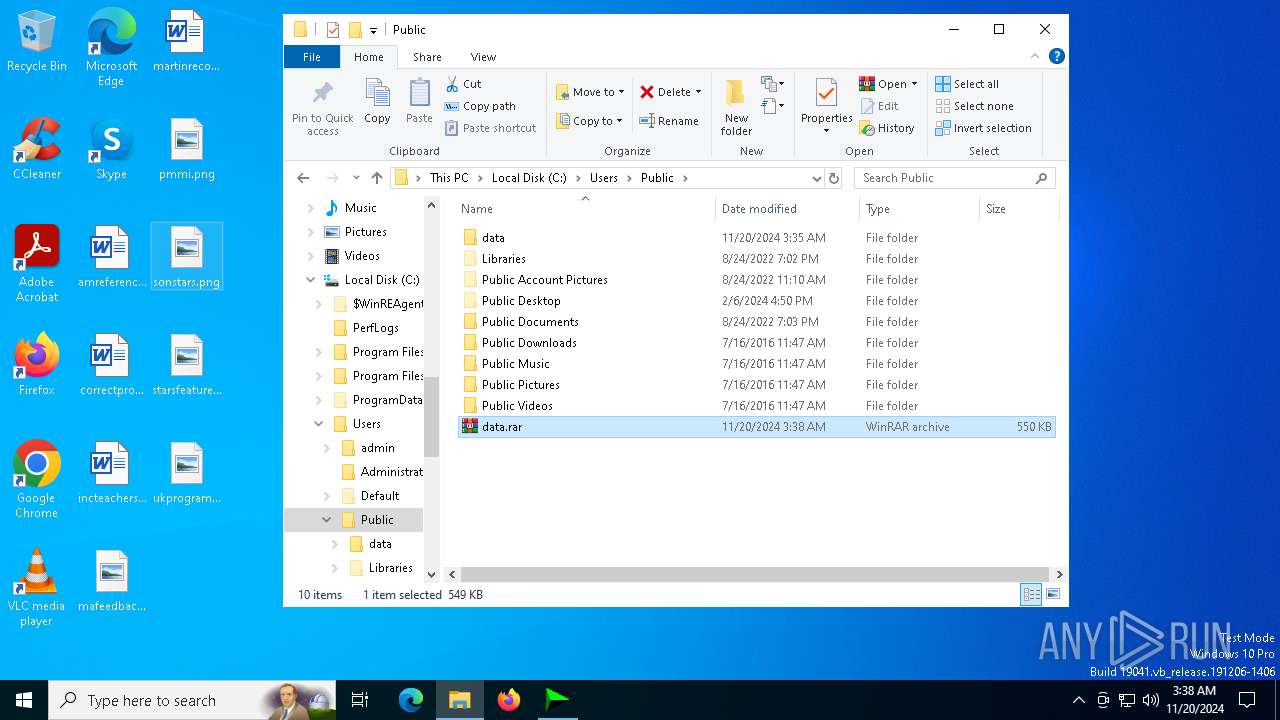
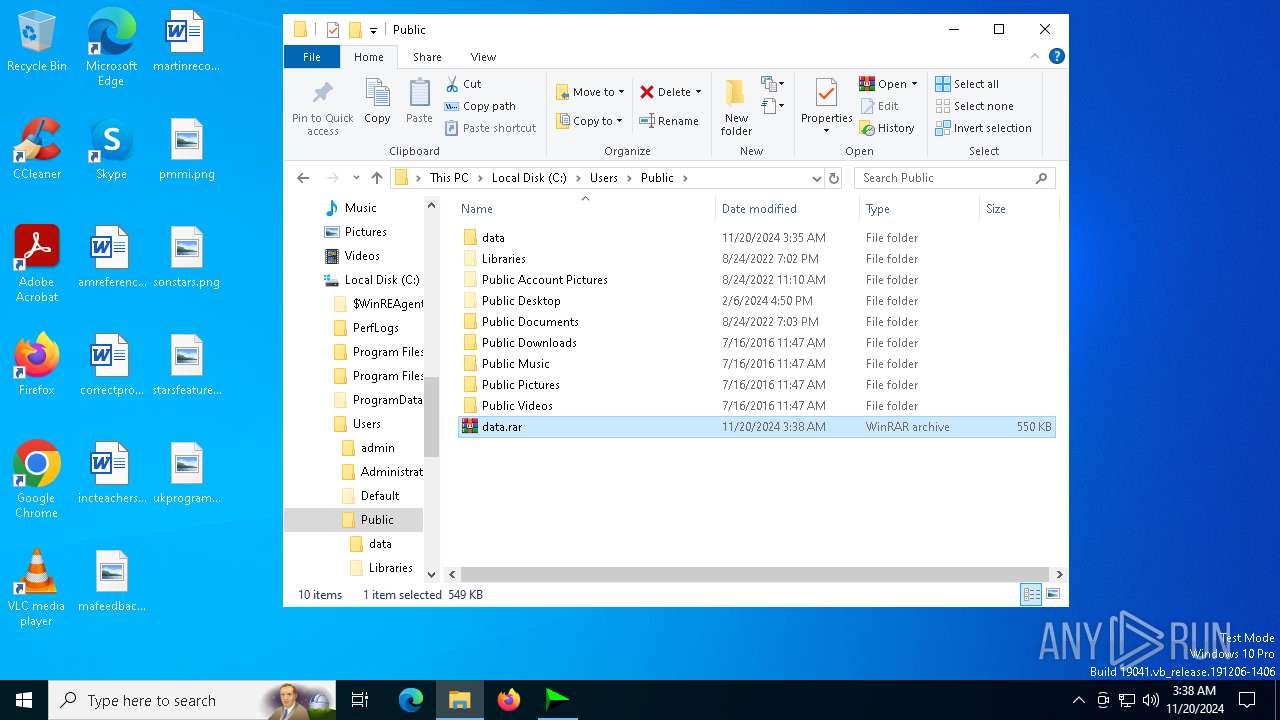
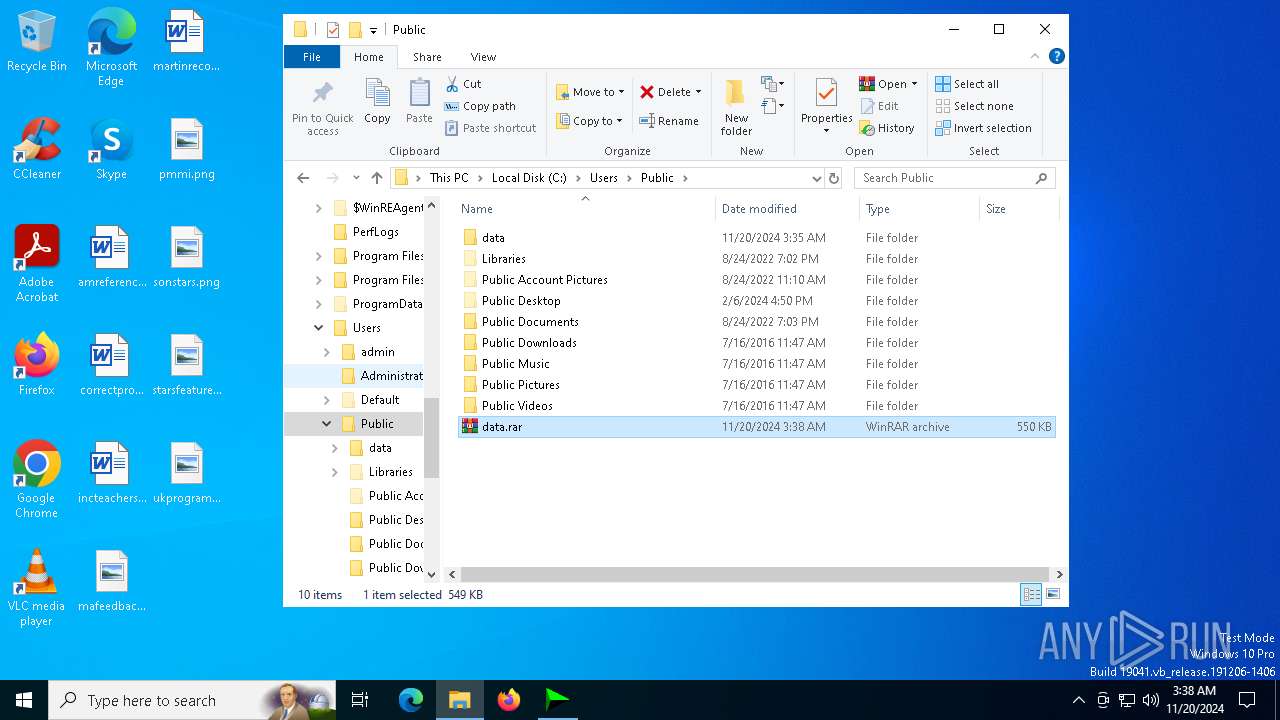
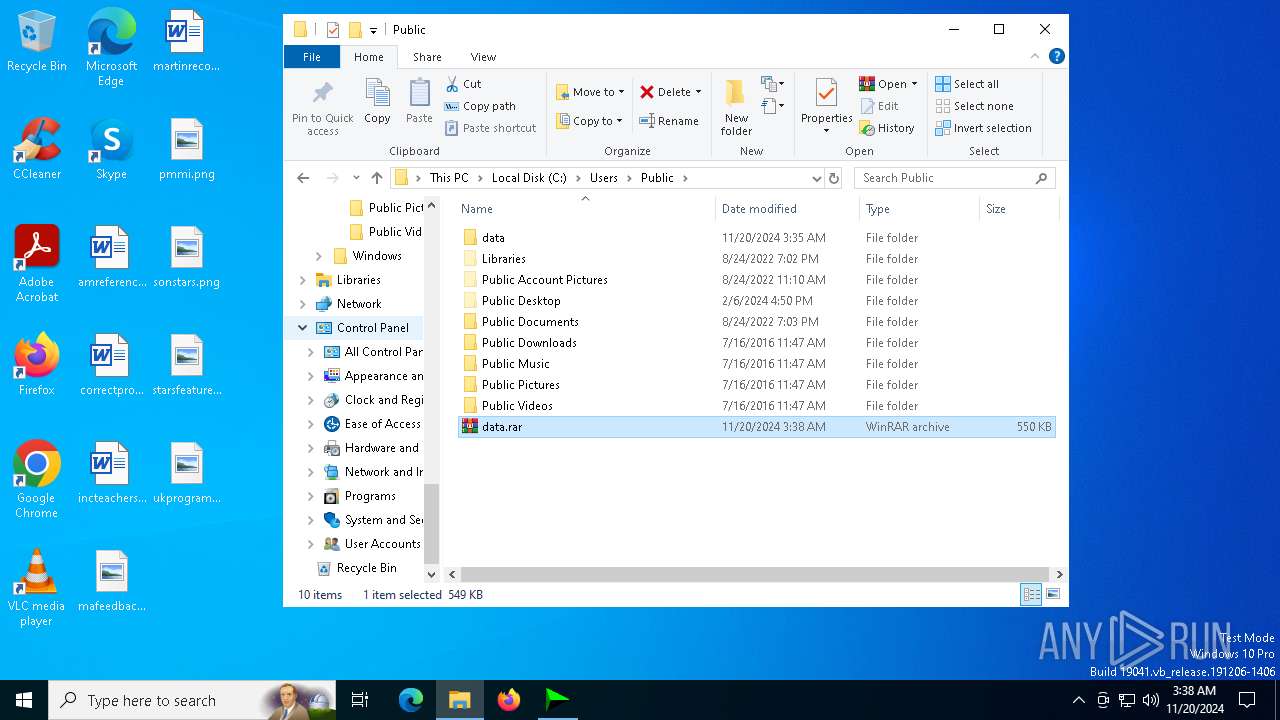
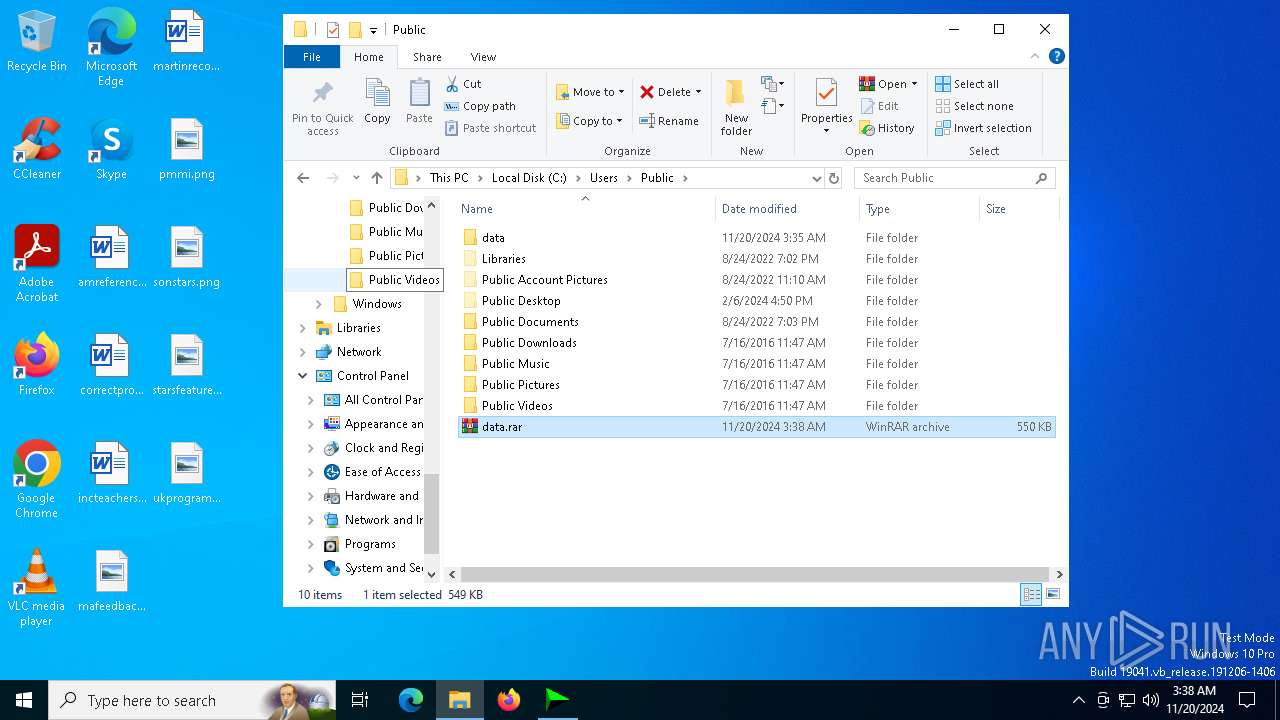
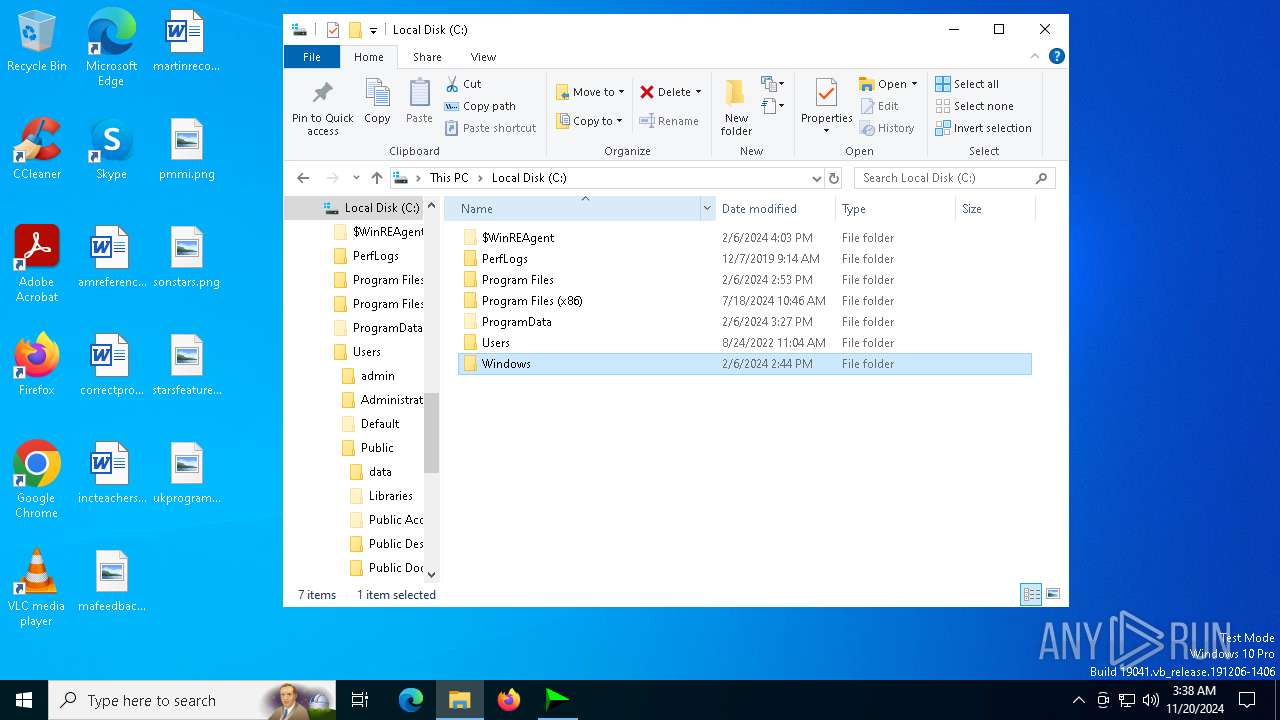
Likely accesses (executes) a file from the Public directory
- cmd.exe (PID: 2828)
- sc.exe (PID: 712)
- mdwslp.exe (PID: 6116)
- cmd.exe (PID: 2076)
- sc.exe (PID: 5592)
- uptimecrx.exe (PID: 2000)
- cmd.exe (PID: 6456)
- cmd.exe (PID: 6236)
- signtool.exe (PID: 4516)
- cmd.exe (PID: 6392)
- sc.exe (PID: 6352)
- signtool.exe (PID: 6472)
- mdwslp.exe (PID: 6636)
- signtool.exe (PID: 7136)
- cmd.exe (PID: 6212)
- sc.exe (PID: 5288)
- cmd.exe (PID: 4280)
- mdwslp.exe (PID: 4968)
- cmd.exe (PID: 4196)
- uptimecrx.exe (PID: 2332)
- cmd.exe (PID: 4536)
- sc.exe (PID: 4208)
- signtool.exe (PID: 6392)
- WinRAR.exe (PID: 6656)
Starts CMD.EXE for commands execution
- IDM_6.4x_Crack.exe (PID: 2396)
- 6gl7oc.exe (PID: 2940)
- mdwslp.exe (PID: 6116)
- uptimecrx.exe (PID: 2332)
Starts SC.EXE for service management
- cmd.exe (PID: 2828)
- cmd.exe (PID: 5496)
- cmd.exe (PID: 2076)
- cmd.exe (PID: 1512)
- cmd.exe (PID: 6392)
- cmd.exe (PID: 6984)
- cmd.exe (PID: 6508)
- cmd.exe (PID: 4280)
- cmd.exe (PID: 6332)
- cmd.exe (PID: 4536)
- cmd.exe (PID: 848)
Executes as Windows Service
- mdwslp.exe (PID: 6116)
- uptimecrx.exe (PID: 2000)
- mdwslp.exe (PID: 6636)
- mdwslp.exe (PID: 4968)
- uptimecrx.exe (PID: 2332)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3428)
- cmd.exe (PID: 7092)
- cmd.exe (PID: 6980)
- cmd.exe (PID: 5664)
INFO
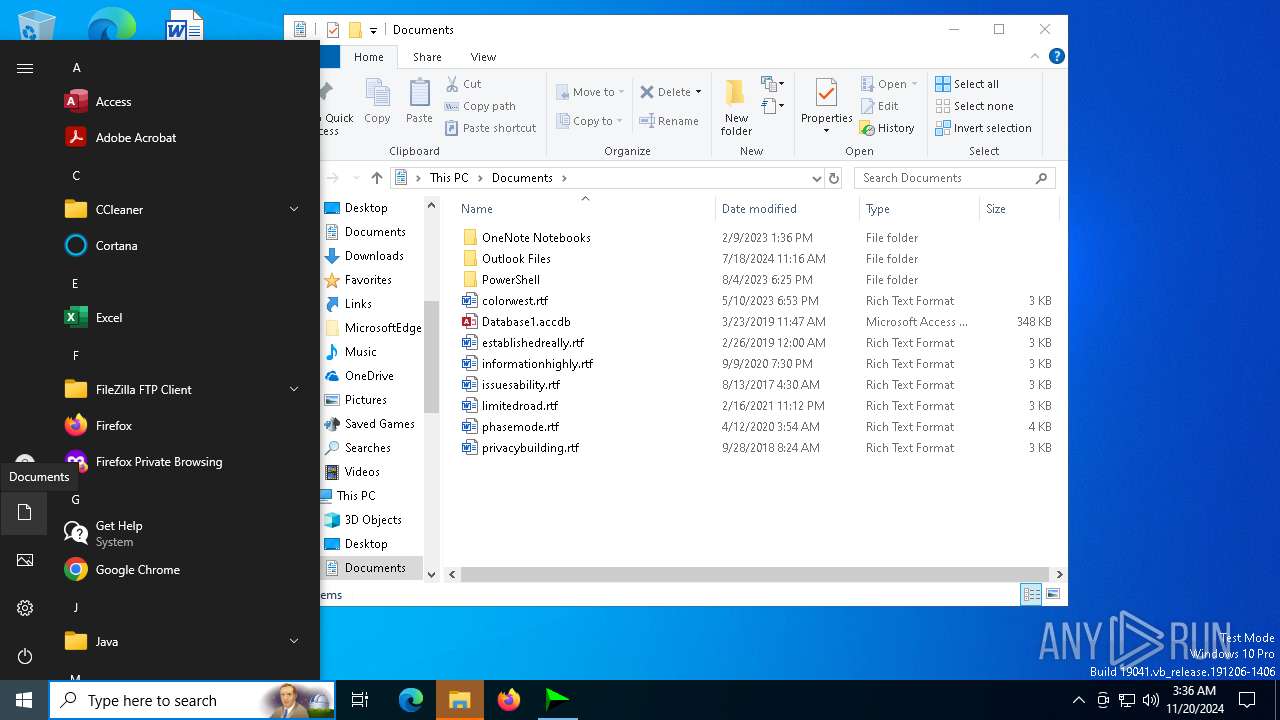
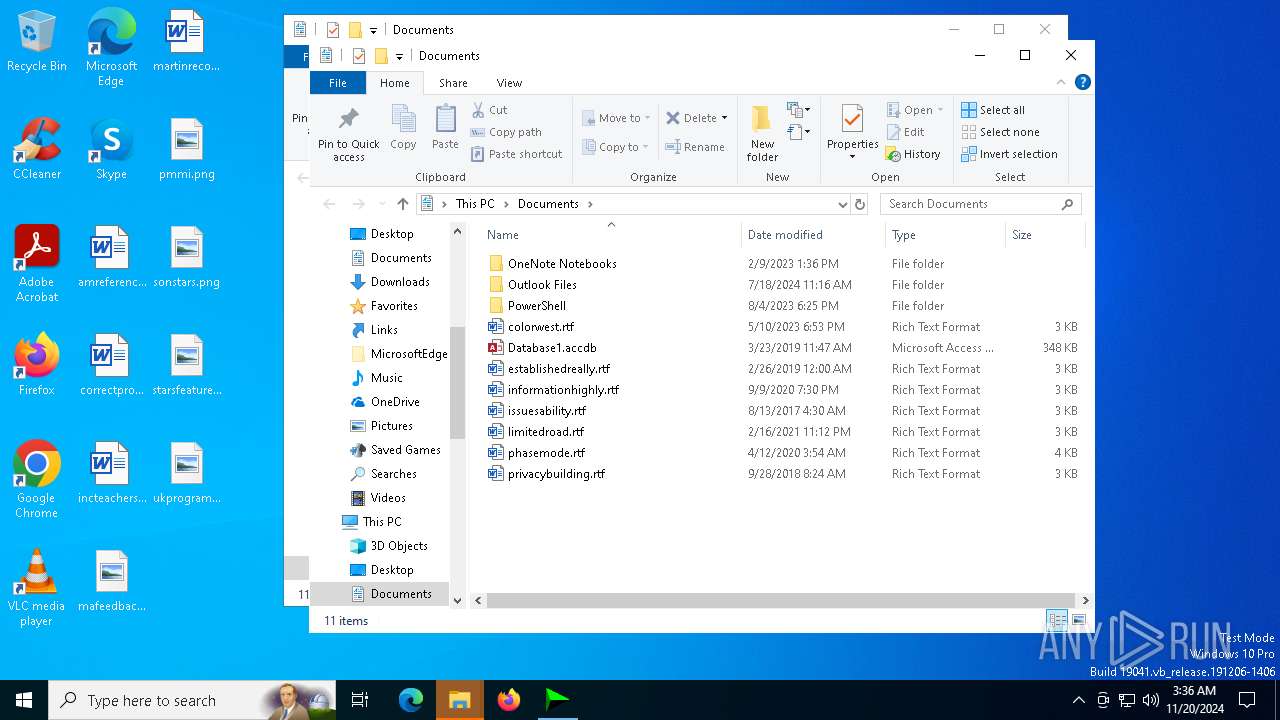
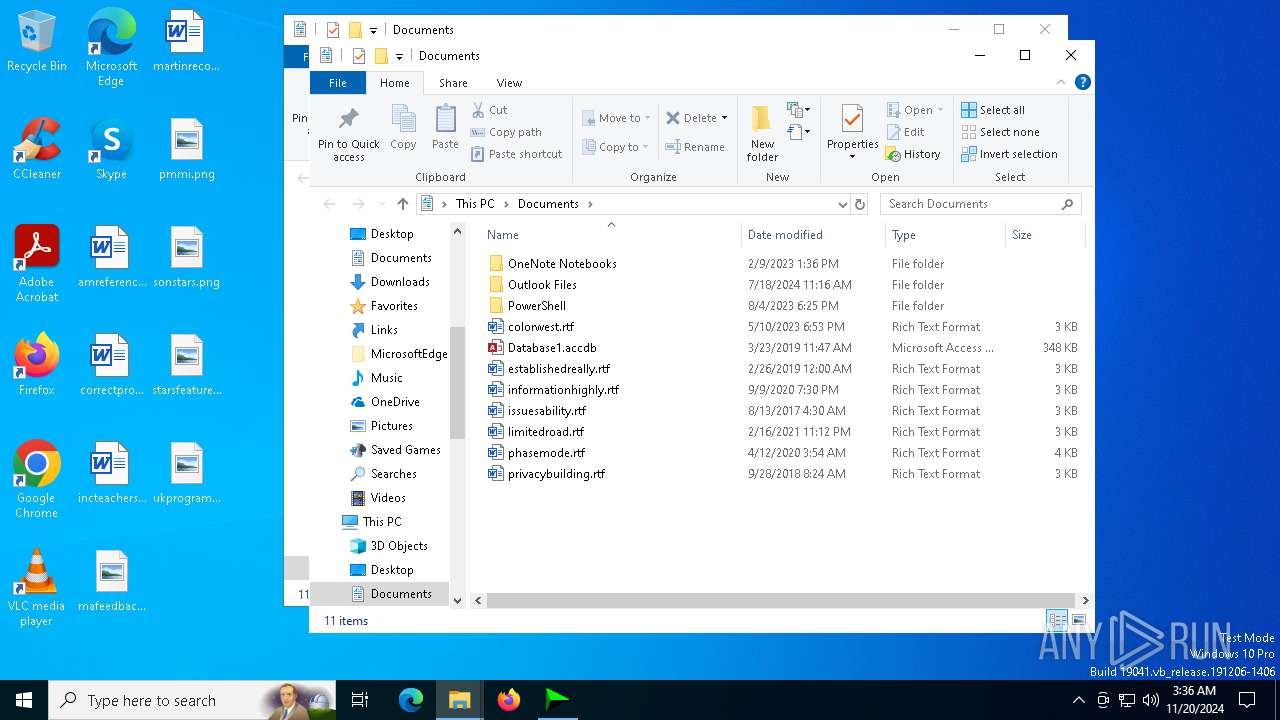
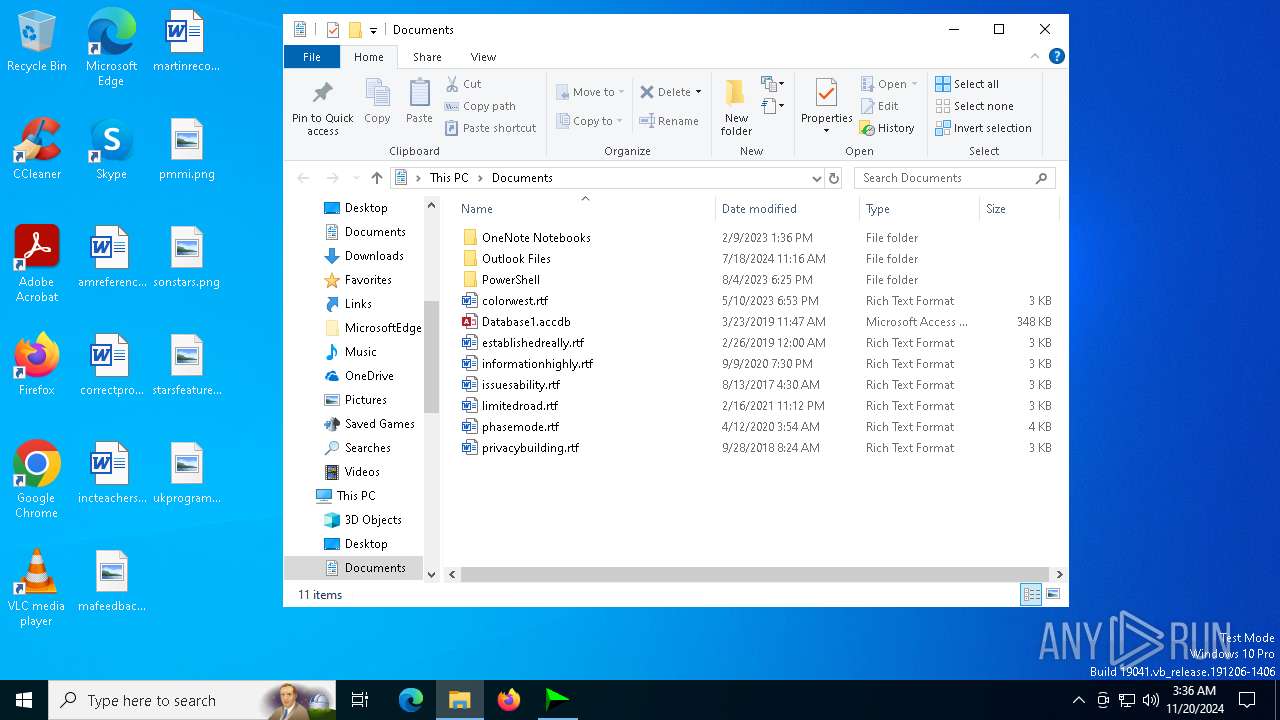
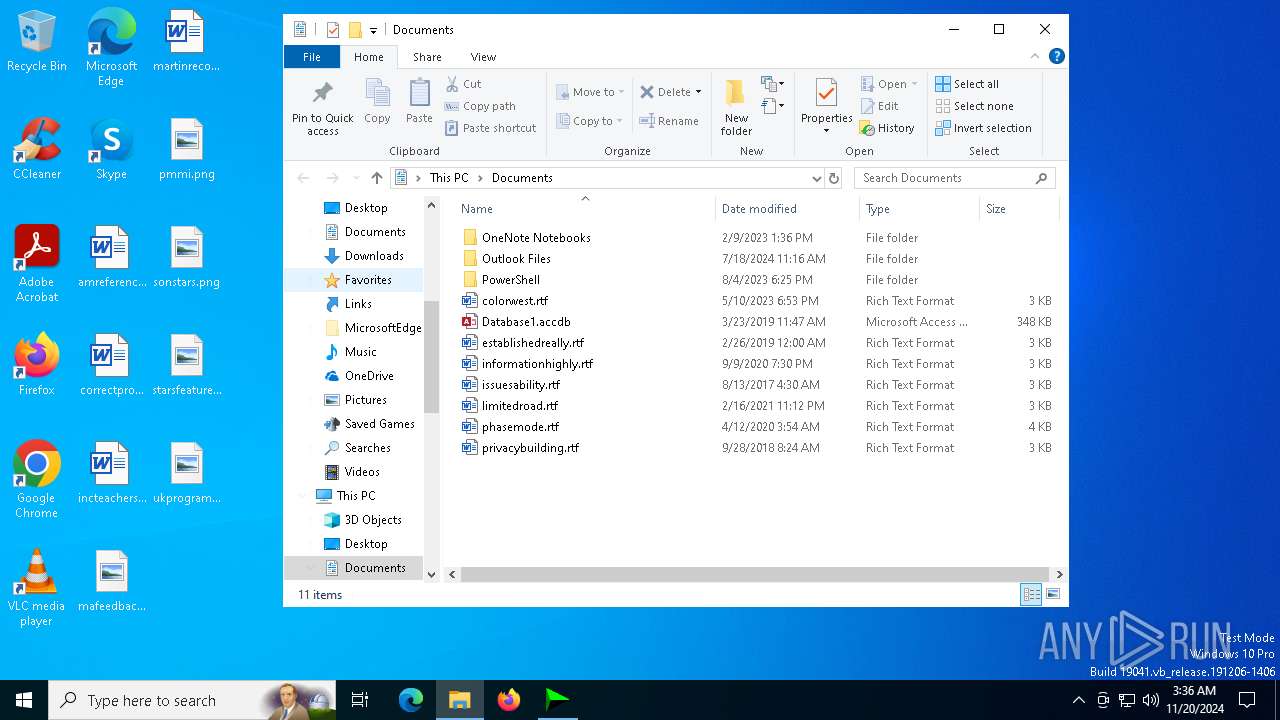
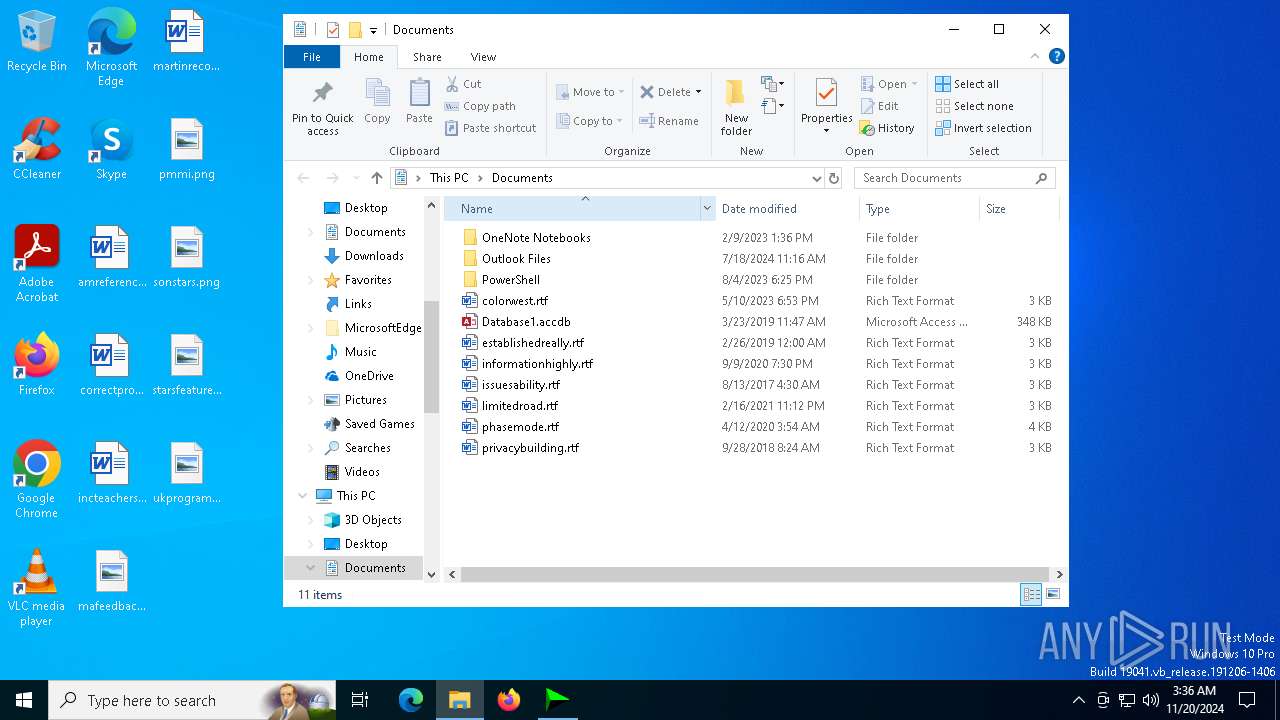
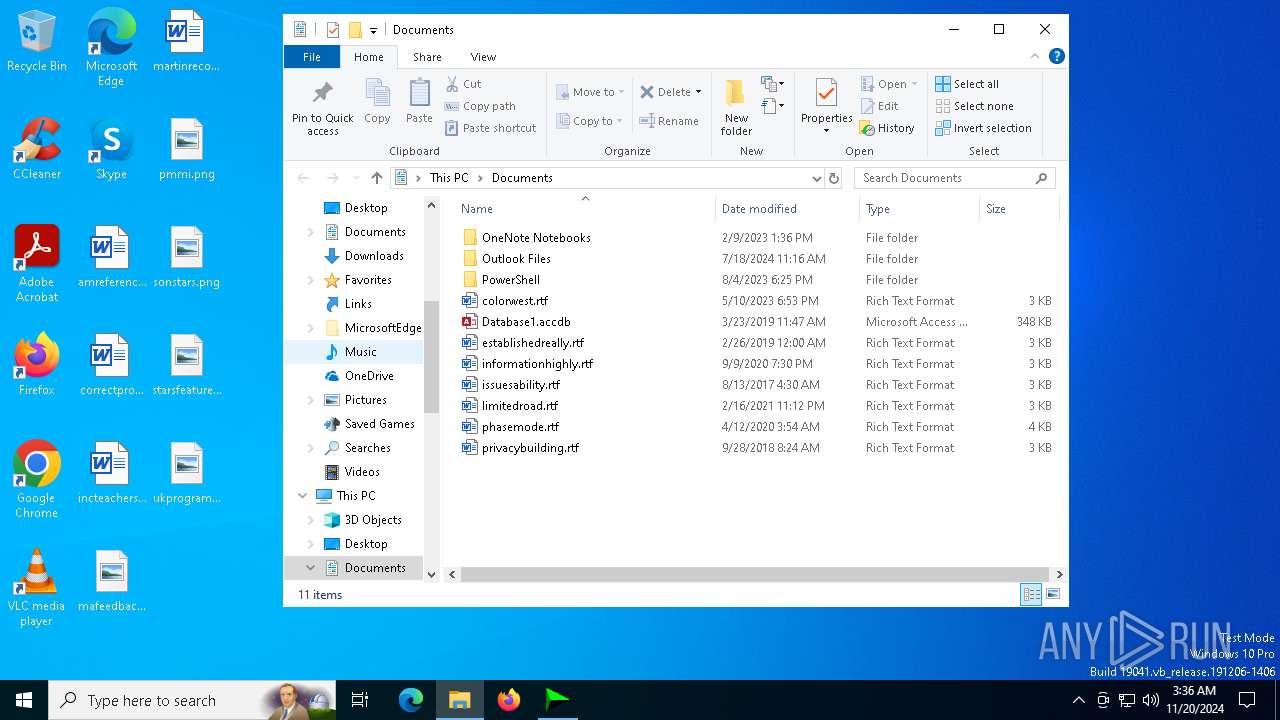
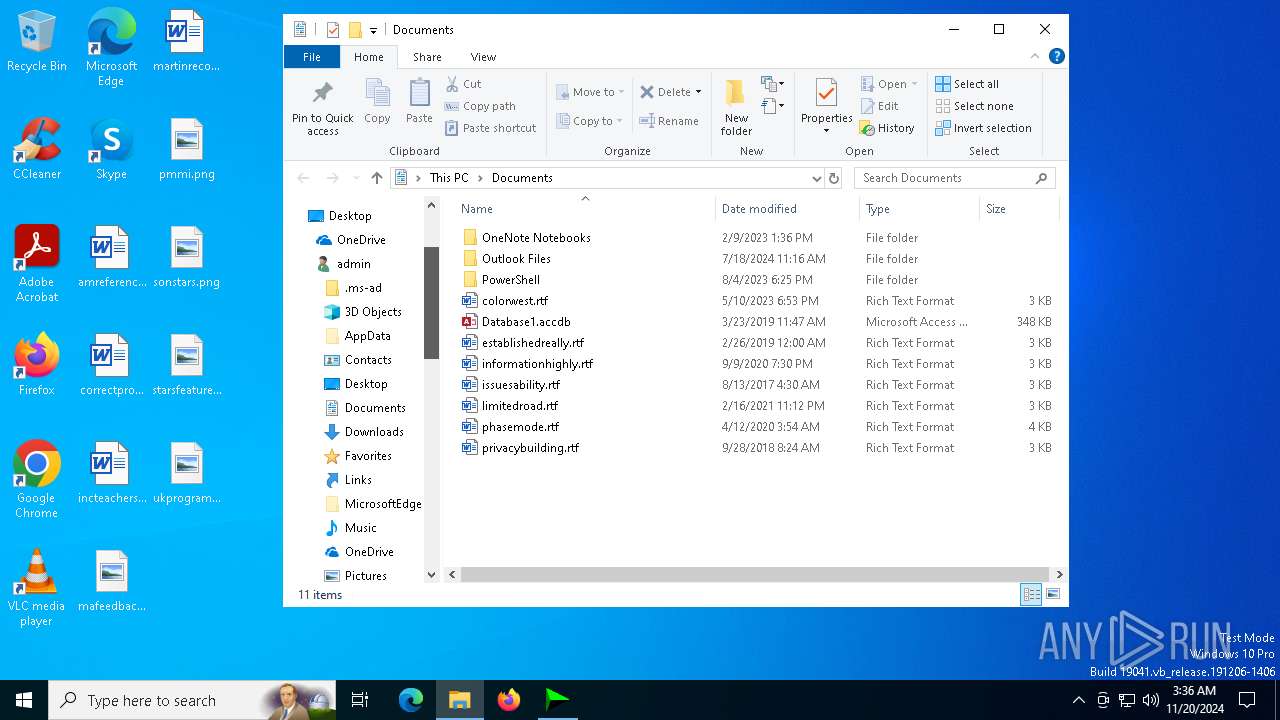
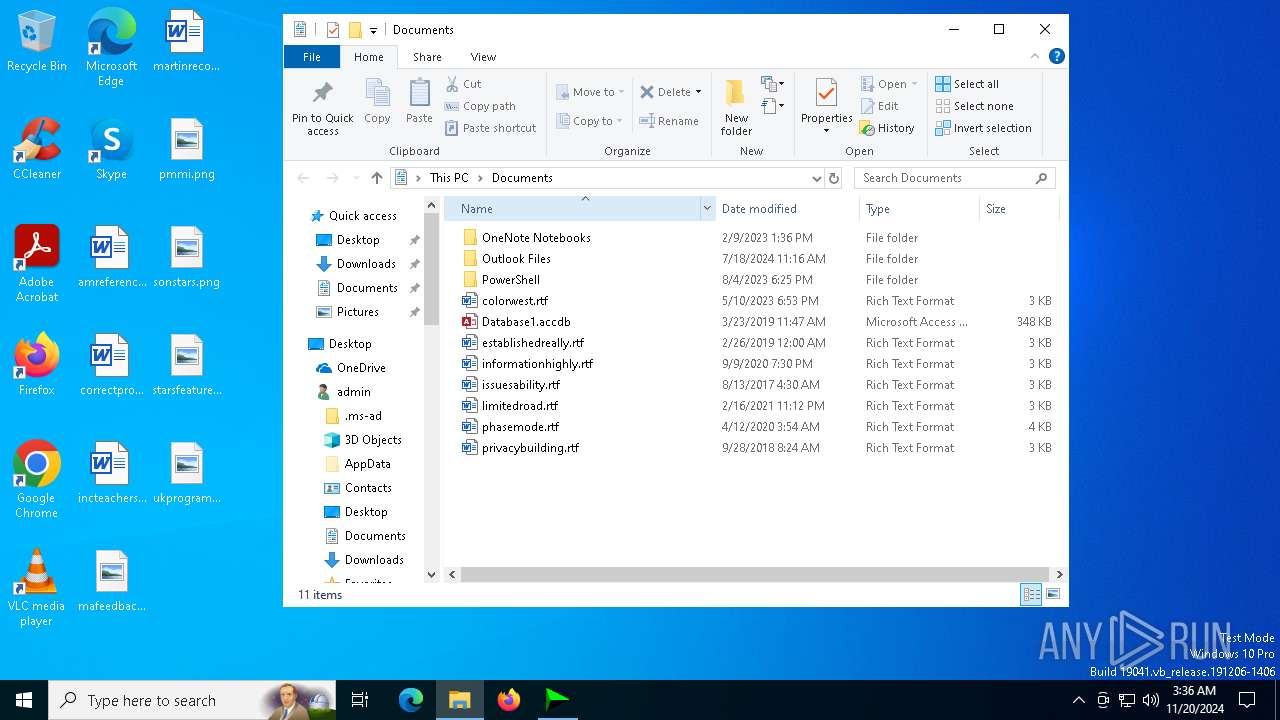
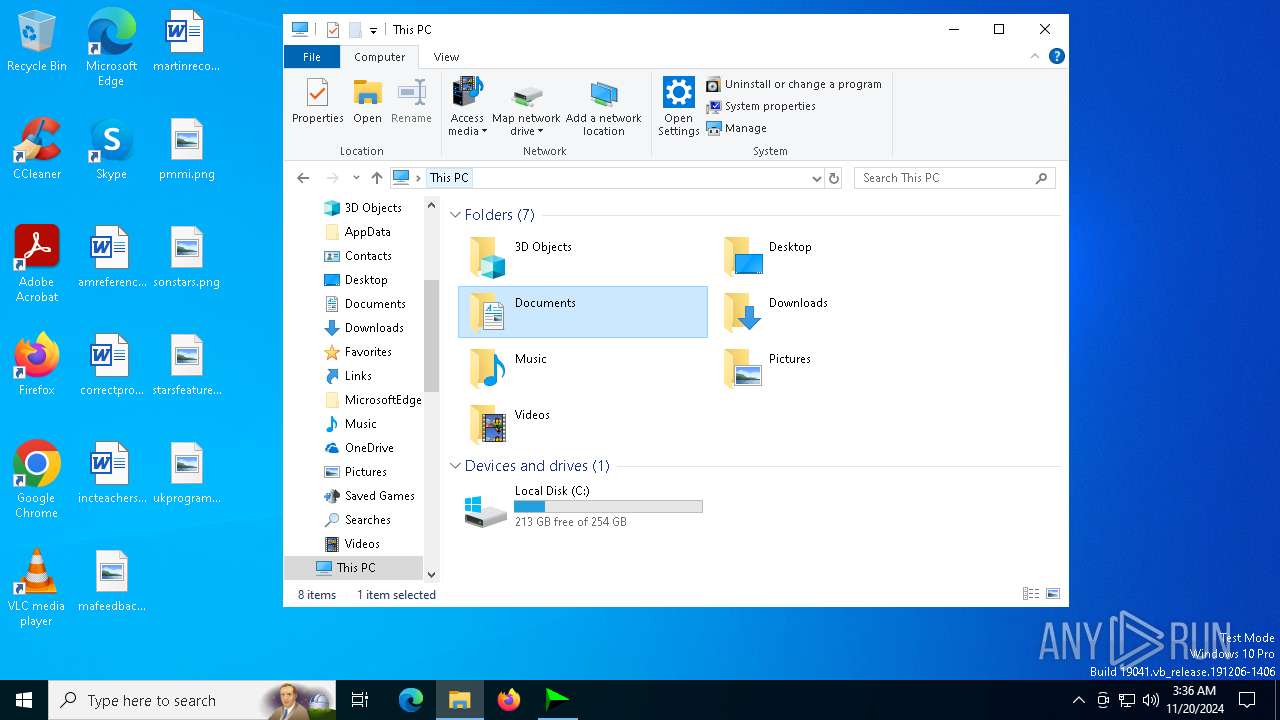
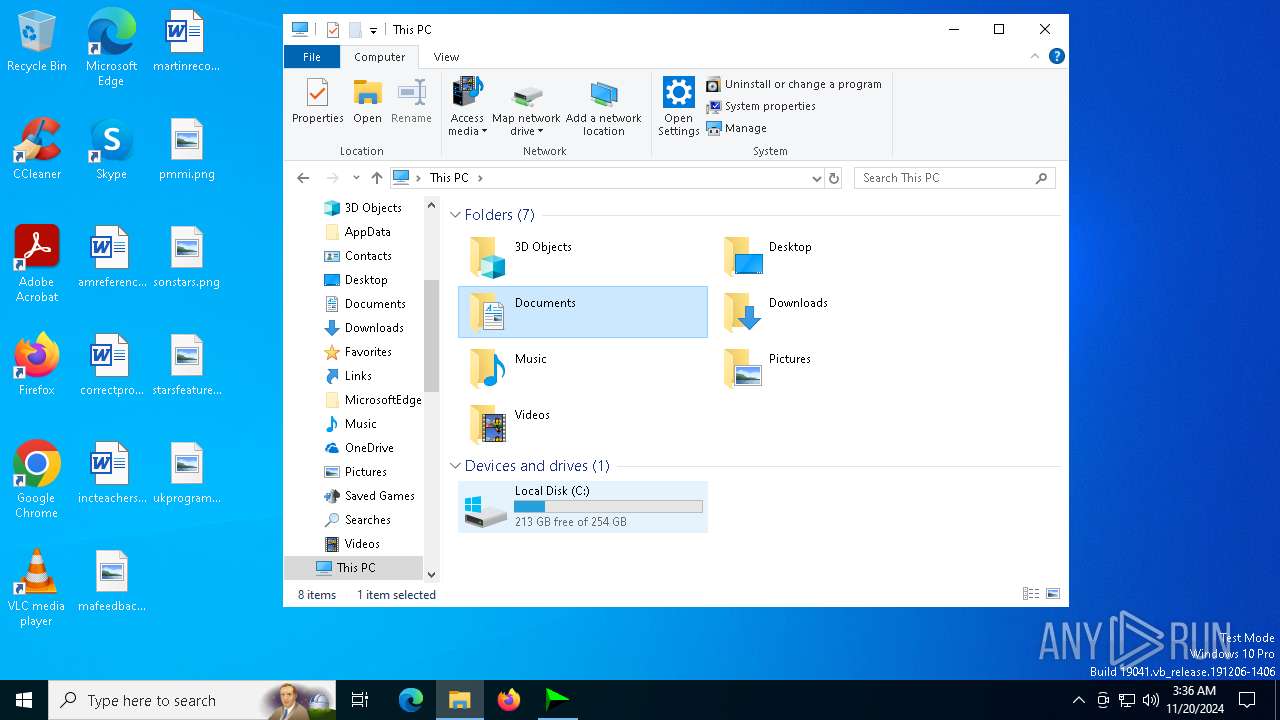
Creates files or folders in the user directory
- IDM_6.4x_Crack_v19.7.exe (PID: 2632)
Reads the software policy settings
- IDM_6.4x_Crack_v19.7.exe (PID: 2632)
- IDM_6.4x_Crack.exe (PID: 2396)
- signtool.exe (PID: 6472)
Checks proxy server information
- IDM_6.4x_Crack_v19.7.exe (PID: 2632)
- IDM_6.4x_Crack.exe (PID: 2396)
Reads the machine GUID from the registry
- IDM_6.4x_Crack_v19.7.exe (PID: 2632)
- IDM_6.4x_Crack.exe (PID: 2396)
- signtool.exe (PID: 6472)
Reads the computer name
- IDM_6.4x_Crack_v19.7.exe (PID: 2632)
- IDM_6.4x_Crack.exe (PID: 2396)
- mdwslp.exe (PID: 6116)
- uptimecrx.exe (PID: 2000)
- IDM_6.4x_Crack_v19.7.exe (PID: 6268)
- signtool.exe (PID: 6472)
Checks supported languages
- IDM_6.4x_Crack_v19.7.exe (PID: 2632)
- IDM_6.4x_Crack.exe (PID: 2396)
- mdwslp.exe (PID: 6116)
- uptimecrx.exe (PID: 2000)
- IDM_6.4x_Crack_v19.7.exe (PID: 6268)
- 6gl7oc.exe (PID: 2940)
- J4KPYO.exe (PID: 6612)
- signtool.exe (PID: 6472)
Process checks computer location settings
- IDM_6.4x_Crack_v19.7.exe (PID: 2632)
- IDM_6.4x_Crack.exe (PID: 2396)
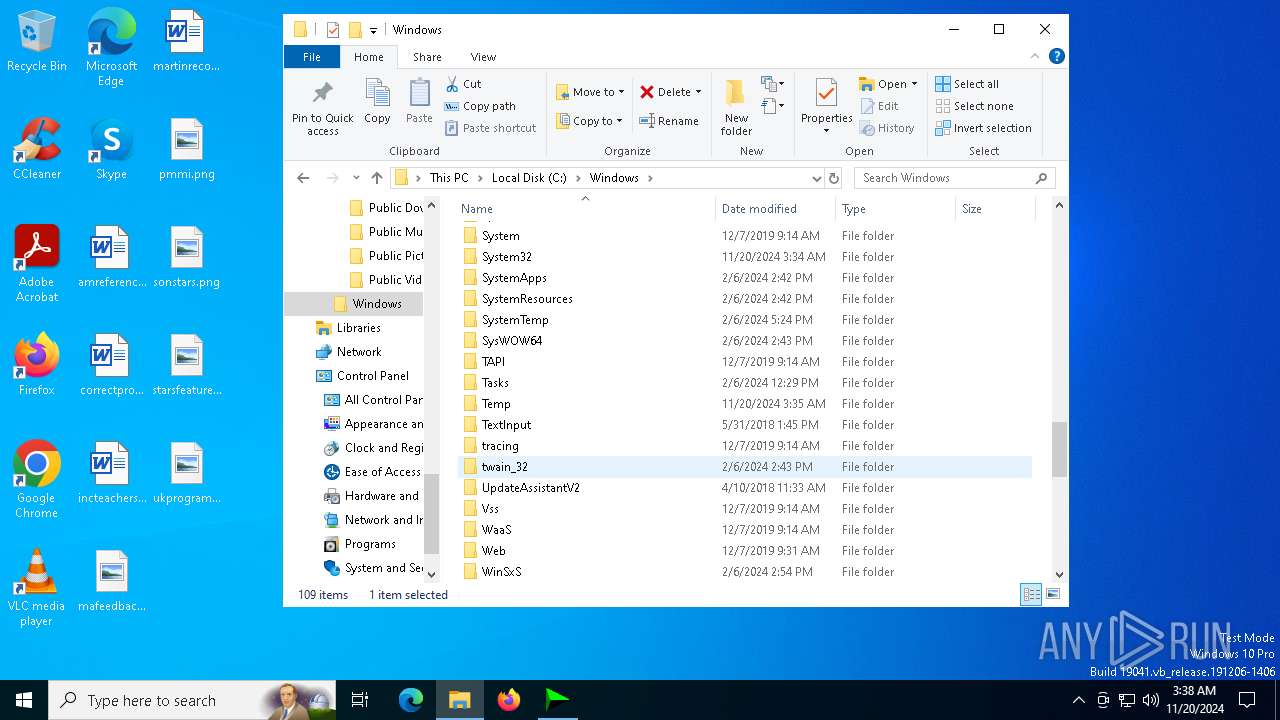
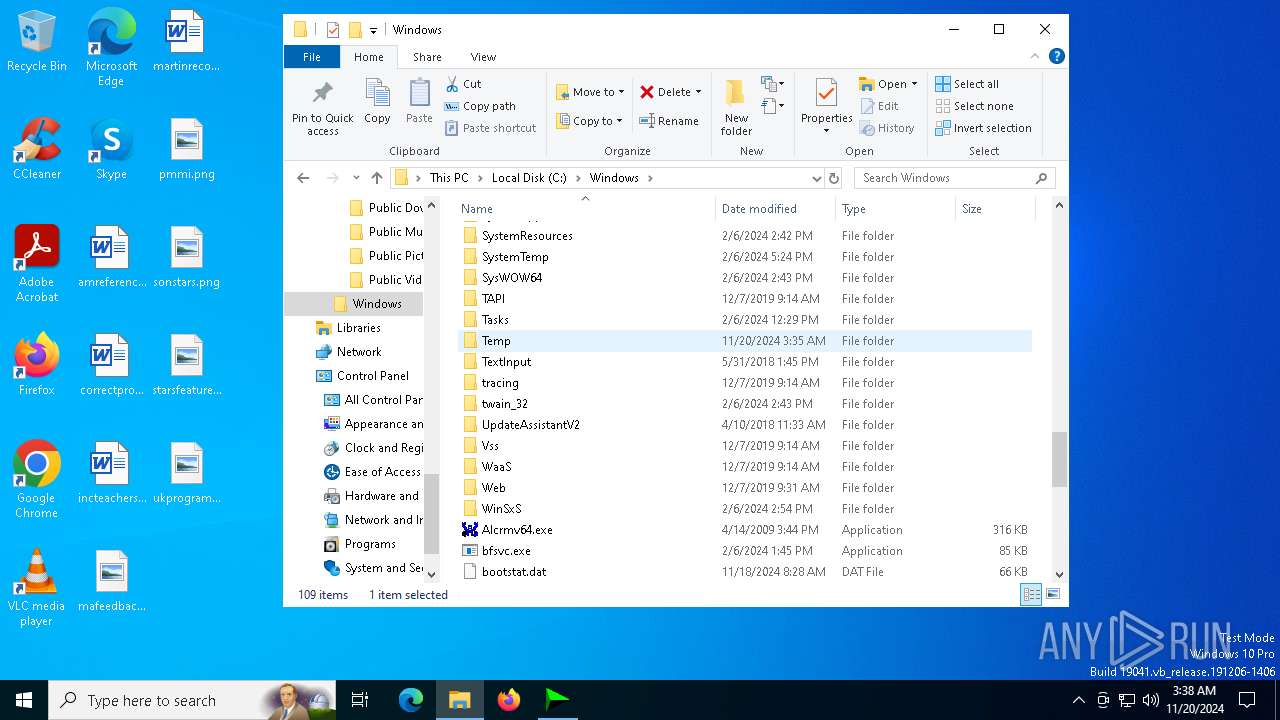
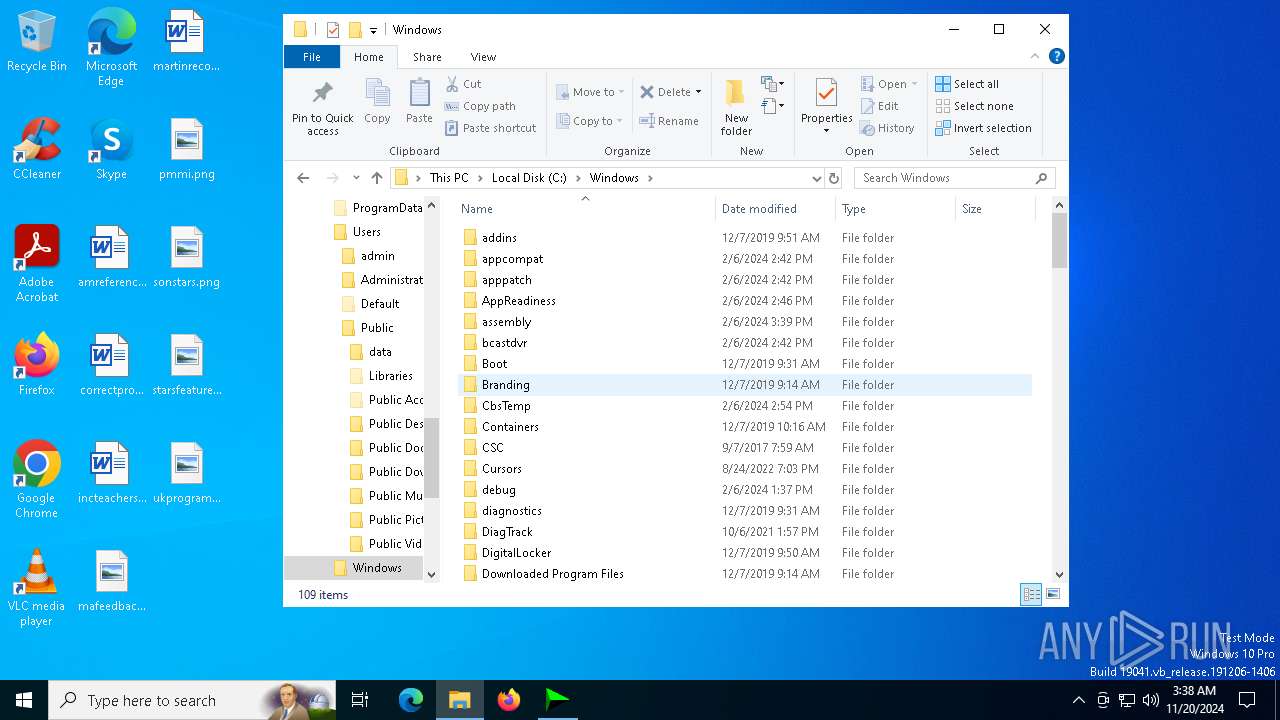
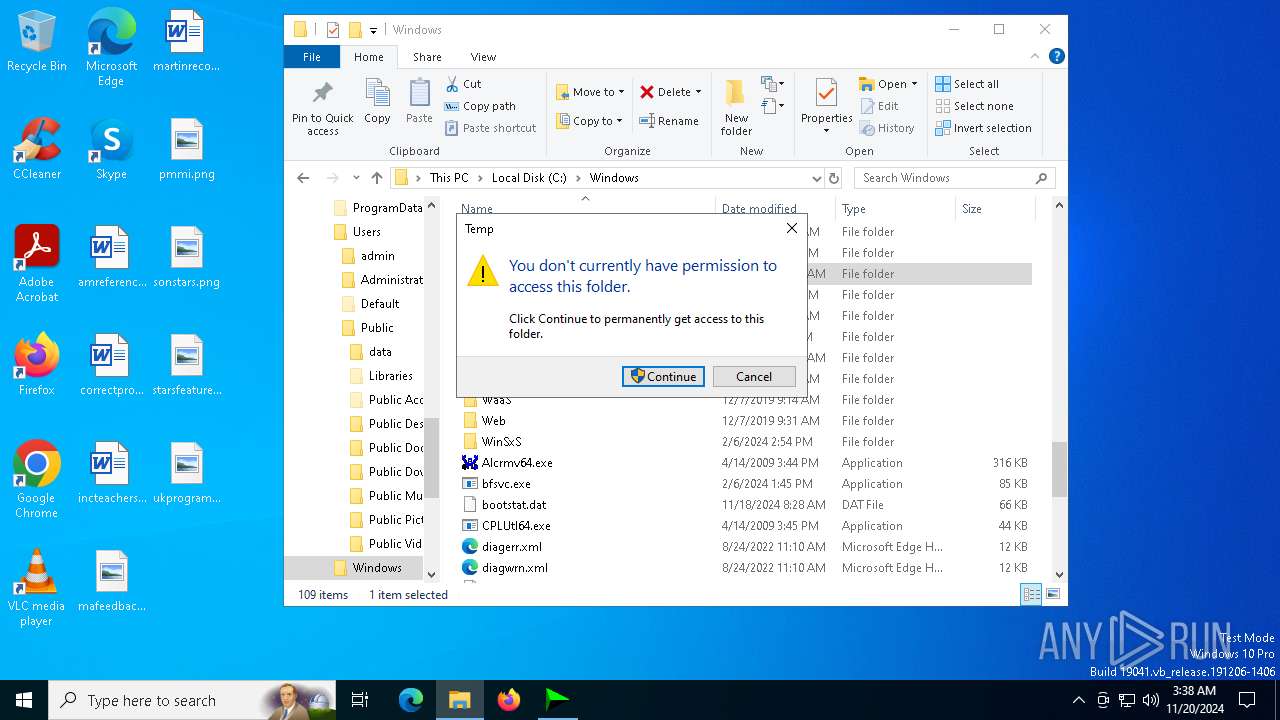
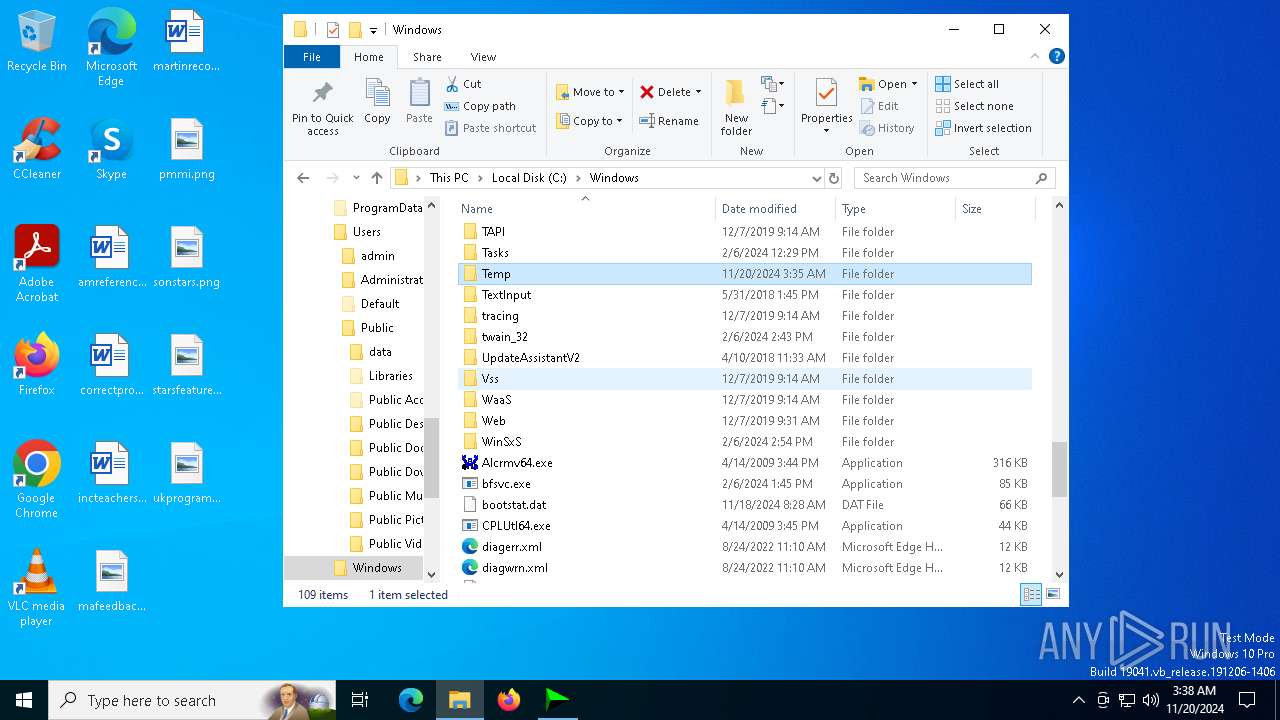
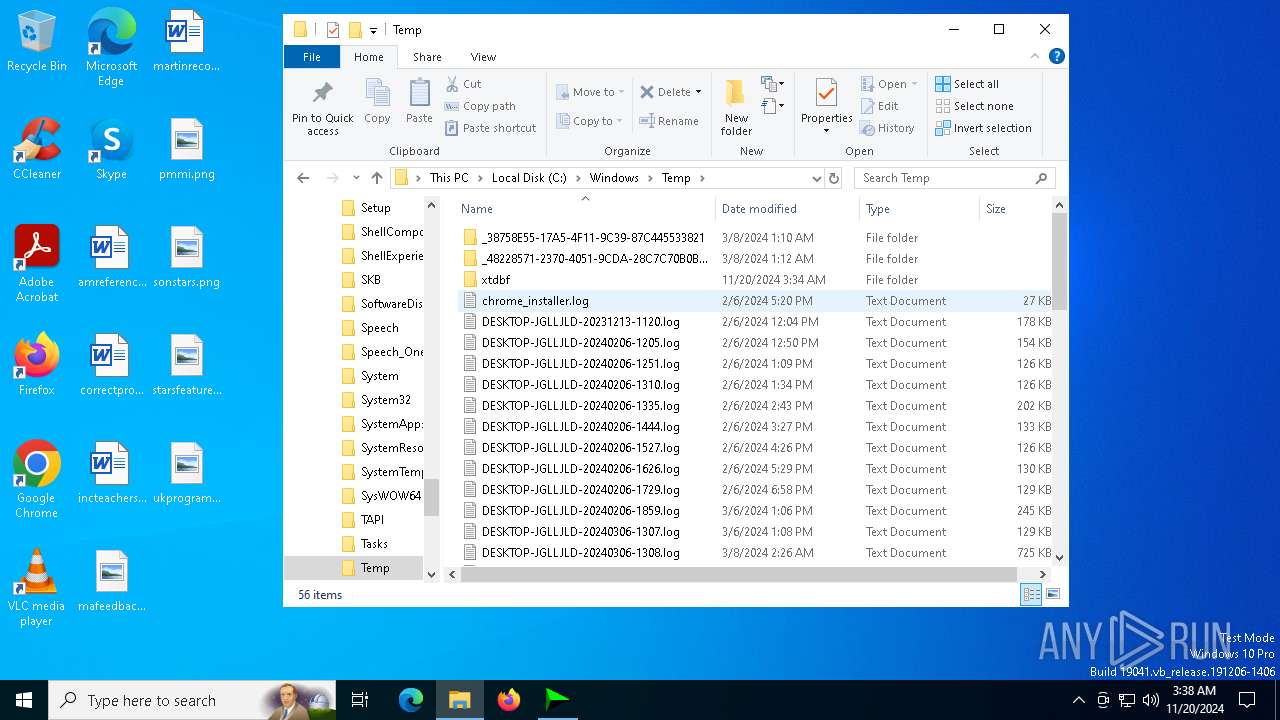
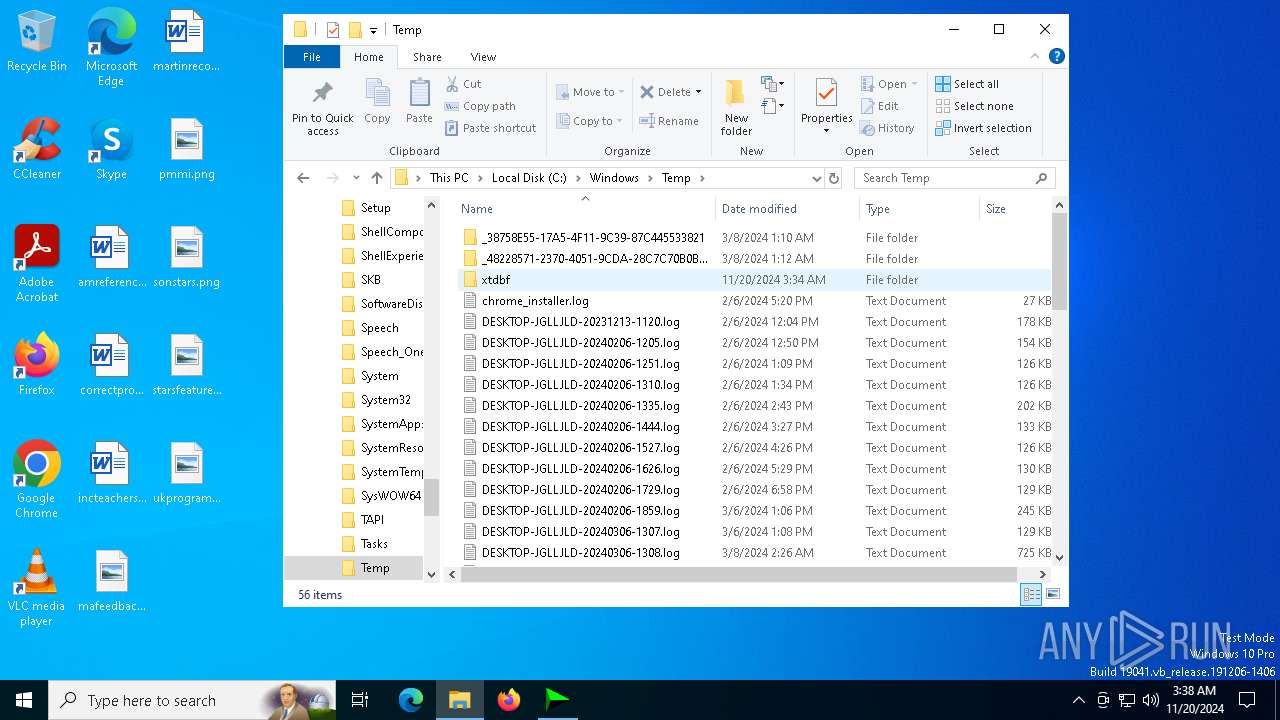
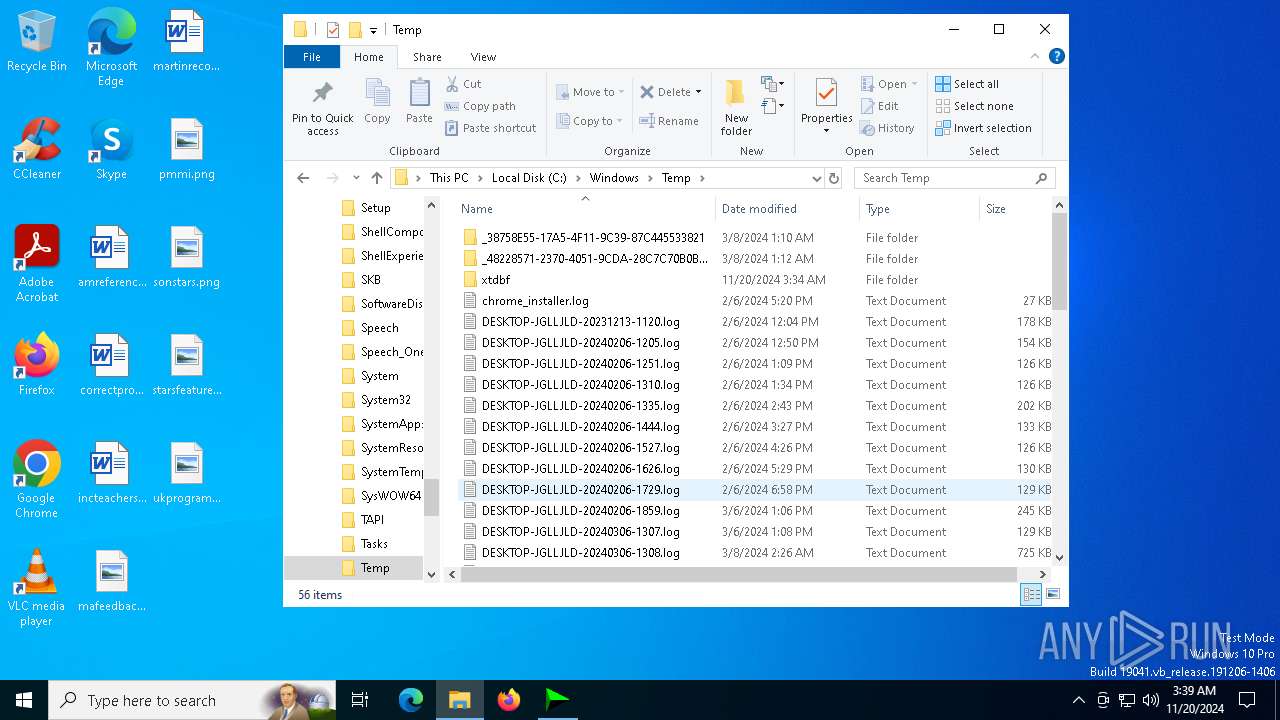
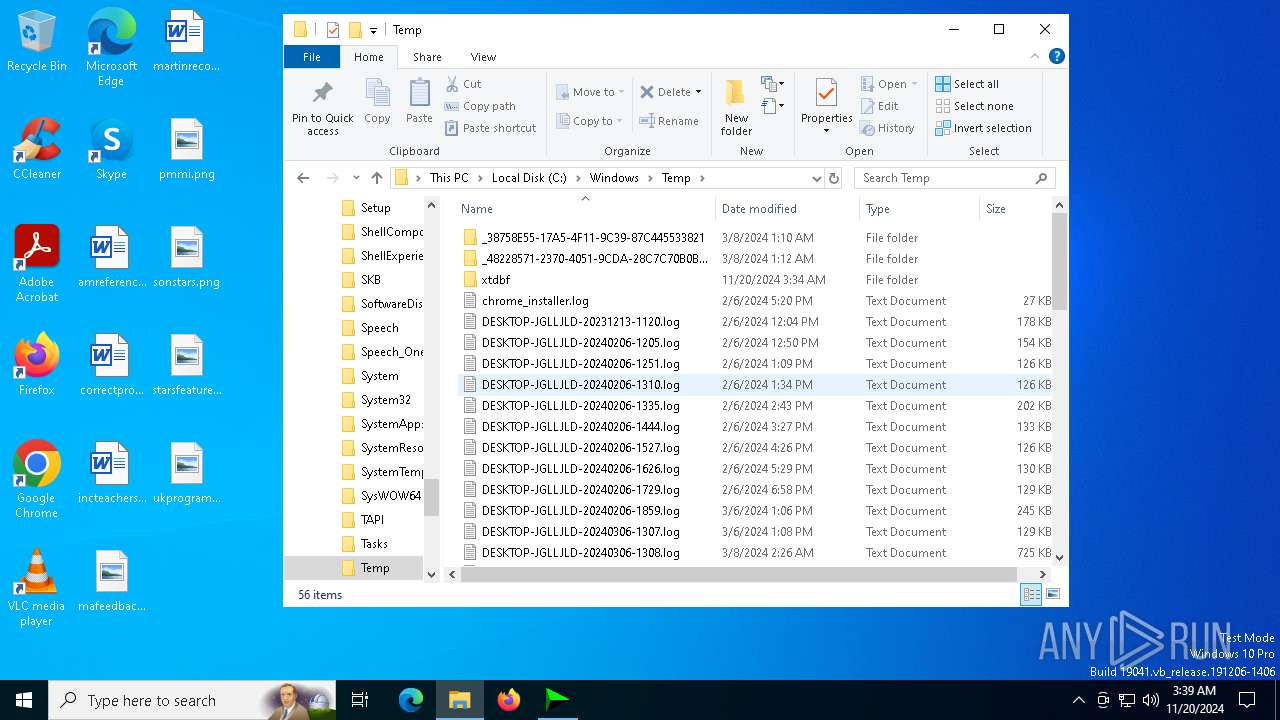
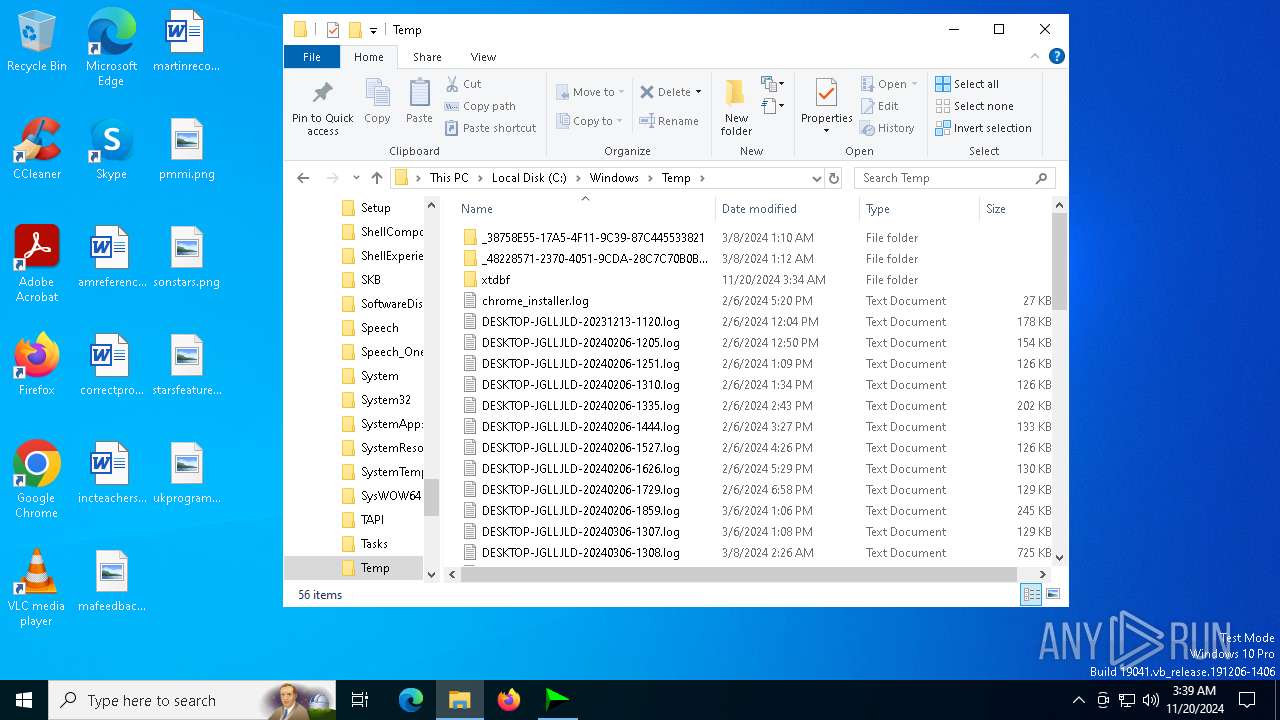
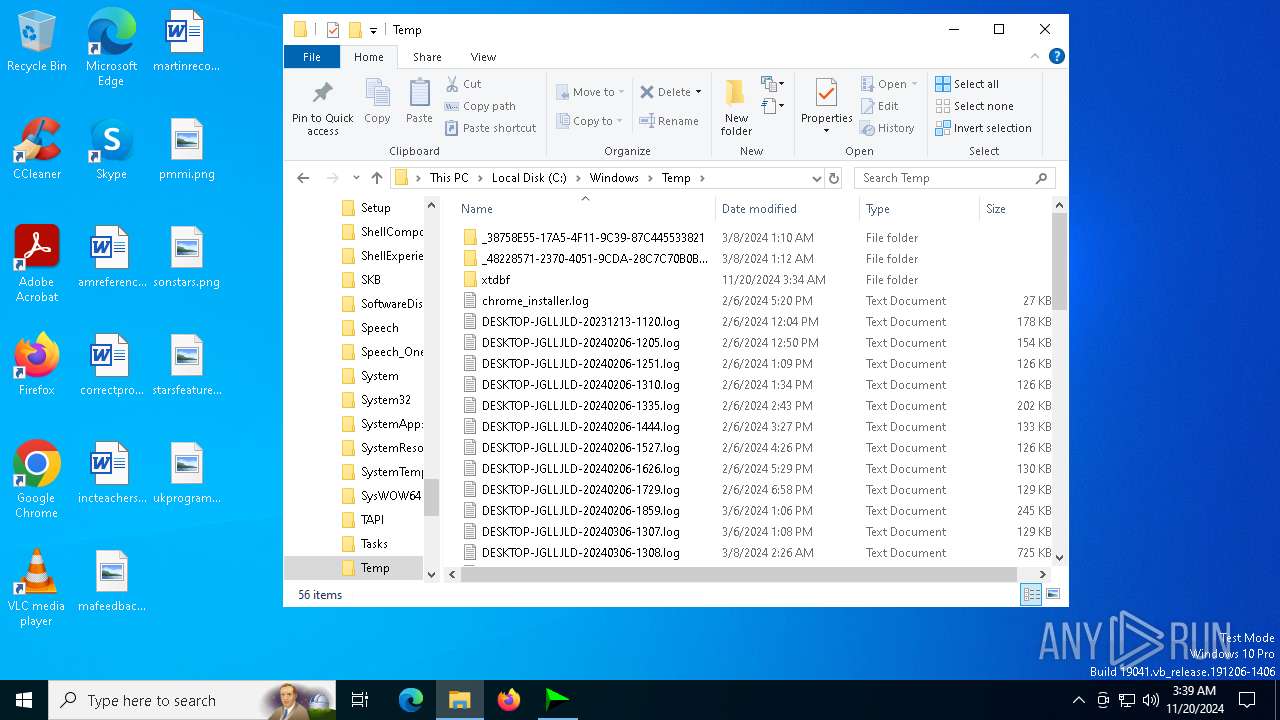
Create files in a temporary directory
- IDM_6.4x_Crack_v19.7.exe (PID: 2632)
The process uses the downloaded file
- IDM_6.4x_Crack_v19.7.exe (PID: 2632)
- IDM_6.4x_Crack.exe (PID: 2396)
- powershell.exe (PID: 2756)
- mdwslp.exe (PID: 6116)
Manual execution by a user
- WinRAR.exe (PID: 6656)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:09:13 05:23:52+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.41 |
| CodeSize: | 296960 |
| InitializedDataSize: | 7142912 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x208a8 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
209
Monitored processes
76
Malicious processes
10
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 712 | sc create XblGame binPath="C:\Users\Public\data\mdwslp.exe" start= auto | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 712 | sc start XblGame2 | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 848 | "C:\Windows\System32\cmd.exe" /C sc start XblGame | C:\Windows\System32\cmd.exe | — | uptimecrx.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 1056 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1472 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1512 | "C:\Windows\System32\cmd.exe" /C sc start XblGame2 | C:\Windows\System32\cmd.exe | — | IDM_6.4x_Crack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2000 | C:\Users\Public\data\uptimecrx.exe | C:\Users\Public\data\uptimecrx.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 2076 | "C:\Windows\System32\cmd.exe" /C sc create XblGame2 binPath="C:\Users\Public\data\uptimecrx.exe" start= auto | C:\Windows\System32\cmd.exe | — | IDM_6.4x_Crack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2332 | C:\Users\Public\data\uptimecrx.exe | C:\Users\Public\data\uptimecrx.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM | |||||||||||||||
| 2352 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 2396 | "C:\Users\admin\AppData\Local\Temp\.appjoiner\gen\956281\0\IDM_6.4x_Crack.exe" | C:\Users\admin\AppData\Local\Temp\.appjoiner\gen\956281\0\IDM_6.4x_Crack.exe | IDM_6.4x_Crack_v19.7.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
12 112
Read events
12 090
Write events
21
Delete events
1
Modification events
| (PID) Process: | (2632) IDM_6.4x_Crack_v19.7.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2632) IDM_6.4x_Crack_v19.7.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2632) IDM_6.4x_Crack_v19.7.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2396) IDM_6.4x_Crack.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2396) IDM_6.4x_Crack.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2396) IDM_6.4x_Crack.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6268) IDM_6.4x_Crack_v19.7.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (6268) IDM_6.4x_Crack_v19.7.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Wow6432Node\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (6268) IDM_6.4x_Crack_v19.7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (6268) IDM_6.4x_Crack_v19.7.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableRegistryTools |
Value: 0 | |||
Executable files
12
Suspicious files
28
Text files
21
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2396 | IDM_6.4x_Crack.exe | C:\Users\Public\data\zcrxdebug.txt | text | |
MD5:38F6AB17C6E85C0526885D059367E138 | SHA256:621AEEBCEEF82E4108C1A19E9114E998C53BB79C7E0A366031DEF44509AC0DF0 | |||
| 2396 | IDM_6.4x_Crack.exe | C:\Windows\System32\ntdb.dat | executable | |
MD5:817AC44171AAA80E179B45B91E61E9F9 | SHA256:FEEF3273EE5064828553078E7001B488C05DB8BE7A2114BB02D5801ADF8E904F | |||
| 2632 | IDM_6.4x_Crack_v19.7.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | der | |
MD5:67E486B2F148A3FCA863728242B6273E | SHA256:FACAF1C3A4BF232ABCE19A2D534E495B0D3ADC7DBE3797D336249AA6F70ADCFB | |||
| 2396 | IDM_6.4x_Crack.exe | C:\Users\Public\data\ver.dat | binary | |
MD5:C2846DD09C460773E434A46376F3A878 | SHA256:B2E9457022303C98FFEAE3B020062870426DAD2FE4D3887B2BD938F3BCC177D3 | |||
| 2396 | IDM_6.4x_Crack.exe | C:\Windows\System32\signtool.exe | executable | |
MD5:31FAED2662785243E1C4675D47F02665 | SHA256:A6C1AC1AD29D4EA2C57339F86846FA73B441D30B49B15604E0CF79A605C53128 | |||
| 2396 | IDM_6.4x_Crack.exe | C:\Windows\System32\mi_nt_svc.dat | executable | |
MD5:D9AA5776CF71EFD408C4B48B1587B80D | SHA256:B460B3E8C0795B5BC2E9F2406E0A66AB2FF13B1A3D7CEF0C92B9D28B240A7EAF | |||
| 2632 | IDM_6.4x_Crack_v19.7.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B46811C17859FFB409CF0E904A4AA8F8 | binary | |
MD5:13895D113EDBFE0597AEEDB5E1F9EB00 | SHA256:C3642B852DEE7A58AA834F816DF9F0ACF313FEDC25301BBF77D9B977C6C69E4A | |||
| 2396 | IDM_6.4x_Crack.exe | C:\Users\Public\data\set.dat | binary | |
MD5:337126DAD75533D3F123A8F55A5394E3 | SHA256:A064DBBF3FC8479A3601AB2CDBB1FAA943761592A37A525313FA7552F6318C8B | |||
| 2632 | IDM_6.4x_Crack_v19.7.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | binary | |
MD5:8BF0F8AA45914E6A0B8DE044D8A7B939 | SHA256:0652BF4292B3179546B27FEFE313F736D6DF504699109668B34A94AECA07B9B0 | |||
| 6116 | mdwslp.exe | C:\Users\Public\data\ext\content_script.js | text | |
MD5:A127D316F16D9A6942A79434579C7C36 | SHA256:52418D1D907AE8F8F7B66E2B193407F1CC5F98B232E34E513A45E2C5330E7BE2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
58
DNS requests
34
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2632 | IDM_6.4x_Crack_v19.7.exe | GET | 200 | 142.250.184.195:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
2632 | IDM_6.4x_Crack_v19.7.exe | GET | 200 | 142.250.184.195:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
4932 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6472 | signtool.exe | POST | 200 | 91.199.212.79:80 | http://timestamp.sectigo.com/ | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4932 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 91.199.212.79:80 | http://timestamp.sectigo.com/ | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4932 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6024 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2632 | IDM_6.4x_Crack_v19.7.exe | 104.21.94.97:443 | dash.zintrack.com | CLOUDFLARENET | — | unknown |
2632 | IDM_6.4x_Crack_v19.7.exe | 142.250.184.195:80 | c.pki.goog | GOOGLE | US | whitelisted |
2396 | IDM_6.4x_Crack.exe | 104.21.94.97:443 | dash.zintrack.com | CLOUDFLARENET | — | unknown |
4932 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4932 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
dash.zintrack.com |
| unknown |
c.pki.goog |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
timestamp.sectigo.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |