| File name: | PowderLauncher.exe |
| Full analysis: | https://app.any.run/tasks/fc189fe4-ffa8-44a0-91da-bf42eba894cb |
| Verdict: | Malicious activity |
| Analysis date: | October 25, 2024, 12:24:39 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
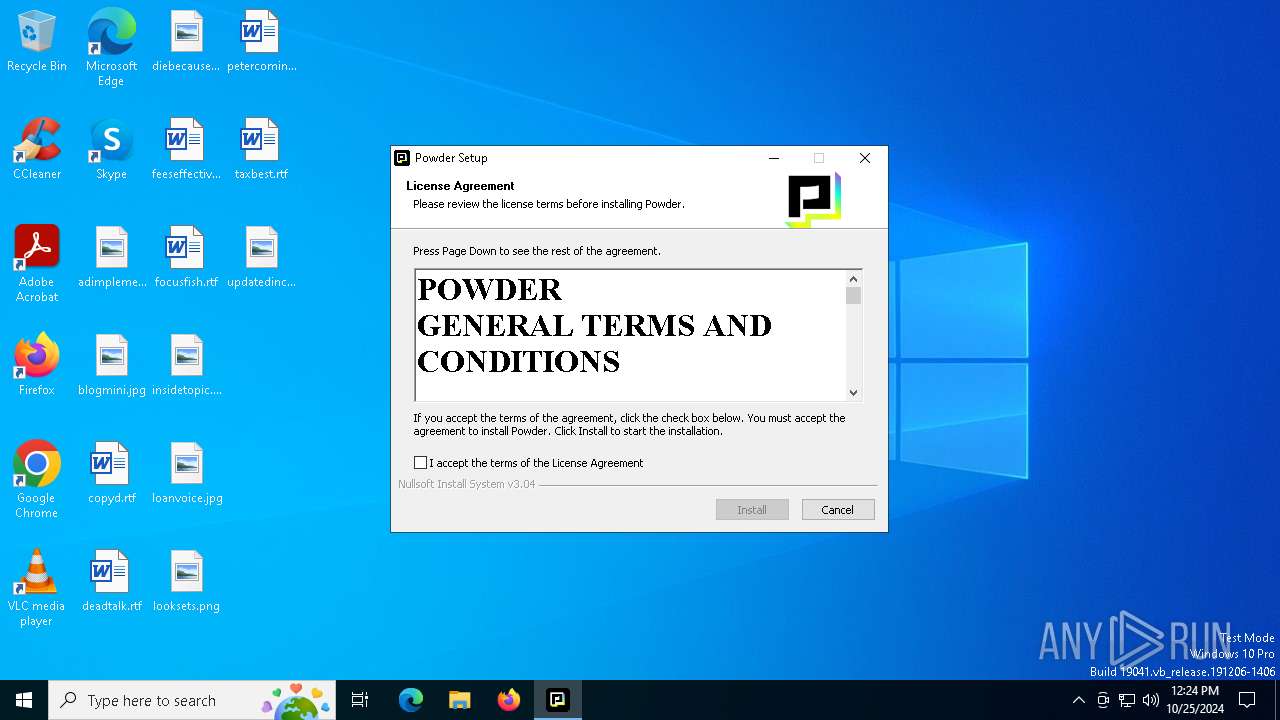
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 0857D684C488B78094FFAD69047B9A28 |
| SHA1: | 22076B2C1FA2B74394879F106A7198025EDFAE00 |
| SHA256: | F5D443EDFF1A5742642FA3931BED0B5473BD4B187F71A470A26463A7A25F2405 |
| SSDEEP: | 12288:l2dV0owNR/CJ21KzdBF7HZ+mdJiCjBEiuyGE7eA4WM:l2dVZuZCJ21evHAm3i+BEiBGMTM |
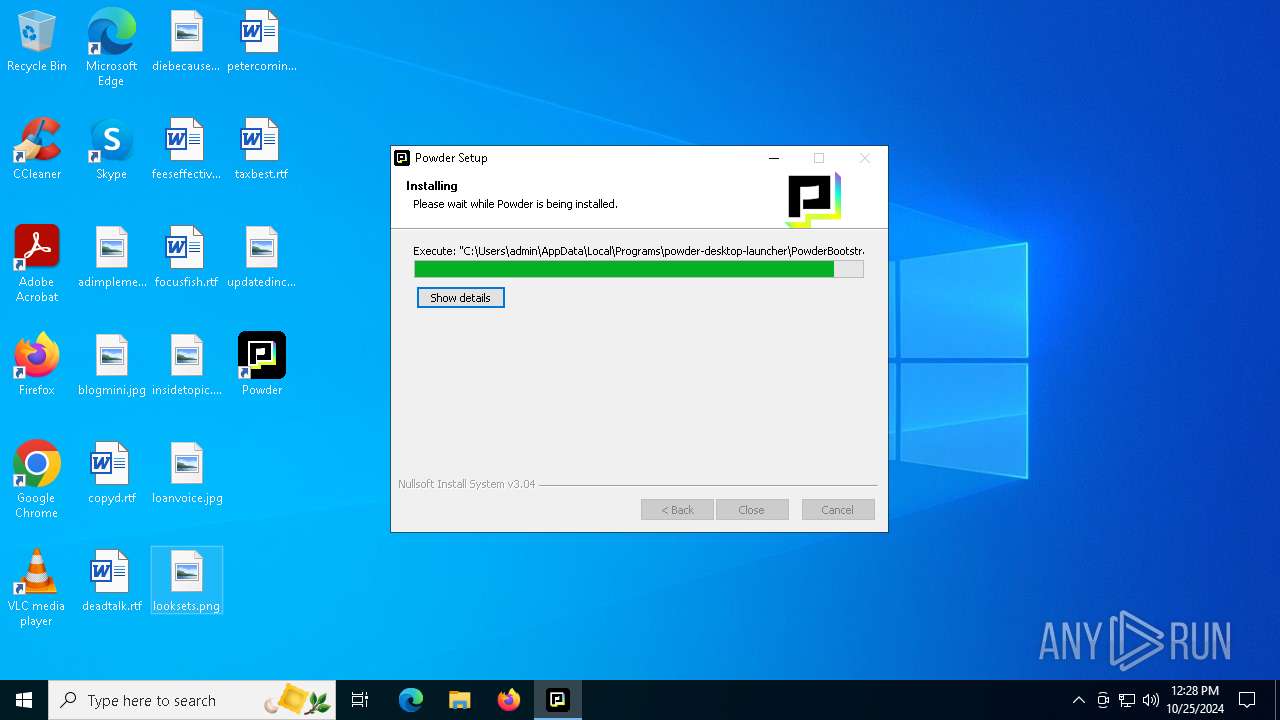
MALICIOUS
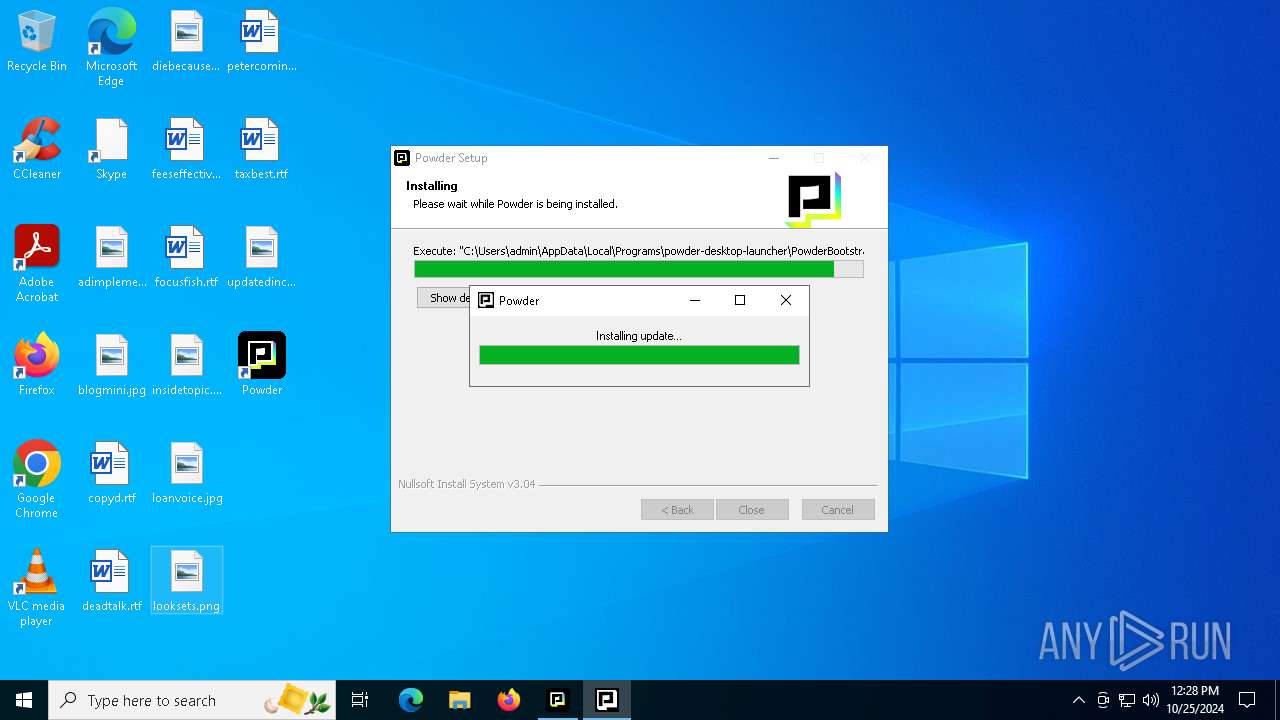
Changes the autorun value in the registry
- PowderLauncher.exe (PID: 4072)
SUSPICIOUS
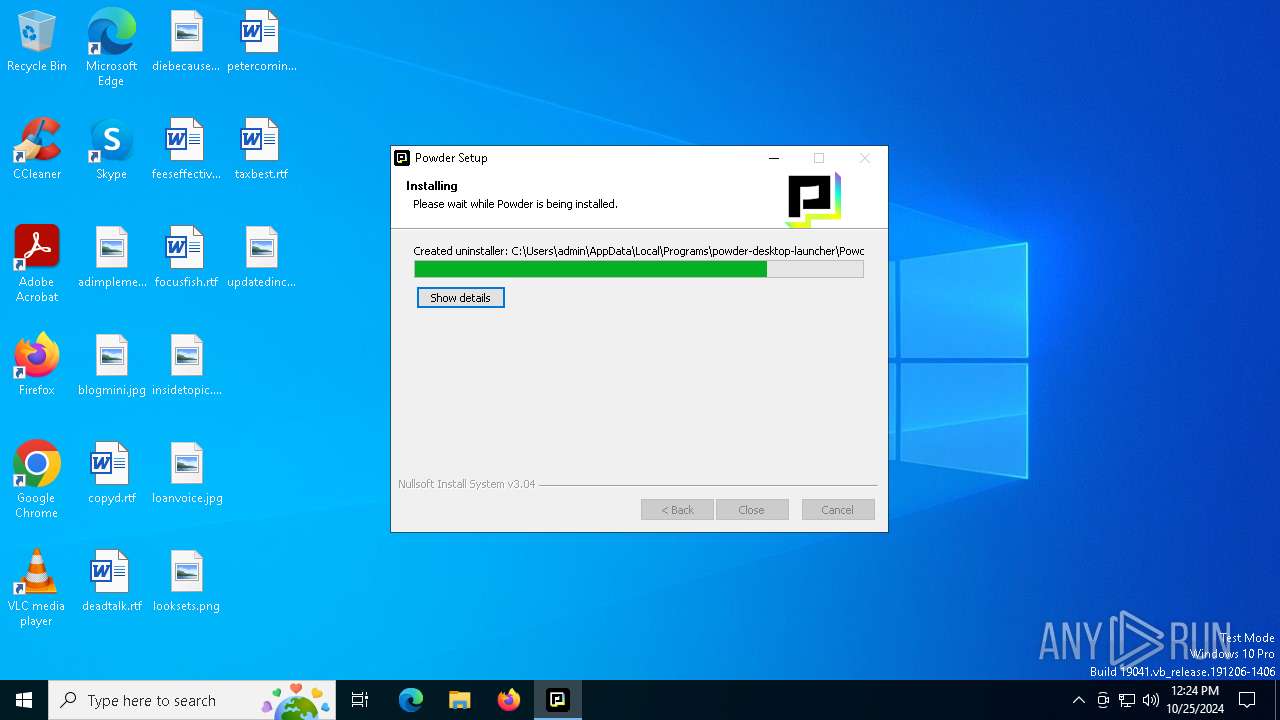
Executable content was dropped or overwritten
- PowderLauncher.exe (PID: 4072)
- PowderLauncherUninstaller.exe (PID: 5084)
- Powder-6.15.0.exe (PID: 6300)
Malware-specific behavior (creating "System.dll" in Temp)
- Powder-6.15.0.exe (PID: 6300)
Process drops legitimate windows executable
- Powder-6.15.0.exe (PID: 6300)
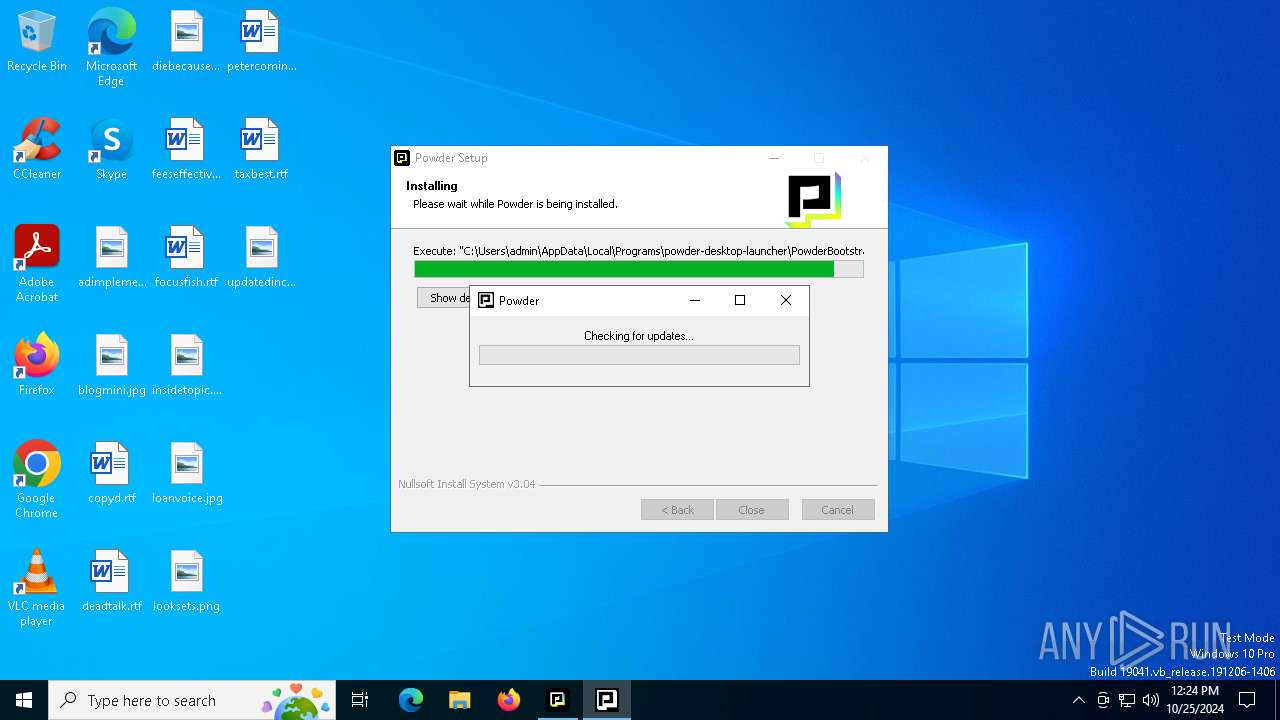
Application launched itself
- Powder.exe (PID: 1432)
Starts itself from another location
- PowderLauncher.exe (PID: 4072)
- PowderLauncherUninstaller.exe (PID: 5084)
Checks for external IP
- svchost.exe (PID: 2172)
- Powder.exe (PID: 1432)
Get information on the list of running processes
- Powder-6.15.0.exe (PID: 6300)
- cmd.exe (PID: 1580)
Starts CMD.EXE for commands execution
- Powder-6.15.0.exe (PID: 6300)
Drops 7-zip archiver for unpacking
- Powder-6.15.0.exe (PID: 6300)
INFO
Checks supported languages
- PowderLauncher.exe (PID: 4072)
- PowderBootstrap.exe (PID: 3828)
Reads the computer name
- PowderLauncher.exe (PID: 4072)
- PowderBootstrap.exe (PID: 3828)
Create files in a temporary directory
- PowderLauncher.exe (PID: 4072)
- PowderBootstrap.exe (PID: 3828)
Creates files or folders in the user directory
- PowderLauncher.exe (PID: 4072)
Reads the machine GUID from the registry
- PowderBootstrap.exe (PID: 3828)
Reads Environment values
- PowderBootstrap.exe (PID: 3828)
Disables trace logs
- PowderBootstrap.exe (PID: 3828)
Checks proxy server information
- PowderBootstrap.exe (PID: 3828)
Reads the software policy settings
- PowderBootstrap.exe (PID: 3828)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:15 22:24:46+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x338f |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
160
Monitored processes
22
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 916 | C:\Users\admin\AppData\Local\Programs\powder-desktop\PowderRecorderCli.exe --commandPipeName=POWDER_PIPE_6e7c32ad-4180-4bf3-9628-ad93343cbdd5 driver_version_check | C:\Users\admin\AppData\Local\Programs\powder-desktop\PowderRecorderCli.exe | — | Powder.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1432 | "C:\Users\admin\AppData\Local\Programs\powder-desktop\Powder.exe" | C:\Users\admin\AppData\Local\Programs\powder-desktop\Powder.exe | PowderBootstrap.exe | ||||||||||||
User: admin Company: Powder Integrity Level: MEDIUM Description: Powder Version: 6.15.0 Modules
| |||||||||||||||
| 1580 | cmd /c tasklist /FI "USERNAME eq %USERNAME%" /FI "IMAGENAME eq Powder.exe" | %SYSTEMROOT%\System32\find.exe "Powder.exe" | C:\Windows\SysWOW64\cmd.exe | — | Powder-6.15.0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1732 | "C:\Users\admin\AppData\Local\Programs\powder-desktop\Powder.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --user-data-dir="C:\Users\admin\AppData\Roaming\powder-desktop" --field-trial-handle=2204,i,5367666849426699763,17990168403769506909,262144 --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version --mojo-platform-channel-handle=2200 /prefetch:3 | C:\Users\admin\AppData\Local\Programs\powder-desktop\Powder.exe | — | Powder.exe | |||||||||||
User: admin Company: Powder Integrity Level: MEDIUM Description: Powder Version: 6.15.0 Modules
| |||||||||||||||
| 1748 | "C:\Users\admin\AppData\Local\Temp\~nsu.tmp\Un_A.exe" /S _?=C:\Users\admin\AppData\Local\Programs\powder-desktop-launcher\ | C:\Users\admin\AppData\Local\Temp\~nsu.tmp\Un_A.exe | — | PowderLauncherUninstaller.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2172 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2236 | "C:\Users\admin\AppData\Local\Programs\powder-desktop\Powder.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\powder-desktop" --app-path="C:\Users\admin\AppData\Local\Programs\powder-desktop\resources\app.asar" --enable-sandbox --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --field-trial-handle=3064,i,5367666849426699763,17990168403769506909,262144 --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version --mojo-platform-channel-handle=3060 /prefetch:1 | C:\Users\admin\AppData\Local\Programs\powder-desktop\Powder.exe | — | Powder.exe | |||||||||||
User: admin Company: Powder Integrity Level: LOW Description: Powder Exit code: 0 Version: 6.15.0 Modules
| |||||||||||||||
| 3568 | C:\Users\admin\AppData\Local\Programs\powder-desktop\PostInstaller.exe -install-system-dependencies -app-root "C:\Users\admin\AppData\Local\Programs\powder-desktop" -first-install -fromLauncher -customer-data "" | C:\Users\admin\AppData\Local\Programs\powder-desktop\PostInstaller.exe | — | Powder-6.15.0.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 3792 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | PowderRecorderCli.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3828 | "C:\Users\admin\AppData\Local\Programs\powder-desktop-launcher\PowderBootstrap.exe" --first-install --exe-folder "C:\Users\admin\AppData\Local\Programs\powder-desktop" --override_install_path "" --store "" | C:\Users\admin\AppData\Local\Programs\powder-desktop-launcher\PowderBootstrap.exe | PowderLauncher.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
Total events
7 285
Read events
7 237
Write events
29
Delete events
19
Modification events
| (PID) Process: | (4072) PowderLauncher.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Powder |
Value: "C:\Users\admin\AppData\Local\Programs\powder-desktop-launcher\PowderBootstrap.exe" --first-install --exe-folder "C:\Users\admin\AppData\Local\Programs\powder-desktop" --override_install_path "" --store "" | |||
| (PID) Process: | (3828) PowderBootstrap.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PowderBootstrap_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3828) PowderBootstrap.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PowderBootstrap_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (3828) PowderBootstrap.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PowderBootstrap_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3828) PowderBootstrap.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PowderBootstrap_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (3828) PowderBootstrap.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PowderBootstrap_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (3828) PowderBootstrap.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PowderBootstrap_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3828) PowderBootstrap.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PowderBootstrap_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3828) PowderBootstrap.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PowderBootstrap_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3828) PowderBootstrap.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PowderBootstrap_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
159
Suspicious files
356
Text files
543
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3828 | PowderBootstrap.exe | C:\Users\admin\AppData\Local\Temp\PowderUpdateTemp\Powder-6.15.0.exe | — | |
MD5:— | SHA256:— | |||
| 6300 | Powder-6.15.0.exe | C:\Users\admin\AppData\Local\Temp\nsu82FB.tmp\package.7z | — | |
MD5:— | SHA256:— | |||
| 6300 | Powder-6.15.0.exe | C:\Users\admin\AppData\Local\Temp\nsu82FB.tmp\7z-out\ai-configs\audio_cues\Laughing\modelv2.pwdmdl | — | |
MD5:— | SHA256:— | |||
| 4072 | PowderLauncher.exe | C:\Users\admin\AppData\Local\Temp\nshB39A.tmp\StdUtils.dll | executable | |
MD5:C6A6E03F77C313B267498515488C5740 | SHA256:B72E9013A6204E9F01076DC38DABBF30870D44DFC66962ADBF73619D4331601E | |||
| 4072 | PowderLauncher.exe | C:\Users\admin\AppData\Local\Programs\powder-desktop-launcher\Newtonsoft.Json.dll | executable | |
MD5:081D9558BBB7ADCE142DA153B2D5577A | SHA256:B624949DF8B0E3A6153FDFB730A7C6F4990B6592EE0D922E1788433D276610F3 | |||
| 6300 | Powder-6.15.0.exe | C:\Users\admin\AppData\Local\Temp\nsu82FB.tmp\7z-out\ai-configs\audio_cues\Llm\events.json | text | |
MD5:CF41543371C28F1FC4ED506BE01FA5F5 | SHA256:F9CA3BFAC987B910A398D69EE6624F1CF79C94608411CC712711E1E78E27ACBF | |||
| 6300 | Powder-6.15.0.exe | C:\Users\admin\AppData\Local\Temp\nsu82FB.tmp\nsis7z.dll | executable | |
MD5:80E44CE4895304C6A3A831310FBF8CD0 | SHA256:B393F05E8FF919EF071181050E1873C9A776E1A0AE8329AEFFF7007D0CADF592 | |||
| 6300 | Powder-6.15.0.exe | C:\Users\admin\AppData\Local\Temp\nsu82FB.tmp\7z-out\ai-configs\audio_cues\Laughing\events.json | text | |
MD5:909F7F47623FA1F15E72D453453E02F5 | SHA256:3D2A44FB3F462797B6AD21F3E65D7EC21EED576AAF93D9A4BB69657F418690E5 | |||
| 6300 | Powder-6.15.0.exe | C:\Users\admin\AppData\Local\Temp\nsu82FB.tmp\7z-out\ai-configs\other_cues\Community\events.json | text | |
MD5:DF1653A8697969B85462E0155E8A8E5B | SHA256:752DD9E5727E63D0D971EFAC0B6F5070FED56E96ED8FA0154E393BAE5AD4761A | |||
| 6300 | Powder-6.15.0.exe | C:\Users\admin\AppData\Local\Temp\nsu82FB.tmp\7z-out\ai-configs\src\lua\postprocess\event.lua | text | |
MD5:409BCDA04CBF0B0A0E4E405BB020B643 | SHA256:75979905E3C9D0AC2D0090154A65BBABBE48EF3890DCFB656C3B74778F27C0B4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
69
DNS requests
29
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
624 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6712 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1176 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6712 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3524 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4360 | SearchApp.exe | 104.126.37.170:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4360 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3828 | PowderBootstrap.exe | 143.204.215.63:443 | pc-releases.powder.gg | AMAZON-02 | US | unknown |
624 | svchost.exe | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
624 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
pc-releases.powder.gg |
| unknown |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1432 | Powder.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup Domain (myip .opendns .com in DNS lookup) |
2172 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (icanhazip .com) |
1432 | Powder.exe | Device Retrieving External IP Address Detected | ET INFO Observed External IP Lookup Domain (icanhazip .com in TLS SNI) |