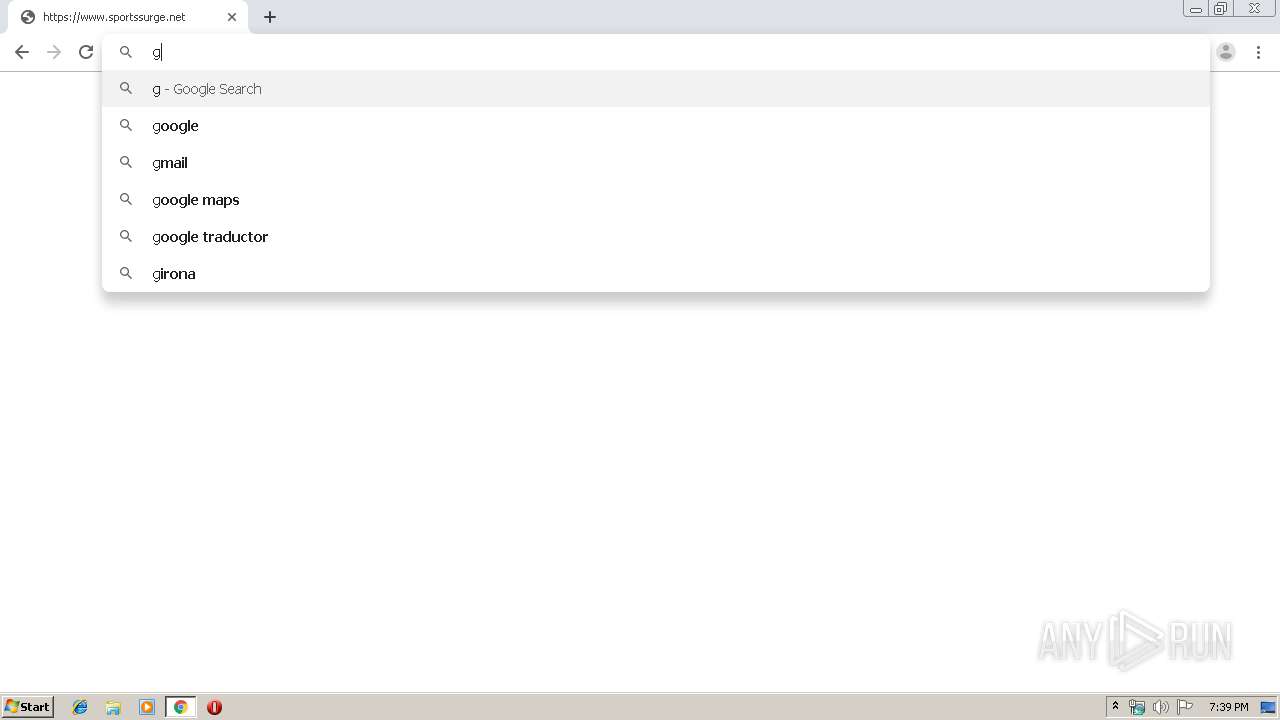
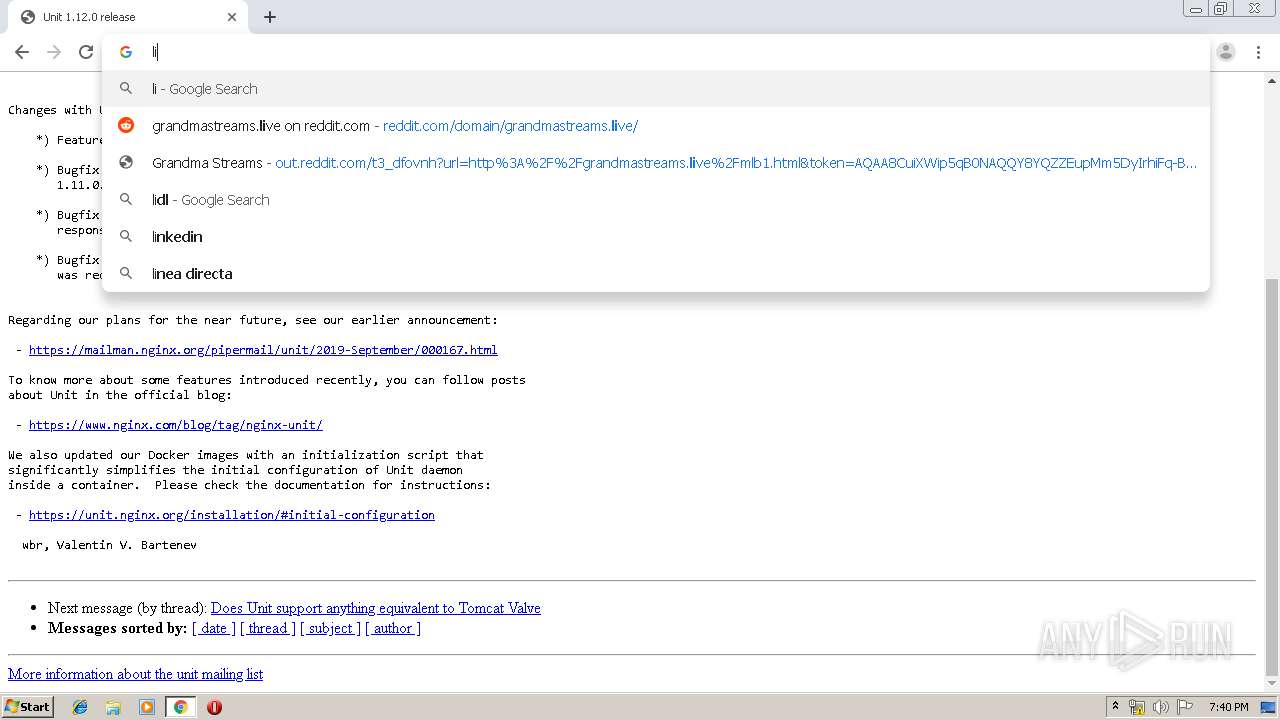
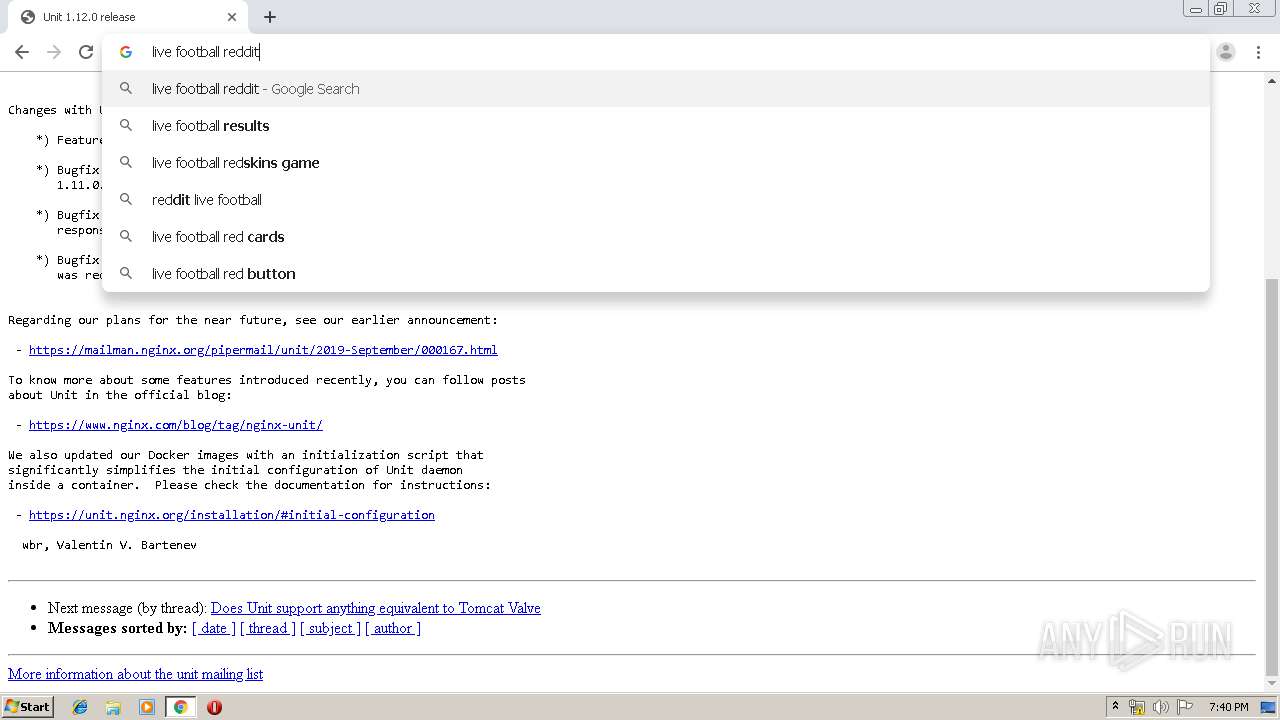
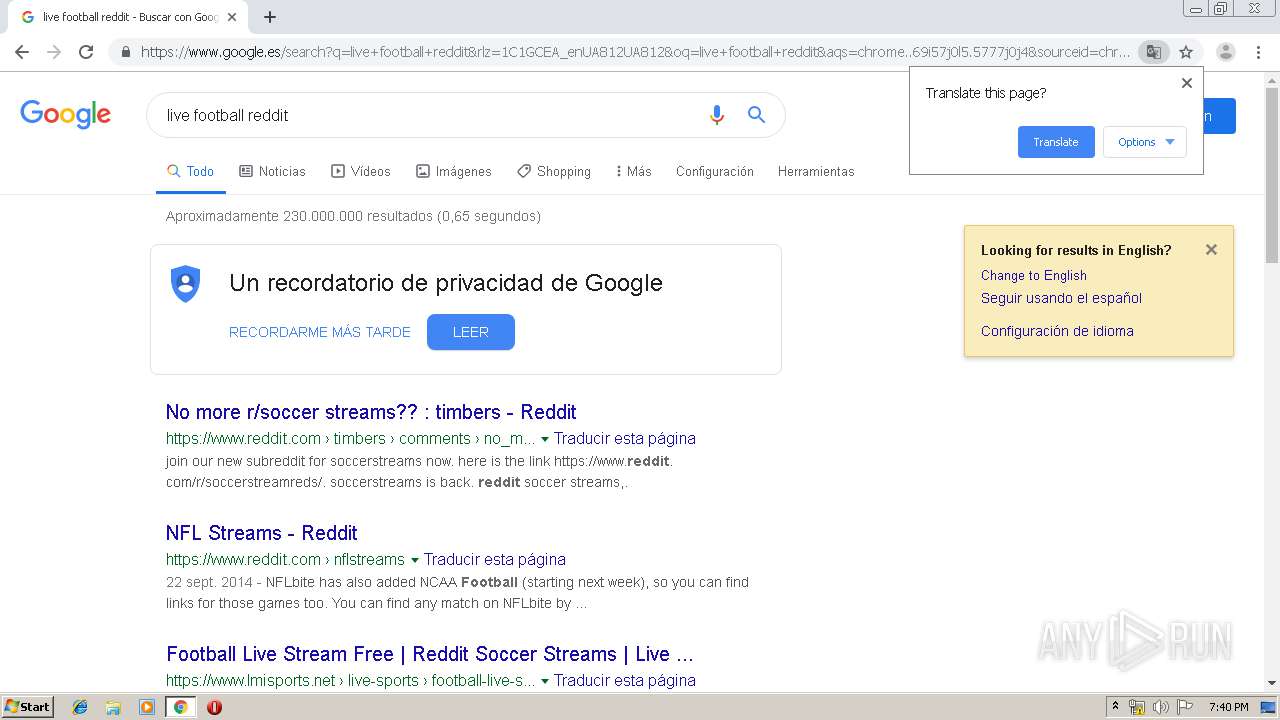
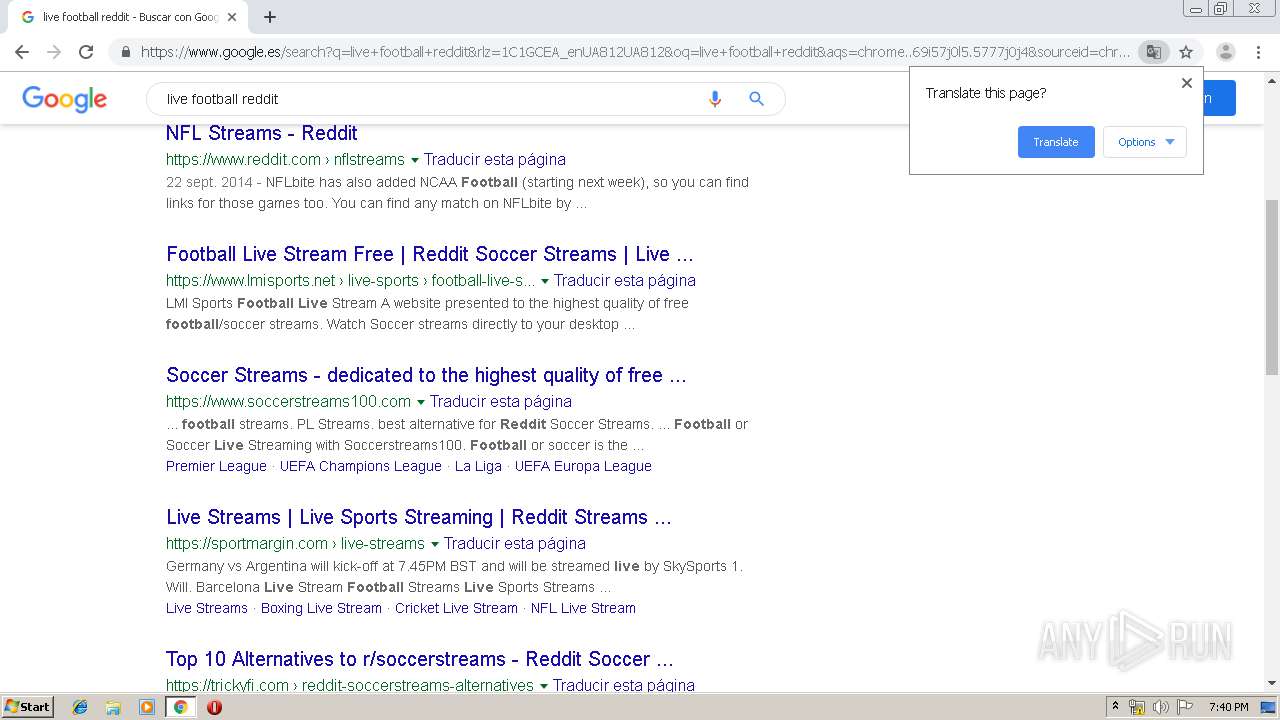
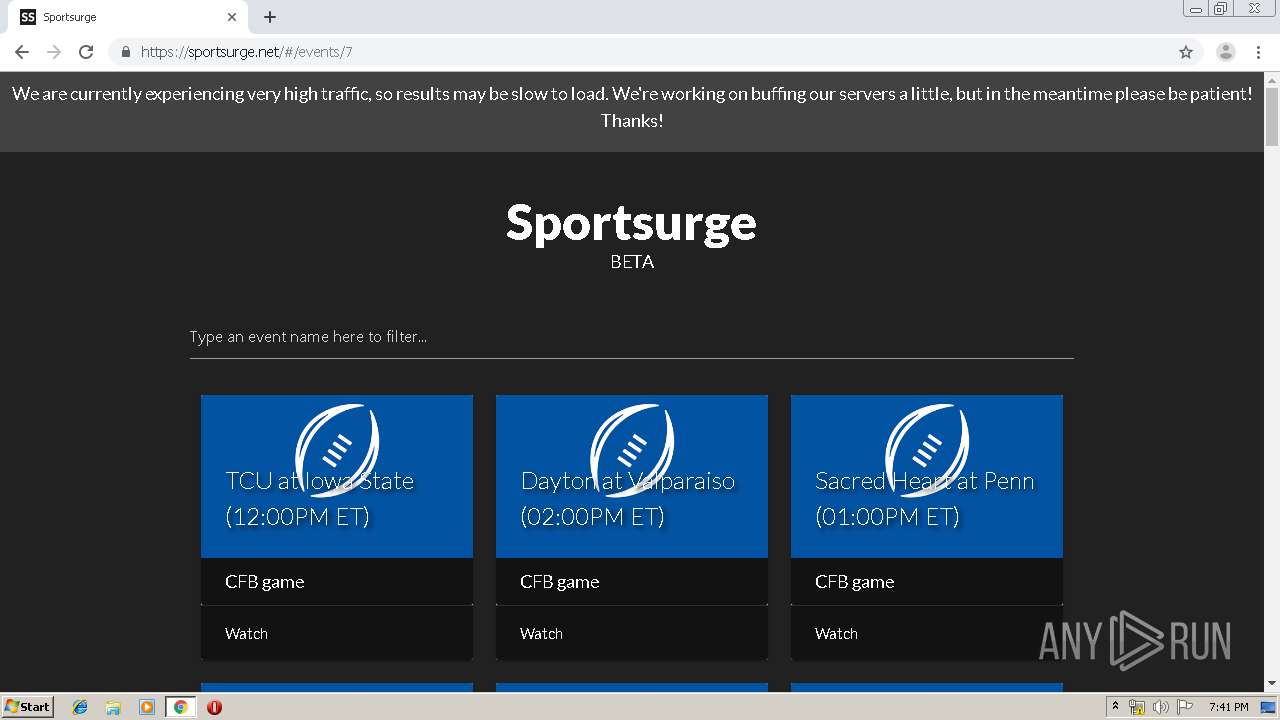
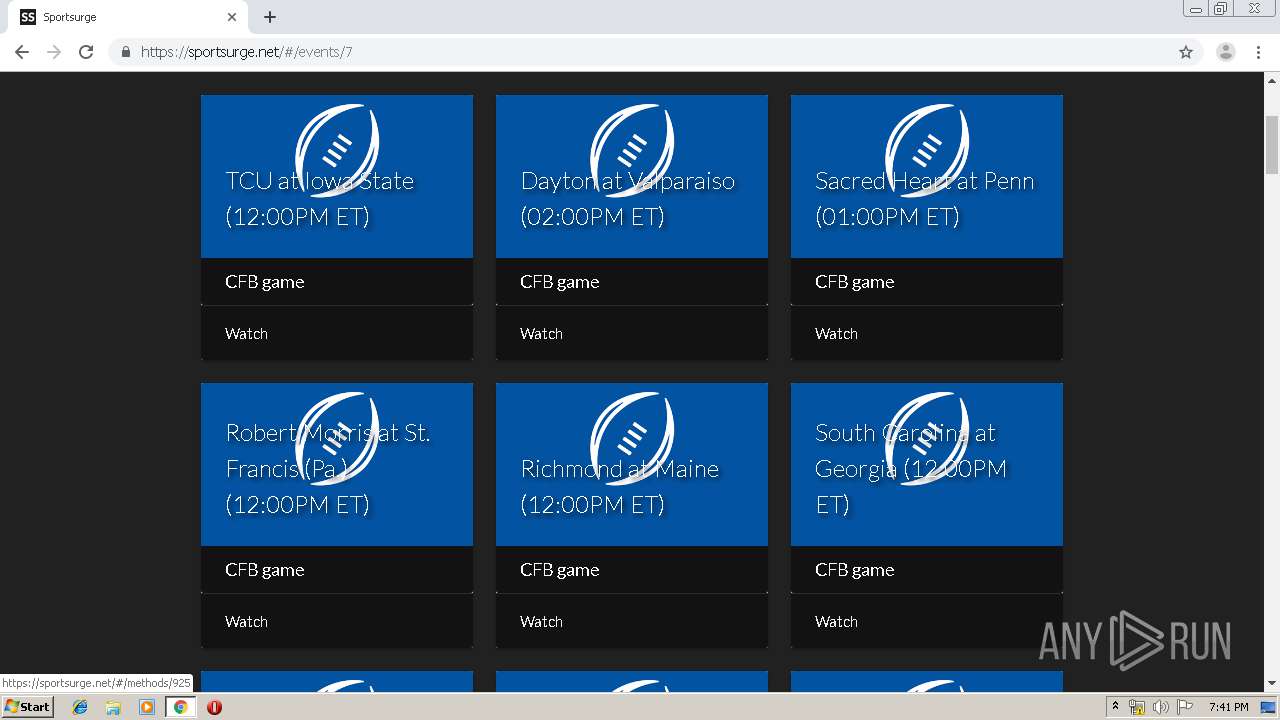
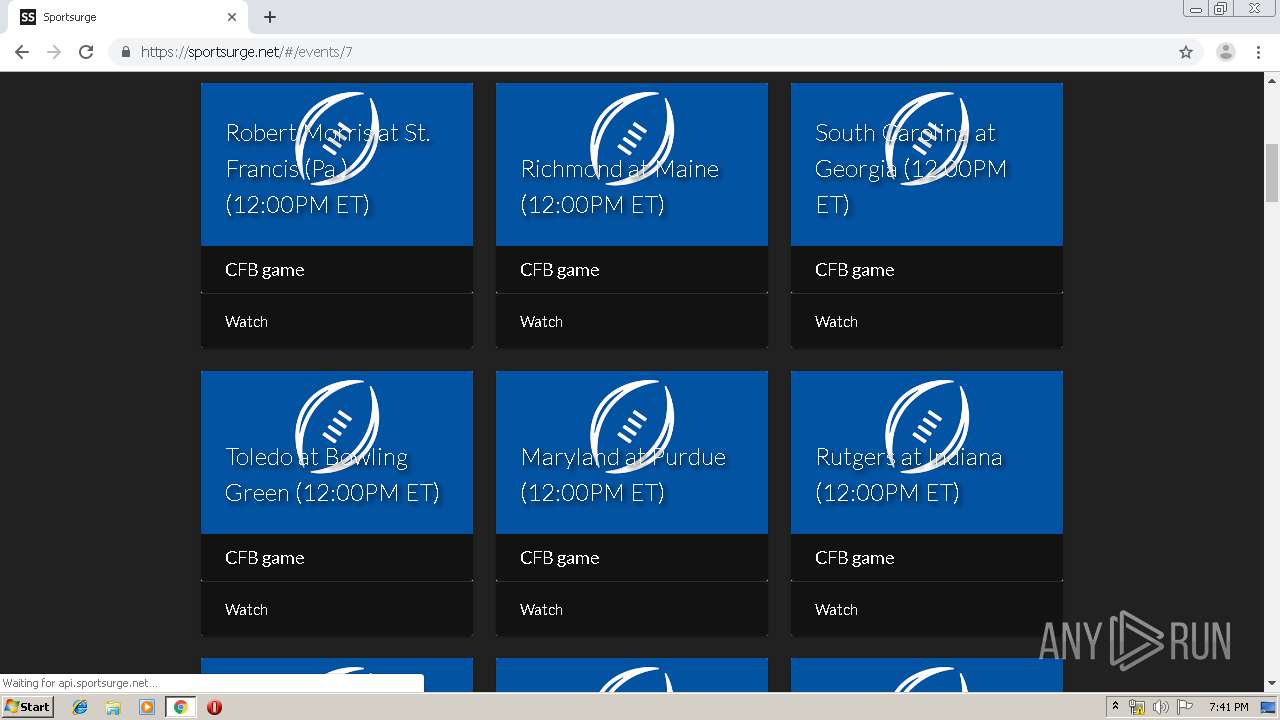
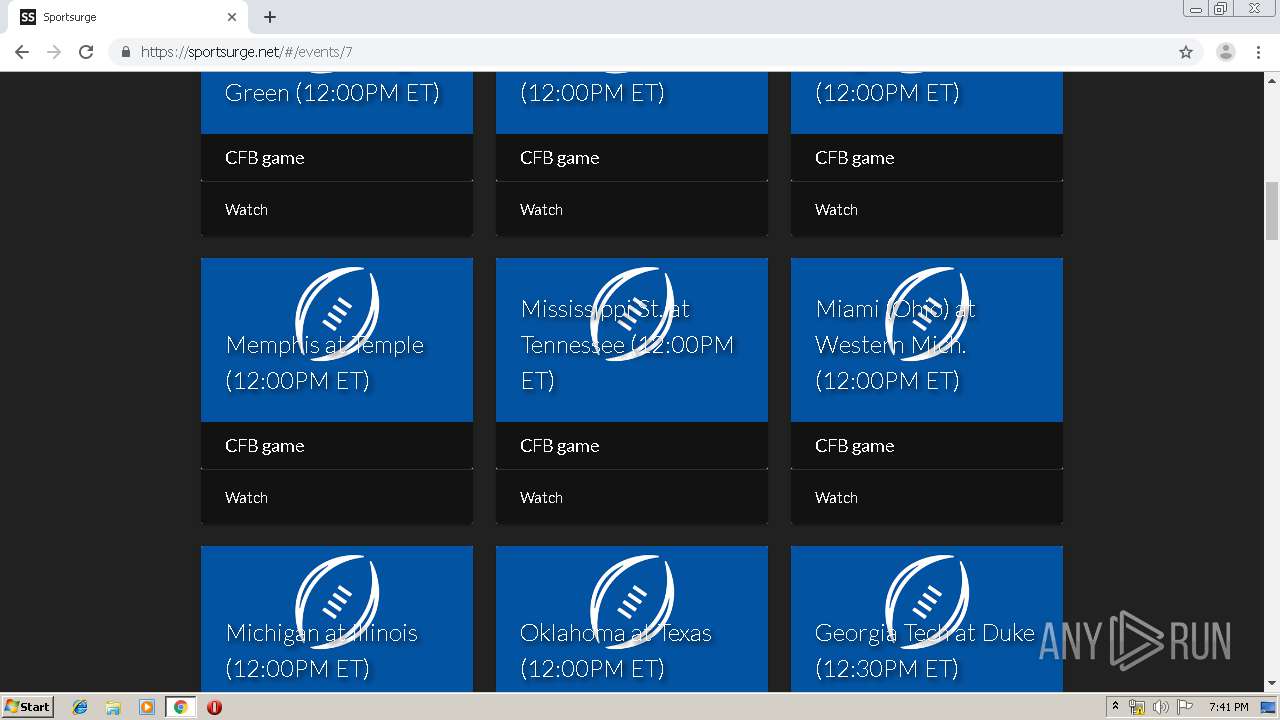
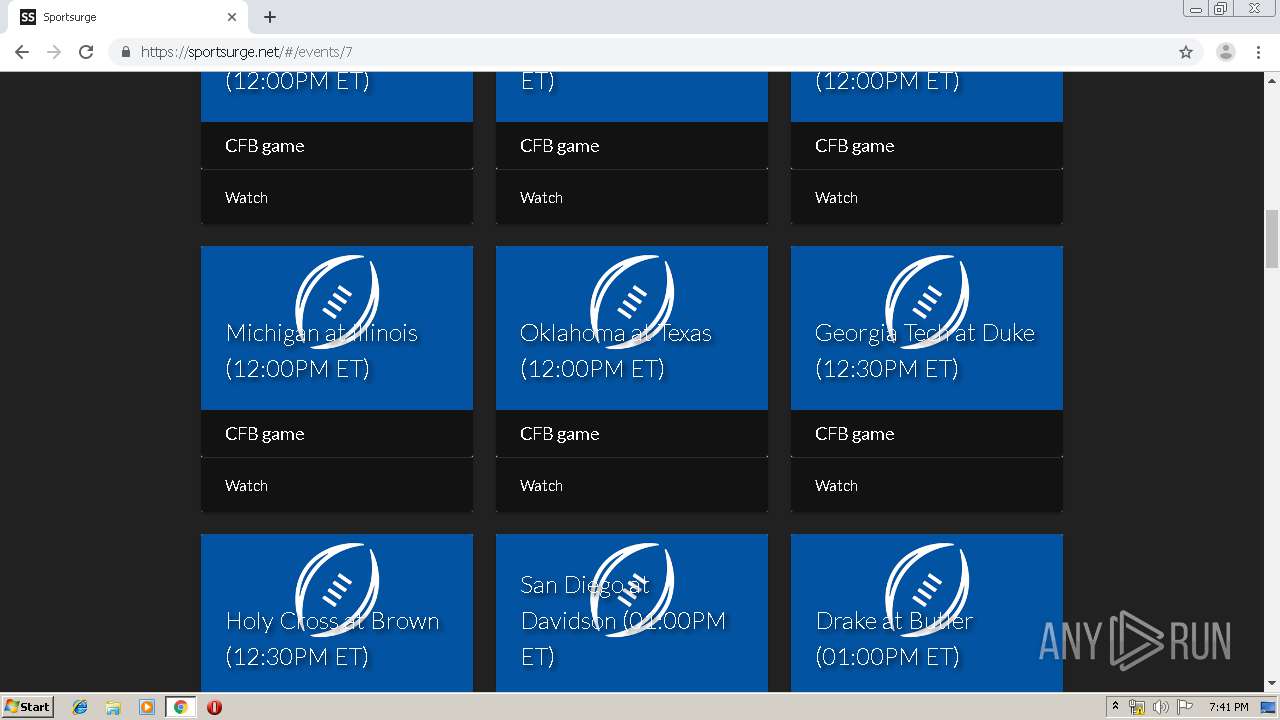
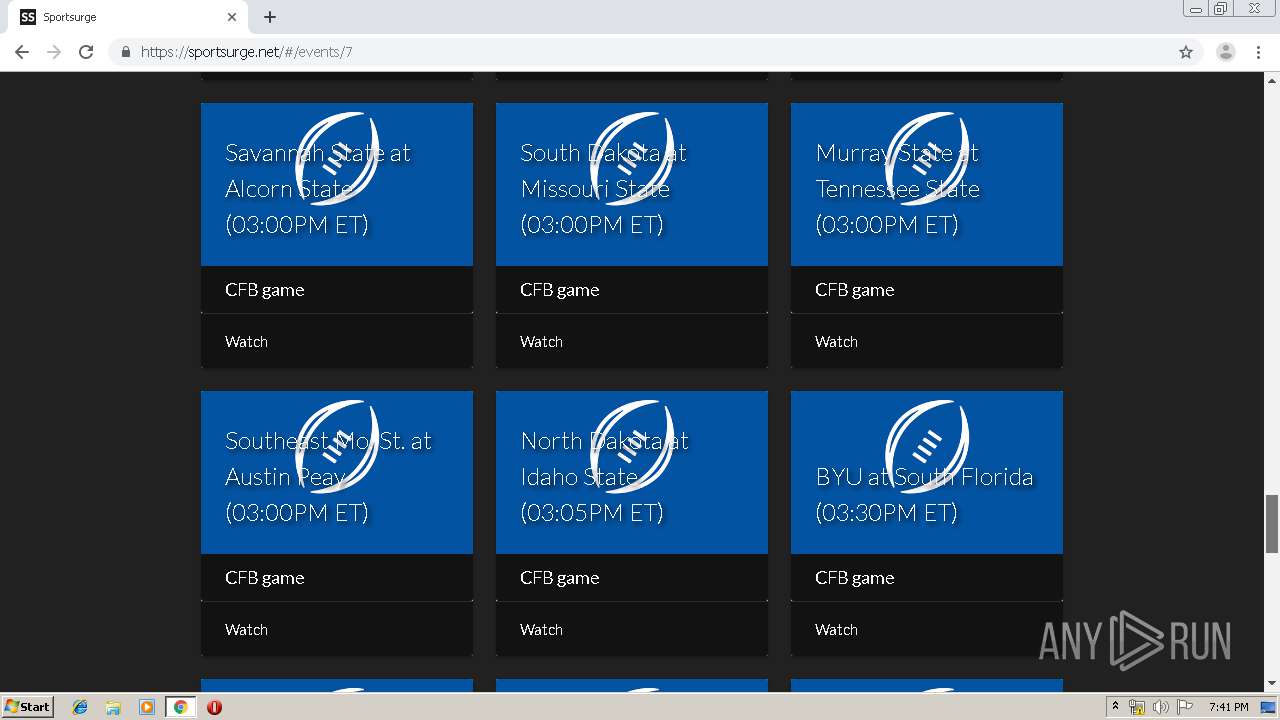
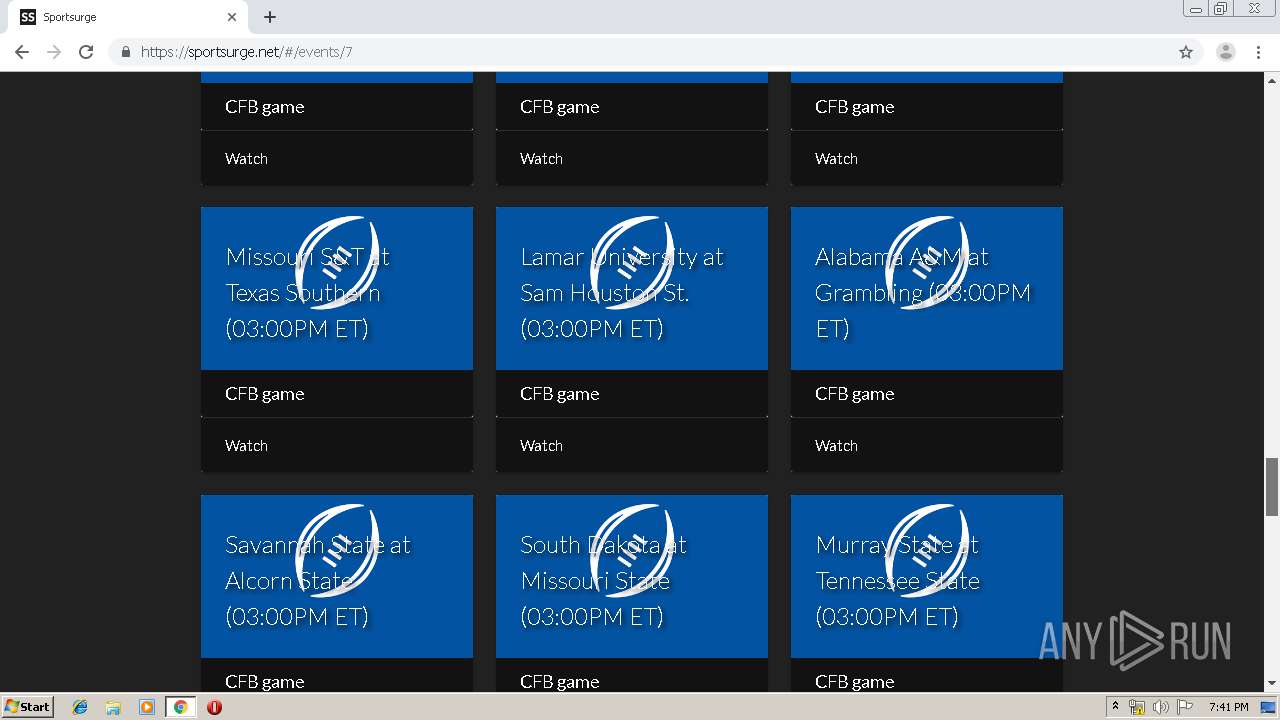
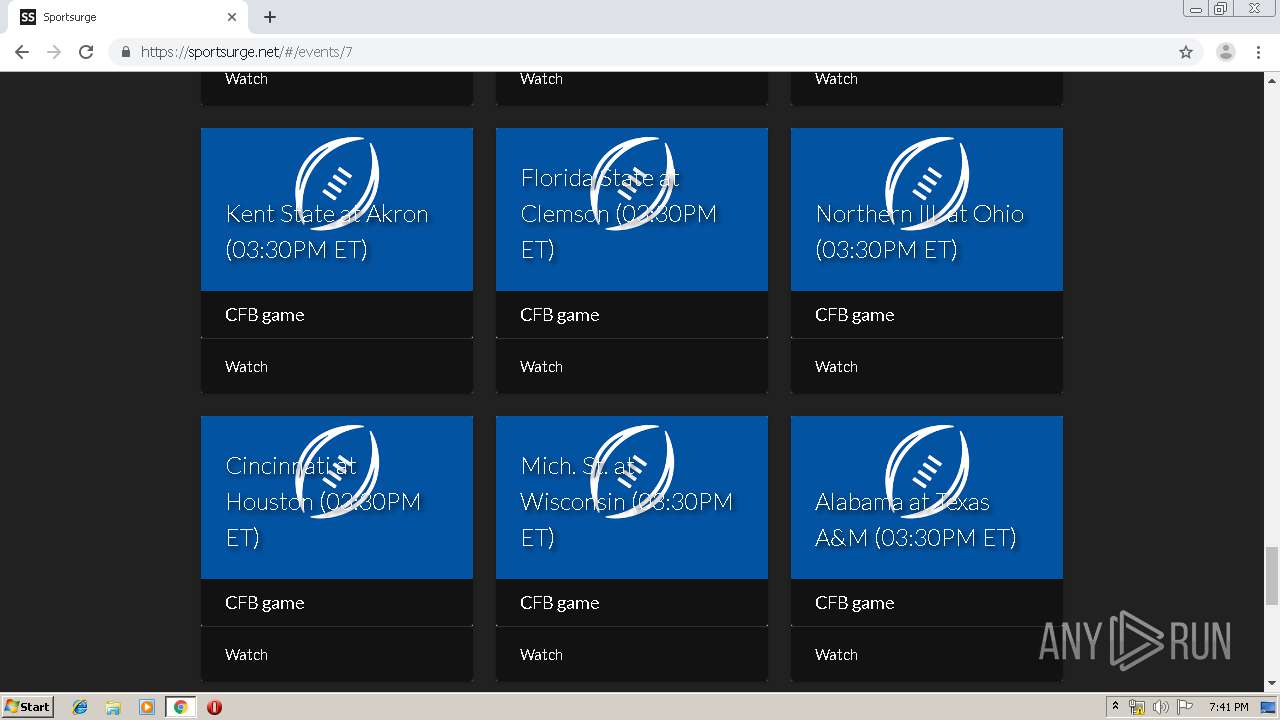
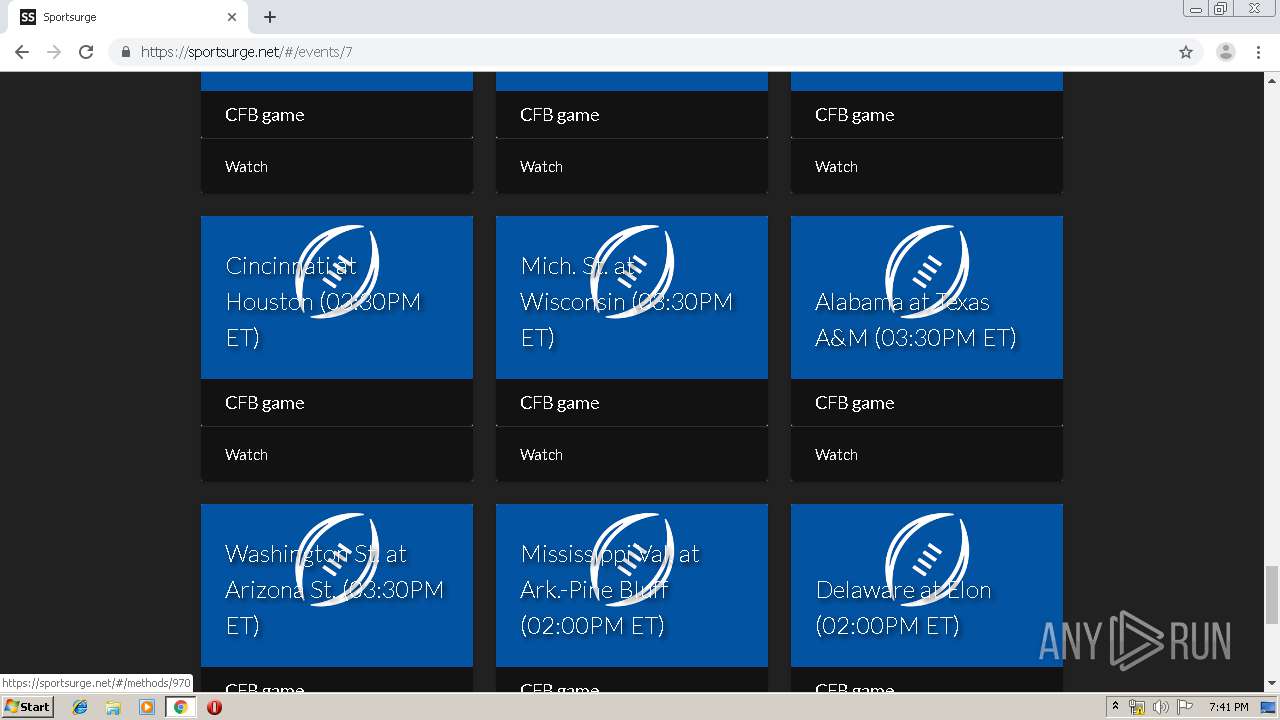
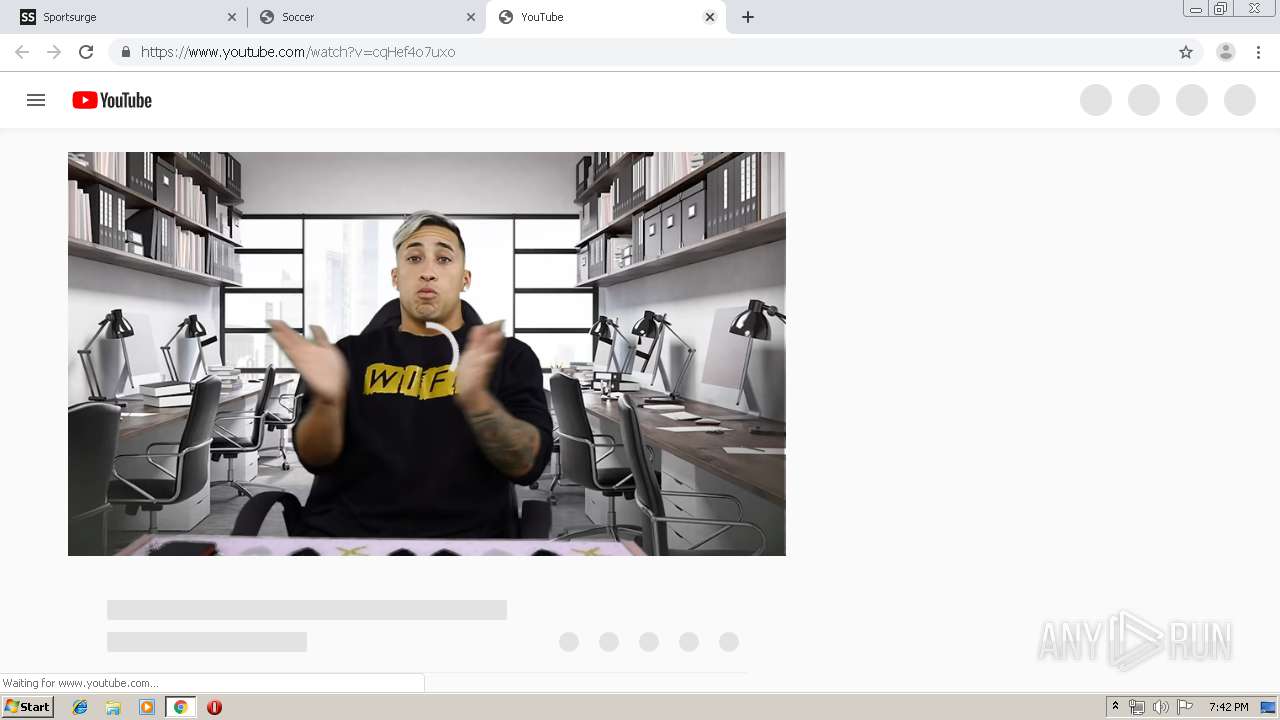
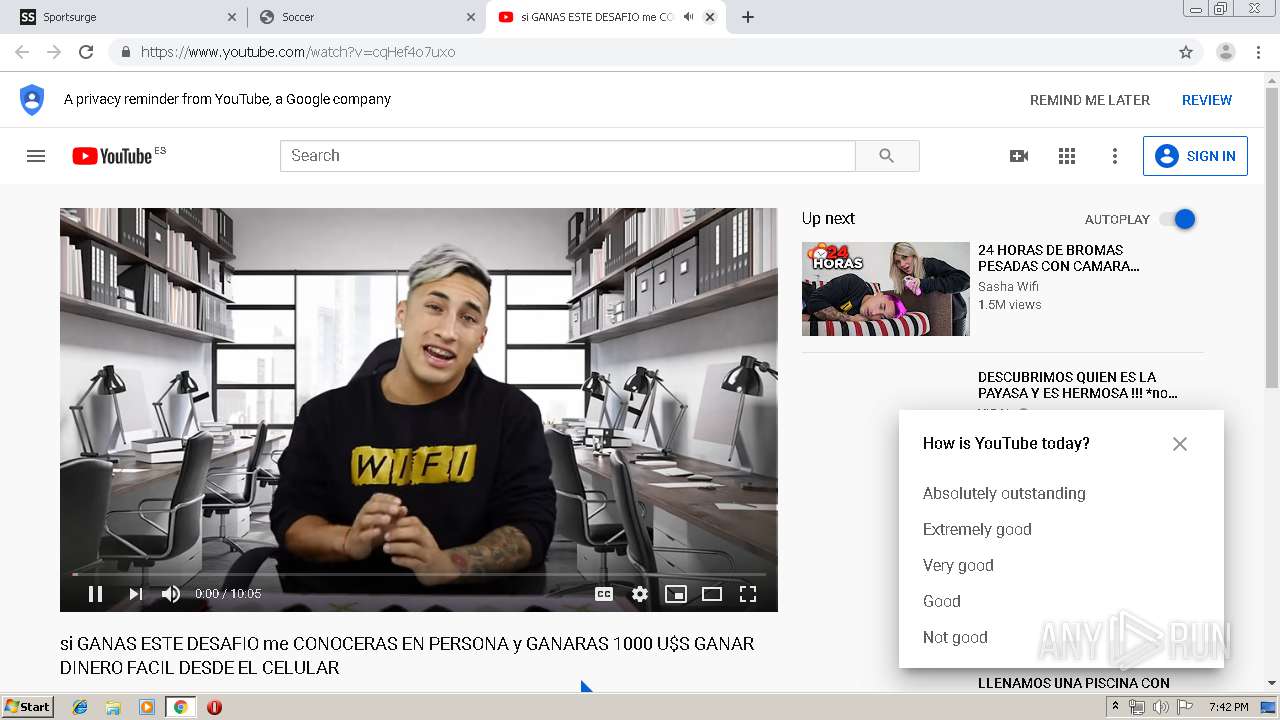
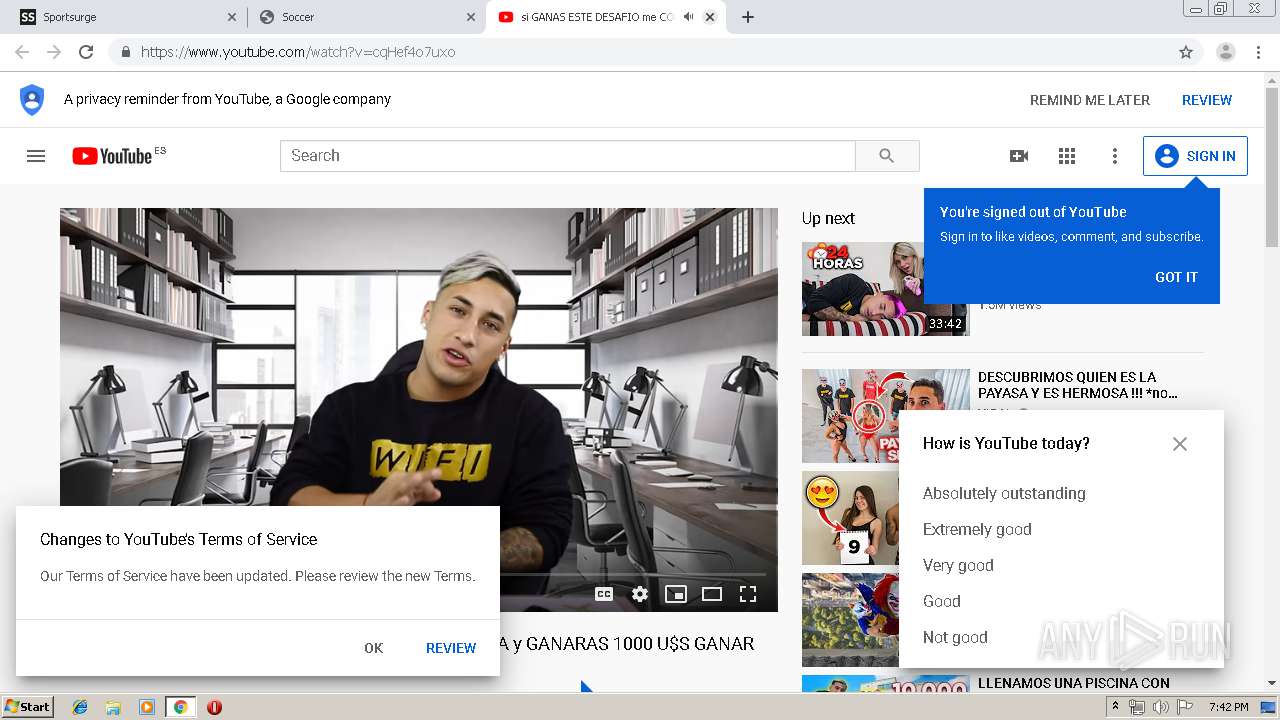
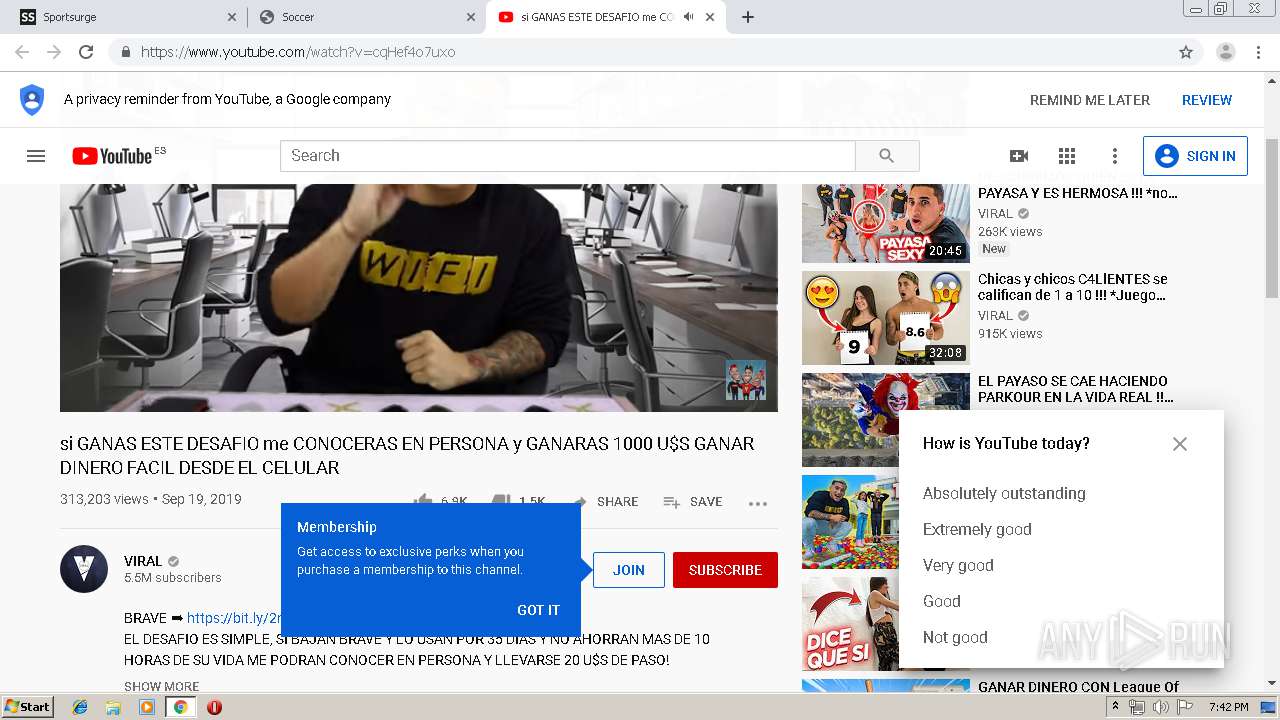
| URL: | http://www.sportsurge.net |
| Full analysis: | https://app.any.run/tasks/3ea3e3e5-a9cd-42b8-9fb5-bf61f8511f42 |
| Verdict: | Malicious activity |
| Analysis date: | October 12, 2019, 18:38:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 618E02F1C146C7BCD8ED30E22FAFBDB6 |
| SHA1: | 23FD332103D443BE4A3CDFFAD2289876D6E3A093 |
| SHA256: | F5BB0AC5B2872110ACA177A5CDE3C02C965025684D2DFE6BEE6D441F6ADEBD41 |
| SSDEEP: | 3:N1KJS46ALL0:Cc4rs |
MALICIOUS
Connects to CnC server
- chrome.exe (PID: 2084)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2140)
INFO
Application launched itself
- chrome.exe (PID: 2140)
Reads the hosts file
- chrome.exe (PID: 2140)
- chrome.exe (PID: 2084)
Creates files in the user directory
- chrome.exe (PID: 2140)
Changes settings of System certificates
- chrome.exe (PID: 2084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
118
Monitored processes
83
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4684849524459331683 --renderer-client-id=76 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6604 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9634120670364537253 --mojo-platform-channel-handle=4508 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=9815737498637983087 --mojo-platform-channel-handle=4816 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1316 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4524632175149008177 --renderer-client-id=45 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4452 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3295645210890272530 --renderer-client-id=74 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6316 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15152698868168642408 --renderer-client-id=67 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5748 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14022643833616772959 --mojo-platform-channel-handle=4100 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7232679446484502970 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2992 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3181615582871588449 --mojo-platform-channel-handle=3952 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
736
Read events
581
Write events
150
Delete events
5
Modification events
| (PID) Process: | (532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2140-13215379105651250 |
Value: 259 | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2140-13215379105651250 |
Value: 259 | |||
Executable files
0
Suspicious files
338
Text files
432
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7132e73a-5daf-47f8-aec3-15068d4517ff.tmp | — | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39a850.TMP | text | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF39a8dd.TMP | text | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF39a8cd.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
187
TCP/UDP connections
327
DNS requests
214
Threats
47
HTTP requests
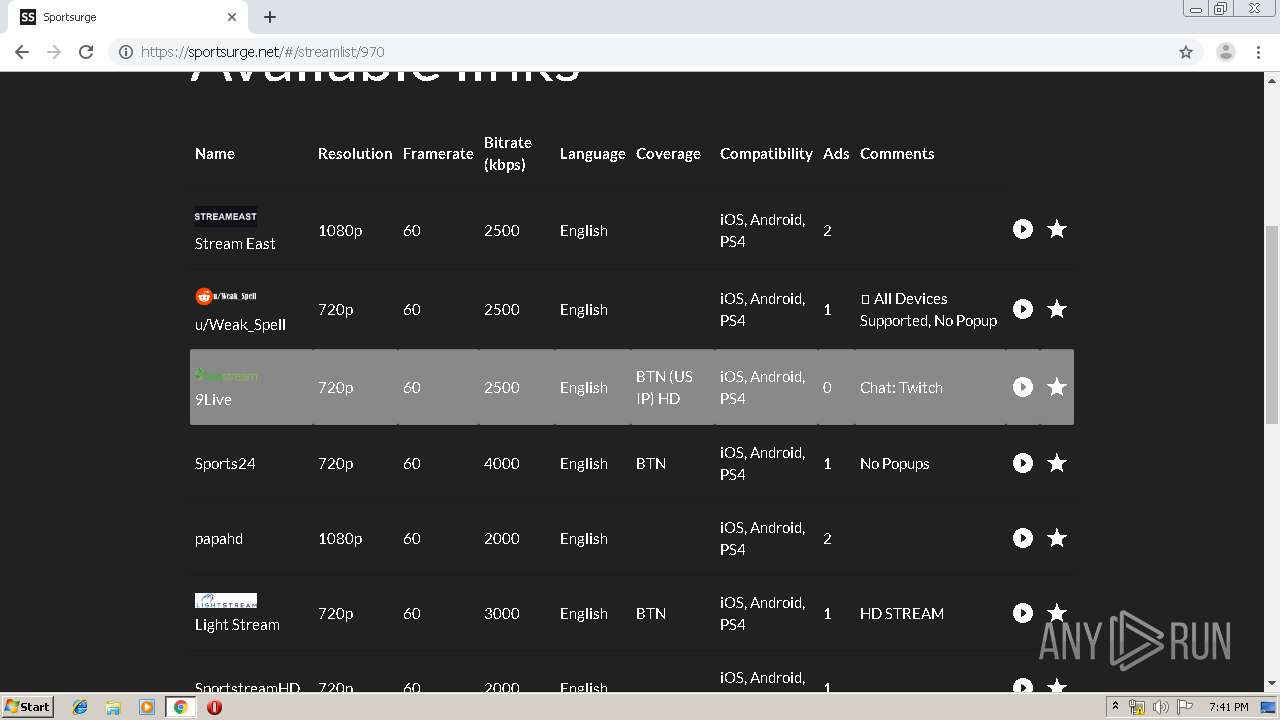
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
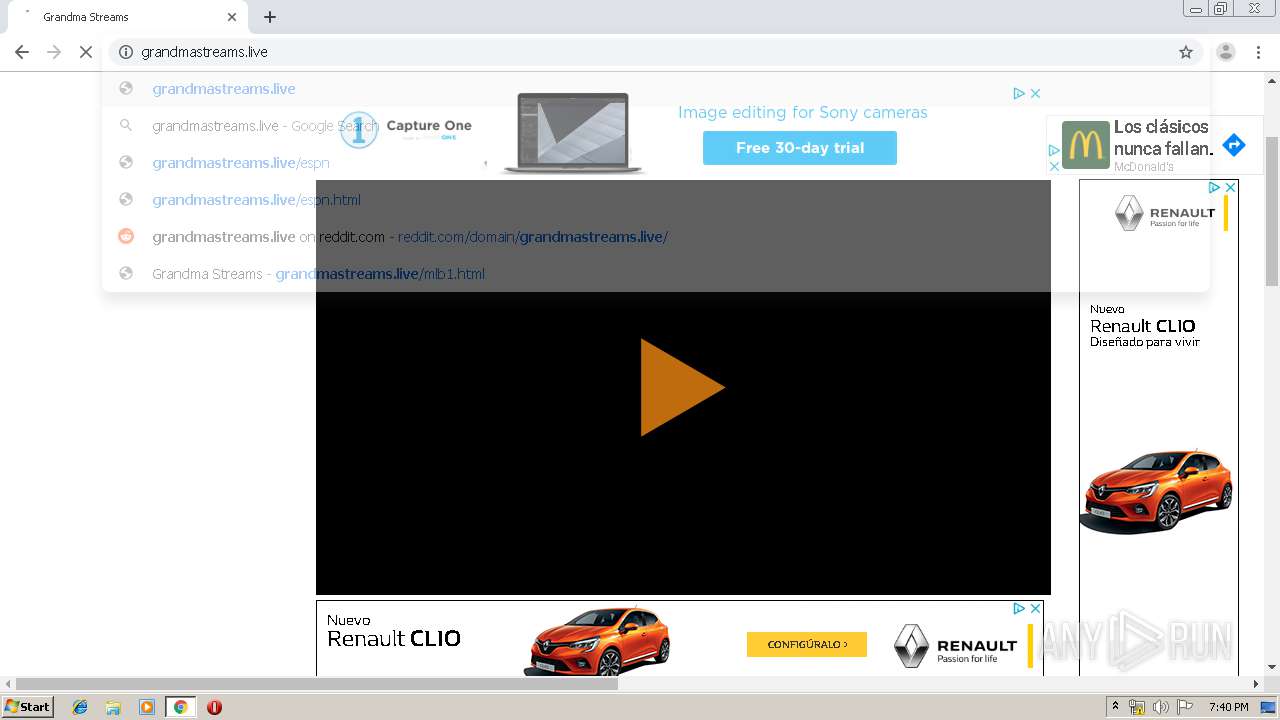
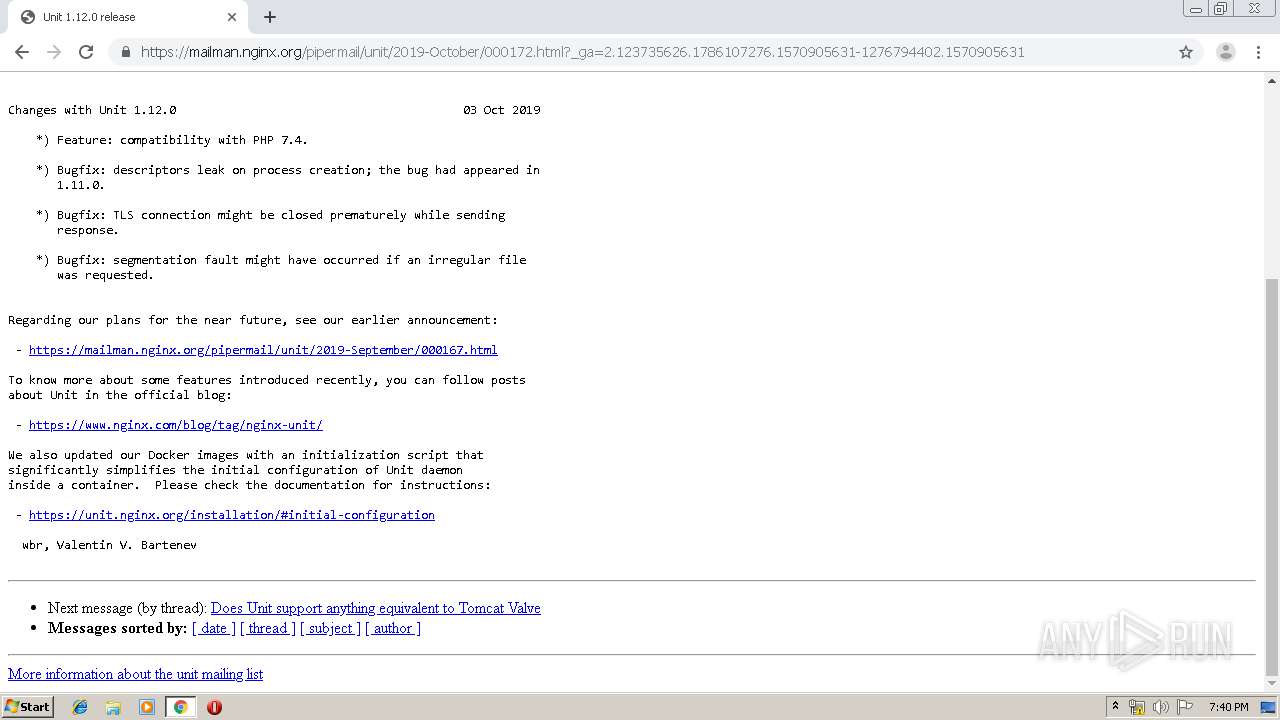
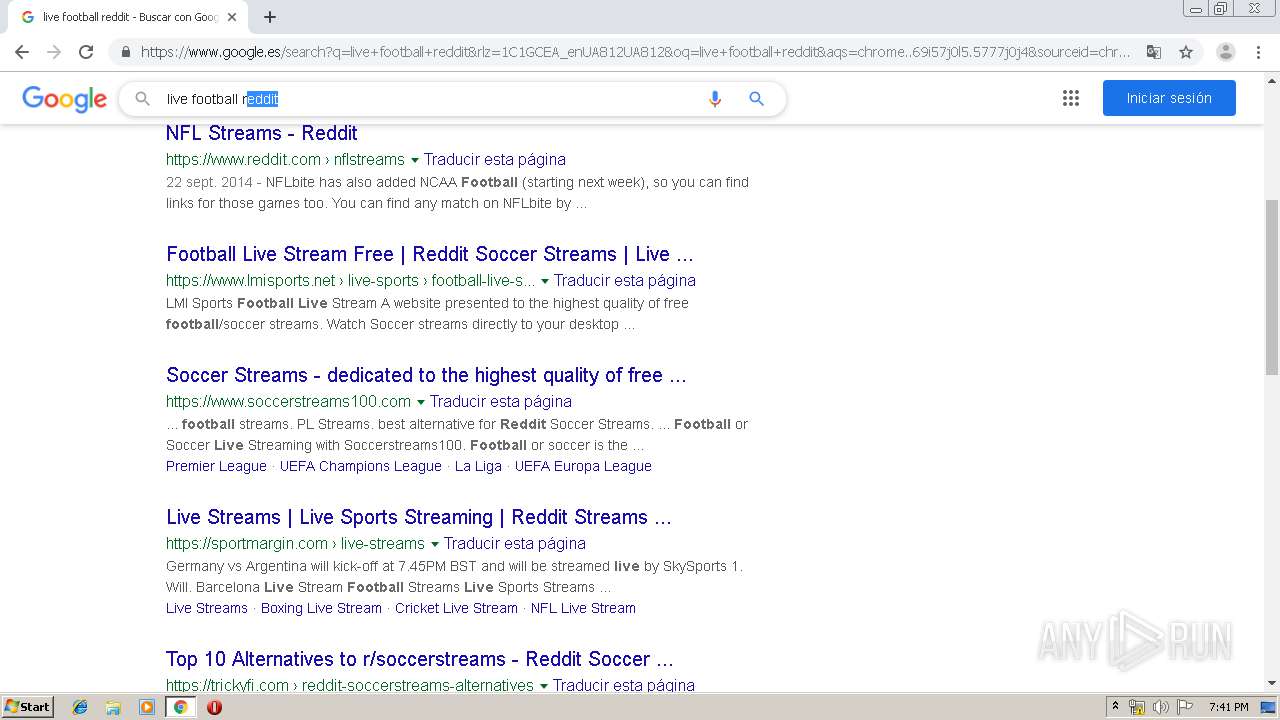
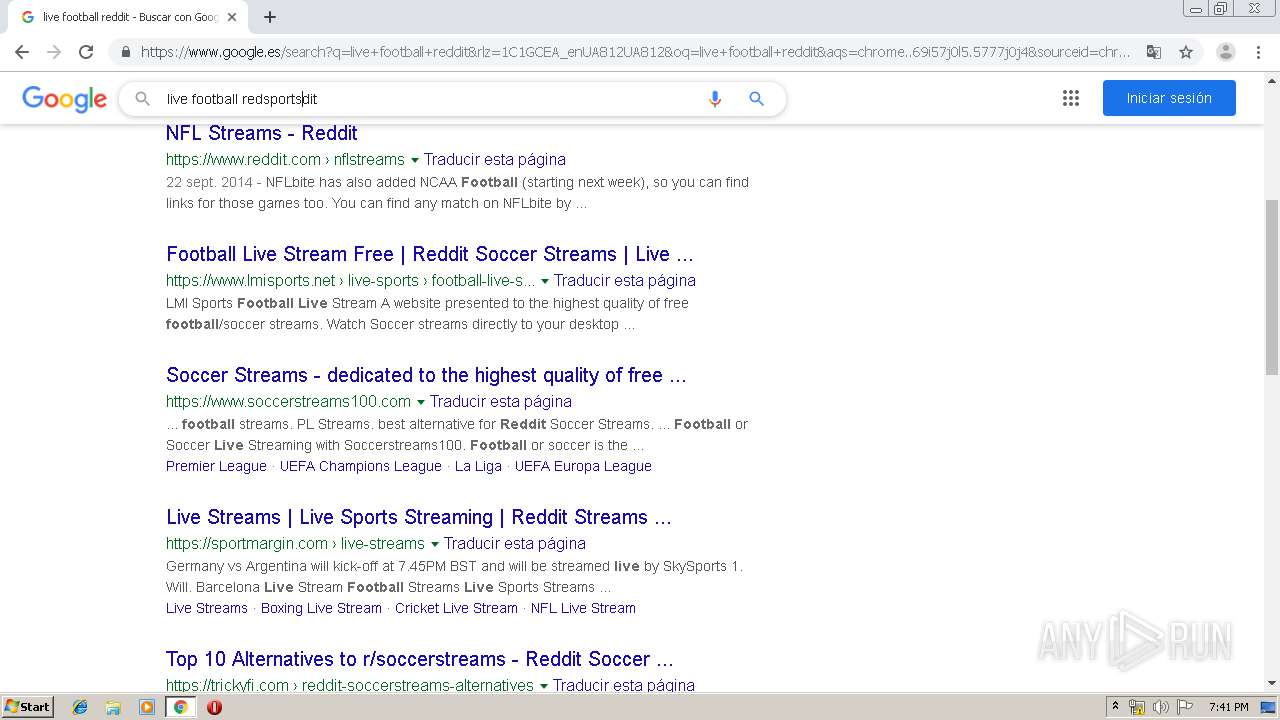
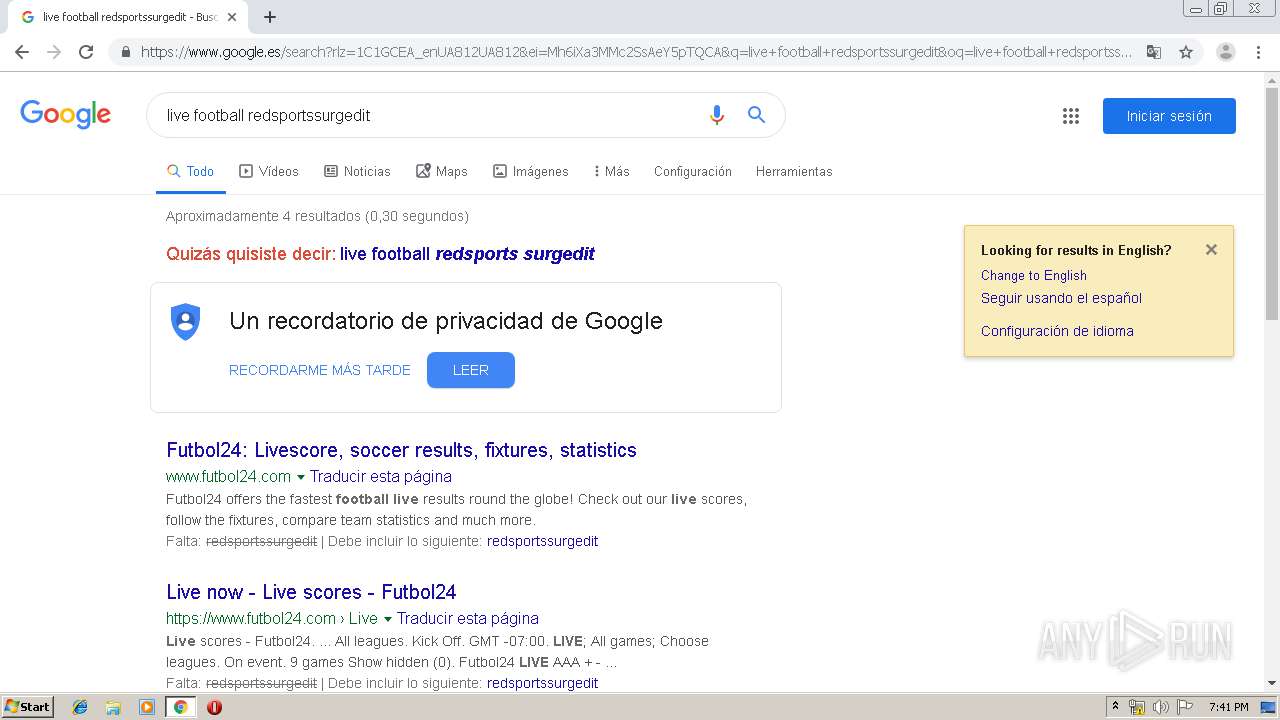
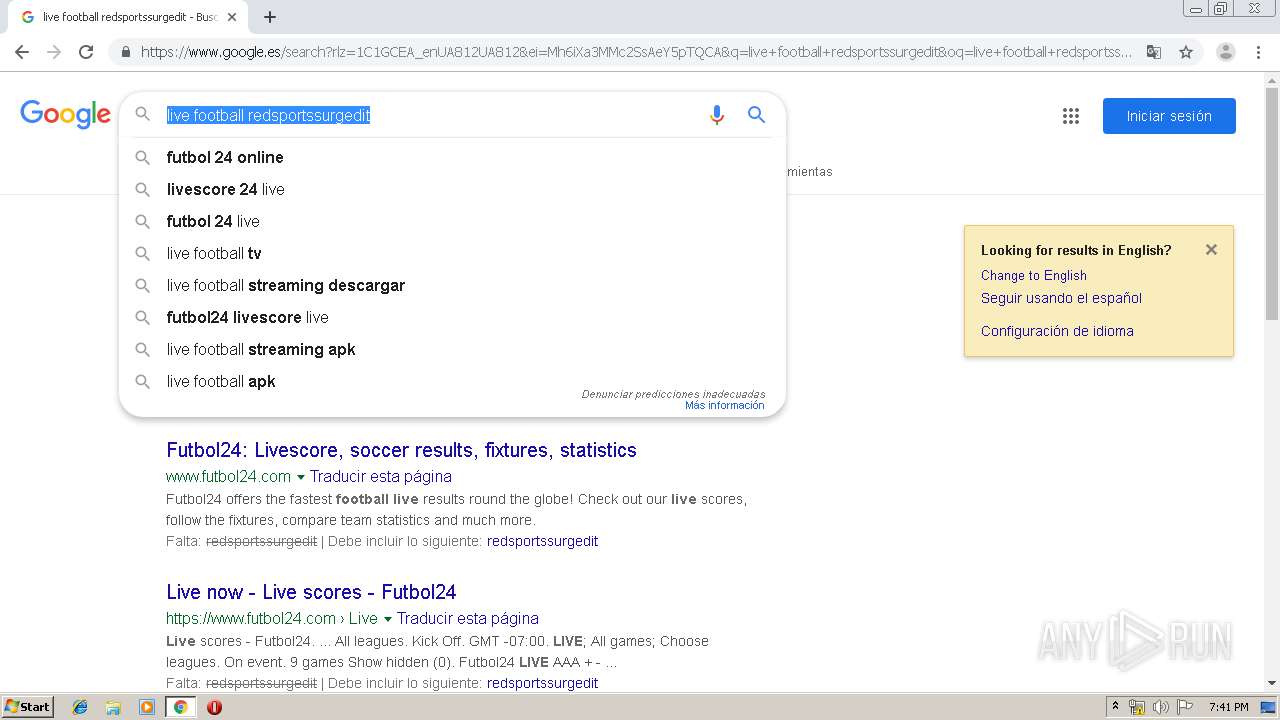
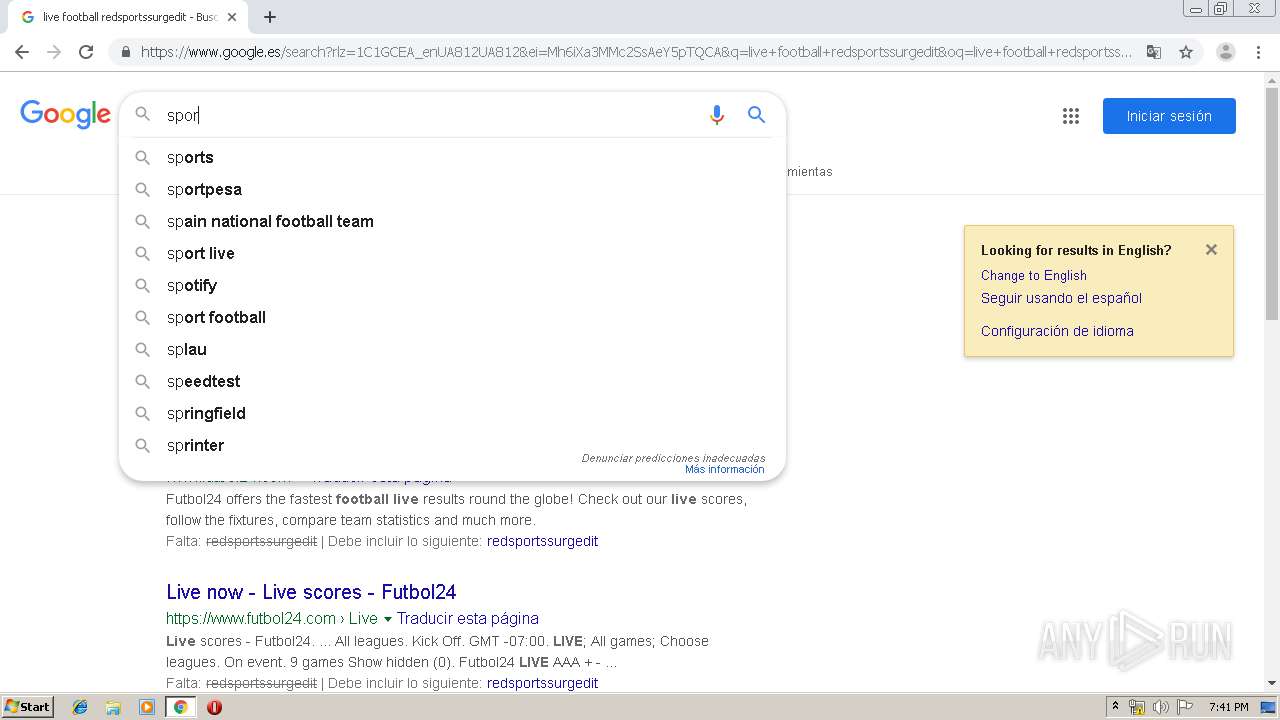
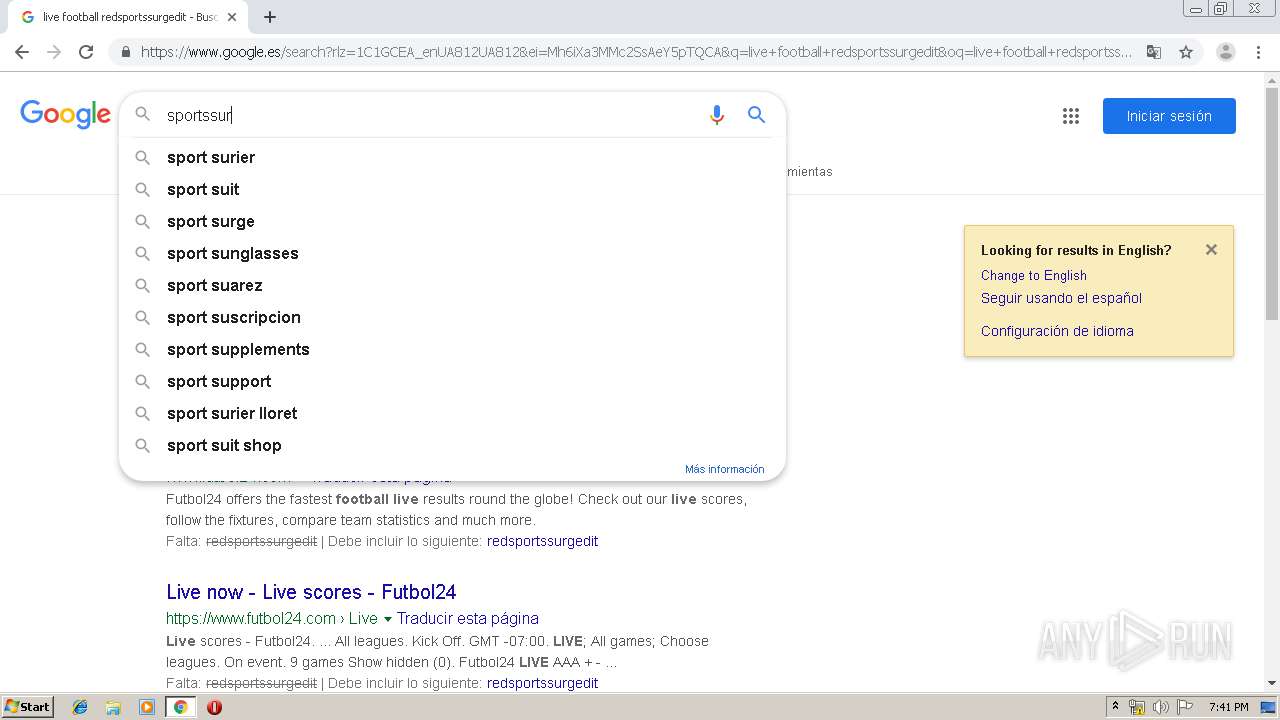
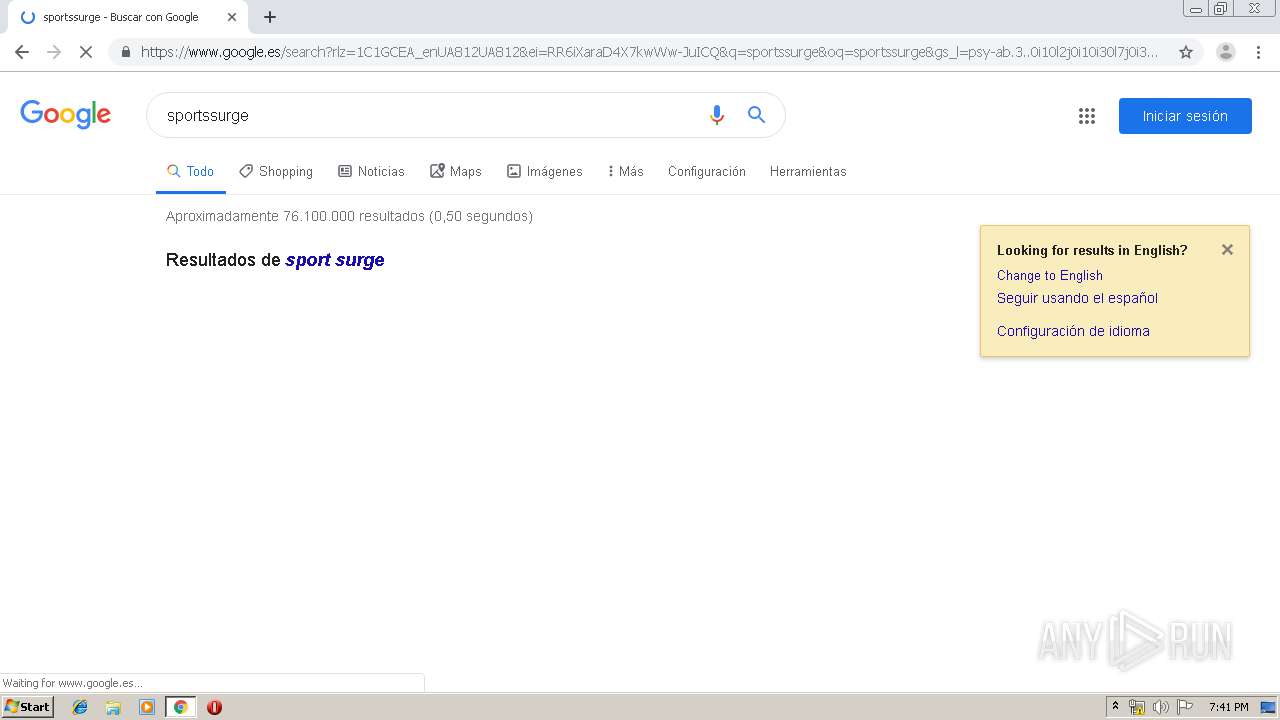
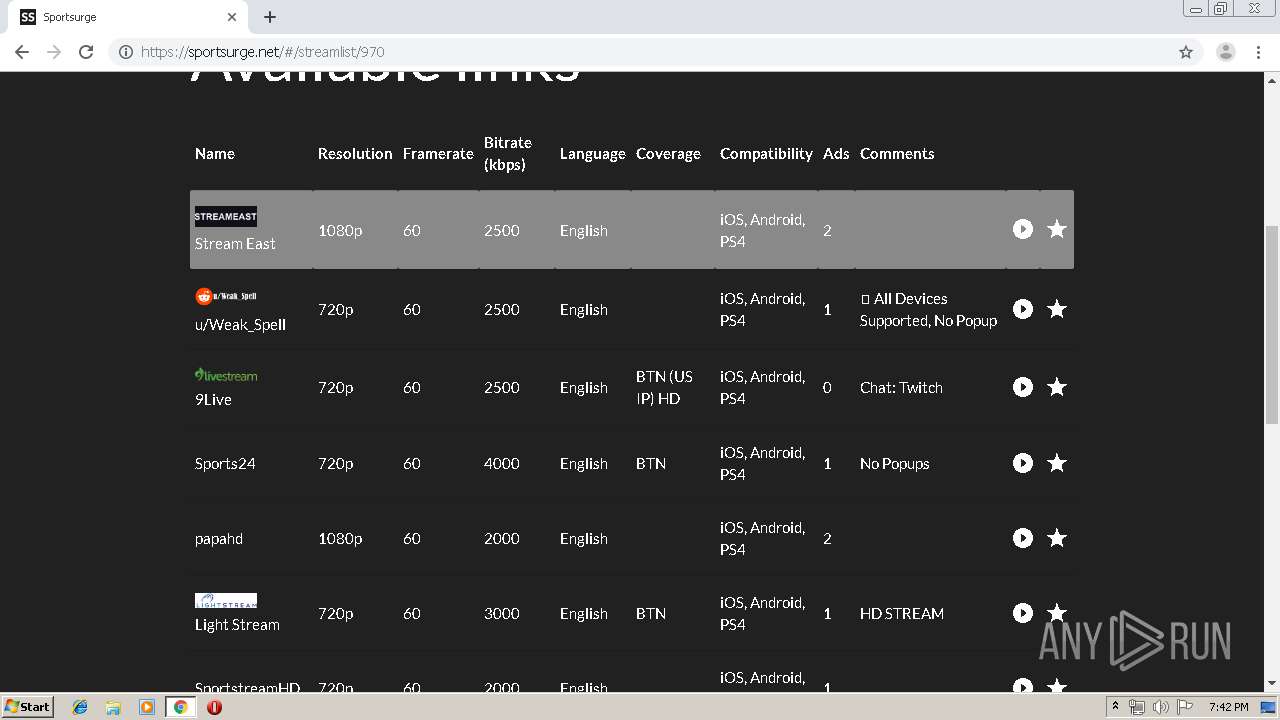
2084 | chrome.exe | GET | 301 | 172.64.130.33:80 | http://www.sportsurge.net/ | US | — | — | suspicious |
2084 | chrome.exe | GET | 204 | 216.58.208.35:80 | http://www.gstatic.com/generate_204 | US | — | — | whitelisted |
2084 | chrome.exe | GET | 204 | 172.217.23.130:80 | http://pagead2.googlesyndication.com/pagead/gen_204?id=ovlp&adf=1386413516&client=ca-pub-2453366679509228&eid=368226600%2C368226610%2C20040013&io=0&saldr=aa&oa=0.00&qid=CKHPiamvl-UCFVXi1QodzXsJUQ&roa=0&slot=6352951011&sp=0%2C0&tgt=ins%2Faswift_0_expand.0&tr=316%2C213.46875%2C1044%2C303.46875&url=http%3A%2F%2Fgrandmastreams.live%2Fmlb1.html&vp=1264x604 | US | — | — | whitelisted |
2084 | chrome.exe | GET | 204 | 216.58.208.35:80 | http://www.gstatic.com/generate_204 | US | — | — | whitelisted |
2084 | chrome.exe | GET | 301 | 151.101.2.109:80 | http://cdn.jsdelivr.net/gh/clappr/clappr@latest/dist/clappr.min.js | US | — | — | whitelisted |
2084 | chrome.exe | GET | 301 | 151.101.2.109:80 | http://cdn.jsdelivr.net/gh/clappr/clappr-level-selector-plugin@latest/dist/level-selector.min.js | US | — | — | whitelisted |
2084 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 509 b | whitelisted |
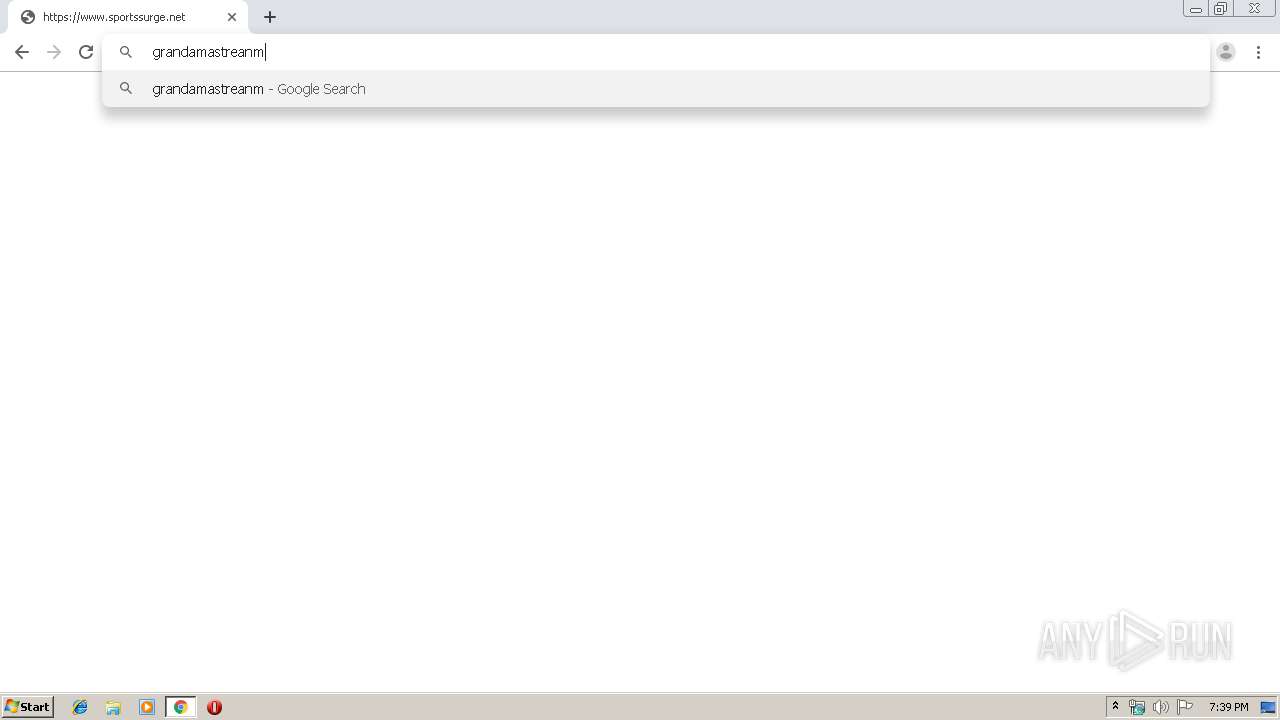
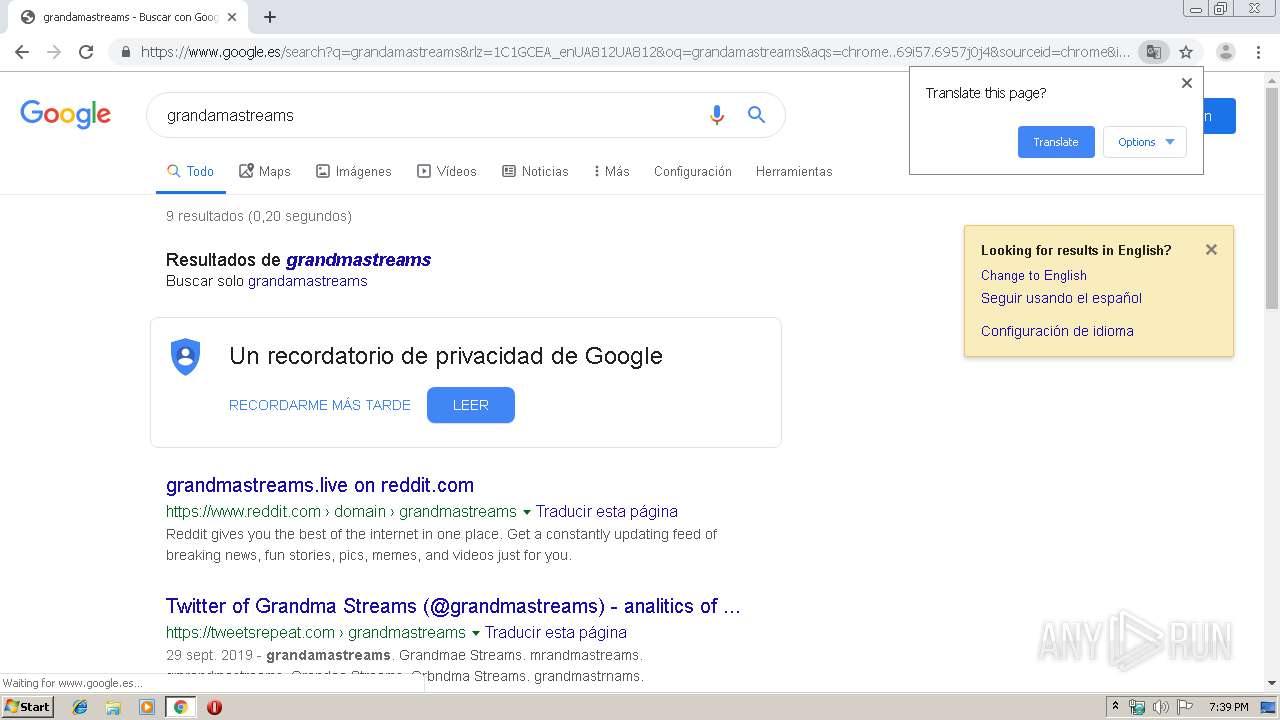
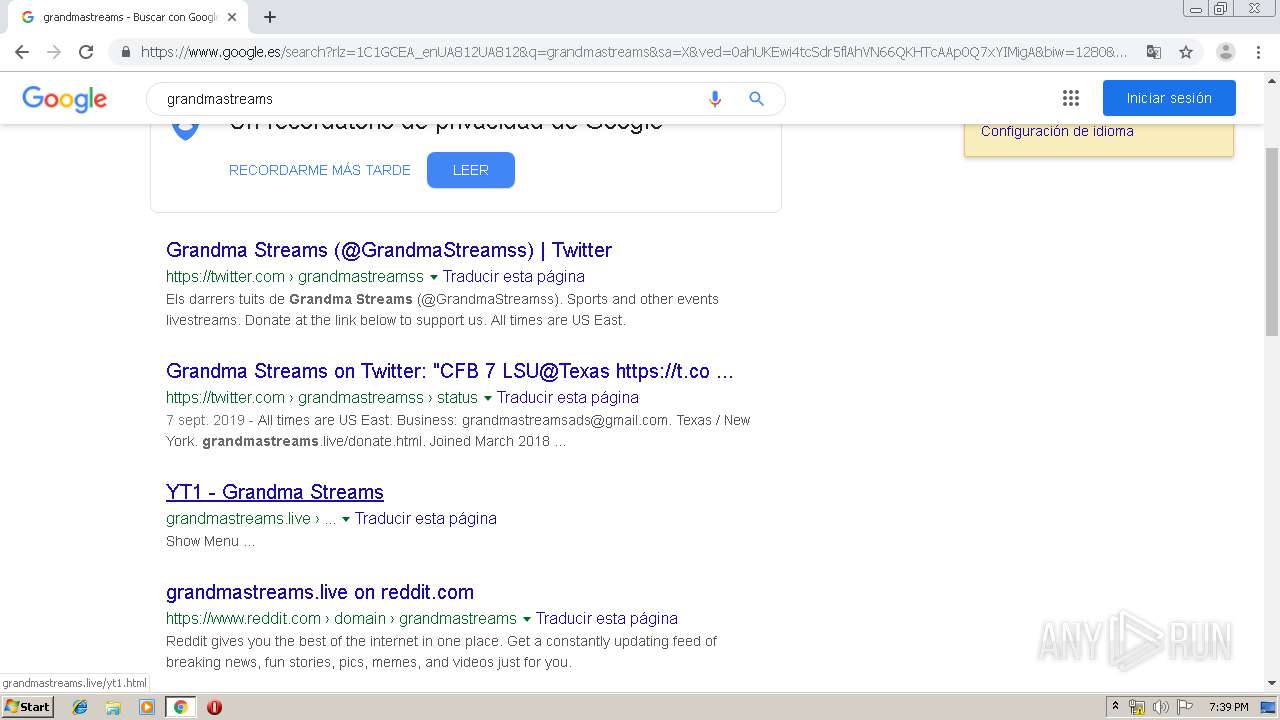
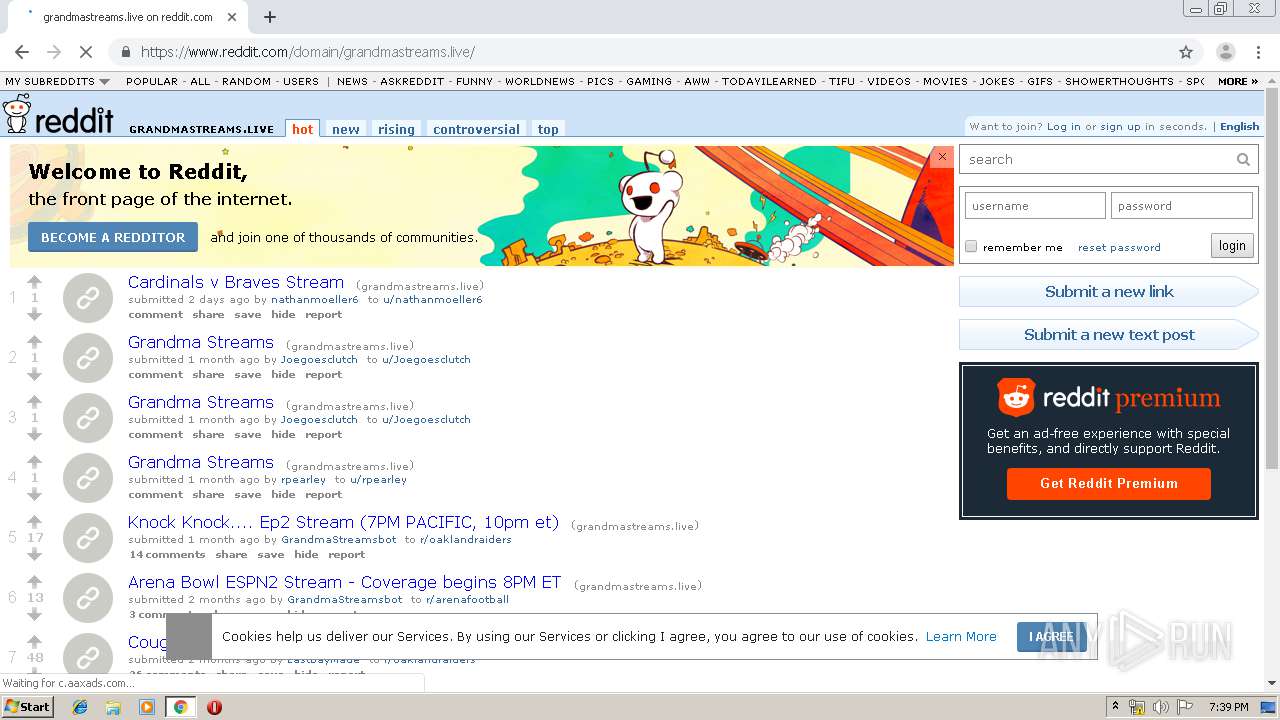
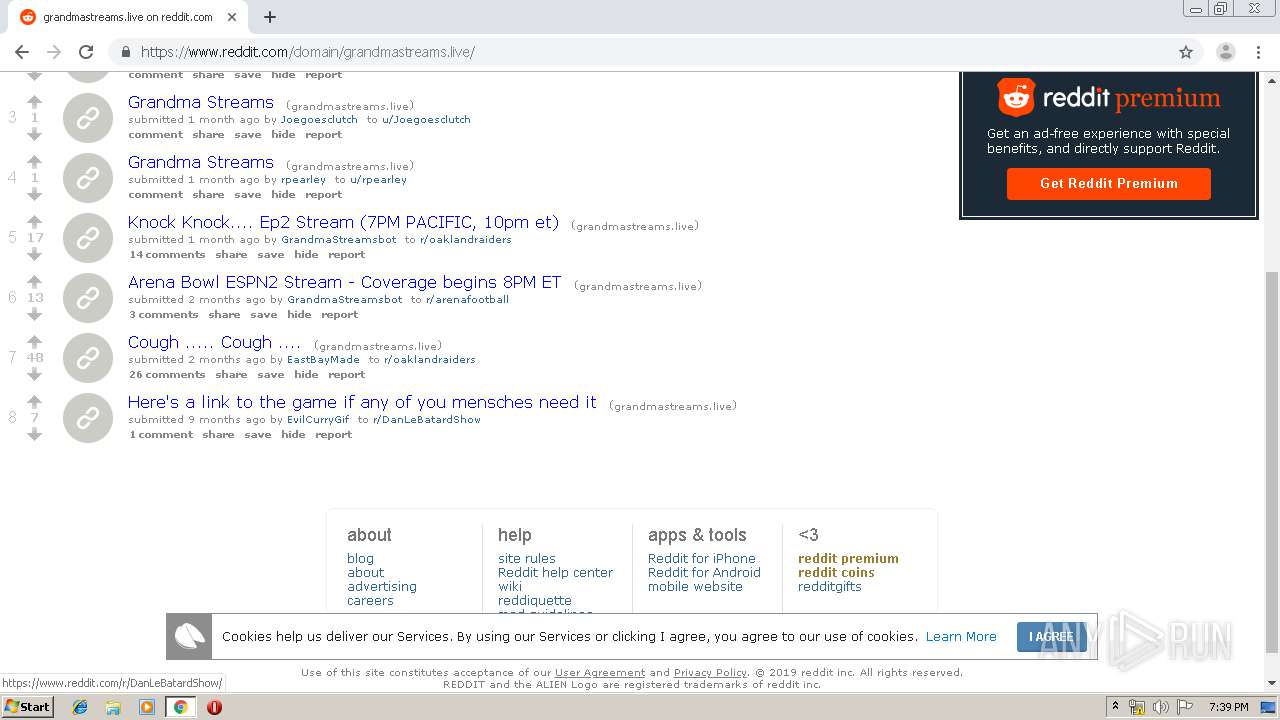
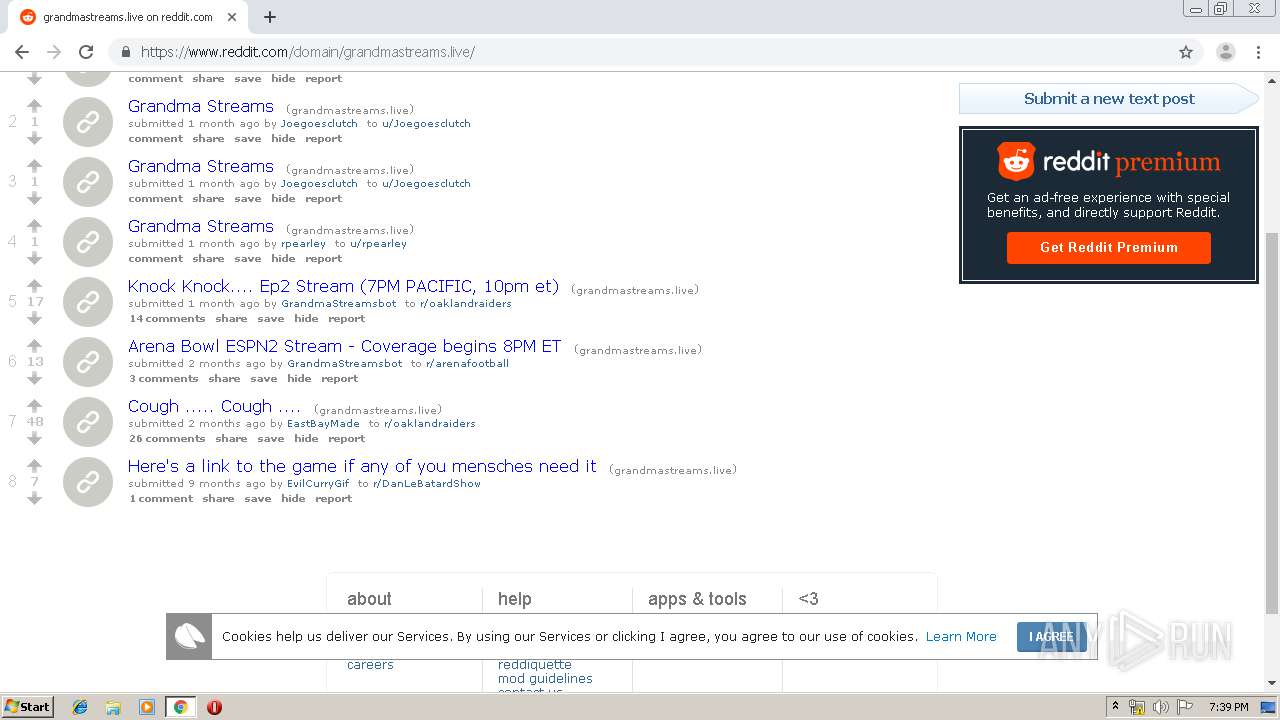
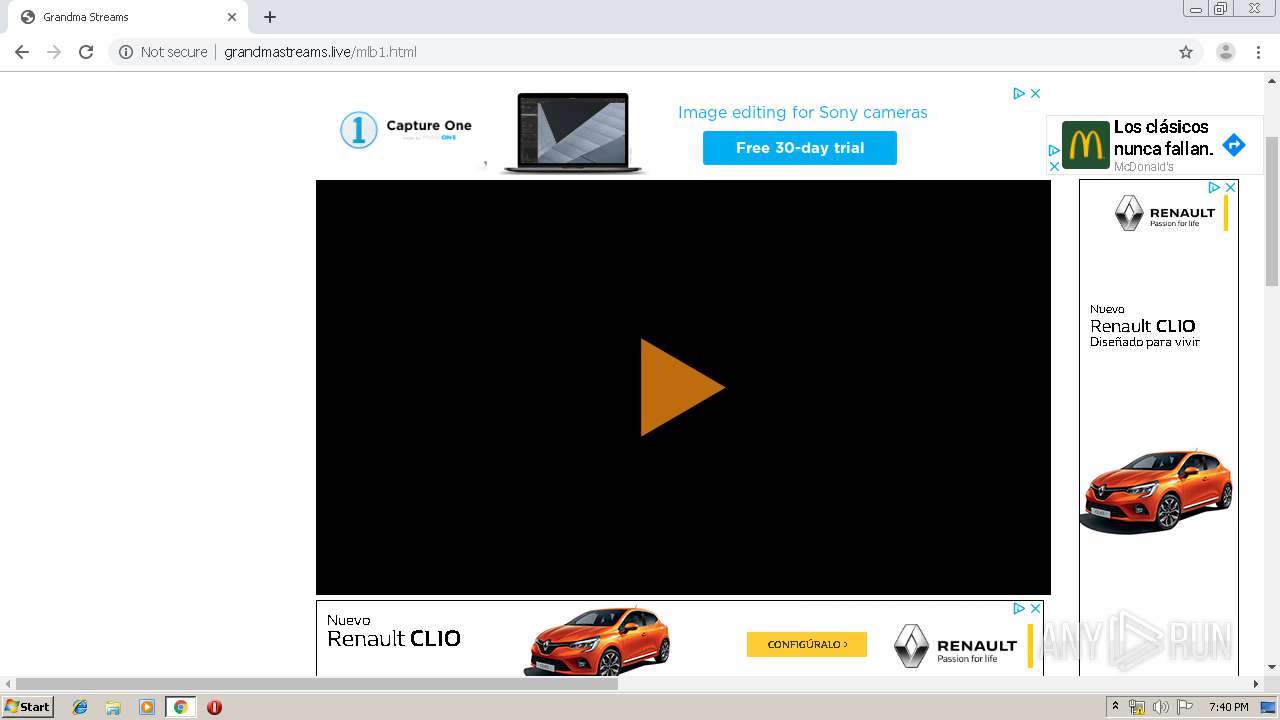
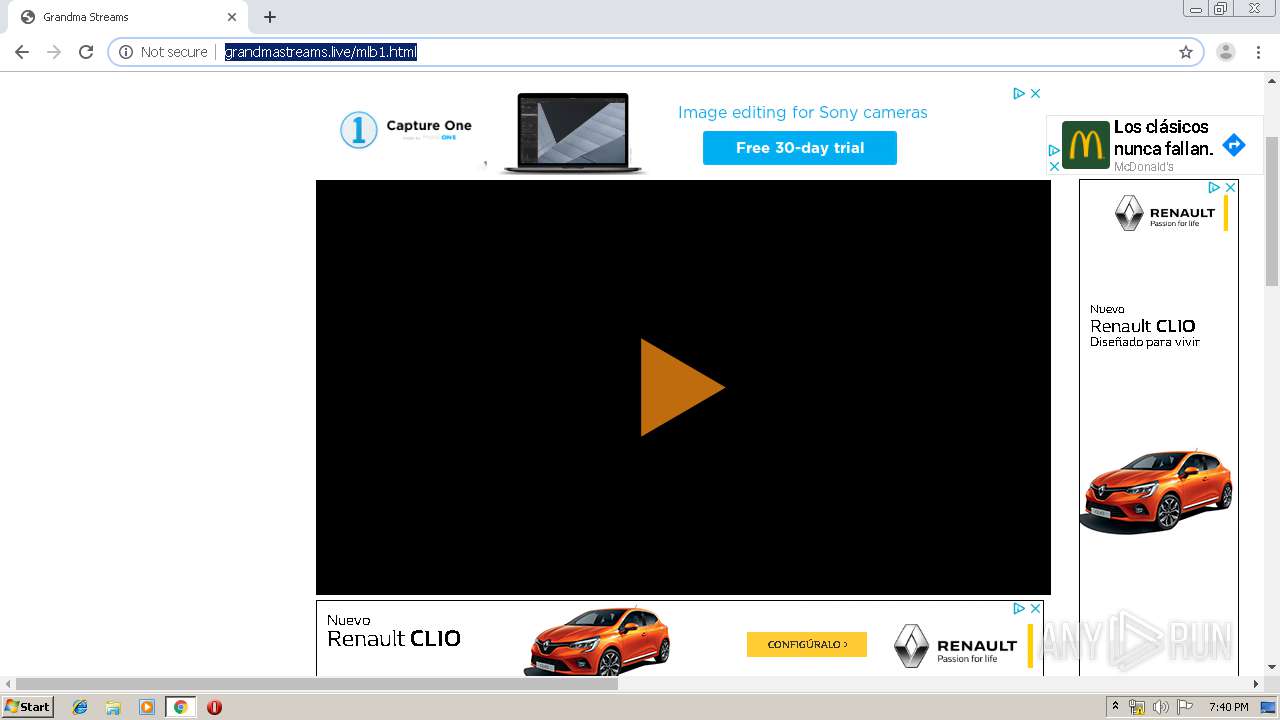
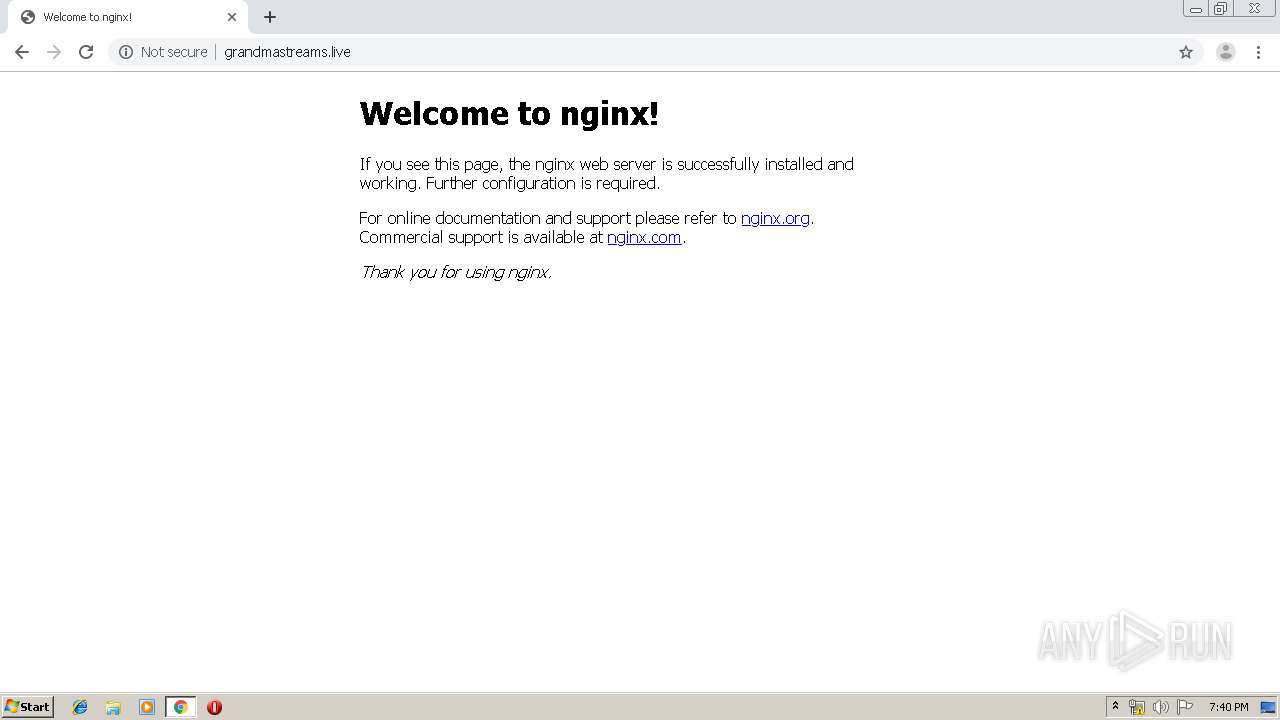
2084 | chrome.exe | GET | 200 | 104.31.11.185:80 | http://grandmastreams.live/mlb1.html | US | html | 10.4 Kb | suspicious |
2084 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
2084 | chrome.exe | GET | 200 | 74.125.173.57:80 | http://r3---sn-4g5ednll.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=82.102.26.195&mm=28&mn=sn-4g5ednll&ms=nvh&mt=1570905369&mv=u&mvi=2&pl=25&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2084 | chrome.exe | 172.217.16.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2084 | chrome.exe | 172.64.130.33:80 | www.sportsurge.net | Cloudflare Inc | US | shared |
— | — | 172.64.130.33:80 | www.sportsurge.net | Cloudflare Inc | US | shared |
2084 | chrome.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
2084 | chrome.exe | 172.217.22.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
2084 | chrome.exe | 172.217.18.174:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2084 | chrome.exe | 216.58.207.67:443 | www.google.es | Google Inc. | US | whitelisted |
2084 | chrome.exe | 173.194.164.169:80 | r3---sn-4g5edned.gvt1.com | Google Inc. | US | whitelisted |
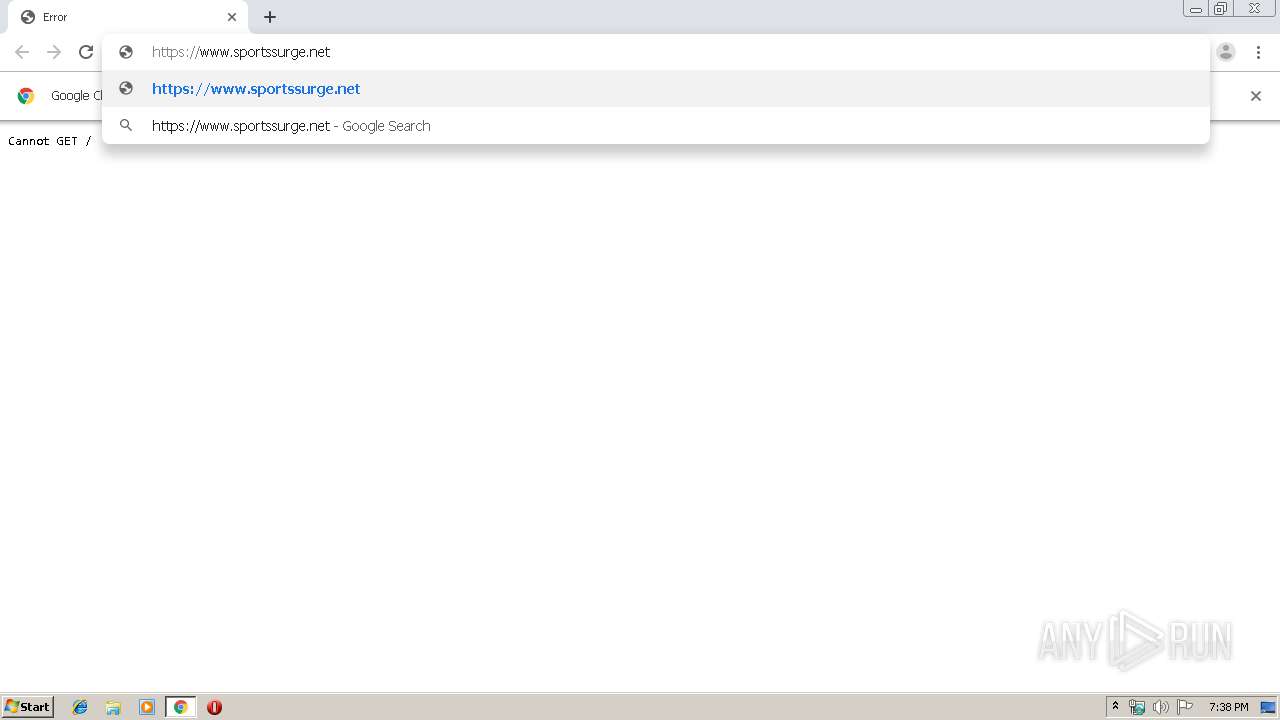
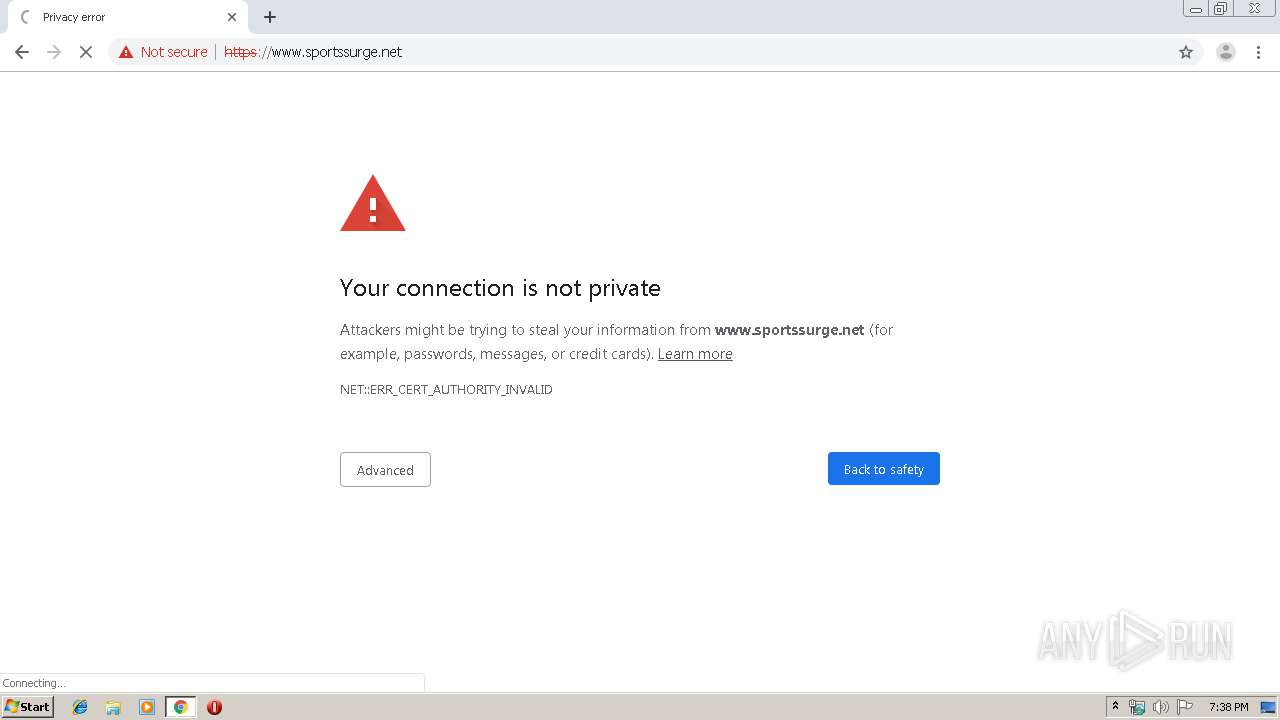
2084 | chrome.exe | 195.22.26.248:443 | www.sportssurge.net | Claranet Ltd | PT | malicious |
2084 | chrome.exe | 205.185.216.10:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
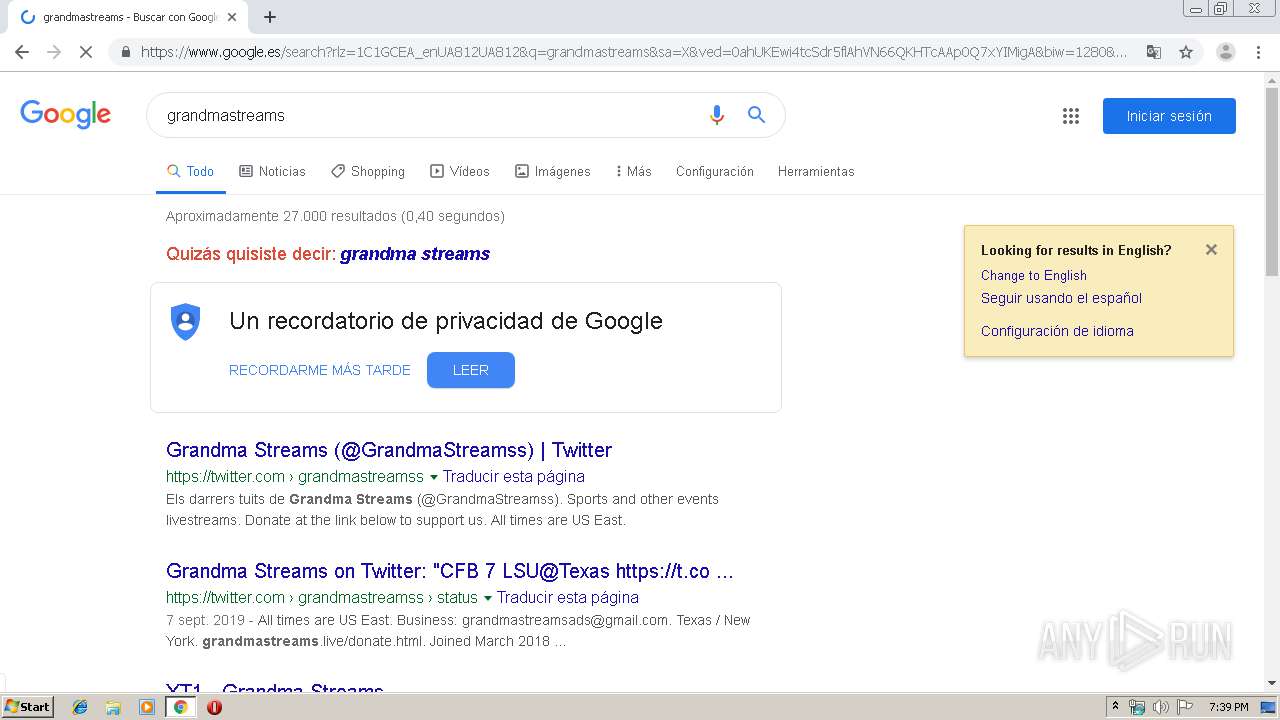
www.sportsurge.net |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
www.google.es |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r3---sn-4g5edned.gvt1.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.sportssurge.net |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2084 | chrome.exe | A Network Trojan was detected | ET CNC Ransomware Tracker Reported CnC Server group 60 |
2084 | chrome.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
2084 | chrome.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
2084 | chrome.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
2084 | chrome.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
2084 | chrome.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
2084 | chrome.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
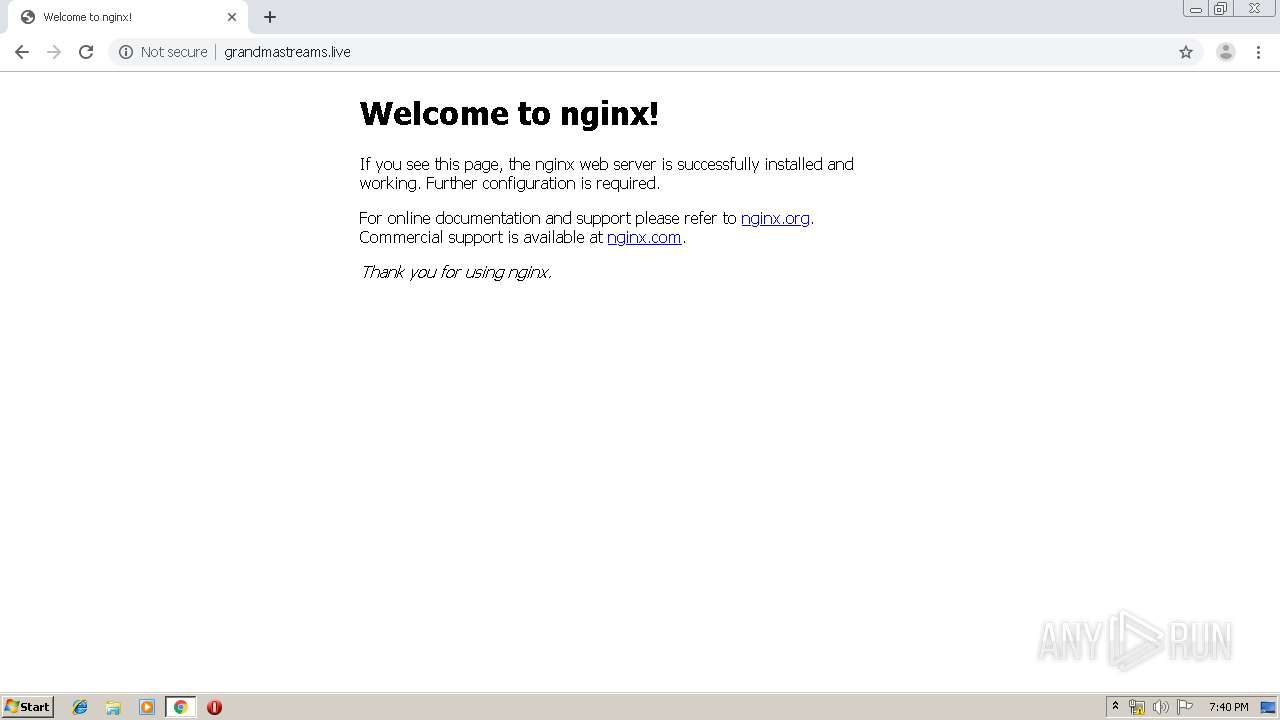
2084 | chrome.exe | Potentially Bad Traffic | ET INFO Unconfigured nginx Access |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
2084 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
1 ETPRO signatures available at the full report