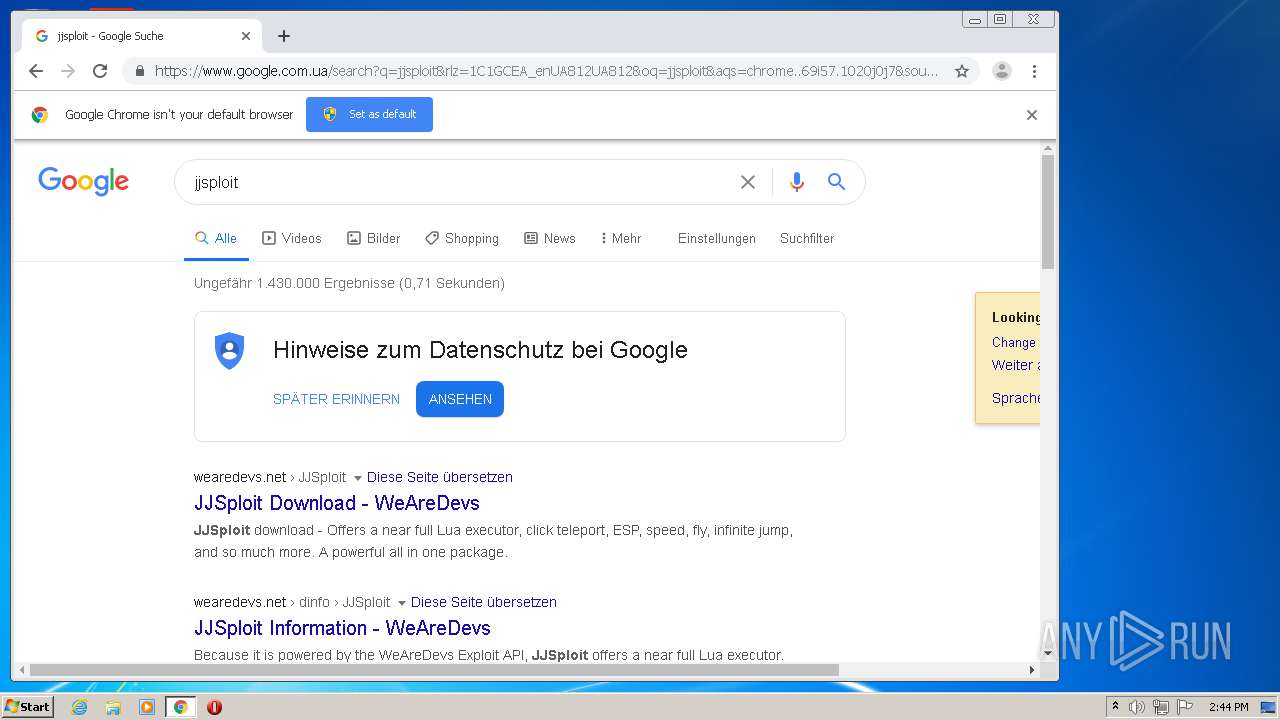
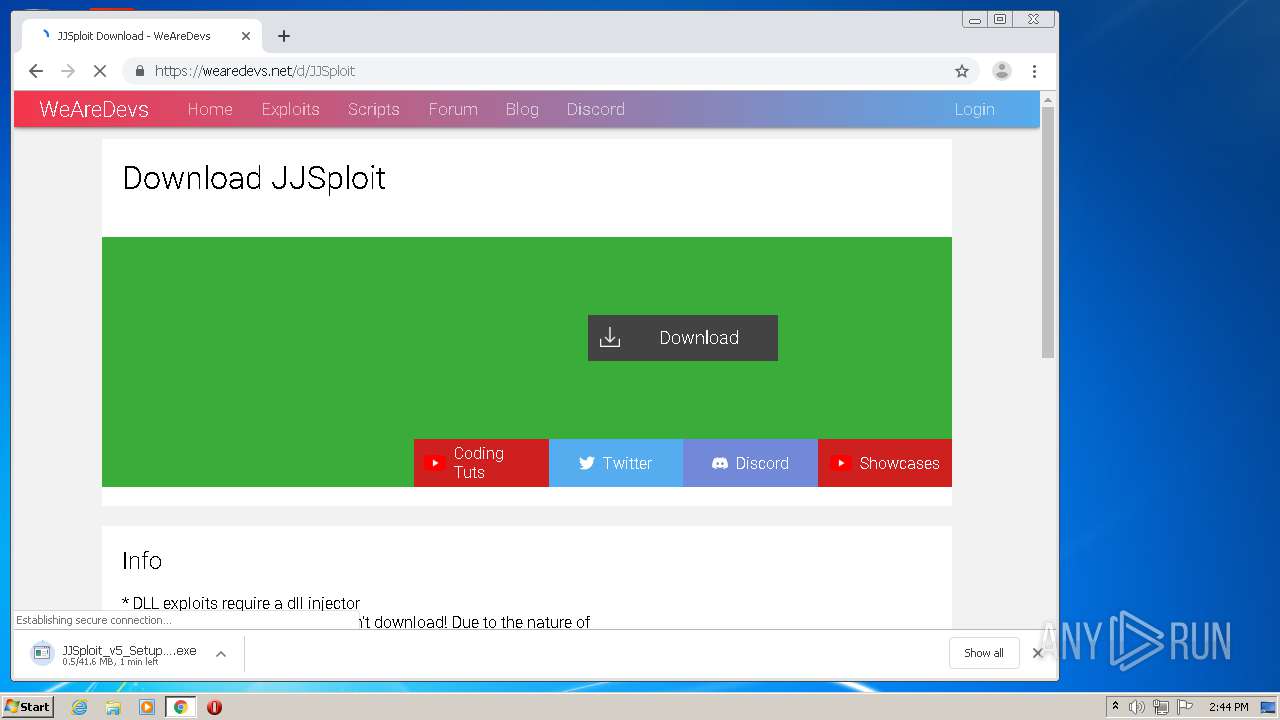
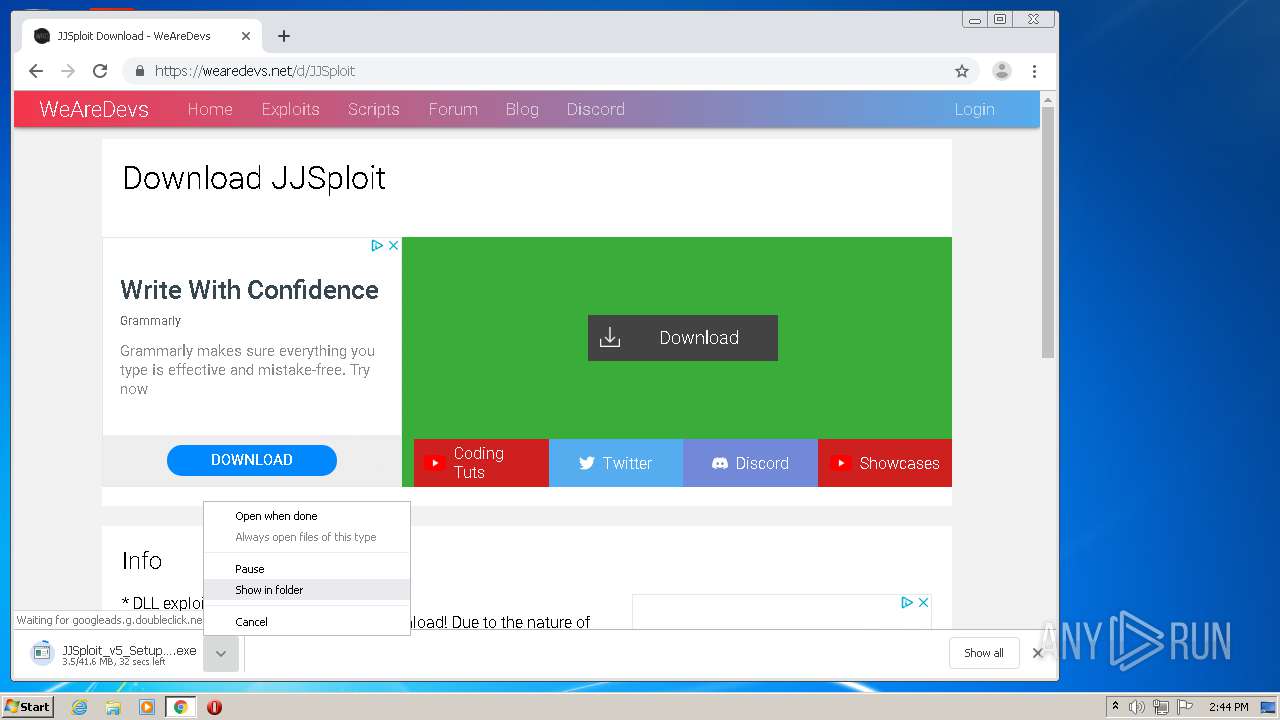
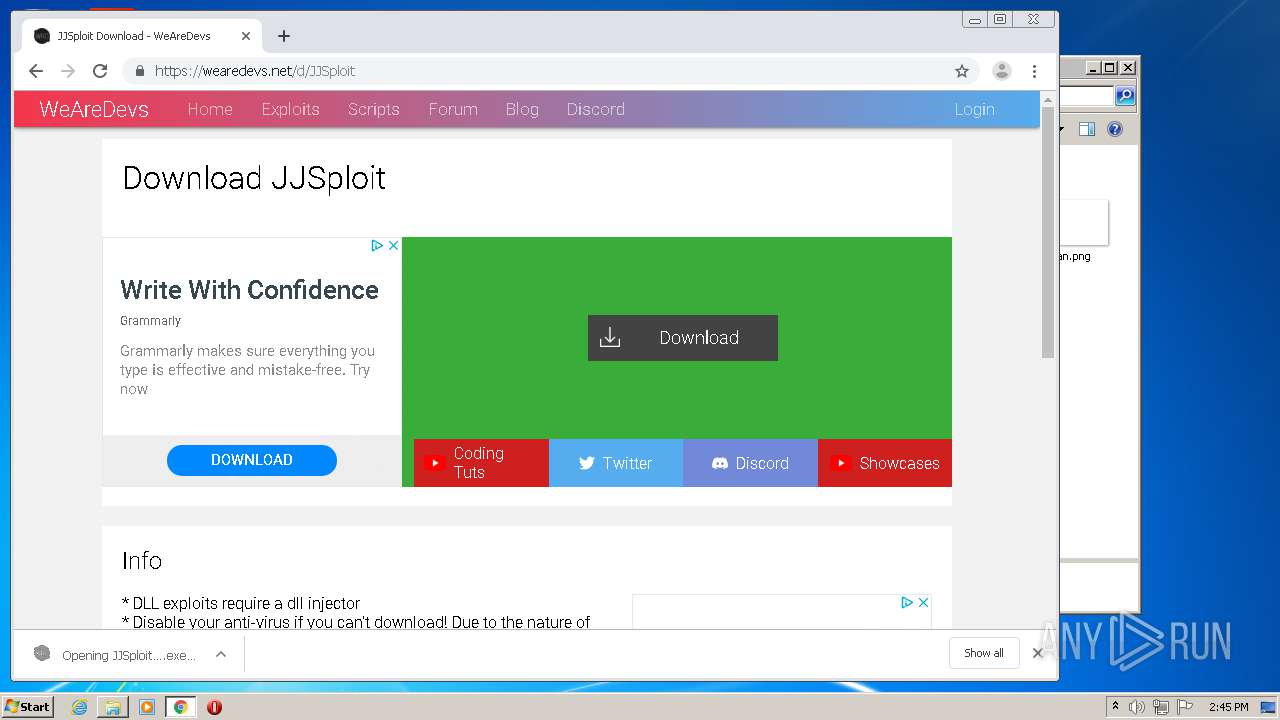
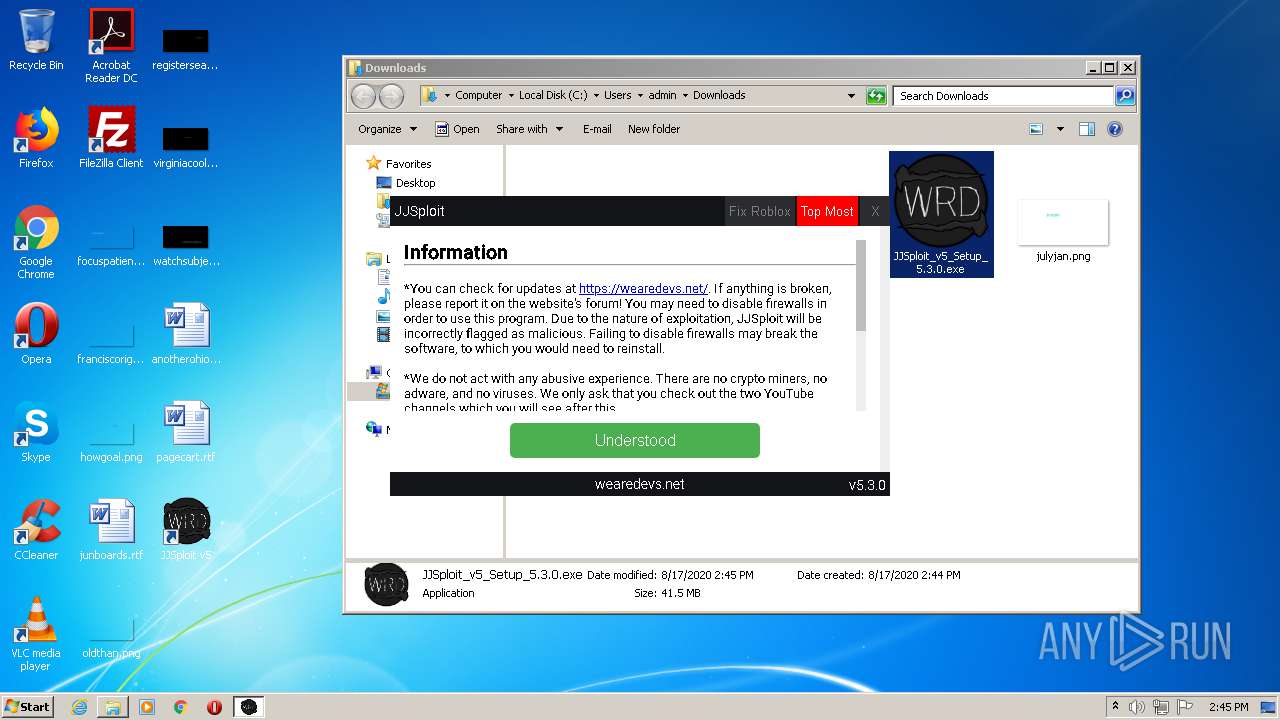
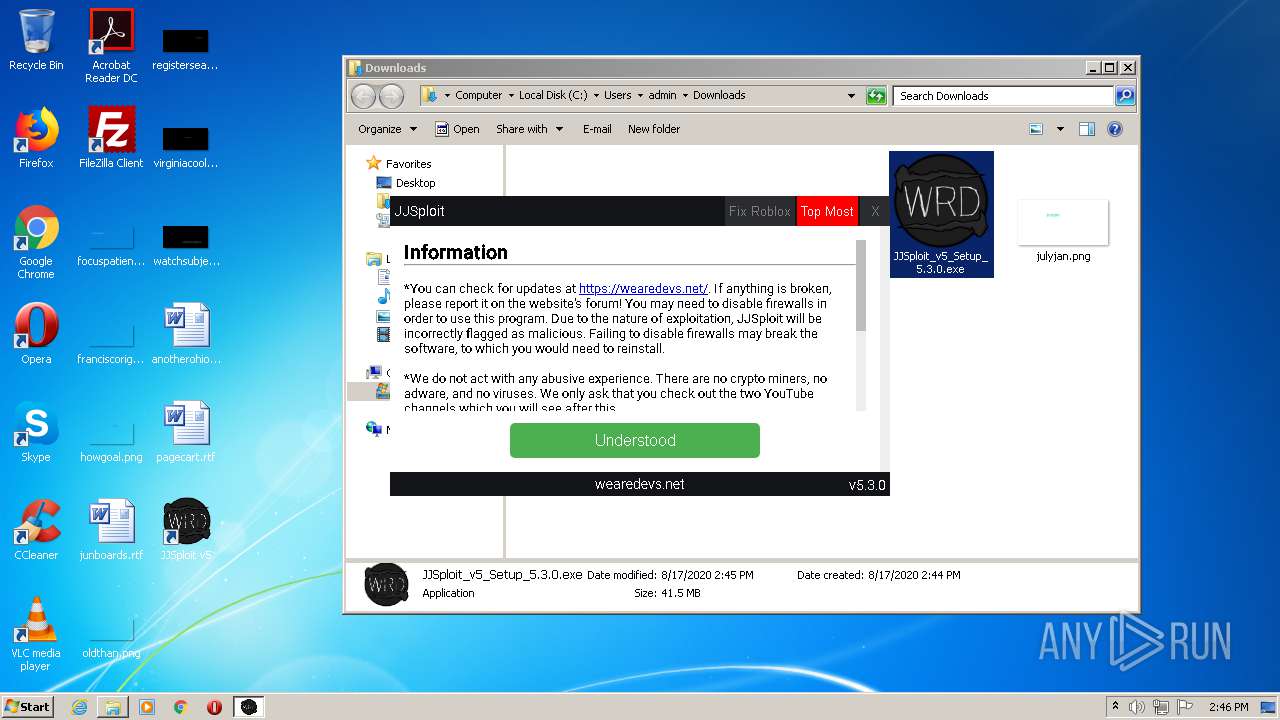
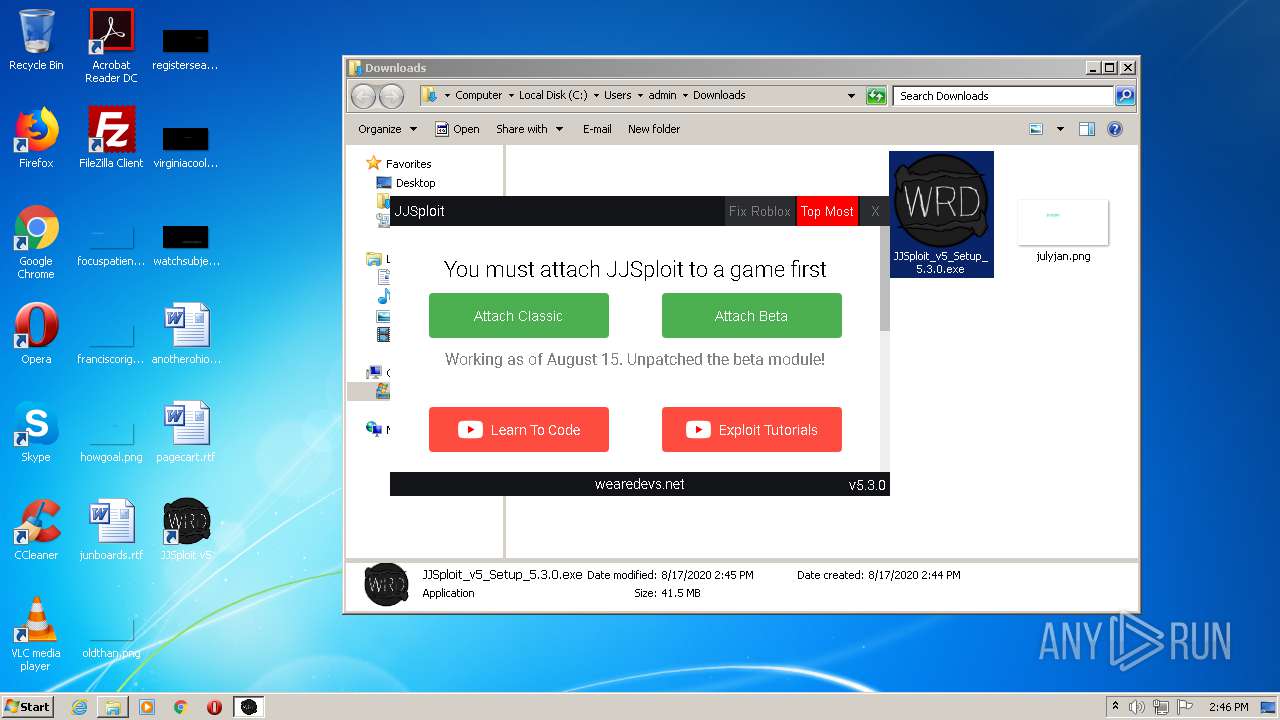
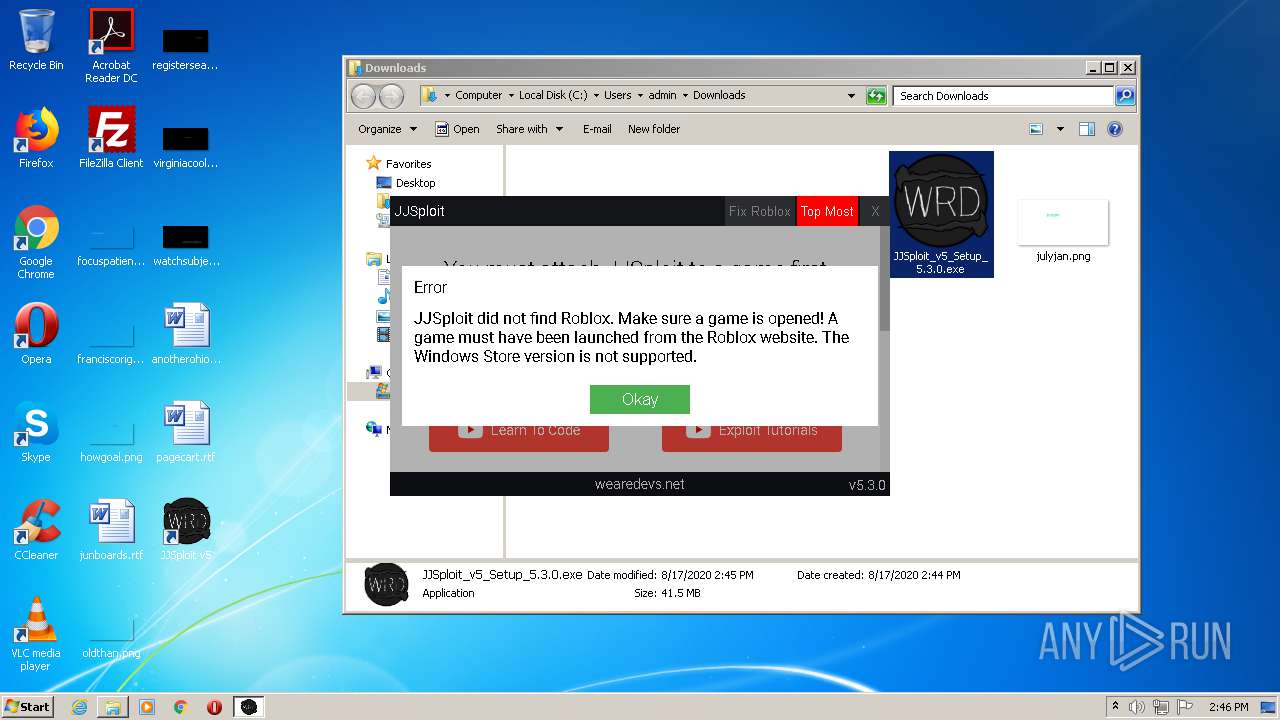
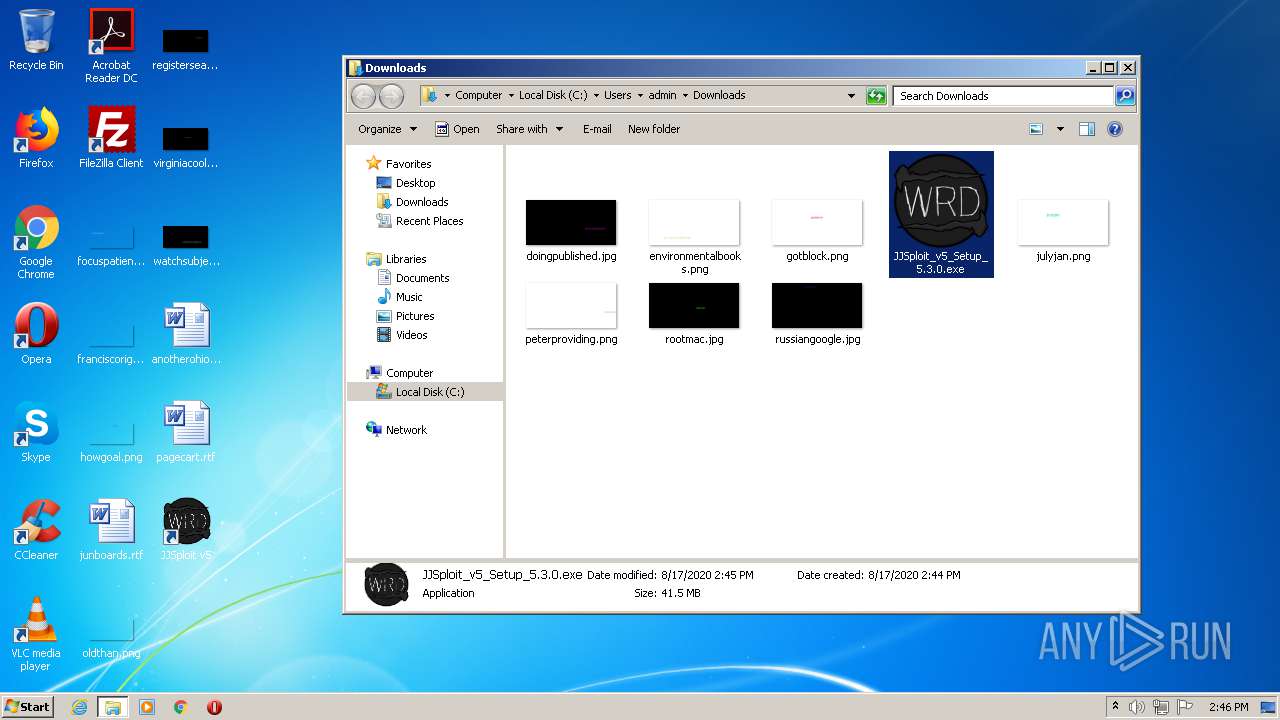
| download: | JJSploit |
| Full analysis: | https://app.any.run/tasks/1b452ece-4746-4438-91de-1eafc8337b03 |
| Verdict: | Malicious activity |
| Analysis date: | August 17, 2020, 13:43:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text |
| MD5: | 6EC2F8CE059DD1B01B8E8A58F5F9316E |
| SHA1: | 68484D8F62292F4A856DFF5AD144718F411A08EF |
| SHA256: | F592D1FFD983E450FC9CACC7F372B9C0D680BFC988BBB73FA026E258E0F2BE20 |
| SSDEEP: | 384:4UWWlUkMmAxUeUmSEiRiT1UOUTVxWdJWDWimWiMStSimSiYSiksVGjfXMZEZjJpP:4lWlU7mgflS5YT1/8xWdJinmnMO7m7YY |
MALICIOUS
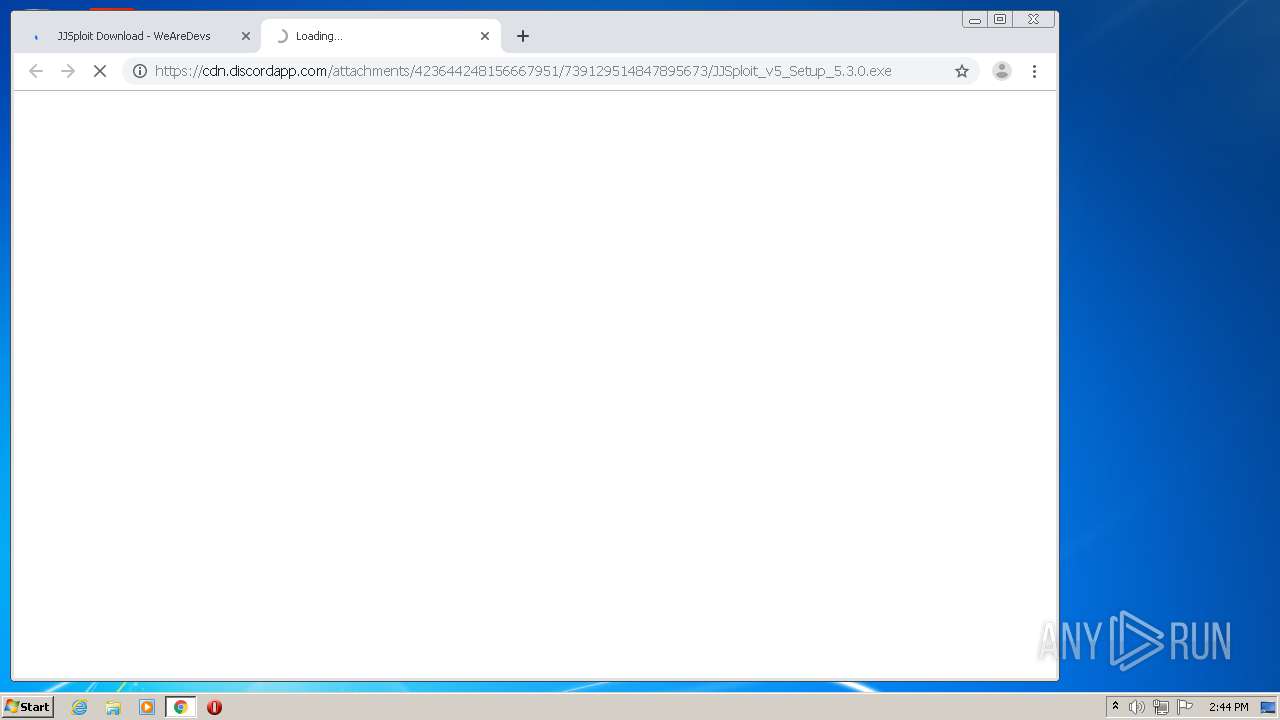
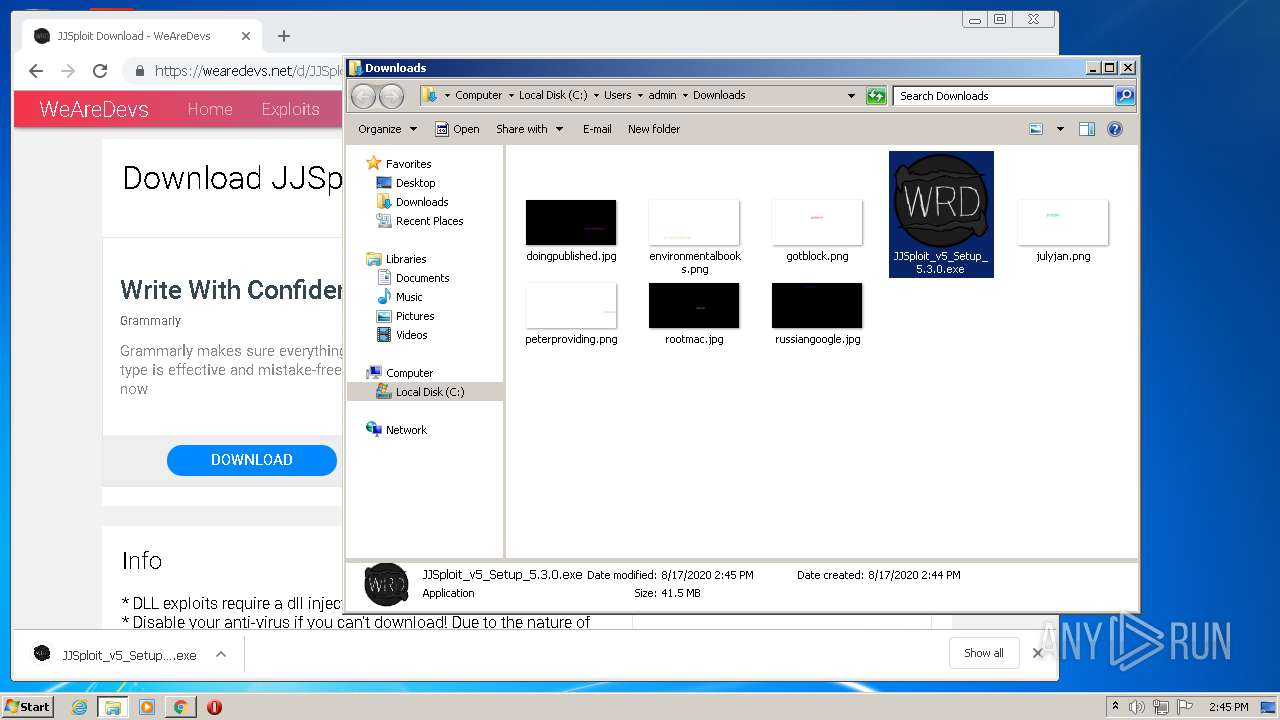
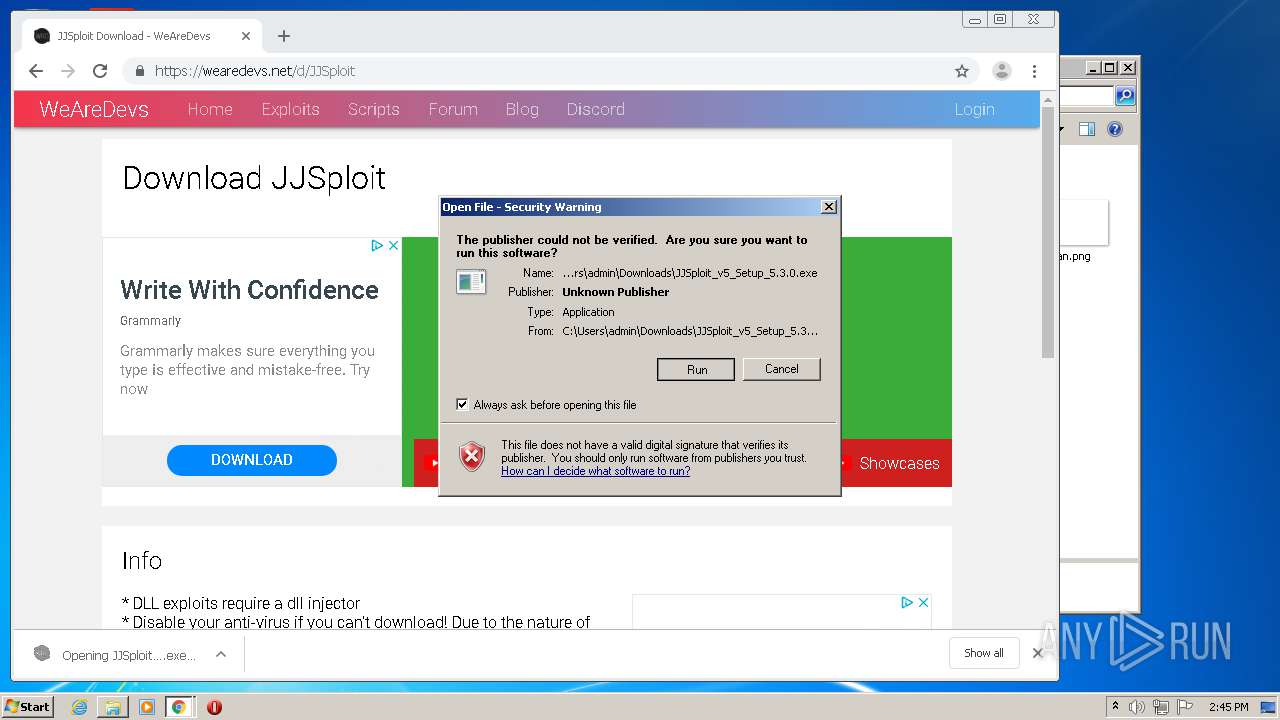
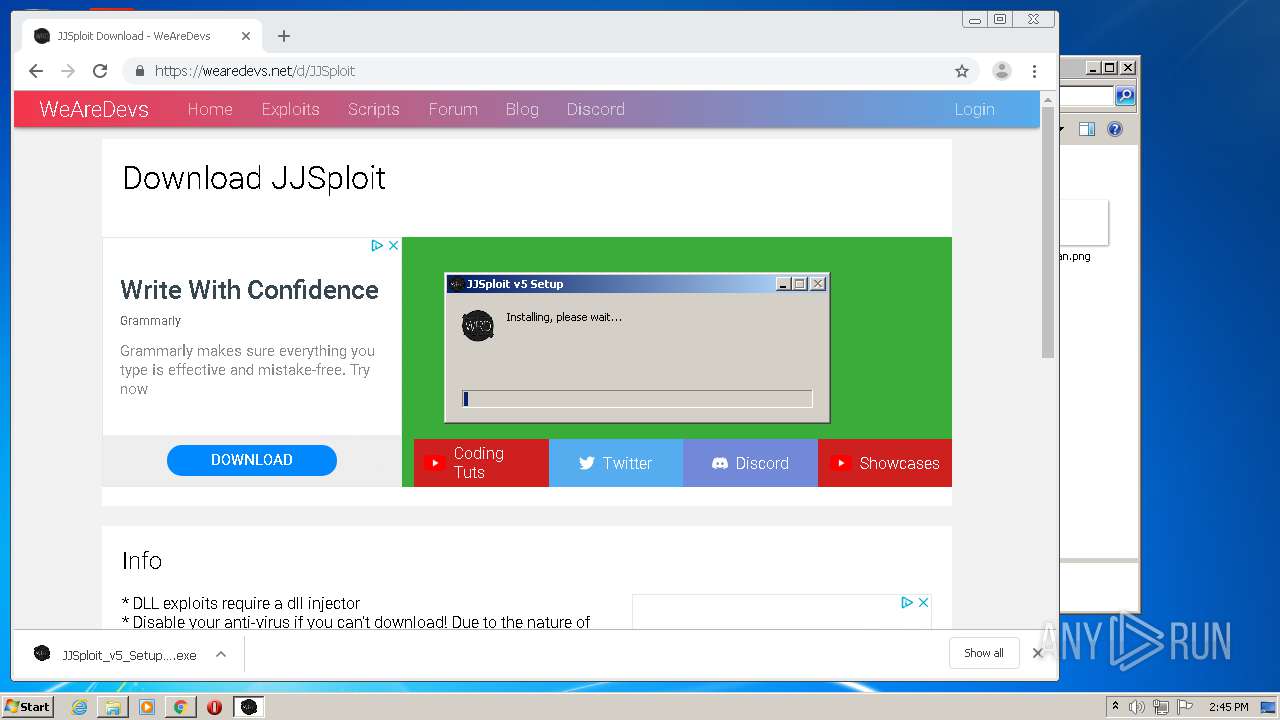
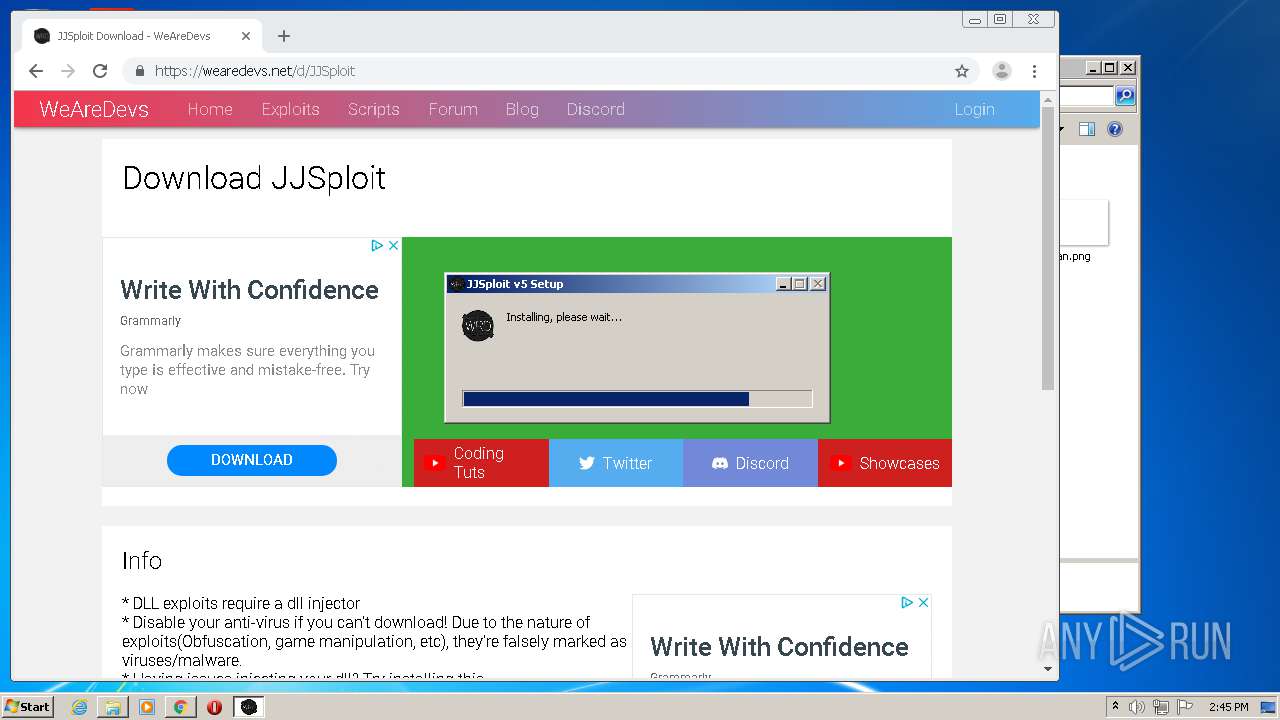
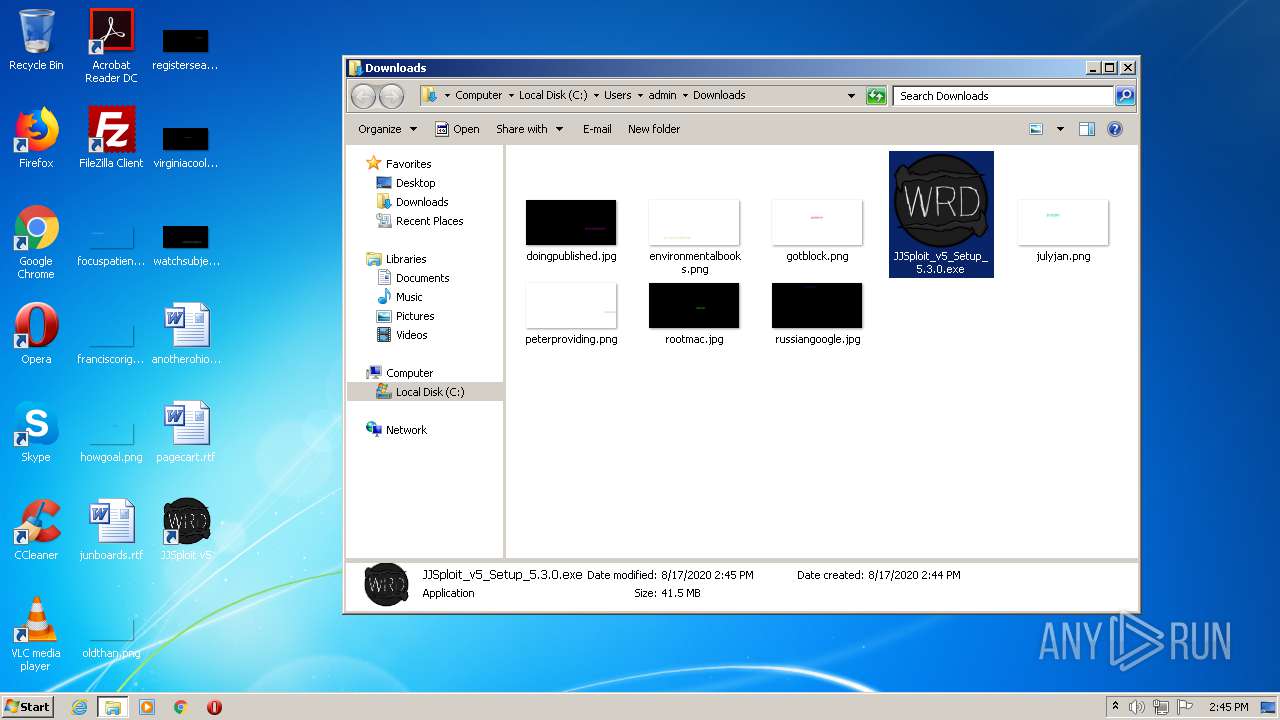
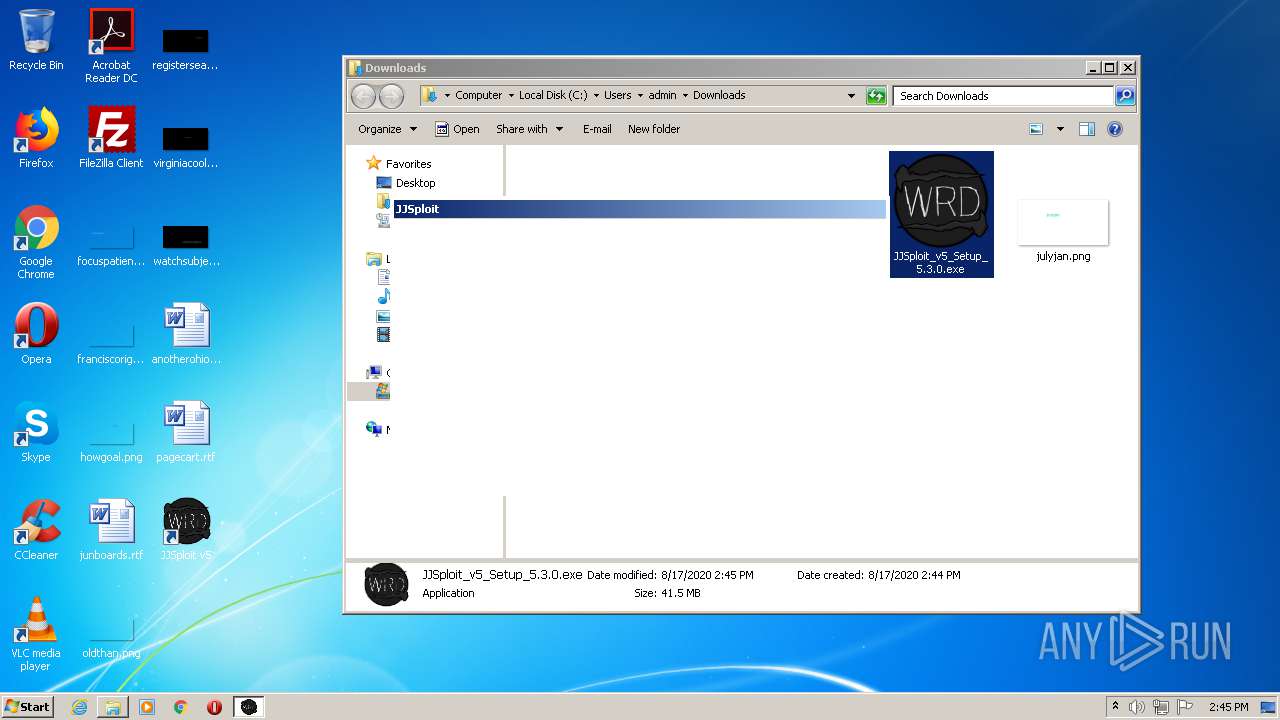
Application was dropped or rewritten from another process
- JJSploit_v5_Setup_5.3.0.exe (PID: 2960)
Loads dropped or rewritten executable
- JJSploit_v5_Setup_5.3.0.exe (PID: 2960)
- JJSploit v5.exe (PID: 2260)
- JJSploit v5.exe (PID: 2764)
- JJSploit v5.exe (PID: 3784)
SUSPICIOUS
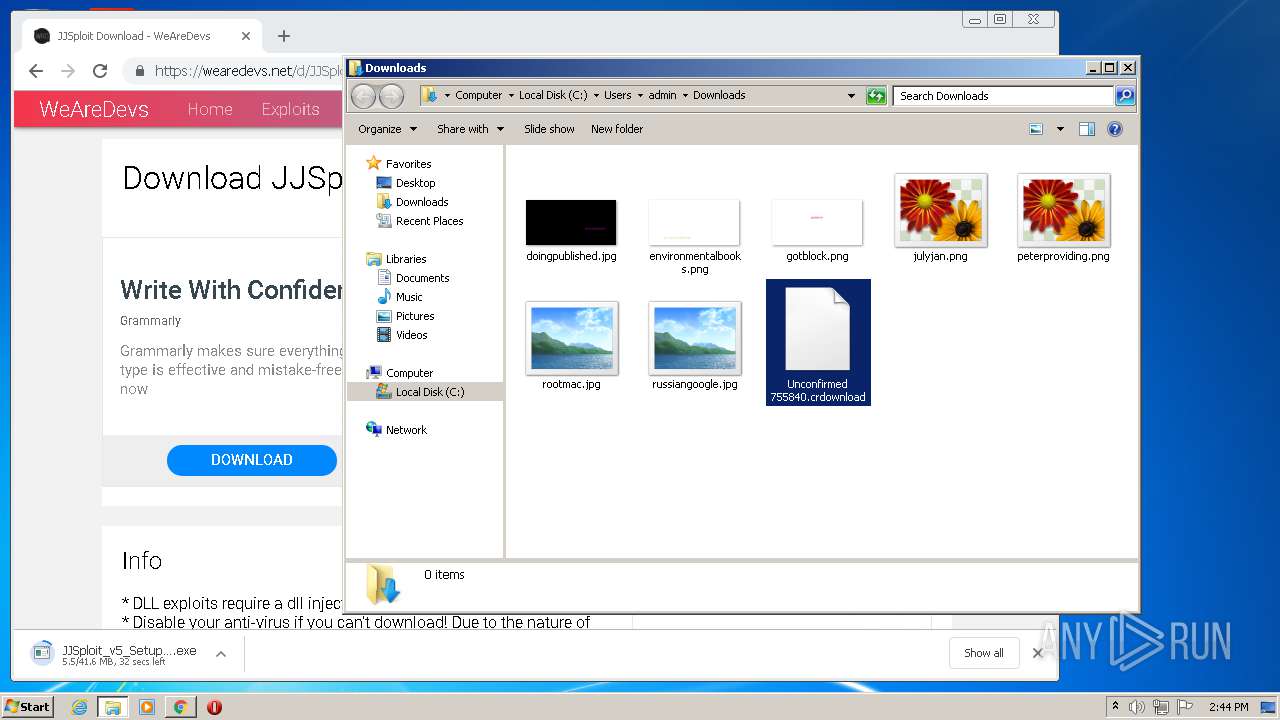
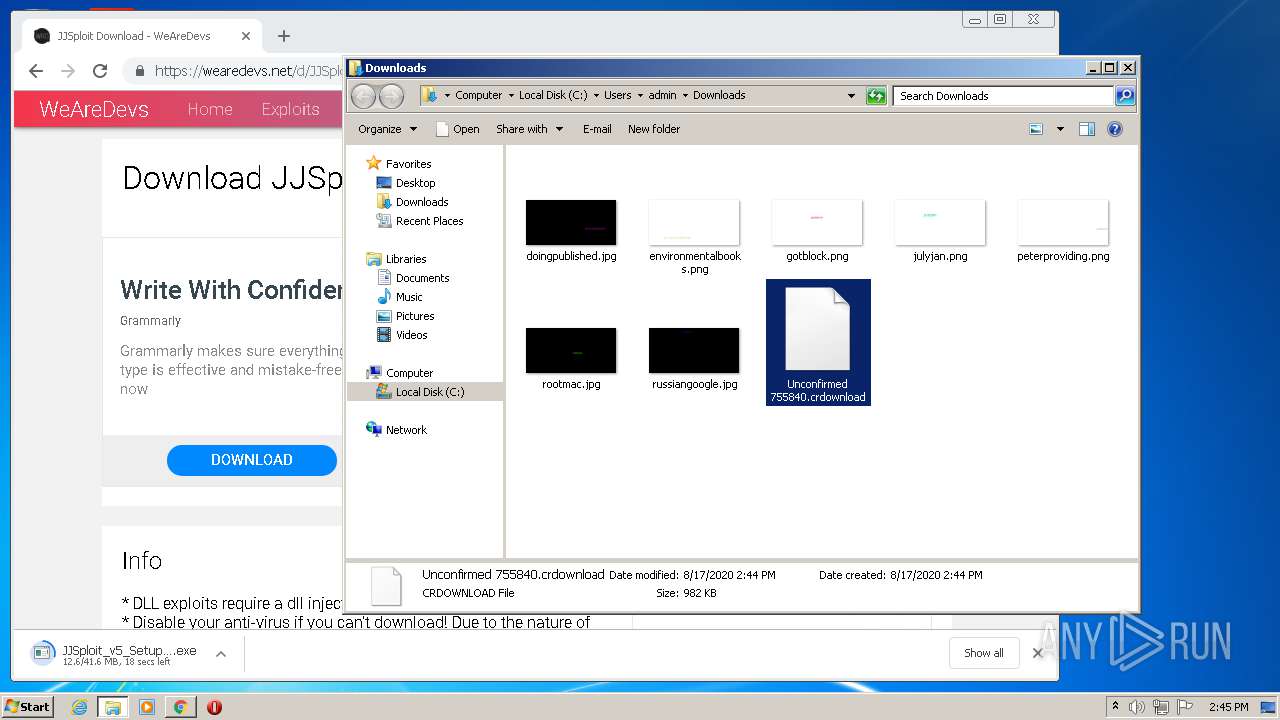
Executable content was dropped or overwritten
- chrome.exe (PID: 3028)
- JJSploit_v5_Setup_5.3.0.exe (PID: 2960)
- JJSploit v5.exe (PID: 2260)
Creates a software uninstall entry
- JJSploit_v5_Setup_5.3.0.exe (PID: 2960)
Creates files in the user directory
- JJSploit_v5_Setup_5.3.0.exe (PID: 2960)
- JJSploit v5.exe (PID: 2260)
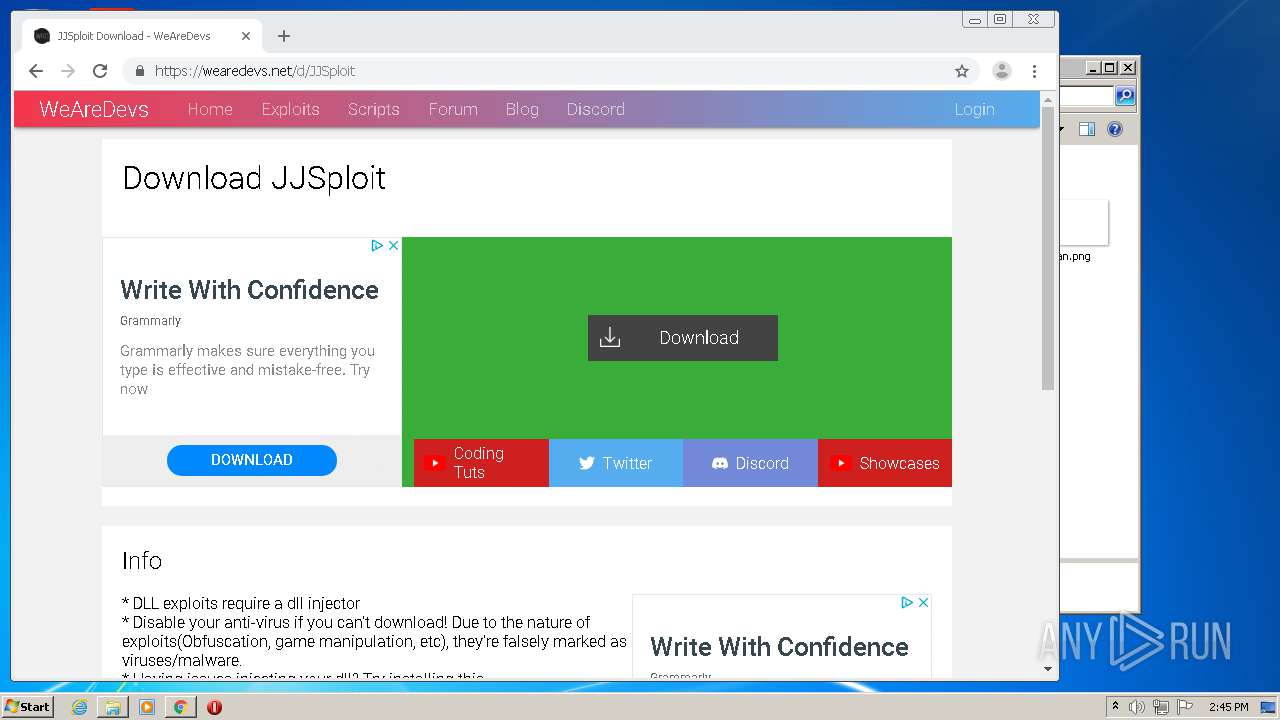
Application launched itself
- JJSploit v5.exe (PID: 2260)
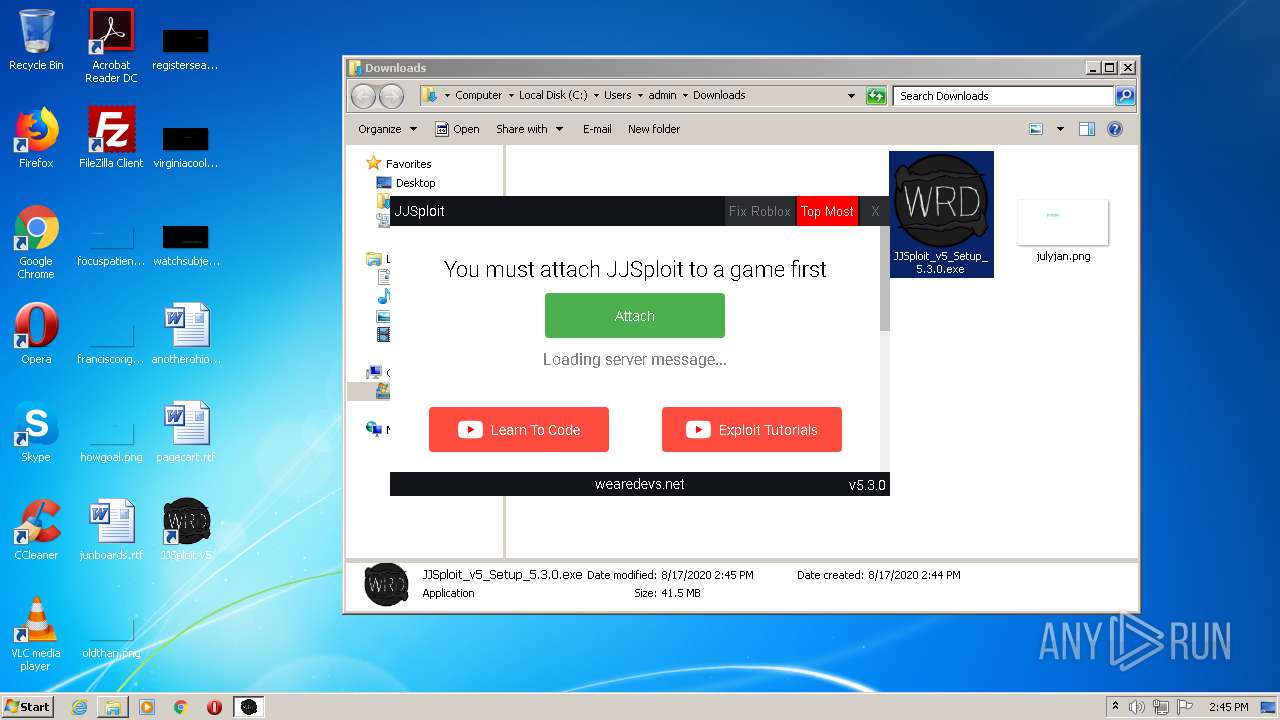
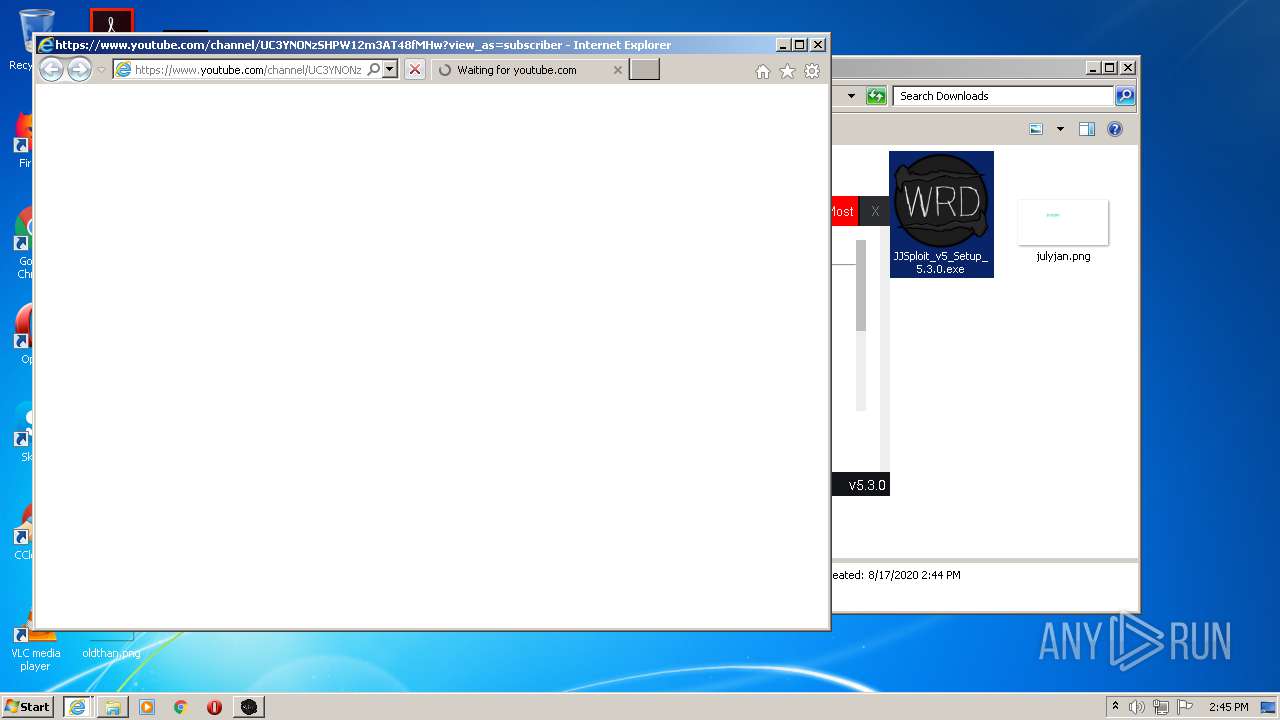
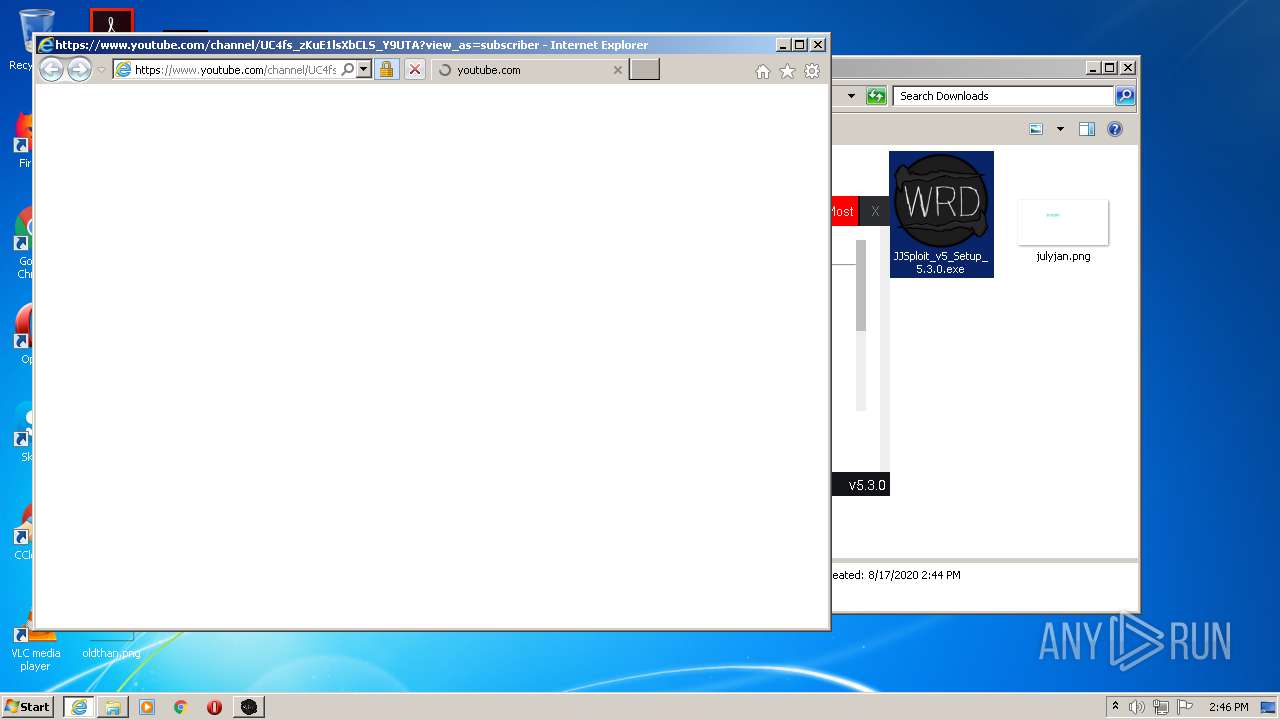
Starts Internet Explorer
- JJSploit v5.exe (PID: 2260)
INFO
Creates files in the user directory
- Opera.exe (PID: 628)
- iexplore.exe (PID: 2292)
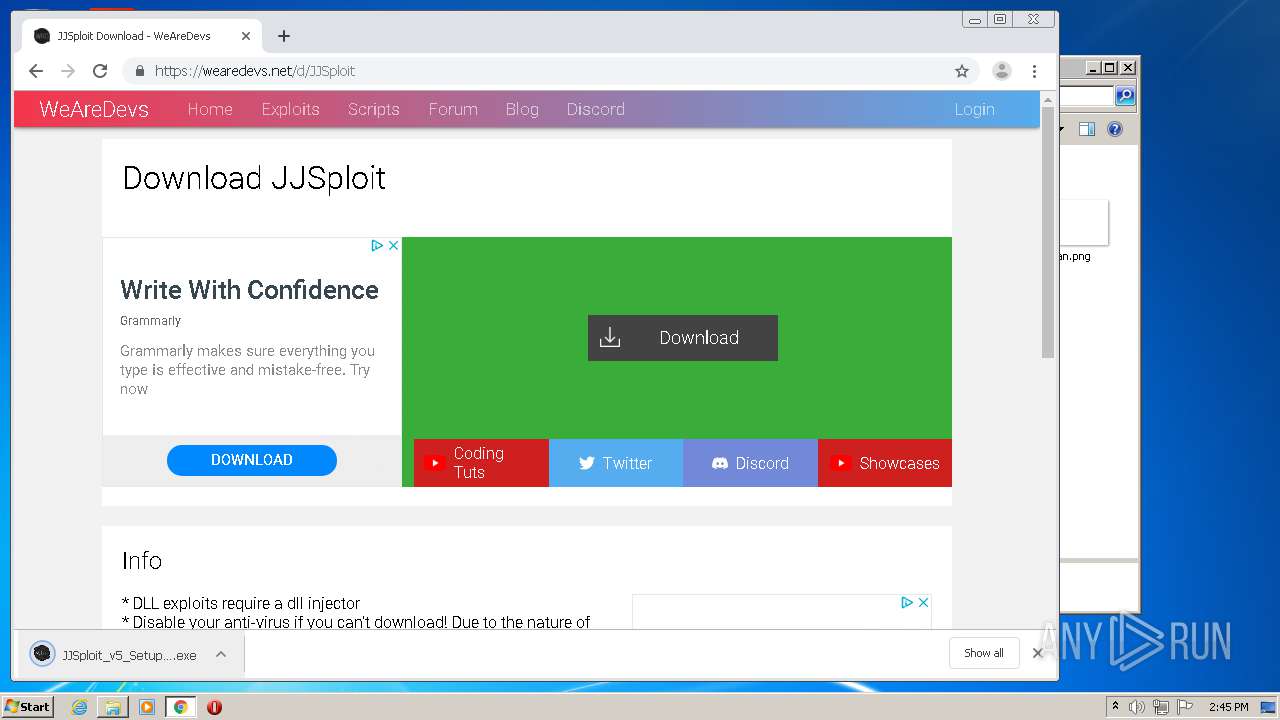
Manual execution by user
- chrome.exe (PID: 3028)
- JJSploit v5.exe (PID: 2260)
Reads settings of System Certificates
- chrome.exe (PID: 3796)
- iexplore.exe (PID: 2292)
- iexplore.exe (PID: 2100)
Application launched itself
- chrome.exe (PID: 3028)
- iexplore.exe (PID: 280)
- iexplore.exe (PID: 3020)
Reads the hosts file
- chrome.exe (PID: 3028)
- chrome.exe (PID: 3796)
- JJSploit v5.exe (PID: 2260)
Reads Internet Cache Settings
- chrome.exe (PID: 3028)
- iexplore.exe (PID: 3020)
- iexplore.exe (PID: 2100)
- iexplore.exe (PID: 2292)
- iexplore.exe (PID: 280)
Changes internet zones settings
- iexplore.exe (PID: 280)
- iexplore.exe (PID: 3020)
Reads internet explorer settings
- iexplore.exe (PID: 2292)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
EXIF
HTML
| viewport: | width=device-width, initial-scale=1, shrink-to-fit=no, maximum-scale=1, user-scalable=0 |
|---|---|
| Keywords: | JJSploit, Exploits, dll, hacks, cheats, developers, social, media |
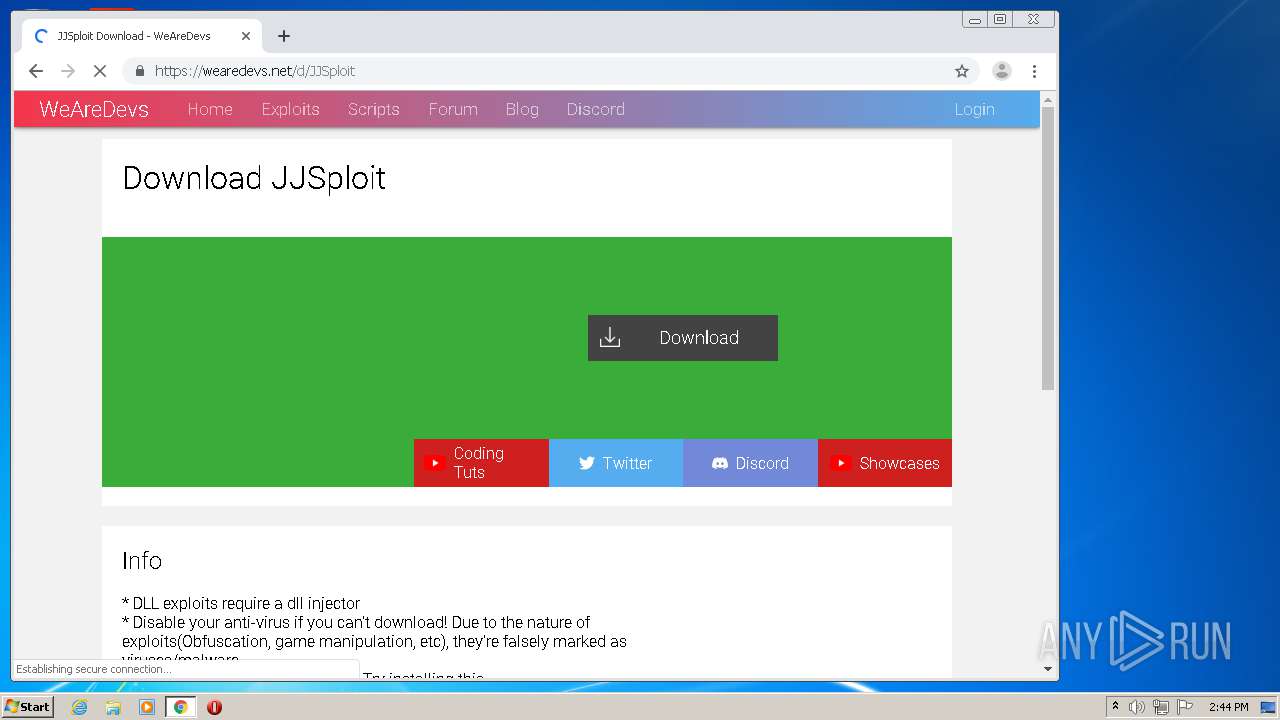
| Description: | JJSploit download - Offers a near full Lua executor, click teleport, ESP, speed, fly, infinite jump, and so much more. A powerful all in one package. |
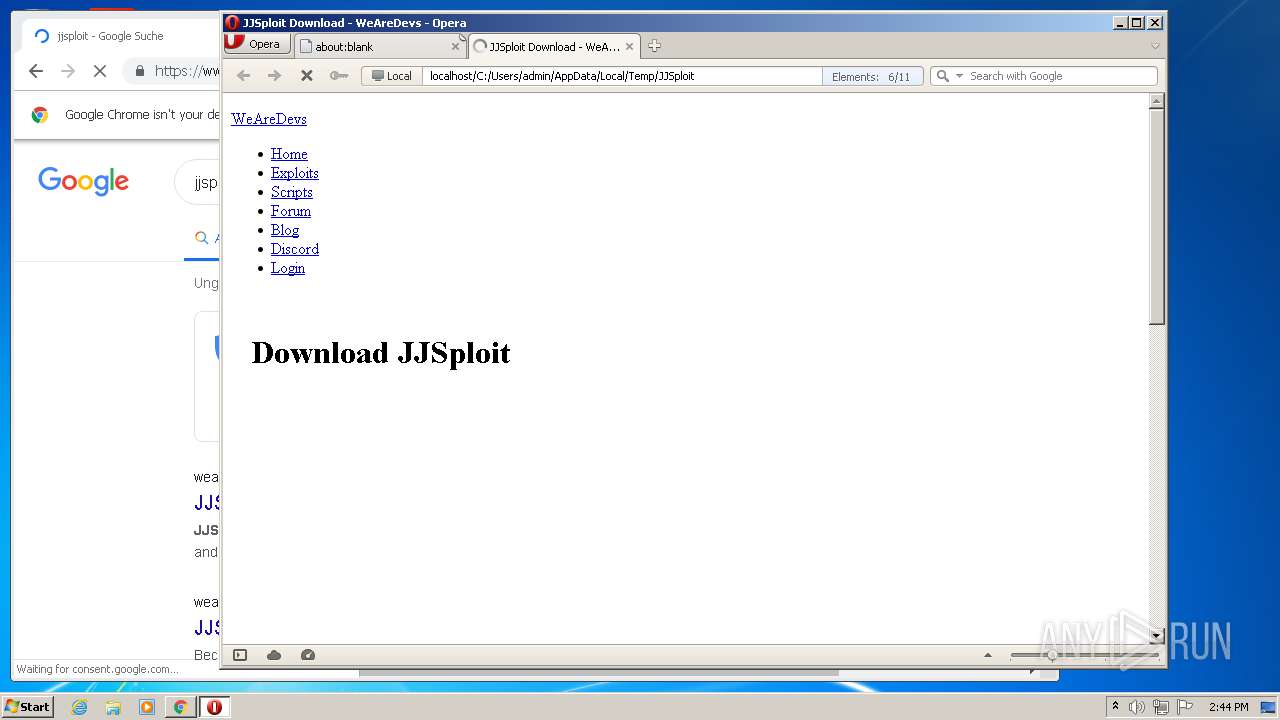
| Title: | JJSploit Download - WeAreDevs |
Total processes
73
Monitored processes
31
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.youtube.com/channel/UC4fs_zKuE1lsXbCLS_Y9UTA?view_as=subscriber | C:\Program Files\Internet Explorer\iexplore.exe | JJSploit v5.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,14052522581384401990,11227537305731806867,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11272851506131621445 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3952 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
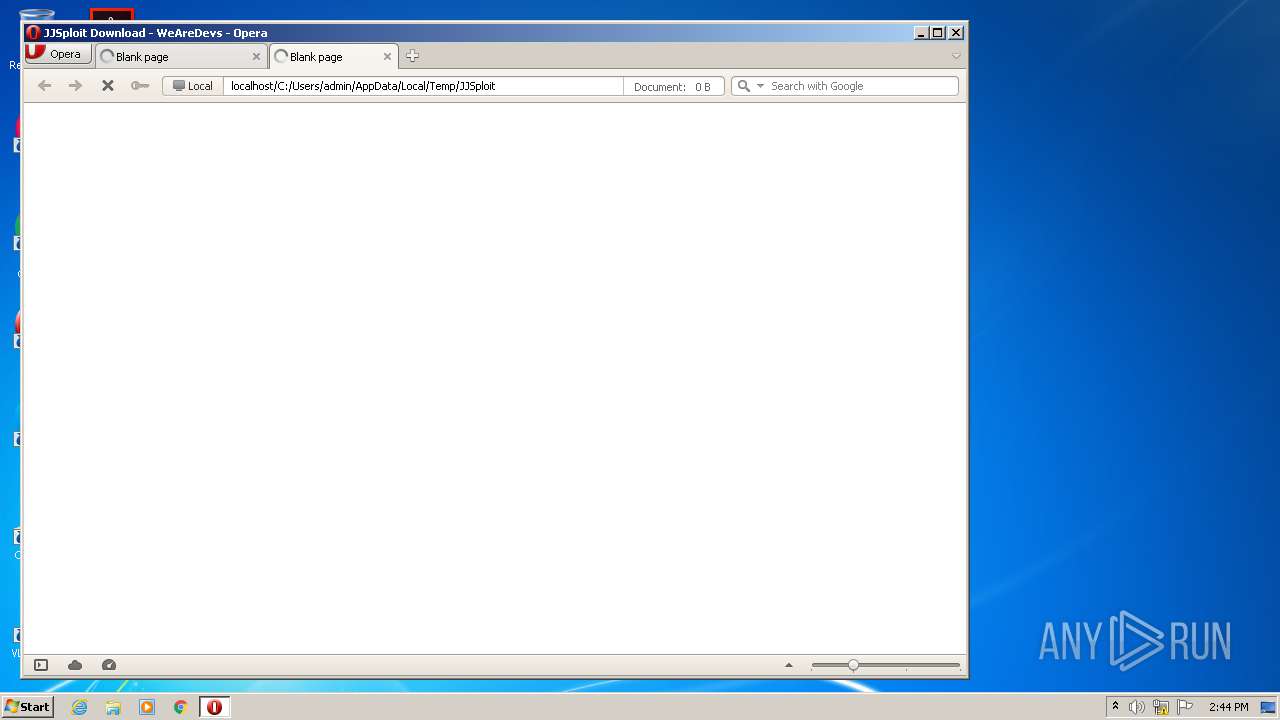
| 628 | "C:\Program Files\Opera\Opera.exe" "C:\Users\admin\AppData\Local\Temp\JJSploit" | C:\Program Files\Opera\Opera.exe | rundll32.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1056,14052522581384401990,11227537305731806867,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=9842680853272009444 --mojo-platform-channel-handle=3184 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,14052522581384401990,11227537305731806867,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11718534930475365064 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1264 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6defa9d0,0x6defa9e0,0x6defa9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1056,14052522581384401990,11227537305731806867,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13796755667905357008 --mojo-platform-channel-handle=3632 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2100 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3020 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
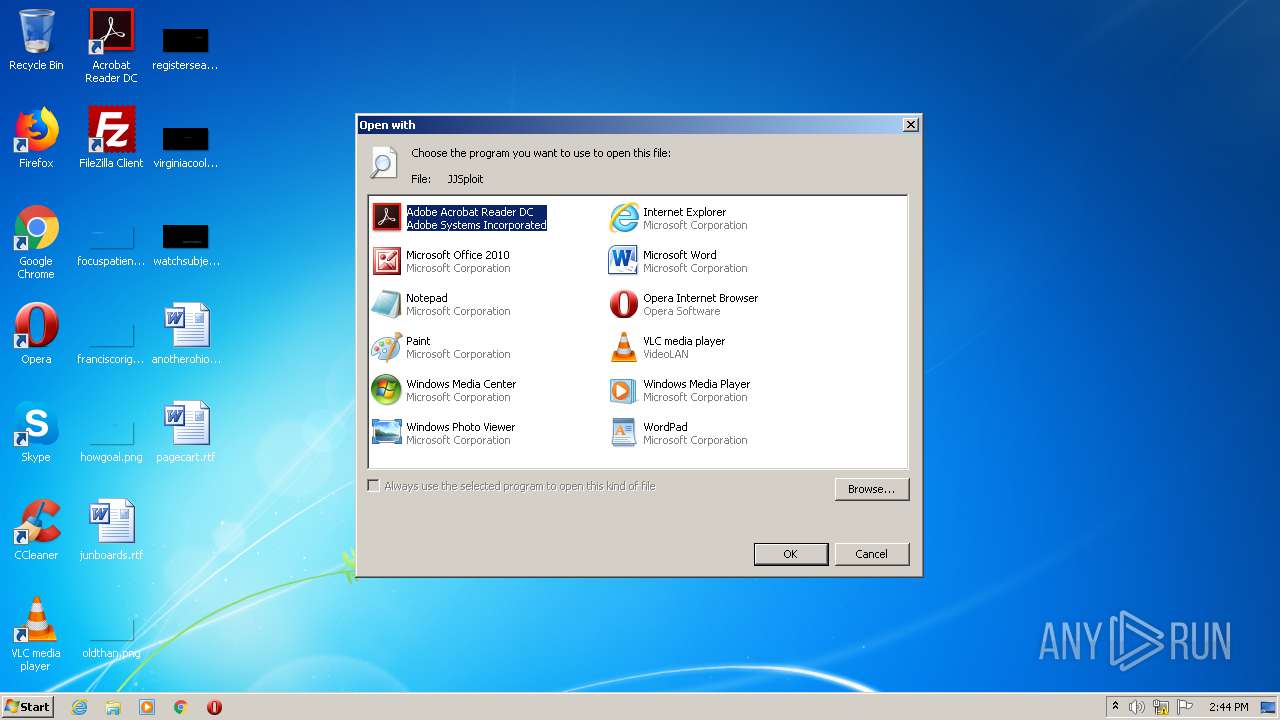
| 2108 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\JJSploit | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2260 | "C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe" | C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe | explorer.exe | ||||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: JJSploit v5 Exit code: 0 Version: 5.3.0 Modules
| |||||||||||||||
Total events
3 199
Read events
2 748
Write events
442
Delete events
9
Modification events
| (PID) Process: | (2108) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe |
Value: Adobe Acrobat Reader DC | |||
| (PID) Process: | (2108) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (2108) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\mspaint.exe |
Value: Paint | |||
| (PID) Process: | (2108) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (2108) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (2108) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Opera\Opera.exe |
Value: Opera Internet Browser | |||
| (PID) Process: | (2108) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Windows Photo Viewer\PhotoViewer.dll |
Value: Windows Photo Viewer | |||
| (PID) Process: | (2108) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\VideoLAN\VLC\vlc.exe |
Value: VLC media player | |||
| (PID) Process: | (2108) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE |
Value: Microsoft Word | |||
| (PID) Process: | (2108) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
22
Suspicious files
148
Text files
149
Unknown types
93
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 628 | Opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\opr895.tmp | — | |
MD5:— | SHA256:— | |||
| 628 | Opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr896.tmp | — | |
MD5:— | SHA256:— | |||
| 628 | Opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr8D5.tmp | — | |
MD5:— | SHA256:— | |||
| 3028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\dc13e944-af30-4096-8547-2da1b8f821c0.tmp | — | |
MD5:— | SHA256:— | |||
| 3028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 628 | Opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\tasks.xml | xml | |
MD5:— | SHA256:— | |||
| 3028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 628 | Opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\autosave.win | text | |
MD5:273F66BBFD419D2108F37D1F3DC9DB34 | SHA256:DB67C59C8D9F772B43EC0FD68680583B033DBAA449DAF673356A4CACDA55043C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
106
DNS requests
60
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2292 | iexplore.exe | GET | — | 172.217.18.3:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCEs0cc0pt0BwIAAAAAc8zc | US | — | — | whitelisted |
2292 | iexplore.exe | GET | — | 172.217.18.3:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCEs0cc0pt0BwIAAAAAc8zc | US | — | — | whitelisted |
2100 | iexplore.exe | GET | 200 | 172.217.18.3:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
628 | Opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 592 b | whitelisted |
628 | Opera.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTlMusCQK2hbCidwnVINVIaWKpcFQQUGKka%2FLJFScFvMDQIK9mHnLAlV3oCEA66W8Py6uVlNg8aUK8Oxs8%3D | US | der | 471 b | whitelisted |
2100 | iexplore.exe | GET | 200 | 172.217.18.3:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2100 | iexplore.exe | GET | 200 | 172.217.18.3:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEAKhmcGKkEWcAgAAAABzzGw%3D | US | der | 471 b | whitelisted |
2292 | iexplore.exe | GET | 200 | 172.217.21.227:80 | http://crl.pki.goog/GTS1O1core.crl | US | der | 1.07 Kb | whitelisted |
2100 | iexplore.exe | GET | 200 | 172.217.18.3:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEAKhmcGKkEWcAgAAAABzzGw%3D | US | der | 471 b | whitelisted |
2292 | iexplore.exe | GET | 200 | 172.217.18.3:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEFsunJE0oJHuAgAAAABzyq0%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 172.217.16.162:445 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
4 | System | 172.217.16.162:139 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
628 | Opera.exe | 185.26.182.94:443 | certs.opera.com | Opera Software AS | — | whitelisted |
628 | Opera.exe | 104.26.6.147:443 | cdn.wearedevs.net | Cloudflare Inc | US | suspicious |
628 | Opera.exe | 104.26.7.147:443 | cdn.wearedevs.net | Cloudflare Inc | US | suspicious |
628 | Opera.exe | 104.17.78.107:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | unknown |
628 | Opera.exe | 104.17.79.107:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
628 | Opera.exe | 185.26.182.93:443 | certs.opera.com | Opera Software AS | — | whitelisted |
628 | Opera.exe | 93.184.220.29:80 | crl4.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3796 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
certs.opera.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
cdn.wearedevs.net |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
crl3.digicert.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |