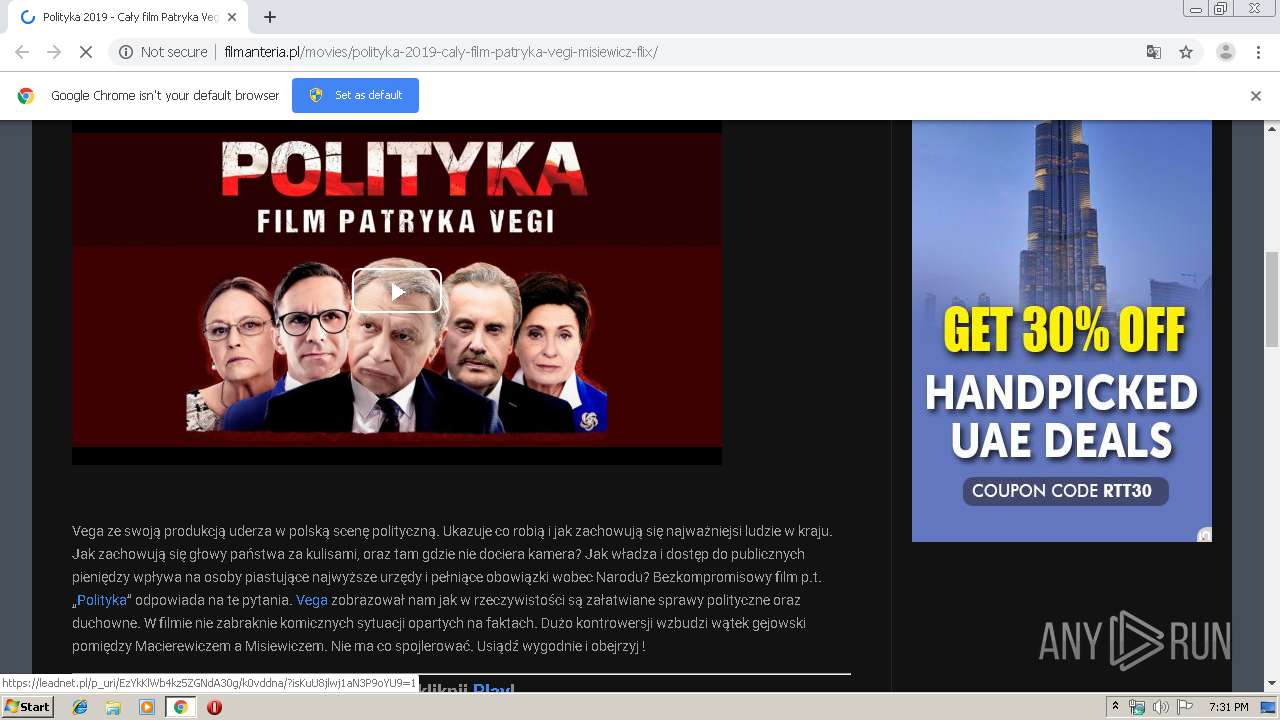
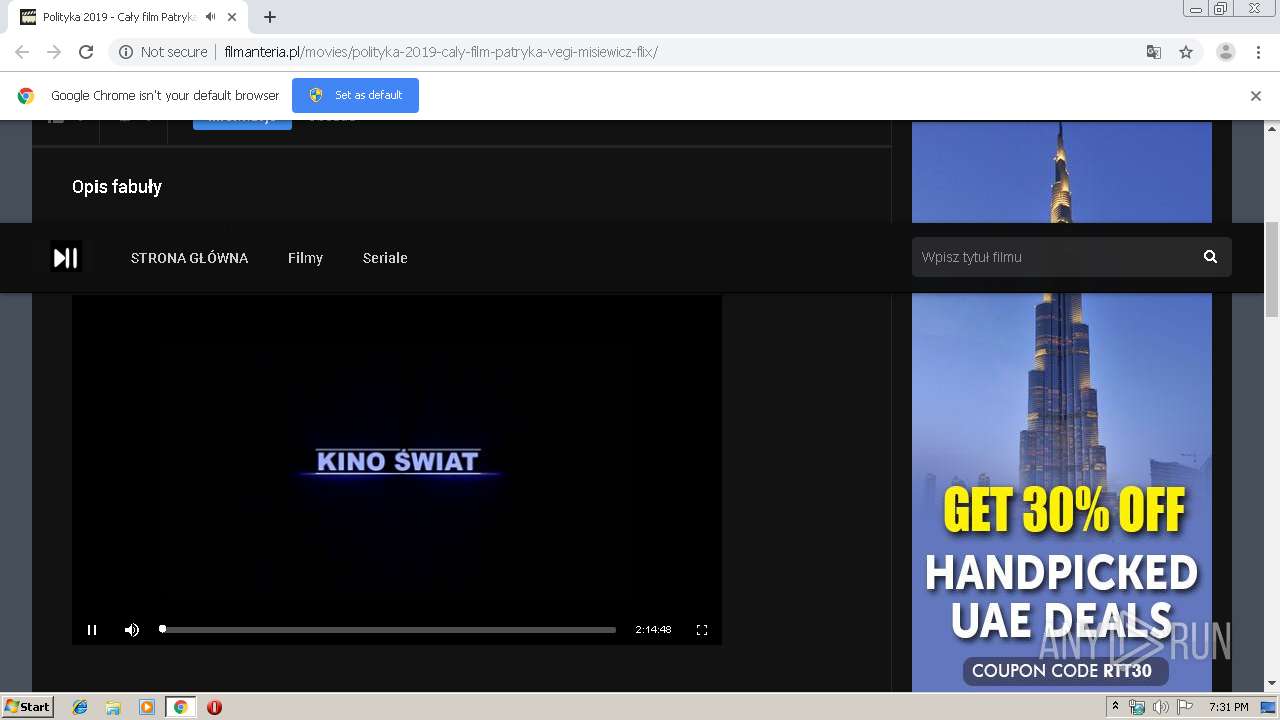
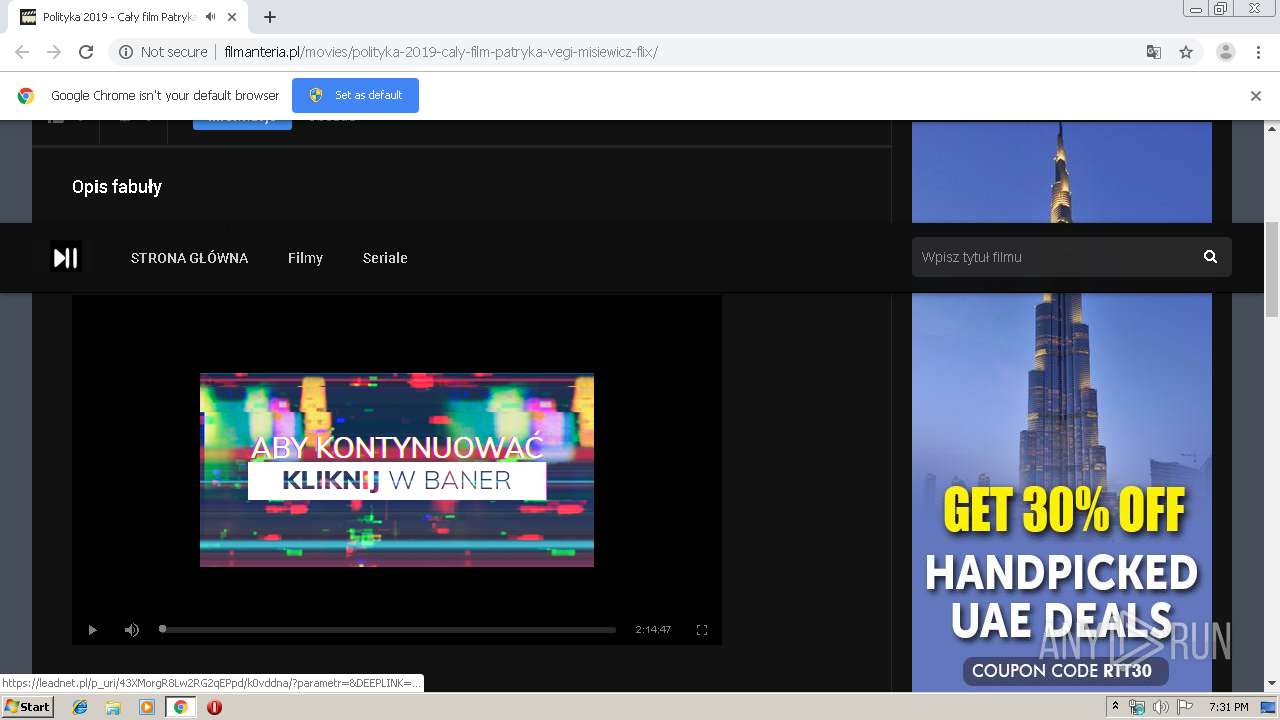
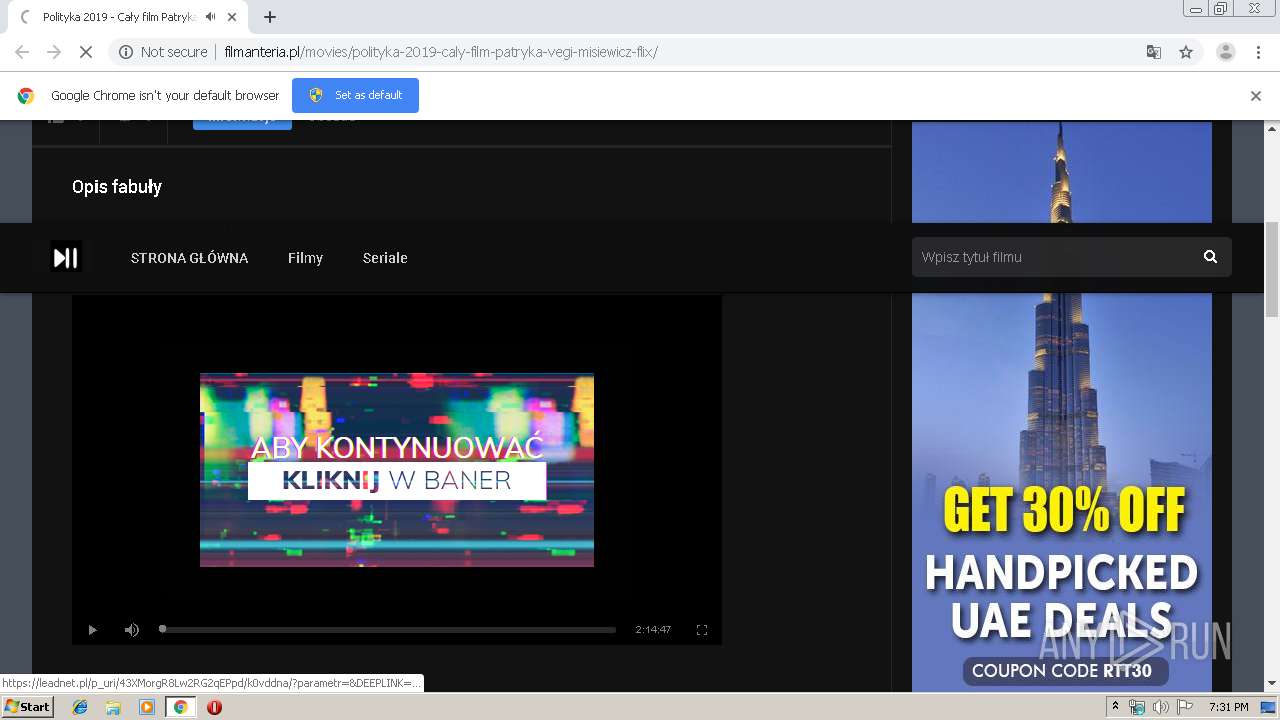
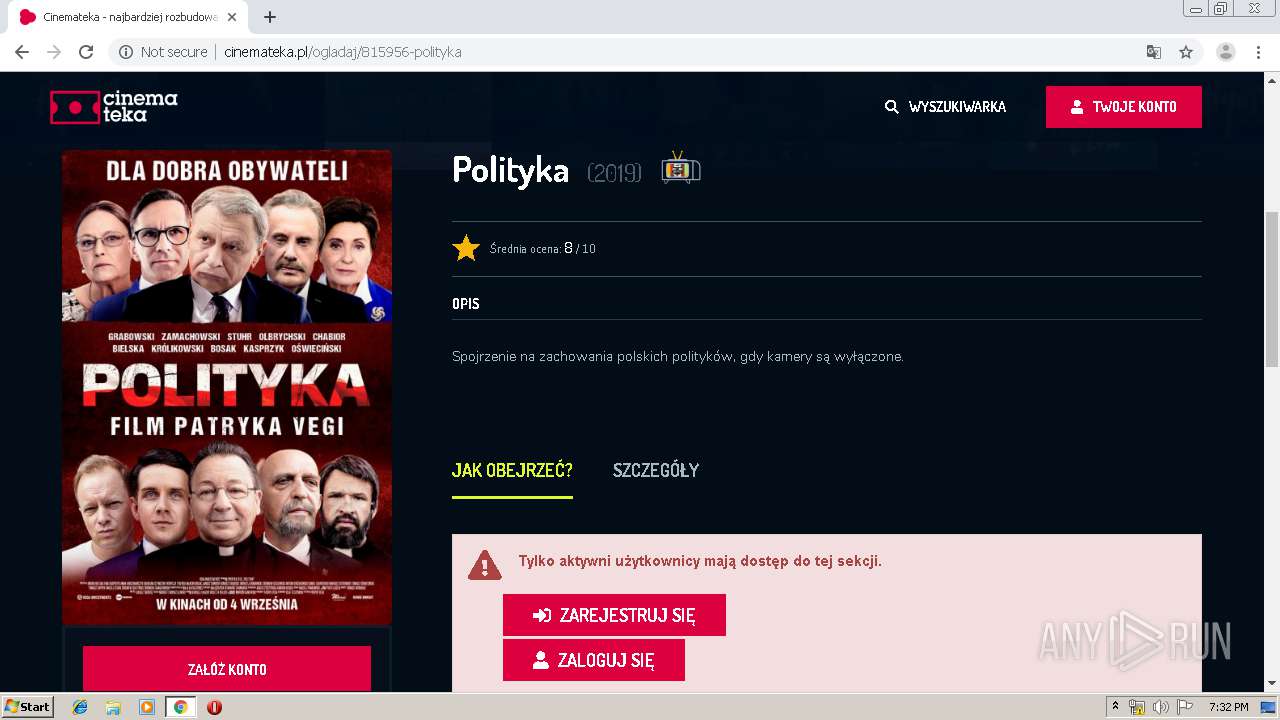
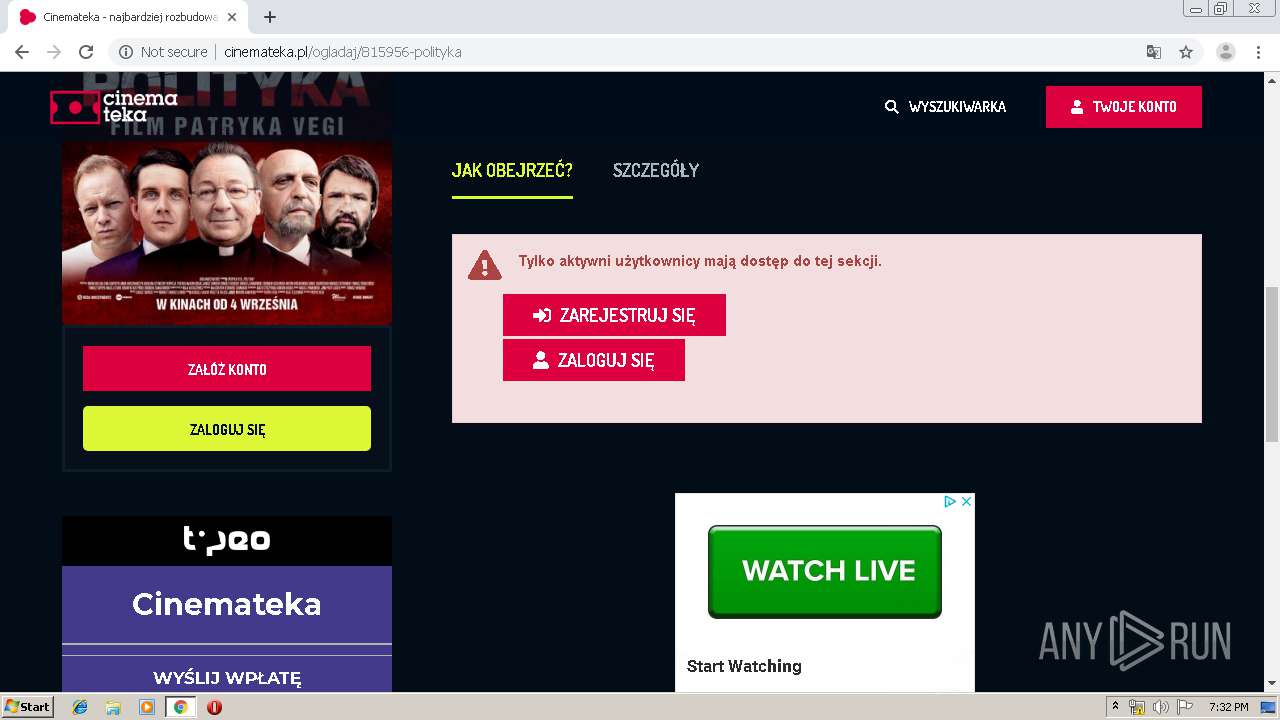
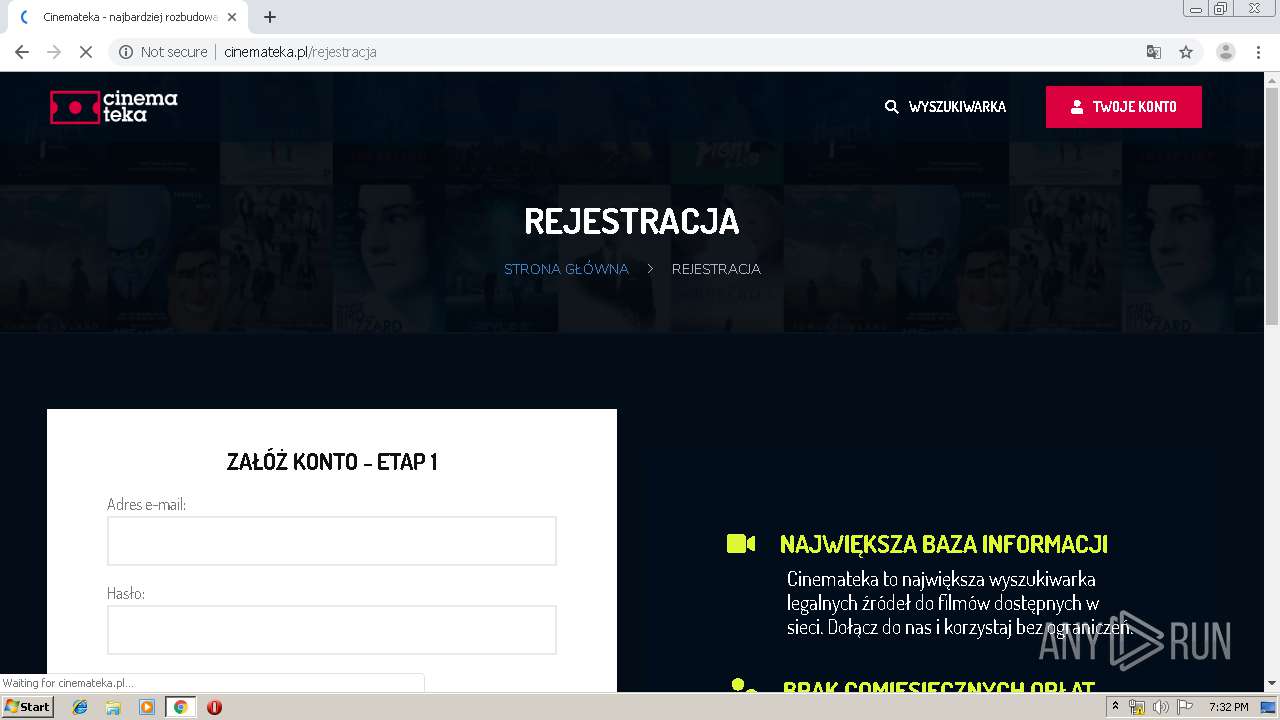
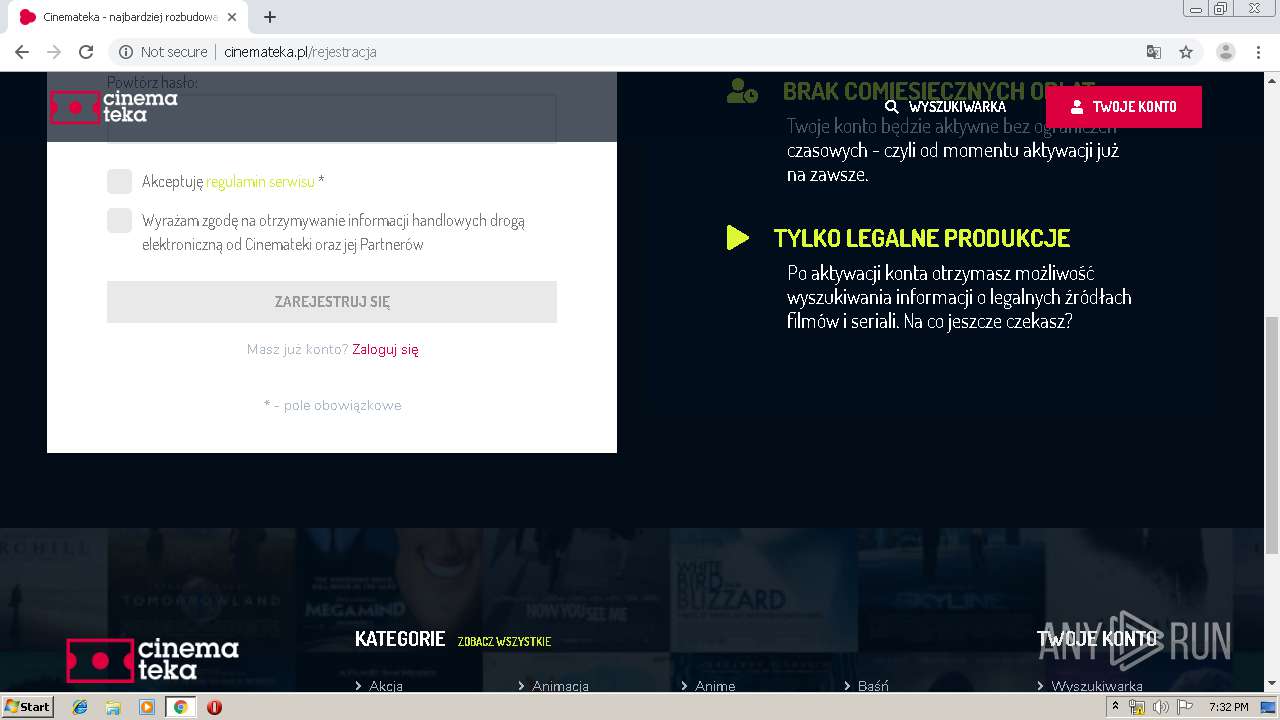
| URL: | http://filmanteria.pl/movies/polityka-2019-caly-film-patryka-vegi-misiewicz-flix/ |
| Full analysis: | https://app.any.run/tasks/9f30a0d4-508c-41ec-a1f3-e0a3368ecb60 |
| Verdict: | No threats detected |
| Analysis date: | November 08, 2019, 19:30:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 88E7E1034D7BA86006B1F5913EB24D74 |
| SHA1: | 4E0FE666D934FA6B7E4E6CE5CBD874997EC9DA56 |
| SHA256: | F5BF808ED1B5B64DEACDE1041CCC69B9D57FF28E27E952A91F7AEA6C6F2F1BAD |
| SSDEEP: | 3:N1KYlM2JT1Q/EFKaccTAPIIUAqKn:CYzT1QWKaccMP13qK |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1608)
INFO
Application launched itself
- chrome.exe (PID: 1608)
Changes settings of System certificates
- chrome.exe (PID: 3784)
Reads the hosts file
- chrome.exe (PID: 3784)
- chrome.exe (PID: 1608)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
84
Monitored processes
50
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=936,8126699356046047243,15623242143448375955,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=334961710044084408 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3396 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=936,8126699356046047243,15623242143448375955,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8743116166307723024 --mojo-platform-channel-handle=5204 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=936,8126699356046047243,15623242143448375955,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14213501164425056690 --mojo-platform-channel-handle=4968 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=936,8126699356046047243,15623242143448375955,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6927381243810884615 --mojo-platform-channel-handle=5080 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 792 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=936,8126699356046047243,15623242143448375955,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10723861963574385472 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3304 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=936,8126699356046047243,15623242143448375955,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17530512051002662446 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3452 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=936,8126699356046047243,15623242143448375955,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4855818030151700568 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3792 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=936,8126699356046047243,15623242143448375955,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8091448516750252619 --renderer-client-id=48 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5768 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=936,8126699356046047243,15623242143448375955,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16677278026200676959 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2204 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=936,8126699356046047243,15623242143448375955,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14600962130047656879 --mojo-platform-channel-handle=3060 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
718
Read events
577
Write events
135
Delete events
6
Modification events
| (PID) Process: | (1608) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1608) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1608) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1608) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1608) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1608) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1608) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1608) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (1608) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1608) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1608-13217715078093500 |
Value: 259 | |||
Executable files
0
Suspicious files
226
Text files
303
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39b754.TMP | — | |
MD5:— | SHA256:— | |||
| 1608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39b754.TMP | — | |
MD5:— | SHA256:— | |||
| 1608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ff5dd2fe-1512-4cf9-b489-004b303b2e00.tmp | — | |
MD5:— | SHA256:— | |||
| 1608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
83
TCP/UDP connections
191
DNS requests
94
Threats
38
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3784 | chrome.exe | GET | 200 | 81.171.31.230:80 | http://filmanteria.pl/movies/polityka-2019-caly-film-patryka-vegi-misiewicz-flix/ | NL | html | 11.1 Kb | suspicious |
3784 | chrome.exe | GET | 200 | 81.171.31.230:80 | http://filmanteria.pl/wp-content/themes/DooPlay%202.1.3.8/assets/css/front.icons.css?ver=2.1.3.8 | NL | text | 1.47 Kb | suspicious |
3784 | chrome.exe | GET | 200 | 81.171.31.230:80 | http://filmanteria.pl/wp-content/themes/DooPlay%202.1.3.8/assets/css/front.style.css?ver=2.1.3.8 | NL | text | 15.7 Kb | suspicious |
3784 | chrome.exe | GET | 200 | 81.171.31.230:80 | http://filmanteria.pl/wp-content/themes/DooPlay%202.1.3.8/assets/css/front.mobile.css?ver=2.1.3.8 | NL | text | 2.12 Kb | suspicious |
3784 | chrome.exe | GET | 200 | 172.217.18.98:80 | http://pagead2.googlesyndication.com/pagead/js/adsbygoogle.js | US | text | 36.7 Kb | whitelisted |
3784 | chrome.exe | GET | 200 | 81.171.31.230:80 | http://filmanteria.pl/wp-content/themes/DooPlay%202.1.3.8/assets/css/front.owl.css?ver=2.1.3.8 | NL | text | 780 b | suspicious |
3784 | chrome.exe | GET | 200 | 81.171.31.230:80 | http://filmanteria.pl/wp-content/themes/DooPlay%202.1.3.8/assets/css/front.gallery.css?ver=2.1.3.8 | NL | text | 1.12 Kb | suspicious |
3784 | chrome.exe | GET | 200 | 81.171.31.230:80 | http://filmanteria.pl/wp-content/themes/DooPlay%202.1.3.8/assets/js/front.ajax.js?ver=2.1.3.8 | NL | text | 2.01 Kb | suspicious |
3784 | chrome.exe | GET | 200 | 81.171.31.230:80 | http://filmanteria.pl/wp-includes/css/dist/block-library/style.min.css?ver=5.1.3 | NL | text | 4.16 Kb | suspicious |
3784 | chrome.exe | GET | 200 | 81.171.31.230:80 | http://filmanteria.pl/wp-content/themes/DooPlay%202.1.3.8/assets/css/colors.dark.css?ver=2.1.3.8 | NL | text | 7.83 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3784 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3784 | chrome.exe | 81.171.31.230:80 | filmanteria.pl | LeaseWeb Netherlands B.V. | NL | malicious |
3784 | chrome.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
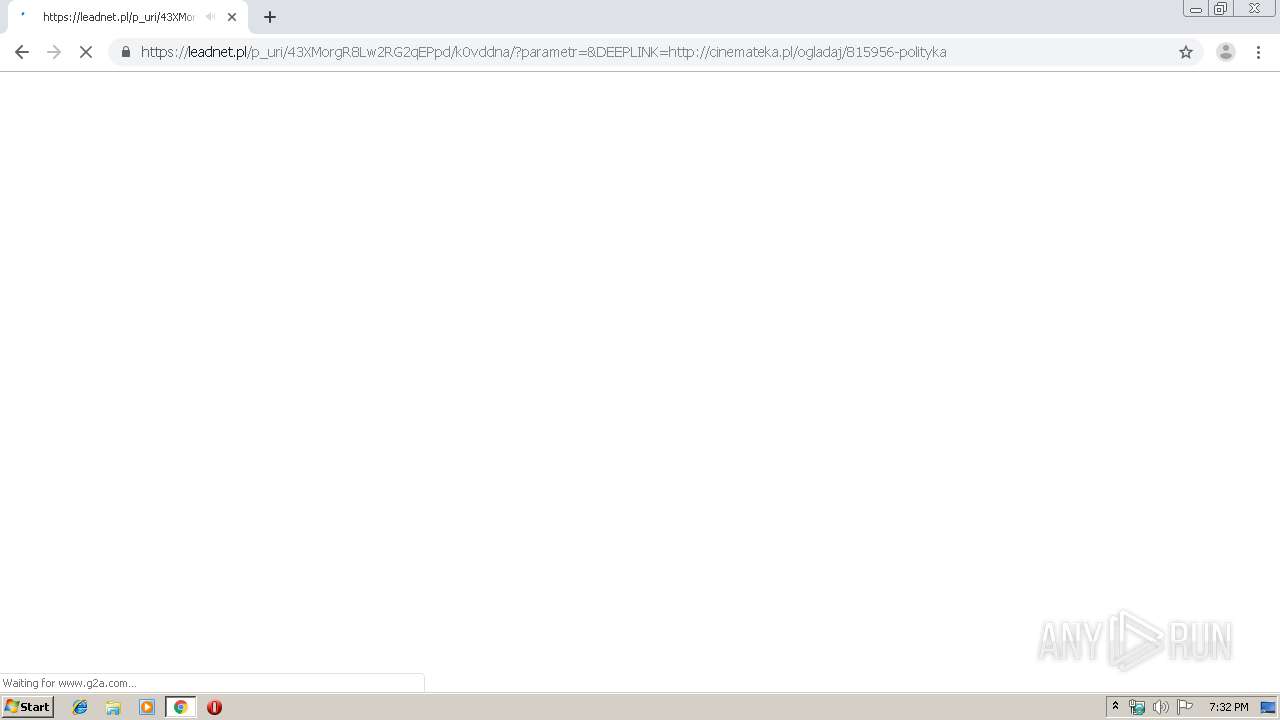
3784 | chrome.exe | 104.27.140.30:443 | lnaff.pl | Cloudflare Inc | US | shared |
3784 | chrome.exe | 172.217.18.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3784 | chrome.exe | 172.217.23.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3784 | chrome.exe | 104.16.59.155:443 | image.tmdb.org | Cloudflare Inc | US | shared |
3784 | chrome.exe | 172.217.23.98:443 | adservice.google.com | Google Inc. | US | whitelisted |
3784 | chrome.exe | 172.217.21.194:443 | www.googletagservices.com | Google Inc. | US | whitelisted |
3784 | chrome.exe | 192.0.73.2:80 | 1.gravatar.com | Automattic, Inc | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
filmanteria.pl |
| suspicious |
accounts.google.com |
| shared |
code.jquery.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
lnaff.pl |
| unknown |
s.w.org |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
image.tmdb.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3784 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3784 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3784 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3784 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3784 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3784 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3784 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3784 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3784 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3784 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |