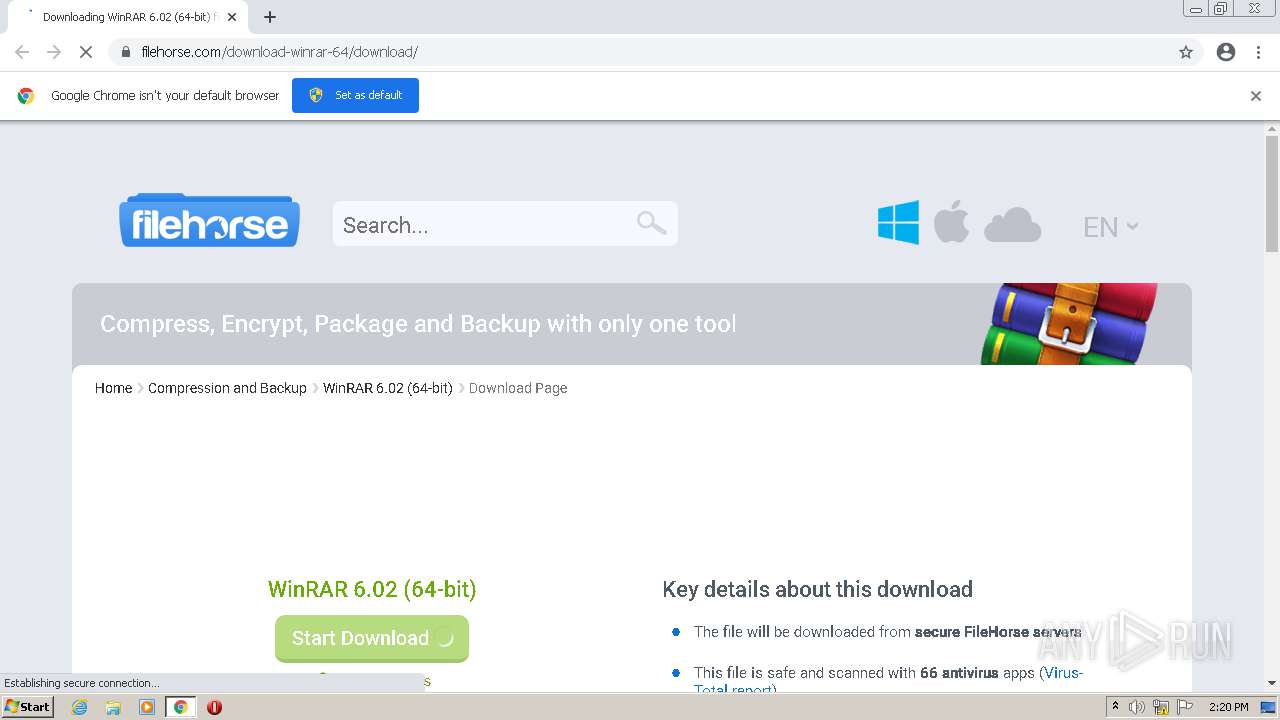
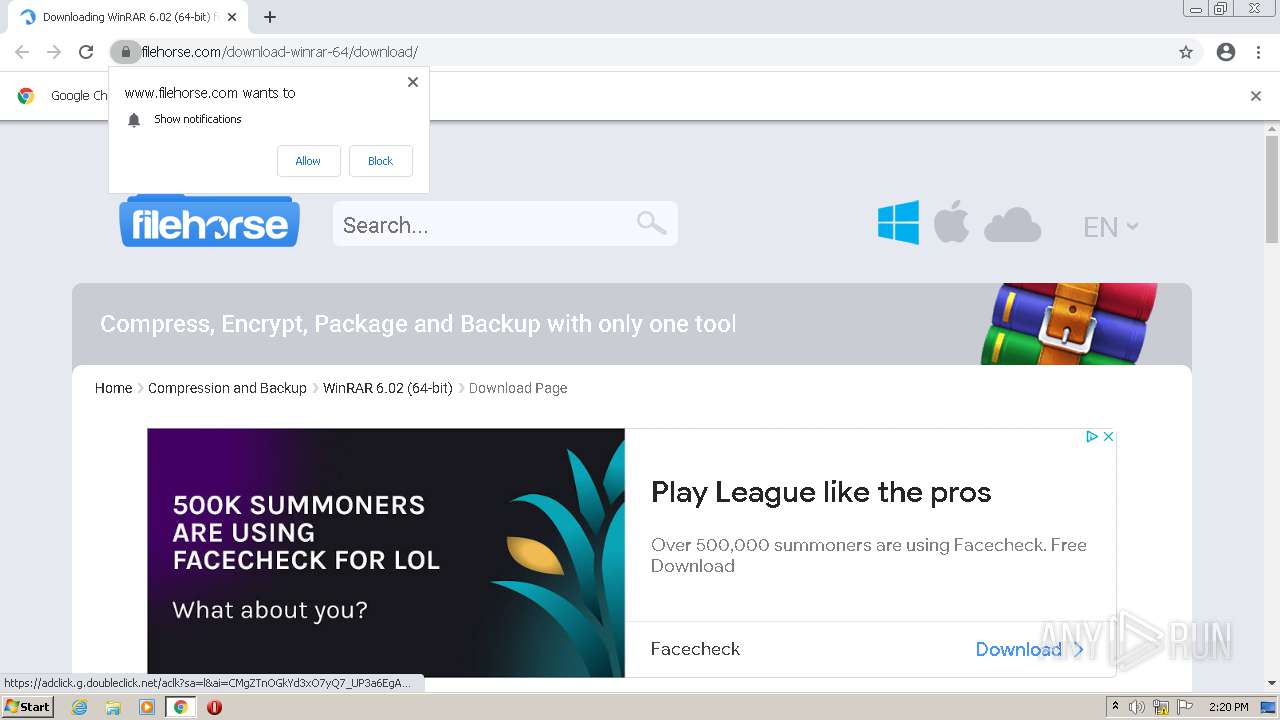
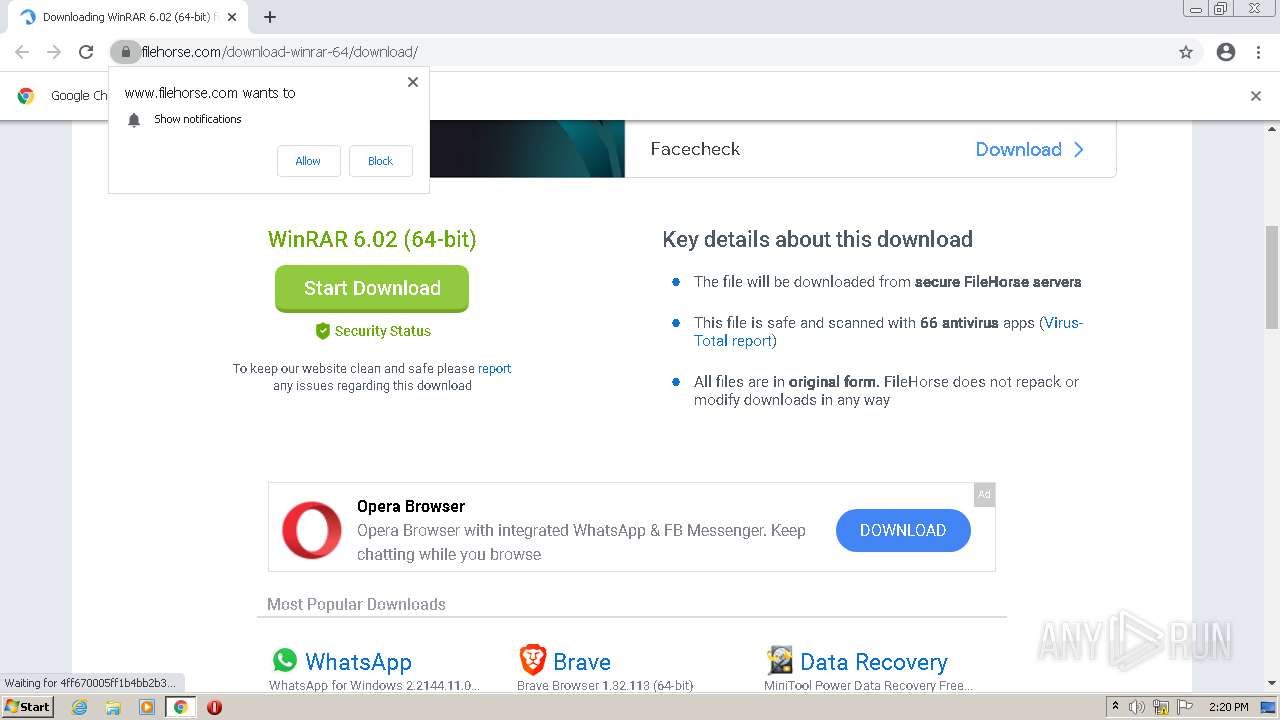
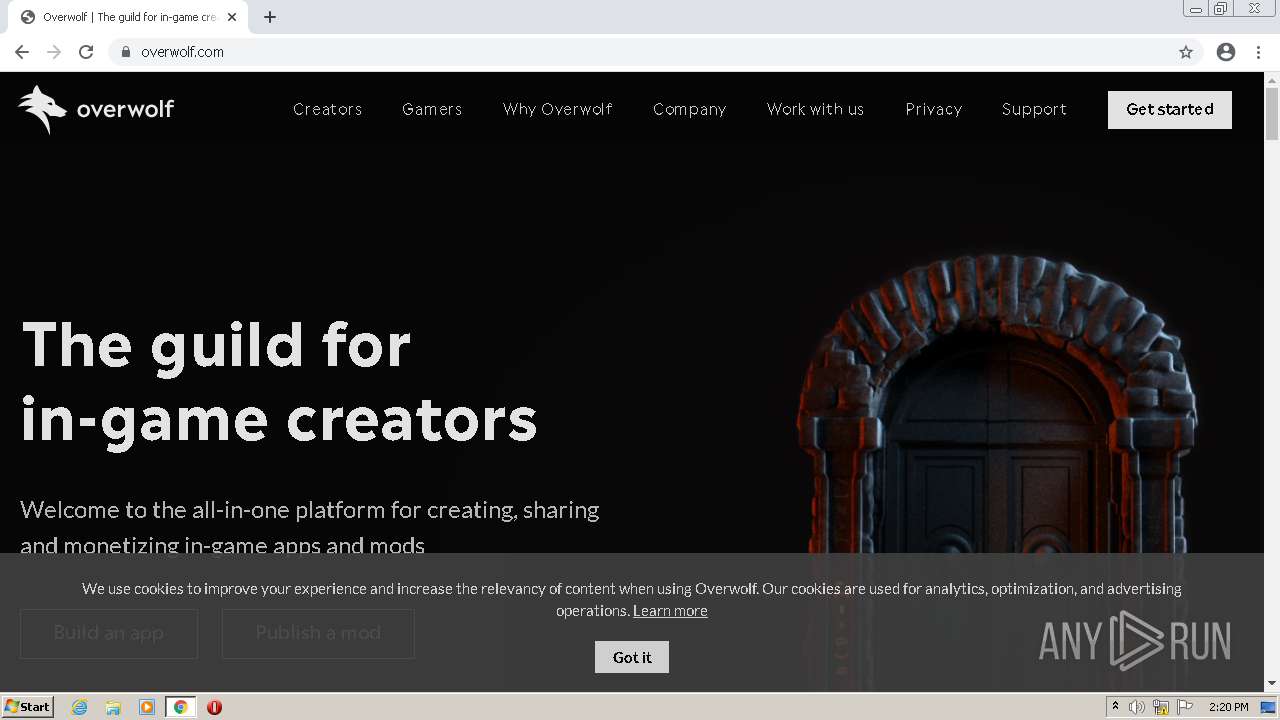
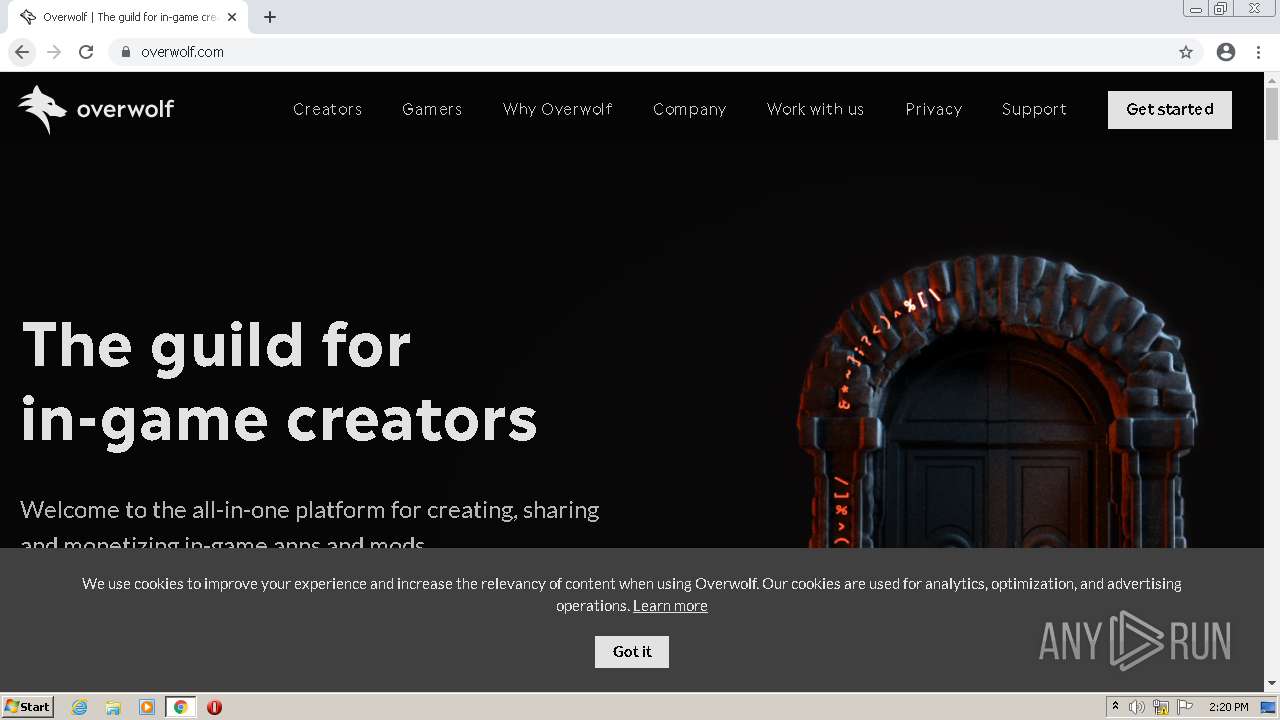
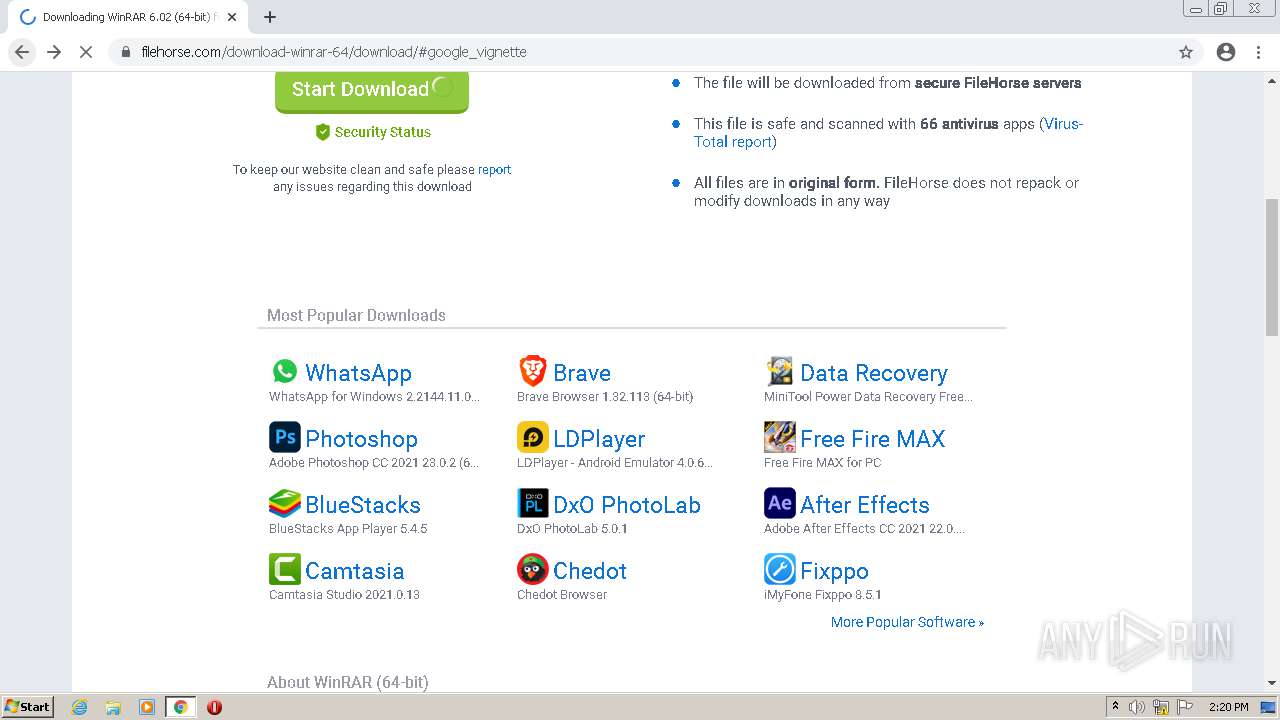
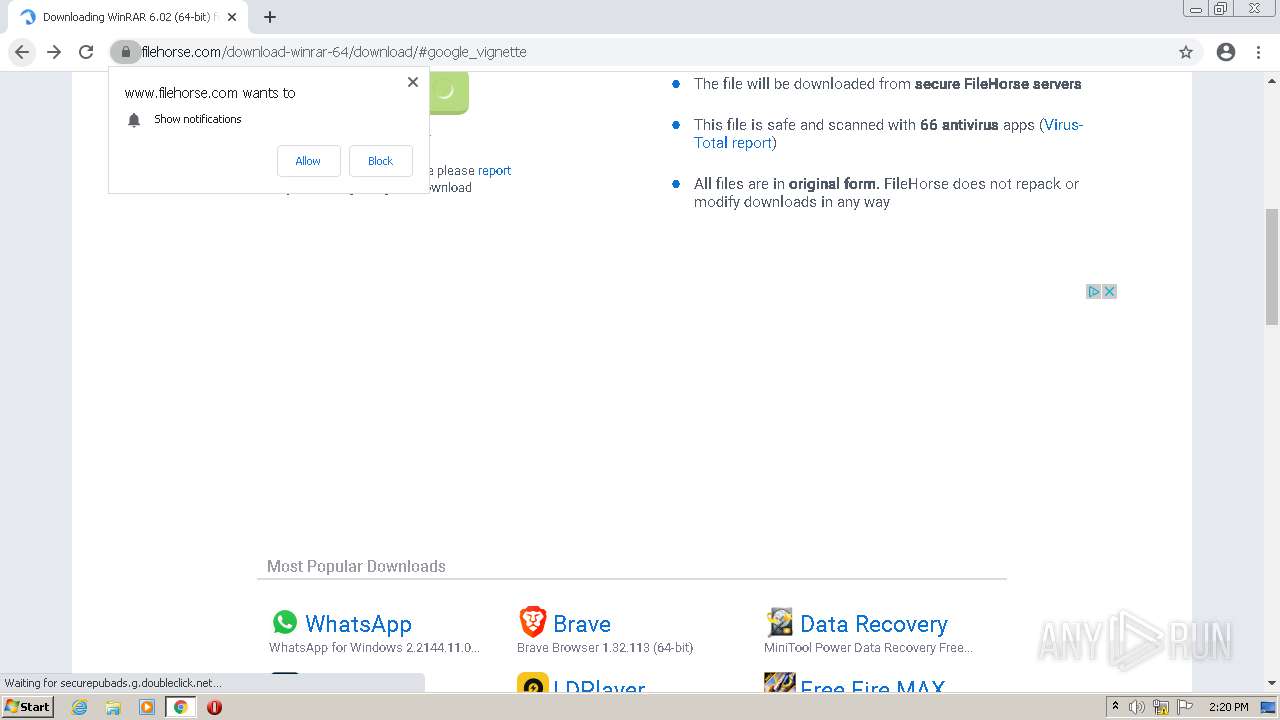
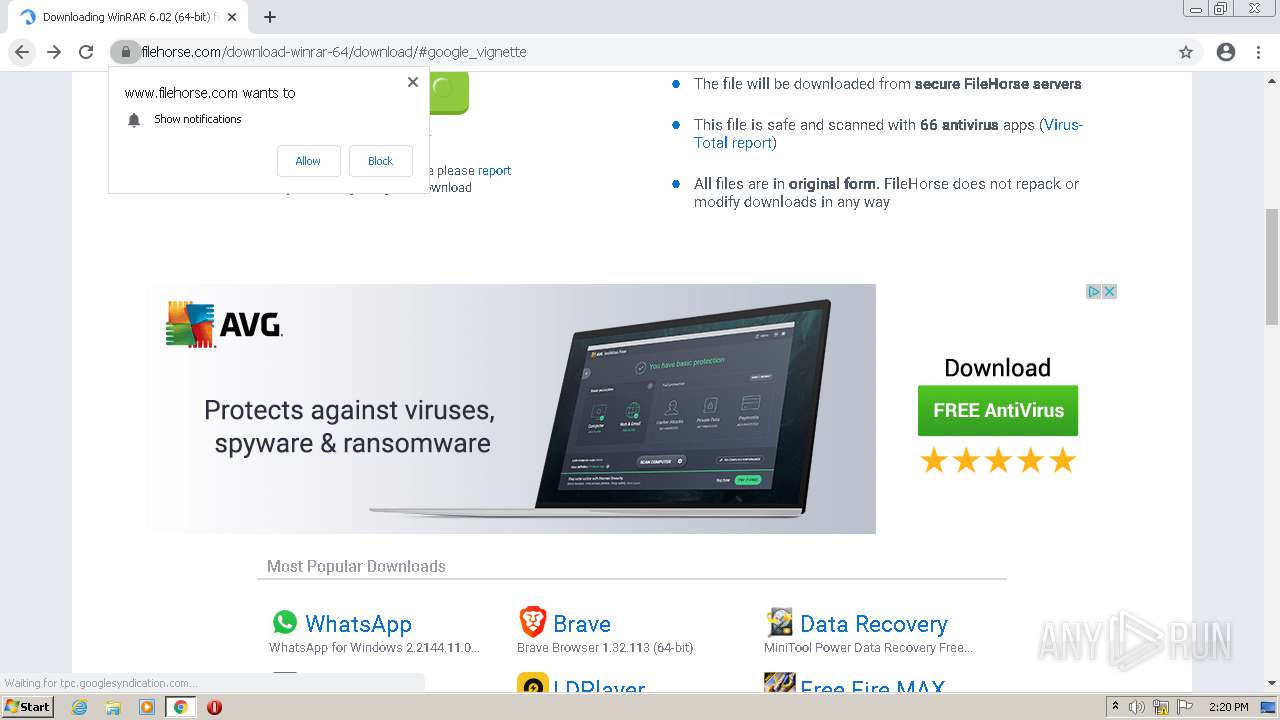
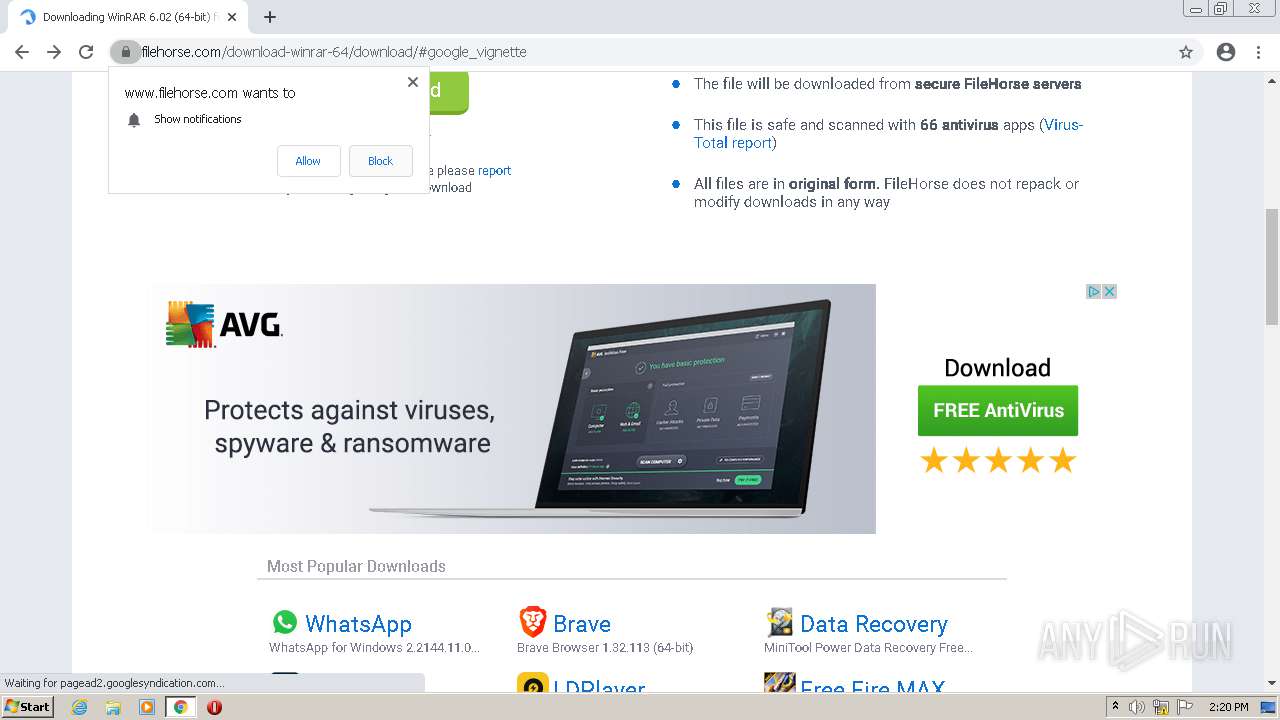
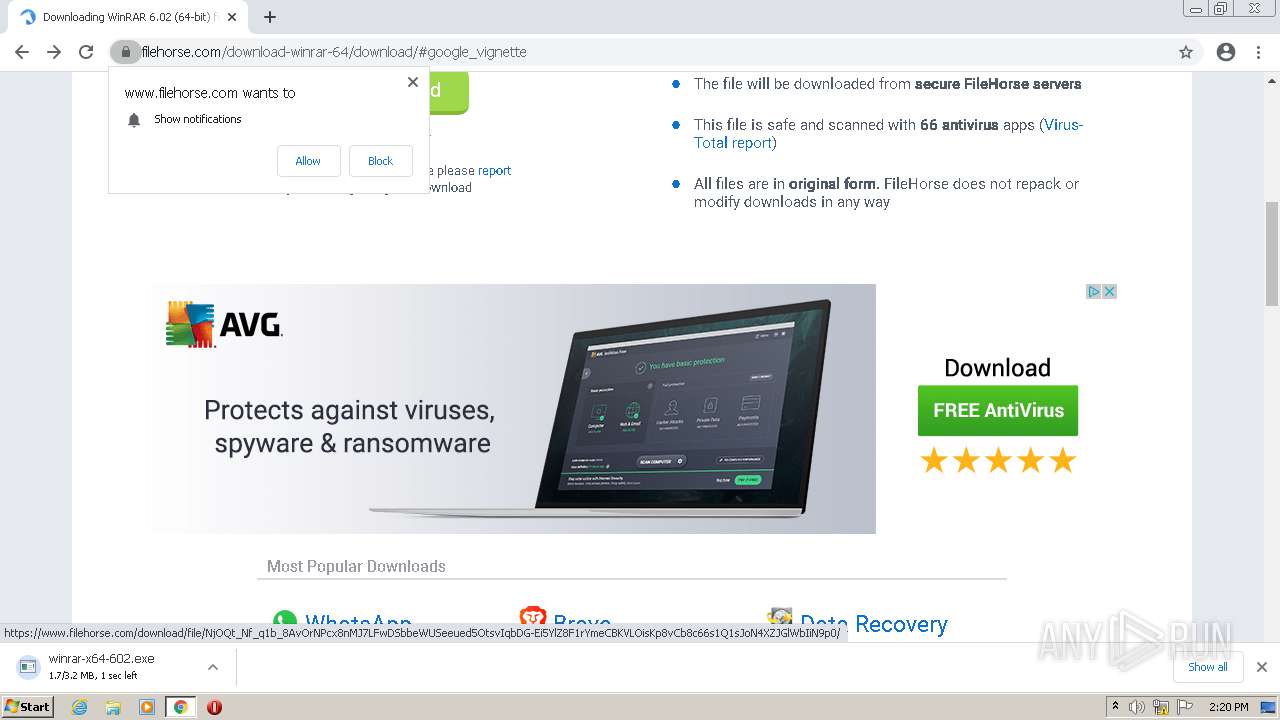
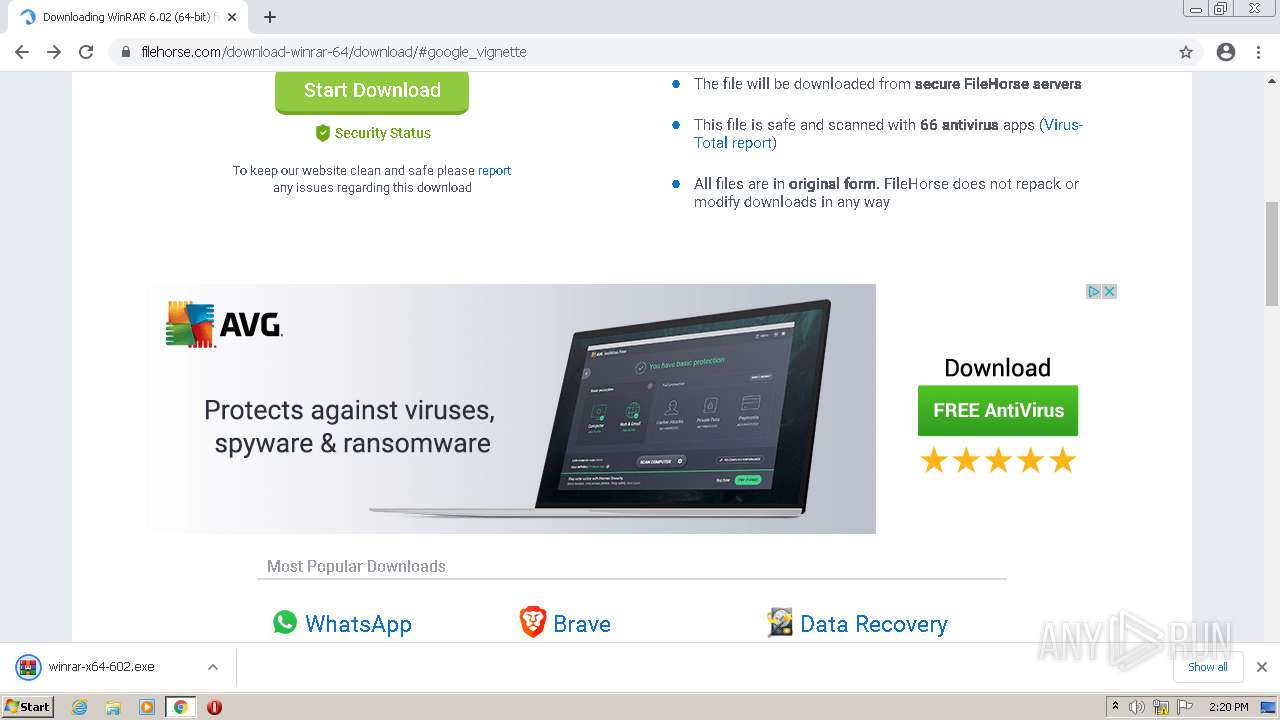
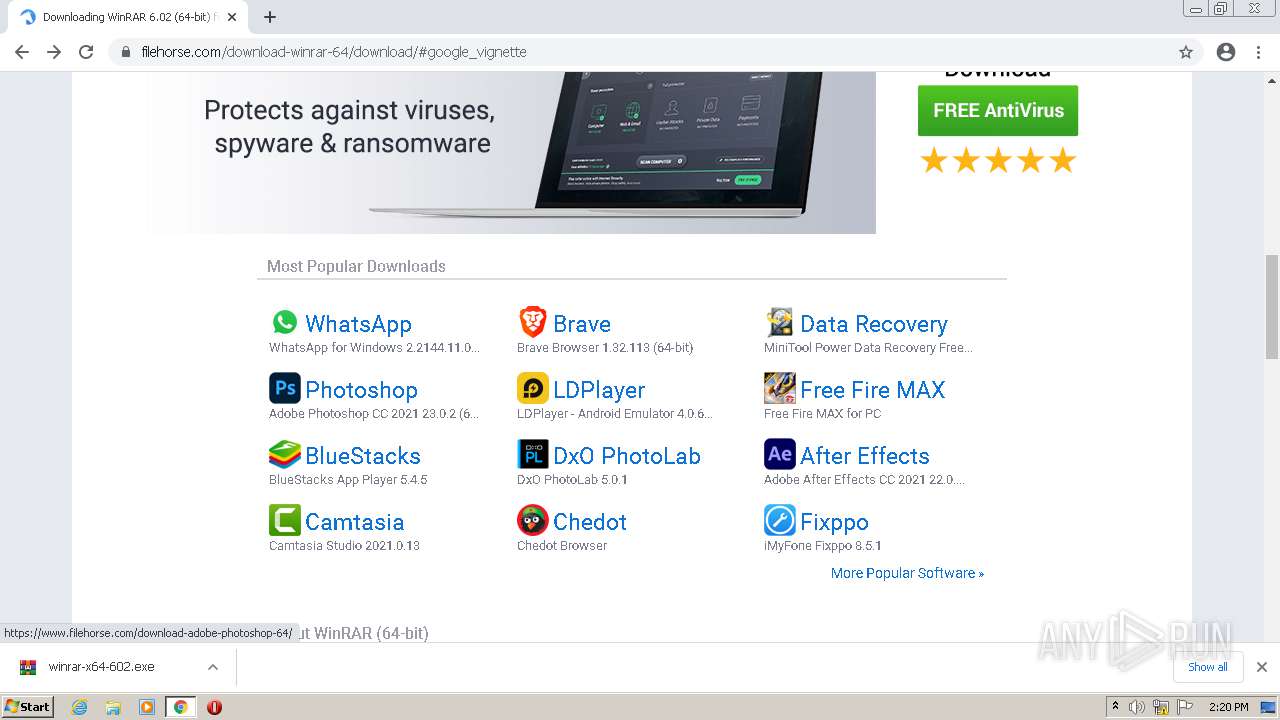
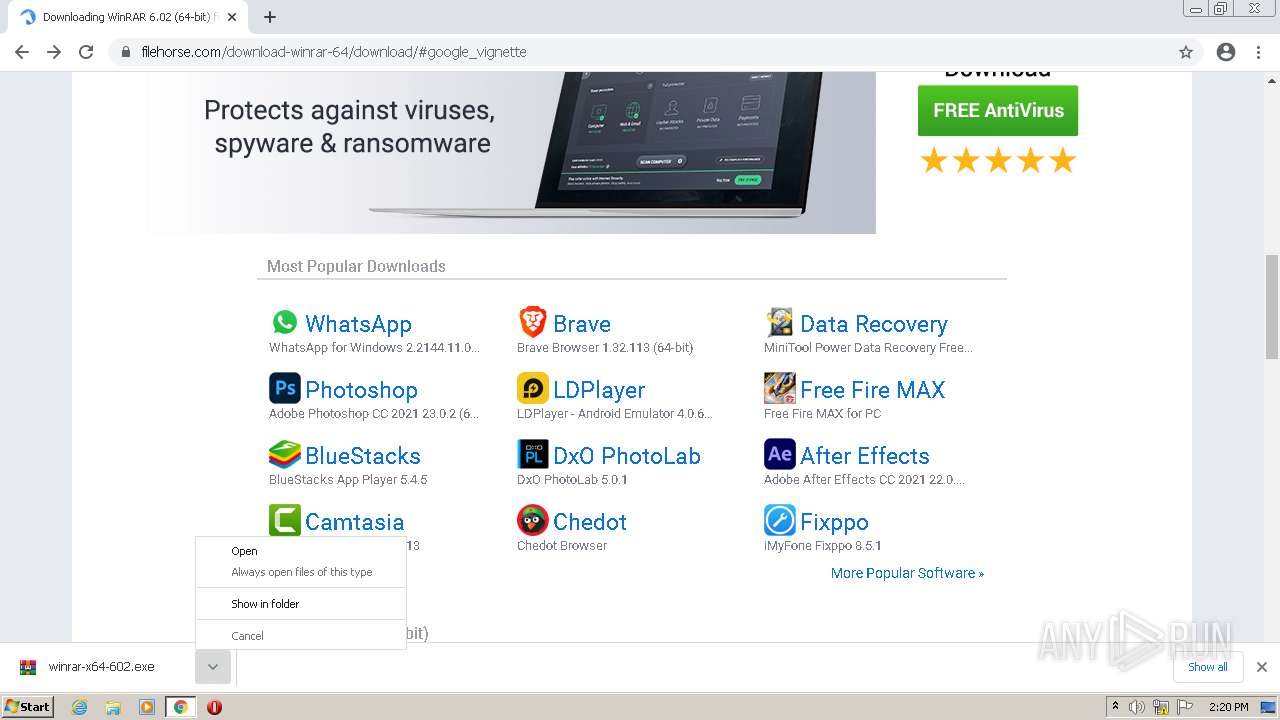
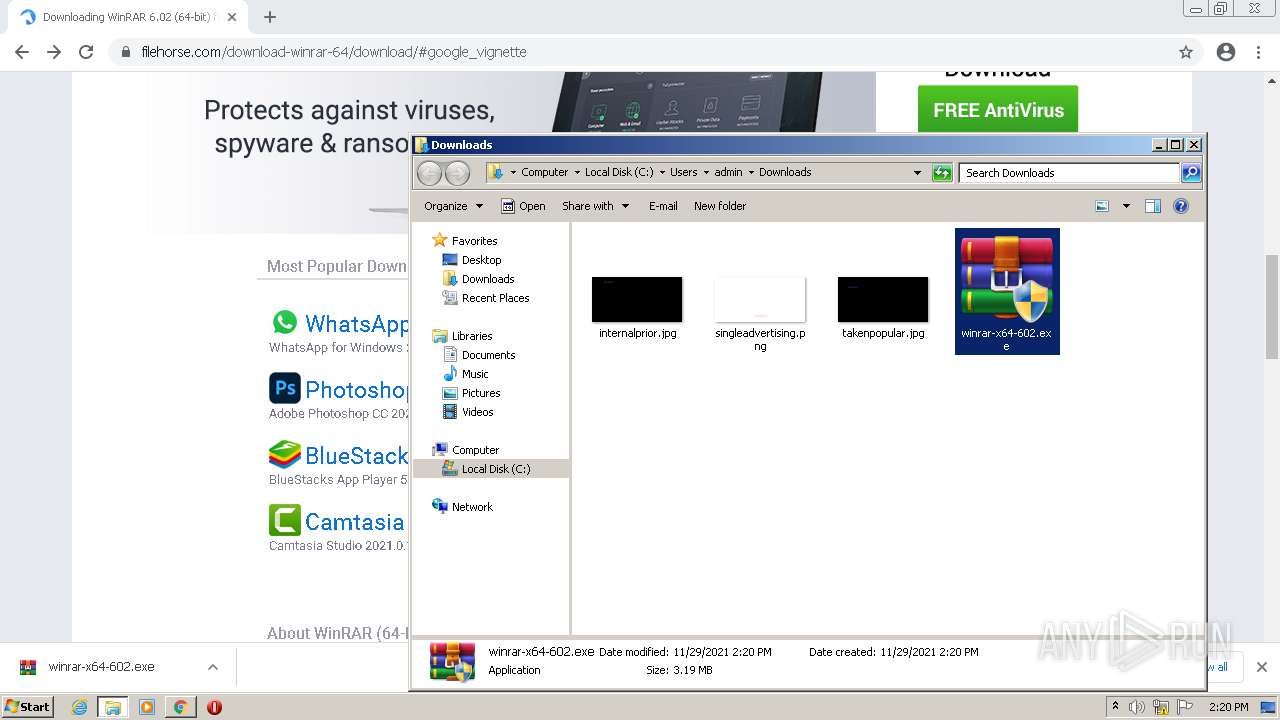
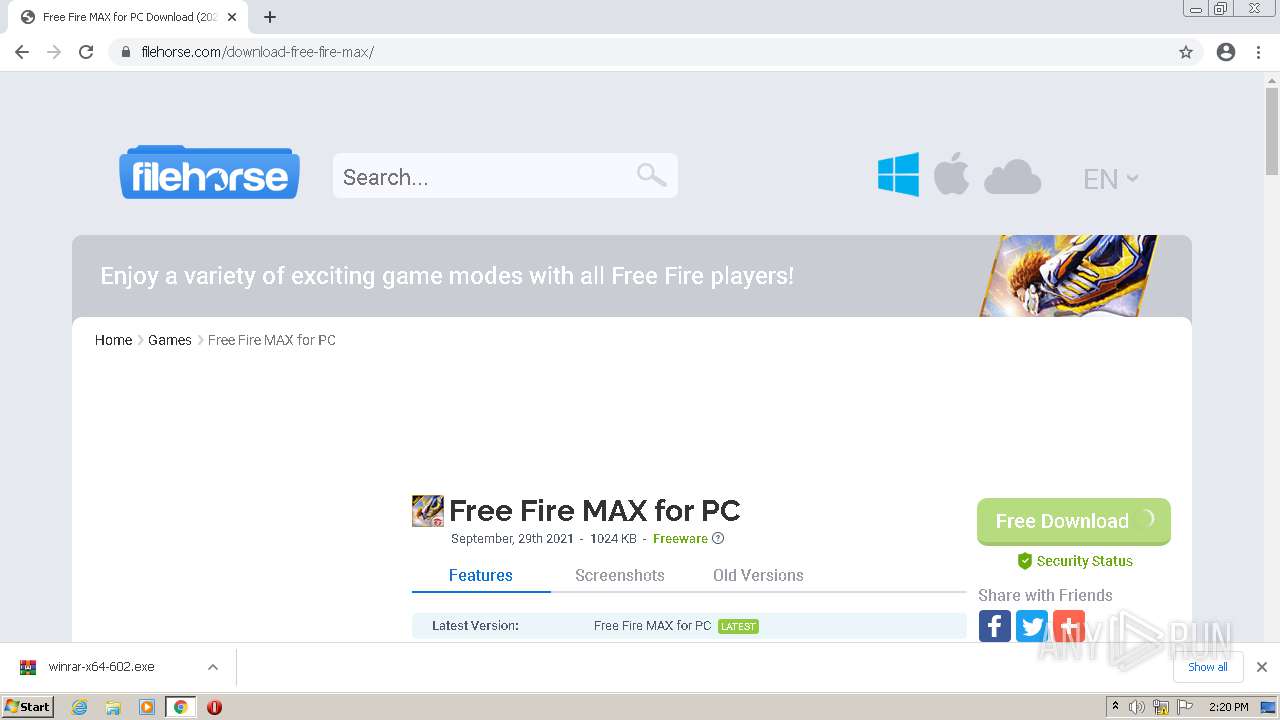
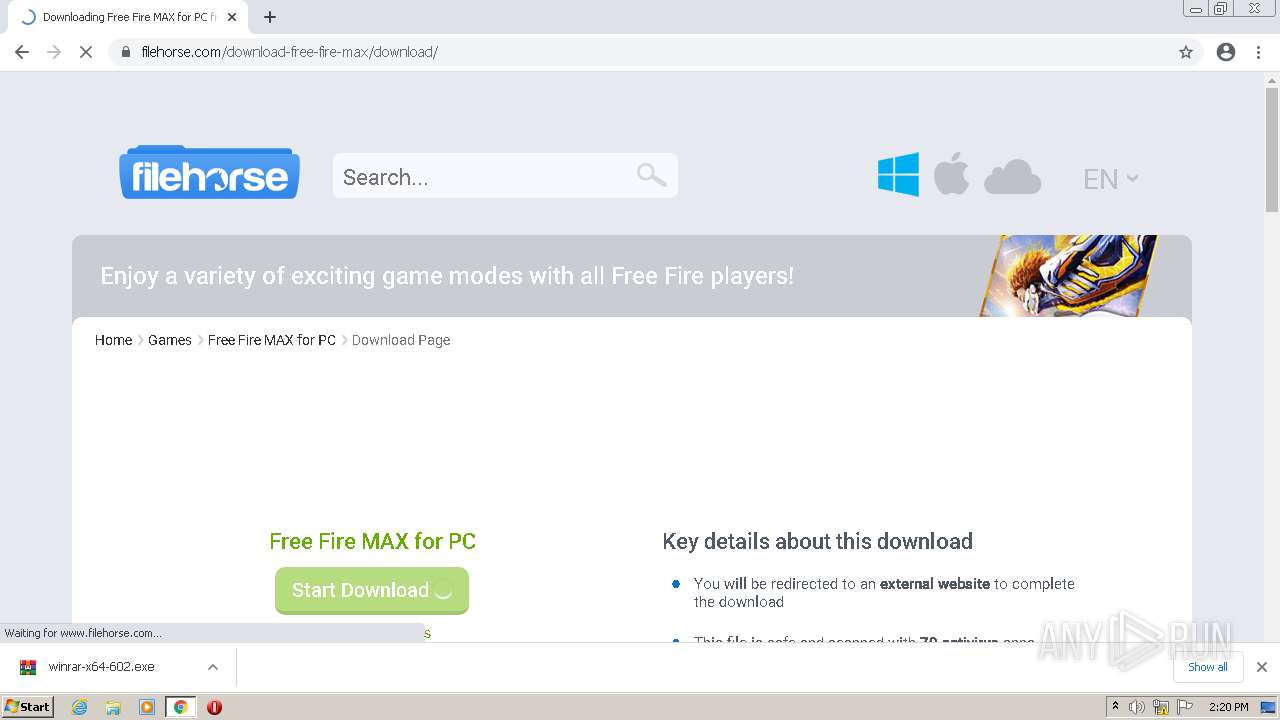
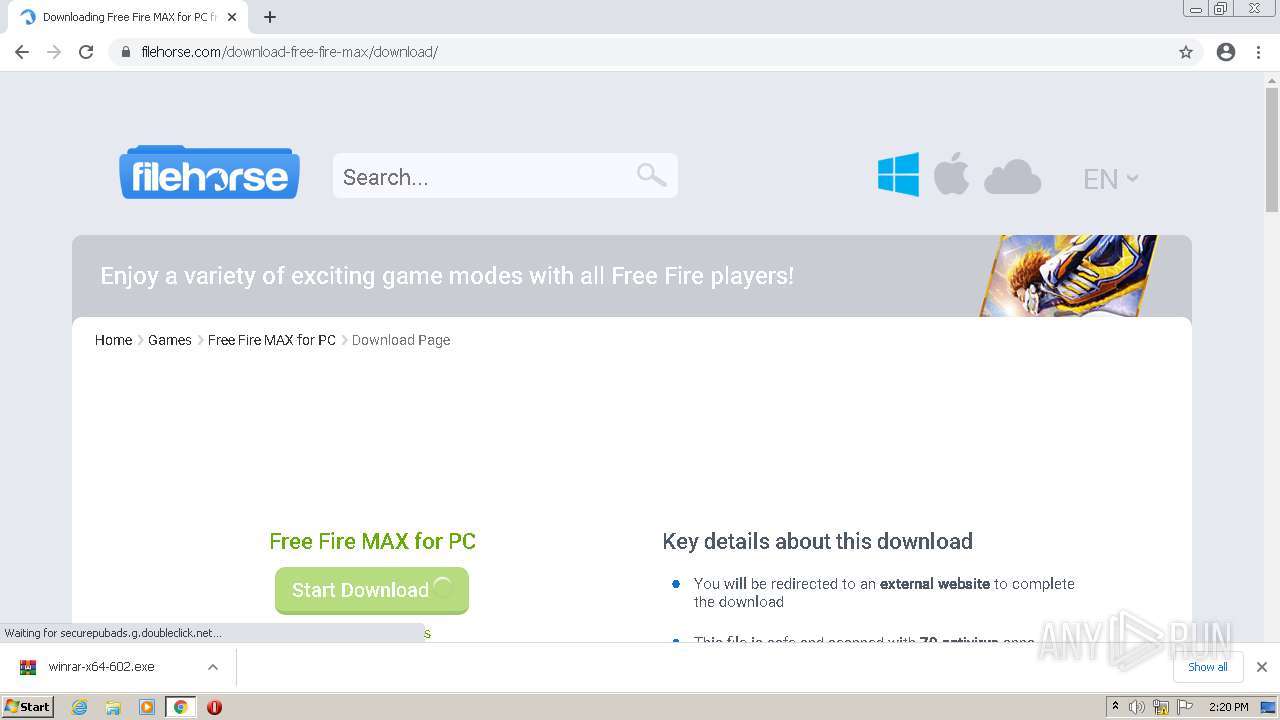
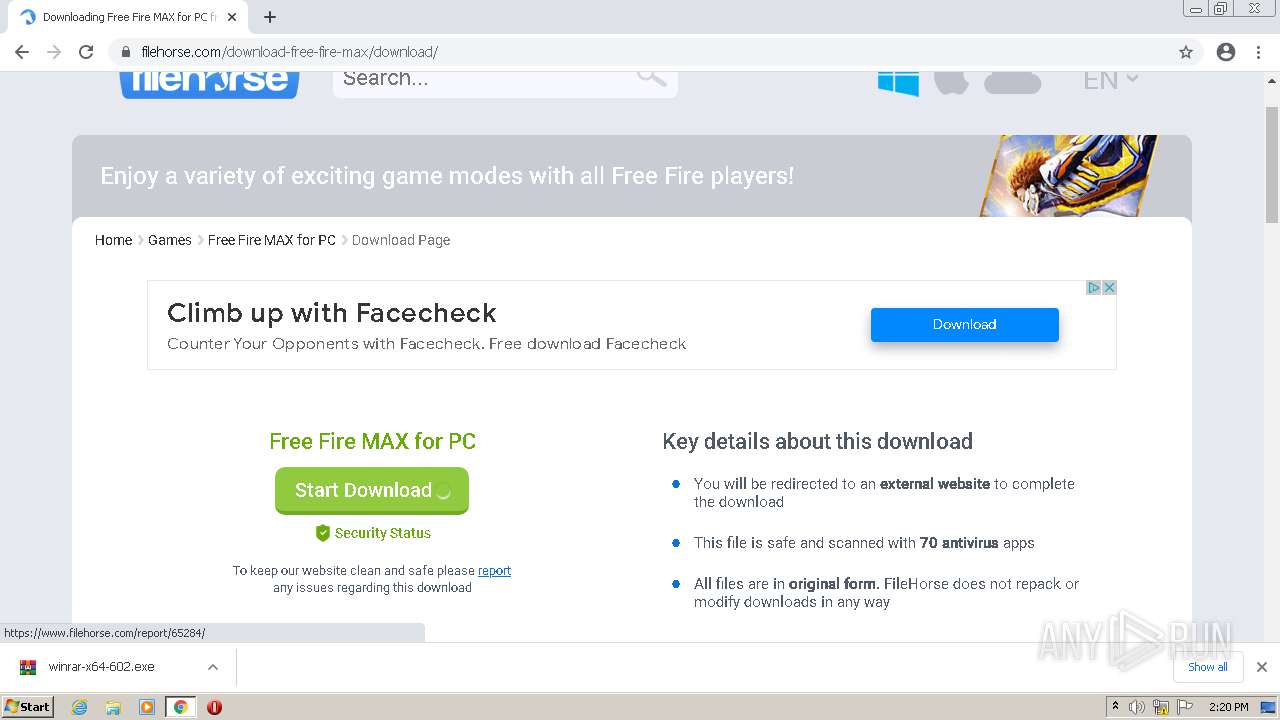
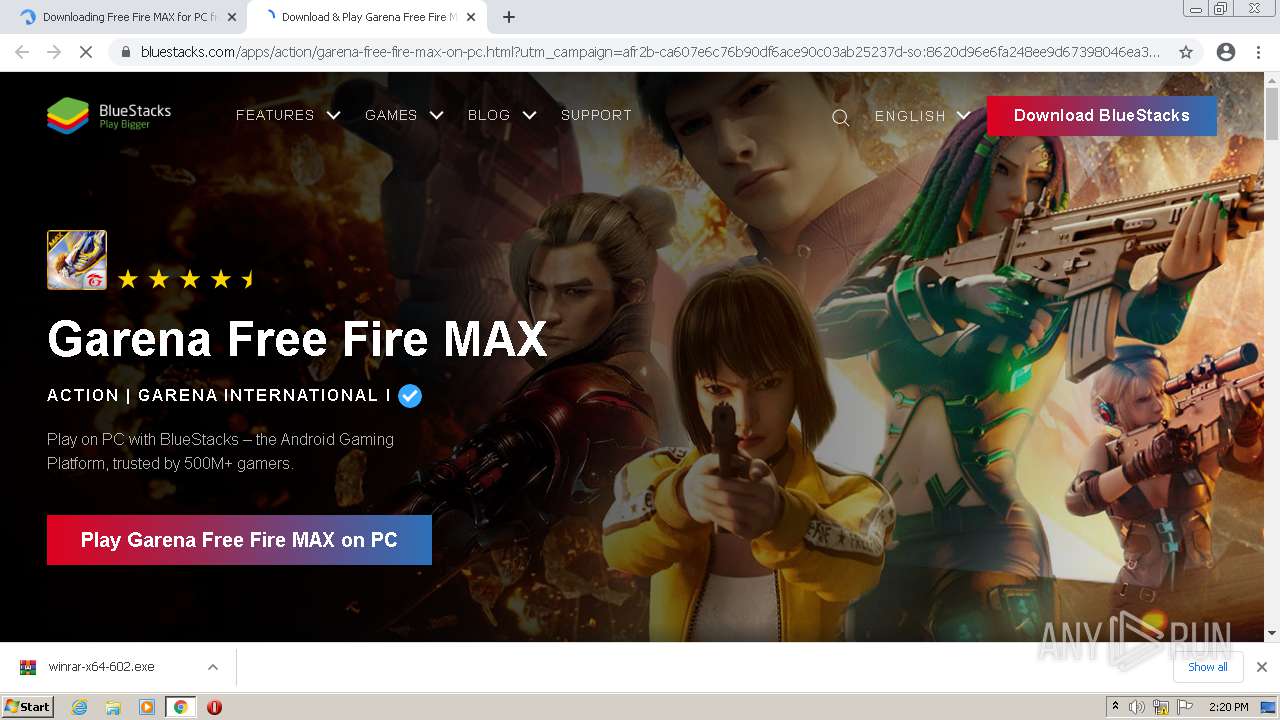
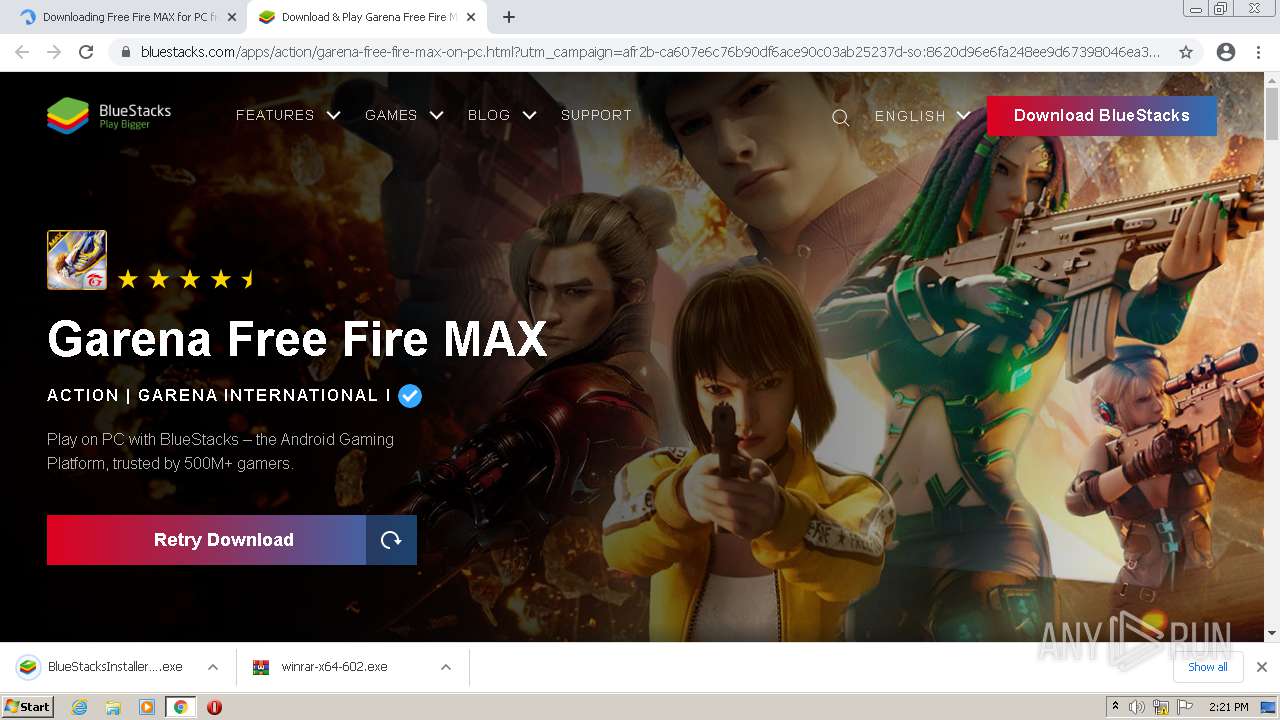
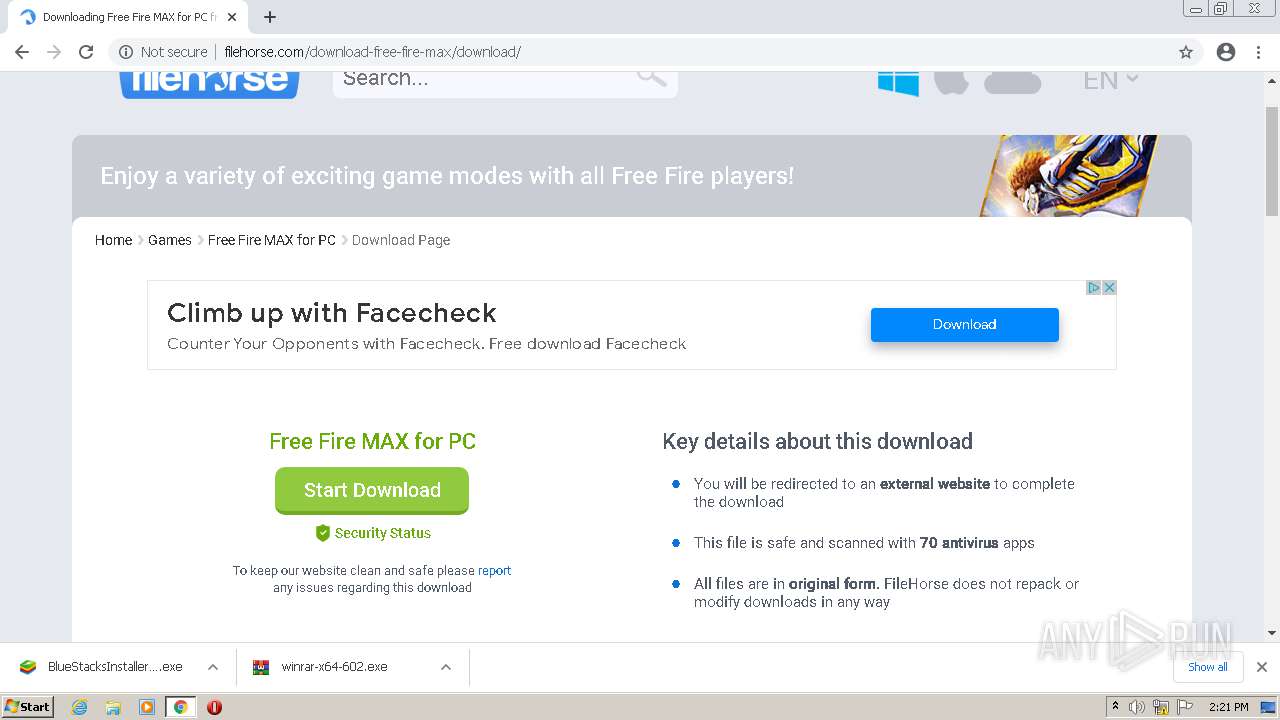
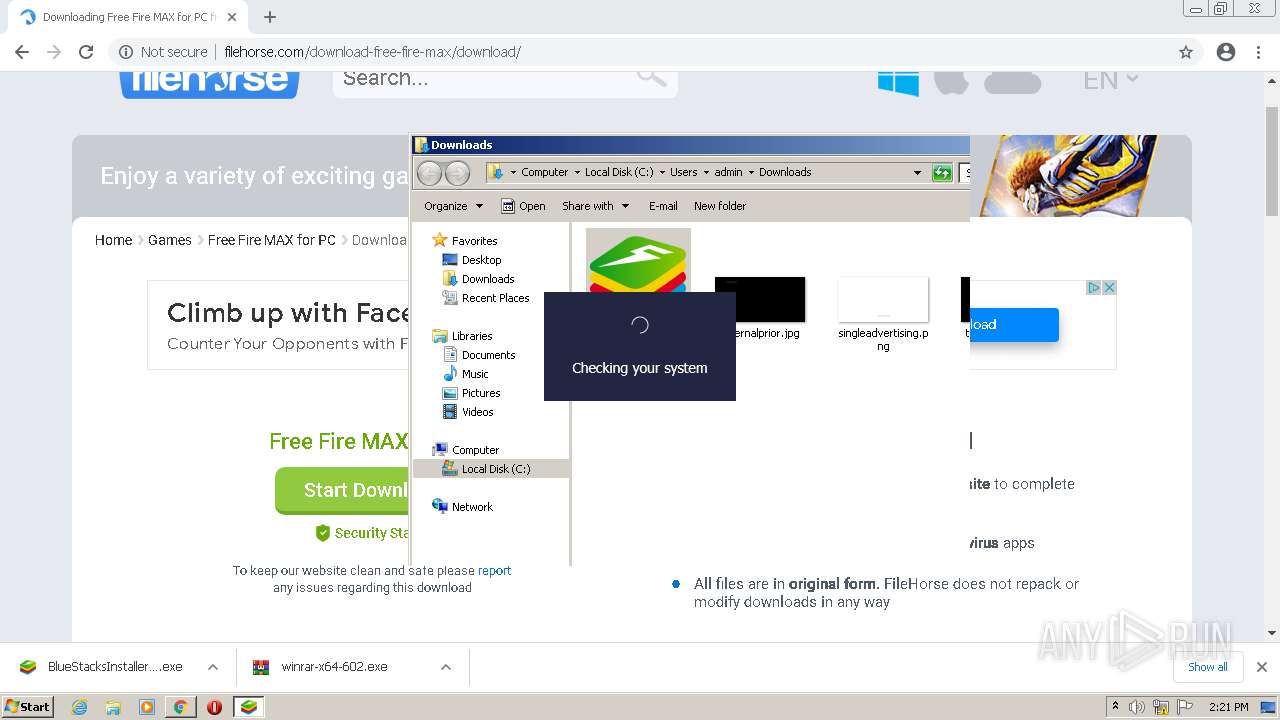
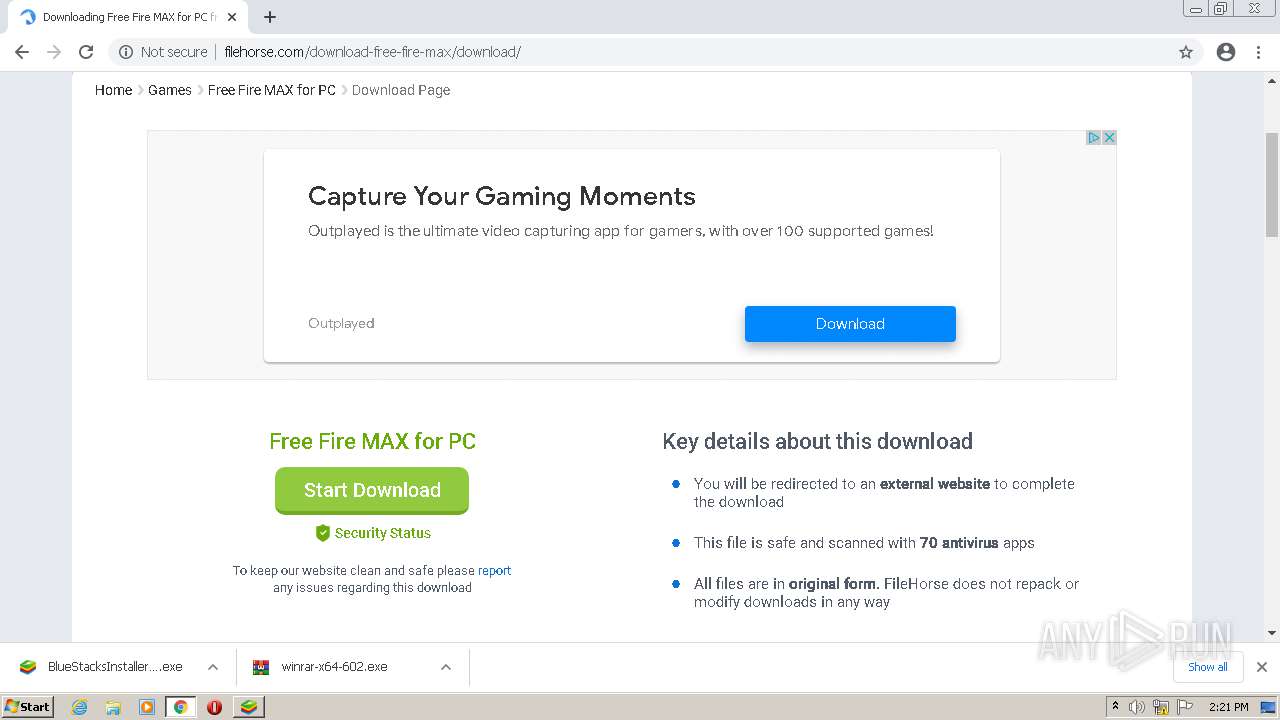
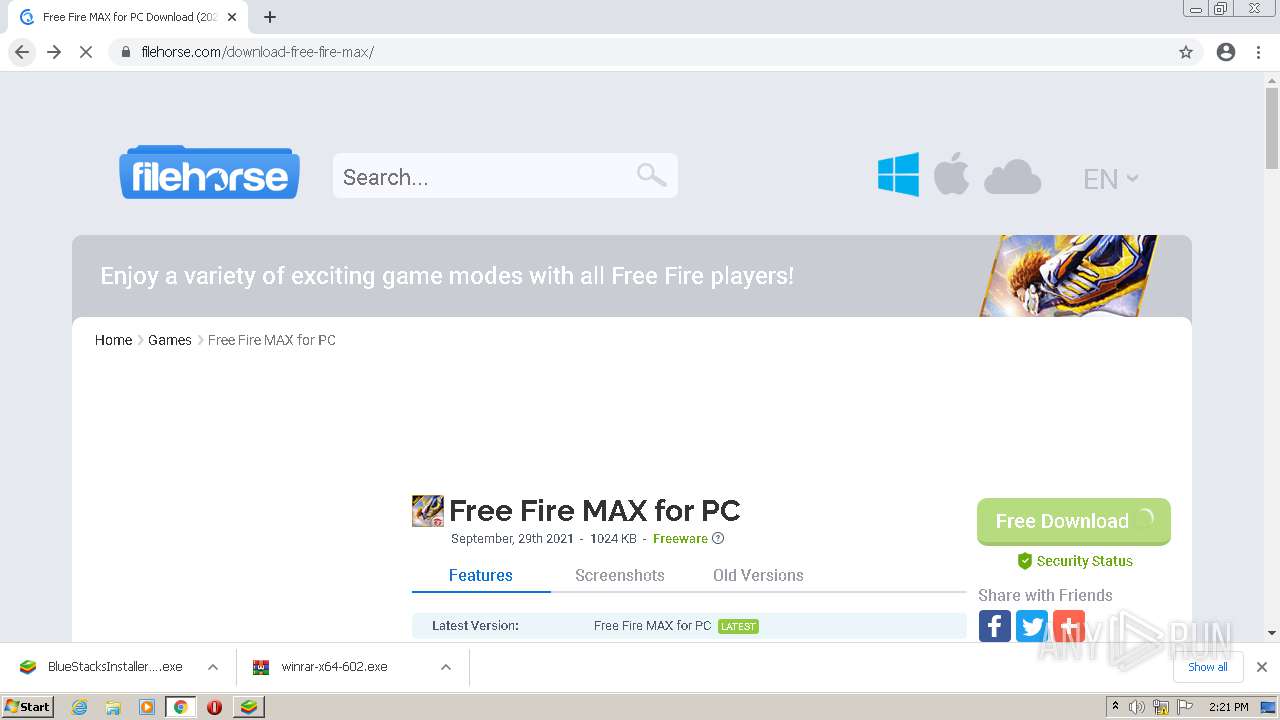
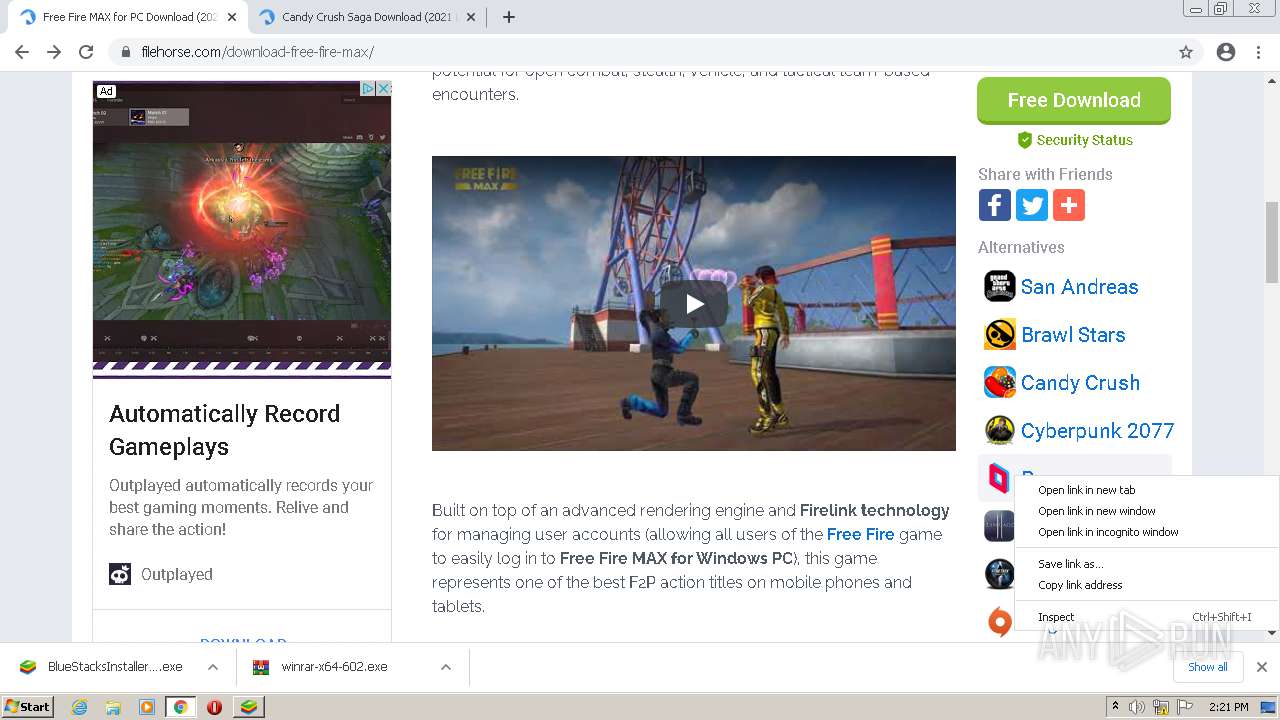
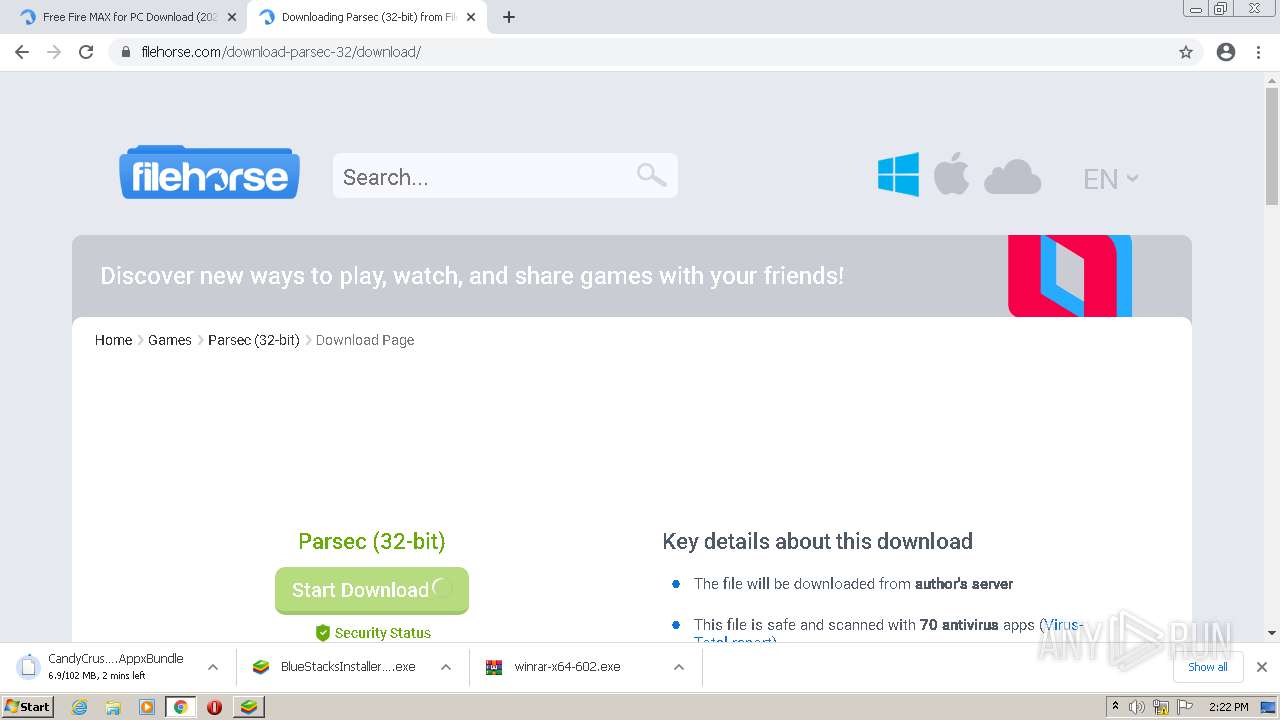
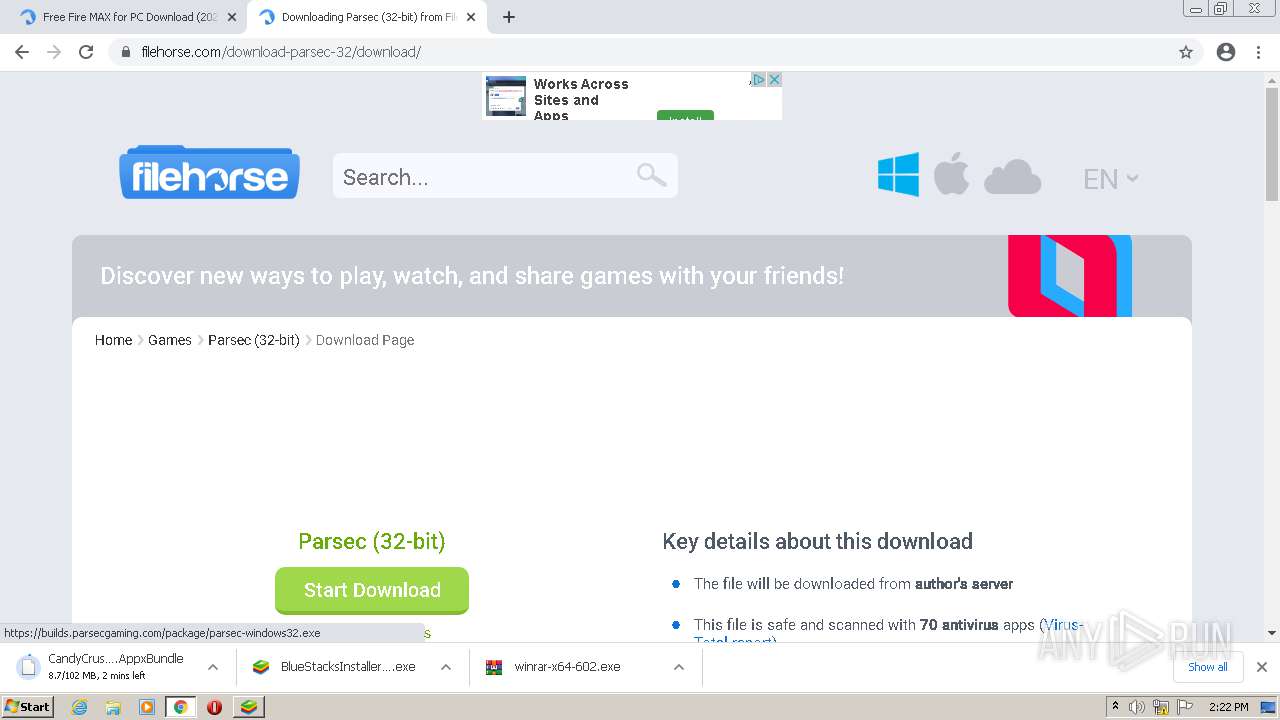
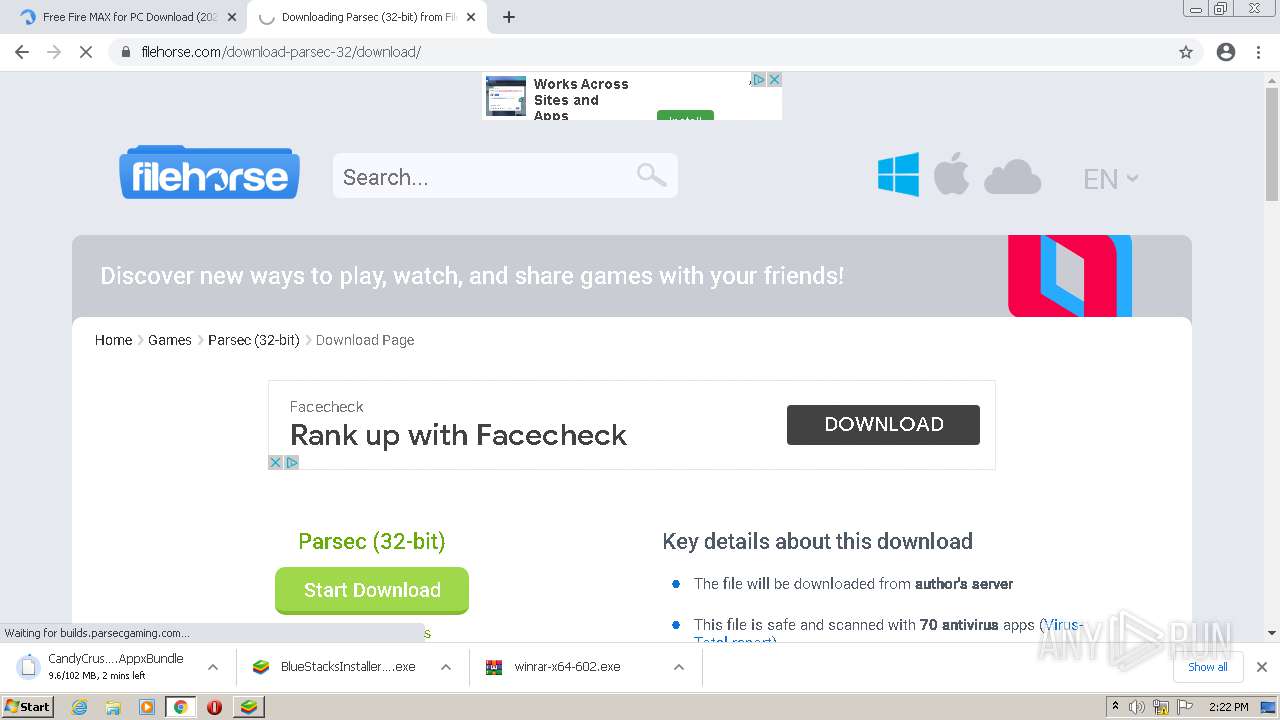
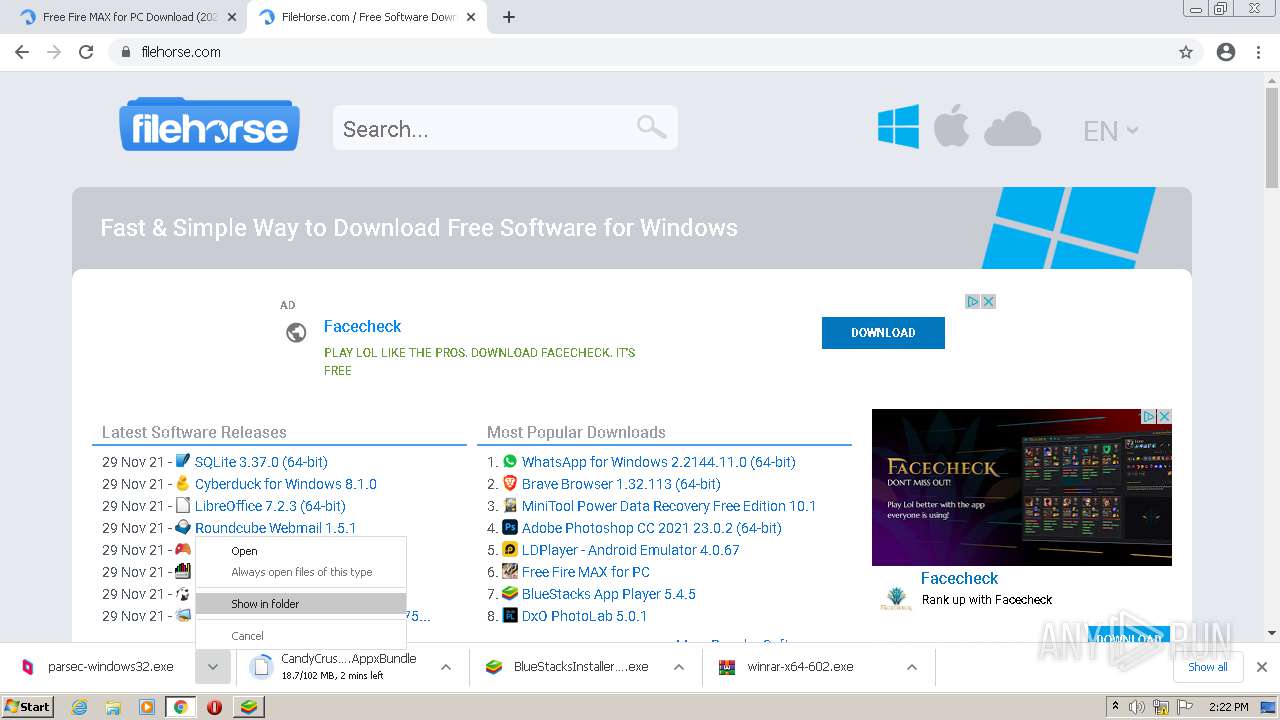
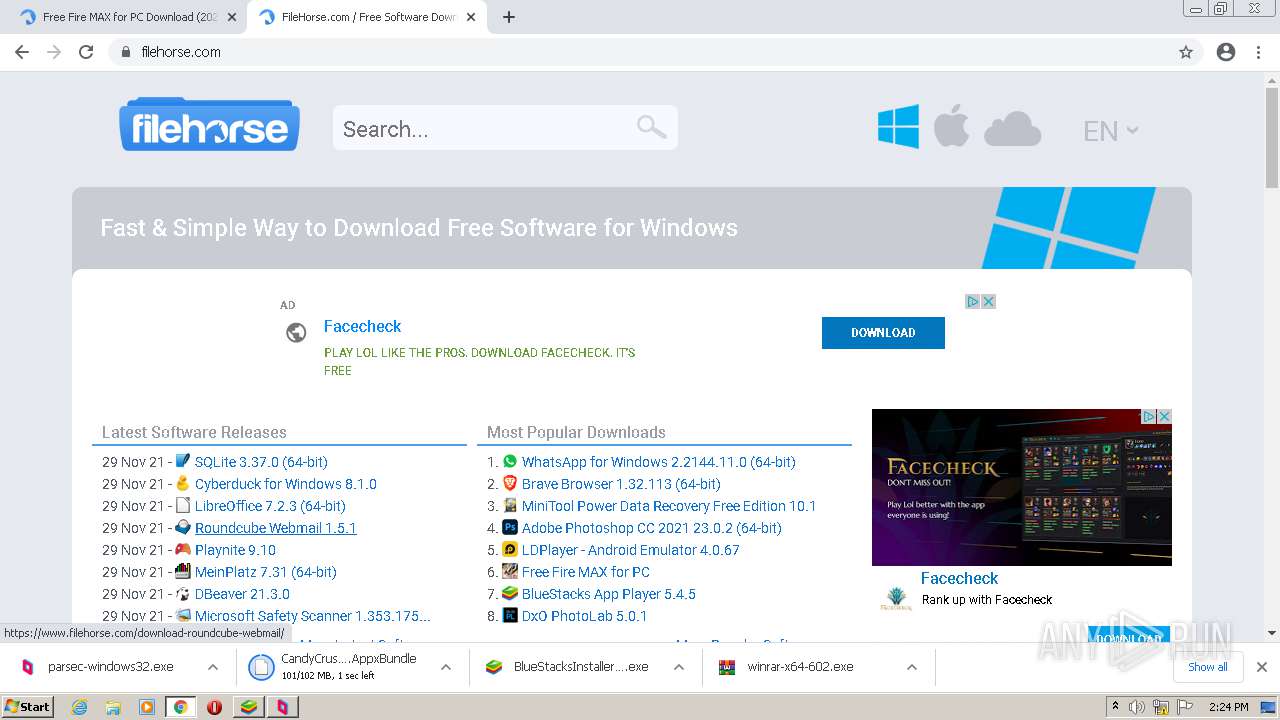
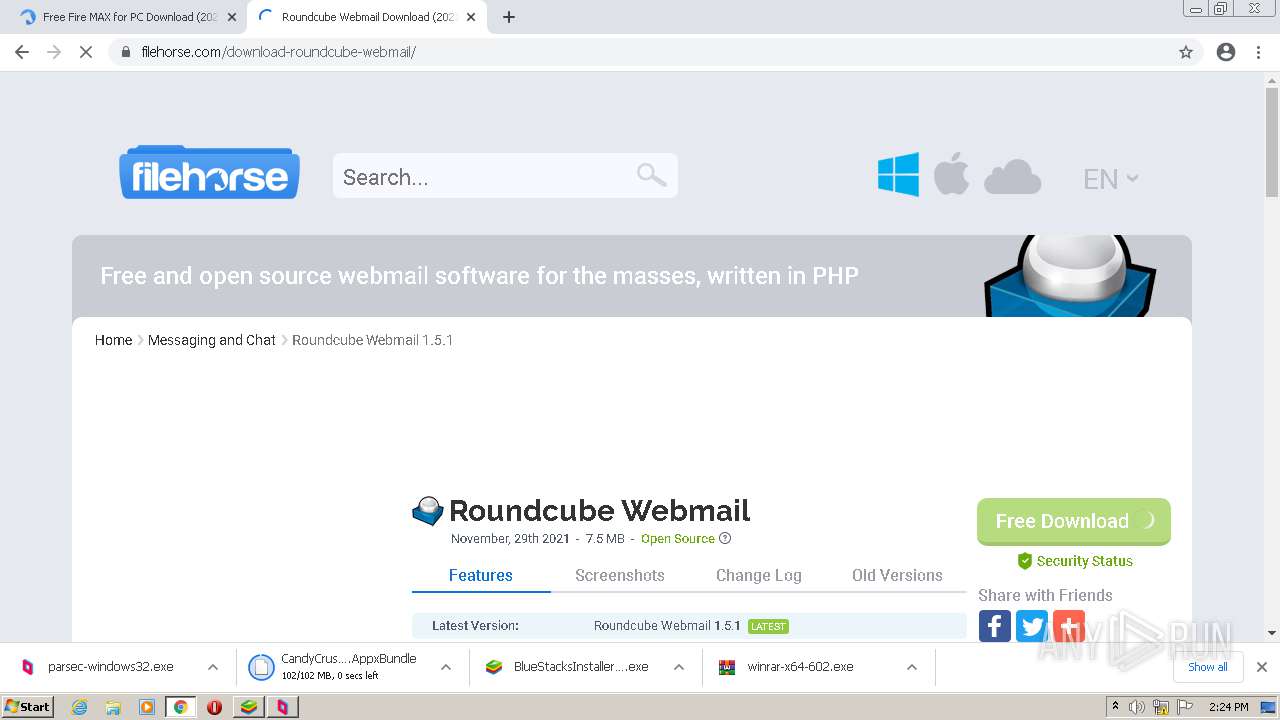
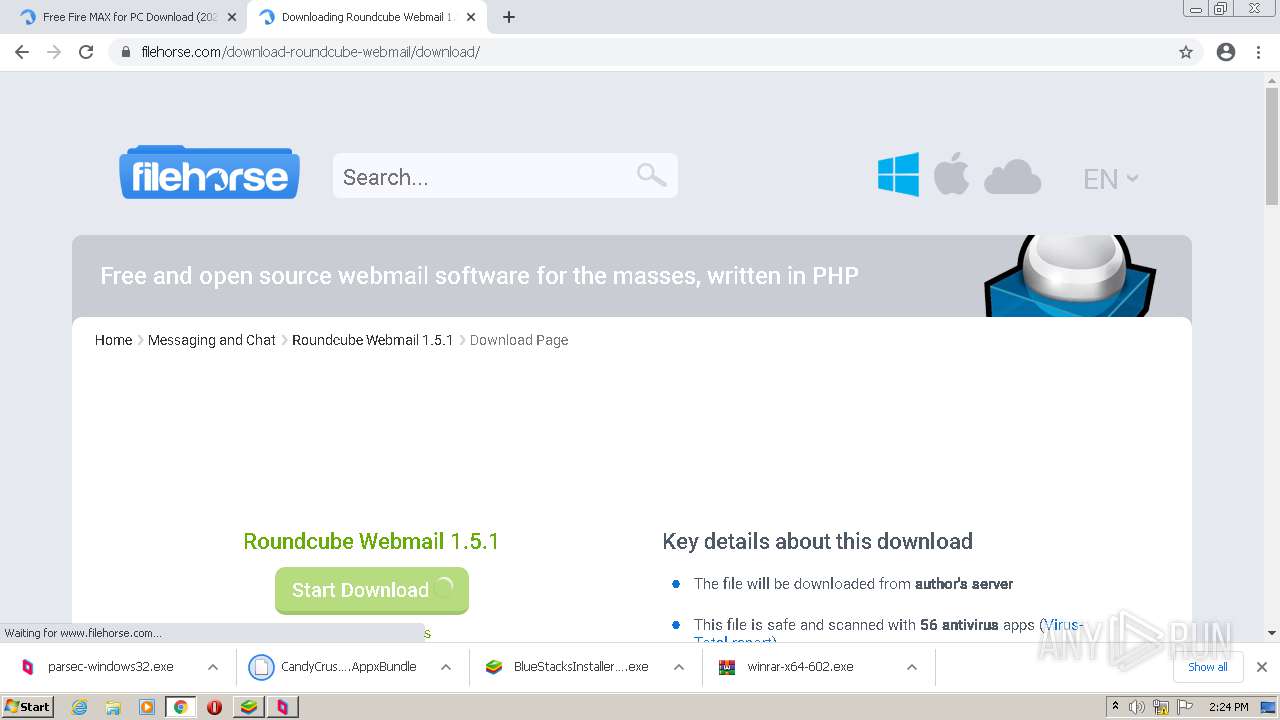
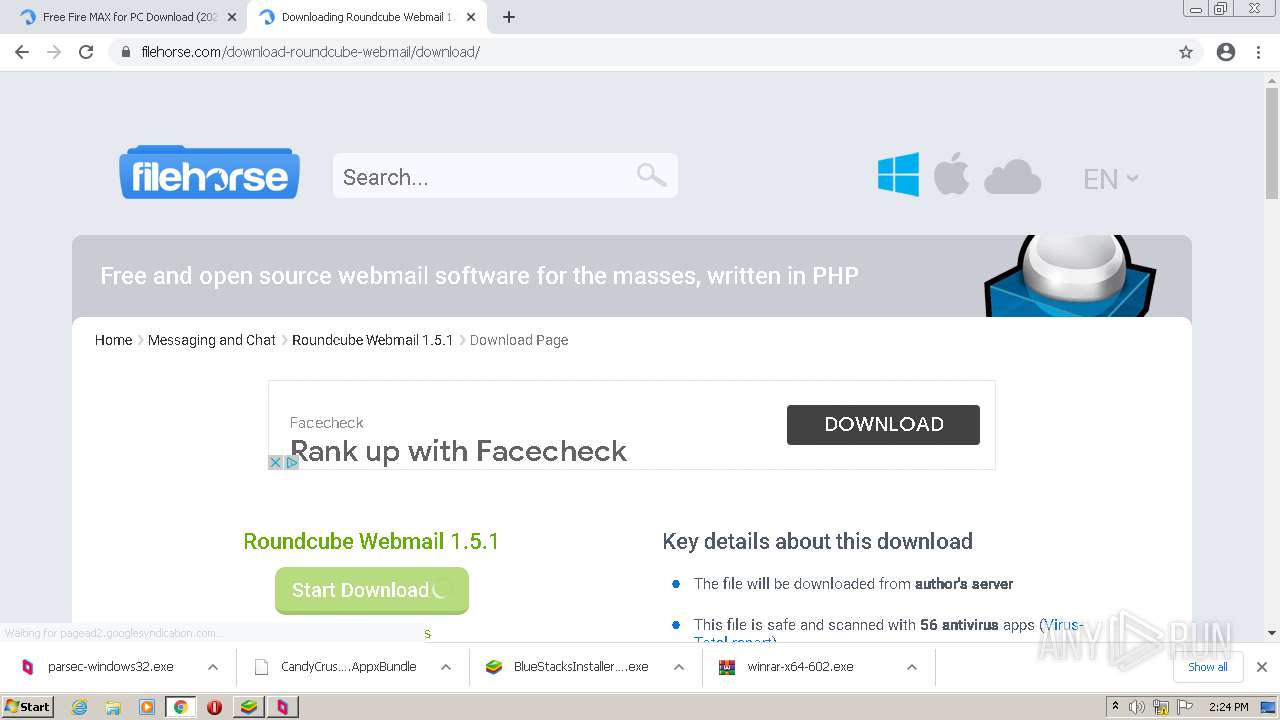
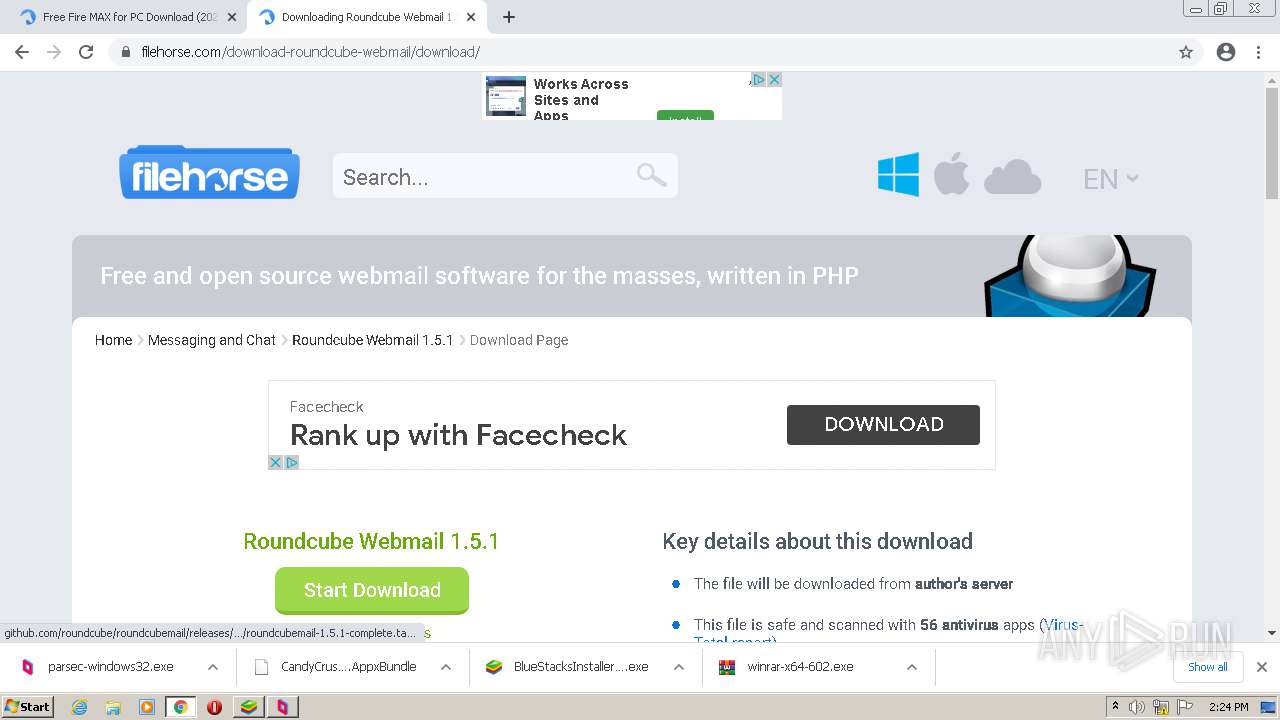
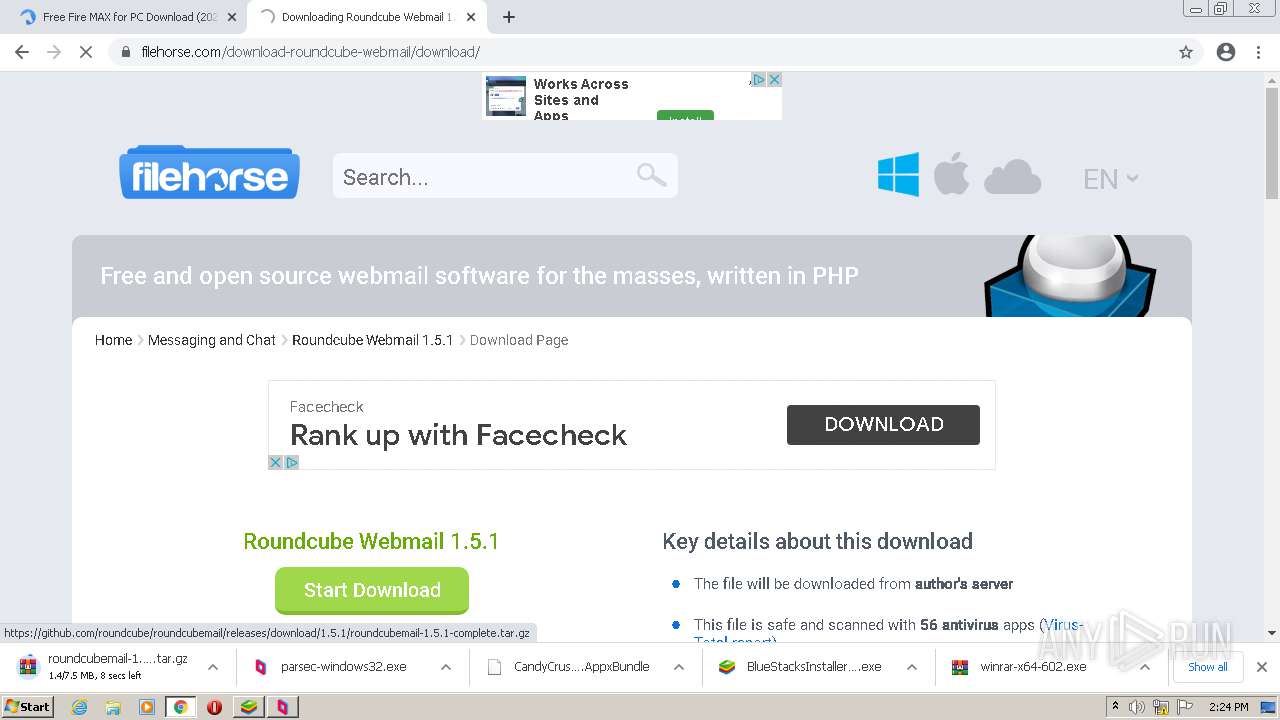
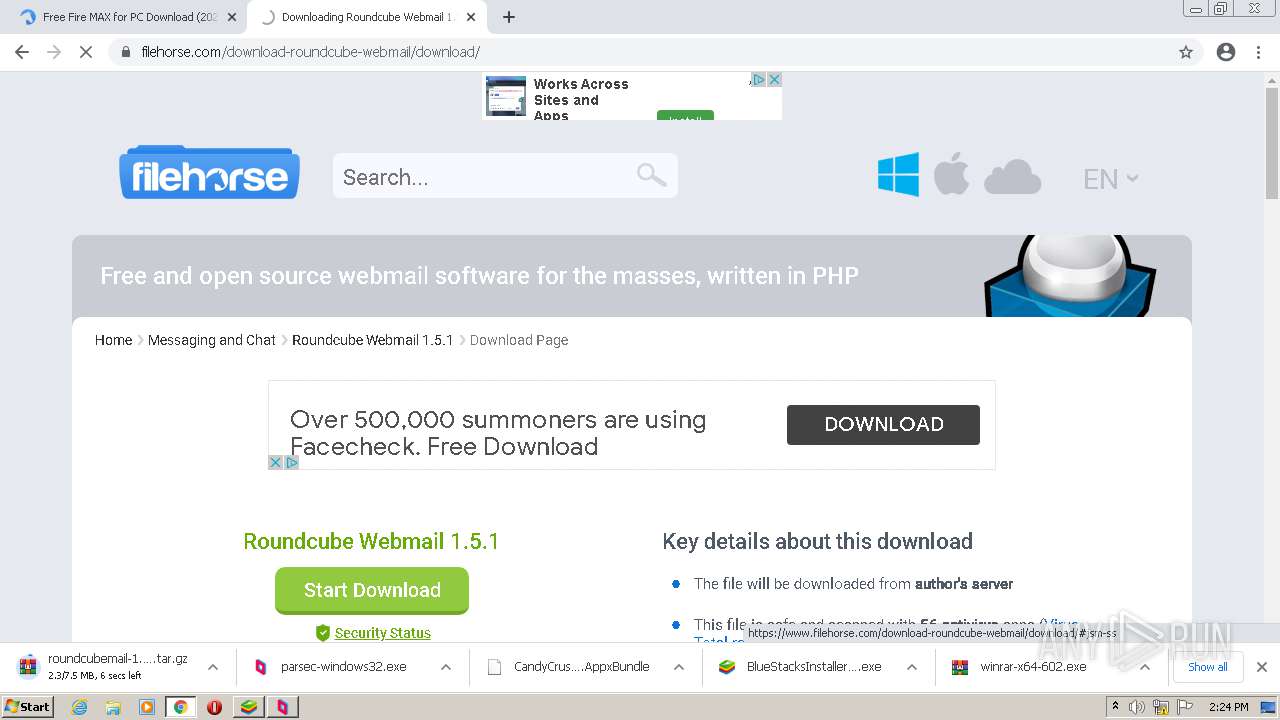
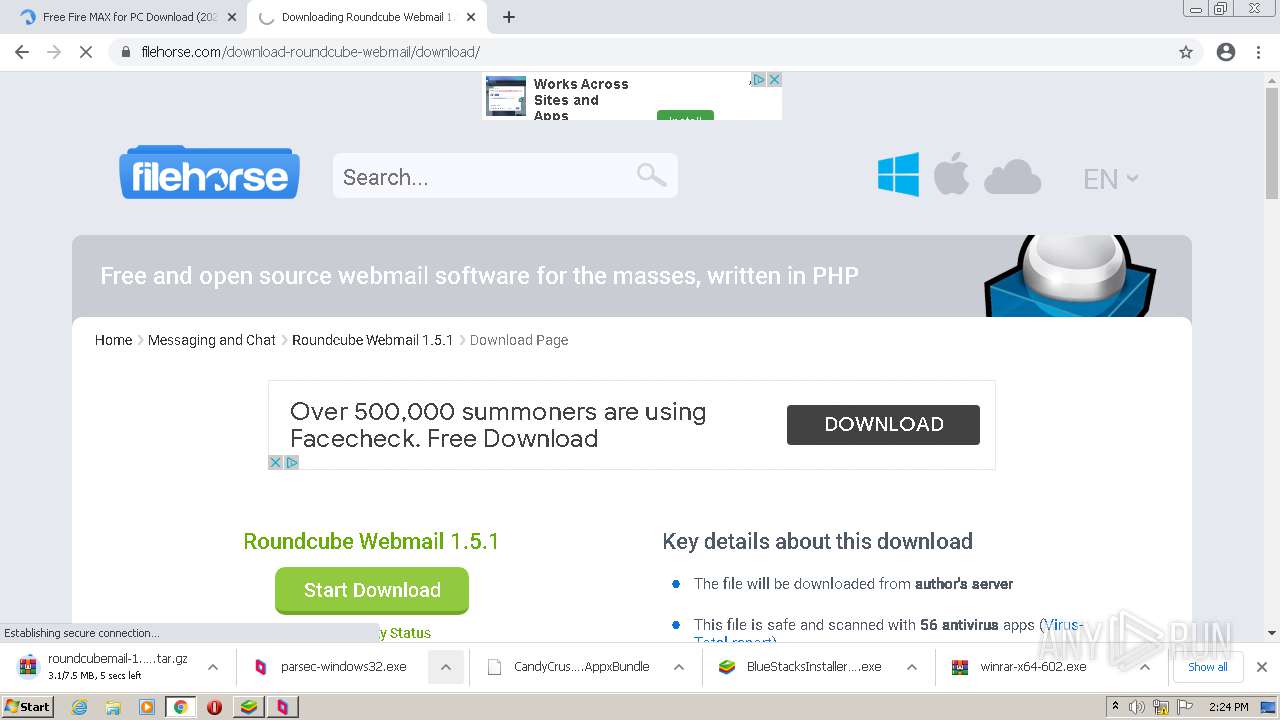
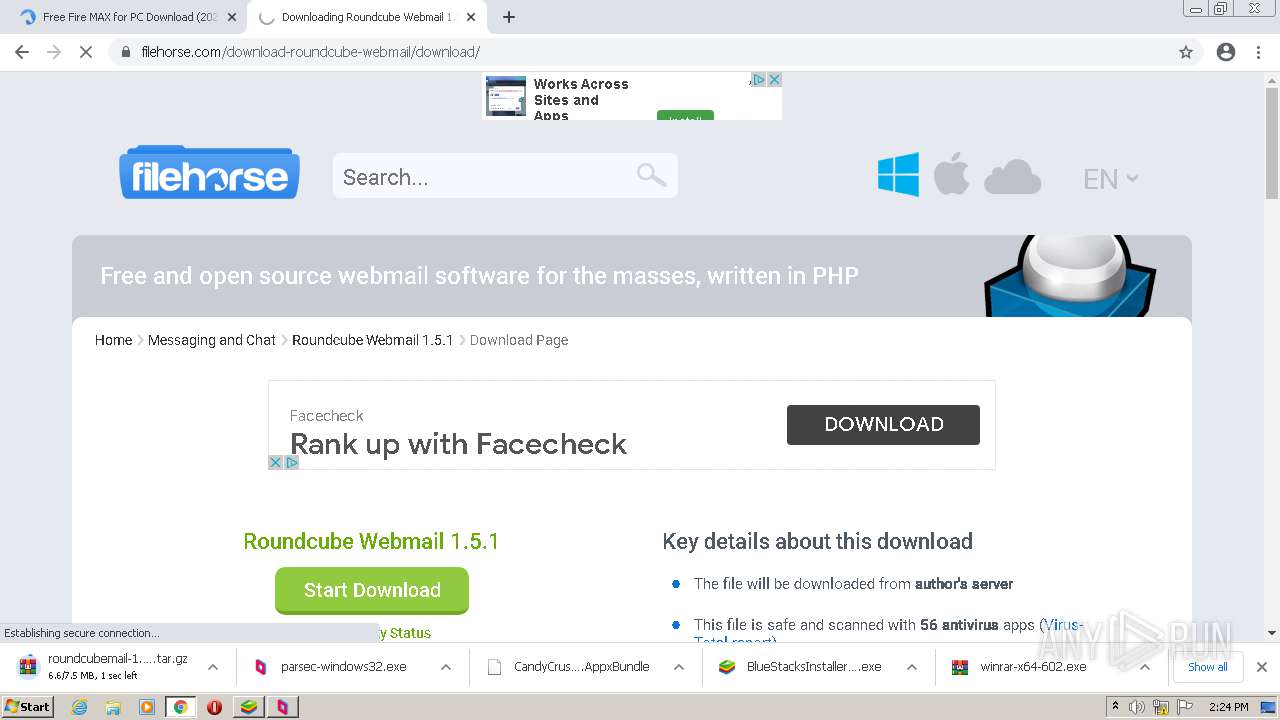
| URL: | https://www.filehorse.com/download-winrar-64/download/ |
| Full analysis: | https://app.any.run/tasks/60103b85-8992-48fc-8ccb-81230e0194b6 |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2021, 14:19:39 |
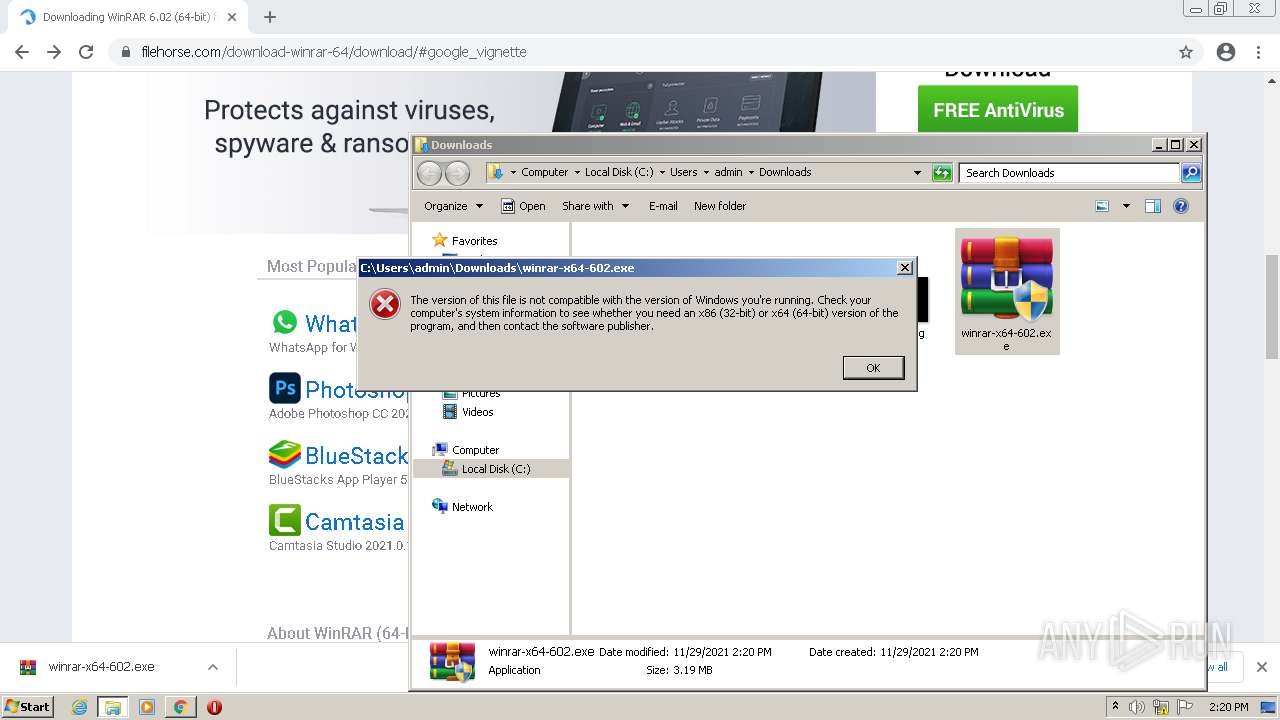
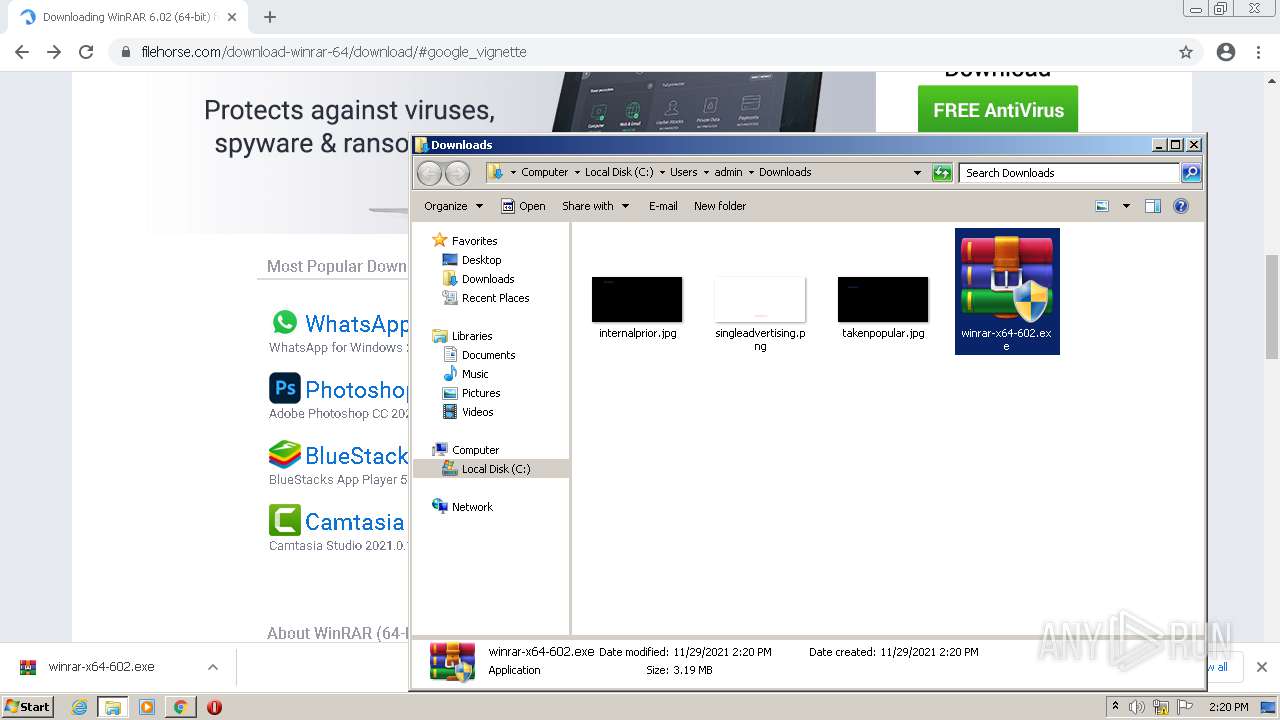
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4771F24A90C5A46C294FE5E2F1C6133F |
| SHA1: | E69C5E734C10C5A8CF42E3E250738F0D64AF0F97 |
| SHA256: | F5CD38996CD99AEA14EAEADBC85A562FDF2F14AC3B2153CD19C8C0A17E64FFFE |
| SSDEEP: | 3:N8DSLQiKbGGBKJSMj+u8kn:2OLQpbGNcMjX |
MALICIOUS
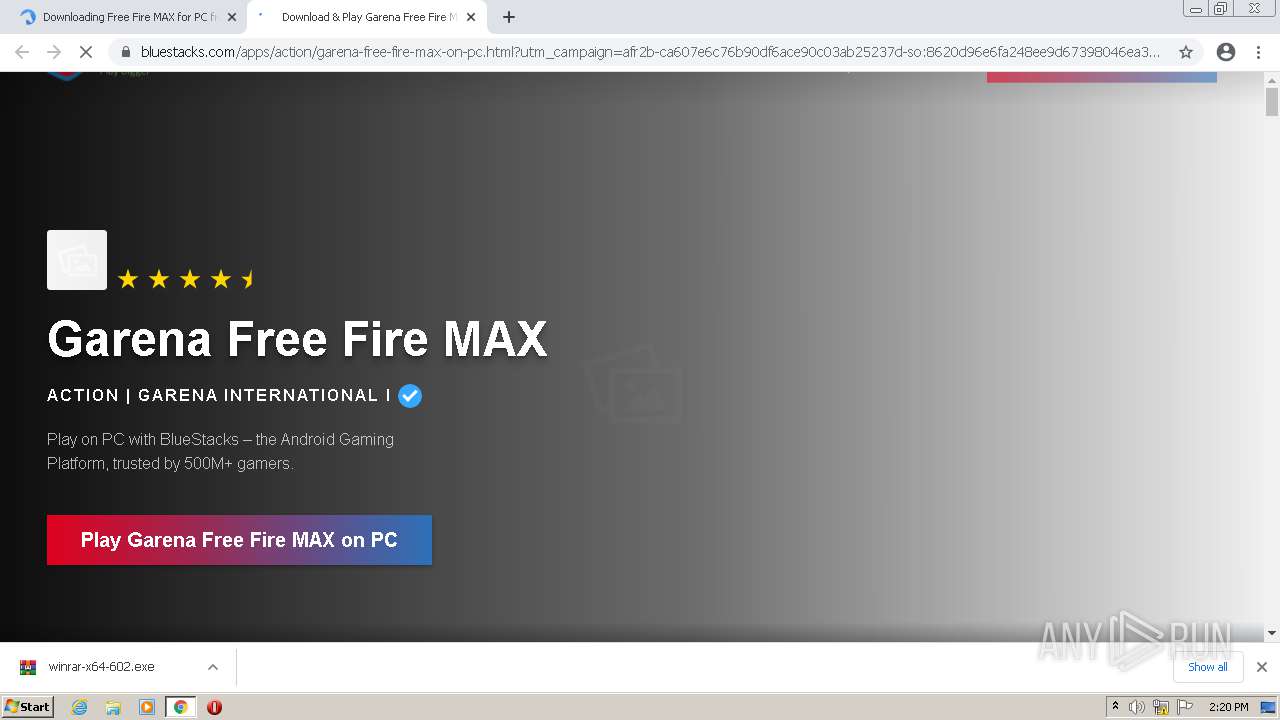
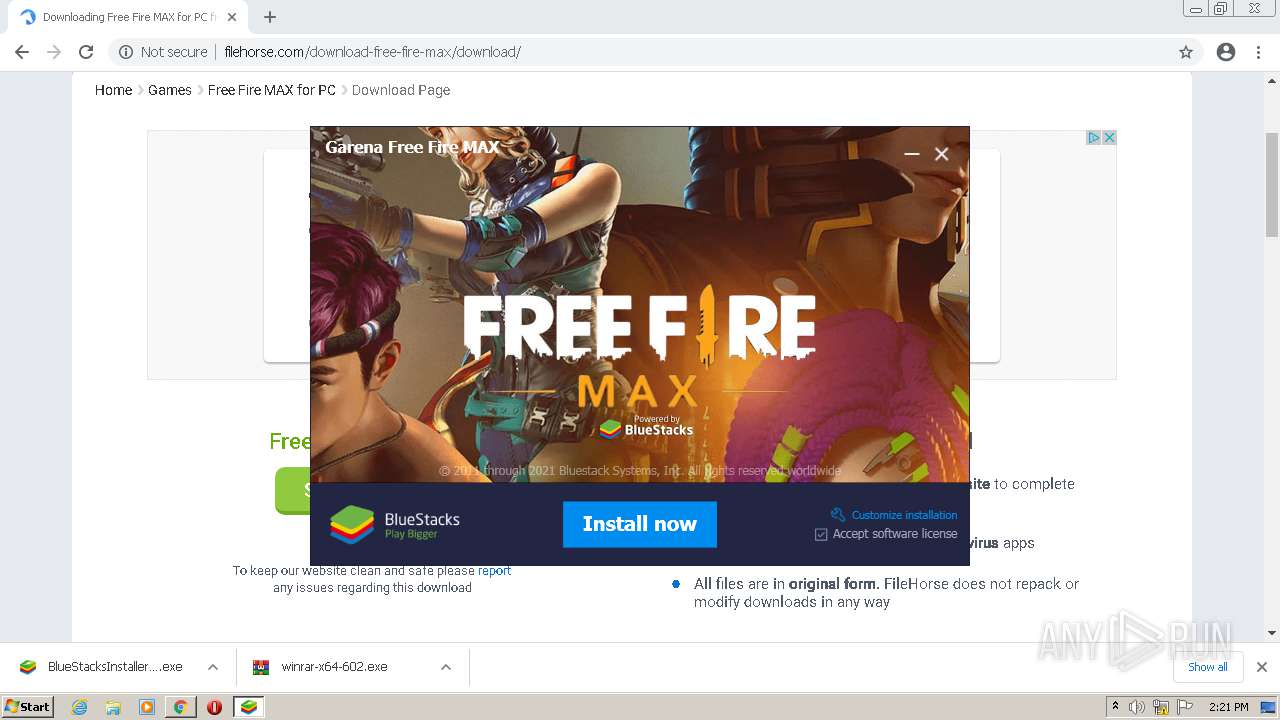
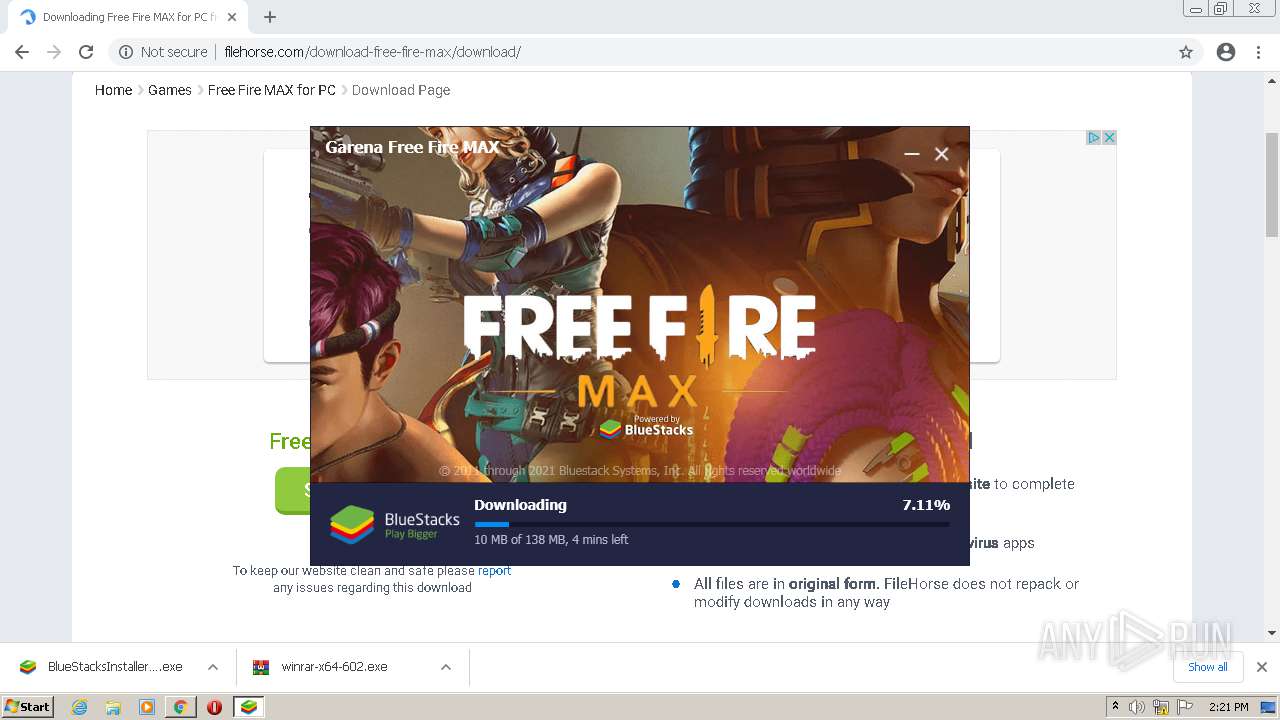
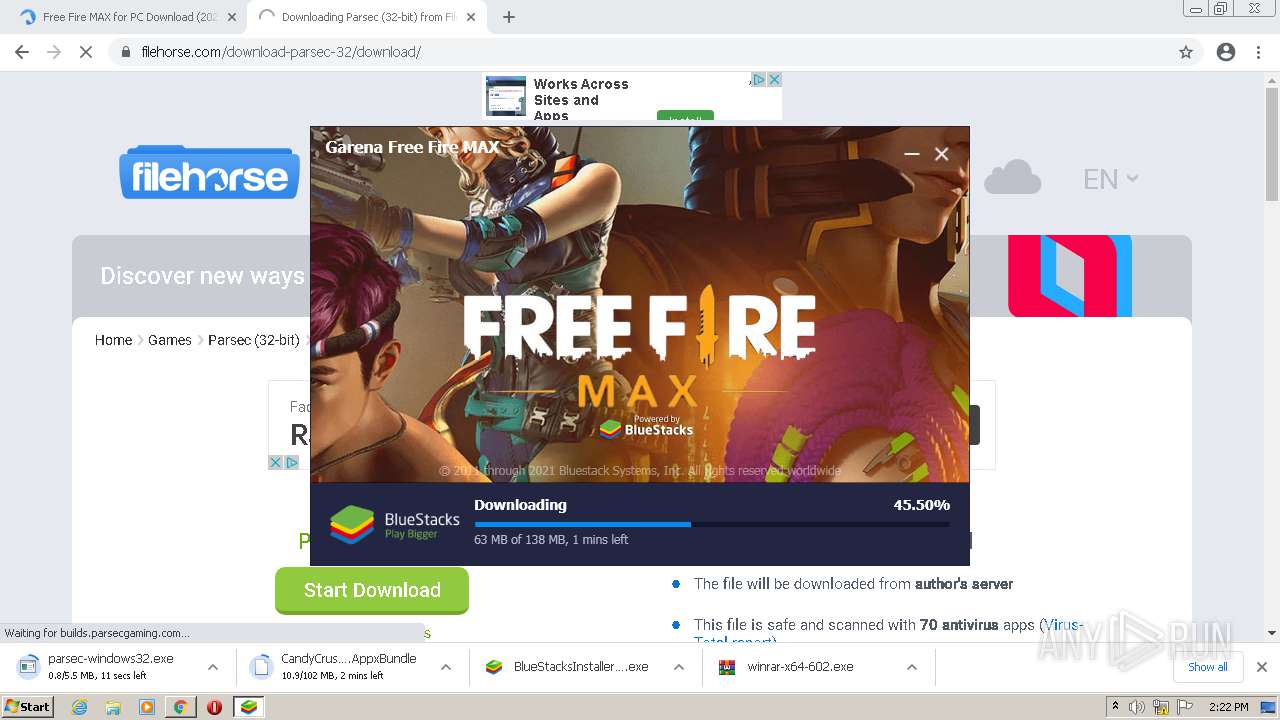
Application was dropped or rewritten from another process
- BlueStacksInstaller_5.4.50.1009_native_ab0d65789ca9f2025a1773d795bb21f7_0_R2FyZW5hIEZyZWUgRmlyZSBNQVg=.exe (PID: 516)
- BlueStacksInstaller.exe (PID: 3860)
- BlueStacksInstaller.exe (PID: 1992)
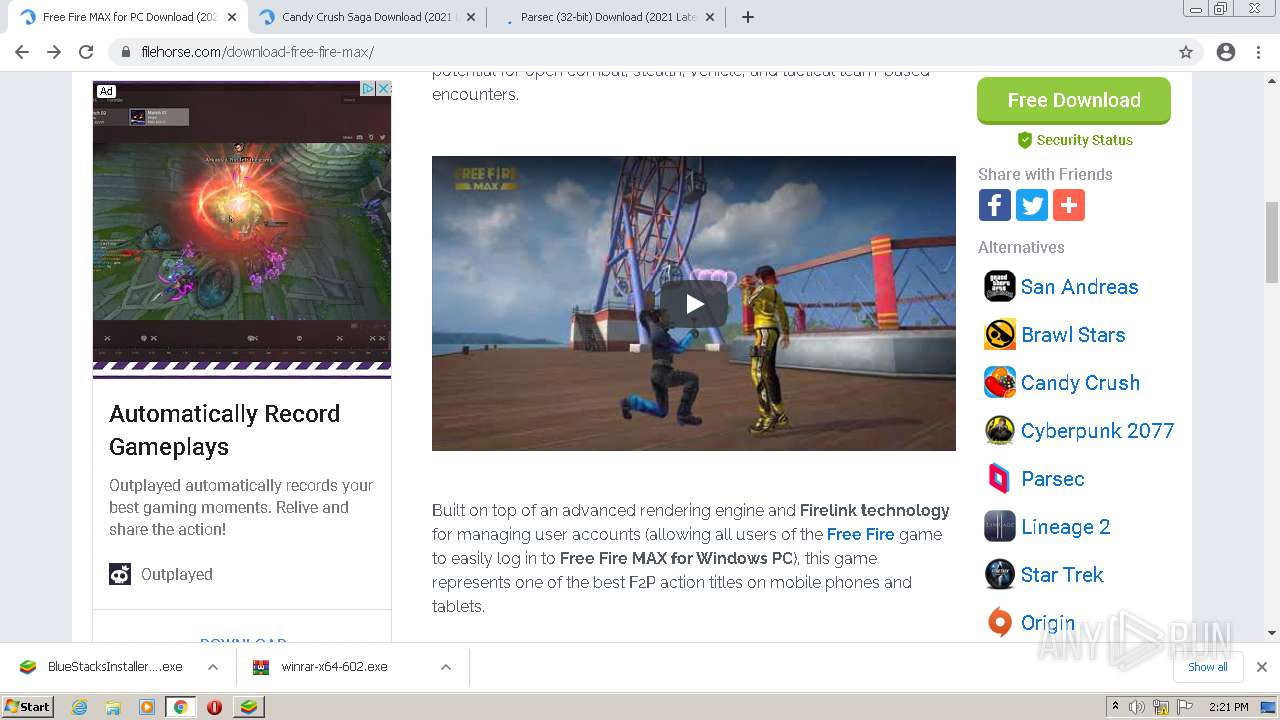
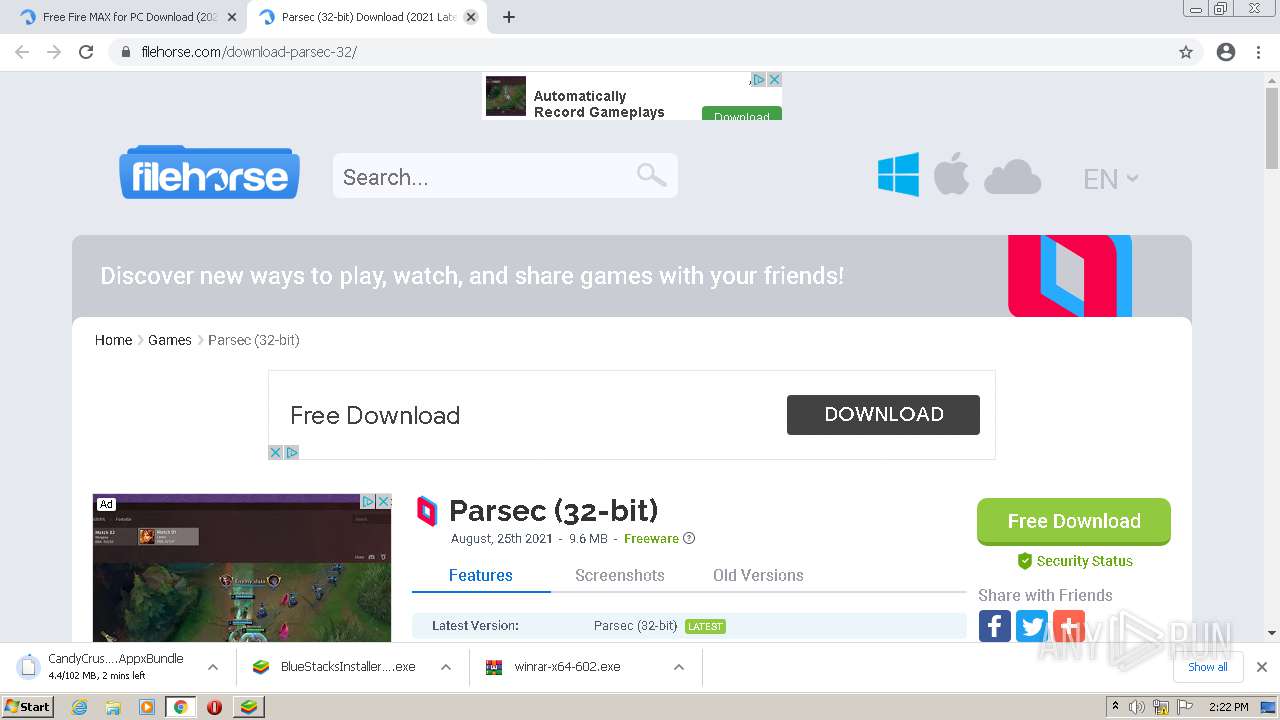
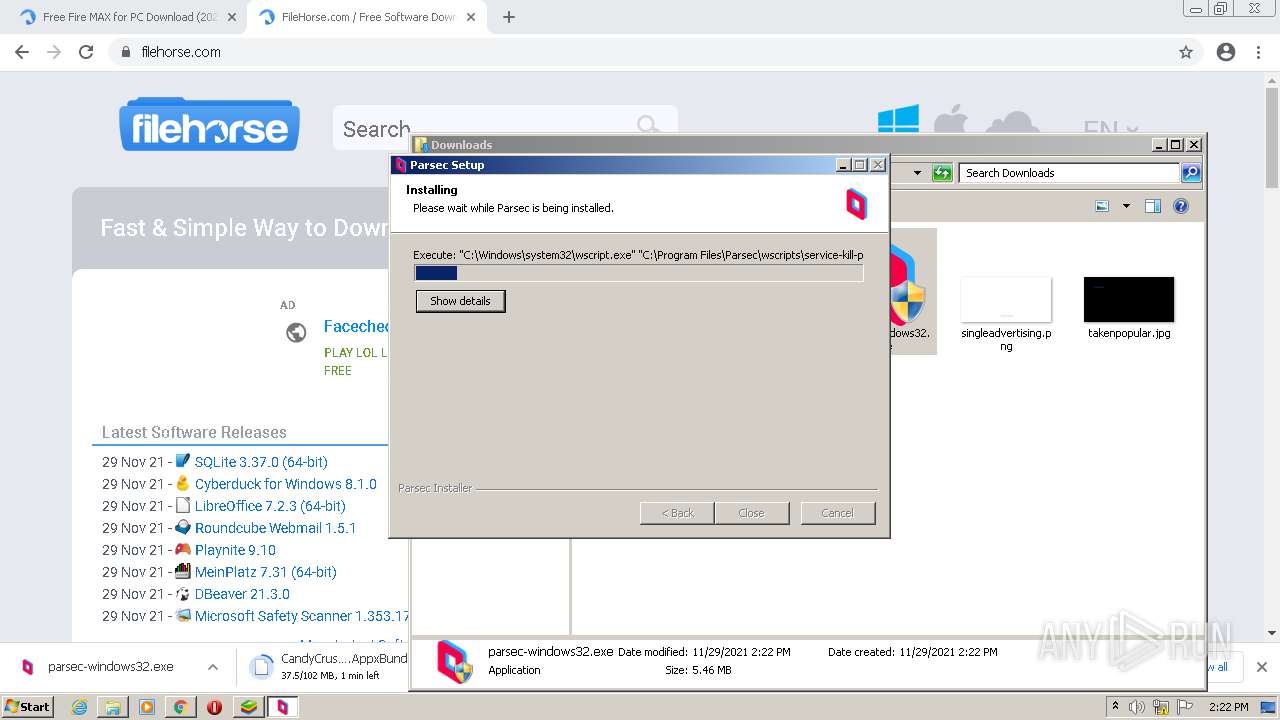
- parsec-windows32.exe (PID: 1888)
- parsec-windows32.exe (PID: 1748)
- pservice.exe (PID: 688)
- parsecd.exe (PID: 1604)
- parsecd.exe (PID: 648)
- BSX-Setup-5.4.50.1009.exe (PID: 2060)
Drops executable file immediately after starts
- BlueStacksInstaller_5.4.50.1009_native_ab0d65789ca9f2025a1773d795bb21f7_0_R2FyZW5hIEZyZWUgRmlyZSBNQVg=.exe (PID: 516)
- parsec-windows32.exe (PID: 1748)
- parsecd.exe (PID: 1604)
Changes settings of System certificates
- BlueStacksInstaller.exe (PID: 1992)
Loads dropped or rewritten executable
- parsec-windows32.exe (PID: 1748)
- parsecd.exe (PID: 1604)
- parsecd.exe (PID: 648)
- BSX-Setup-5.4.50.1009.exe (PID: 2060)
Uses Task Scheduler to run other applications
- wscript.exe (PID: 1876)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2528)
Changes the autorun value in the registry
- parsecd.exe (PID: 648)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 1164)
- BlueStacksInstaller_5.4.50.1009_native_ab0d65789ca9f2025a1773d795bb21f7_0_R2FyZW5hIEZyZWUgRmlyZSBNQVg=.exe (PID: 516)
- parsec-windows32.exe (PID: 1748)
- parsecd.exe (PID: 1604)
- parsecd.exe (PID: 648)
- BSX-Setup-5.4.50.1009.exe (PID: 2060)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 1164)
- BlueStacksInstaller_5.4.50.1009_native_ab0d65789ca9f2025a1773d795bb21f7_0_R2FyZW5hIEZyZWUgRmlyZSBNQVg=.exe (PID: 516)
- parsec-windows32.exe (PID: 1748)
- BSX-Setup-5.4.50.1009.exe (PID: 2060)
Drops a file with a compile date too recent
- BlueStacksInstaller_5.4.50.1009_native_ab0d65789ca9f2025a1773d795bb21f7_0_R2FyZW5hIEZyZWUgRmlyZSBNQVg=.exe (PID: 516)
- parsec-windows32.exe (PID: 1748)
- BSX-Setup-5.4.50.1009.exe (PID: 2060)
- WinRAR.exe (PID: 3928)
Checks supported languages
- BlueStacksInstaller_5.4.50.1009_native_ab0d65789ca9f2025a1773d795bb21f7_0_R2FyZW5hIEZyZWUgRmlyZSBNQVg=.exe (PID: 516)
- BlueStacksInstaller.exe (PID: 3860)
- BlueStacksInstaller.exe (PID: 1992)
- parsec-windows32.exe (PID: 1748)
- wscript.exe (PID: 3700)
- wscript.exe (PID: 1112)
- wscript.exe (PID: 568)
- wscript.exe (PID: 1876)
- wscript.exe (PID: 472)
- pservice.exe (PID: 688)
- wscript.exe (PID: 628)
- parsecd.exe (PID: 1604)
- parsecd.exe (PID: 648)
- BSX-Setup-5.4.50.1009.exe (PID: 2060)
- WScript.exe (PID: 1592)
- cmd.exe (PID: 4056)
- WinRAR.exe (PID: 3928)
Reads the computer name
- BlueStacksInstaller_5.4.50.1009_native_ab0d65789ca9f2025a1773d795bb21f7_0_R2FyZW5hIEZyZWUgRmlyZSBNQVg=.exe (PID: 516)
- BlueStacksInstaller.exe (PID: 3860)
- BlueStacksInstaller.exe (PID: 1992)
- parsec-windows32.exe (PID: 1748)
- wscript.exe (PID: 3700)
- wscript.exe (PID: 1112)
- wscript.exe (PID: 568)
- wscript.exe (PID: 1876)
- wscript.exe (PID: 472)
- wscript.exe (PID: 628)
- pservice.exe (PID: 688)
- parsecd.exe (PID: 1604)
- parsecd.exe (PID: 648)
- BSX-Setup-5.4.50.1009.exe (PID: 2060)
- WScript.exe (PID: 1592)
- WinRAR.exe (PID: 3928)
Application launched itself
- BlueStacksInstaller.exe (PID: 3860)
Reads Environment values
- BlueStacksInstaller.exe (PID: 1992)
- netsh.exe (PID: 3932)
- netsh.exe (PID: 1148)
- netsh.exe (PID: 3672)
- netsh.exe (PID: 2696)
- BSX-Setup-5.4.50.1009.exe (PID: 2060)
- netsh.exe (PID: 1188)
- netsh.exe (PID: 2788)
Adds / modifies Windows certificates
- BlueStacksInstaller.exe (PID: 1992)
Drops a file with too old compile date
- parsec-windows32.exe (PID: 1748)
- BSX-Setup-5.4.50.1009.exe (PID: 2060)
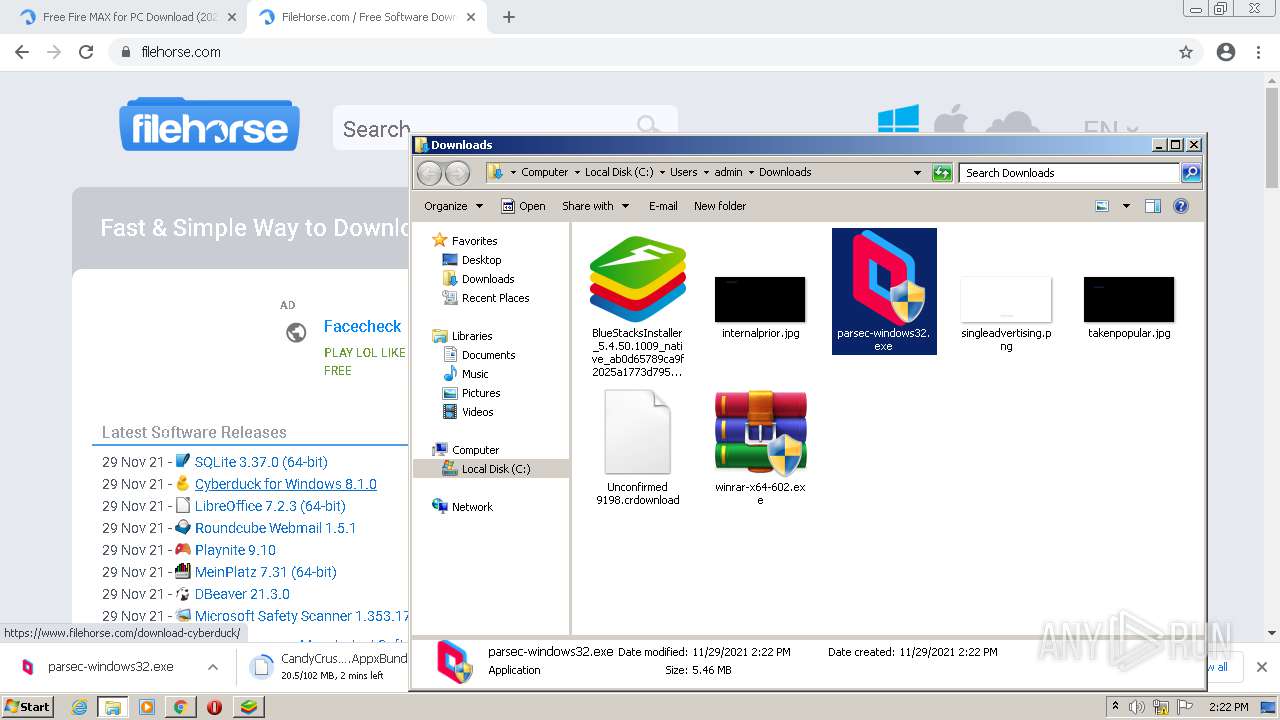
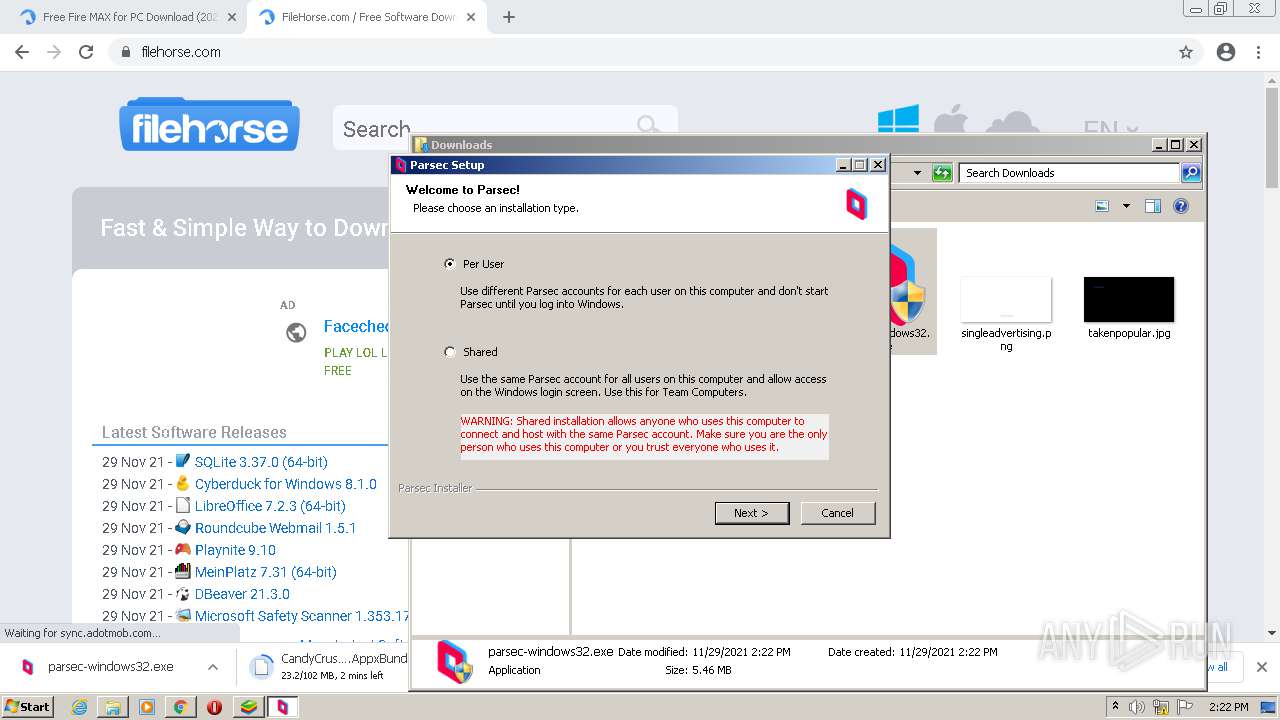
Creates a directory in Program Files
- parsec-windows32.exe (PID: 1748)
- BSX-Setup-5.4.50.1009.exe (PID: 2060)
Creates files in the program directory
- parsec-windows32.exe (PID: 1748)
- parsecd.exe (PID: 1604)
- parsecd.exe (PID: 648)
- BlueStacksInstaller.exe (PID: 1992)
- BSX-Setup-5.4.50.1009.exe (PID: 2060)
Executes scripts
- parsec-windows32.exe (PID: 1748)
- BSX-Setup-5.4.50.1009.exe (PID: 2060)
Starts SC.EXE for service management
- wscript.exe (PID: 3700)
- wscript.exe (PID: 1112)
- wscript.exe (PID: 472)
Uses NETSH.EXE for network configuration
- wscript.exe (PID: 568)
- wscript.exe (PID: 628)
- cmd.exe (PID: 4056)
Creates a software uninstall entry
- parsec-windows32.exe (PID: 1748)
- BSX-Setup-5.4.50.1009.exe (PID: 2060)
Changes default file association
- parsec-windows32.exe (PID: 1748)
- BSX-Setup-5.4.50.1009.exe (PID: 2060)
Executed as Windows Service
- pservice.exe (PID: 688)
Creates files in the Windows directory
- pservice.exe (PID: 688)
Starts CMD.EXE for commands execution
- WScript.exe (PID: 1592)
INFO
Checks supported languages
- chrome.exe (PID: 1164)
- chrome.exe (PID: 2244)
- chrome.exe (PID: 3328)
- chrome.exe (PID: 748)
- chrome.exe (PID: 3812)
- chrome.exe (PID: 760)
- chrome.exe (PID: 2632)
- chrome.exe (PID: 2512)
- chrome.exe (PID: 292)
- chrome.exe (PID: 564)
- chrome.exe (PID: 3004)
- chrome.exe (PID: 2424)
- chrome.exe (PID: 2388)
- chrome.exe (PID: 2336)
- chrome.exe (PID: 3264)
- chrome.exe (PID: 2144)
- chrome.exe (PID: 3068)
- chrome.exe (PID: 3108)
- chrome.exe (PID: 3996)
- chrome.exe (PID: 356)
- chrome.exe (PID: 2608)
- chrome.exe (PID: 1332)
- chrome.exe (PID: 3232)
- chrome.exe (PID: 1984)
- chrome.exe (PID: 2600)
- chrome.exe (PID: 2180)
- chrome.exe (PID: 2628)
- chrome.exe (PID: 2052)
- chrome.exe (PID: 2452)
- chrome.exe (PID: 2676)
- chrome.exe (PID: 2400)
- chrome.exe (PID: 2212)
- chrome.exe (PID: 1604)
- chrome.exe (PID: 3360)
- chrome.exe (PID: 1272)
- chrome.exe (PID: 2840)
- chrome.exe (PID: 2096)
- chrome.exe (PID: 3608)
- chrome.exe (PID: 2212)
- chrome.exe (PID: 956)
- chrome.exe (PID: 2224)
- chrome.exe (PID: 1288)
- chrome.exe (PID: 2508)
- chrome.exe (PID: 2836)
- chrome.exe (PID: 1300)
- chrome.exe (PID: 3952)
- chrome.exe (PID: 3912)
- chrome.exe (PID: 2152)
- chrome.exe (PID: 2292)
- chrome.exe (PID: 2816)
- WISPTIS.EXE (PID: 676)
- chrome.exe (PID: 3452)
- chrome.exe (PID: 2992)
- chrome.exe (PID: 2684)
- chrome.exe (PID: 4056)
- chrome.exe (PID: 3448)
- chrome.exe (PID: 3924)
- chrome.exe (PID: 3540)
- chrome.exe (PID: 3520)
- chrome.exe (PID: 3100)
- chrome.exe (PID: 292)
- chrome.exe (PID: 3388)
- chrome.exe (PID: 392)
- chrome.exe (PID: 2560)
- chrome.exe (PID: 3208)
- chrome.exe (PID: 3108)
- chrome.exe (PID: 1108)
- chrome.exe (PID: 3060)
- chrome.exe (PID: 2568)
- chrome.exe (PID: 1604)
- chrome.exe (PID: 3764)
- chrome.exe (PID: 2092)
- chrome.exe (PID: 3284)
- chrome.exe (PID: 3908)
- chrome.exe (PID: 3060)
- sc.exe (PID: 3420)
- sc.exe (PID: 3100)
- sc.exe (PID: 3936)
- netsh.exe (PID: 3932)
- netsh.exe (PID: 3672)
- netsh.exe (PID: 1148)
- schtasks.exe (PID: 2528)
- sc.exe (PID: 676)
- sc.exe (PID: 4008)
- netsh.exe (PID: 2696)
- chrome.exe (PID: 3120)
- netsh.exe (PID: 1188)
- netsh.exe (PID: 2788)
- chrome.exe (PID: 2092)
- chrome.exe (PID: 3540)
- chrome.exe (PID: 4088)
- chrome.exe (PID: 2260)
- chrome.exe (PID: 1552)
- chrome.exe (PID: 3720)
- chrome.exe (PID: 2192)
Application launched itself
- chrome.exe (PID: 1164)
Reads the computer name
- chrome.exe (PID: 1164)
- chrome.exe (PID: 748)
- chrome.exe (PID: 2244)
- chrome.exe (PID: 3812)
- chrome.exe (PID: 292)
- chrome.exe (PID: 3996)
- chrome.exe (PID: 2144)
- chrome.exe (PID: 2452)
- chrome.exe (PID: 2400)
- chrome.exe (PID: 1604)
- chrome.exe (PID: 2836)
- chrome.exe (PID: 1300)
- WISPTIS.EXE (PID: 676)
- chrome.exe (PID: 1604)
- chrome.exe (PID: 3764)
- sc.exe (PID: 3420)
- sc.exe (PID: 3936)
- sc.exe (PID: 3100)
- netsh.exe (PID: 3932)
- netsh.exe (PID: 1148)
- netsh.exe (PID: 3672)
- schtasks.exe (PID: 2528)
- sc.exe (PID: 676)
- sc.exe (PID: 4008)
- netsh.exe (PID: 2696)
- netsh.exe (PID: 1188)
- netsh.exe (PID: 2788)
- chrome.exe (PID: 3540)
- chrome.exe (PID: 4088)
- chrome.exe (PID: 2192)
Reads the hosts file
- chrome.exe (PID: 1164)
- chrome.exe (PID: 2244)
Reads settings of System Certificates
- chrome.exe (PID: 2244)
- chrome.exe (PID: 1164)
- BlueStacksInstaller.exe (PID: 1992)
- parsecd.exe (PID: 1604)
- pservice.exe (PID: 688)
- parsecd.exe (PID: 648)
Changes settings of System certificates
- chrome.exe (PID: 2244)
Checks Windows Trust Settings
- chrome.exe (PID: 1164)
- wscript.exe (PID: 3700)
- wscript.exe (PID: 568)
- wscript.exe (PID: 1112)
- wscript.exe (PID: 1876)
- wscript.exe (PID: 472)
- wscript.exe (PID: 628)
- parsecd.exe (PID: 1604)
- pservice.exe (PID: 688)
- parsecd.exe (PID: 648)
- WScript.exe (PID: 1592)
Reads the date of Windows installation
- chrome.exe (PID: 2400)
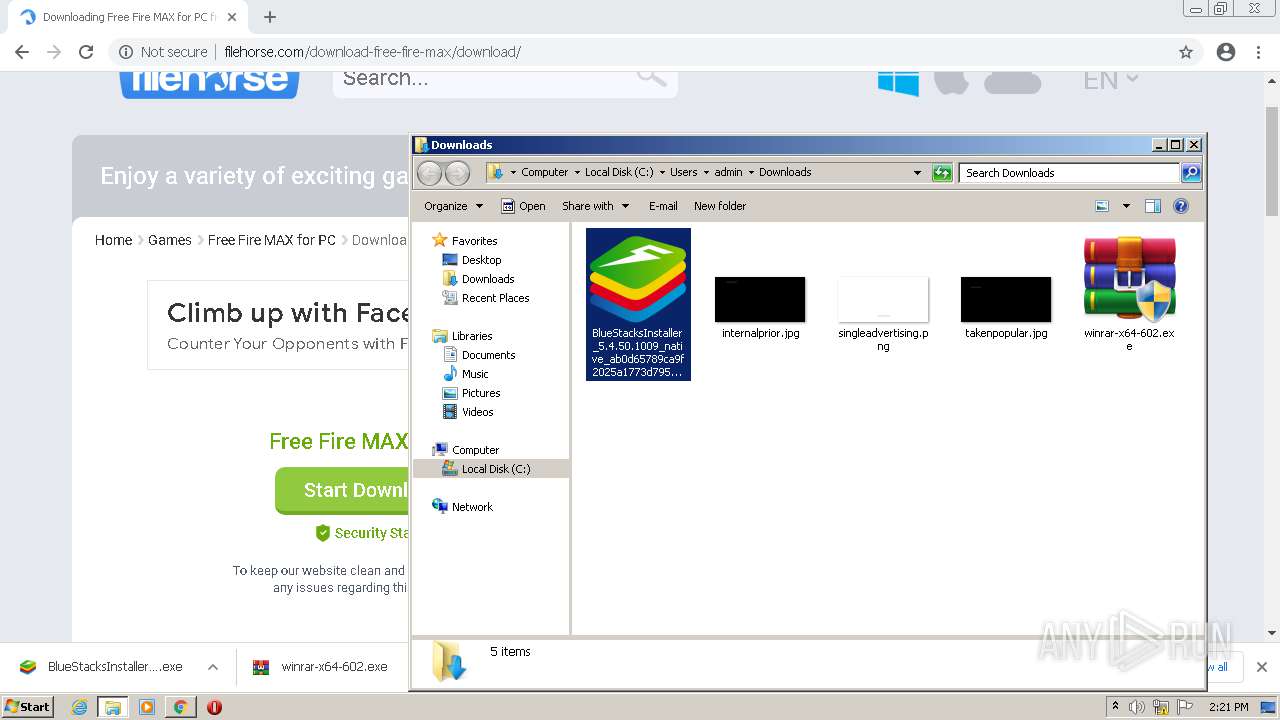
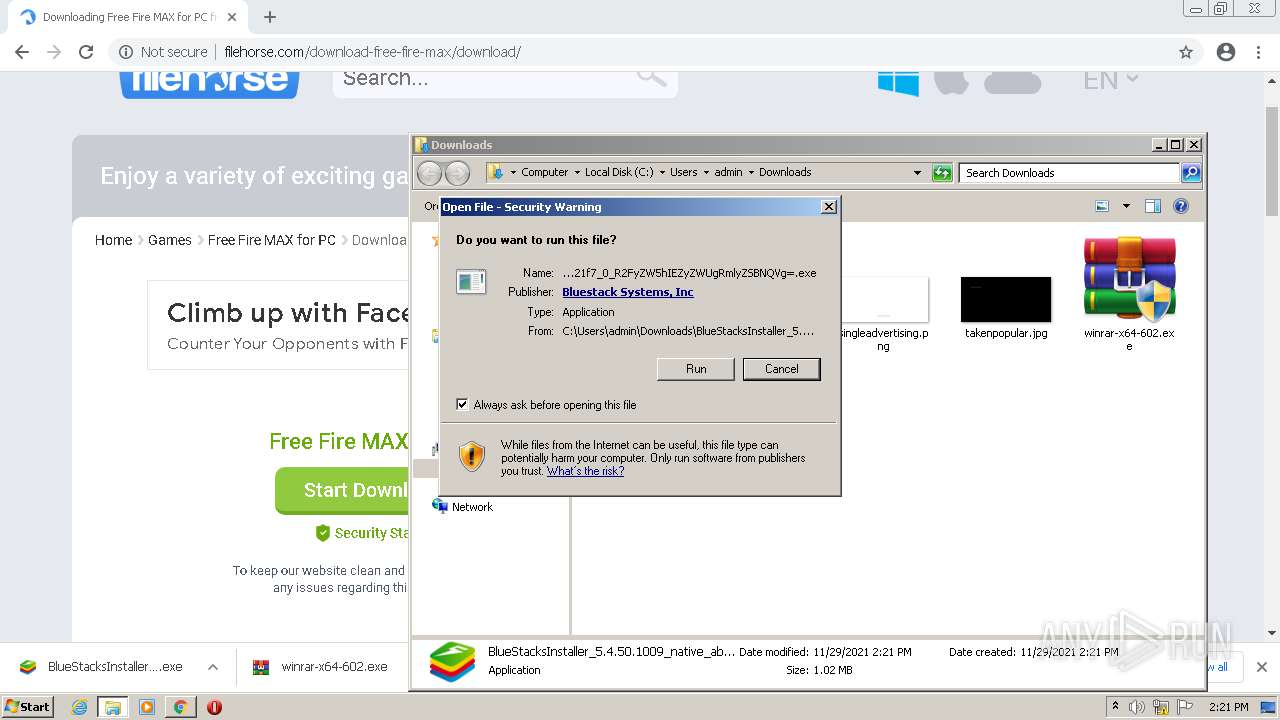
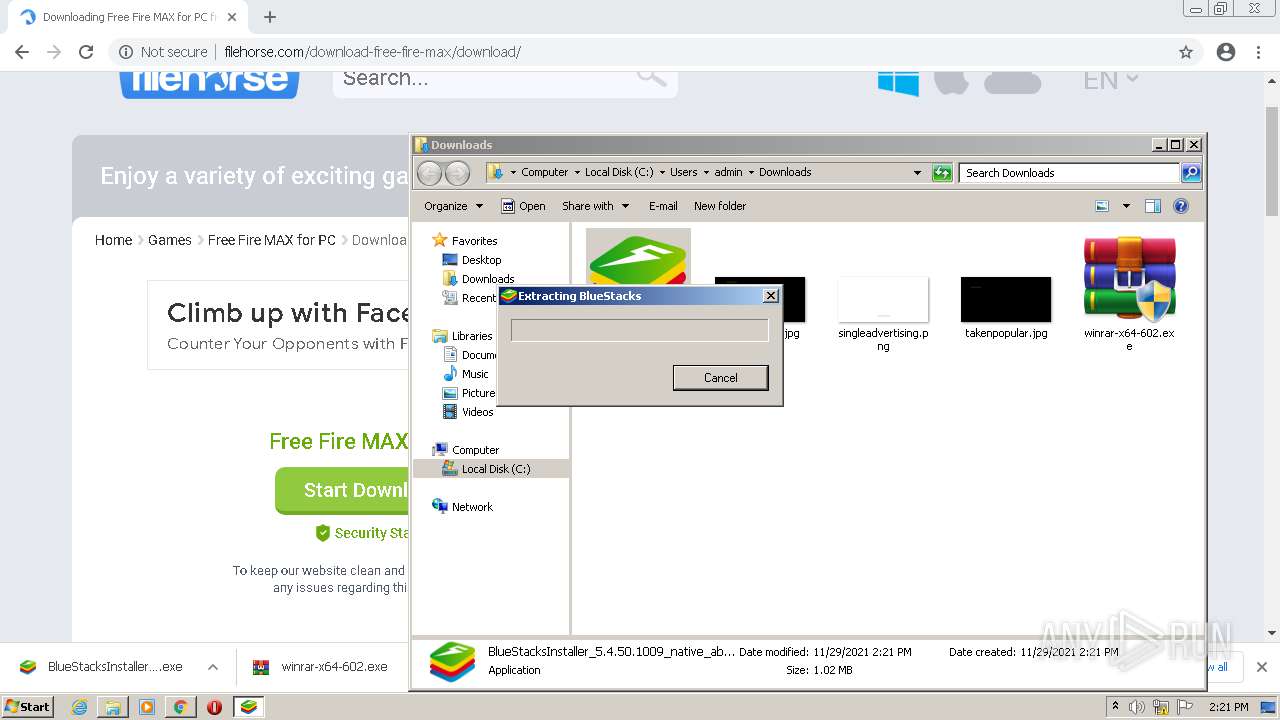
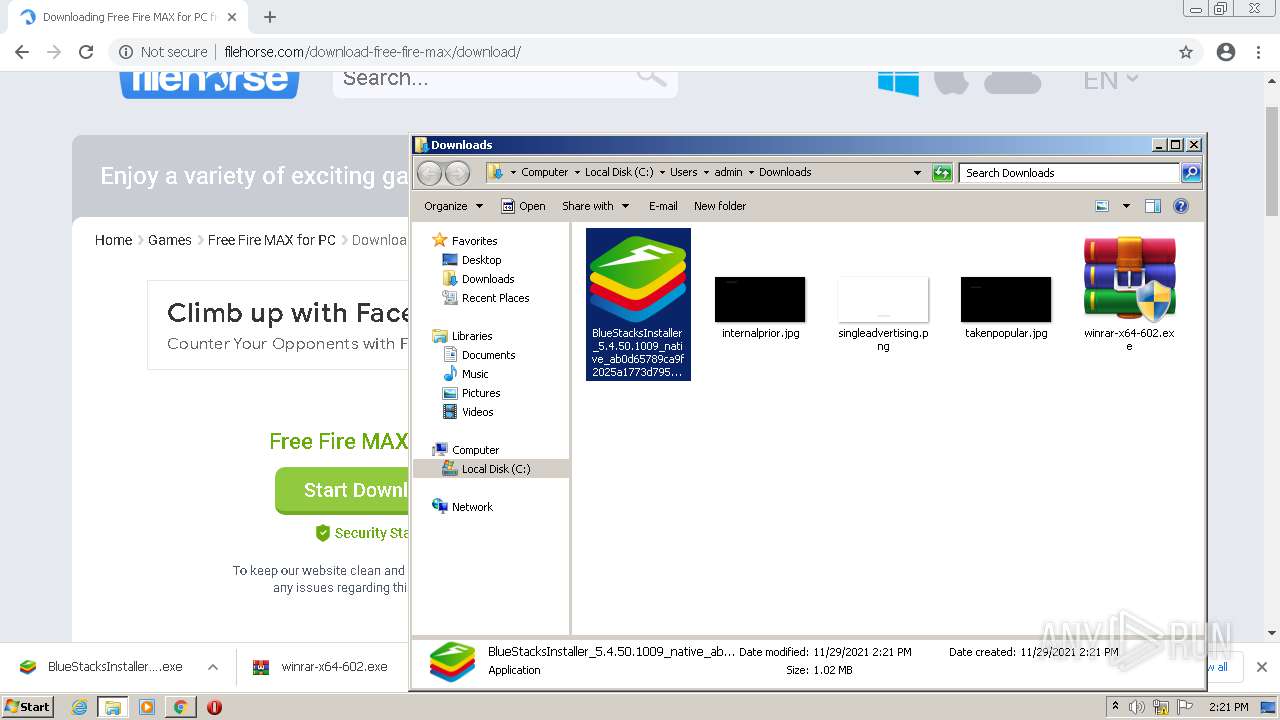
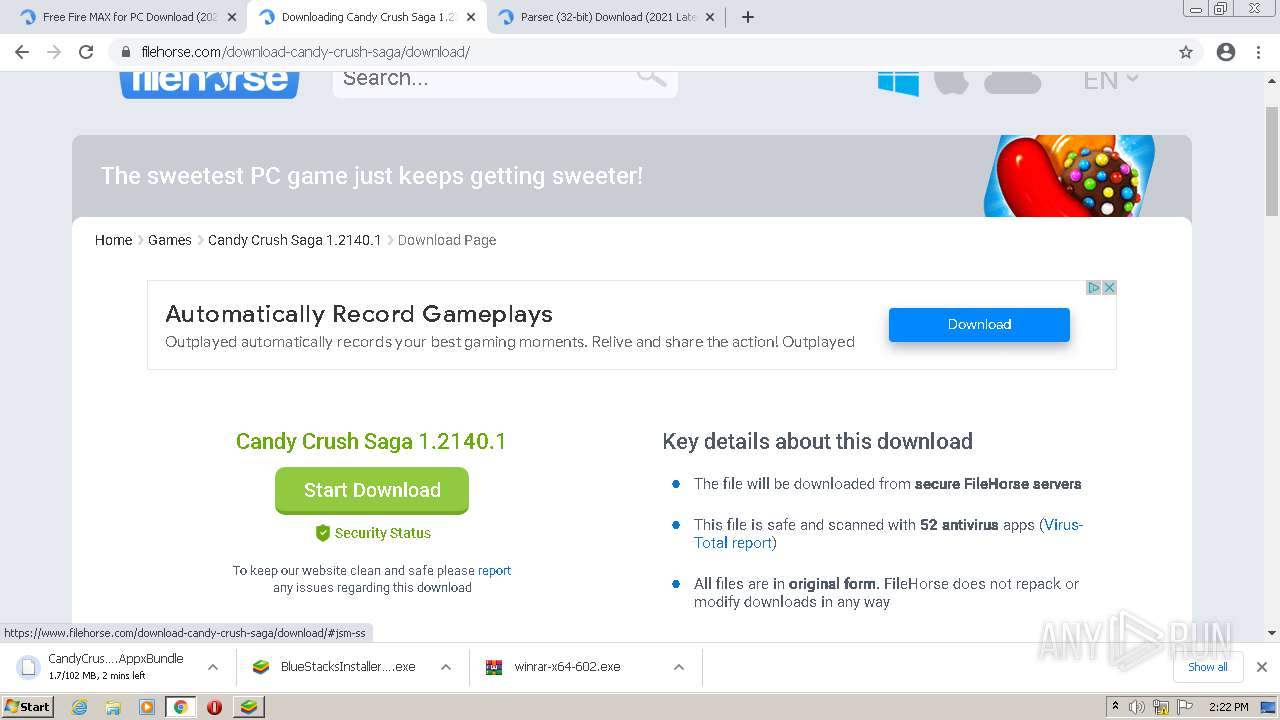
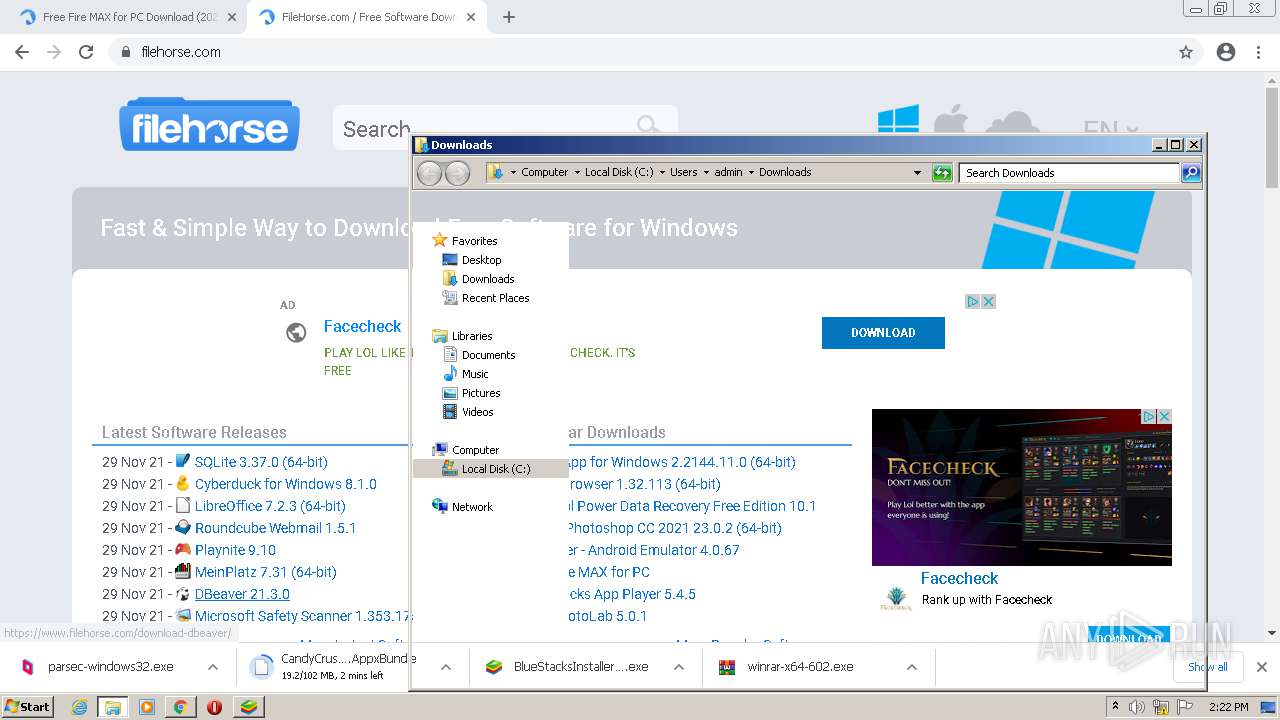
Manual execution by user
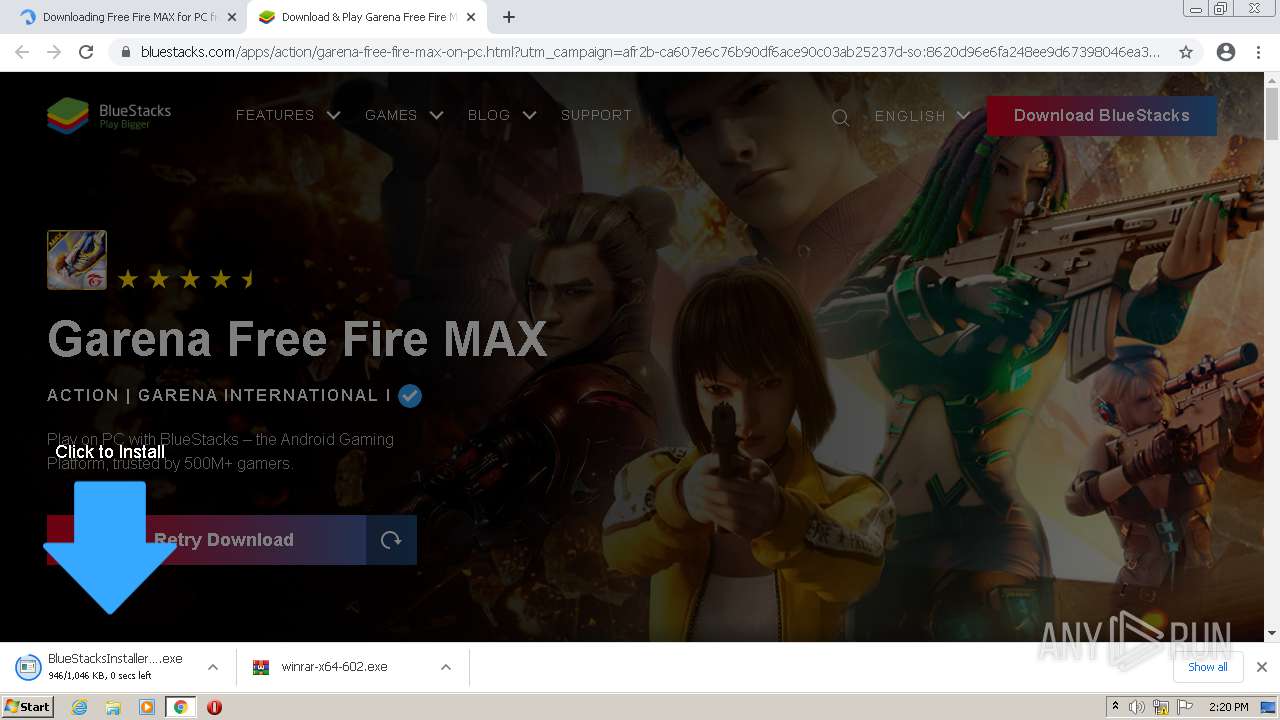
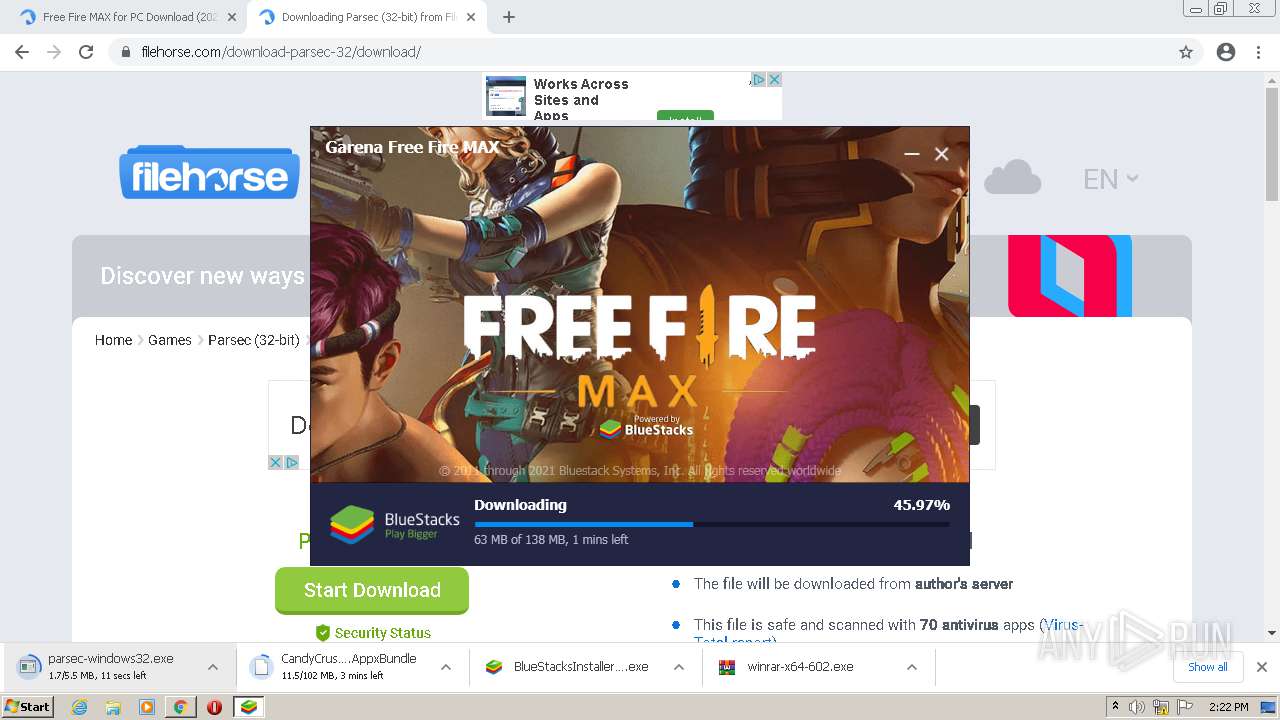
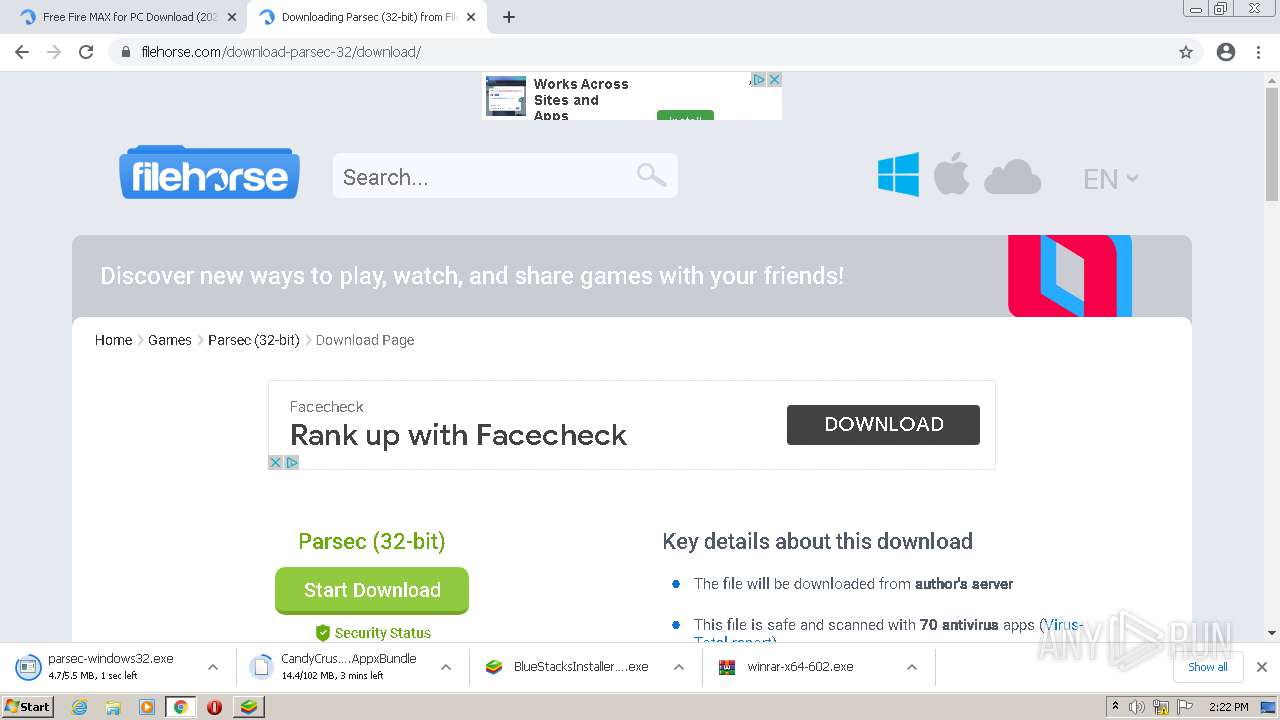
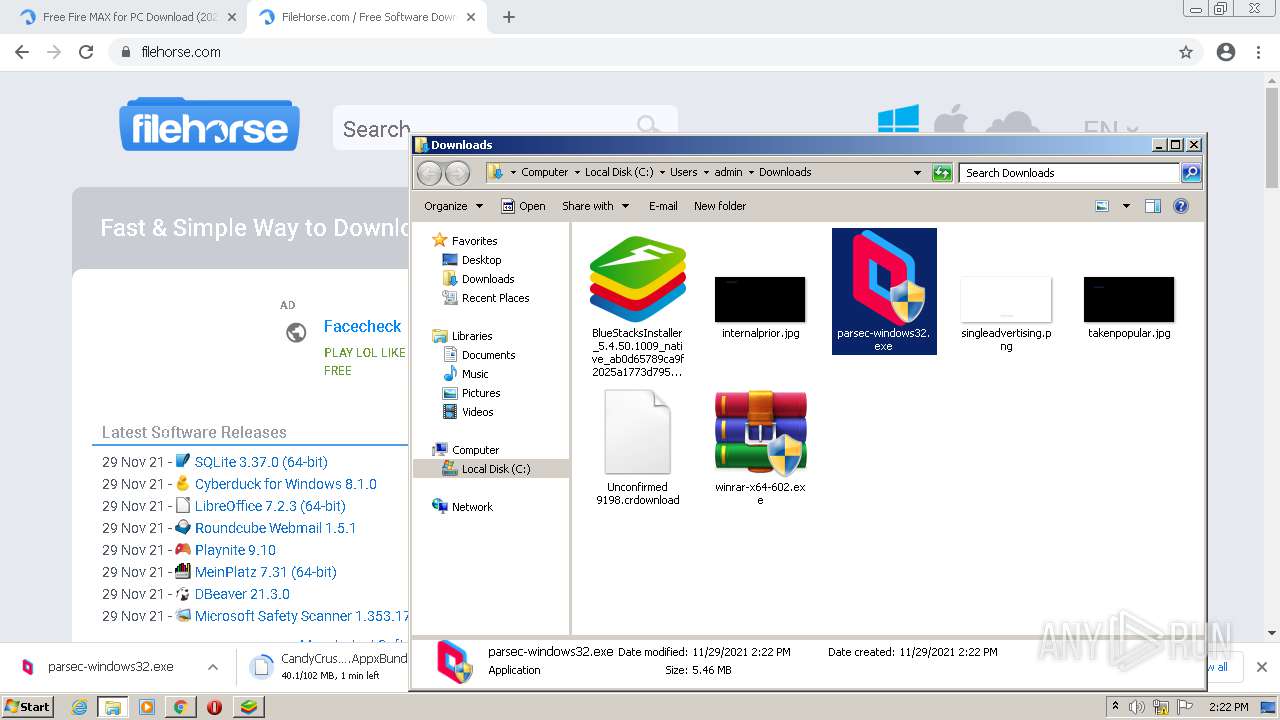
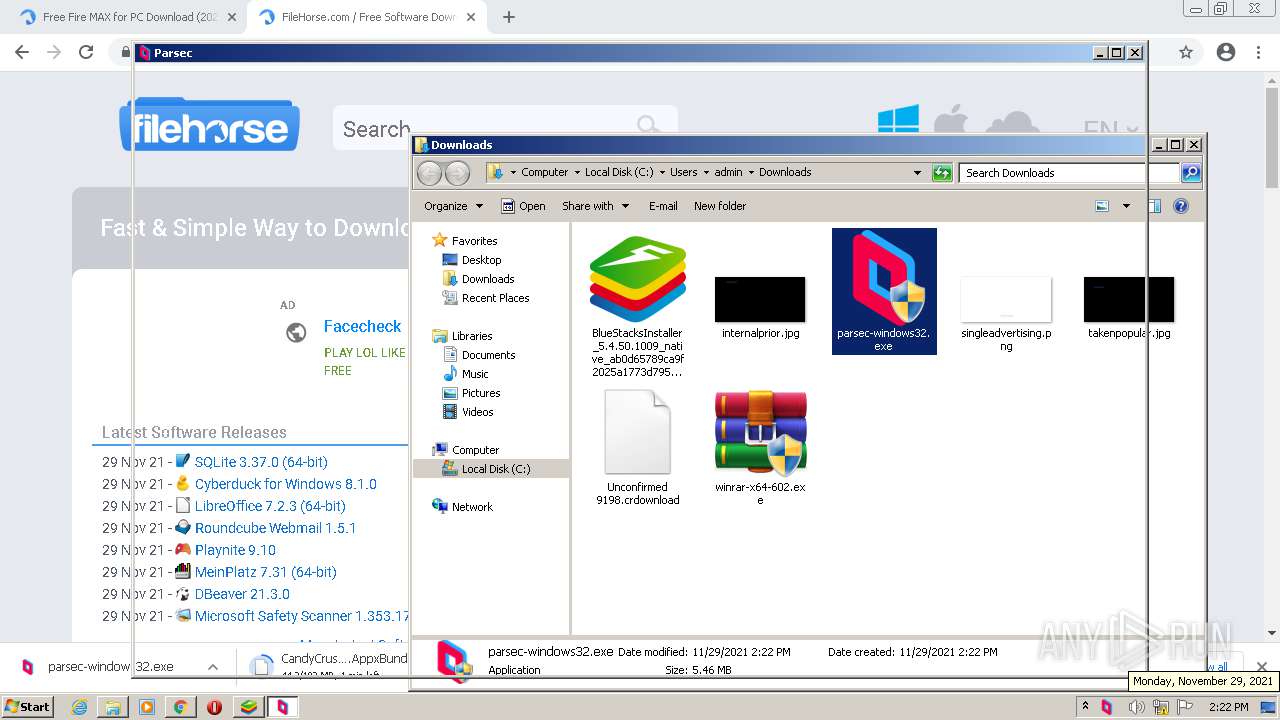
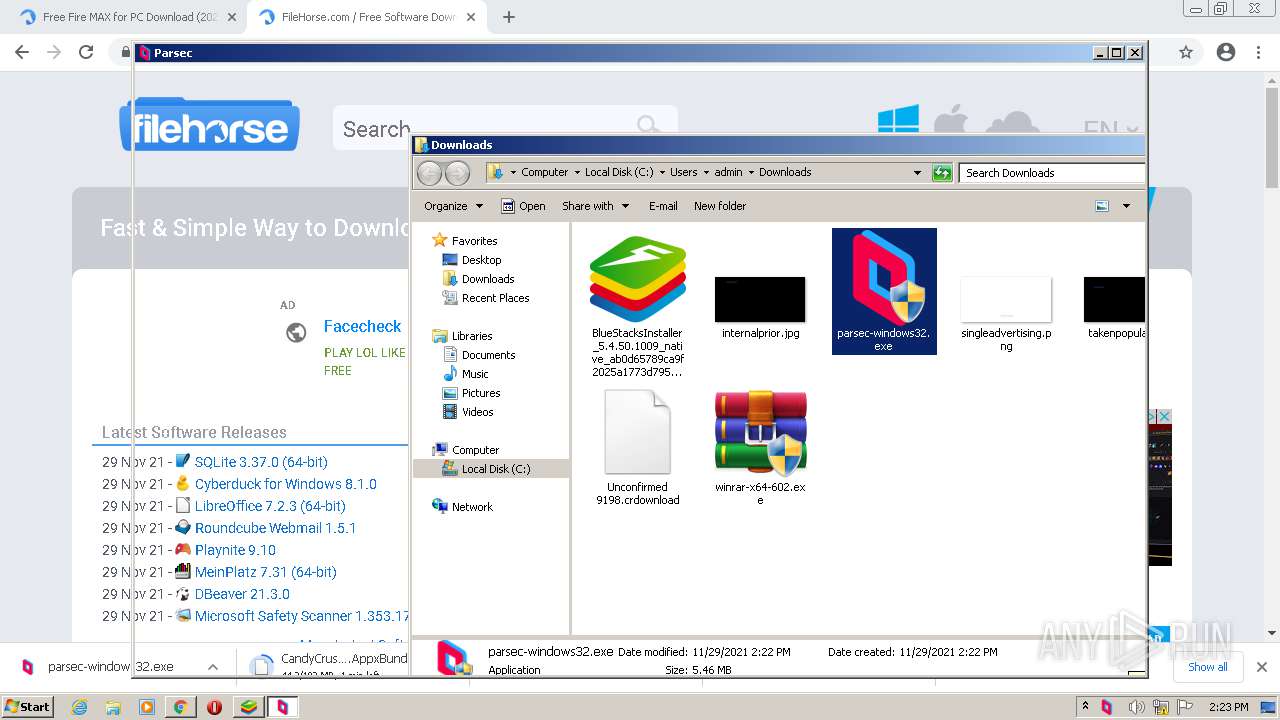
- BlueStacksInstaller_5.4.50.1009_native_ab0d65789ca9f2025a1773d795bb21f7_0_R2FyZW5hIEZyZWUgRmlyZSBNQVg=.exe (PID: 516)
- parsec-windows32.exe (PID: 1888)
- parsec-windows32.exe (PID: 1748)
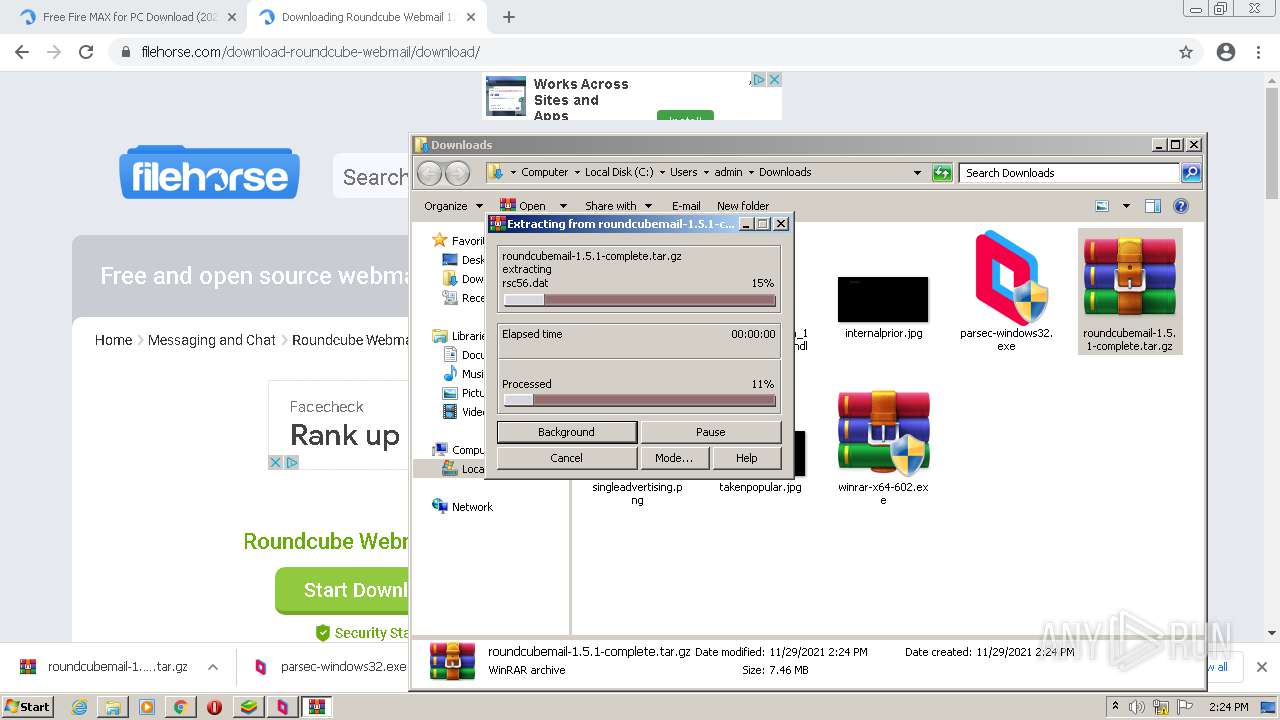
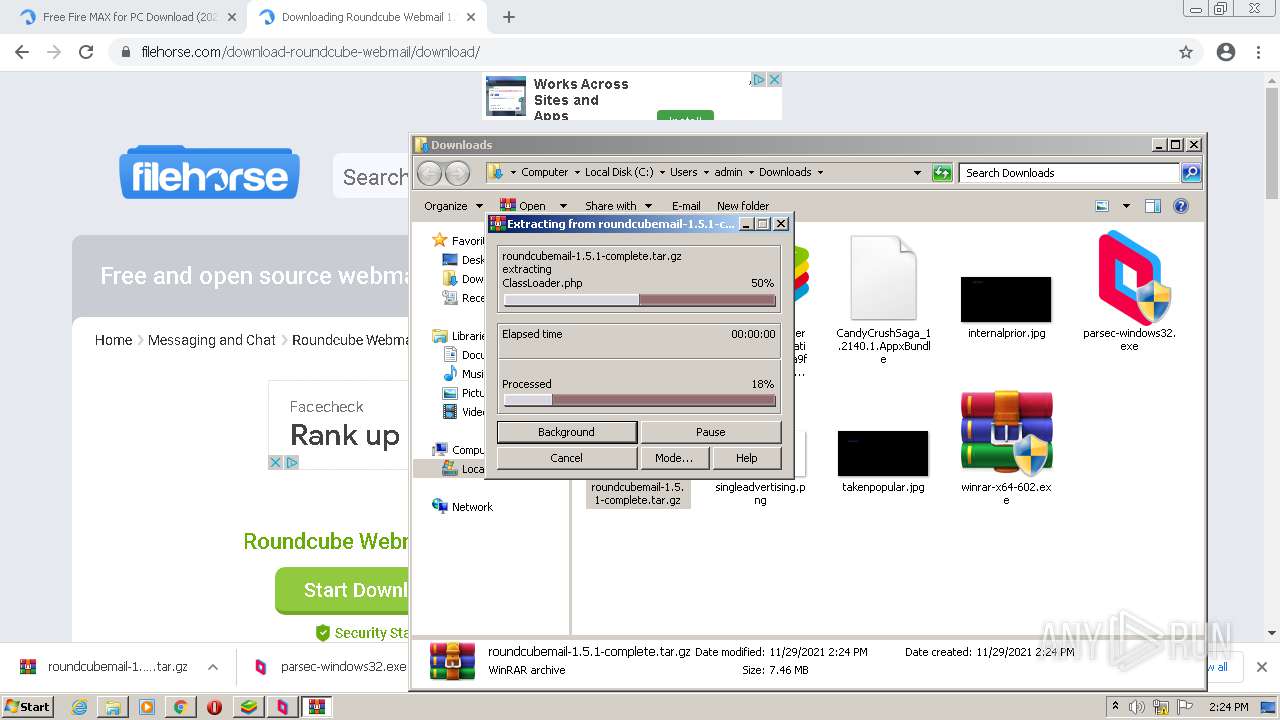
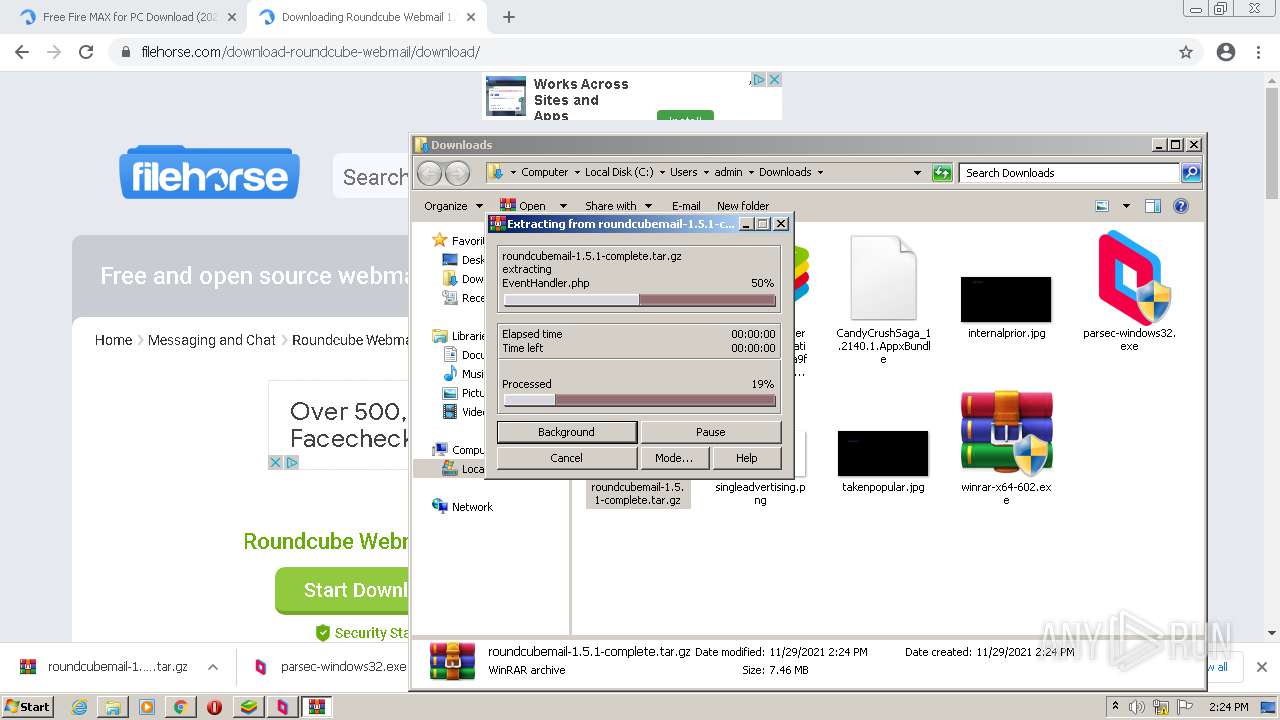
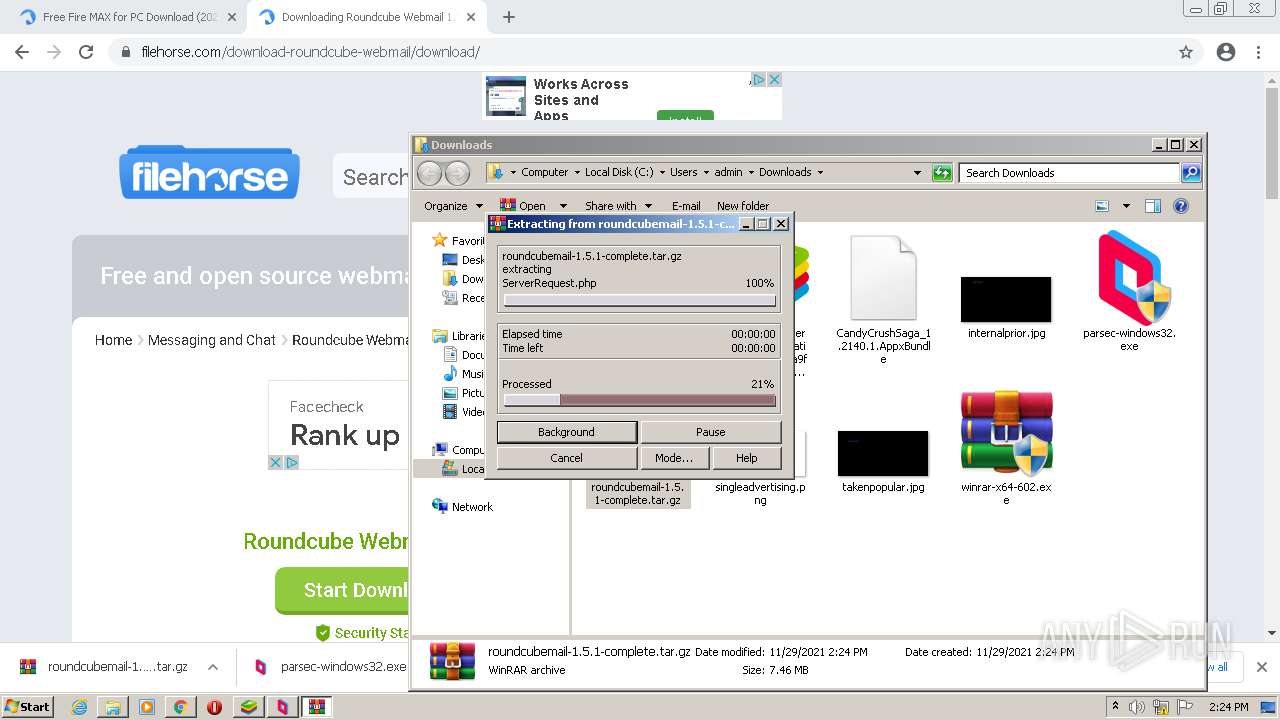
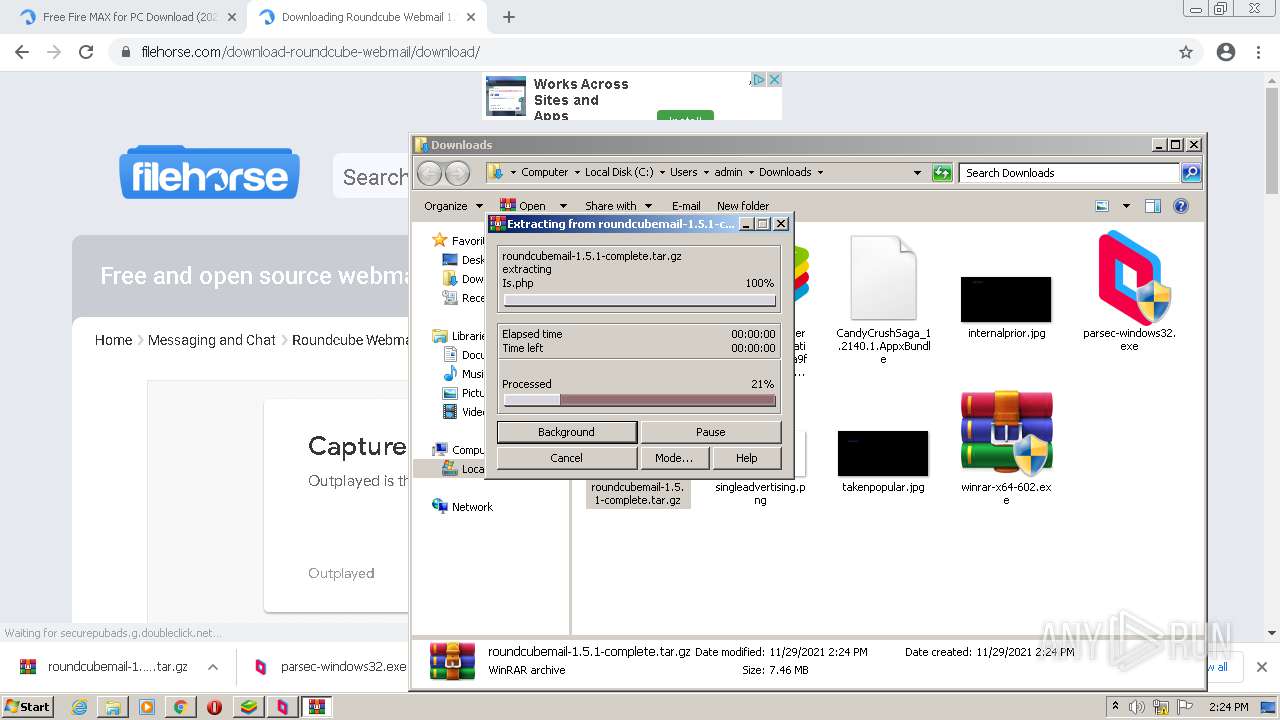
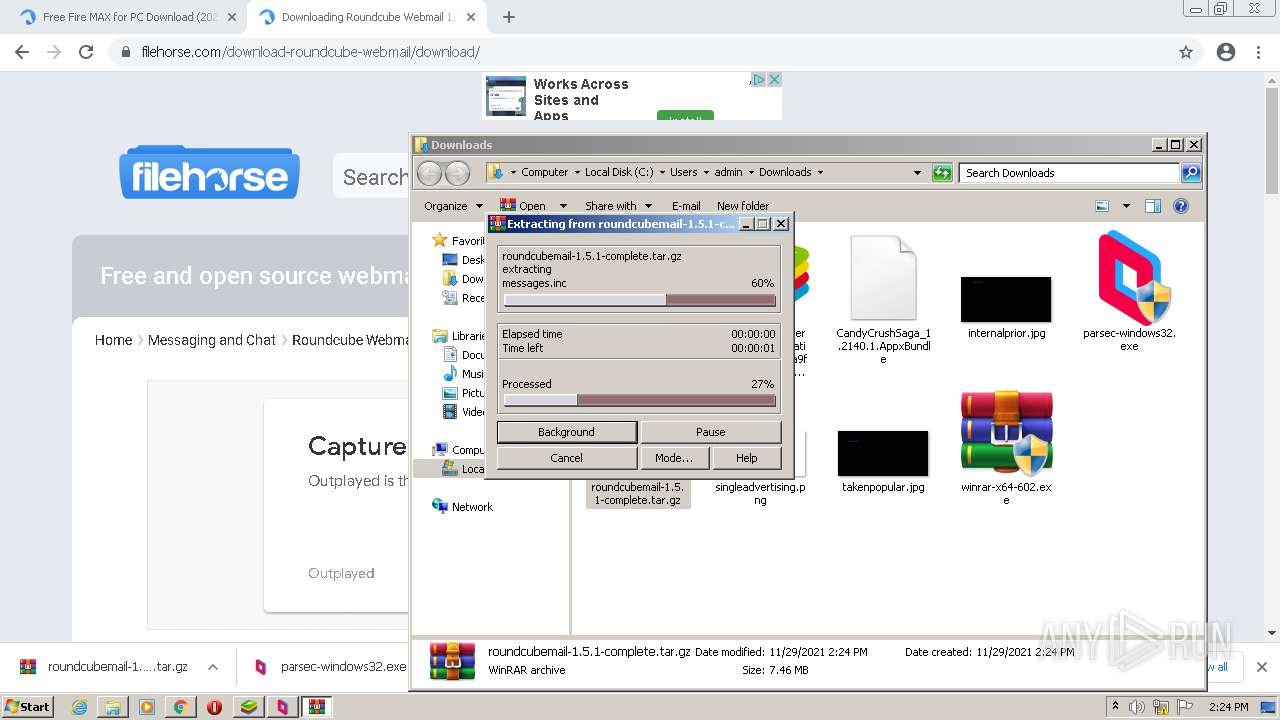
- WinRAR.exe (PID: 3928)
Creates files in the user directory
- chrome.exe (PID: 1164)
Dropped object may contain Bitcoin addresses
- BSX-Setup-5.4.50.1009.exe (PID: 2060)
- WinRAR.exe (PID: 3928)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
175
Monitored processes
114
Malicious processes
8
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1056,17487912810995670378,6278981821839091681,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3188 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1056,17487912810995670378,6278981821839091681,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=5408 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,17487912810995670378,6278981821839091681,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3912 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,17487912810995670378,6278981821839091681,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=59 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5048 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 472 | "C:\Windows\system32\wscript.exe" "C:\Program Files\Parsec\wscripts\service-install.vbs" "C:\Program Files\Parsec\pservice.exe" | C:\Windows\system32\wscript.exe | — | parsec-windows32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft � Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 516 | "C:\Users\admin\Downloads\BlueStacksInstaller_5.4.50.1009_native_ab0d65789ca9f2025a1773d795bb21f7_0_R2FyZW5hIEZyZWUgRmlyZSBNQVg=.exe" | C:\Users\admin\Downloads\BlueStacksInstaller_5.4.50.1009_native_ab0d65789ca9f2025a1773d795bb21f7_0_R2FyZW5hIEZyZWUgRmlyZSBNQVg=.exe | Explorer.EXE | ||||||||||||
User: admin Company: BlueStack Systems Inc. Integrity Level: MEDIUM Description: BlueStacks Setup Exit code: 0 Version: 5.0 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,17487912810995670378,6278981821839091681,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3140 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 568 | "C:\Windows\system32\wscript.exe" "C:\Program Files\Parsec\wscripts\firewall-remove.vbs" | C:\Windows\system32\wscript.exe | — | parsec-windows32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft � Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 628 | "C:\Windows\system32\wscript.exe" "C:\Program Files\Parsec\wscripts\firewall-add.vbs" "C:\Program Files\Parsec\parsecd.exe" | C:\Windows\system32\wscript.exe | — | parsec-windows32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft � Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 648 | "C:\Program Files\Parsec\parsecd.exe" SERVICE_LAUNCHED_V4 | C:\Program Files\Parsec\parsecd.exe | pservice.exe | ||||||||||||
User: SYSTEM Company: Parsec Integrity Level: SYSTEM Description: Parsec Exit code: 0 Version: 150.75.0.0 Modules
| |||||||||||||||
Total events
60 160
Read events
59 344
Write events
811
Delete events
5
Modification events
| (PID) Process: | (1164) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1164) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1164) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1164) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1164) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1164) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1164) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1164) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1164) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (1164) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
128
Suspicious files
322
Text files
1 058
Unknown types
196
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1164 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61A4E18D-48C.pma | — | |
MD5:— | SHA256:— | |||
| 1164 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\24d5beb0-238e-44c7-af03-dc38b9152adb.tmp | text | |
MD5:— | SHA256:— | |||
| 1164 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 1164 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF13f948.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
| 1164 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF13f7ff.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 1164 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 1164 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\28a124c5-28f9-4a98-9ecd-2906921b9cfb.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 1164 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old~RF13fb4b.TMP | text | |
MD5:D0BA19096D6C8F8DE58312E8D938E893 | SHA256:AADE90A7B0984F3C719D528E4E6FAE3854E28B30363BDD4DF65037E69784A078 | |||
| 1164 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old | text | |
MD5:5202CA4D6AF0C37DAEC0D528CC7F2986 | SHA256:8F5B8FF94B14C36EA0CBE8FA0A4D165A632B45F834BBB7239E1A6CF6685F256C | |||
| 1164 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
437
DNS requests
255
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2244 | chrome.exe | GET | 302 | 76.223.111.18:80 | http://eb2.3lift.com/xuid?mid=7666&xuid=f9ad665e-026b-4340-91bc-f06d738df545&dongle=8f7 | US | — | — | shared |
924 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjg0QUFYSnN4MFUtaEQwNDZqVGRkVkFmZw/1.0.6.0_aemomkdncapdnfajjbbcbdebjljbpmpj.crx | US | — | — | whitelisted |
924 | svchost.exe | GET | — | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjg0QUFYSnN4MFUtaEQwNDZqVGRkVkFmZw/1.0.6.0_aemomkdncapdnfajjbbcbdebjljbpmpj.crx | US | — | — | whitelisted |
924 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ewx2jiqzclhlnu3dvppnd5fnw4_2741/jflookgnkcckhobaglndicnbbgbonegd_2741_all_acam7af44kfiybs6mrccc5wajbaq.crx3 | US | — | — | whitelisted |
924 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | — | — | whitelisted |
1992 | BlueStacksInstaller.exe | GET | — | 13.225.77.110:80 | http://cdn3.bluestacks.com/downloads/windows/nxt/5.4.50.1009/bb6a52b6118f4439829431a9165e09c8/Android/Nougat32/Nougat32.7z | US | — | — | shared |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ewx2jiqzclhlnu3dvppnd5fnw4_2741/jflookgnkcckhobaglndicnbbgbonegd_2741_all_acam7af44kfiybs6mrccc5wajbaq.crx3 | US | binary | 8.05 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 45.1 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ewx2jiqzclhlnu3dvppnd5fnw4_2741/jflookgnkcckhobaglndicnbbgbonegd_2741_all_acam7af44kfiybs6mrccc5wajbaq.crx3 | US | binary | 5.63 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 89.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2244 | chrome.exe | 142.250.181.238:443 | clients2.google.com | Google Inc. | US | whitelisted |
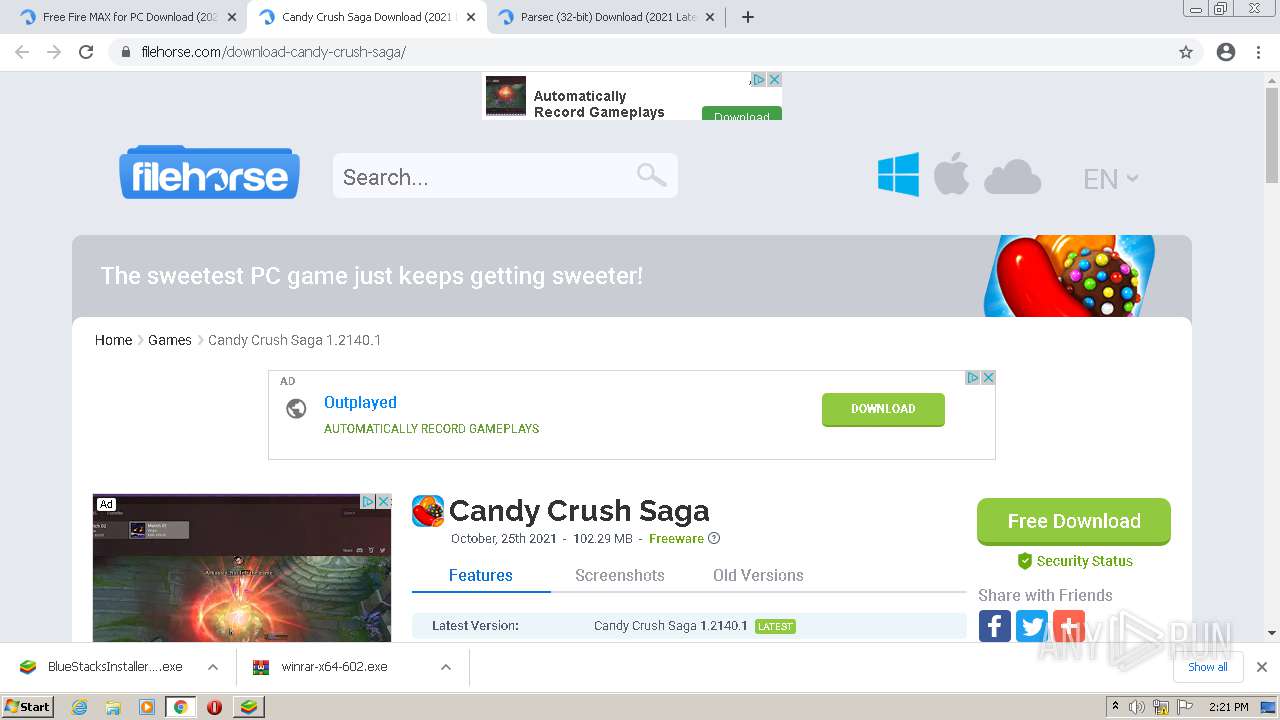
2244 | chrome.exe | 172.67.19.114:443 | www.filehorse.com | — | US | unknown |
2244 | chrome.exe | 142.250.186.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2244 | chrome.exe | 108.177.15.154:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
2244 | chrome.exe | 142.250.186.34:443 | googleads.g.doubleclick.net | Google Inc. | US | suspicious |
2244 | chrome.exe | 142.250.186.46:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2244 | chrome.exe | 172.217.16.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2244 | chrome.exe | 142.250.185.226:443 | adservice.google.com | Google Inc. | US | suspicious |
2244 | chrome.exe | 151.101.2.133:443 | spn-v1.revampcdn.com | Fastly | US | malicious |
2244 | chrome.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
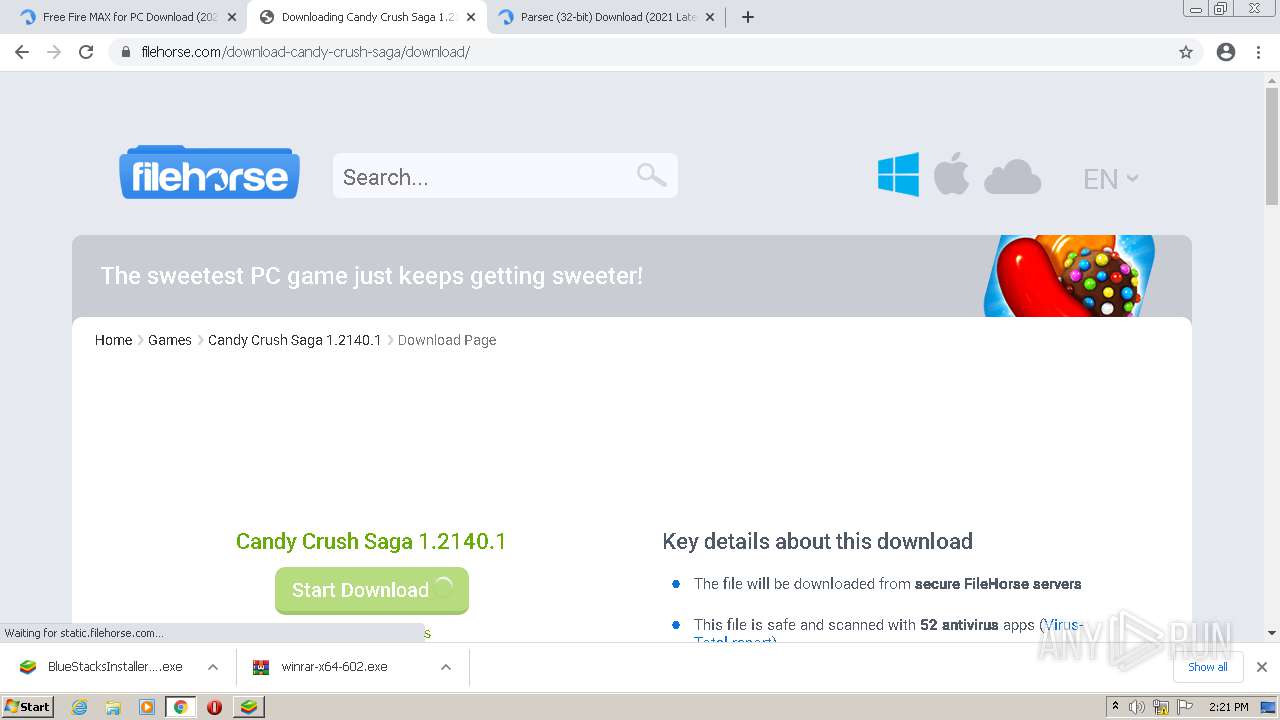
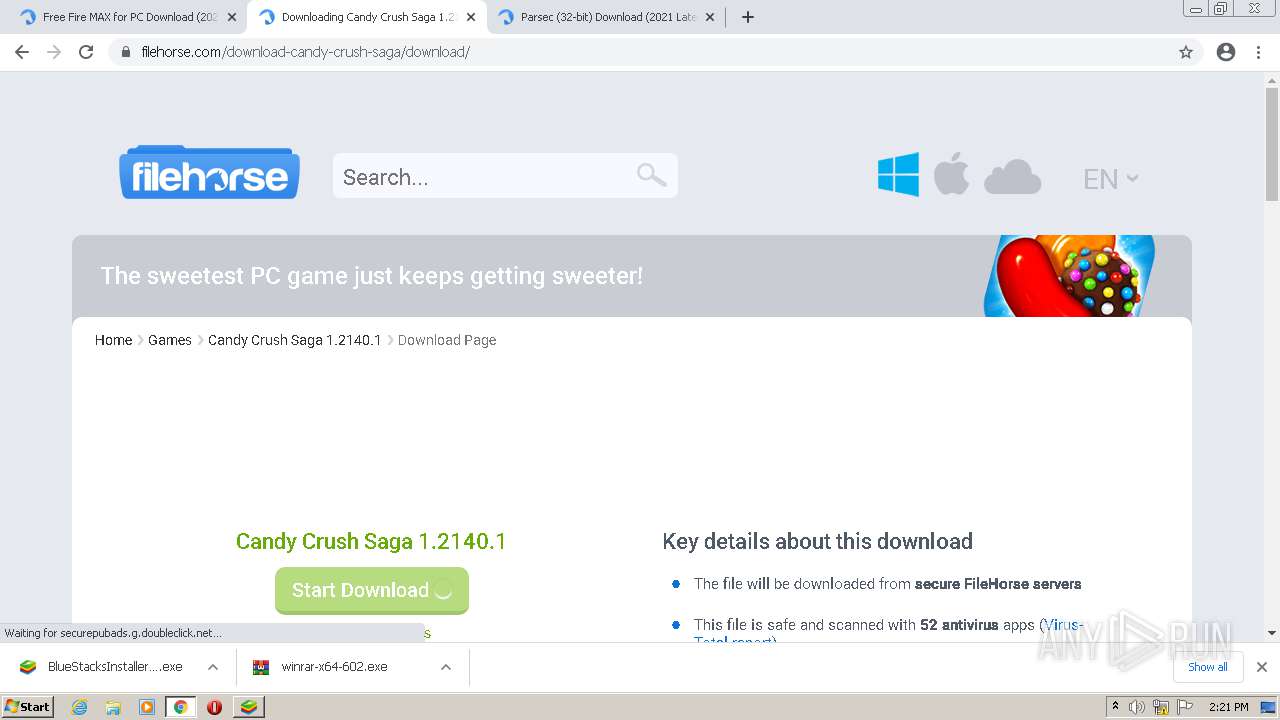
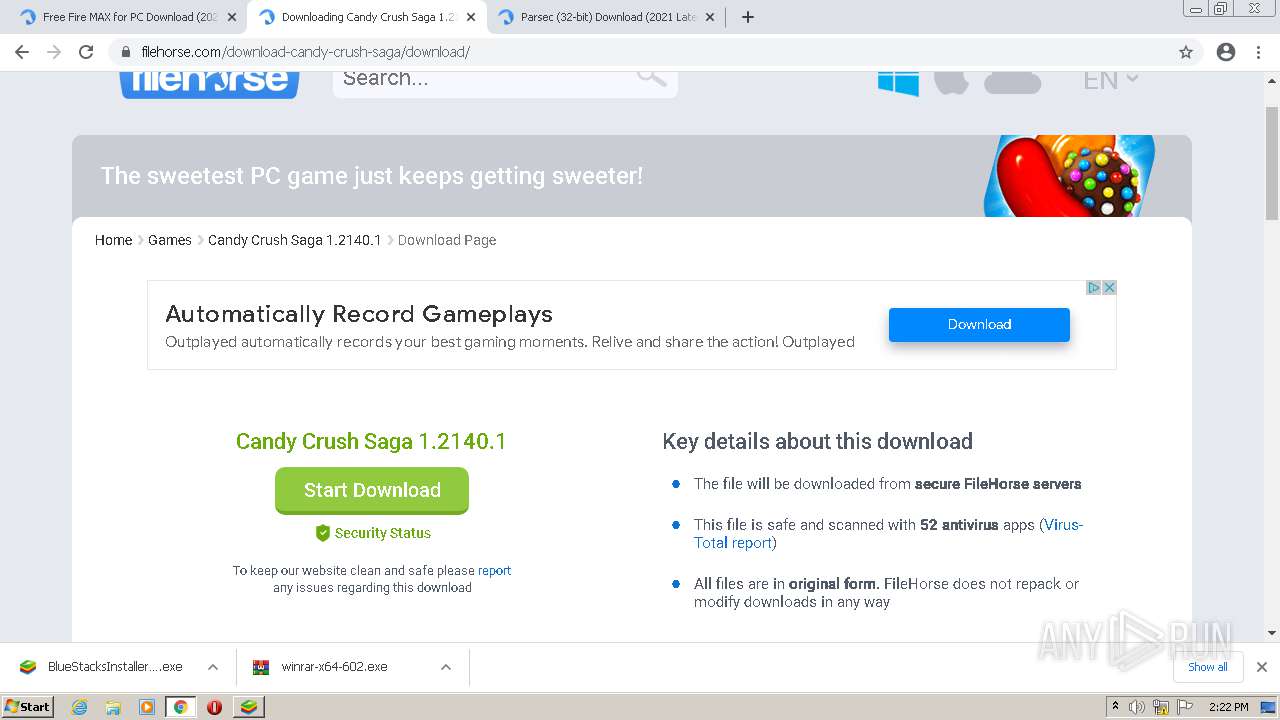
www.filehorse.com |
| whitelisted |
clients2.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
static.filehorse.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |
spn-v1.revampcdn.com |
| suspicious |
fonts.gstatic.com |
| whitelisted |
Threats
Process | Message |
|---|---|
BSX-Setup-5.4.50.1009.exe | C:\Program Files |
BSX-Setup-5.4.50.1009.exe | closebtn |
BSX-Setup-5.4.50.1009.exe | CustomInstall |
BSX-Setup-5.4.50.1009.exe | btnSelectDir |
BSX-Setup-5.4.50.1009.exe | DirText |
BSX-Setup-5.4.50.1009.exe | BtnOneClick |
BSX-Setup-5.4.50.1009.exe | BtnInstallFinished |
BSX-Setup-5.4.50.1009.exe | C:\Program Files |
BSX-Setup-5.4.50.1009.exe | showInstallPage |
BSX-Setup-5.4.50.1009.exe | 0% |