analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
| download: | Document.exe |
| Full analysis: | https://app.any.run/tasks/c12cc8a7-a5e4-4696-89ed-0eac13cca450 |
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2020, 16:23:25 |
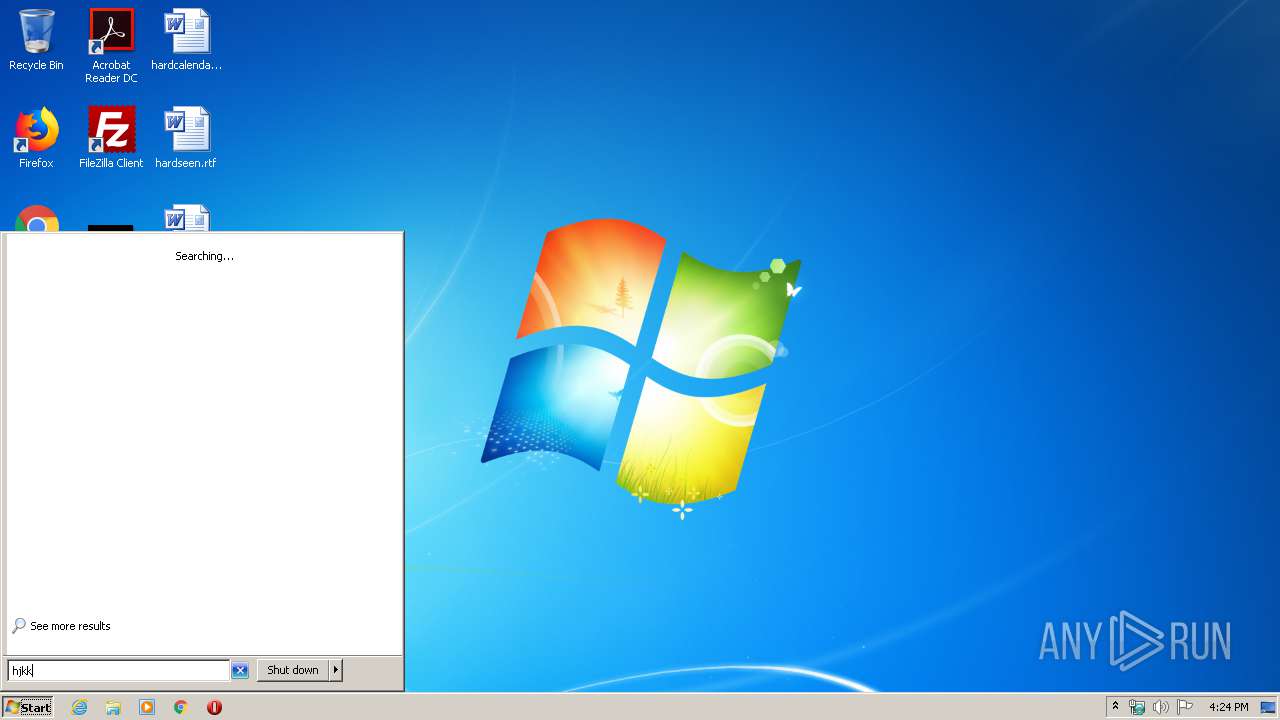
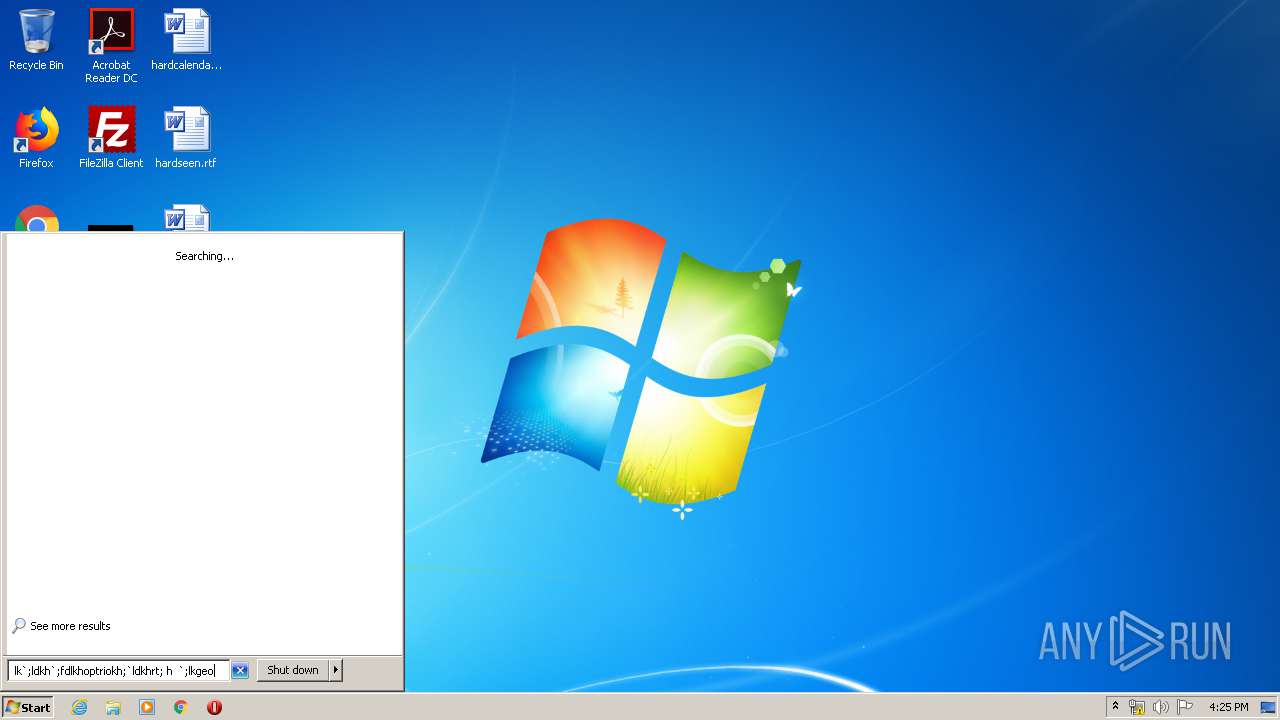
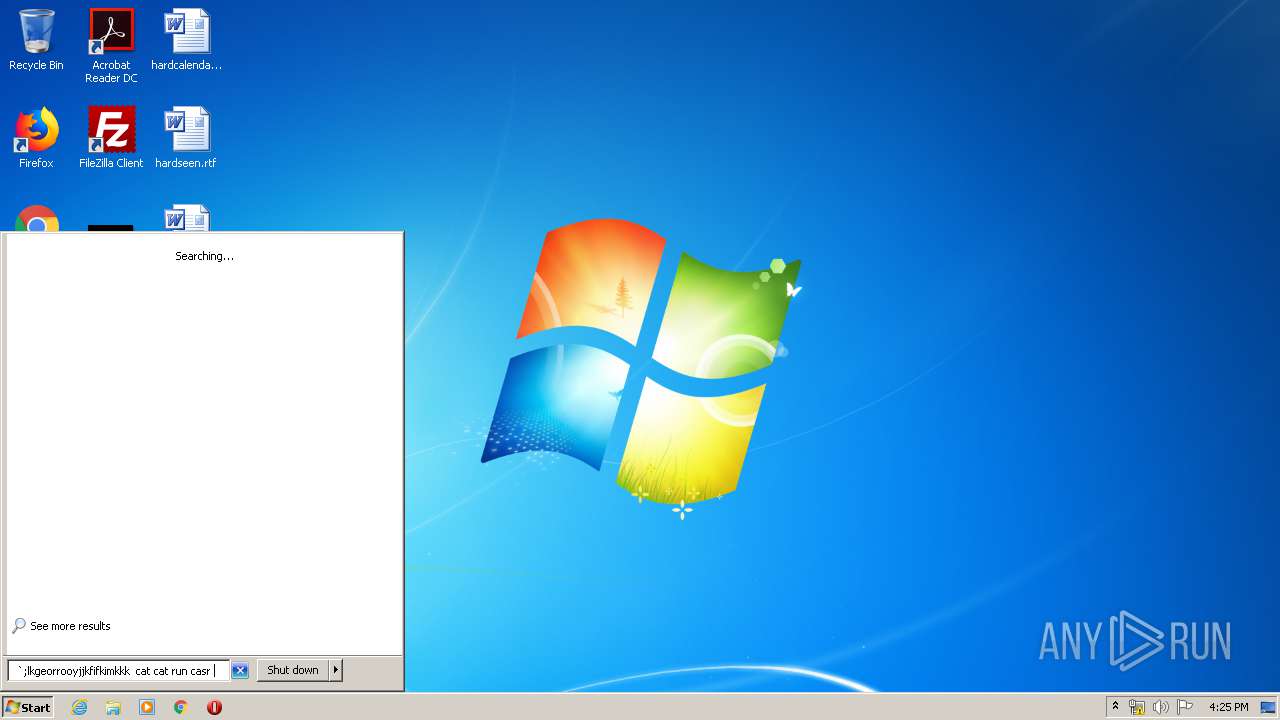
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 087505BAC9F1064757B0C16F883E7966 |
| SHA1: | E888969A254D111302FD9693F4C3A2FBA487BBBB |
| SHA256: | F5A7D425F4DC2CF665DB6EC120D2F22C24798F2C18F93750F4B53642D054BF1E |
| SSDEEP: | 384:tCJIert5Nk+qCaCKNvzm4fZYktmd623tDFdNY6ca2la9FFd0KDxiYJLLhhbCxu:Otv4fZYktd29DrxWa9FFlLL1hbCxu |
MALICIOUS
Starts Visual C# compiler
- Document.exe (PID: 1840)
Changes settings of System certificates
- Document.exe (PID: 1840)
SUSPICIOUS
Executes scripts
- Document.exe (PID: 1840)
Adds / modifies Windows certificates
- Document.exe (PID: 1840)
INFO
Reads settings of System Certificates
- Document.exe (PID: 1840)
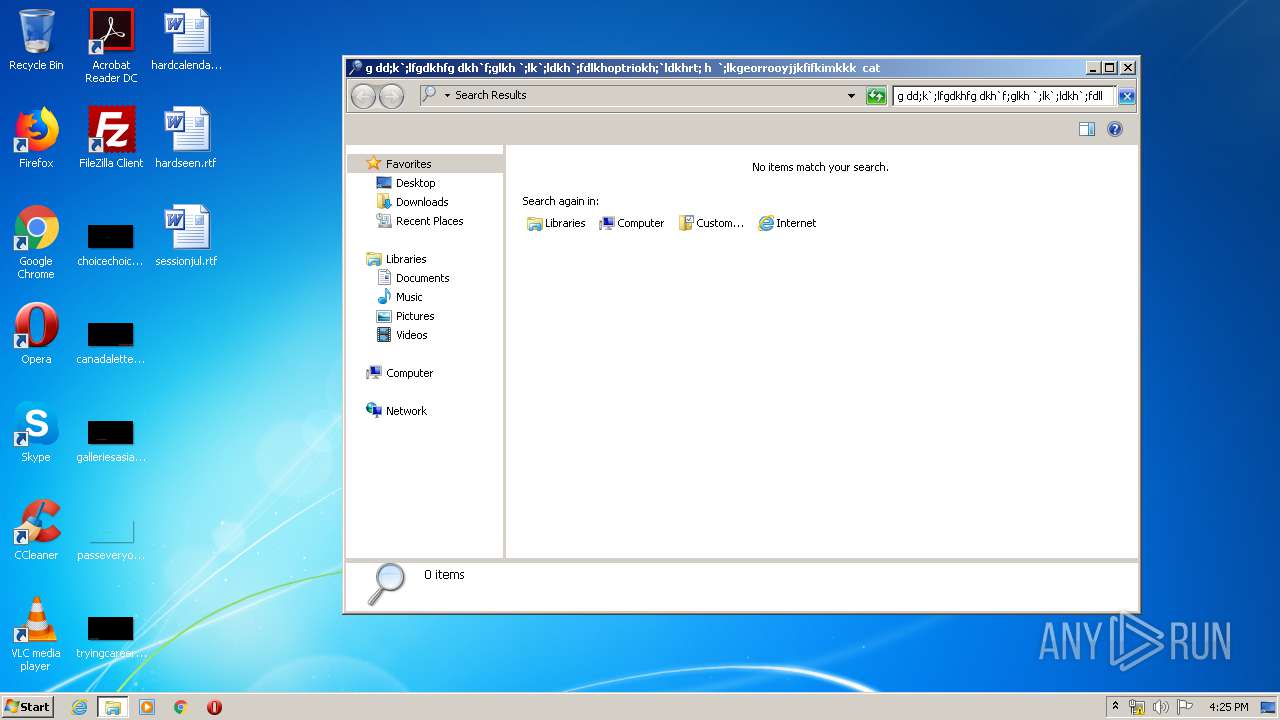
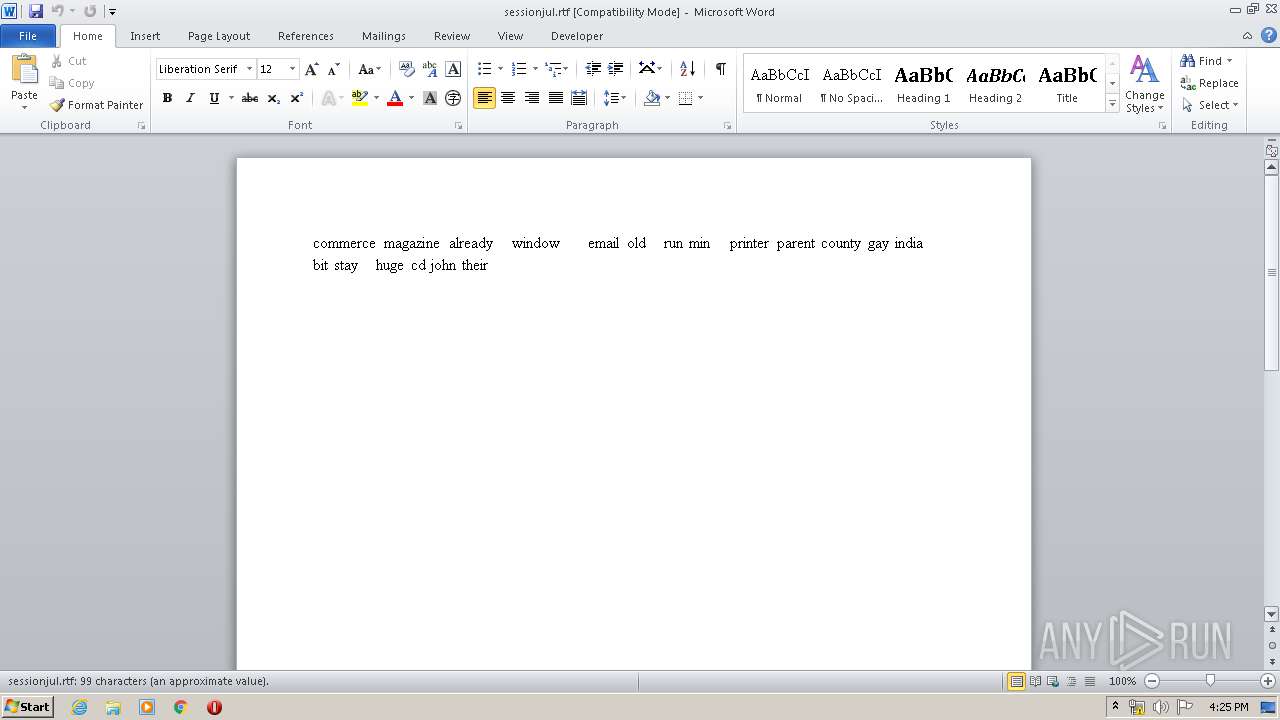
Creates files in the user directory
- WINWORD.EXE (PID: 3248)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3248)
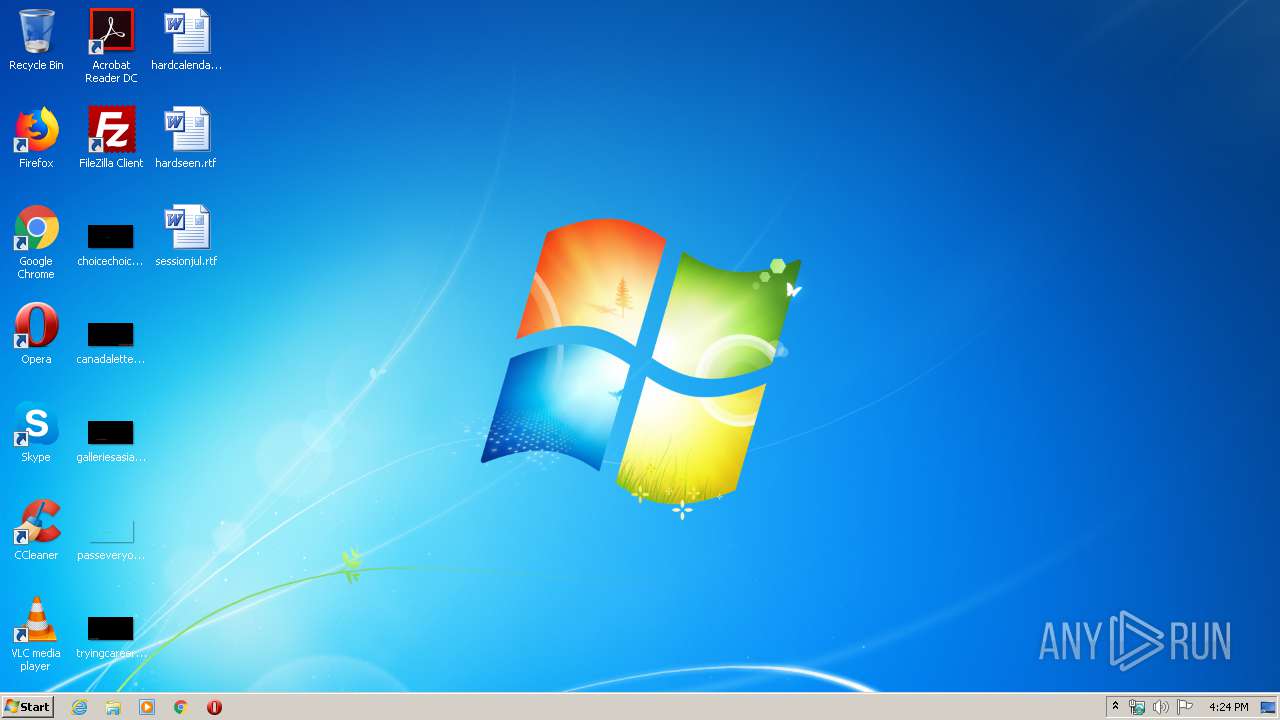
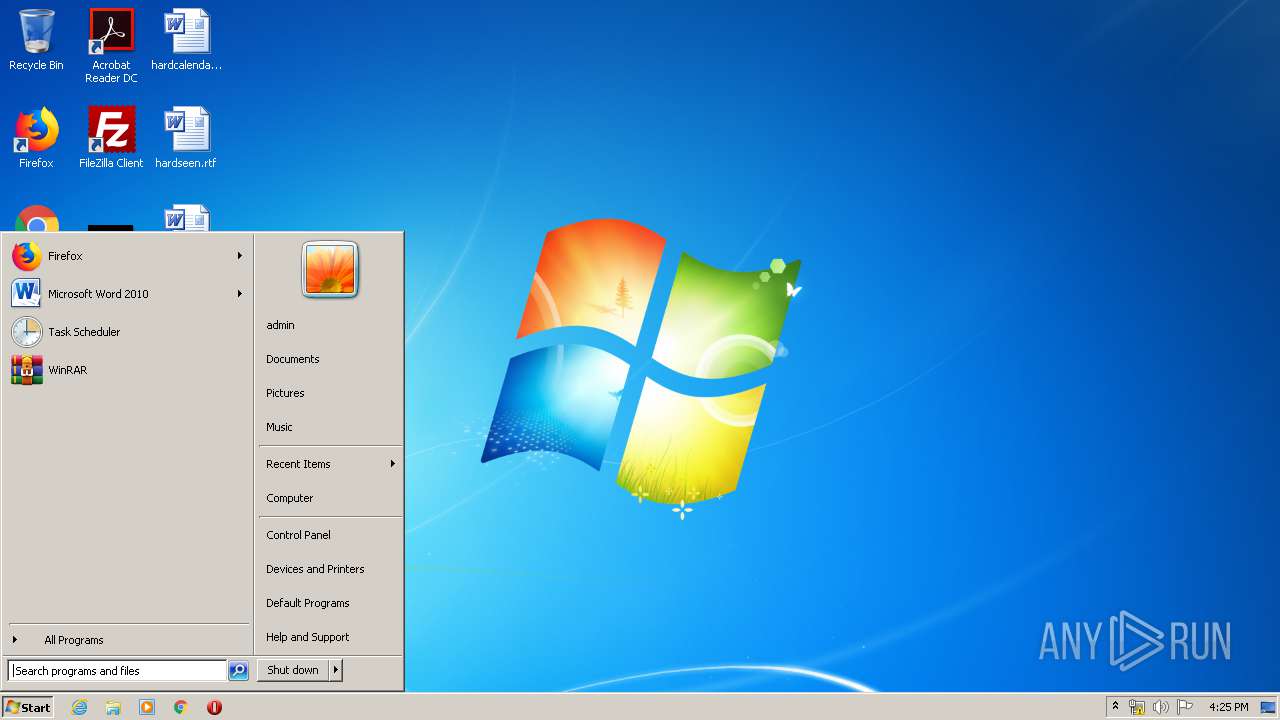
Manual execution by user
- WINWORD.EXE (PID: 3248)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2095:07:18 09:14:39+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 18432 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x665e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.0.62.0 |
| ProductVersionNumber: | 3.0.62.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Adobe Systems, Incorporated |
| FileDescription: | Adobe Owl Canvas |
| FileVersion: | 3.0.62 |
| InternalName: | Adobe Owl Canvas |
| LegalCopyright: | Copyright © 2007-2009 Adobe Systems Incorporated. All Rights Reserved. |
| OriginalFileName: | AdobeOwlCanvas.dll |
| BuildDate: | 2009/12/06-18:06:26 |
| BuildVersion: | 61.2381 |
| ProductName: | Adobe Owl Canvas |
| ProductVersion: | 3.0.62 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Jun-1959 00:46:23 |
| Detected languages: |
|
| CompanyName: | Adobe Systems, Incorporated |
| FileDescription: | Adobe Owl Canvas |
| FileVersion: | 3.0.62 |
| InternalName: | Adobe Owl Canvas |
| LegalCopyright: | Copyright © 2007-2009 Adobe Systems Incorporated. All Rights Reserved. |
| OriginalFilename: | AdobeOwlCanvas.dll |
| BuildDate: | 2009/12/06-18:06:26 |
| BuildVersion: | 61.2381 |
| ProductName: | Adobe Owl Canvas |
| ProductVersion: | 3.0.62 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 12-Jun-1959 00:46:23 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00004664 | 0x00004800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.58539 |
.rsrc | 0x00008000 | 0x0000043C | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.99007 |
.reloc | 0x0000A000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0776332 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.47857 | 996 | Latin 1 / Western European | English - United States | RT_VERSION |
Imports
mscoree.dll |
Total processes
72
Monitored processes
33
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 1840 | "C:\Users\admin\AppData\Local\Temp\Document.exe" | C:\Users\admin\AppData\Local\Temp\Document.exe | explorer.exe | |
User: admin Company: Adobe Systems, Incorporated Integrity Level: MEDIUM Description: Adobe Owl Canvas Exit code: 0 Version: 3.0.62 | ||||
| 2592 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess.exe | — | Document.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: AddInProcess.exe Exit code: 4294967295 Version: 4.7.3062.0 built by: NET472REL1 | ||||
| 2860 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe | — | Document.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: AddInProcess.exe Exit code: 4294967295 Version: 4.7.3062.0 built by: NET472REL1 | ||||
| 3200 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInUtil.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInUtil.exe | — | Document.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: AddInUtil.exe Exit code: 4294967295 Version: 4.7.3062.0 built by: NET472REL1 | ||||
| 3040 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\AppLaunch.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\AppLaunch.exe | — | Document.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET ClickOnce Launch Utility Exit code: 4294967295 Version: 4.7.3062.0 built by: NET472REL1 | ||||
| 3524 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_compiler.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_compiler.exe | — | Document.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: aspnet_compiler.exe Exit code: 4294967295 Version: 4.7.3062.0 built by: NET472REL1 | ||||
| 1544 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_regbrowsers.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_regbrowsers.exe | — | Document.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: aspnet_regbrowsers.exe Exit code: 4294967295 Version: 4.7.3062.0 built by: NET472REL1 | ||||
| 3832 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_regiis.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_regiis.exe | — | Document.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: aspnet_regiis.exe Exit code: 4294967295 Version: 4.7.3062.0 built by: NET472REL1 | ||||
| 1688 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_regsql.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_regsql.exe | — | Document.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: aspnet_regsql.exe Exit code: 4294967295 Version: 4.7.3062.0 built by: NET472REL1 | ||||
| 4008 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_state.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_state.exe | — | Document.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ASP.NET State Server Exit code: 4294967295 Version: 4.7.3062.0 built by: NET472REL1 | ||||
Total events
4 655
Read events
801
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
2
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3248 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR2190.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3248 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{E6CD5B50-315B-42E9-BD7D-01E10B31A4C0}.tmp | — | |
MD5:— | SHA256:— | |||
| 3248 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{1BF12C63-9A17-4E61-91D4-F00F62374969}.tmp | — | |
MD5:— | SHA256:— | |||
| 3248 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{4C309A5A-730B-4AB2-9BE3-12A1C013E4E3}.tmp | — | |
MD5:— | SHA256:— | |||
| 3248 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\sessionjul.rtf.LNK | lnk | |
MD5:205579B1A467A524F48F7F99FCDC7913 | SHA256:05AA433BD52674154193A0C4FF9DDA2FAB41A05E8DB2D8C1137AC8F9F0777E0B | |||
| 3248 | WINWORD.EXE | C:\Users\admin\Desktop\~$ssionjul.rtf | pgc | |
MD5:535589F462969D1F1463F3E62E72C262 | SHA256:986D93F65D633BAF894A422F6C5B085750F4BA105A9807390C5F001D3175A27B | |||
| 3248 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | ini | |
MD5:F2A111E172428B8130BD924783483344 | SHA256:25728B0B3B17D8D601E2C82A6F615469D88D7BED87371A0DC8A232586E4A45BF | |||
| 3248 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:1EB8DA6D98577C1264F47C2BFCA4D42E | SHA256:9428D7B4E7917699B06E3588EB7BDEDBA083E984BA4D4F030096F24DB5CBE038 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1840 | Document.exe | 81.177.165.131:443 | b.fastyou.ru | JSC RTComm.RU | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
b.fastyou.ru |
| unknown |