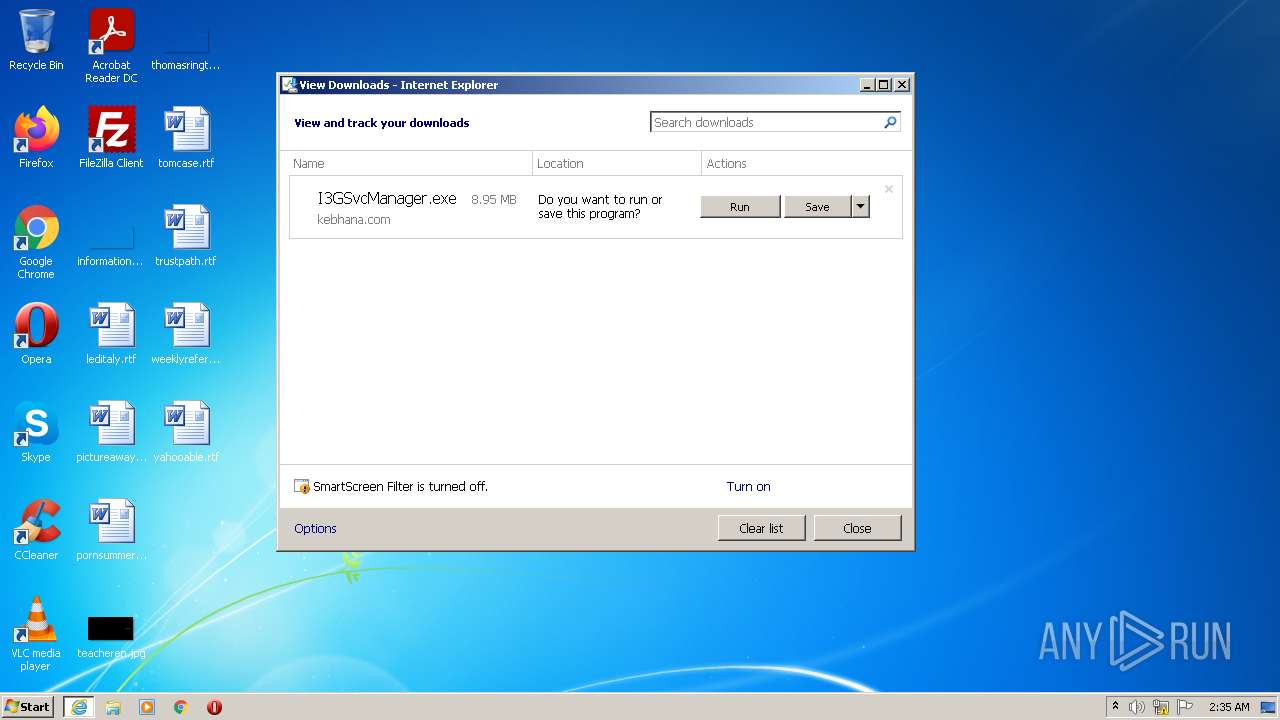
| URL: | https://www.kebhana.com/interezen/agent/np_v6/I3GSvcManager.exe |
| Full analysis: | https://app.any.run/tasks/4ac84348-82bb-4c3a-b433-3272ab916262 |
| Verdict: | Malicious activity |
| Analysis date: | July 22, 2022, 01:35:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 171462332F333A00893E083C313DE922 |
| SHA1: | 5667984CA521146F2BFC96852F58D15A59169F1C |
| SHA256: | F5A585110564DB0B59105B1789F558F3D5D51848C943EAD80D83E7D31535BC16 |
| SSDEEP: | 3:N8DSLlEUIKHZTK3FELM:2OL75Tm+LM |
MALICIOUS
Drops executable file immediately after starts
- iexplore.exe (PID: 2932)
- iexplore.exe (PID: 2876)
- I3GSvcManager.exe (PID: 2284)
- vcredist_x86.exe (PID: 2900)
Application was dropped or rewritten from another process
- I3GSvcManager.exe (PID: 2284)
- I3GSvcManager.exe (PID: 2216)
- certutil.exe (PID: 388)
- certmgr.exe (PID: 2752)
- I3GMainSvc.exe (PID: 4056)
- I3GMainSvc.exe (PID: 2660)
- certutil.exe (PID: 4052)
- vcredist_x86.exe (PID: 2900)
- I3GMainSvc.exe (PID: 2108)
- I3GInit.exe (PID: 1032)
- I3GProc.exe (PID: 1664)
Actions looks like stealing of personal data
- I3GSvcManager.exe (PID: 2284)
- certutil.exe (PID: 4052)
- certutil.exe (PID: 388)
Changes settings of System certificates
- certmgr.exe (PID: 2752)
- I3GInit.exe (PID: 1032)
Changes the autorun value in the registry
- I3GSvcManager.exe (PID: 2284)
Steals credentials from Web Browsers
- certutil.exe (PID: 4052)
- certutil.exe (PID: 388)
- I3GSvcManager.exe (PID: 2284)
Loads dropped or rewritten executable
- certutil.exe (PID: 4052)
- certutil.exe (PID: 388)
- I3GProc.exe (PID: 1664)
- install.exe (PID: 3172)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2876)
Drops a file with a compile date too recent
- iexplore.exe (PID: 2876)
- iexplore.exe (PID: 2932)
- I3GSvcManager.exe (PID: 2284)
- vcredist_x86.exe (PID: 2900)
Executable content was dropped or overwritten
- iexplore.exe (PID: 2876)
- I3GSvcManager.exe (PID: 2284)
- vcredist_x86.exe (PID: 2900)
- iexplore.exe (PID: 2932)
Reads Environment values
- I3GSvcManager.exe (PID: 2284)
- netsh.exe (PID: 2020)
- vcredist_x86.exe (PID: 2900)
Creates files in the Windows directory
- I3GSvcManager.exe (PID: 2284)
- msiexec.exe (PID: 3444)
Creates a directory in Program Files
- I3GSvcManager.exe (PID: 2284)
Reads the computer name
- I3GSvcManager.exe (PID: 2284)
- vcredist_x86.exe (PID: 2900)
- msiexec.exe (PID: 3444)
- install.exe (PID: 3172)
- certutil.exe (PID: 4052)
- I3GProc.exe (PID: 1664)
- certutil.exe (PID: 388)
- I3GMainSvc.exe (PID: 4056)
- I3GMainSvc.exe (PID: 2660)
- I3GMainSvc.exe (PID: 2108)
- I3GInit.exe (PID: 1032)
Creates files in the program directory
- I3GSvcManager.exe (PID: 2284)
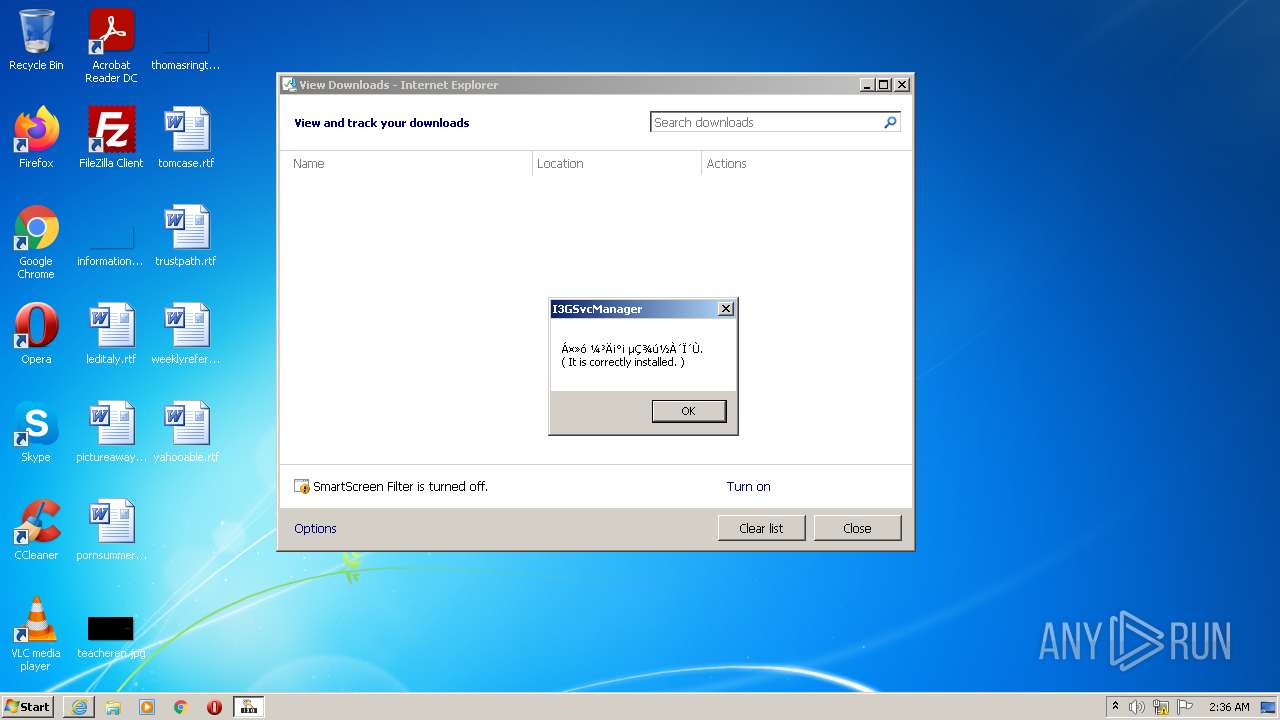
Creates a software uninstall entry
- I3GSvcManager.exe (PID: 2284)
Uses NETSH.EXE for network configuration
- I3GSvcManager.exe (PID: 2284)
Checks supported languages
- vcredist_x86.exe (PID: 2900)
- msiexec.exe (PID: 3444)
- certmgr.exe (PID: 2752)
- I3GSvcManager.exe (PID: 2284)
- certutil.exe (PID: 4052)
- certutil.exe (PID: 388)
- I3GProc.exe (PID: 1664)
- I3GMainSvc.exe (PID: 4056)
- I3GMainSvc.exe (PID: 2108)
- I3GMainSvc.exe (PID: 2660)
- I3GInit.exe (PID: 1032)
- install.exe (PID: 3172)
Reads Windows owner or organization settings
- msiexec.exe (PID: 3444)
Reads the Windows organization settings
- msiexec.exe (PID: 3444)
Removes files from Windows directory
- msiexec.exe (PID: 3444)
Creates files in the user directory
- certutil.exe (PID: 388)
Executed as Windows Service
- I3GMainSvc.exe (PID: 2108)
INFO
Checks supported languages
- iexplore.exe (PID: 2932)
- iexplore.exe (PID: 2876)
- netsh.exe (PID: 2020)
Application launched itself
- iexplore.exe (PID: 2932)
Changes internet zones settings
- iexplore.exe (PID: 2932)
Reads the computer name
- iexplore.exe (PID: 2876)
- iexplore.exe (PID: 2932)
- netsh.exe (PID: 2020)
Checks Windows Trust Settings
- iexplore.exe (PID: 2876)
- iexplore.exe (PID: 2932)
- msiexec.exe (PID: 3444)
- I3GInit.exe (PID: 1032)
Reads settings of System Certificates
- iexplore.exe (PID: 2876)
- iexplore.exe (PID: 2932)
- msiexec.exe (PID: 3444)
- certmgr.exe (PID: 2752)
- I3GInit.exe (PID: 1032)
Creates files in the user directory
- iexplore.exe (PID: 2876)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2932)
Reads the date of Windows installation
- iexplore.exe (PID: 2932)
Changes settings of System certificates
- iexplore.exe (PID: 2932)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2932)
Dropped object may contain Bitcoin addresses
- I3GSvcManager.exe (PID: 2284)
Creates a software uninstall entry
- msiexec.exe (PID: 3444)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
60
Monitored processes
16
Malicious processes
7
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 388 | "C:\Program Files\IPinside_LWS\certfr\certutil.exe" -A -n "Interezen CA" -t "CP,CP," -i "C:\Program Files\IPinside_LWS\interezen-rootca.crt" -d "sql:C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default" | C:\Program Files\IPinside_LWS\certfr\certutil.exe | I3GSvcManager.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1032 | "C:\Program Files\IPinside_LWS\I3GInit.exe" | C:\Program Files\IPinside_LWS\I3GInit.exe | — | I3GProc.exe | |||||||||||
User: admin Company: Interezen. Co., Ltd. Integrity Level: HIGH Exit code: 0 Version: 3.0.0.2 Modules
| |||||||||||||||
| 1664 | "C:\Program Files\IPinside_LWS\I3GProc.exe" | C:\Program Files\IPinside_LWS\I3GProc.exe | — | I3GSvcManager.exe | |||||||||||
User: admin Company: Interezen. Co., Ltd. Integrity Level: HIGH Description: Interezen Process Exit code: 0 Version: 3.0.0.16 Modules
| |||||||||||||||
| 2020 | "C:\Windows\System32\netsh.exe" advfirewall firewall add rule name = "Interezen Process" dir=in action=allow program="C:\Program Files\IPinside_LWS\I3GProc.exe" enable=yes | C:\Windows\System32\netsh.exe | — | I3GSvcManager.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2108 | "C:\Program Files\IPinside_LWS\I3GMainSvc.exe" | C:\Program Files\IPinside_LWS\I3GMainSvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Interezen. Co., Ltd. Integrity Level: SYSTEM Description: Interezen Service Program Exit code: 0 Version: 3.0.0.3 Modules
| |||||||||||||||
| 2216 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\I3GSvcManager.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\I3GSvcManager.exe | — | iexplore.exe | |||||||||||
User: admin Company: Interezen. Co., Ltd. Integrity Level: MEDIUM Description: I3GManager LWS Module Installer Exit code: 3221226540 Version: 3.0.0.16 Modules
| |||||||||||||||
| 2284 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\I3GSvcManager.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\I3GSvcManager.exe | iexplore.exe | ||||||||||||
User: admin Company: Interezen. Co., Ltd. Integrity Level: HIGH Description: I3GManager LWS Module Installer Exit code: 0 Version: 3.0.0.16 Modules
| |||||||||||||||
| 2660 | "C:\Program Files\IPinside_LWS\I3GMainSvc.exe" -start | C:\Program Files\IPinside_LWS\I3GMainSvc.exe | — | I3GSvcManager.exe | |||||||||||
User: admin Company: Interezen. Co., Ltd. Integrity Level: HIGH Description: Interezen Service Program Exit code: 0 Version: 3.0.0.3 Modules
| |||||||||||||||
| 2752 | "C:\Program Files\IPinside_LWS\certmgr.exe" /add /c interezen-rootca.crt /s /r localMachine root | C:\Program Files\IPinside_LWS\certmgr.exe | — | I3GSvcManager.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ECM Certificate Manager Exit code: 0 Version: 5.131.1863.1 Modules
| |||||||||||||||
| 2876 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2932 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
95 787
Read events
95 280
Write events
492
Delete events
15
Modification events
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30973291 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30973291 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
30
Suspicious files
8
Text files
19
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2876 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\2A7611428D62805A3E4E5BC4103D82E4_E16F3AF852C0CB92002C8B8BAE928280 | der | |
MD5:— | SHA256:— | |||
| 2876 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\285248A5750721A9ACC886EF3622CE11_A7F2AA59210F69E9F18B03B2DC954BA3 | binary | |
MD5:— | SHA256:— | |||
| 2876 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\I3GSvcManager[1].exe | executable | |
MD5:— | SHA256:— | |||
| 2876 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\285248A5750721A9ACC886EF3622CE11_A7F2AA59210F69E9F18B03B2DC954BA3 | der | |
MD5:— | SHA256:— | |||
| 2932 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 2932 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2876 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\1NSN2JPS.txt | text | |
MD5:— | SHA256:— | |||
| 2932 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:— | SHA256:— | |||
| 2932 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 2876 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\2A7611428D62805A3E4E5BC4103D82E4_E16F3AF852C0CB92002C8B8BAE928280 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
15
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2876 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://status.thawte.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQnt%2BO7KdI35ubyUVwz39VP7XeuiQQU5wH8DBYYyn2yjOyHJ6NvYYE7hDkCEAY6MdGABYaHkydFFJ7FwJU%3D | US | der | 471 b | whitelisted |
2932 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
2876 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAaWj5ZK6CNWx04XwrU2WwA%3D | US | der | 471 b | whitelisted |
2932 | iexplore.exe | GET | 200 | 8.248.117.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?933bead0edc51bf2 | US | compressed | 4.70 Kb | whitelisted |
2932 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2876 | iexplore.exe | GET | 200 | 8.248.117.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?22d680452c1be668 | US | compressed | 4.70 Kb | whitelisted |
2932 | iexplore.exe | GET | 200 | 8.248.117.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?5d5316d772b7bea3 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2932 | iexplore.exe | 8.248.117.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | malicious |
2932 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2876 | iexplore.exe | 59.11.68.10:443 | www.kebhana.com | Hana Bank Co. | KR | unknown |
2932 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2932 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2876 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2876 | iexplore.exe | 8.248.117.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.kebhana.com |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
status.thawte.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |