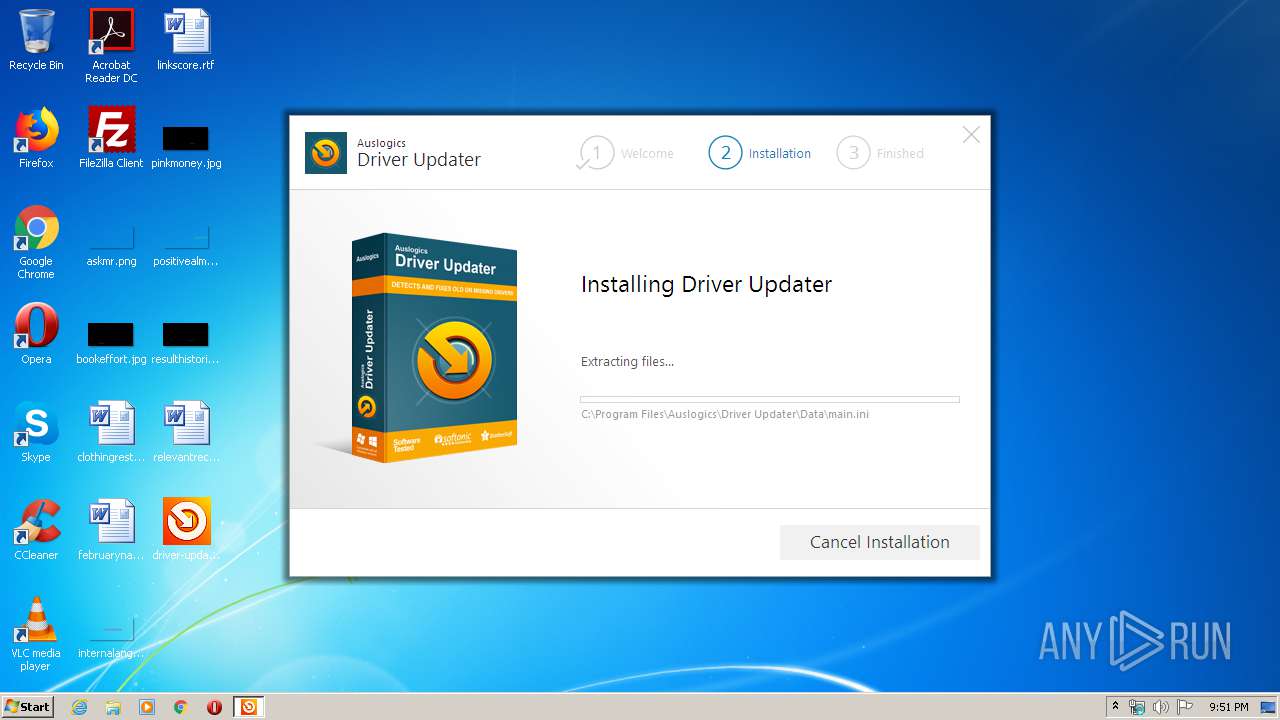
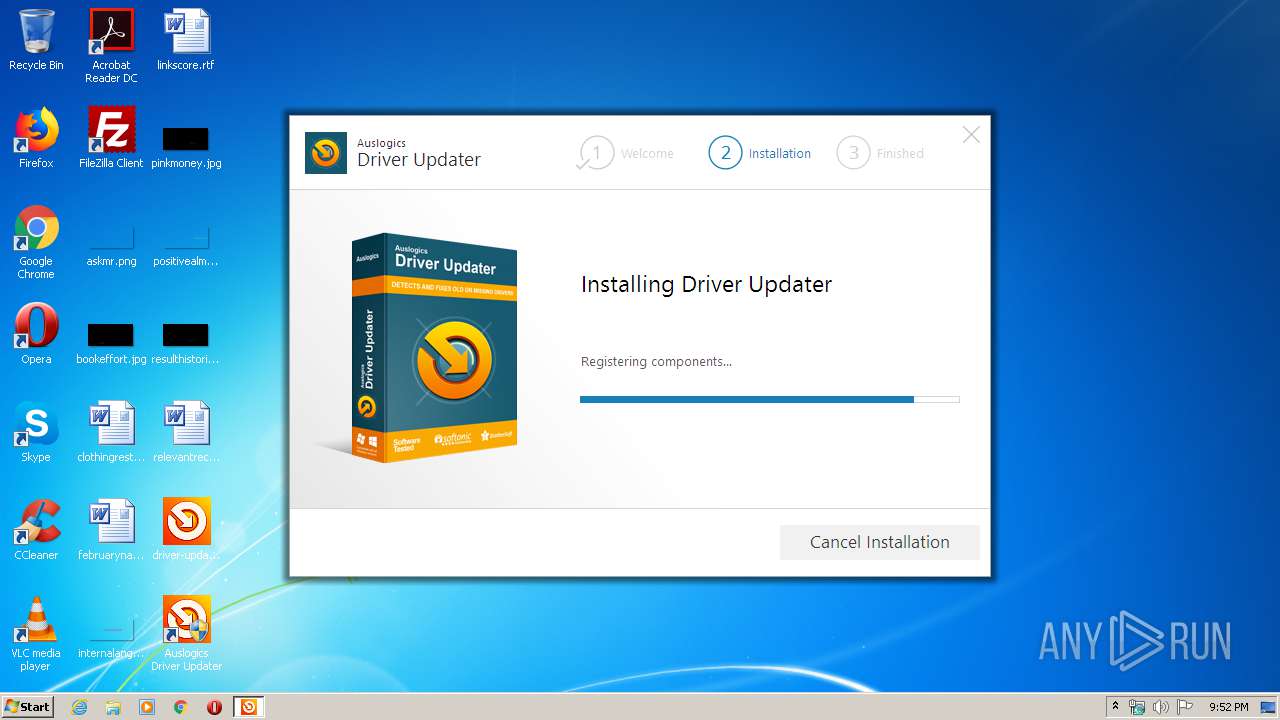
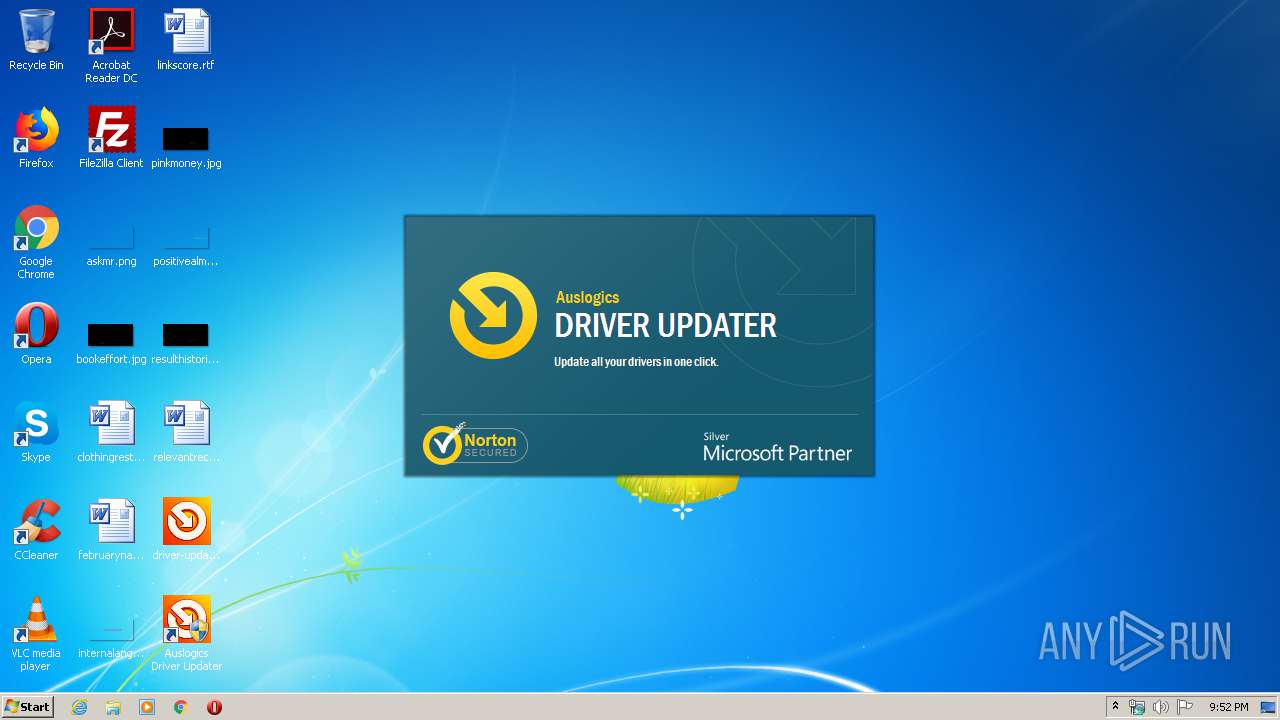
| download: | driver-updater-setup.exe |
| Full analysis: | https://app.any.run/tasks/2ad3dfe6-36e4-4fe8-8172-bd2db6a757cb |
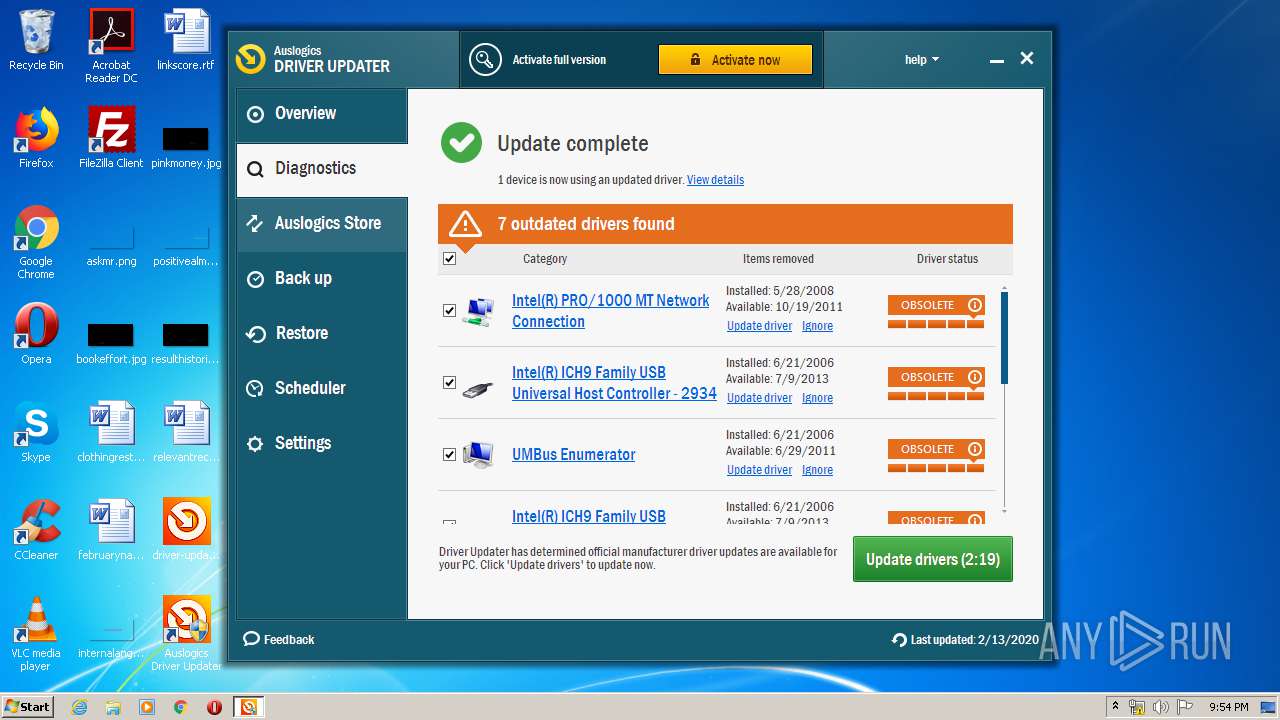
| Verdict: | Malicious activity |
| Analysis date: | February 13, 2020, 21:51:18 |
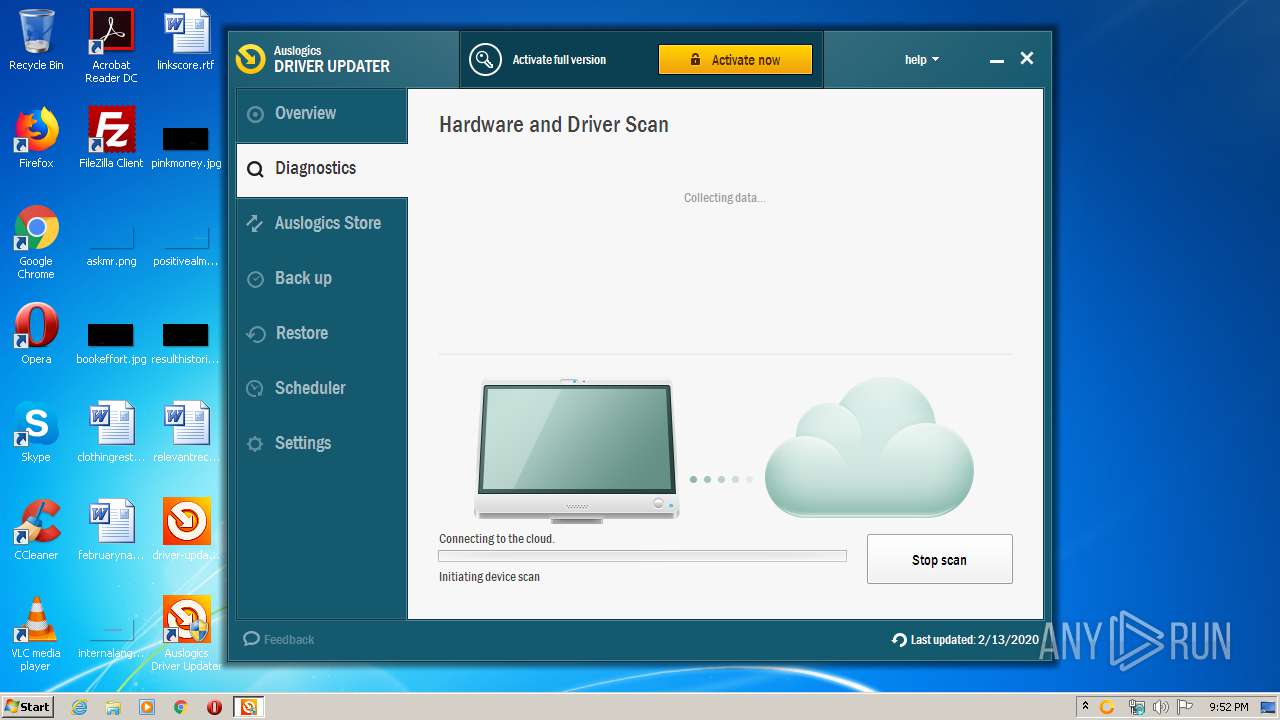
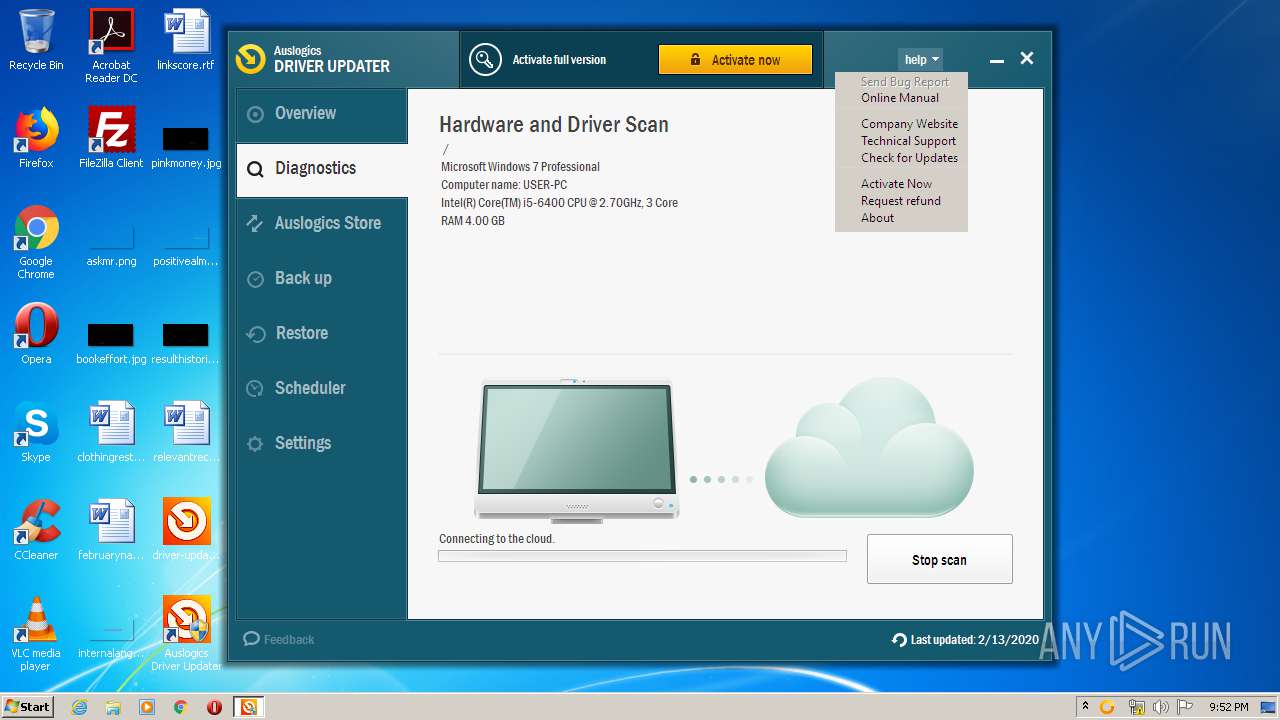
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B565F21A1CF0D93DC7A64474D29E66E9 |
| SHA1: | 5294852730CCB7986969A8F25A216761F860328B |
| SHA256: | F57C4629389670E0A5DAC07C541EB2E218E00FBEFB84AC7A4655A8FC181BD67F |
| SSDEEP: | 196608:cLJoG4XaKwPH+p1T4CfsX/1MIgM+RJNM1JF/eIWXDM5/rrmP+Y5drdw8FqfQST:cLRcwf+74g6MlM+PNM172DMJrAHxFS |
MALICIOUS
Application was dropped or rewritten from another process
- DriverUpdater.exe (PID: 2660)
- DriverUpdater.exe (PID: 1504)
- dpinst32.exe (PID: 3824)
Loads dropped or rewritten executable
- DriverUpdater.exe (PID: 2660)
- DriverUpdater.exe (PID: 1504)
- DrvInst.exe (PID: 548)
- dpinst32.exe (PID: 3824)
Loads the Task Scheduler COM API
- driver-updater-setup.tmp (PID: 3952)
- DriverUpdater.exe (PID: 2660)
- DriverUpdater.exe (PID: 1504)
Changes settings of System certificates
- driver-updater-setup.tmp (PID: 3952)
- DriverUpdater.exe (PID: 1504)
- DriverUpdater.exe (PID: 2660)
SUSPICIOUS
Reads the machine GUID from the registry
- driver-updater-setup.tmp (PID: 3952)
- DriverUpdater.exe (PID: 2660)
- DriverUpdater.exe (PID: 1504)
Reads Windows Product ID
- driver-updater-setup.tmp (PID: 3952)
- DriverUpdater.exe (PID: 2660)
- DriverUpdater.exe (PID: 1504)
Reads Windows owner or organization settings
- driver-updater-setup.tmp (PID: 3952)
Reads the Windows organization settings
- driver-updater-setup.tmp (PID: 3952)
Executable content was dropped or overwritten
- driver-updater-setup.exe (PID: 3356)
- driver-updater-setup.exe (PID: 2860)
- driver-updater-setup.tmp (PID: 3952)
- dpinst32.exe (PID: 3824)
- DriverUpdater.exe (PID: 1504)
- DrvInst.exe (PID: 3892)
- DrvInst.exe (PID: 548)
Reads Internet Cache Settings
- driver-updater-setup.tmp (PID: 3952)
- DriverUpdater.exe (PID: 2660)
- taskhost.exe (PID: 2908)
- DriverUpdater.exe (PID: 1504)
Reads the cookies of Google Chrome
- driver-updater-setup.tmp (PID: 3952)
Reads the cookies of Mozilla Firefox
- driver-updater-setup.tmp (PID: 3952)
Executed as Windows Service
- taskhost.exe (PID: 664)
- taskhost.exe (PID: 2784)
- taskhost.exe (PID: 2428)
- taskhost.exe (PID: 2908)
- vssvc.exe (PID: 1992)
Creates files in the user directory
- driver-updater-setup.tmp (PID: 3952)
Adds / modifies Windows certificates
- DriverUpdater.exe (PID: 1504)
- driver-updater-setup.tmp (PID: 3952)
- DriverUpdater.exe (PID: 2660)
Searches for installed software
- DriverUpdater.exe (PID: 1504)
Executed via COM
- DllHost.exe (PID: 3736)
- DllHost.exe (PID: 852)
- DrvInst.exe (PID: 3892)
- DrvInst.exe (PID: 548)
- rundll32.exe (PID: 2300)
- DrvInst.exe (PID: 1332)
- DllHost.exe (PID: 576)
Creates files in the program directory
- DriverUpdater.exe (PID: 1504)
- dpinst32.exe (PID: 3824)
Creates files in the Windows directory
- dpinst32.exe (PID: 3824)
- DrvInst.exe (PID: 3892)
- DrvInst.exe (PID: 548)
Removes files from Windows directory
- DrvInst.exe (PID: 3892)
- DrvInst.exe (PID: 548)
Creates files in the driver directory
- DrvInst.exe (PID: 3892)
- DrvInst.exe (PID: 548)
Reads the BIOS version
- DriverUpdater.exe (PID: 1504)
Creates a software uninstall entry
- dpinst32.exe (PID: 3824)
INFO
Creates a software uninstall entry
- driver-updater-setup.tmp (PID: 3952)
Reads settings of System Certificates
- DriverUpdater.exe (PID: 2660)
- driver-updater-setup.tmp (PID: 3952)
- DriverUpdater.exe (PID: 1504)
Application was dropped or rewritten from another process
- driver-updater-setup.tmp (PID: 4040)
- driver-updater-setup.tmp (PID: 3952)
Loads dropped or rewritten executable
- driver-updater-setup.tmp (PID: 3952)
Creates files in the program directory
- driver-updater-setup.tmp (PID: 3952)
Low-level read access rights to disk partition
- vssvc.exe (PID: 1992)
Changes settings of System certificates
- DrvInst.exe (PID: 3892)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 3892)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (57.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (18.2) |
| .exe | | | Win16/32 Executable Delphi generic (8.3) |
| .exe | | | Generic Win/DOS Executable (8) |
| .exe | | | DOS Executable Generic (8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:06 16:39:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 66560 |
| InitializedDataSize: | 79360 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x117dc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.22.0.2 |
| ProductVersionNumber: | 1.22.0.2 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Auslogics |
| FileDescription: | Auslogics Driver Updater Installation File |
| FileVersion: | 1.x |
| LegalCopyright: | Copyright © 2008-2019 Auslogics Labs Pty Ltd |
| ProductName: | Auslogics Driver Updater |
| ProductVersion: | 1.22.0.2 |
| OriginalFileName: | driver-updater-setup.exe |
| InternalName: | driver-updater-setup |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Apr-2016 14:39:04 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Auslogics |
| FileDescription: | Auslogics Driver Updater Installation File |
| FileVersion: | 1.x |
| LegalCopyright: | Copyright © 2008-2019 Auslogics Labs Pty Ltd |
| ProductName: | Auslogics Driver Updater |
| ProductVersion: | 1.22.0.2 |
| OriginalFilename: | driver-updater-setup.exe |
| InternalName: | driver-updater-setup |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 06-Apr-2016 14:39:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F244 | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37521 |
.itext | 0x00011000 | 0x00000F64 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.7322 |
.data | 0x00012000 | 0x00000C88 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.29672 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x00011588 | 0x00011600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.02795 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.01388 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.07394 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.31982 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.05236 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.5747 | 1736 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 6.07053 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 6.0658 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 3.23334 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 3.59032 | 488 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
63
Monitored processes
19
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 548 | DrvInst.exe "2" "201" "ROOT\UMBUS\0000" "C:\Windows\INF\oem4.inf" "zumbus.inf:Microsoft.NTx86:UmBusRoot_Device:4.8.2148.0:root\umbus" "618607533" "00000338" "000005CC" "000005D0" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 576 | C:\Windows\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 664 | "taskhost.exe" | C:\Windows\system32\taskhost.exe | — | services.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 852 | C:\Windows\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1332 | DrvInst.exe "2" "201" "UMB\UMB\1&841921D&0&PRINTERBUSENUMERATOR" "C:\Windows\INF\oem4.inf" "zumbus.inf:Microsoft.NTx86:UmBus_Device:4.8.2148.0:umb\umbus" "6640409db" "0000032C" "000005D8" "000003B8" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1504 | "C:\Program Files\Auslogics\Driver Updater\DriverUpdater.exe" | C:\Program Files\Auslogics\Driver Updater\DriverUpdater.exe | driver-updater-setup.tmp | ||||||||||||
User: admin Company: Auslogics Integrity Level: HIGH Description: Driver Updater Exit code: 0 Version: 1.22.0.2 Modules
| |||||||||||||||
| 1992 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2300 | C:\Windows\System32\rundll32.exe shell32.dll,SHCreateLocalServerRunDll {995C996E-D918-4a8c-A302-45719A6F4EA7} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2428 | "taskhost.exe" | C:\Windows\system32\taskhost.exe | — | services.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2660 | "C:\Program Files\Auslogics\Driver Updater\DriverUpdater.exe" /install /setautostart | C:\Program Files\Auslogics\Driver Updater\DriverUpdater.exe | driver-updater-setup.tmp | ||||||||||||
User: admin Company: Auslogics Integrity Level: HIGH Description: Driver Updater Exit code: 0 Version: 1.22.0.2 Modules
| |||||||||||||||
Total events
6 692
Read events
4 843
Write events
1 815
Delete events
34
Modification events
| (PID) Process: | (3952) driver-updater-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 700F0000A46DCBC9B7E2D501 | |||
| (PID) Process: | (3952) driver-updater-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 86E90C1D818DDAA61F380ECC982FFA9AD0DF138C84CBCA9C89C6E27395E7D2E0 | |||
| (PID) Process: | (3952) driver-updater-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3952) driver-updater-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Auslogics\Driver Updater\1.x\Settings |
| Operation: | write | Name: | General.Tracking.URLMarkers |
Value: driverupdaternosid | |||
| (PID) Process: | (3952) driver-updater-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Auslogics\Driver Updater\1.x\Settings |
| Operation: | write | Name: | General.Language |
Value: ENU | |||
| (PID) Process: | (3952) driver-updater-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Auslogics |
| Operation: | write | Name: | ClientID |
Value: {1468B952-C795-4D6E-BF41-644C96C1DEB6} | |||
| (PID) Process: | (3952) driver-updater-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3952) driver-updater-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3952) driver-updater-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3952) driver-updater-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
45
Suspicious files
50
Text files
516
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3952 | driver-updater-setup.tmp | C:\Users\admin\AppData\Local\Temp\is-0OD2J.tmp\CFAHelper.dll | executable | |
MD5:— | SHA256:— | |||
| 3952 | driver-updater-setup.tmp | C:\Users\admin\AppData\Local\Temp\is-0OD2J.tmp\Localizer.dll | executable | |
MD5:— | SHA256:— | |||
| 3952 | driver-updater-setup.tmp | C:\Users\admin\AppData\Local\Temp\is-0OD2J.tmp\main.ini | text | |
MD5:— | SHA256:— | |||
| 3952 | driver-updater-setup.tmp | C:\Users\admin\AppData\Local\Temp\is-0OD2J.tmp\AxComponentsRTL.bpl | executable | |
MD5:— | SHA256:— | |||
| 3952 | driver-updater-setup.tmp | C:\Users\admin\AppData\Local\Temp\is-0OD2J.tmp\deu.lng | binary | |
MD5:— | SHA256:— | |||
| 3952 | driver-updater-setup.tmp | C:\Program Files\Auslogics\Driver Updater\is-CTG8V.tmp | — | |
MD5:— | SHA256:— | |||
| 2860 | driver-updater-setup.exe | C:\Users\admin\AppData\Local\Temp\is-JM4OV.tmp\driver-updater-setup.tmp | executable | |
MD5:— | SHA256:— | |||
| 3952 | driver-updater-setup.tmp | C:\Program Files\Auslogics\Driver Updater\is-Q1010.tmp | — | |
MD5:— | SHA256:— | |||
| 3952 | driver-updater-setup.tmp | C:\Users\admin\AppData\Local\Temp\is-0OD2J.tmp\esp.lng | binary | |
MD5:— | SHA256:— | |||
| 3952 | driver-updater-setup.tmp | C:\Program Files\Auslogics\Driver Updater\Lang\is-94LIG.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
150
TCP/UDP connections
13
DNS requests
8
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1504 | DriverUpdater.exe | HEAD | 200 | 192.155.86.205:80 | http://ads.auslogics.com/uploads/fd3d3998e1afd4ec0b76f1e14668c203.png | US | — | — | whitelisted |
1504 | DriverUpdater.exe | HEAD | 200 | 192.155.86.205:80 | http://ads.auslogics.com/uploads/fcc3710e71ffbcda297c9dff5d62c4bf.png | US | — | — | whitelisted |
1504 | DriverUpdater.exe | HEAD | 200 | 192.155.86.205:80 | http://ads.auslogics.com/uploads/3d05ebedf8b5b24d255918e2a1a139af.png | US | — | — | whitelisted |
1504 | DriverUpdater.exe | HEAD | 200 | 192.155.86.205:80 | http://ads.auslogics.com/uploads/17aa519a4aed70882a74a9f9982ccc8e.png | US | — | — | whitelisted |
1504 | DriverUpdater.exe | HEAD | 200 | 192.155.86.205:80 | http://ads.auslogics.com/uploads/bf11d4822c024e6783715b218ffff527.png | US | — | — | whitelisted |
1504 | DriverUpdater.exe | HEAD | 200 | 192.155.86.205:80 | http://ads.auslogics.com/uploads/179b7e32b1d1cad171f837d5fab6c5ee.png | US | — | — | whitelisted |
1504 | DriverUpdater.exe | HEAD | 200 | 192.155.86.205:80 | http://ads.auslogics.com/uploads/83bb8664bcbba05a69bb303e82a55175.png | US | — | — | whitelisted |
1504 | DriverUpdater.exe | HEAD | 200 | 192.155.86.205:80 | http://ads.auslogics.com/uploads/5e9720270d36130022d468d2e8e49bfa.png | US | — | — | whitelisted |
1504 | DriverUpdater.exe | HEAD | 200 | 192.155.86.205:80 | http://ads.auslogics.com/uploads/2a708241631bc11fff3060b0763355d9.png | US | — | — | whitelisted |
1504 | DriverUpdater.exe | HEAD | 200 | 192.155.86.205:80 | http://ads.auslogics.com/uploads/3de84a09f2c21b700de3ee1c1cf9d2f9.png | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1504 | DriverUpdater.exe | 192.155.86.205:443 | ads.auslogics.com | Linode, LLC | US | malicious |
1504 | DriverUpdater.exe | 143.204.208.24:80 | files.driverhive.com | — | US | suspicious |
3952 | driver-updater-setup.tmp | 172.217.16.142:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
3952 | driver-updater-setup.tmp | 45.79.82.237:443 | www.auslogics.com | Linode, LLC | US | malicious |
3952 | driver-updater-setup.tmp | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2660 | DriverUpdater.exe | 172.217.16.142:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
1504 | DriverUpdater.exe | 45.79.82.237:443 | www.auslogics.com | Linode, LLC | US | malicious |
1504 | DriverUpdater.exe | 192.155.86.205:80 | ads.auslogics.com | Linode, LLC | US | malicious |
1504 | DriverUpdater.exe | 52.200.144.234:80 | ws.driverhive.com | Amazon.com, Inc. | US | unknown |
1504 | DriverUpdater.exe | 172.217.16.142:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google-analytics.com |
| whitelisted |
www.auslogics.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
status.rapidssl.com |
| shared |
ads.auslogics.com |
| whitelisted |
ws.driverhive.com |
| unknown |
files.driverhive.com |
| whitelisted |
debuglogs.auslogics.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1504 | DriverUpdater.exe | Potentially Bad Traffic | ET INFO Suspicious Mozilla User-Agent - Likely Fake (Mozilla/4.0) |
4 ETPRO signatures available at the full report
Process | Message |
|---|---|
DriverUpdater.exe | Executable: C:\Program Files\Auslogics\Driver Updater\DriverUpdater.exe
|
DriverUpdater.exe | Begin logger initialization...
|
DriverUpdater.exe | Initializing thread ID = 0xF94 - Context: DriverHiveEngine - entry point
|
DriverUpdater.exe | [2020-02-13 21:52:27:677] [dhEngineInit] Machine Key: {0A02F2B5-5C0C-43A8-9B2B-3978D2C3F0C3}
|
DriverUpdater.exe | [2020-02-13 21:52:27:677] [dhEngineInit] Allow unsigned drivers: FALSE
|
DriverUpdater.exe | End logger initialization
|
DriverUpdater.exe | [2020-02-13 21:52:27:677] [dhEngineInit] Default Locale ID: 1033
|
DriverUpdater.exe | EL not enabled
|
DriverUpdater.exe | Maximum filesize set to 4194304 bytes
|
DriverUpdater.exe | [2020-02-13 21:52:27:677] [dhEngineInit] Windows version: 6.1.7601 Platform: 2
|