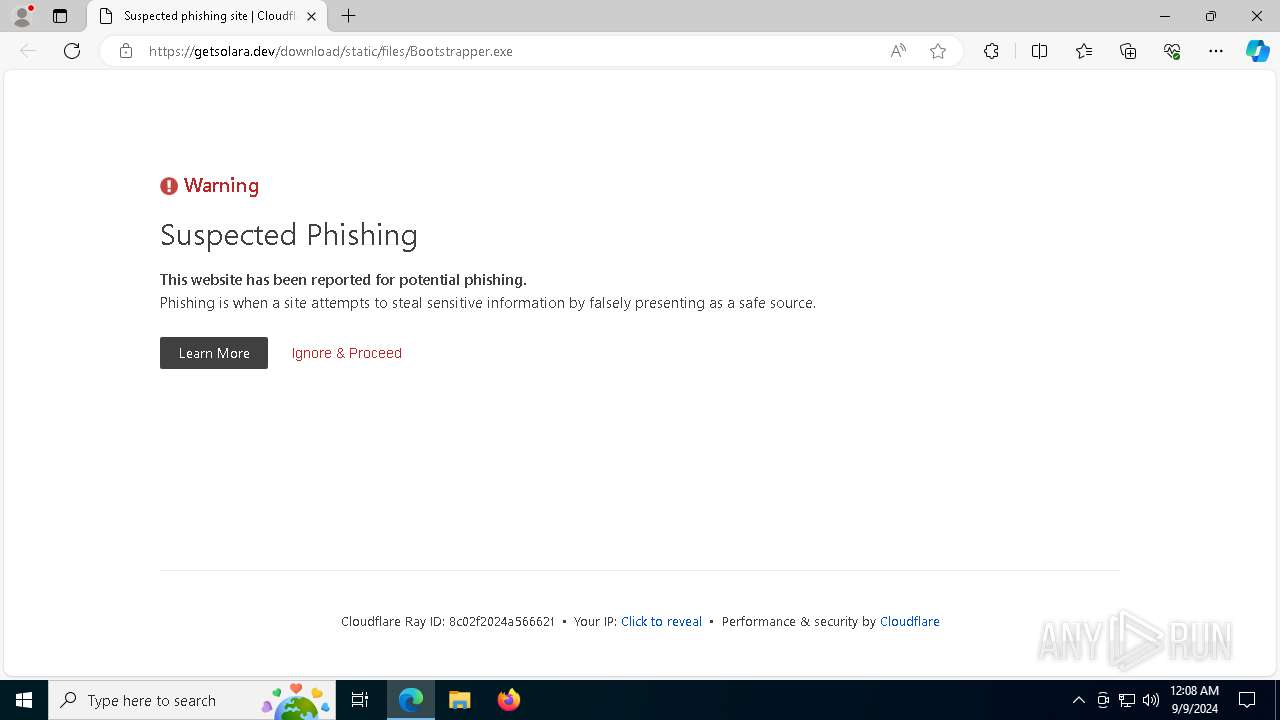
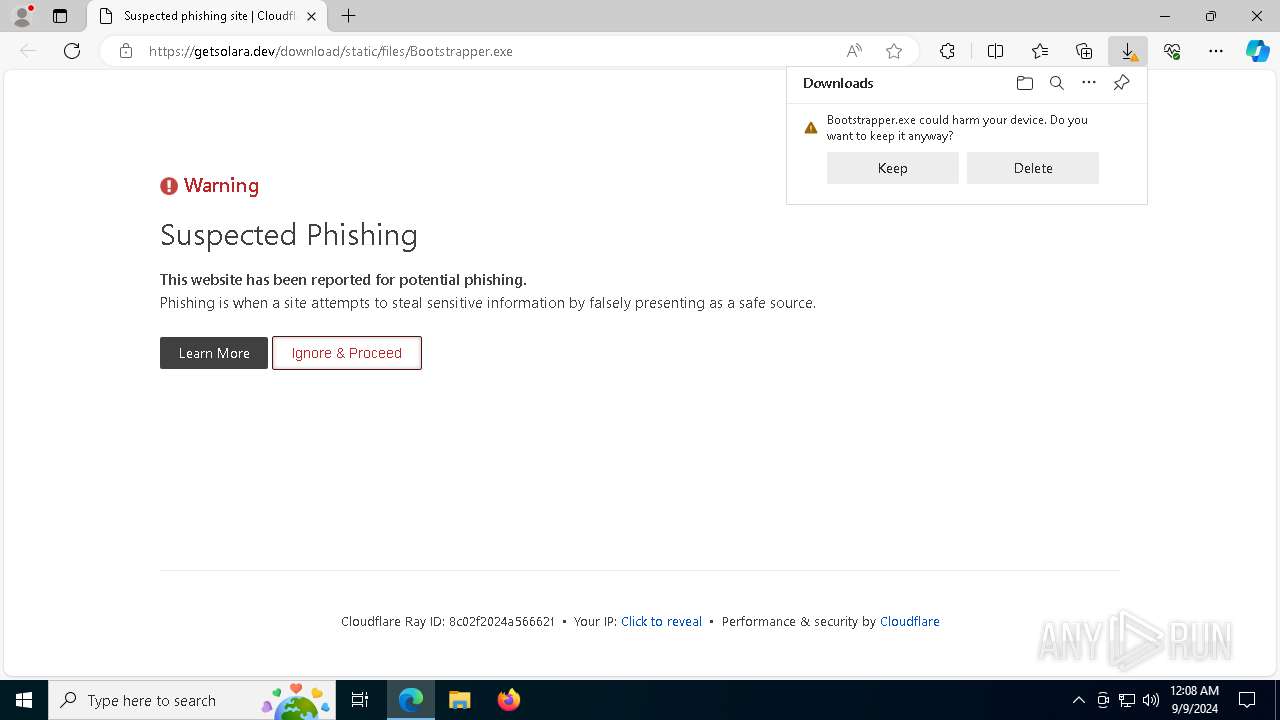
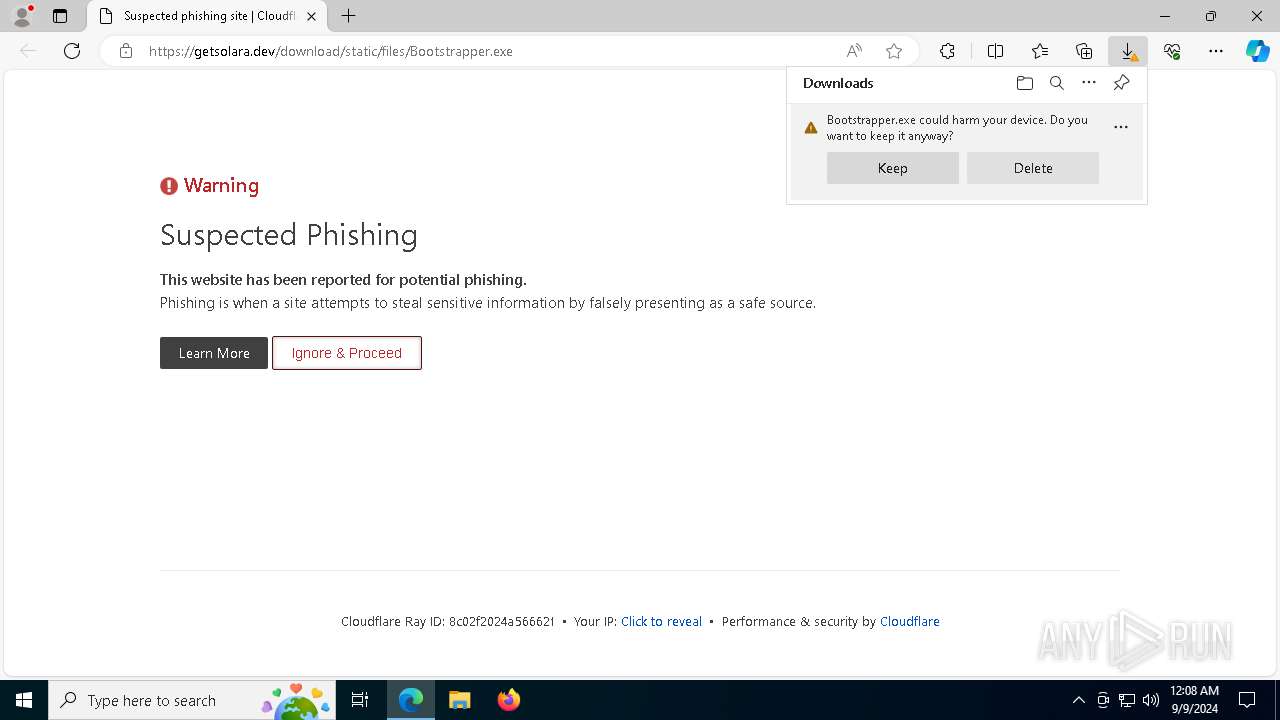
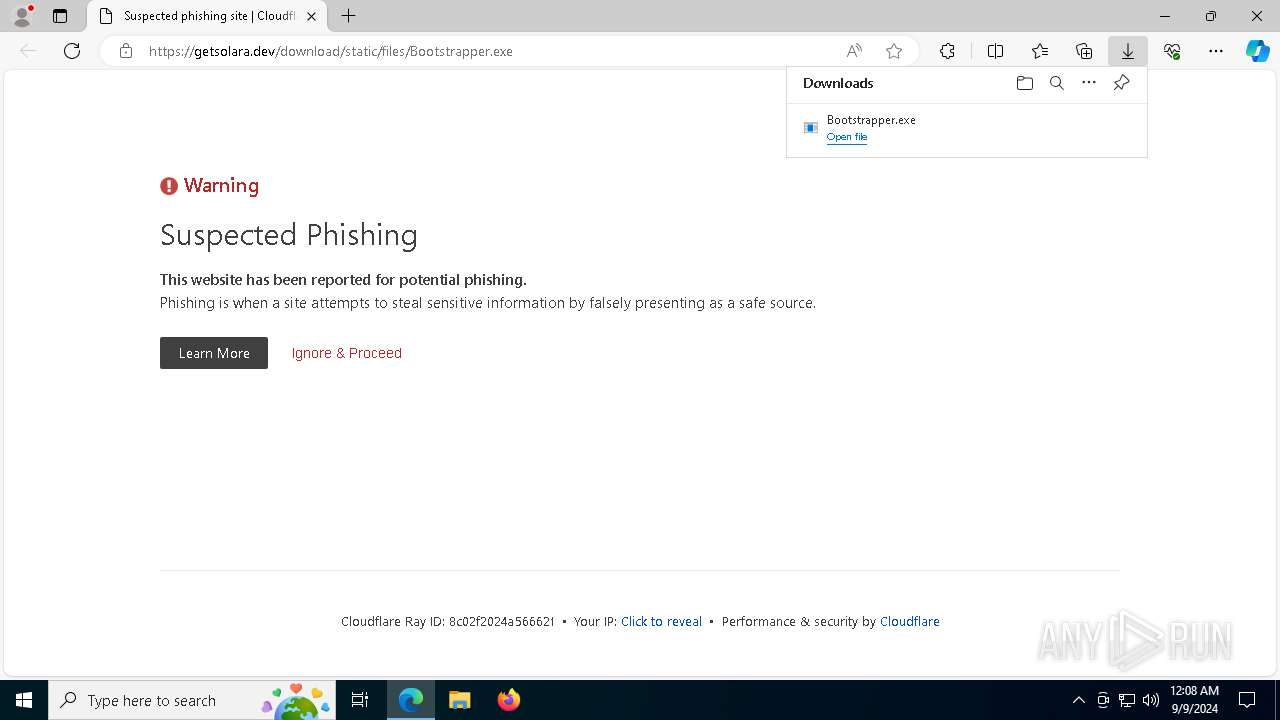
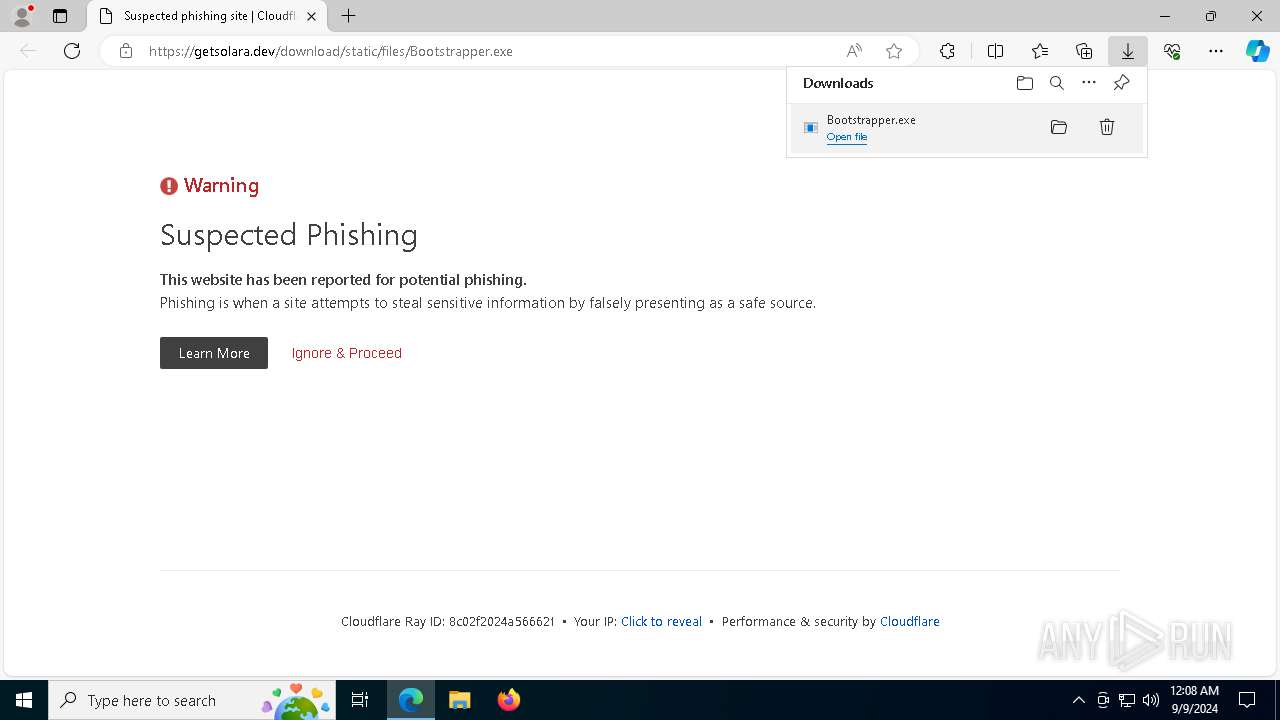
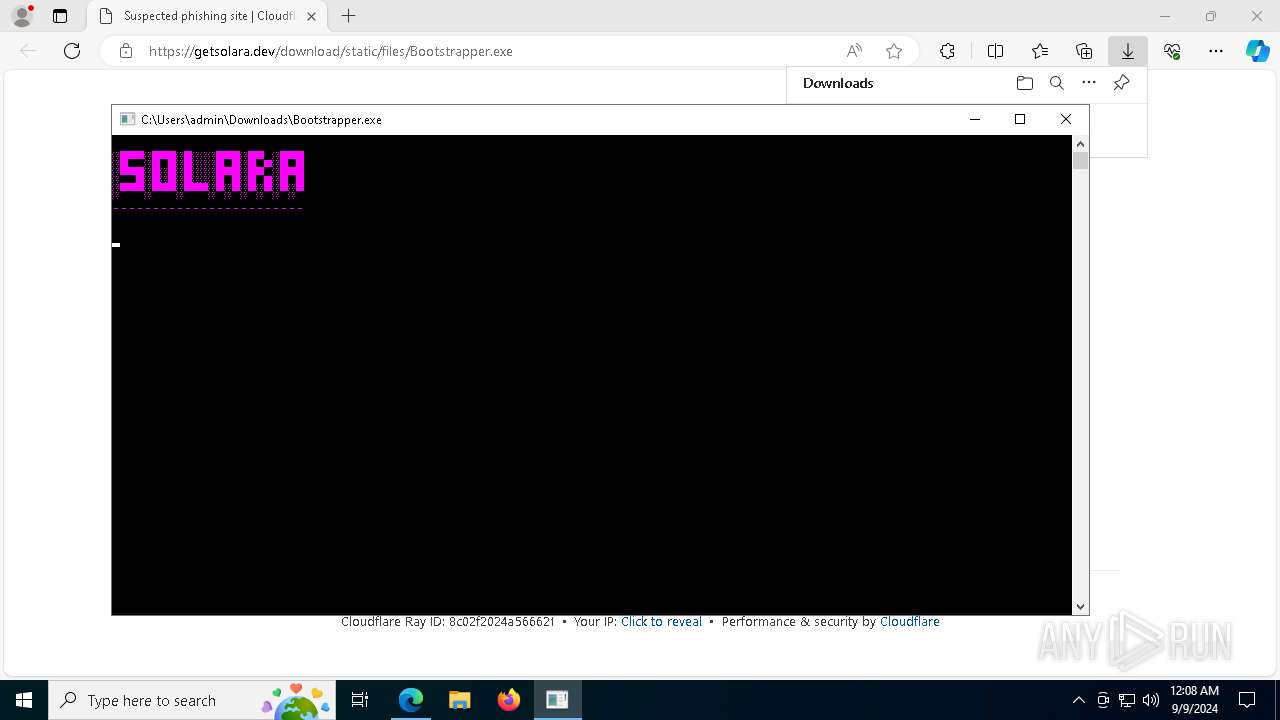
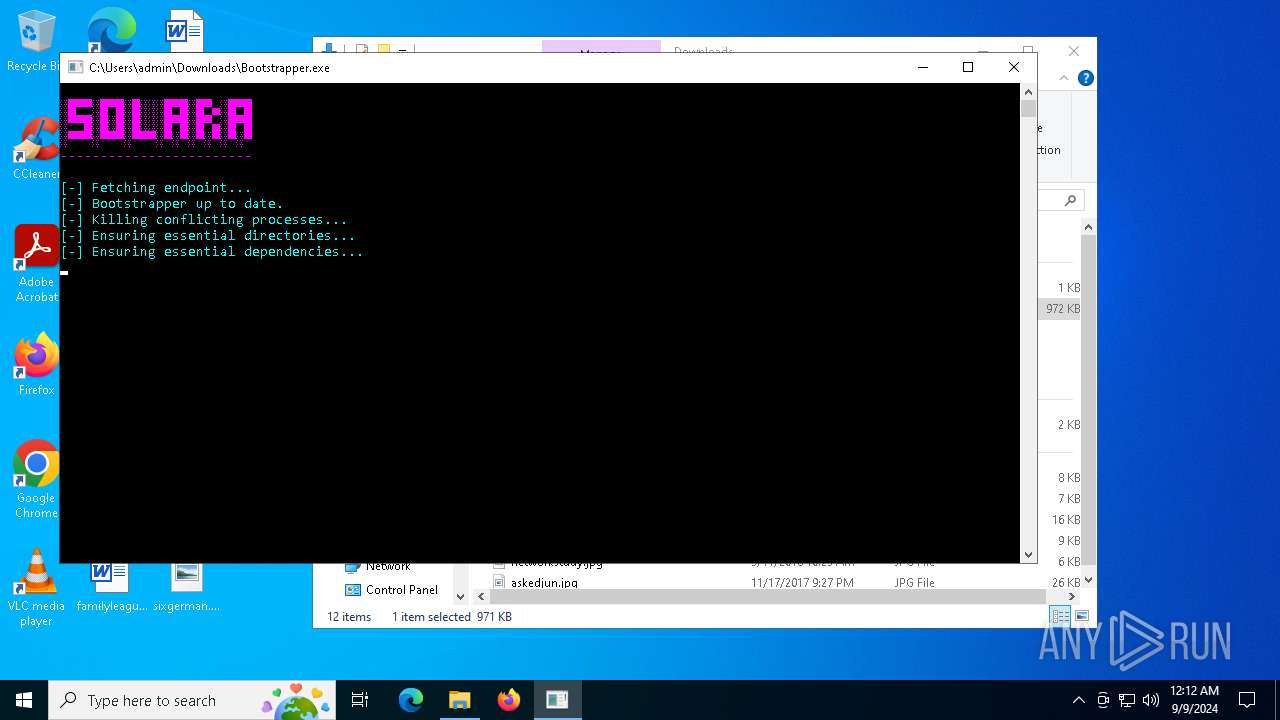
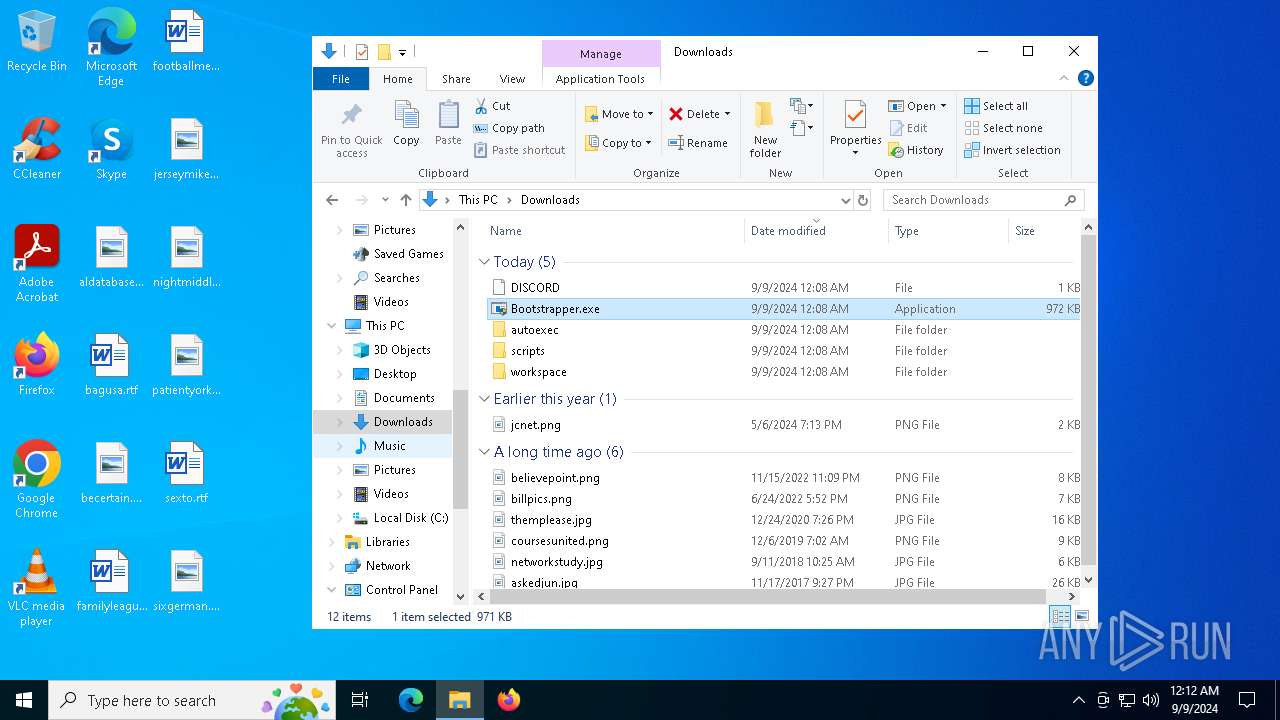
| URL: | https://getsolara.dev/download/static/files/Bootstrapper.exe |
| Full analysis: | https://app.any.run/tasks/9bba4112-f473-4981-a4f0-47258a625141 |
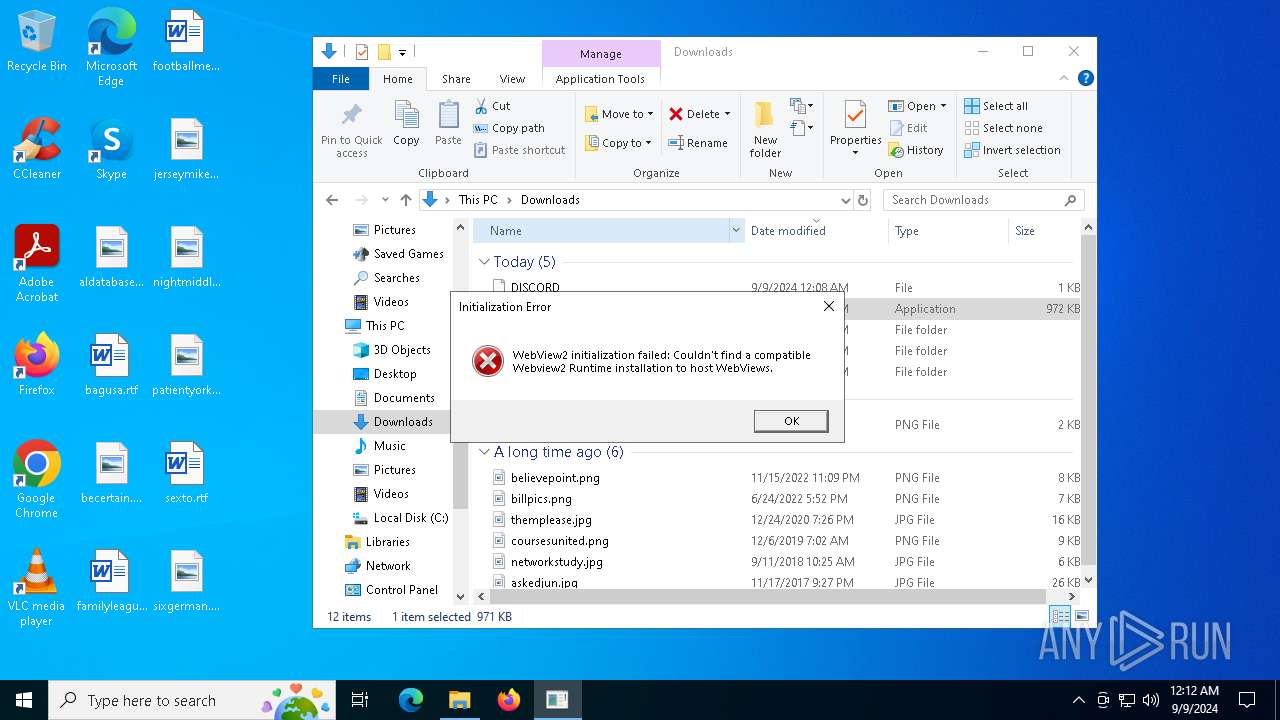
| Verdict: | Malicious activity |
| Analysis date: | September 09, 2024, 00:08:37 |
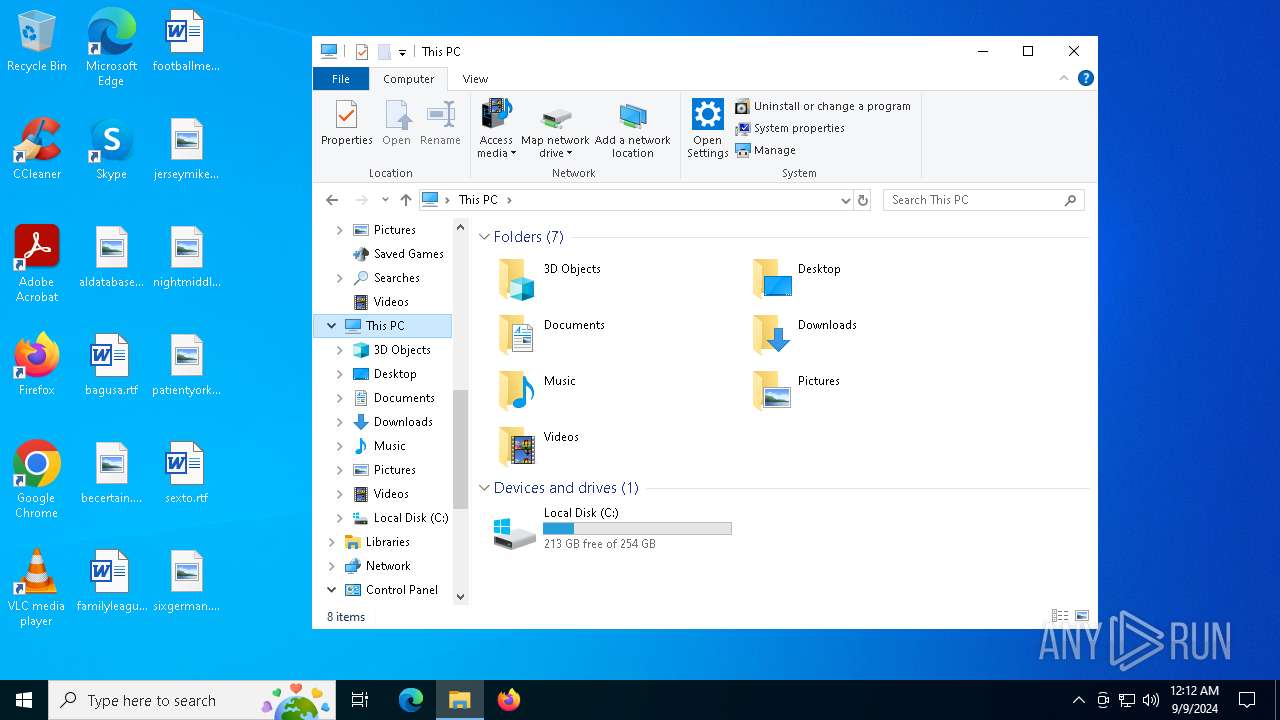
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 20E9FC3E4A7107090C8A7C4931808090 |
| SHA1: | 5D35F721BE48045589FC146EC7A2D07CEE2CE510 |
| SHA256: | F5B744F61D2B2EA0D224C820F2557D45285D563BDA6CF9B1368FD0626FDF9D6F |
| SSDEEP: | 3:N8h/J+y4ZKQ5KRRRw4A:2xw4A |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- Bootstrapper.exe (PID: 7832)
- msiexec.exe (PID: 7408)
- msiexec.exe (PID: 7732)
- Solara.exe (PID: 1748)
- Bootstrapper.exe (PID: 5644)
Reads the date of Windows installation
- Bootstrapper.exe (PID: 7832)
- Bootstrapper.exe (PID: 5644)
Checks Windows Trust Settings
- msiexec.exe (PID: 5044)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 5044)
Uses WEVTUTIL.EXE to install publishers and event logs from the manifest
- msiexec.exe (PID: 7732)
- wevtutil.exe (PID: 3040)
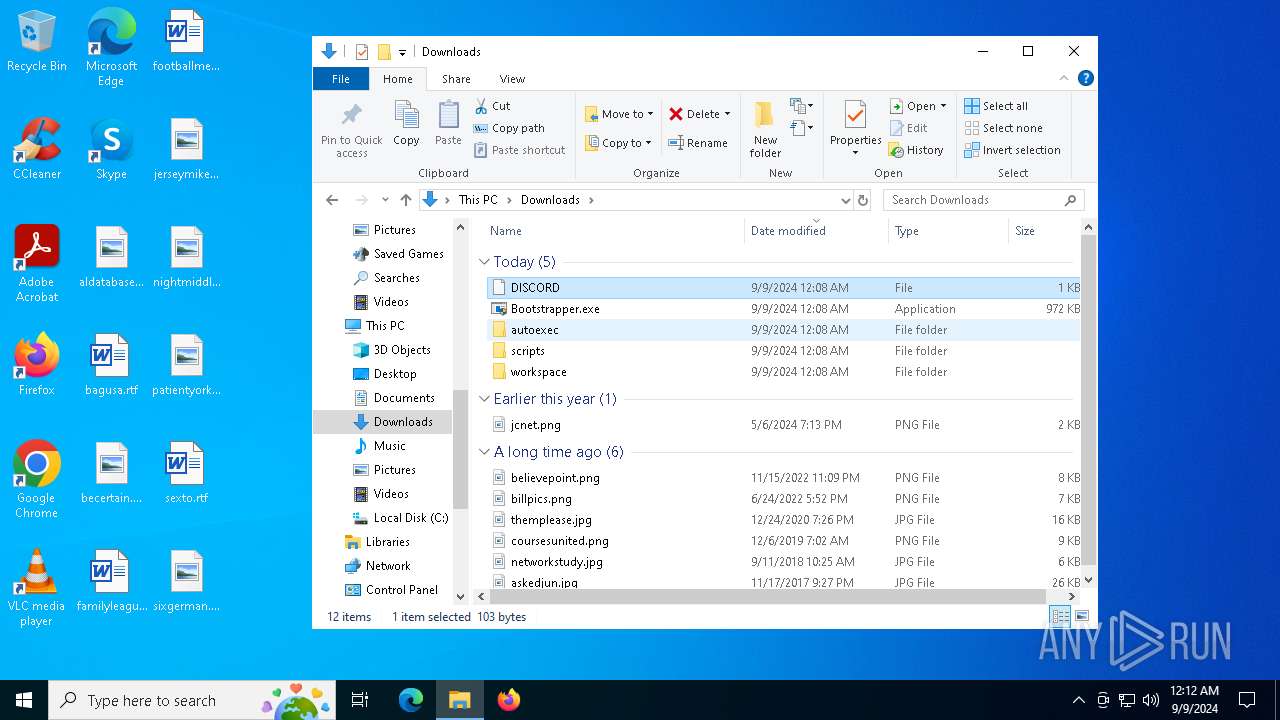
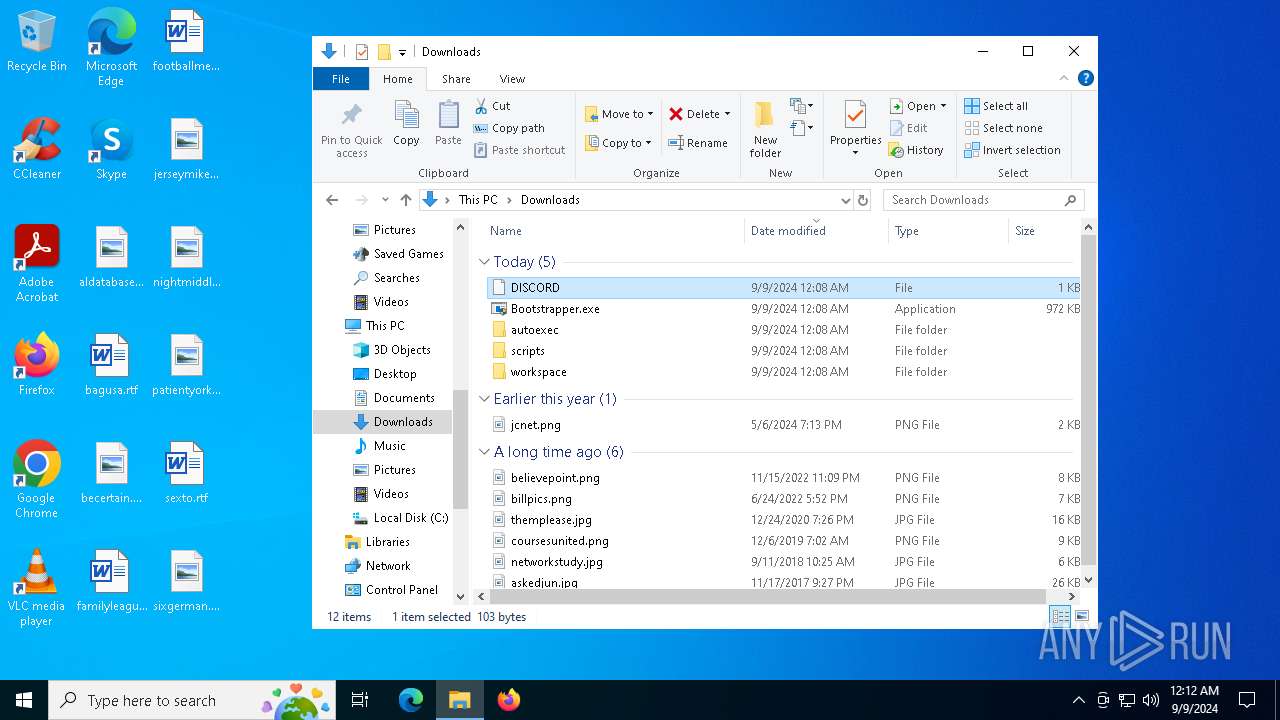
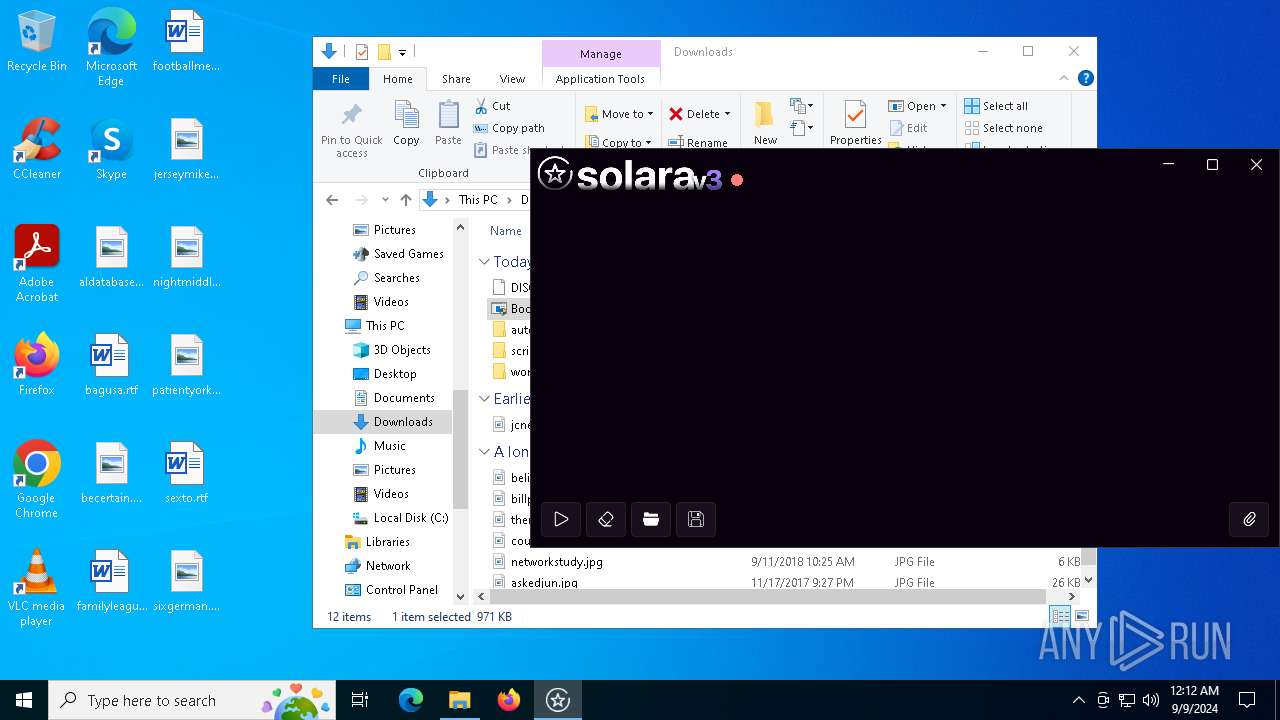
Executable content was dropped or overwritten
- Bootstrapper.exe (PID: 7832)
Process drops legitimate windows executable
- Bootstrapper.exe (PID: 7832)
The process drops C-runtime libraries
- Bootstrapper.exe (PID: 7832)
Executes script using NodeJS
- node.exe (PID: 7716)
Reads the BIOS version
- Solara.exe (PID: 1748)
INFO
The process uses the downloaded file
- msedge.exe (PID: 3112)
- Bootstrapper.exe (PID: 7832)
- msedge.exe (PID: 5344)
- Bootstrapper.exe (PID: 5644)
Executable content was dropped or overwritten
- msedge.exe (PID: 5344)
- msedge.exe (PID: 6672)
- msiexec.exe (PID: 5044)
Application launched itself
- msedge.exe (PID: 5344)
- msiexec.exe (PID: 5044)
- msedge.exe (PID: 8036)
Reads the machine GUID from the registry
- Bootstrapper.exe (PID: 7832)
- msiexec.exe (PID: 5044)
- Bootstrapper.exe (PID: 5644)
- Solara.exe (PID: 1748)
Reads the computer name
- Bootstrapper.exe (PID: 7832)
- msiexec.exe (PID: 5044)
- msiexec.exe (PID: 7028)
- msiexec.exe (PID: 7408)
- msiexec.exe (PID: 7732)
- identity_helper.exe (PID: 6324)
- Bootstrapper.exe (PID: 5644)
- Solara.exe (PID: 1748)
Checks supported languages
- Bootstrapper.exe (PID: 7832)
- msiexec.exe (PID: 5044)
- msiexec.exe (PID: 7732)
- msiexec.exe (PID: 7408)
- msiexec.exe (PID: 7028)
- identity_helper.exe (PID: 6324)
- Bootstrapper.exe (PID: 5644)
- node.exe (PID: 1288)
- Solara.exe (PID: 1748)
- node.exe (PID: 7716)
Reads Environment values
- Bootstrapper.exe (PID: 7832)
- identity_helper.exe (PID: 6324)
- Bootstrapper.exe (PID: 5644)
- Solara.exe (PID: 1748)
Create files in a temporary directory
- Bootstrapper.exe (PID: 7832)
Process checks computer location settings
- Bootstrapper.exe (PID: 7832)
- Bootstrapper.exe (PID: 5644)
Reads the software policy settings
- Bootstrapper.exe (PID: 7832)
- msiexec.exe (PID: 5044)
- Bootstrapper.exe (PID: 5644)
- Solara.exe (PID: 1748)
Disables trace logs
- Bootstrapper.exe (PID: 7832)
- Bootstrapper.exe (PID: 5644)
- Solara.exe (PID: 1748)
Checks proxy server information
- Bootstrapper.exe (PID: 7832)
- Bootstrapper.exe (PID: 5644)
- Solara.exe (PID: 1748)
Creates files or folders in the user directory
- msiexec.exe (PID: 5044)
Creates files in the program directory
- Bootstrapper.exe (PID: 7832)
Creates a software uninstall entry
- msiexec.exe (PID: 5044)
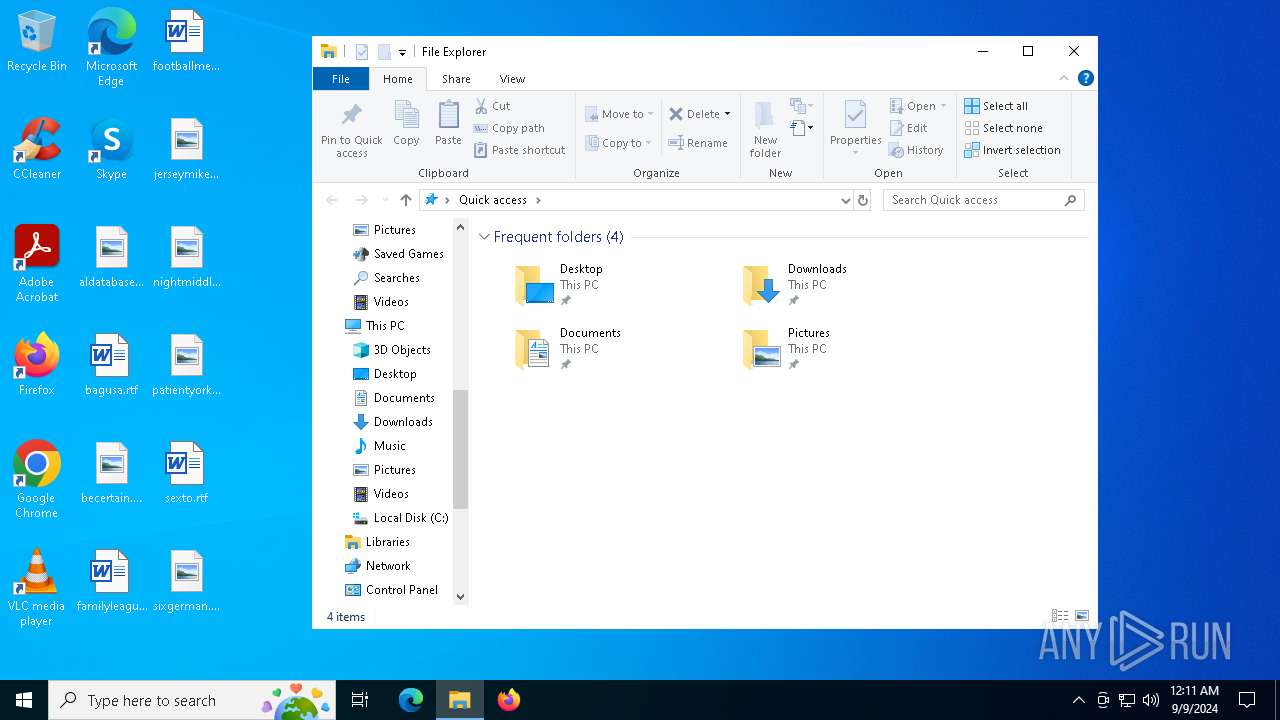
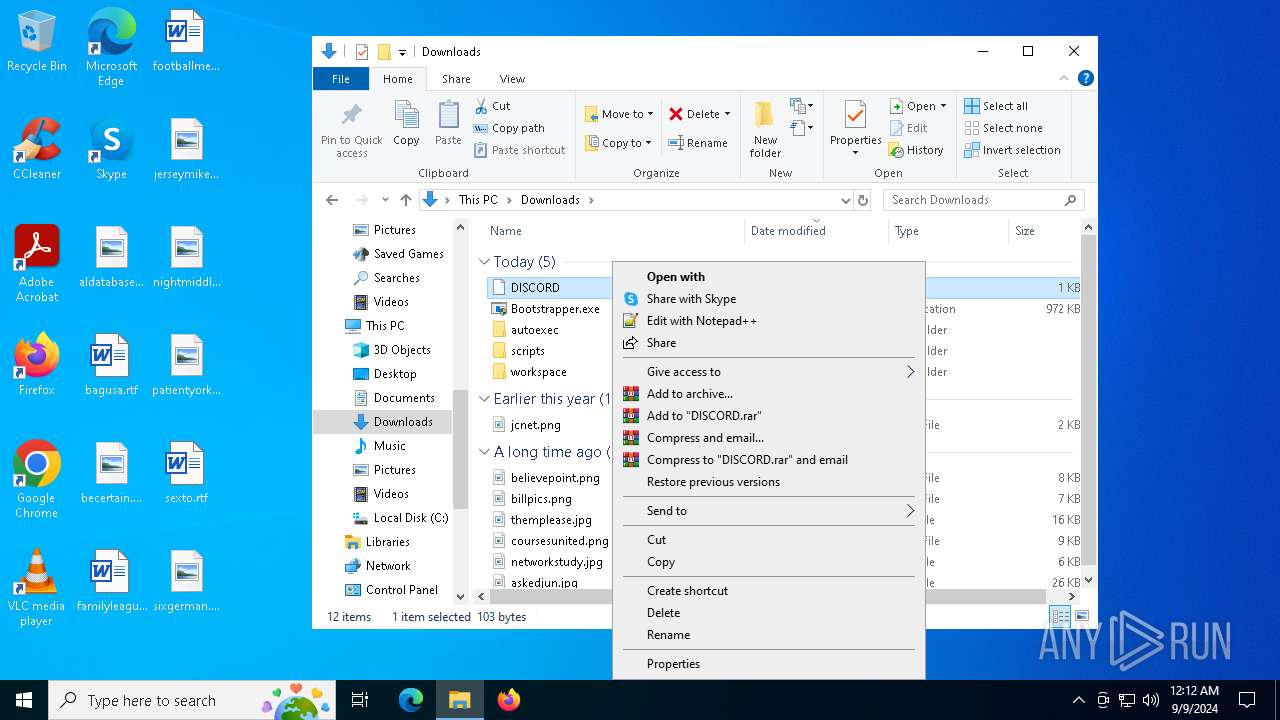
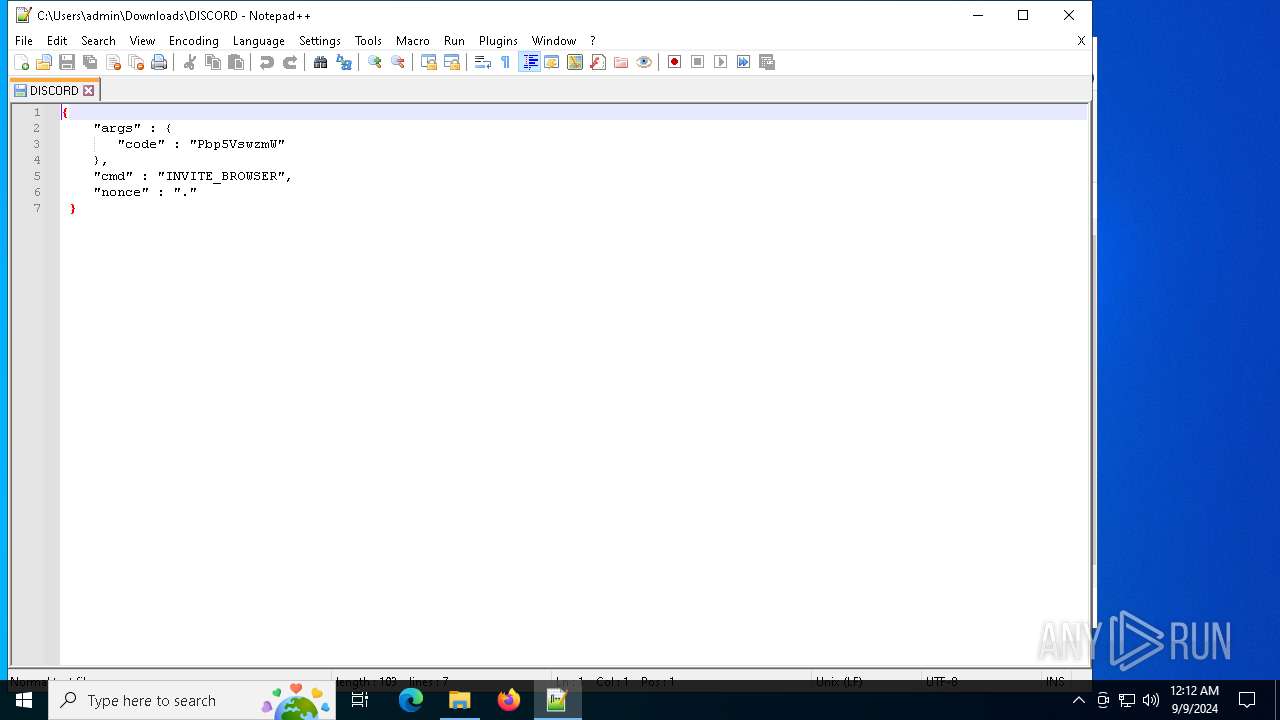
Manual execution by a user
- notepad++.exe (PID: 7640)
- Bootstrapper.exe (PID: 5644)
- Bootstrapper.exe (PID: 6336)
Sends debugging messages
- notepad++.exe (PID: 7640)
Process checks whether UAC notifications are on
- Solara.exe (PID: 1748)
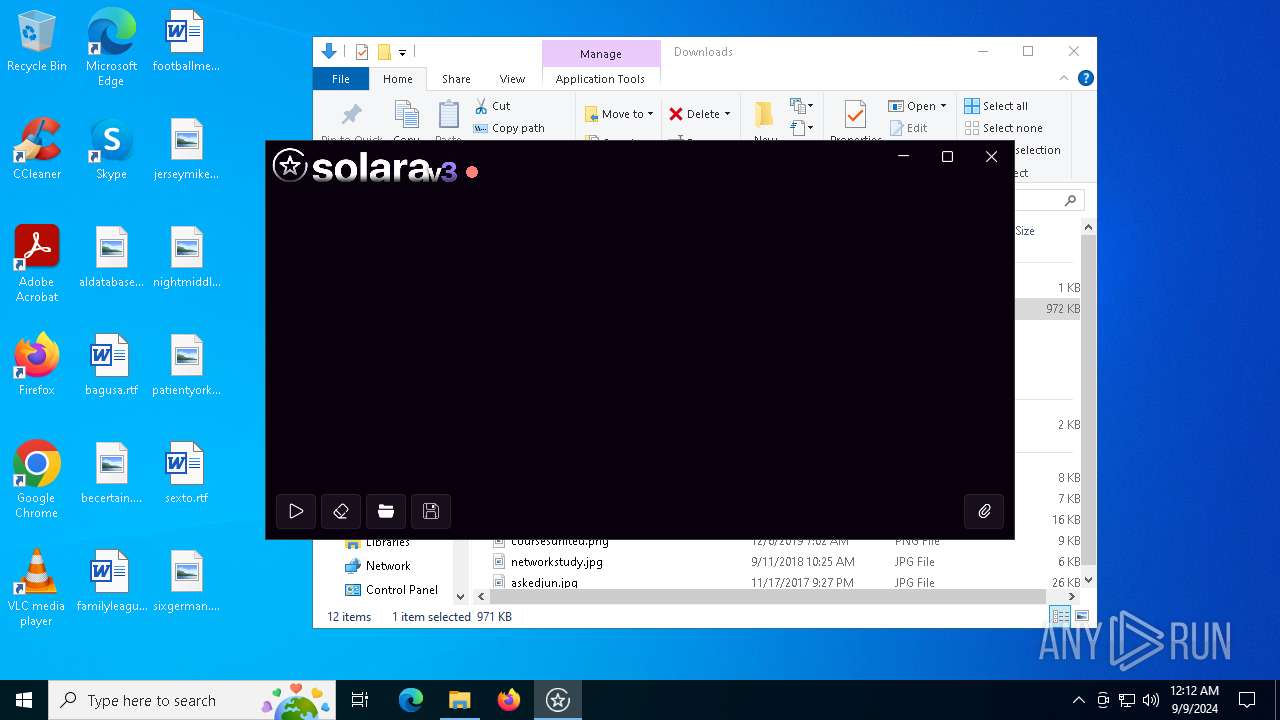
Themida protector has been detected
- Solara.exe (PID: 1748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
212
Monitored processes
79
Malicious processes
1
Suspicious processes
2
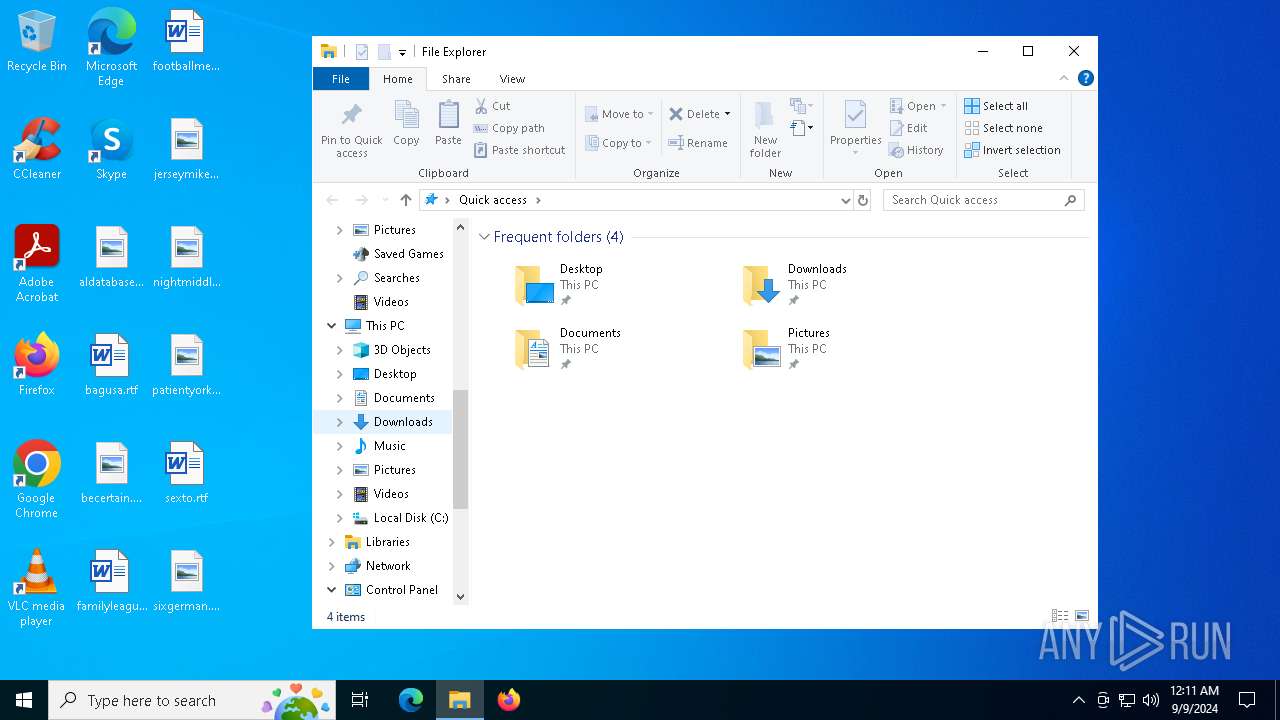
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7516 --field-trial-handle=2356,i,5506304834292860126,3908978022929421453,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 812 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=4364 --field-trial-handle=2356,i,5506304834292860126,3908978022929421453,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1020 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6360 --field-trial-handle=2356,i,5506304834292860126,3908978022929421453,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1116 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5876 --field-trial-handle=2356,i,5506304834292860126,3908978022929421453,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1148 | "wevtutil.exe" im "C:\Program Files\nodejs\node_etw_provider.man" /fromwow64 | C:\Windows\System32\wevtutil.exe | — | wevtutil.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Eventing Command Line Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1156 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7352 --field-trial-handle=2356,i,5506304834292860126,3908978022929421453,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1288 | "node" -v | C:\Program Files\nodejs\node.exe | — | Bootstrapper.exe | |||||||||||
User: admin Company: Node.js Integrity Level: HIGH Description: Node.js JavaScript Runtime Exit code: 0 Version: 18.16.0 Modules
| |||||||||||||||
| 1488 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5116 --field-trial-handle=2376,i,6210943394809417879,4088414246233369960,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
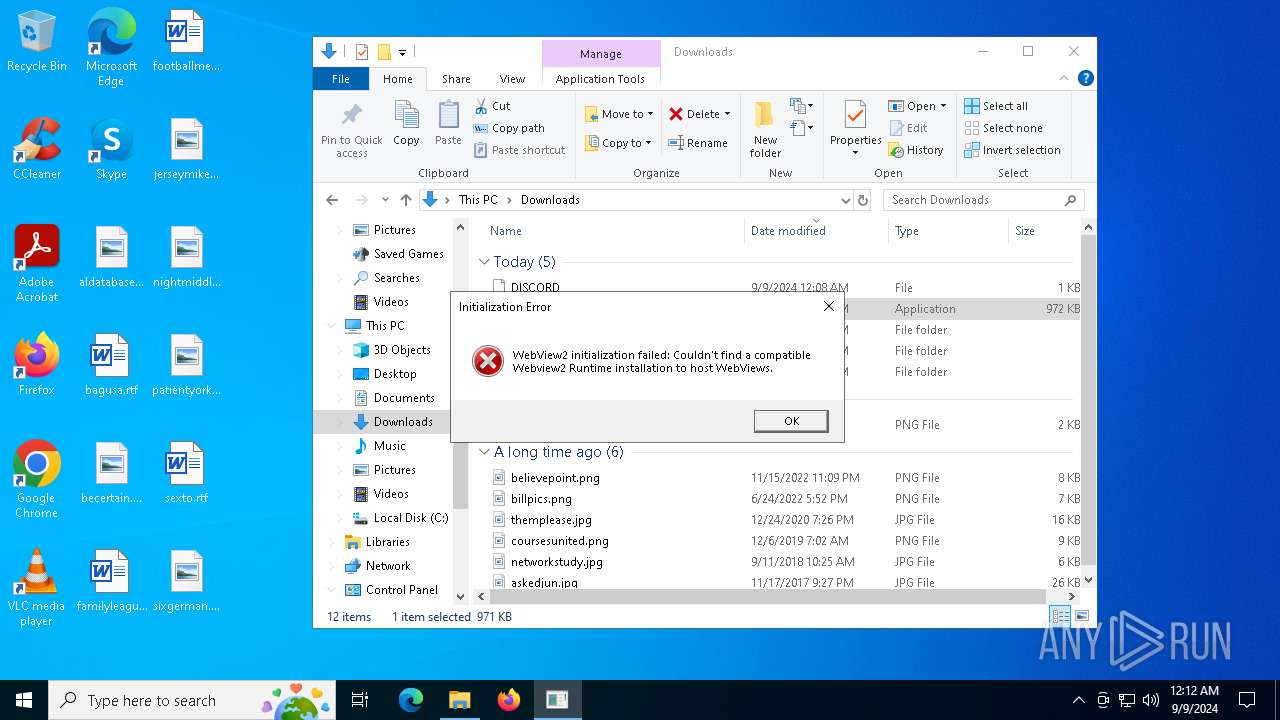
| 1748 | "C:\ProgramData\Solara\Solara.exe" | C:\ProgramData\Solara\Solara.exe | Bootstrapper.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: WpfApp1 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1992 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x294,0x298,0x29c,0x28c,0x2a4,0x7fffd20f5fd8,0x7fffd20f5fe4,0x7fffd20f5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
20 806
Read events
17 844
Write events
2 954
Delete events
8
Modification events
| (PID) Process: | (5344) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\Profiles |
| Operation: | write | Name: | EnhancedLinkOpeningDefault |
Value: Default | |||
| (PID) Process: | (5344) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459388 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6B55975D-1EBA-40C3-B367-990CAB0D5420} | |||
| (PID) Process: | (5344) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459388 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6D1B8A61-44DC-45D9-8FE6-17D0D0C5833D} | |||
| (PID) Process: | (3112) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000DFFED0714C02DB01 | |||
| (PID) Process: | (7832) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7832) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7832) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (7832) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (7832) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (7832) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
41
Suspicious files
1 430
Text files
1 662
Unknown types
21
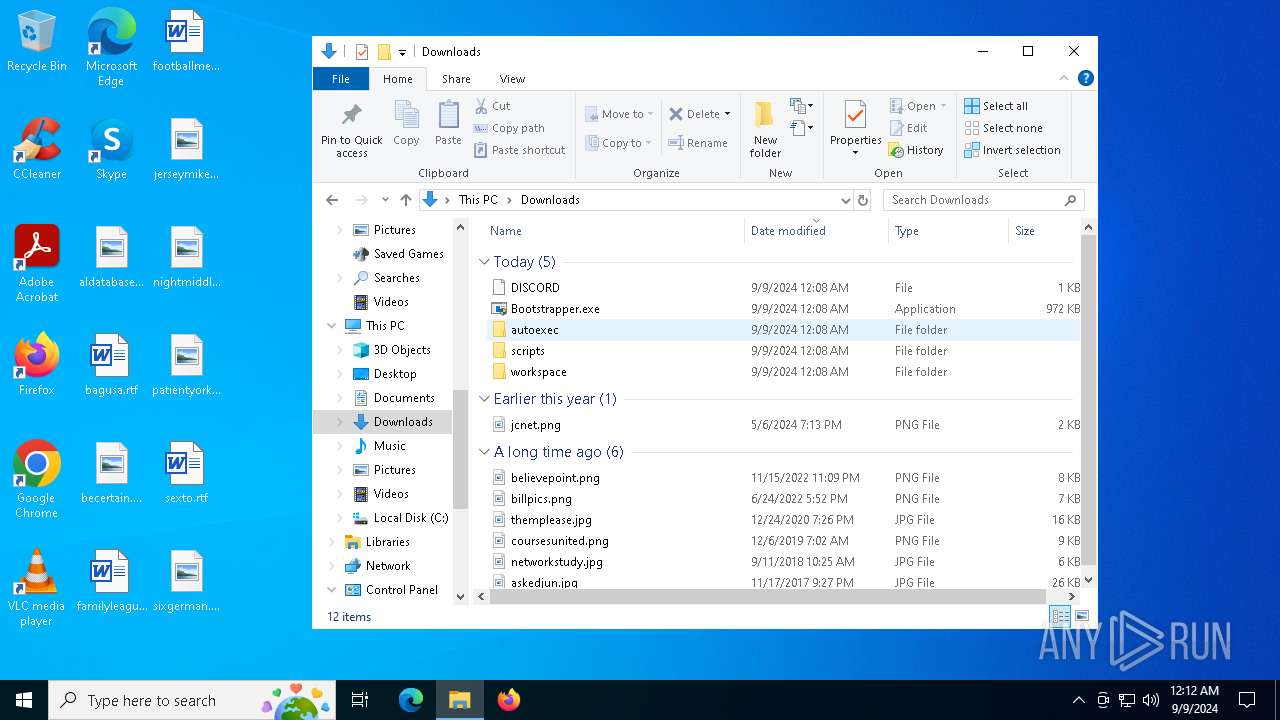
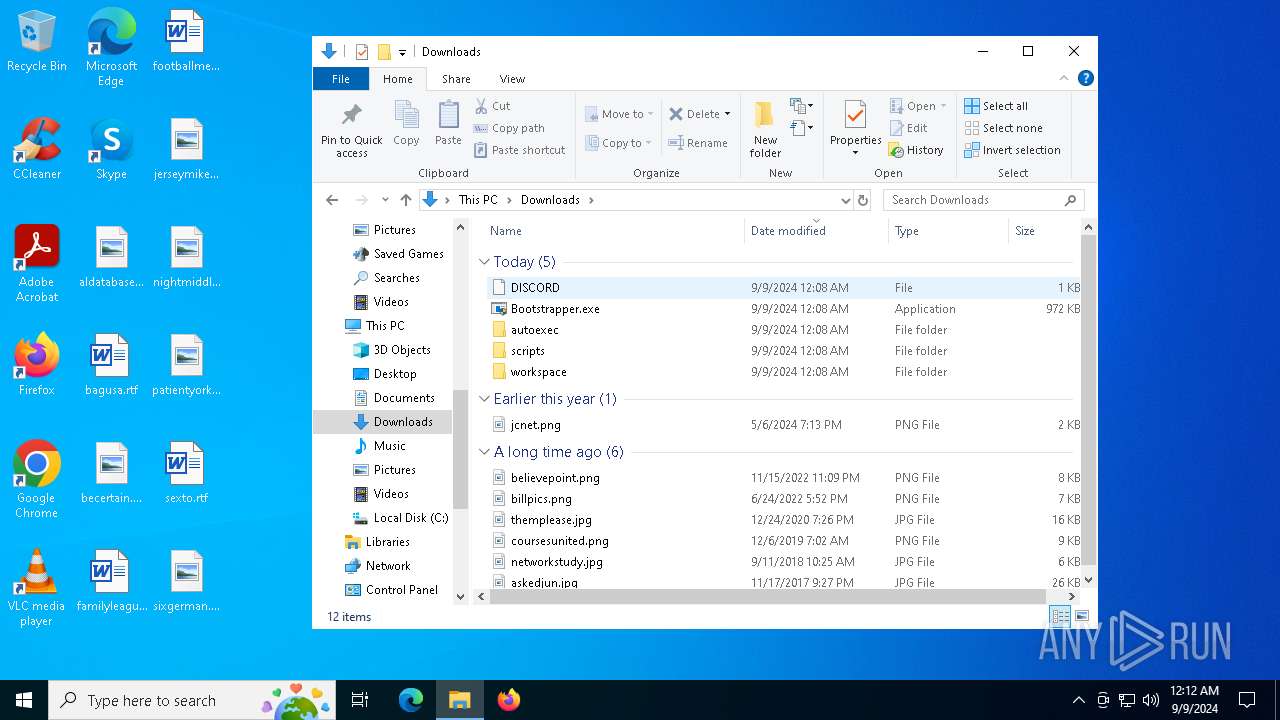
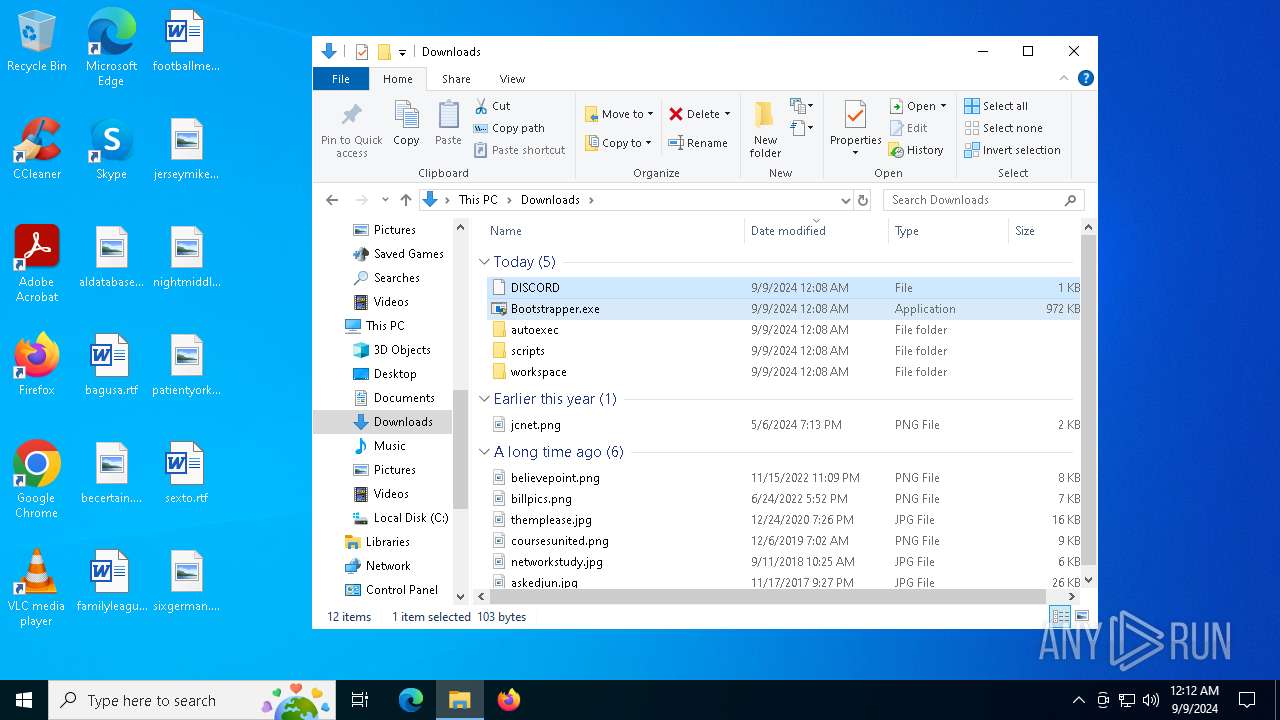
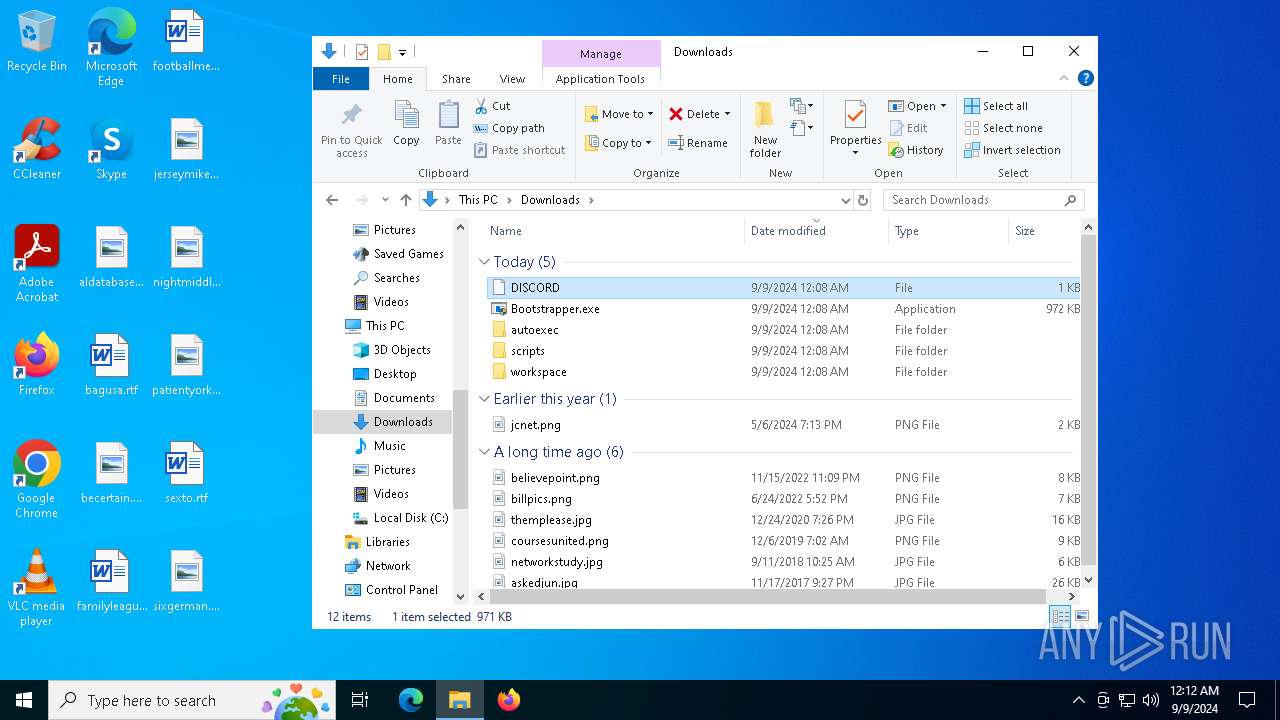
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF129da0.TMP | — | |
MD5:— | SHA256:— | |||
| 5344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF129daf.TMP | — | |
MD5:— | SHA256:— | |||
| 5344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF129dbf.TMP | — | |
MD5:— | SHA256:— | |||
| 5344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF129dbf.TMP | — | |
MD5:— | SHA256:— | |||
| 5344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF129dbf.TMP | — | |
MD5:— | SHA256:— | |||
| 5344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
54
TCP/UDP connections
90
DNS requests
74
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
8176 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
1780 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
8176 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
5044 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEAQJGBtf1btmdVNDtW%2BVUAg%3D | US | binary | 471 b | whitelisted |
5044 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSnR4FoxLLkI7vkvsUIFlZt%2BlGH3gQUWsS5eyoKo6XqcQPAYPkt9mV1DlgCEAOO2y%2FG5AVzGnYPFRYUTIU%3D | US | binary | 471 b | whitelisted |
7052 | svchost.exe | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/e1a6d3cd-ea4e-4162-9204-fbacd2128109?P1=1726096213&P2=404&P3=2&P4=EmkQdAbyLAvdJ5P9qqs1WAnbdfxkhldV%2f6y0oP%2byN%2bEH81Mc17fY%2bE6misAqwlyKrja8Ykpqif9rM1Rp0hz6wg%3d%3d | US | — | — | whitelisted |
7052 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/e1a6d3cd-ea4e-4162-9204-fbacd2128109?P1=1726096213&P2=404&P3=2&P4=EmkQdAbyLAvdJ5P9qqs1WAnbdfxkhldV%2f6y0oP%2byN%2bEH81Mc17fY%2bE6misAqwlyKrja8Ykpqif9rM1Rp0hz6wg%3d%3d | US | binary | 1.09 Kb | whitelisted |
7052 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/e1a6d3cd-ea4e-4162-9204-fbacd2128109?P1=1726096213&P2=404&P3=2&P4=EmkQdAbyLAvdJ5P9qqs1WAnbdfxkhldV%2f6y0oP%2byN%2bEH81Mc17fY%2bE6misAqwlyKrja8Ykpqif9rM1Rp0hz6wg%3d%3d | US | binary | 3.96 Kb | whitelisted |
7052 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/e1a6d3cd-ea4e-4162-9204-fbacd2128109?P1=1726096213&P2=404&P3=2&P4=EmkQdAbyLAvdJ5P9qqs1WAnbdfxkhldV%2f6y0oP%2byN%2bEH81Mc17fY%2bE6misAqwlyKrja8Ykpqif9rM1Rp0hz6wg%3d%3d | US | binary | 1.85 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4324 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 104.21.93.27:443 | getsolara.dev | CLOUDFLARENET | — | malicious |
— | — | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
getsolara.dev |
| malicious |
api.edgeoffer.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Pages platform for frontend developers to collaborate and deploy websites (pages .dev) |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|