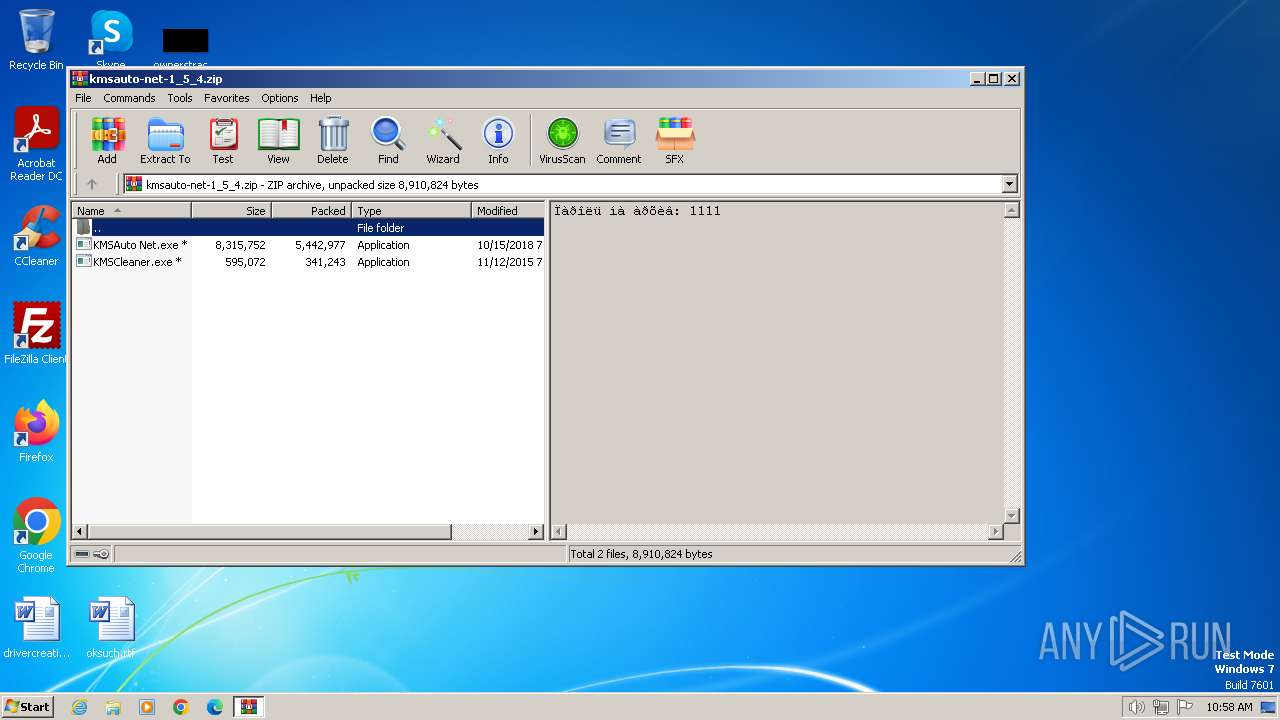
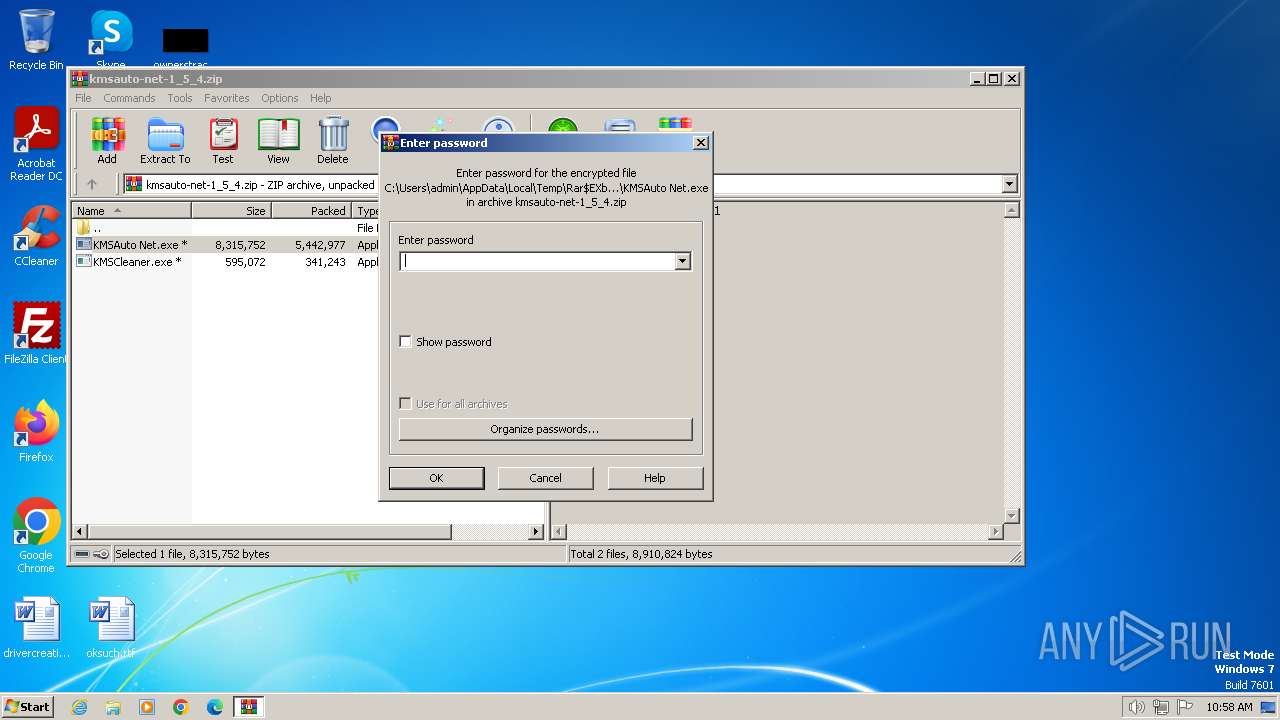
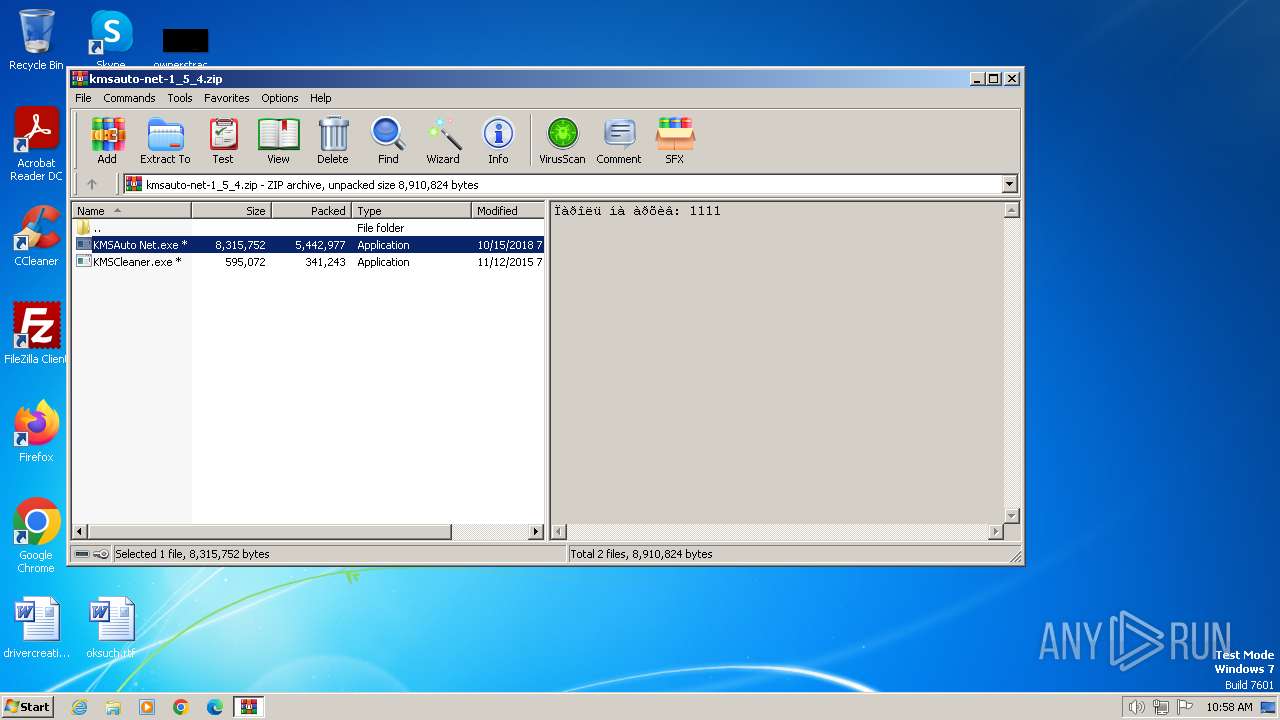
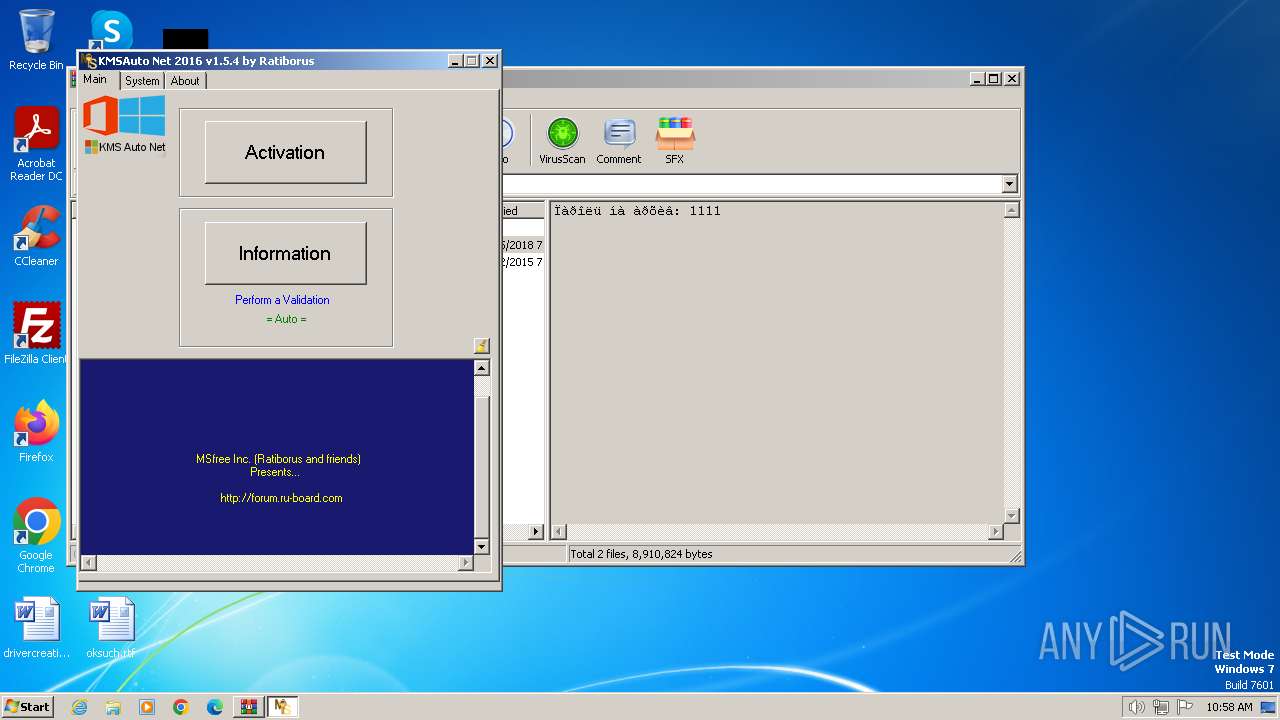
| File name: | kmsauto-net-1_5_4.zip |
| Full analysis: | https://app.any.run/tasks/d8558ec9-f1ba-42ad-af3e-a821dd90dd9e |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2024, 09:58:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=AES Encrypted |
| MD5: | 77B1A945EBA1451B24D08A1D3B99E08C |
| SHA1: | D20F524A697408607652377EF6568CCBE95E17E9 |
| SHA256: | F5C4883CD596C64288B1581F6B59999CD123A6C180B89E8388063A973FFDD7B6 |
| SSDEEP: | 98304:/iDT1ubpC9gd1vqNp8CBxpxmjre32BwpwMbwuM8UVsdpf9MBp8Pr3KPrlhf+/6Si:2xdYRo34 |
MALICIOUS
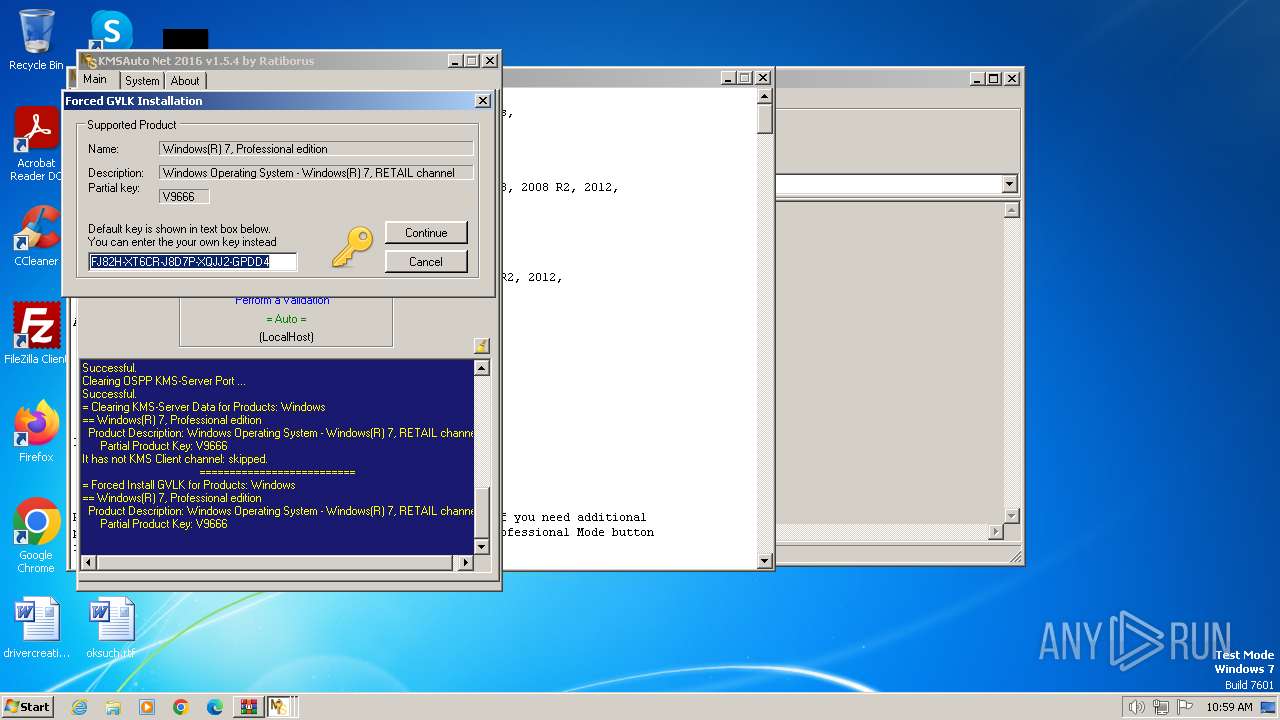
Drops the executable file immediately after the start
- KMSAuto Net.exe (PID: 1824)
- bin.dat (PID: 2348)
- AESDecoder.exe (PID: 2516)
- wzt.dat (PID: 3980)
- bin_x86.dat (PID: 1628)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 4008)
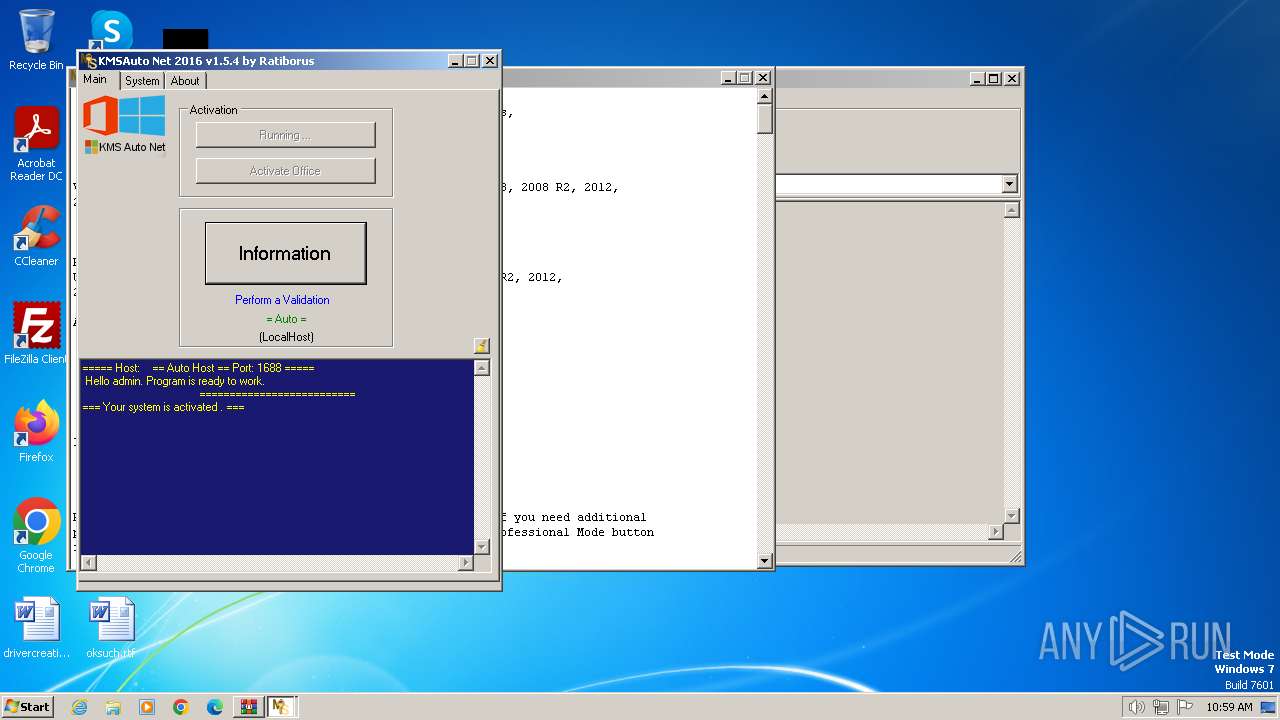
Starts CMD.EXE for commands execution
- KMSAuto Net.exe (PID: 1824)
- cmd.exe (PID: 4064)
Reads Internet Explorer settings
- KMSAuto Net.exe (PID: 1824)
Drops 7-zip archiver for unpacking
- KMSAuto Net.exe (PID: 1824)
Adds/modifies Windows certificates
- certmgr.exe (PID: 1792)
- certmgr.exe (PID: 3444)
Starts application with an unusual extension
- cmd.exe (PID: 2020)
- cmd.exe (PID: 948)
- cmd.exe (PID: 2096)
Process drops legitimate windows executable
- wzt.dat (PID: 3980)
- bin_x86.dat (PID: 1628)
Application launched itself
- cmd.exe (PID: 4064)
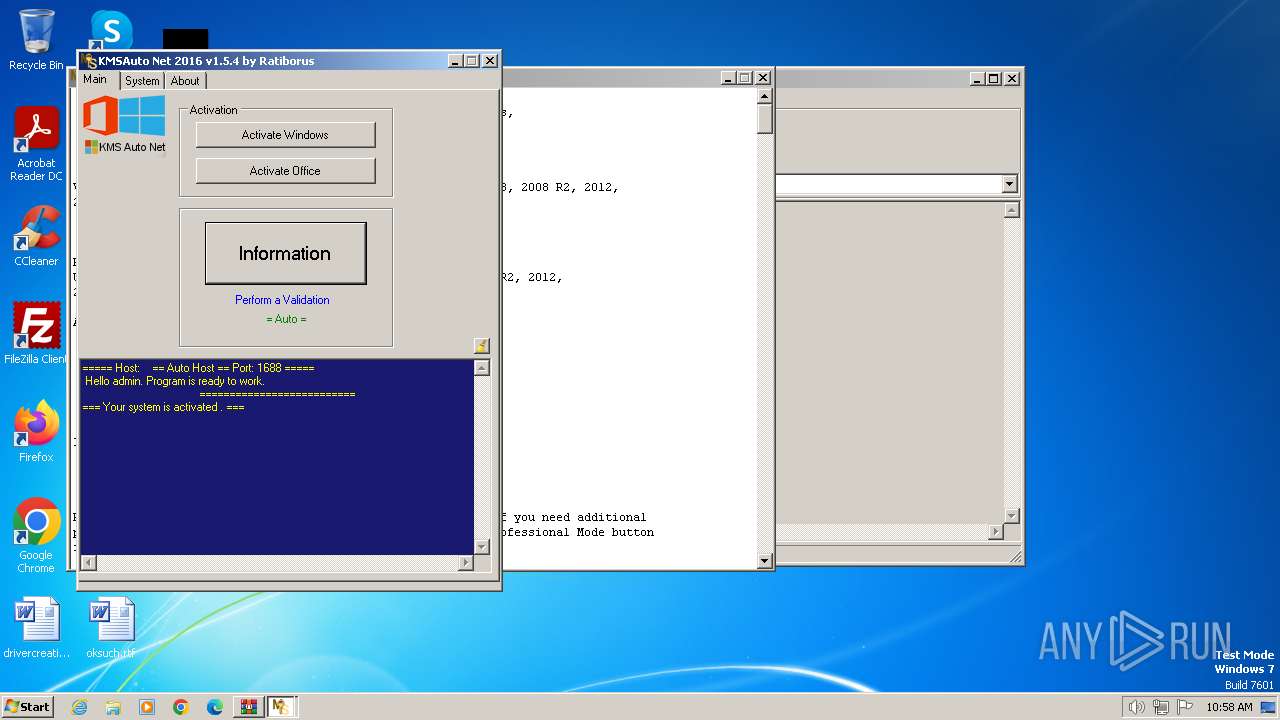
Creates or modifies Windows services
- KMSAuto Net.exe (PID: 1824)
Uses NETSH.EXE to add a firewall rule or allowed programs
- KMSAuto Net.exe (PID: 1824)
Starts SC.EXE for service management
- KMSAuto Net.exe (PID: 1824)
Executes as Windows Service
- KMSSS.exe (PID: 1268)
Uses REG/REGEDIT.EXE to modify registry
- KMSAuto Net.exe (PID: 1824)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- KMSAuto Net.exe (PID: 1824)
INFO
Reads the machine GUID from the registry
- KMSAuto Net.exe (PID: 1824)
- KMSSS.exe (PID: 1268)
Checks supported languages
- KMSAuto Net.exe (PID: 1824)
- wzt.dat (PID: 3980)
- bin.dat (PID: 2348)
- AESDecoder.exe (PID: 2516)
- certmgr.exe (PID: 1792)
- certmgr.exe (PID: 3444)
- KMSSS.exe (PID: 1268)
- bin_x86.dat (PID: 1628)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 4008)
Reads the computer name
- KMSAuto Net.exe (PID: 1824)
- KMSSS.exe (PID: 1268)
Creates files or folders in the user directory
- KMSAuto Net.exe (PID: 1824)
Reads Environment values
- KMSAuto Net.exe (PID: 1824)
Reads product name
- KMSAuto Net.exe (PID: 1824)
Creates files in the program directory
- cmd.exe (PID: 2968)
- KMSAuto Net.exe (PID: 1824)
- AESDecoder.exe (PID: 2516)
- wzt.dat (PID: 3980)
- bin.dat (PID: 2348)
- KMSSS.exe (PID: 1268)
- bin_x86.dat (PID: 1628)
Reads Microsoft Office registry keys
- KMSAuto Net.exe (PID: 1824)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2018:10:15 09:59:34 |
| ZipCRC: | 0x0da1fbfe |
| ZipCompressedSize: | 5442977 |
| ZipUncompressedSize: | 8315752 |
| ZipFileName: | KMSAuto Net.exe |
Total processes
107
Monitored processes
39
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 712 | C:\Windows\System32\cmd.exe /D /c del /F /Q "wzt.dat" | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 920 | C:\Windows\System32\cmd.exe /D /c del /F /Q "AESDecoder.exe" | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 948 | C:\Windows\System32\cmd.exe /D /c bin_x86.dat -y -pkmsauto | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1264 | C:\Windows\System32\Netsh Advfirewall Firewall delete rule name="0pen Port KMS" protocol=TCP | C:\Windows\System32\netsh.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1268 | "C:\ProgramData\KMSAuto\bin\KMSSS.exe" -Port 1688 -PWin RandomKMSPID -PO14 RandomKMSPID -PO15 RandomKMSPID -PO16 RandomKMSPID -AI 43200 -RI 43200 -Log -IP | C:\ProgramData\KMSAuto\bin\KMSSS.exe | — | services.exe | |||||||||||
User: SYSTEM Company: MSFree Inc. Integrity Level: SYSTEM Description: KMS emulator by Ratiborus. Version: 2.0.7.0 Modules
| |||||||||||||||
| 1404 | "C:\Windows\System32\cmd.exe" /c rd "C:\ProgramData\KMSAuto\wzt" /S /Q | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1628 | bin_x86.dat -y -pkmsauto | C:\ProgramData\KMSAuto\bin_x86.dat | — | cmd.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7z Console SFX Exit code: 0 Version: 15.14 Modules
| |||||||||||||||
| 1792 | certmgr.exe -add wzteam.cer -n wzteam -s -r localMachine ROOT | C:\ProgramData\KMSAuto\wzt\certmgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ECM Certificate Manager Exit code: 0 Version: 6.3.9600.17298 (winblue.141024-1500) Modules
| |||||||||||||||
| 1812 | C:\Windows\System32\reg delete "HKEY_USERS\S-1-5-20\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform\0ff1ce15-a989-479d-af46-f275c6370663" /f | C:\Windows\System32\reg.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1824 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb4008.10004\KMSAuto Net.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb4008.10004\KMSAuto Net.exe | WinRAR.exe | ||||||||||||
User: admin Company: MSFree Inc. Integrity Level: HIGH Description: KMSAuto Net Version: 1.5.4 Modules
| |||||||||||||||
Total events
7 658
Read events
7 514
Write events
138
Delete events
6
Modification events
| (PID) Process: | (4008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (4008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (4008) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (4008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (4008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (4008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\kmsauto-net-1_5_4.zip | |||
| (PID) Process: | (4008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
20
Suspicious files
5
Text files
3
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4008 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb4008.10004\KMSAuto Net.exe | executable | |
MD5:— | SHA256:— | |||
| 4008 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb4008.10004\KMSCleaner.exe | executable | |
MD5:— | SHA256:— | |||
| 1824 | KMSAuto Net.exe | C:\Users\admin\AppData\Local\MSfree Inc\kmsauto.ini | text | |
MD5:— | SHA256:— | |||
| 3516 | cmd.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb4008.10004\test.test | text | |
MD5:— | SHA256:— | |||
| 1824 | KMSAuto Net.exe | C:\ProgramData\KMSAuto\wzt.dat | executable | |
MD5:— | SHA256:— | |||
| 3980 | wzt.dat | C:\ProgramData\KMSAuto\wzt\wzteam.cer | binary | |
MD5:— | SHA256:— | |||
| 3980 | wzt.dat | C:\ProgramData\KMSAuto\wzt\certmgr.exe | executable | |
MD5:— | SHA256:— | |||
| 1824 | KMSAuto Net.exe | C:\ProgramData\KMSAuto\bin.dat | executable | |
MD5:— | SHA256:— | |||
| 2348 | bin.dat | C:\ProgramData\KMSAuto\bin\TunMirror2.exe.aes | binary | |
MD5:— | SHA256:— | |||
| 2348 | bin.dat | C:\ProgramData\KMSAuto\bin\KMSSS.exe.aes | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |