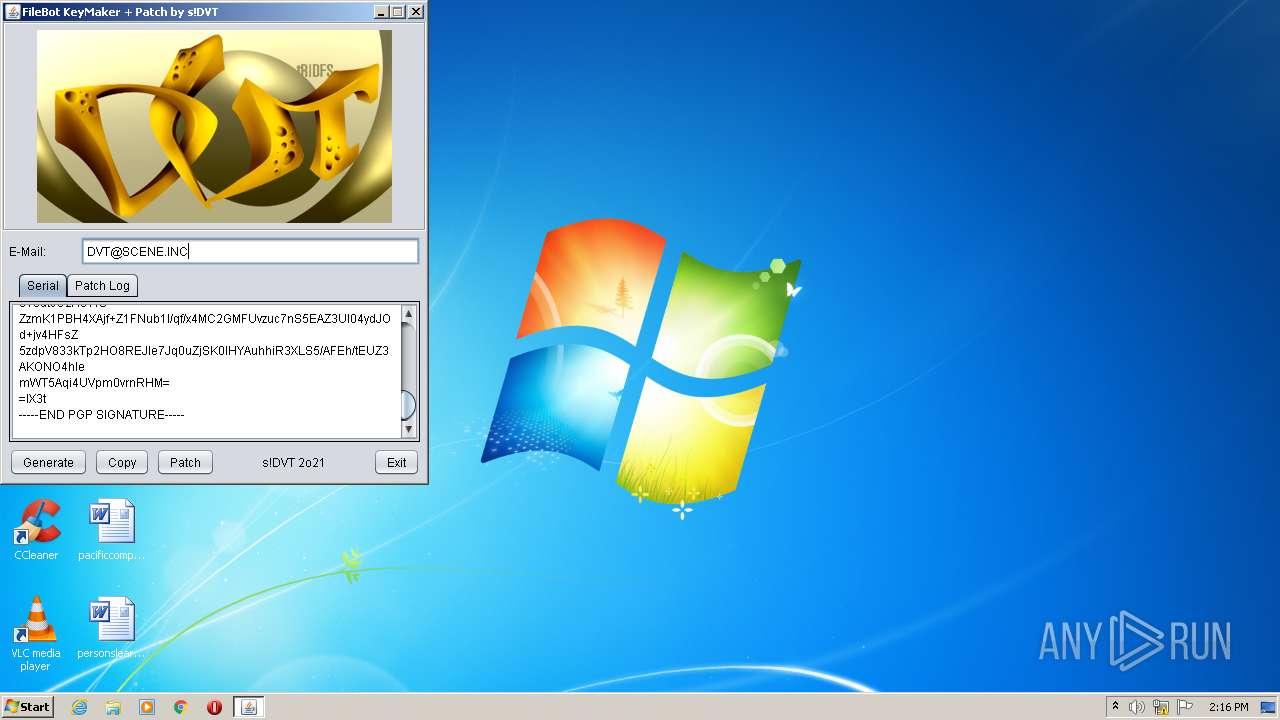
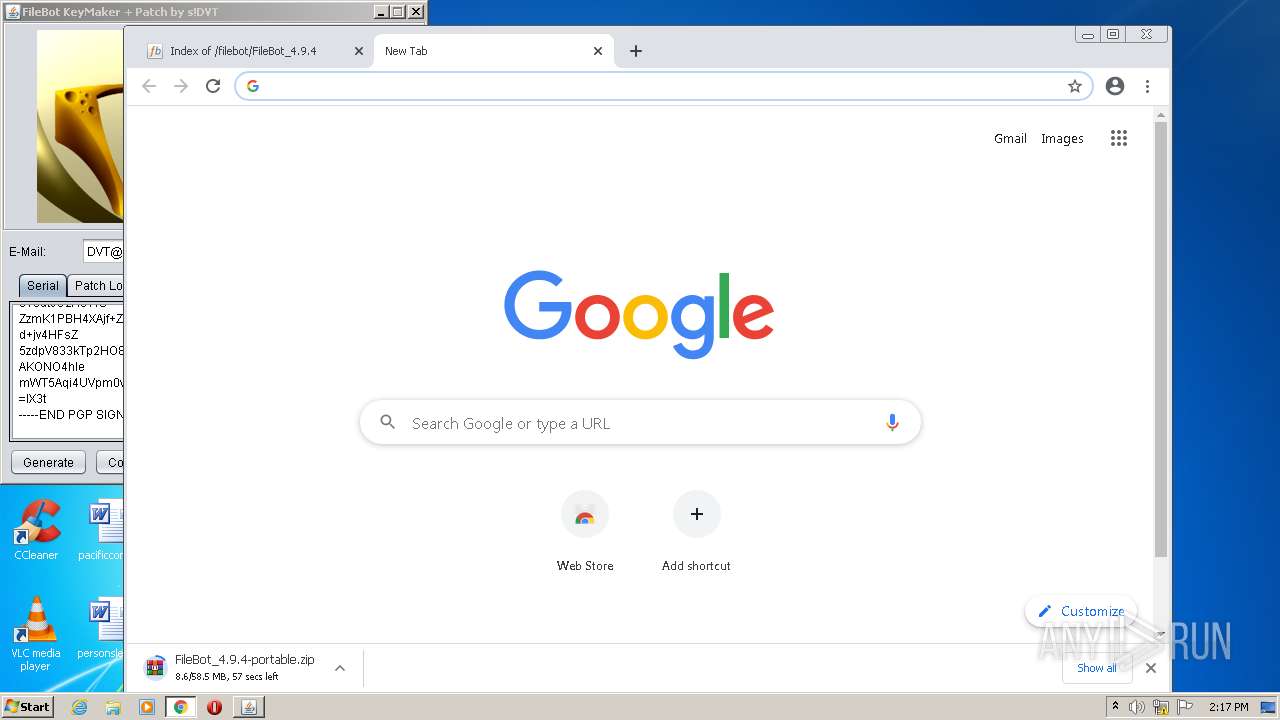
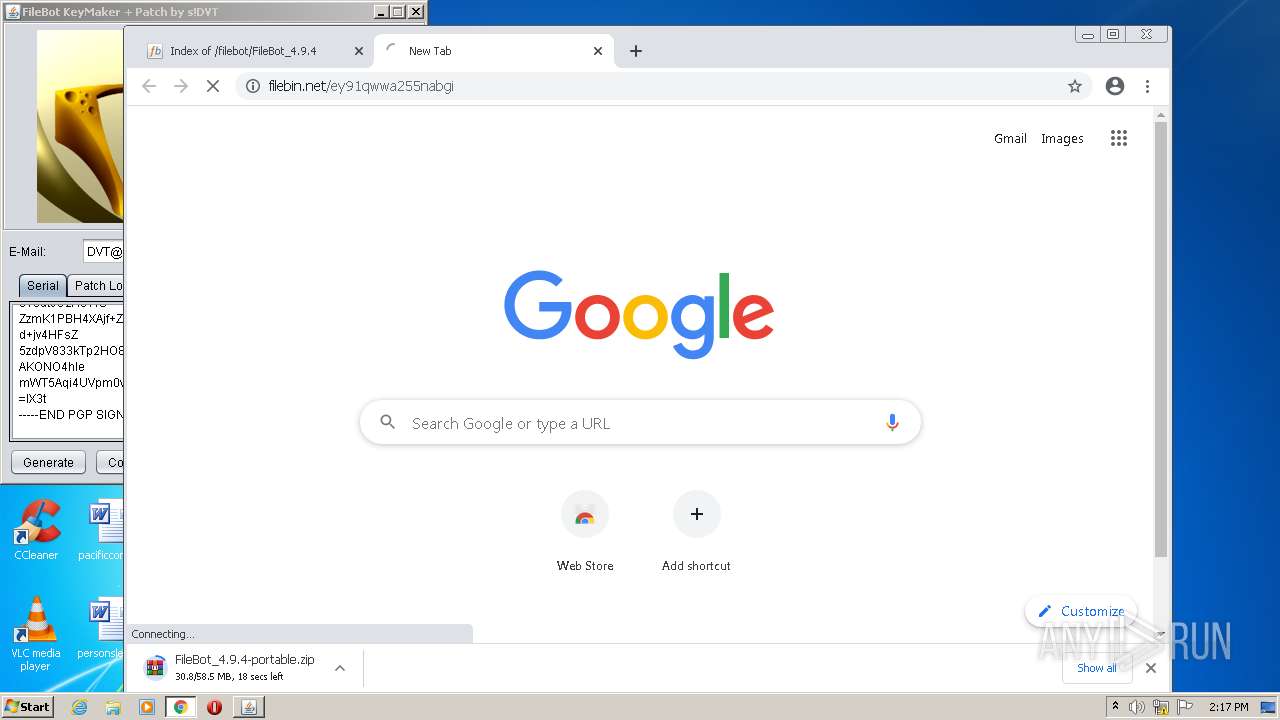
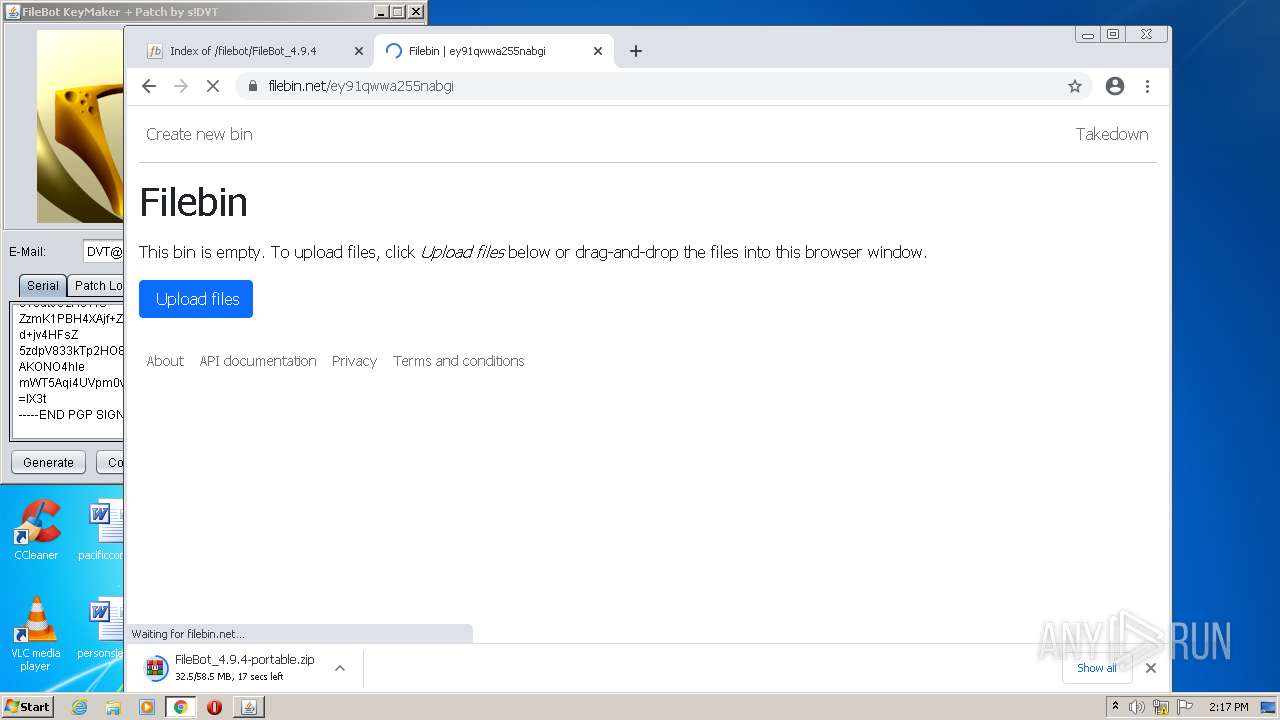
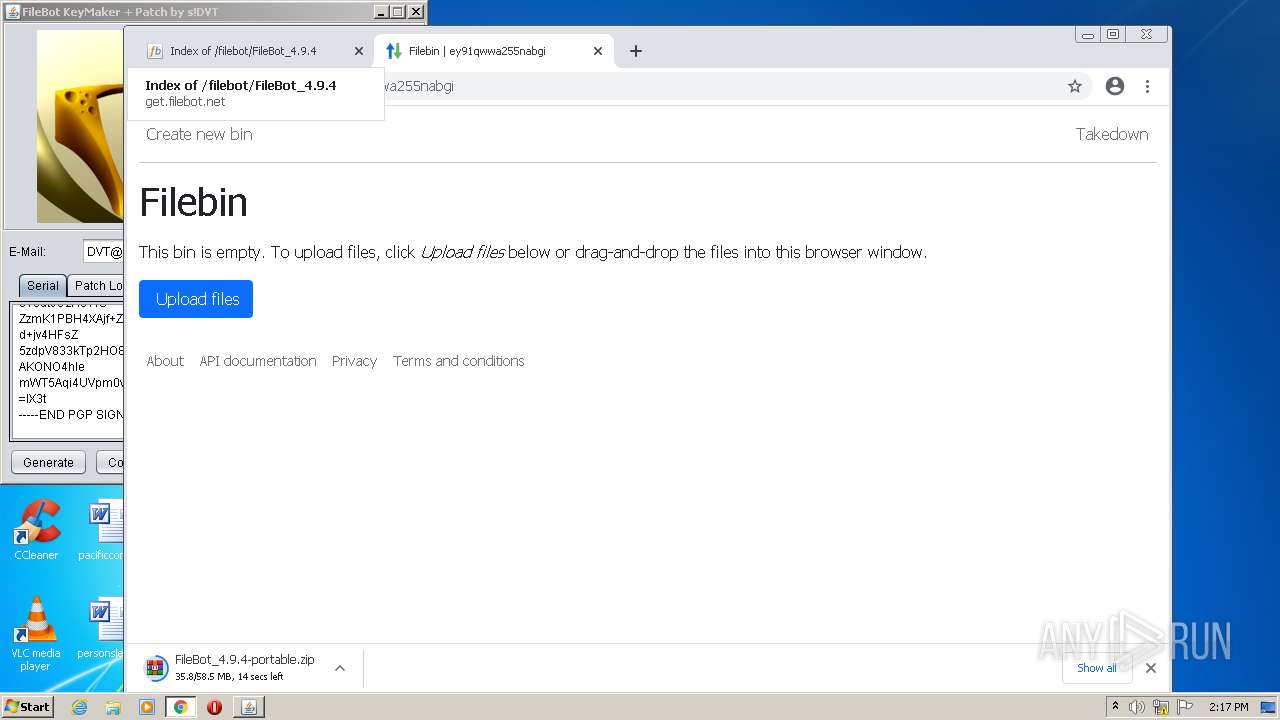
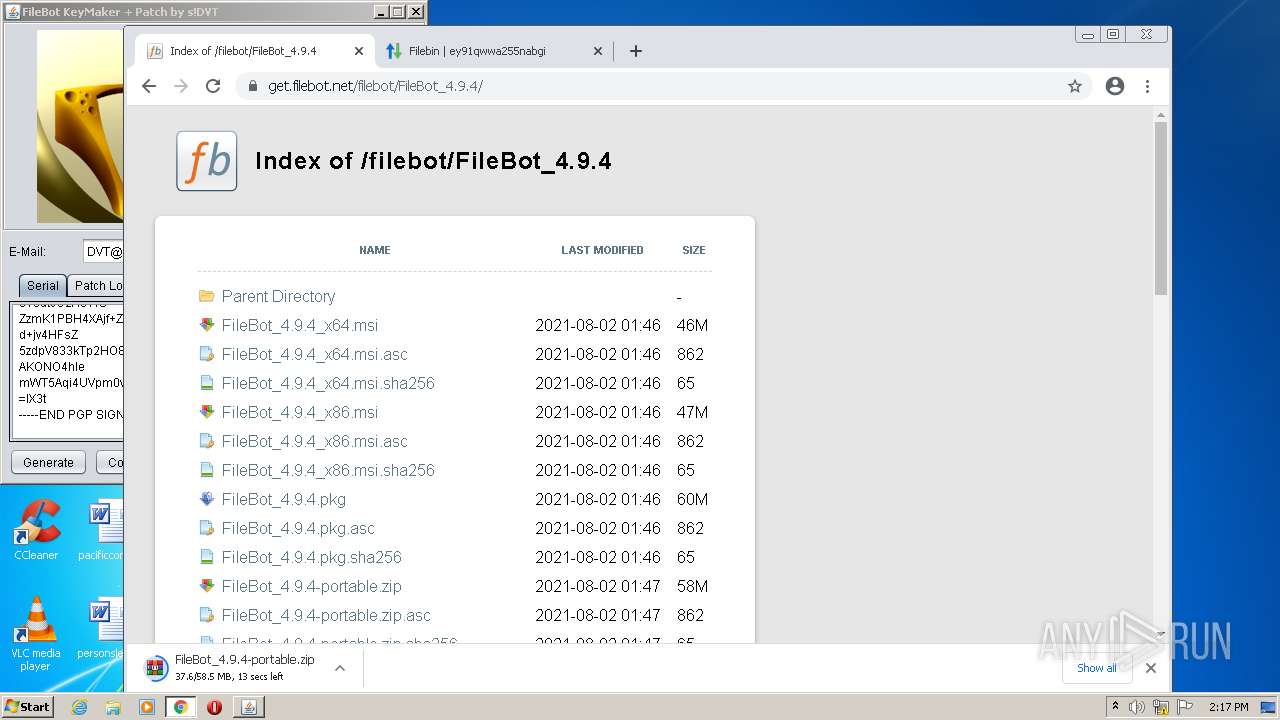
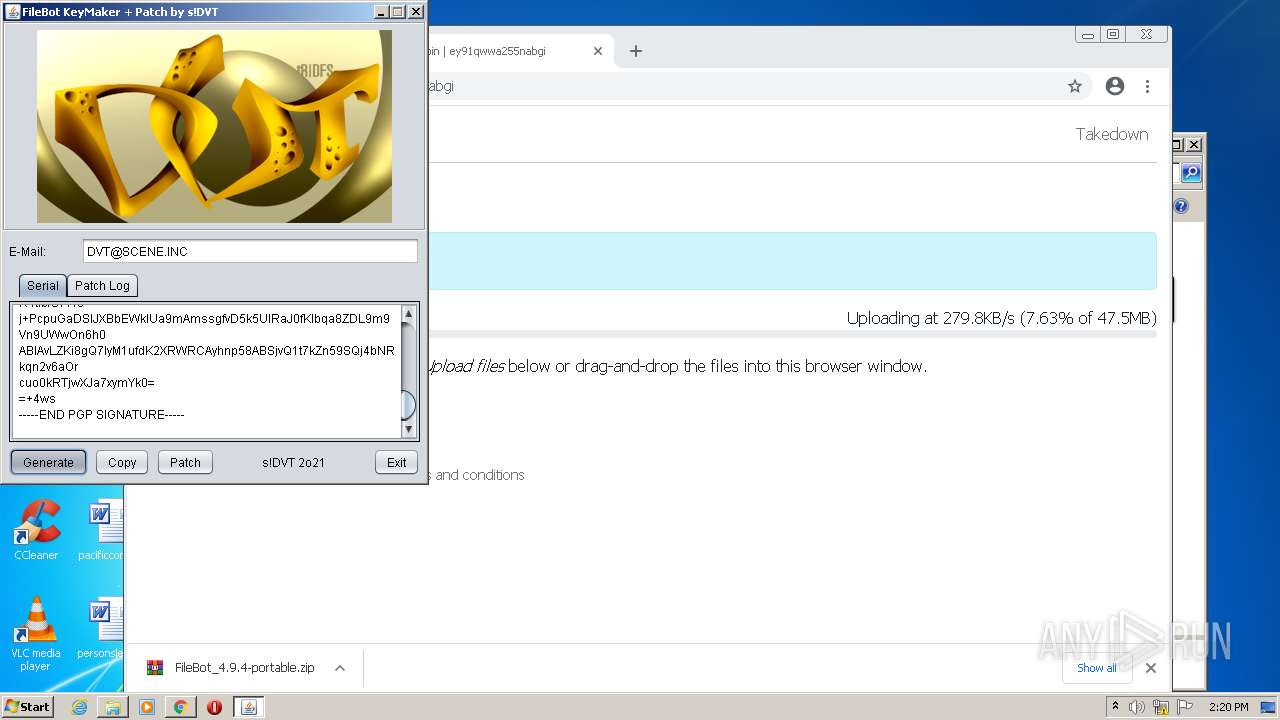
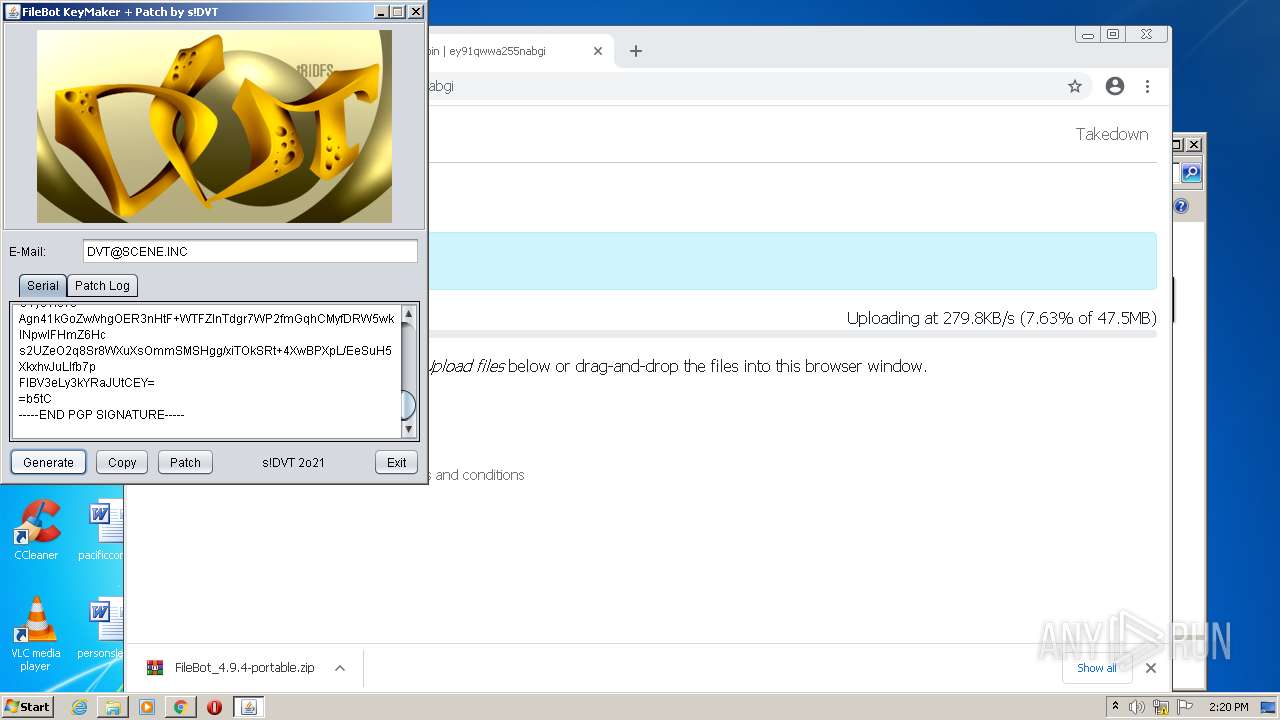
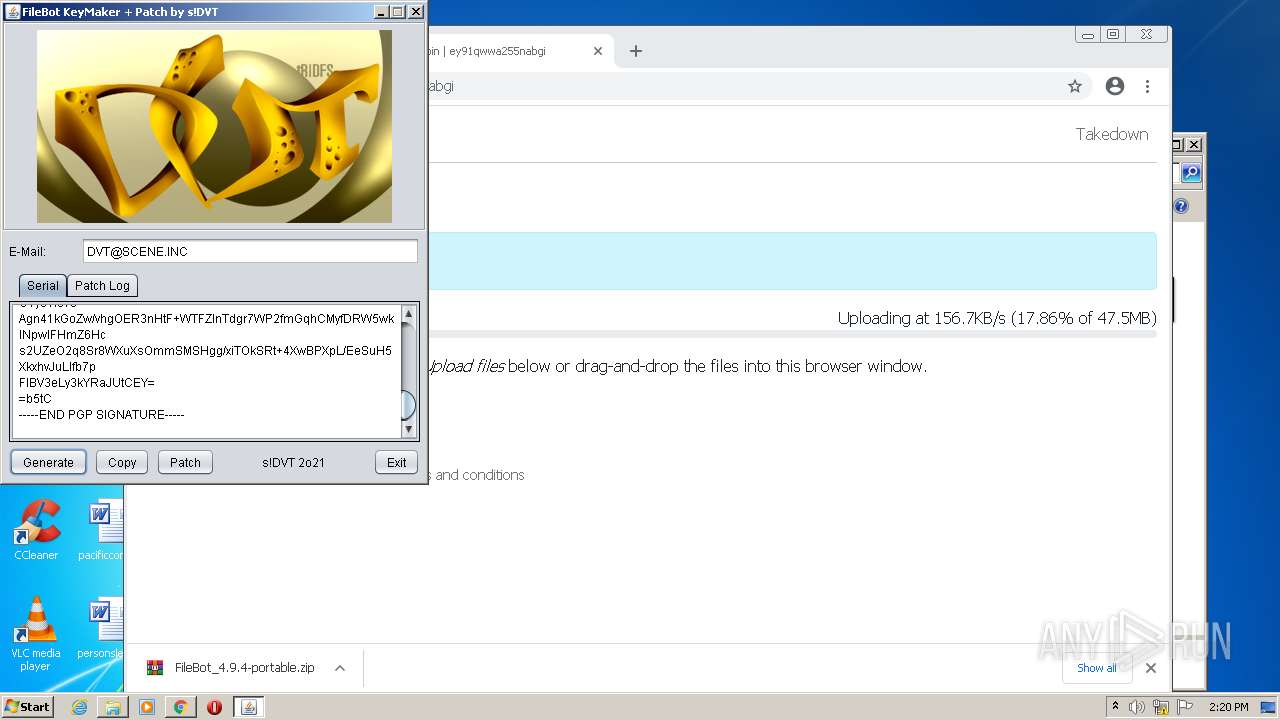
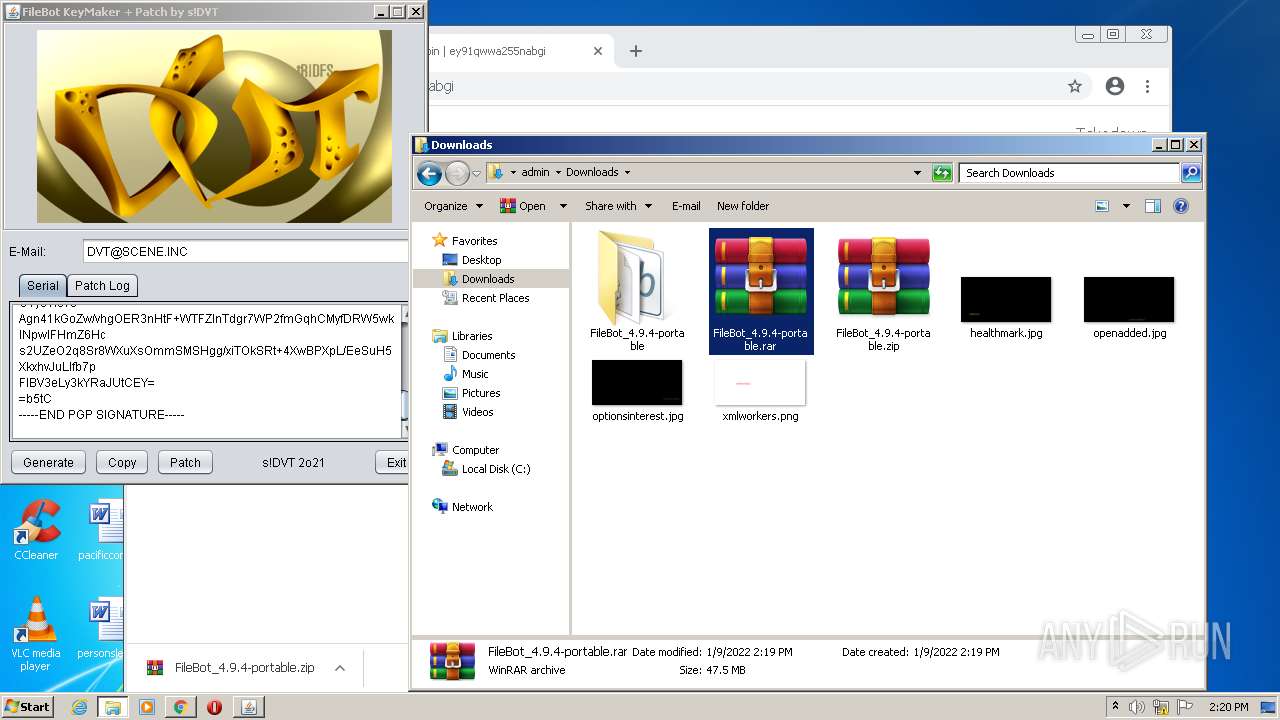
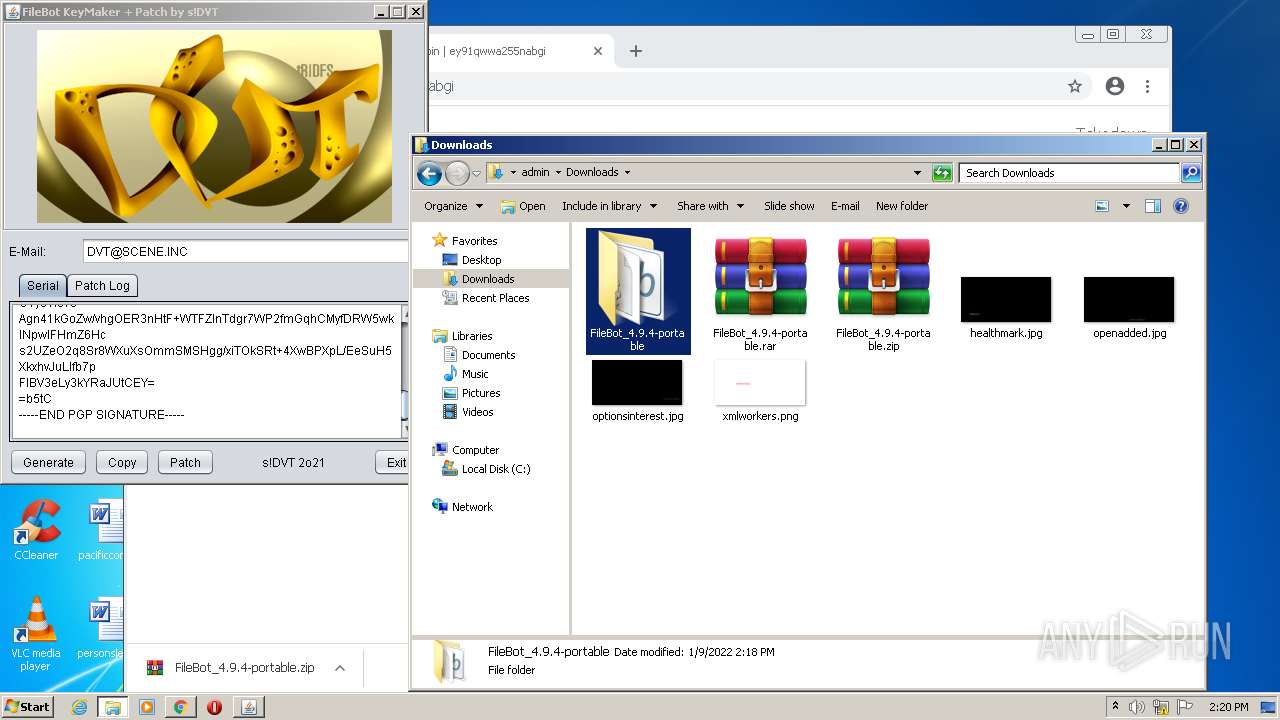
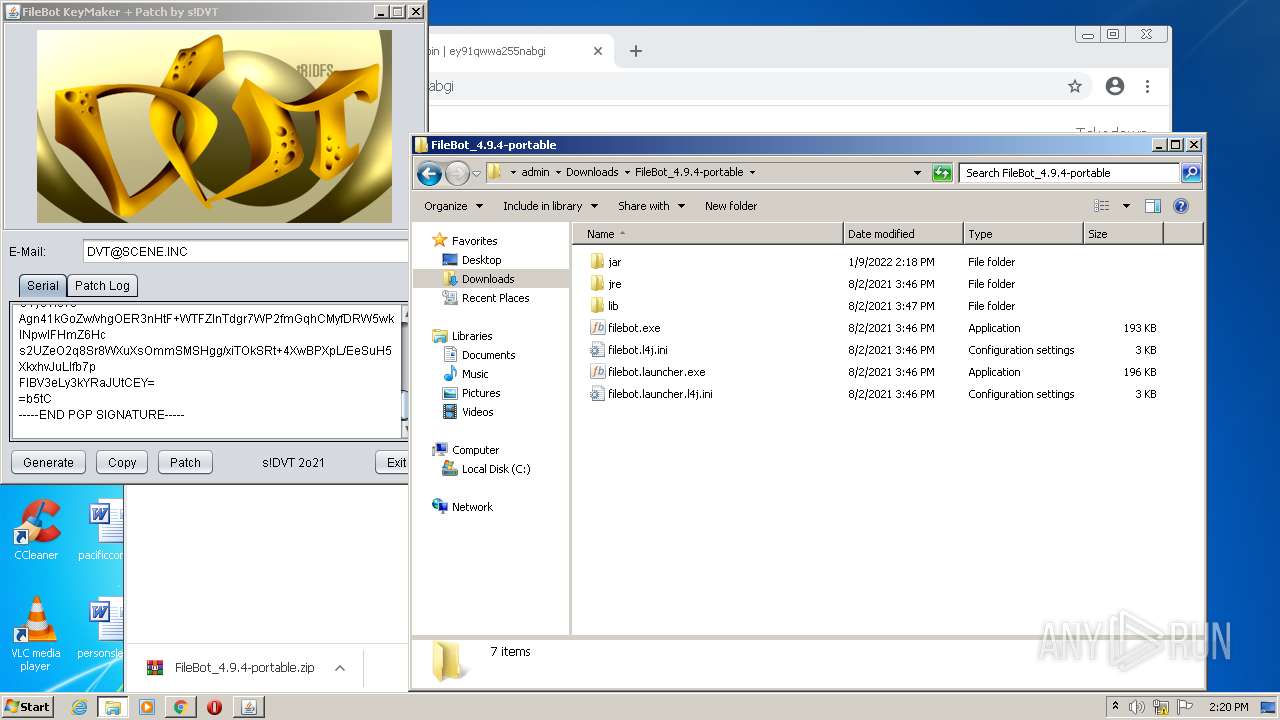
| File name: | dvt-FileBot-KeyMaker.jar |
| Full analysis: | https://app.any.run/tasks/02fe081c-3180-431c-a4d8-79b916b13c82 |
| Verdict: | Malicious activity |
| Analysis date: | January 09, 2022, 14:16:39 |
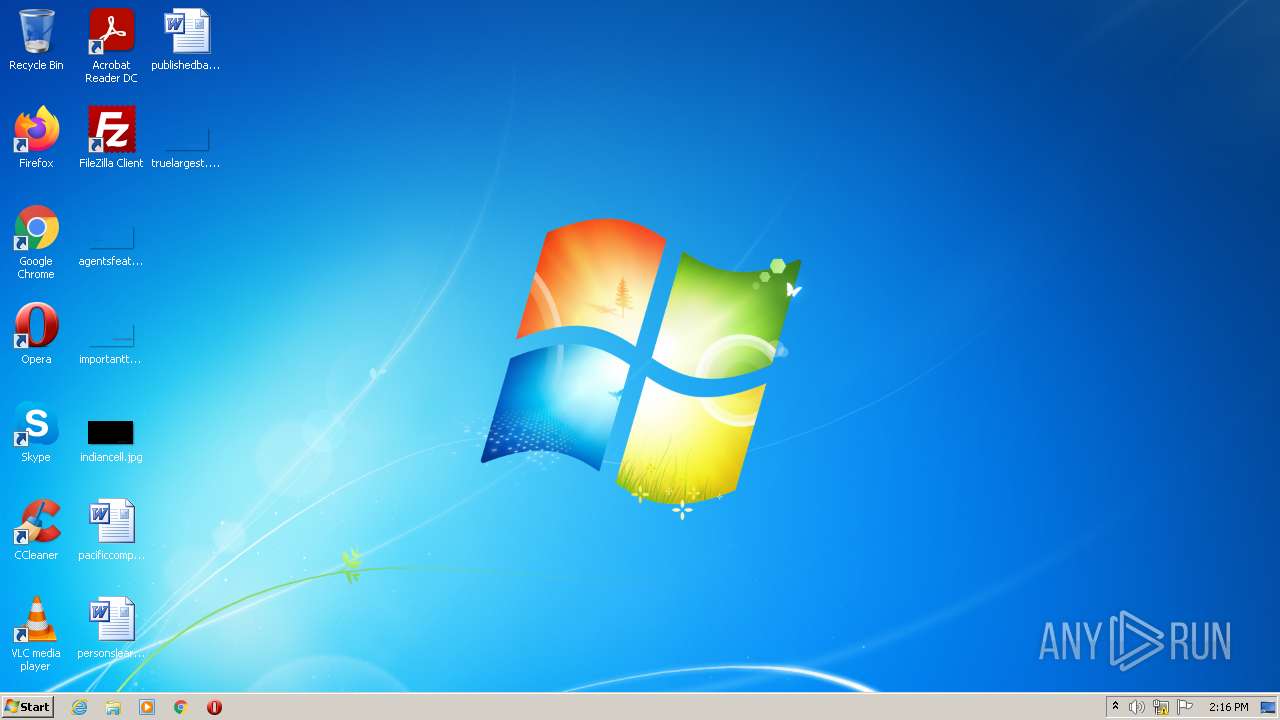
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | D7681083FA1E4173FBA3DC273E87695B |
| SHA1: | E06E4159077CA67CDBE805217CBABD09E437C59E |
| SHA256: | F58FAD3E2E8AD4C0CDD72F1E20428E4BFCAC8D927AB0690A40EECD74BA6B4C77 |
| SSDEEP: | 196608:LflmOcM5CbPF3HT1If2rud+1payGsilZtUQR4No5/e:LflmxM2ZzE3+1payGmQCy5/e |
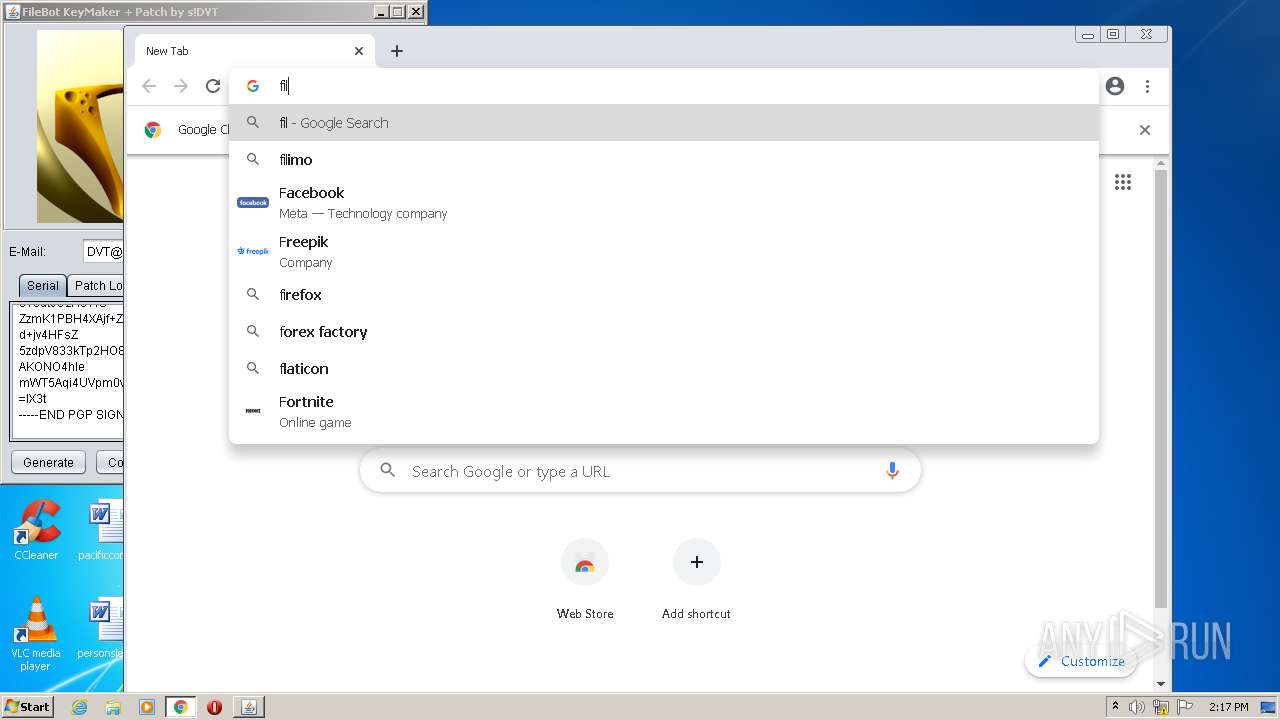
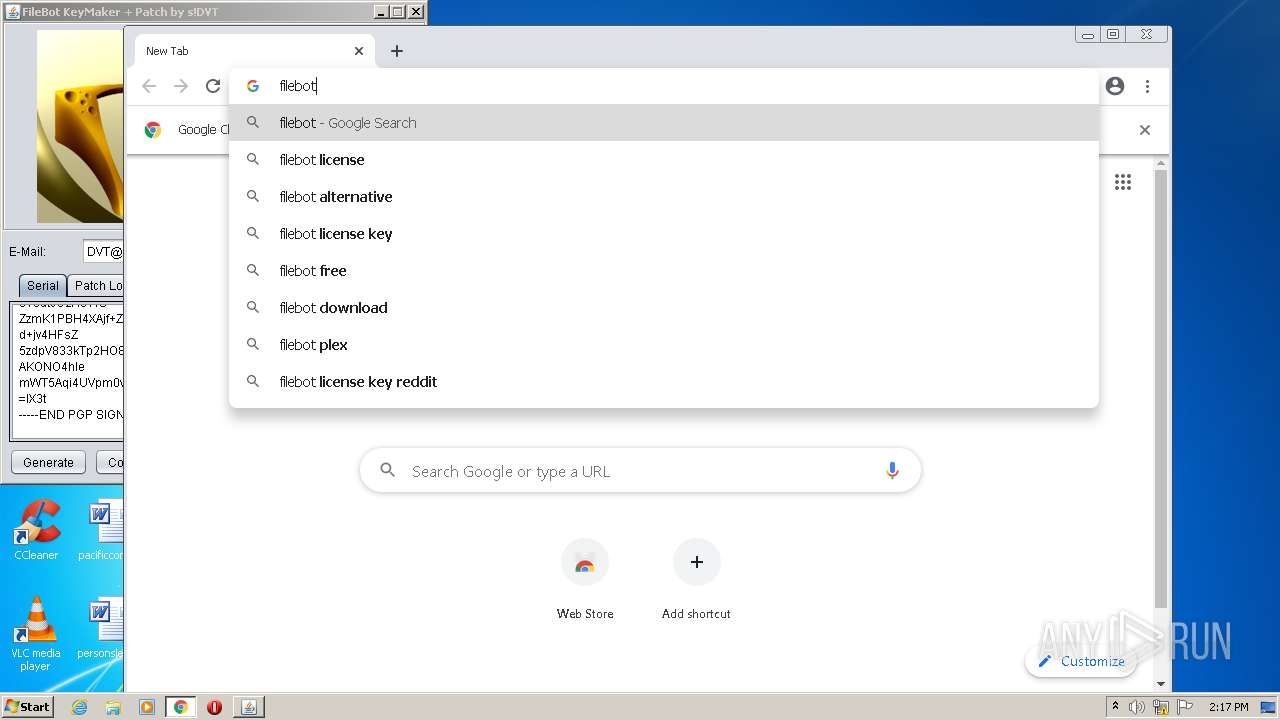
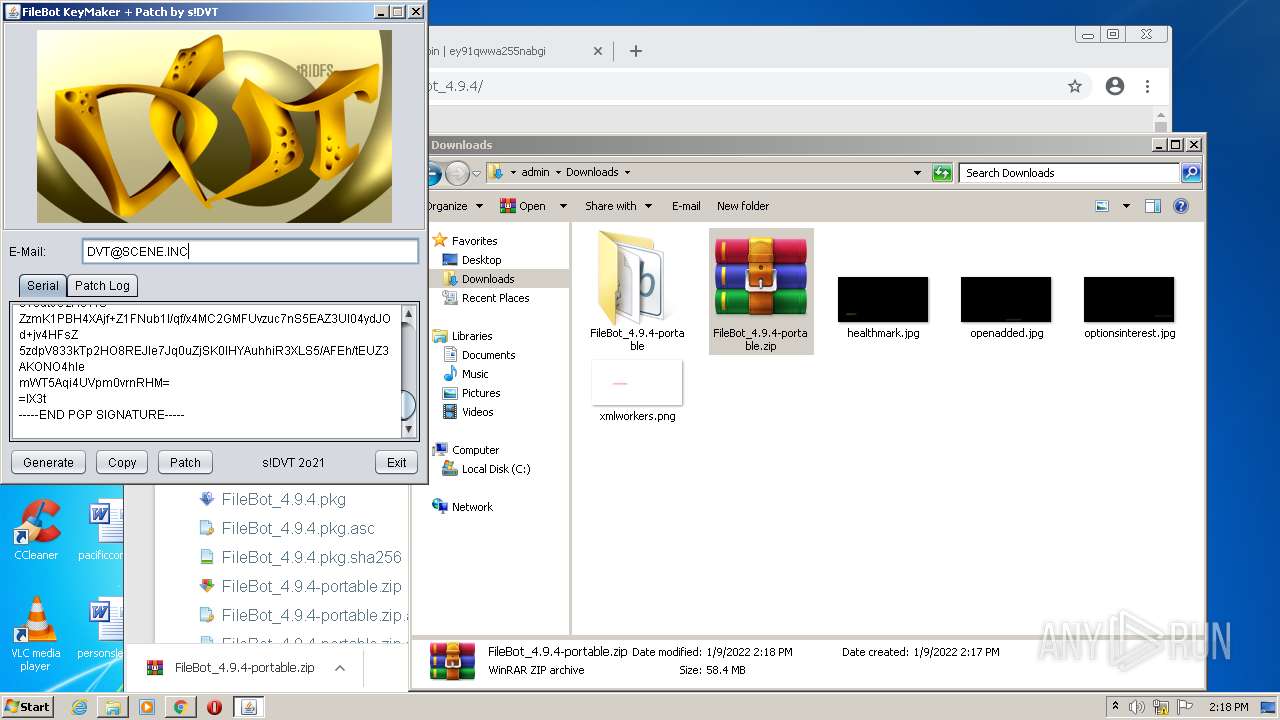
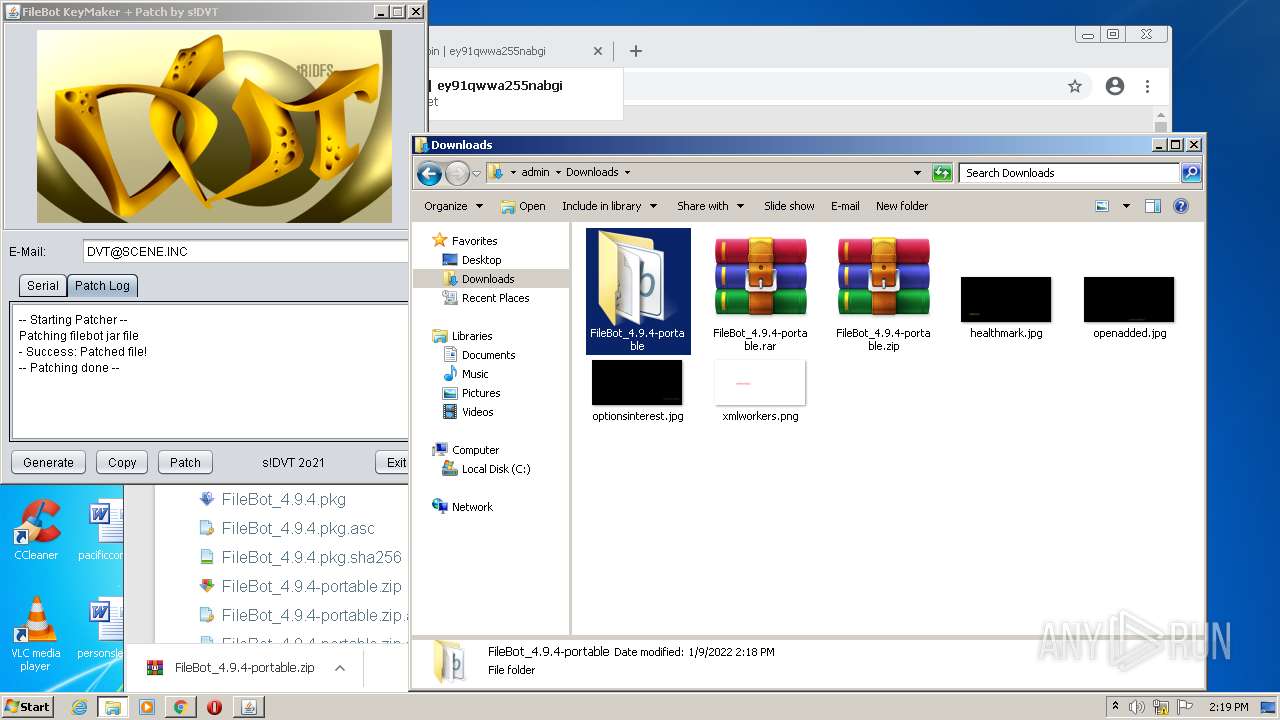
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 2632)
- WinRAR.exe (PID: 3120)
SUSPICIOUS
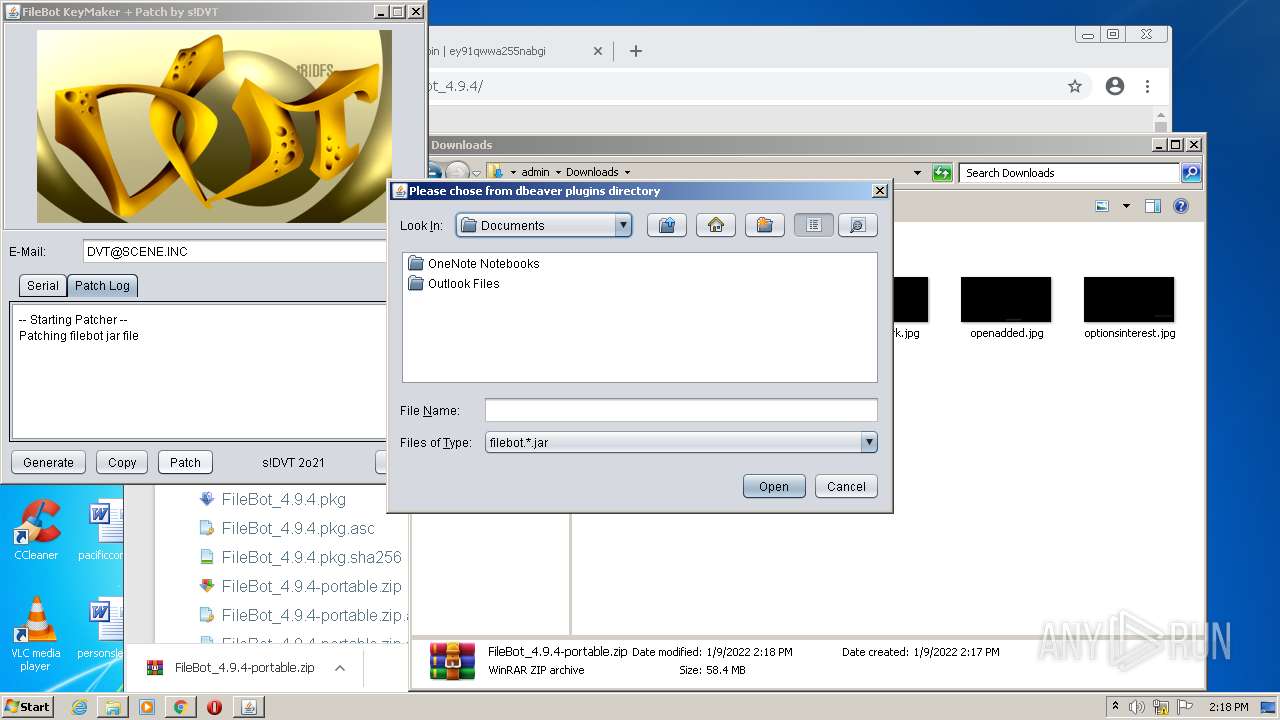
Uses ICACLS.EXE to modify access control list
- javaw.exe (PID: 2420)
Creates files in the program directory
- javaw.exe (PID: 2420)
Reads the computer name
- javaw.exe (PID: 2420)
- WinRAR.exe (PID: 3120)
- WinRAR.exe (PID: 2152)
Checks supported languages
- javaw.exe (PID: 2420)
- WinRAR.exe (PID: 3120)
- WinRAR.exe (PID: 2152)
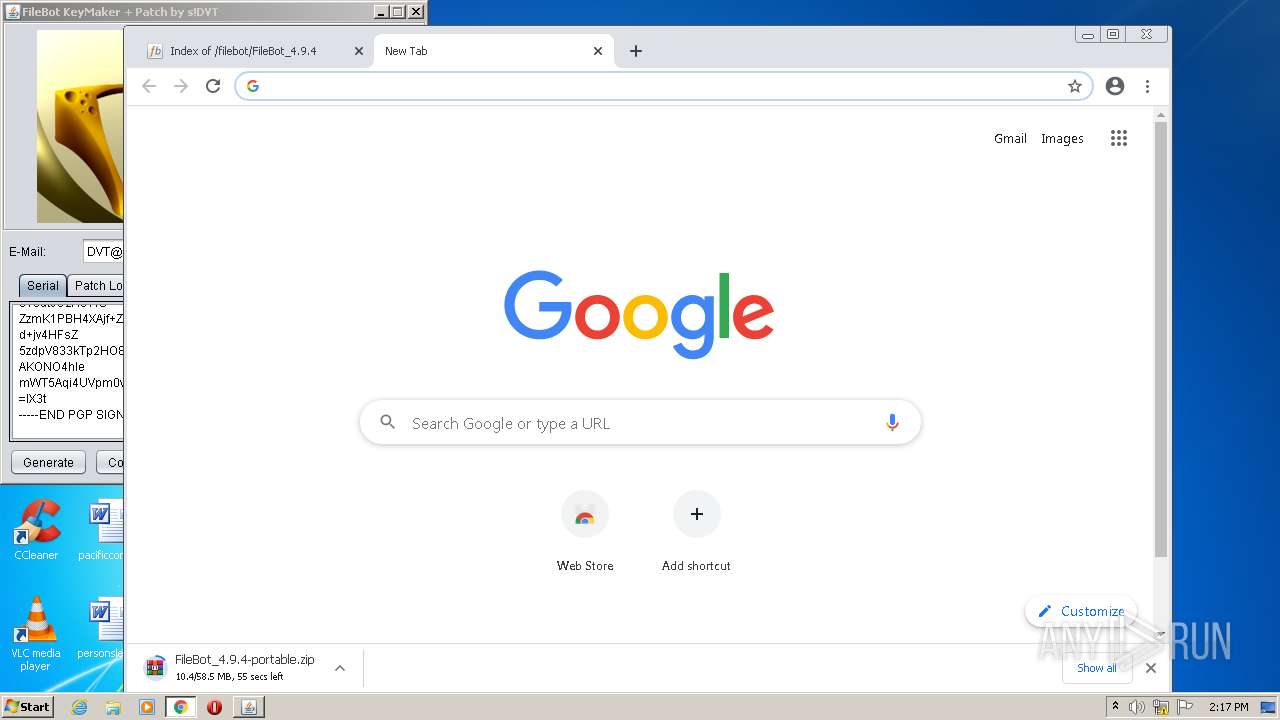
Modifies files in Chrome extension folder
- chrome.exe (PID: 1148)
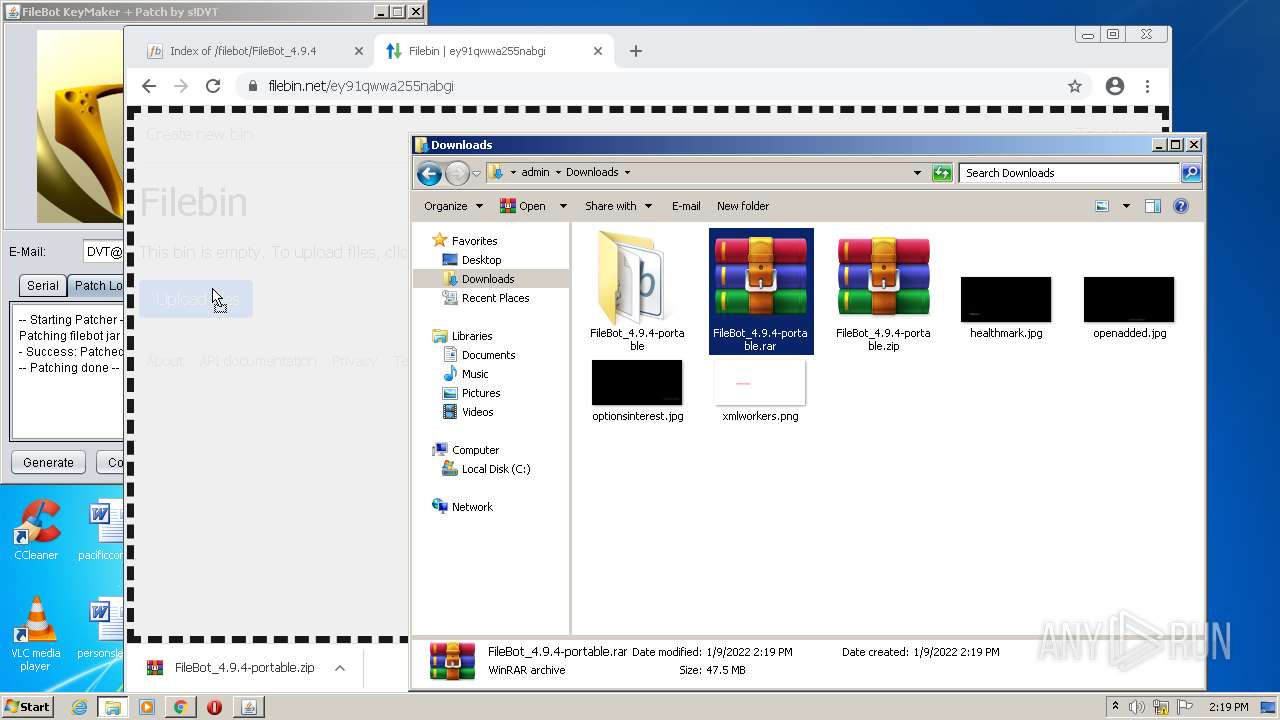
Drops a file with too old compile date
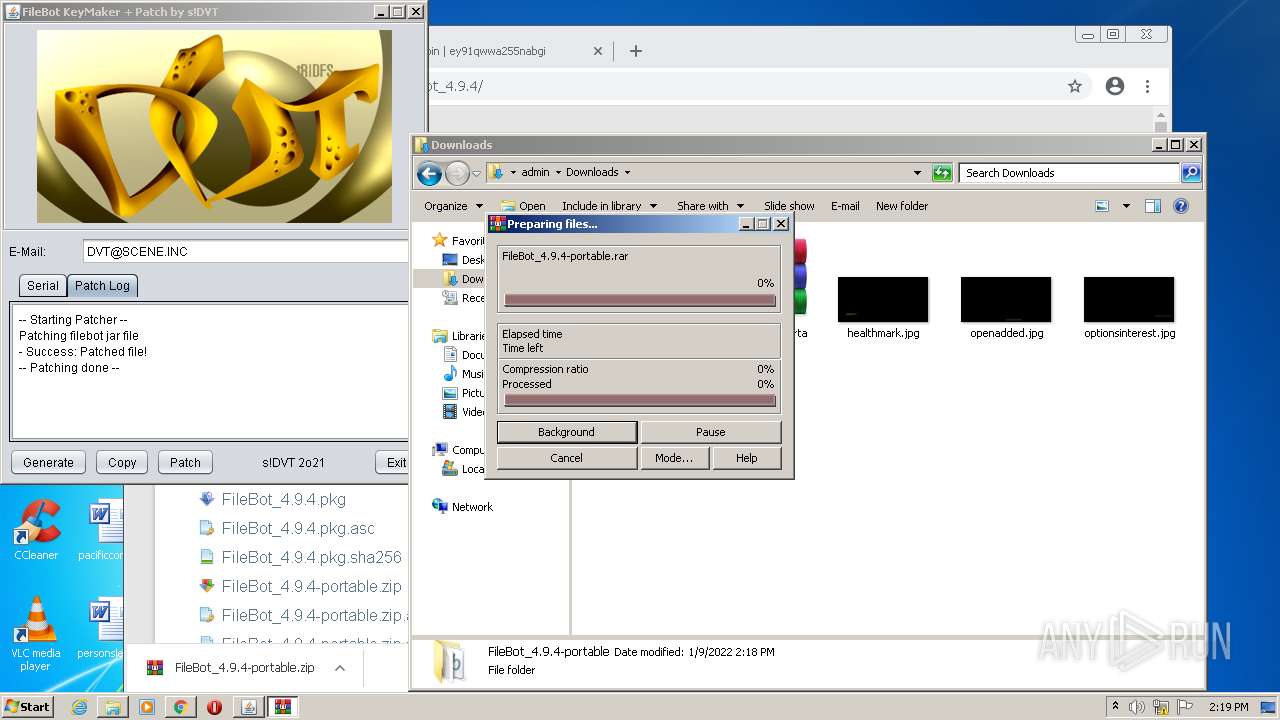
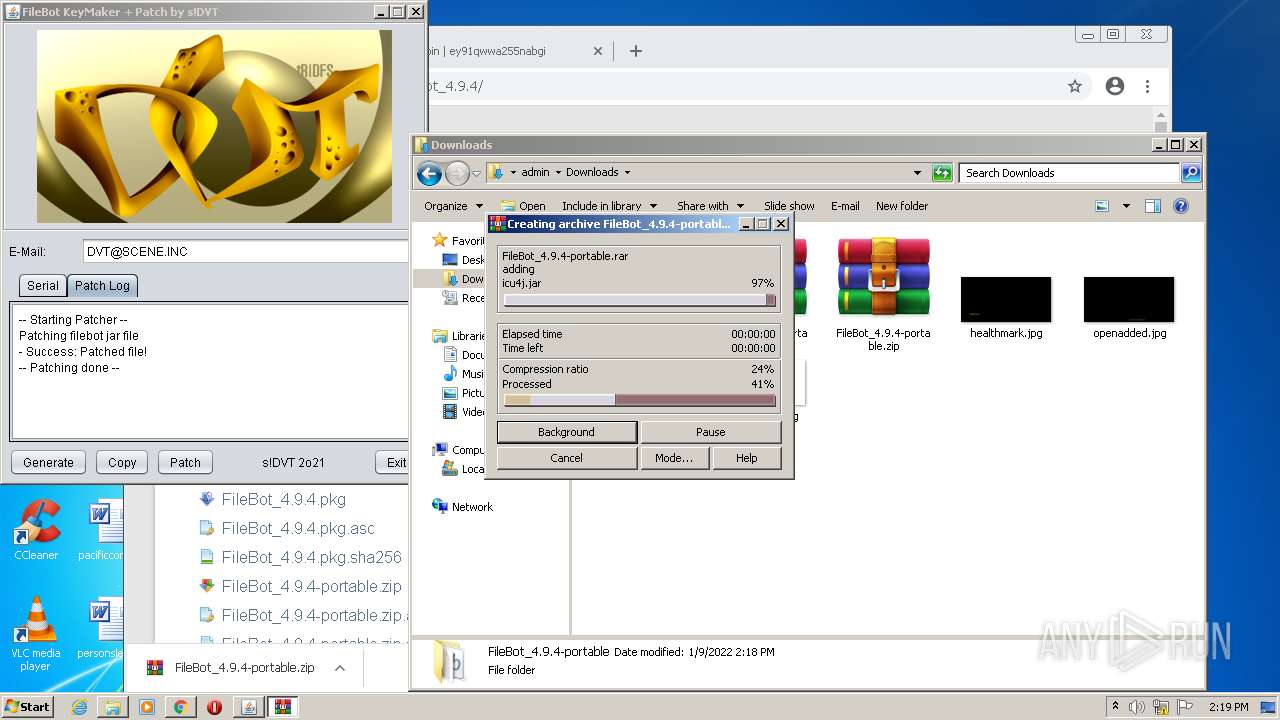
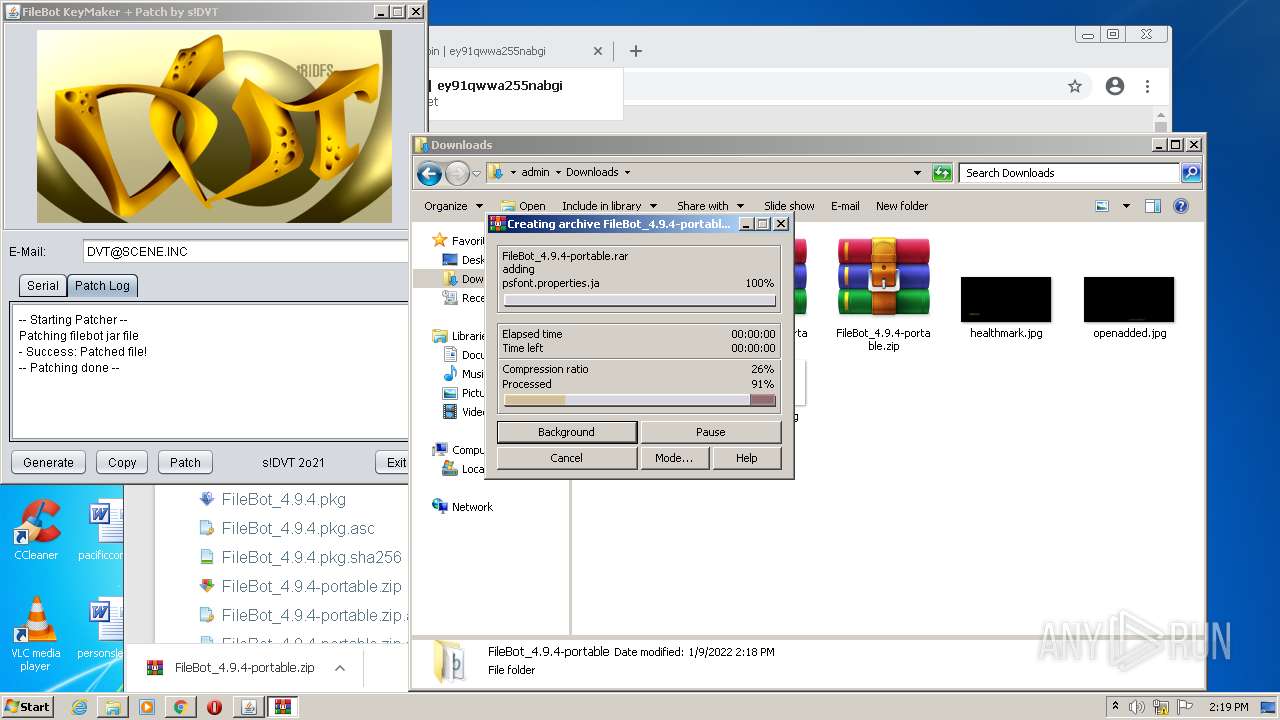
- WinRAR.exe (PID: 3120)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 3120)
- chrome.exe (PID: 2632)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 3120)
Executable content was dropped or overwritten
- chrome.exe (PID: 2632)
- WinRAR.exe (PID: 3120)
INFO
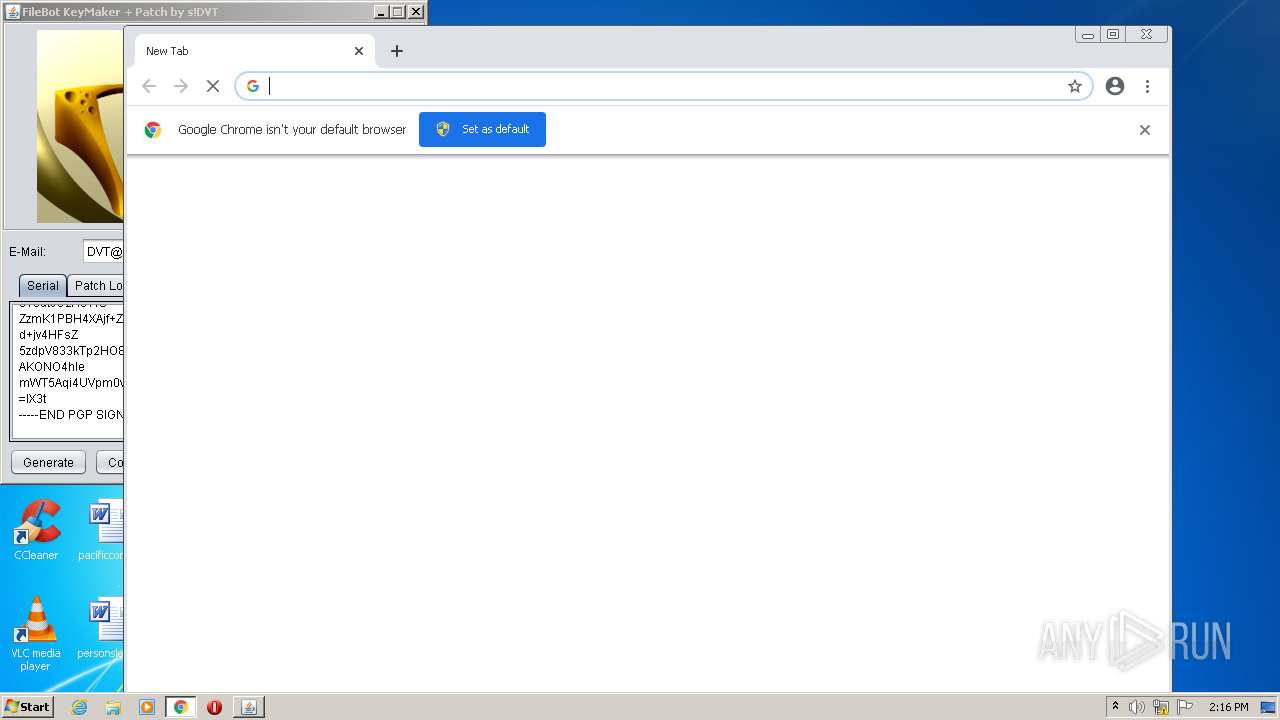
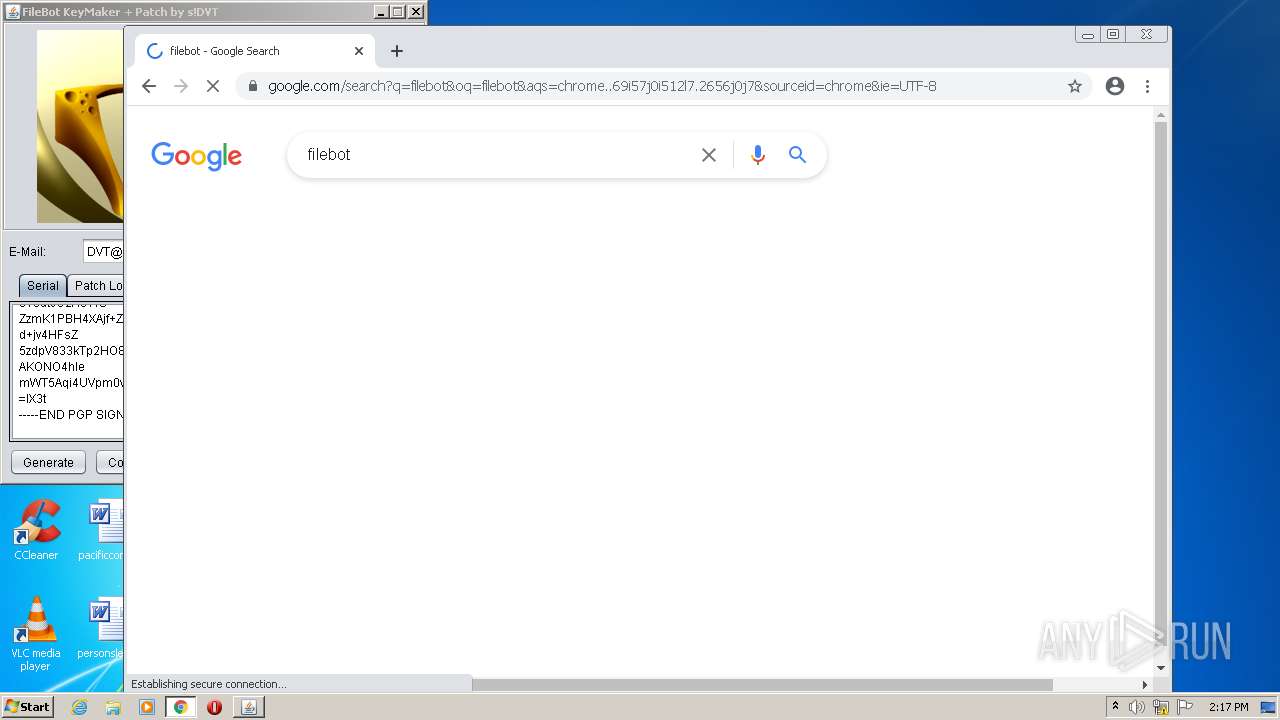
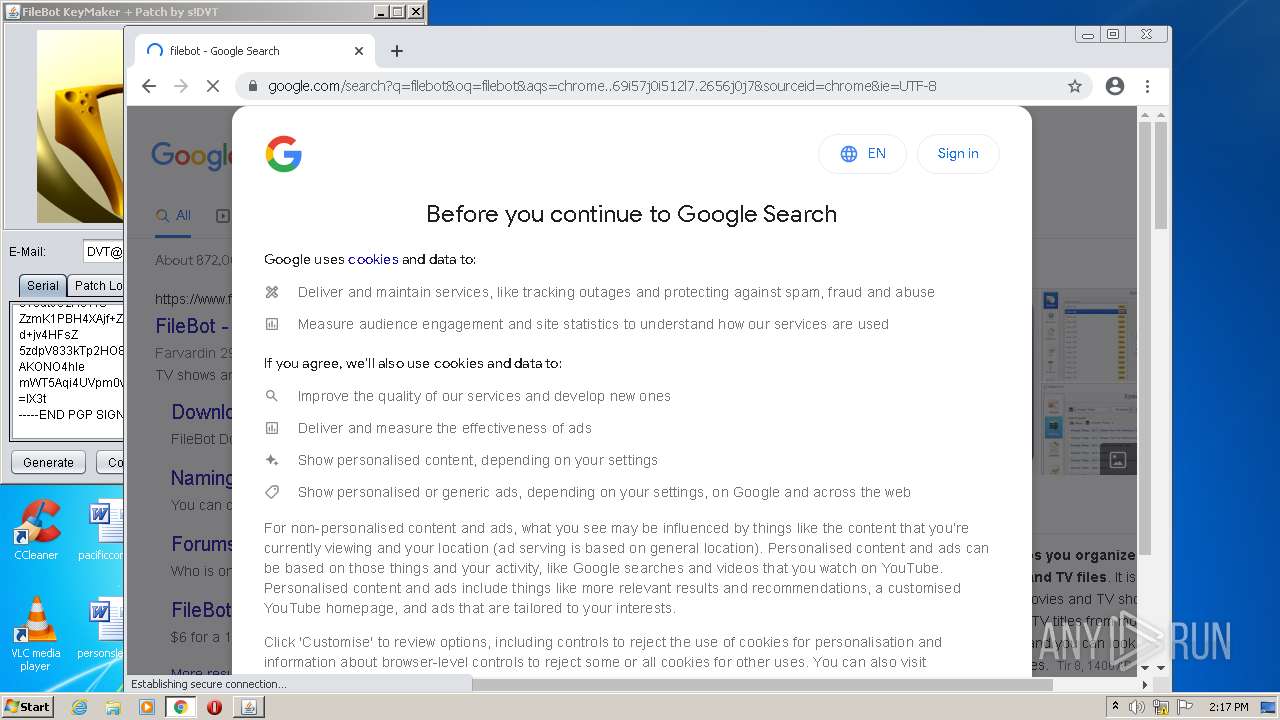
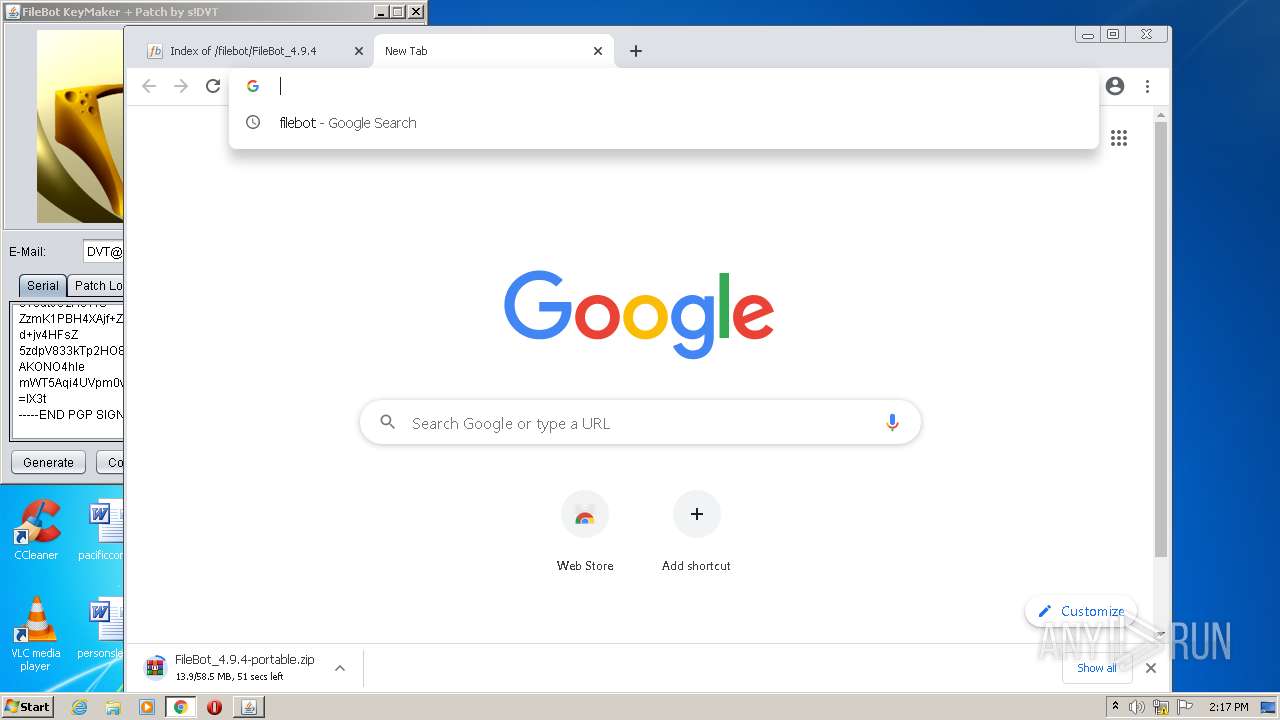
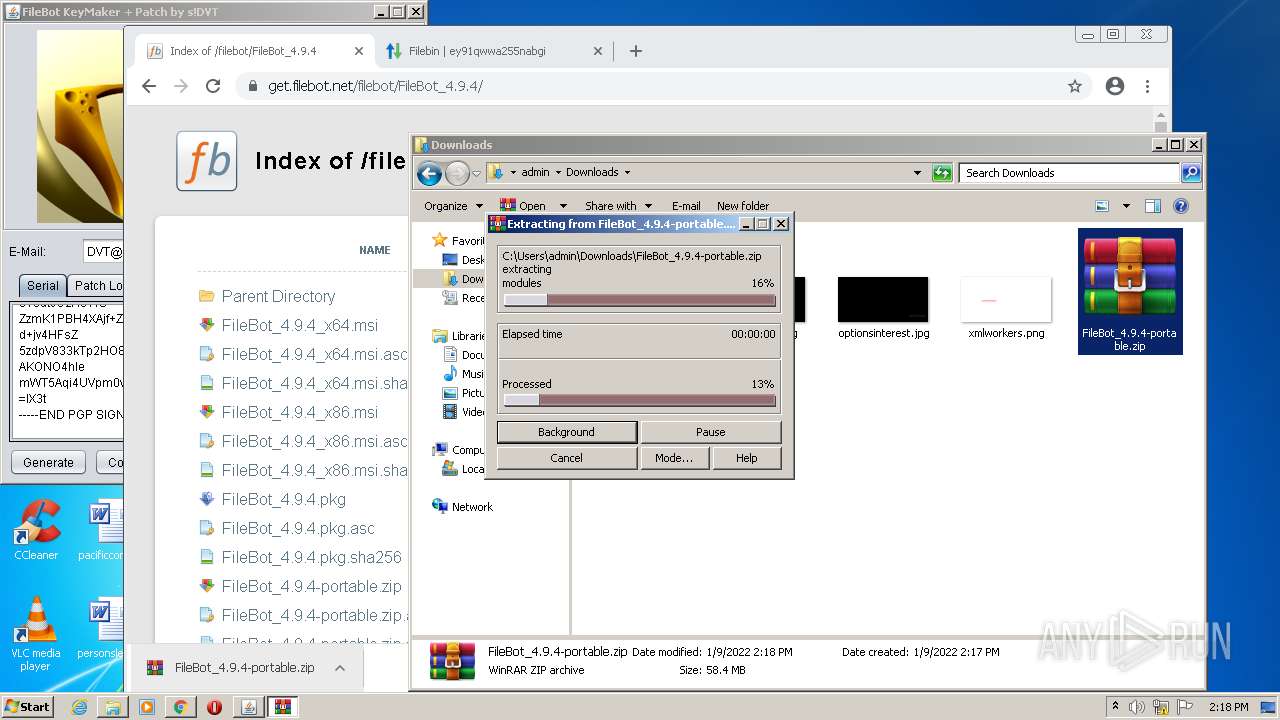
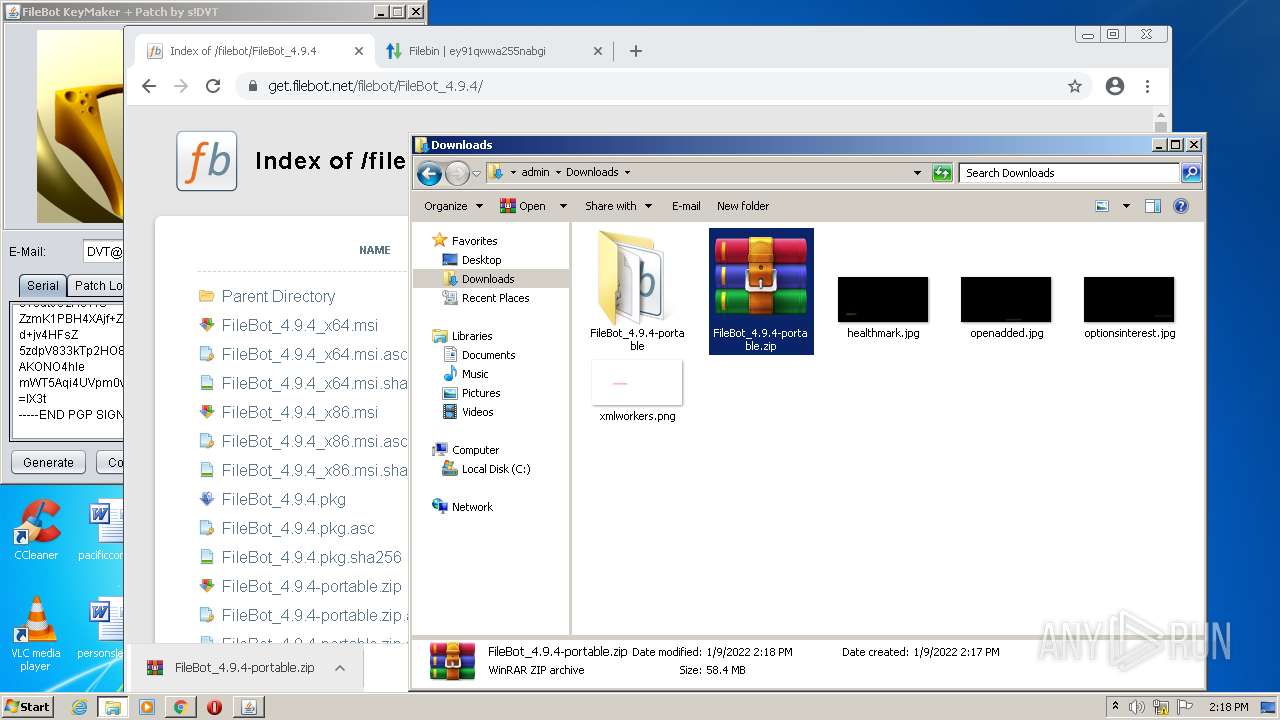
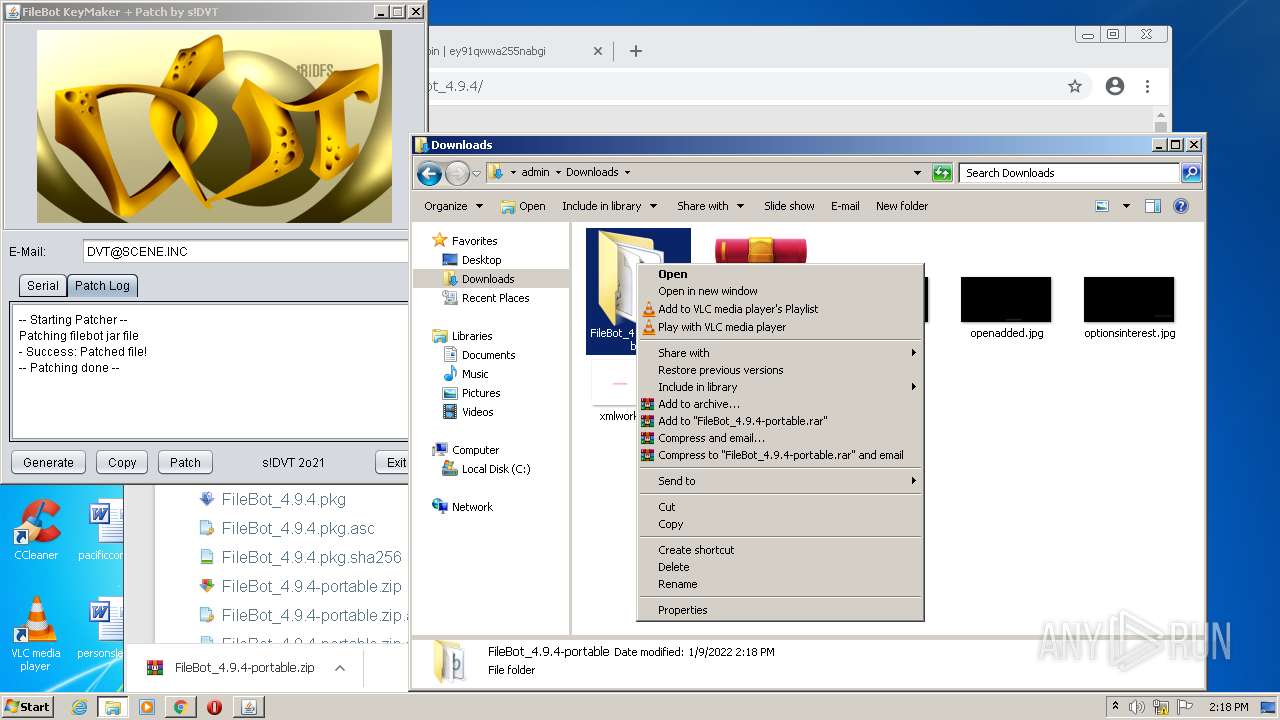
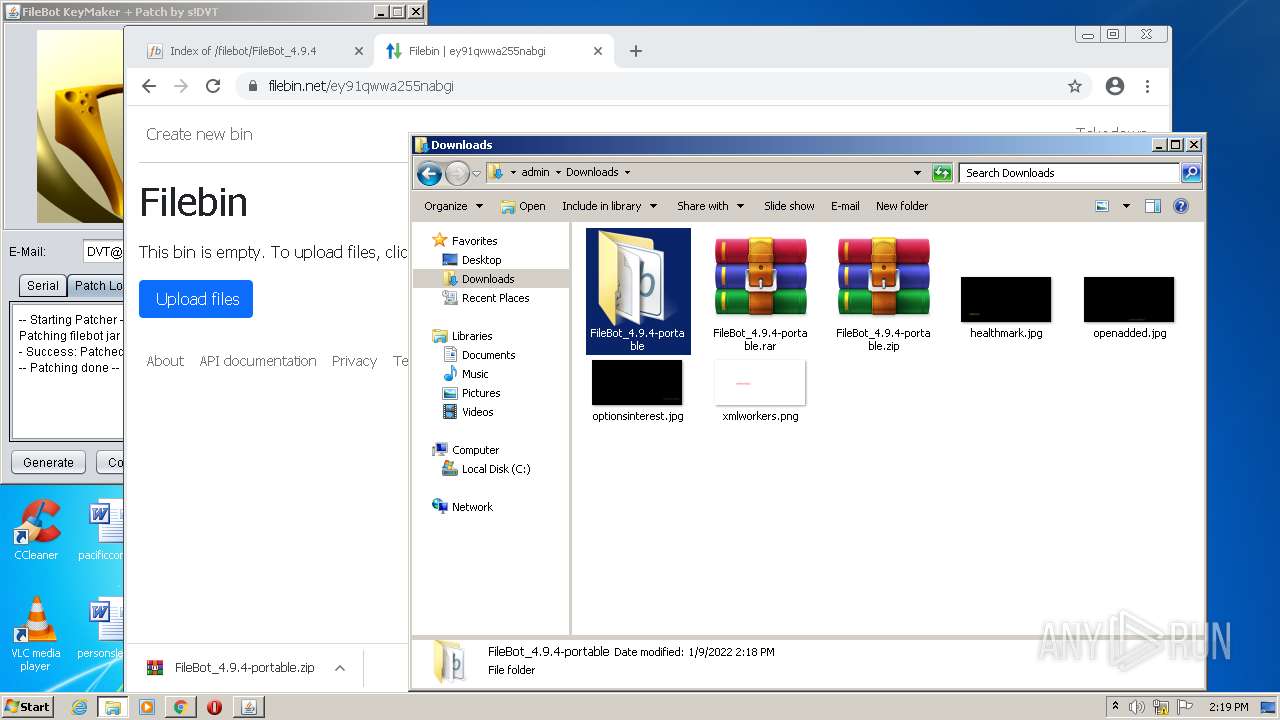
Manual execution by user
- chrome.exe (PID: 1148)
- explorer.exe (PID: 956)
- WinRAR.exe (PID: 3120)
- WinRAR.exe (PID: 2152)
Application launched itself
- chrome.exe (PID: 1148)
Reads the hosts file
- chrome.exe (PID: 1148)
- chrome.exe (PID: 3616)
Reads the computer name
- chrome.exe (PID: 572)
- chrome.exe (PID: 3616)
- chrome.exe (PID: 1148)
- icacls.exe (PID: 1996)
- chrome.exe (PID: 2496)
- chrome.exe (PID: 4024)
- chrome.exe (PID: 2128)
- chrome.exe (PID: 3996)
- chrome.exe (PID: 1708)
- explorer.exe (PID: 956)
- chrome.exe (PID: 3056)
- chrome.exe (PID: 3044)
Checks supported languages
- icacls.exe (PID: 1996)
- chrome.exe (PID: 2952)
- chrome.exe (PID: 3804)
- chrome.exe (PID: 2992)
- chrome.exe (PID: 1148)
- chrome.exe (PID: 3616)
- chrome.exe (PID: 572)
- chrome.exe (PID: 1088)
- chrome.exe (PID: 2156)
- chrome.exe (PID: 3652)
- chrome.exe (PID: 2496)
- chrome.exe (PID: 1228)
- chrome.exe (PID: 636)
- chrome.exe (PID: 3656)
- chrome.exe (PID: 3228)
- chrome.exe (PID: 3760)
- chrome.exe (PID: 3092)
- chrome.exe (PID: 4024)
- chrome.exe (PID: 3088)
- chrome.exe (PID: 3664)
- chrome.exe (PID: 1644)
- chrome.exe (PID: 2128)
- chrome.exe (PID: 1244)
- chrome.exe (PID: 3900)
- chrome.exe (PID: 3880)
- chrome.exe (PID: 3996)
- chrome.exe (PID: 2520)
- chrome.exe (PID: 3064)
- chrome.exe (PID: 2324)
- chrome.exe (PID: 1708)
- explorer.exe (PID: 956)
- chrome.exe (PID: 3056)
- chrome.exe (PID: 1876)
- chrome.exe (PID: 2632)
- chrome.exe (PID: 2276)
- chrome.exe (PID: 3164)
- chrome.exe (PID: 3044)
- chrome.exe (PID: 3900)
- chrome.exe (PID: 1988)
- chrome.exe (PID: 3328)
- chrome.exe (PID: 984)
- chrome.exe (PID: 1508)
- chrome.exe (PID: 3768)
Reads settings of System Certificates
- chrome.exe (PID: 3616)
Reads the date of Windows installation
- chrome.exe (PID: 3996)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 3120)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .jar | | | Java Archive (78.3) |
|---|---|---|
| .zip | | | ZIP compressed archive (21.6) |
EXIF
ZIP
| ZipFileName: | META-INF/MANIFEST.MF |
|---|---|
| ZipUncompressedSize: | 135 |
| ZipCompressedSize: | 121 |
| ZipCRC: | 0x581b76c8 |
| ZipModifyDate: | 2021:12:23 20:38:20 |
| ZipCompression: | Deflated |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 10 |
Total processes
93
Monitored processes
46
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1052,6067094809244186034,2310741036897002874,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1028 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,6067094809244186034,2310741036897002874,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3472 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 956 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1052,6067094809244186034,2310741036897002874,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1832 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,6067094809244186034,2310741036897002874,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1912 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1228 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,6067094809244186034,2310741036897002874,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3436 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,6067094809244186034,2310741036897002874,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3308 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1052,6067094809244186034,2310741036897002874,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2904 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,6067094809244186034,2310741036897002874,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3404 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
17 106
Read events
16 919
Write events
179
Delete events
8
Modification events
| (PID) Process: | (2420) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
| (PID) Process: | (1148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1148) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
92
Suspicious files
258
Text files
294
Unknown types
18
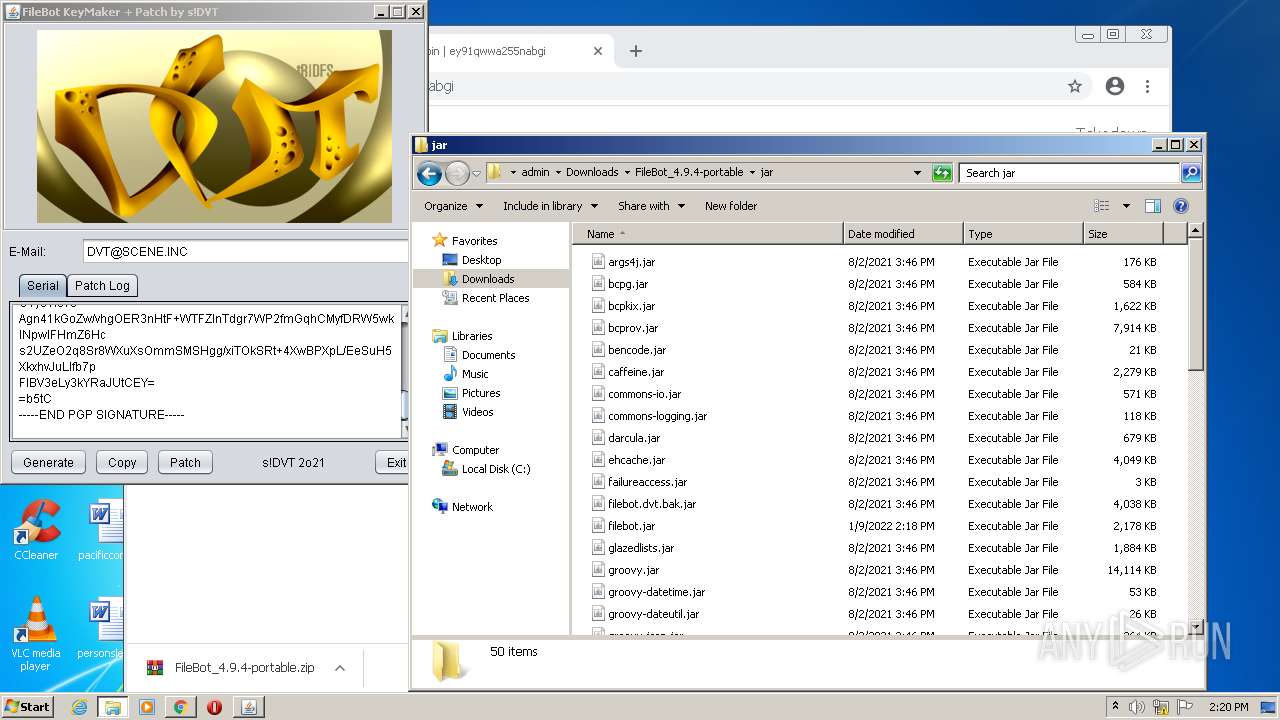
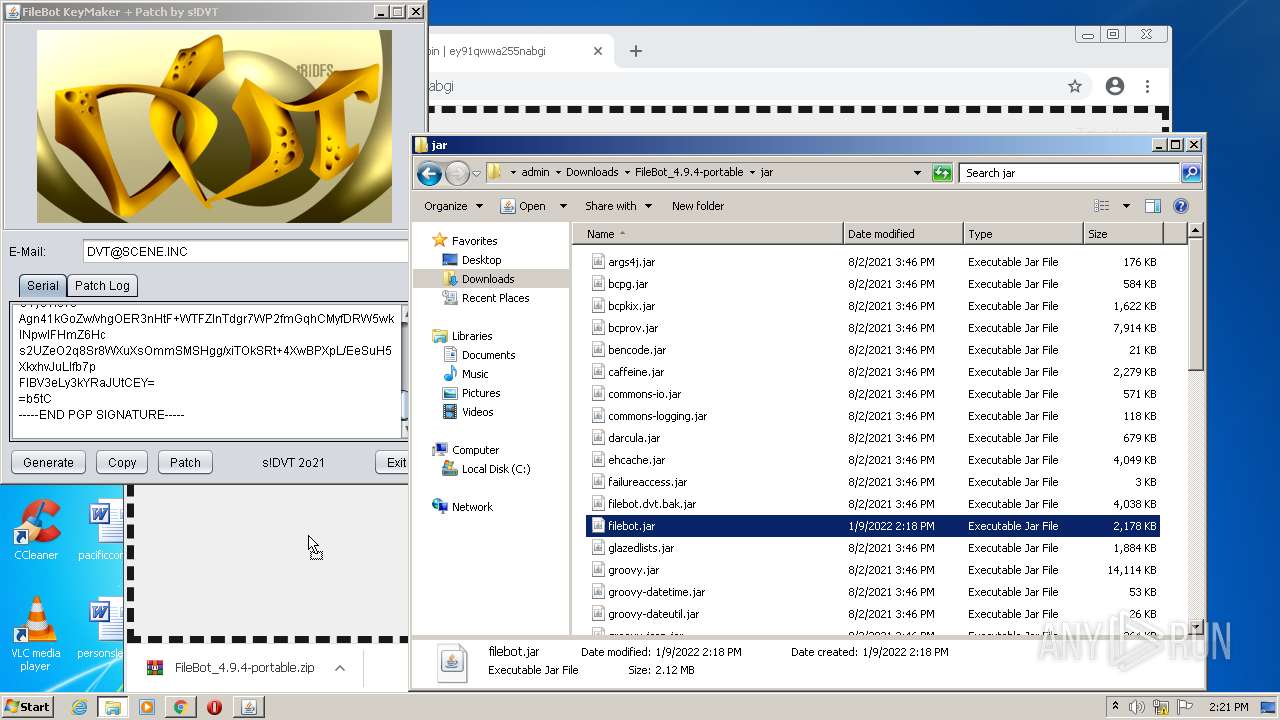
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61DAEE57-47C.pma | — | |
MD5:— | SHA256:— | |||
| 2420 | javaw.exe | C:\ProgramData\Oracle\Java\.oracle_jre_usage\17dfc292991c8061.timestamp | text | |
MD5:— | SHA256:— | |||
| 2420 | javaw.exe | C:\Users\admin\AppData\Local\Temp\JarClassLoader\bcpg-jdk15on-1.69.jar.5784122180888271907.tmp | java | |
MD5:226C67230ECC051E5FC880752E62E5E9 | SHA256:A3984FF7FD9518D00094E34F3D3E714A4823F2505ADA1C19B35C129E26F63934 | |||
| 2420 | javaw.exe | C:\Users\admin\AppData\Local\Temp\JarClassLoader\javamod-1.0.jar.810845254945072352.tmp | java | |
MD5:1900184D00811521D853E151BC3A62CB | SHA256:4C77C2849AE798C993DDB2EF04FC60ED0BDF35C9338053F1EBF93660B26C2CF1 | |||
| 1148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2420 | javaw.exe | C:\Users\admin\AppData\Local\Temp\JavaMod9106544893339069835ReadFile | xm | |
MD5:06A527FA151A271E3009C16EDE953B35 | SHA256:E19C4B7920AF8E7D60ADE5A1839669B0D59998C31A781CDCB90B65AB09794EDE | |||
| 1148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF141480.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 1148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF14153c.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 2420 | javaw.exe | C:\Users\admin\AppData\Local\Temp\JarClassLoader\javassist-3.28.0-GA.jar.812024031640459451.tmp | java | |
MD5:1A2DD8C76321CEF26CC2669FE70A2557 | SHA256:57D0A9E9286F82F4EAA851125186997F811BEFCE0E2060FF0A15A77F5A9DD9A7 | |||
| 1148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
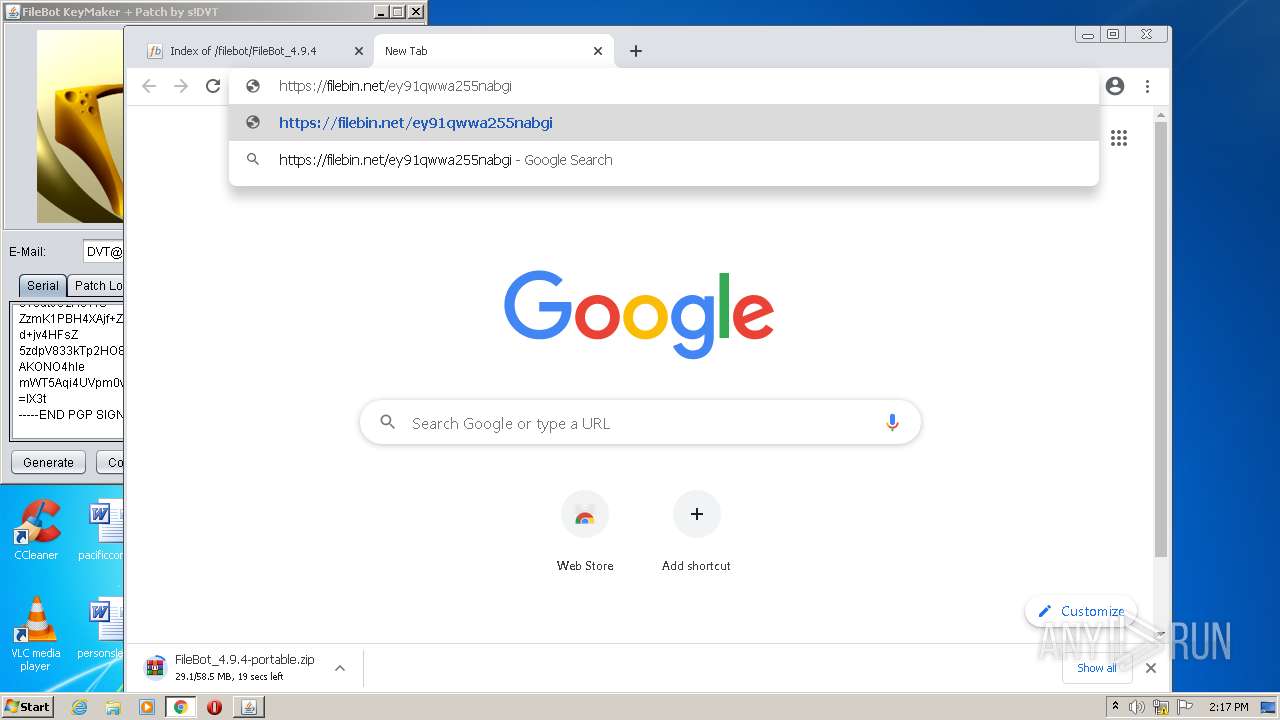
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
76
TCP/UDP connections
56
DNS requests
40
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
924 | svchost.exe | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | — | — | whitelisted |
924 | svchost.exe | HEAD | 302 | 142.250.185.206:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | — | — | whitelisted |
924 | svchost.exe | HEAD | 200 | 74.125.108.199:80 | http://r2---sn-1gi7znek.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=85.203.45.7&mm=28&mn=sn-1gi7znek&ms=nvh&mt=1641737542&mv=m&mvi=2&pl=24&rmhost=r3---sn-1gi7znek.gvt1.com&shardbypass=yes | US | — | — | whitelisted |
3616 | chrome.exe | GET | 302 | 142.250.185.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 554 b | whitelisted |
924 | svchost.exe | GET | 206 | 74.125.108.199:80 | http://r2---sn-1gi7znek.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=85.203.45.7&mm=28&mn=sn-1gi7znek&ms=nvh&mt=1641737542&mv=m&mvi=2&pl=24&rmhost=r3---sn-1gi7znek.gvt1.com&shardbypass=yes | US | binary | 5.63 Kb | whitelisted |
924 | svchost.exe | GET | 302 | 142.250.185.206:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 575 b | whitelisted |
924 | svchost.exe | GET | 302 | 142.250.185.206:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 575 b | whitelisted |
924 | svchost.exe | GET | 302 | 142.250.185.206:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 575 b | whitelisted |
924 | svchost.exe | GET | 302 | 142.250.185.206:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 575 b | whitelisted |
924 | svchost.exe | GET | 206 | 74.125.108.199:80 | http://r2---sn-1gi7znek.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=85.203.45.7&mm=28&mn=sn-1gi7znek&ms=nvh&mt=1641737542&mv=m&mvi=2&pl=24&rmhost=r3---sn-1gi7znek.gvt1.com&shardbypass=yes | US | binary | 9.50 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
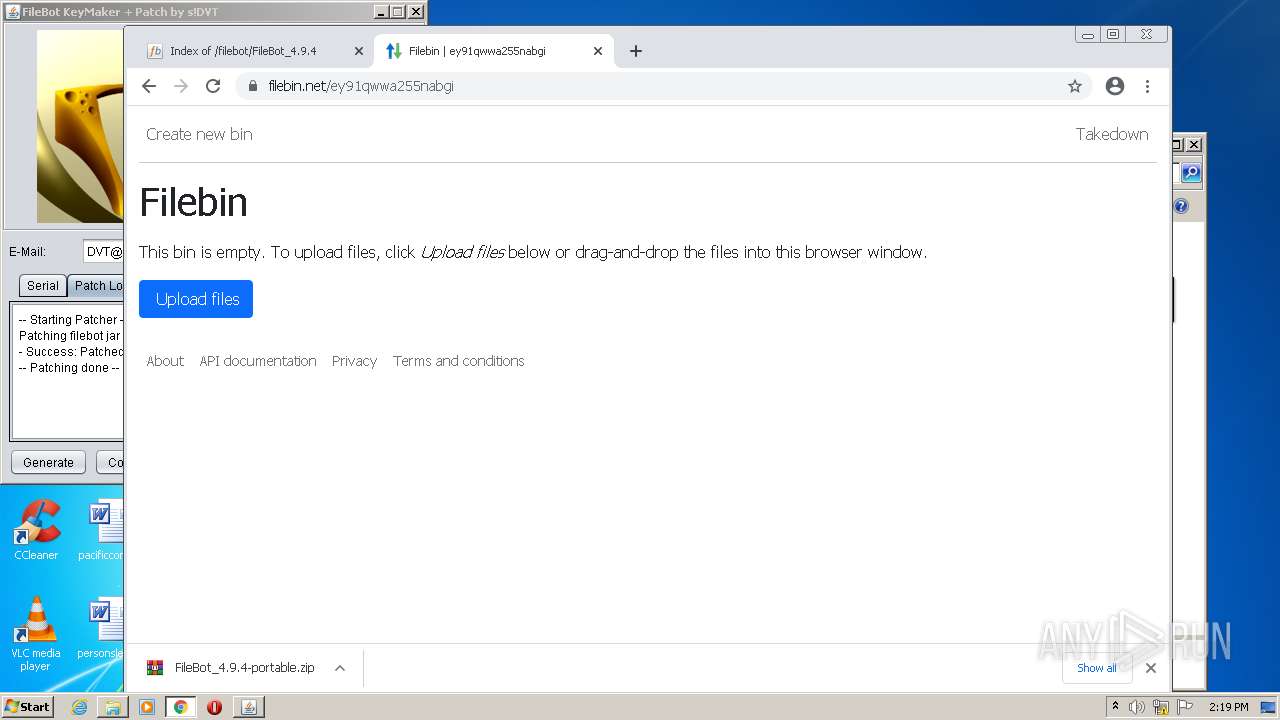
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3616 | chrome.exe | 104.16.18.94:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | unknown |
3616 | chrome.exe | 34.104.35.123:80 | edgedl.me.gvt1.com | — | US | whitelisted |
3616 | chrome.exe | 172.66.40.60:443 | cdn.paddle.com | — | US | suspicious |
3616 | chrome.exe | 142.250.185.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
3616 | chrome.exe | 142.250.186.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3616 | chrome.exe | 142.250.185.132:443 | www.google.com | Google Inc. | US | whitelisted |
3616 | chrome.exe | 142.250.185.238:443 | clients2.google.com | Google Inc. | US | whitelisted |
3616 | chrome.exe | 142.250.185.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3616 | chrome.exe | 142.250.184.206:443 | apis.google.com | Google Inc. | US | whitelisted |
3616 | chrome.exe | 142.250.184.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
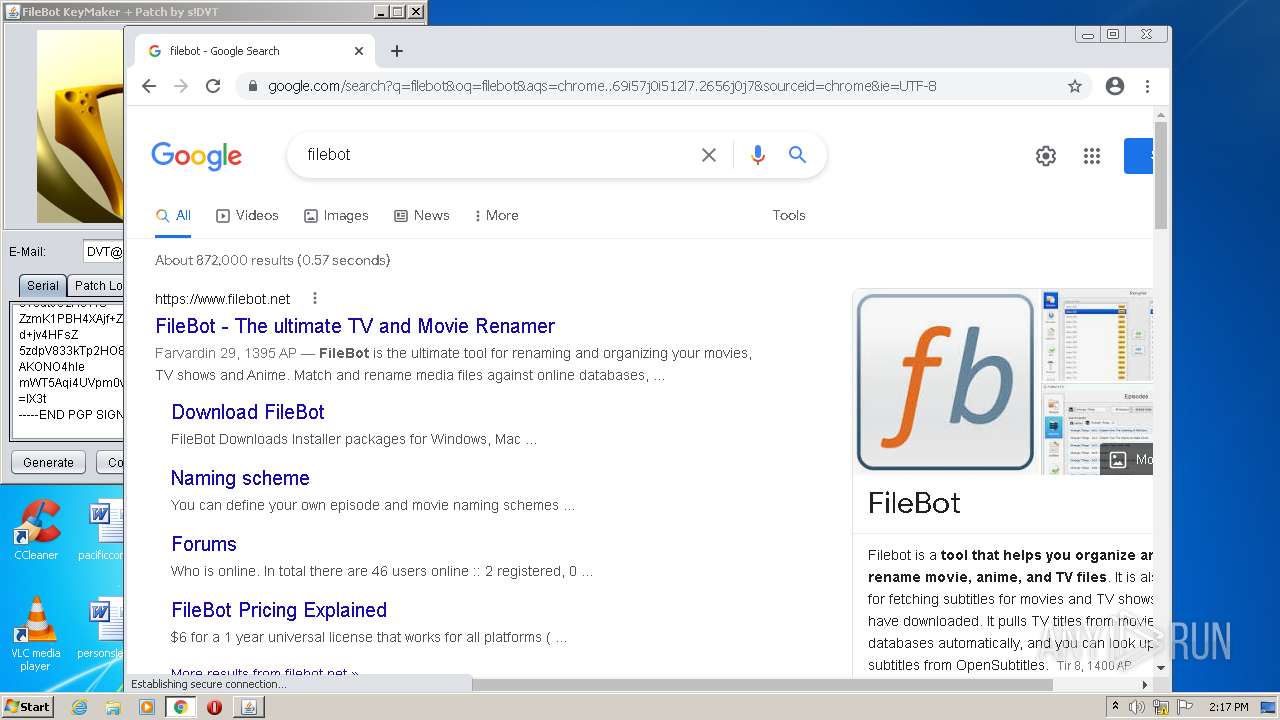
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |