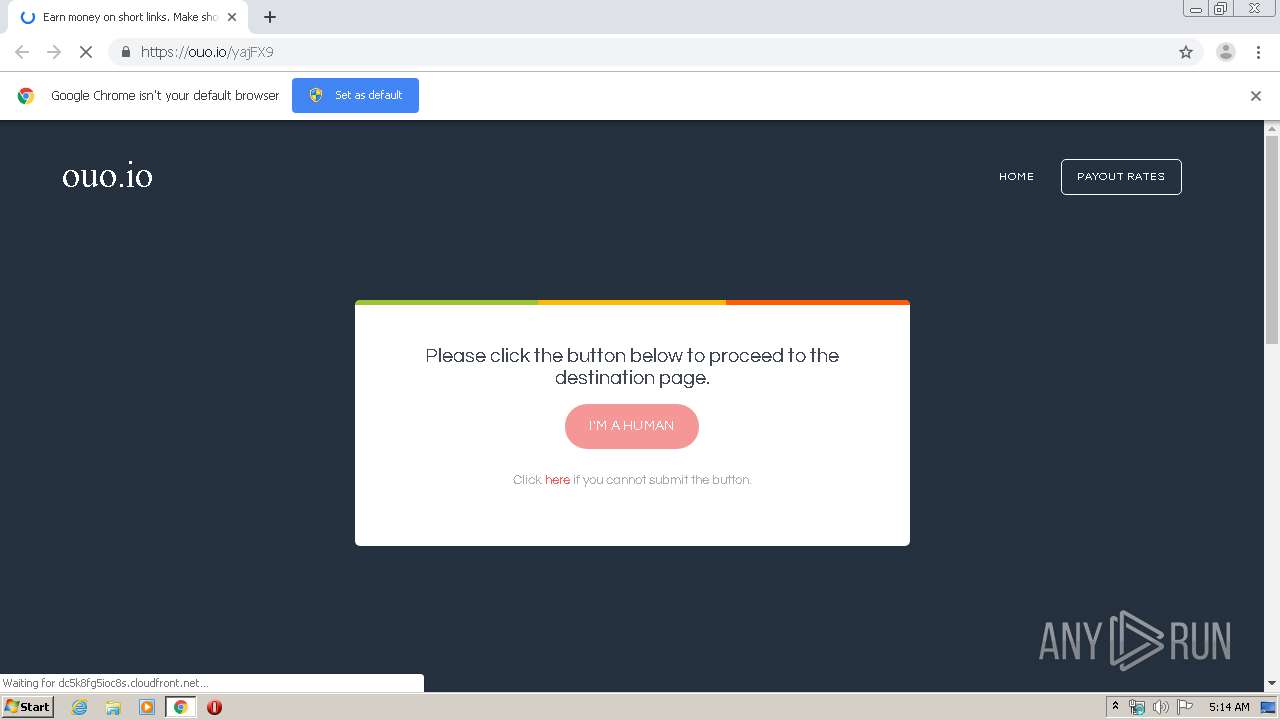
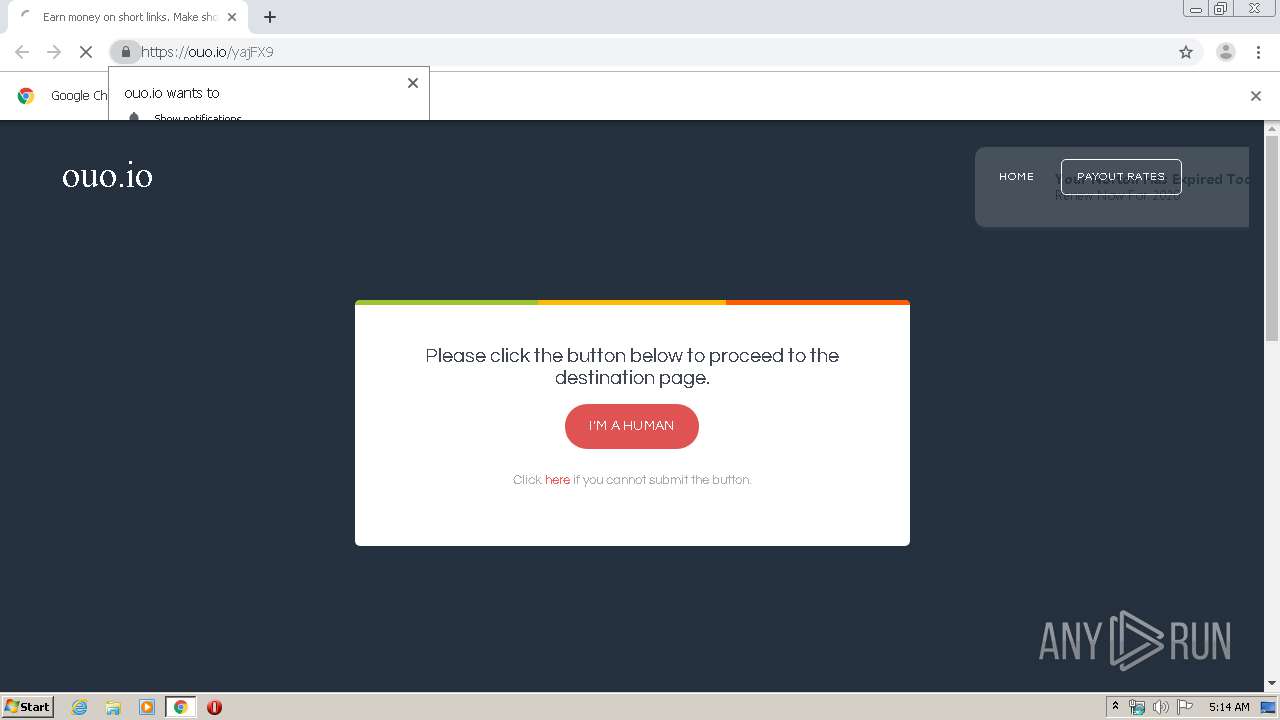
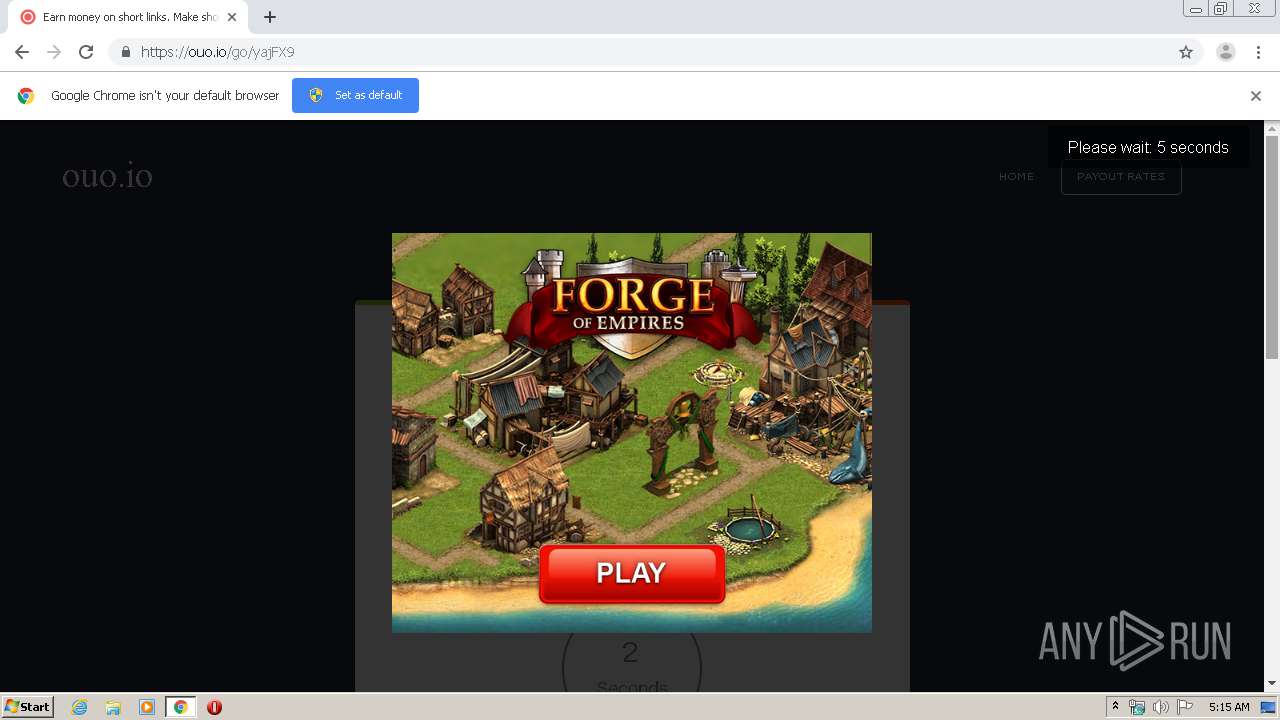
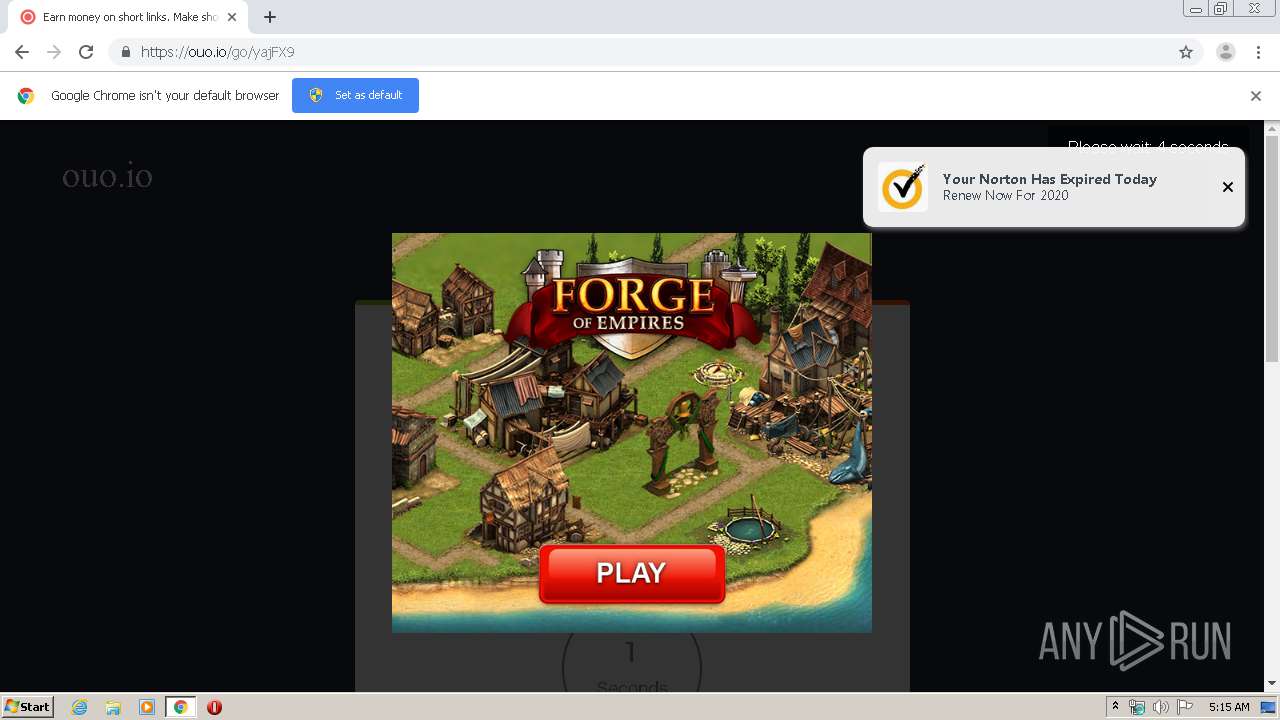
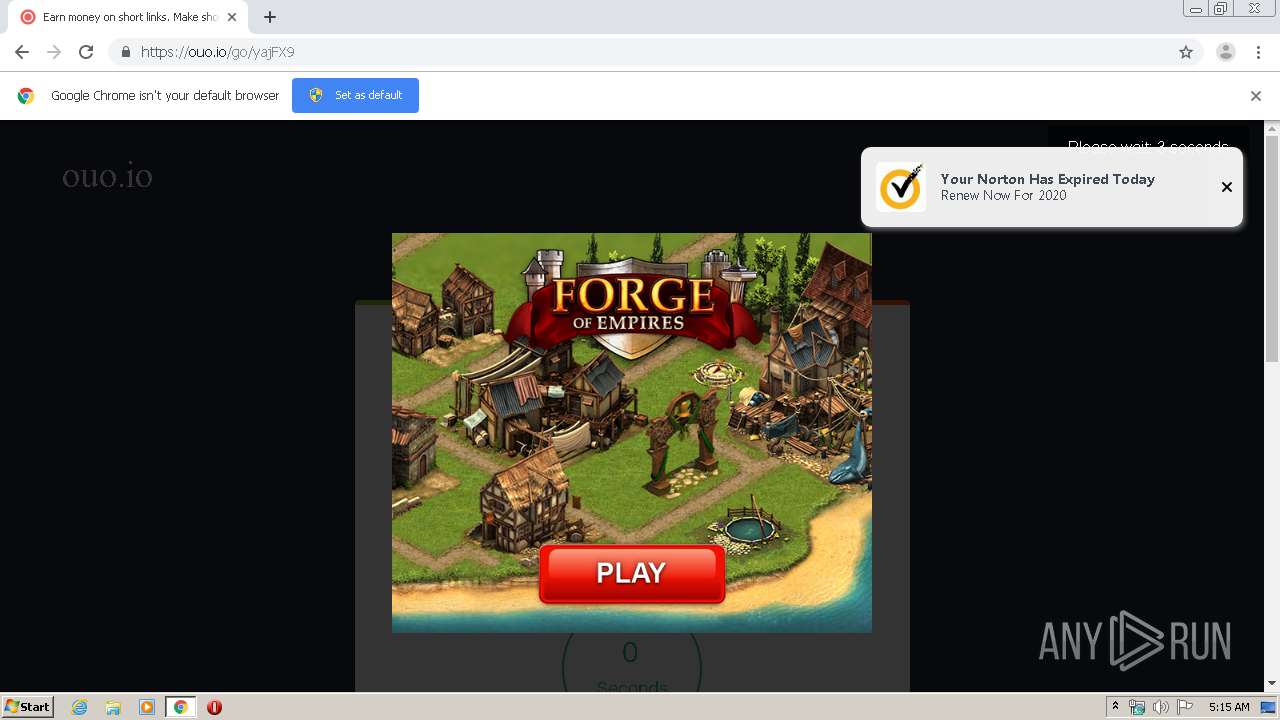
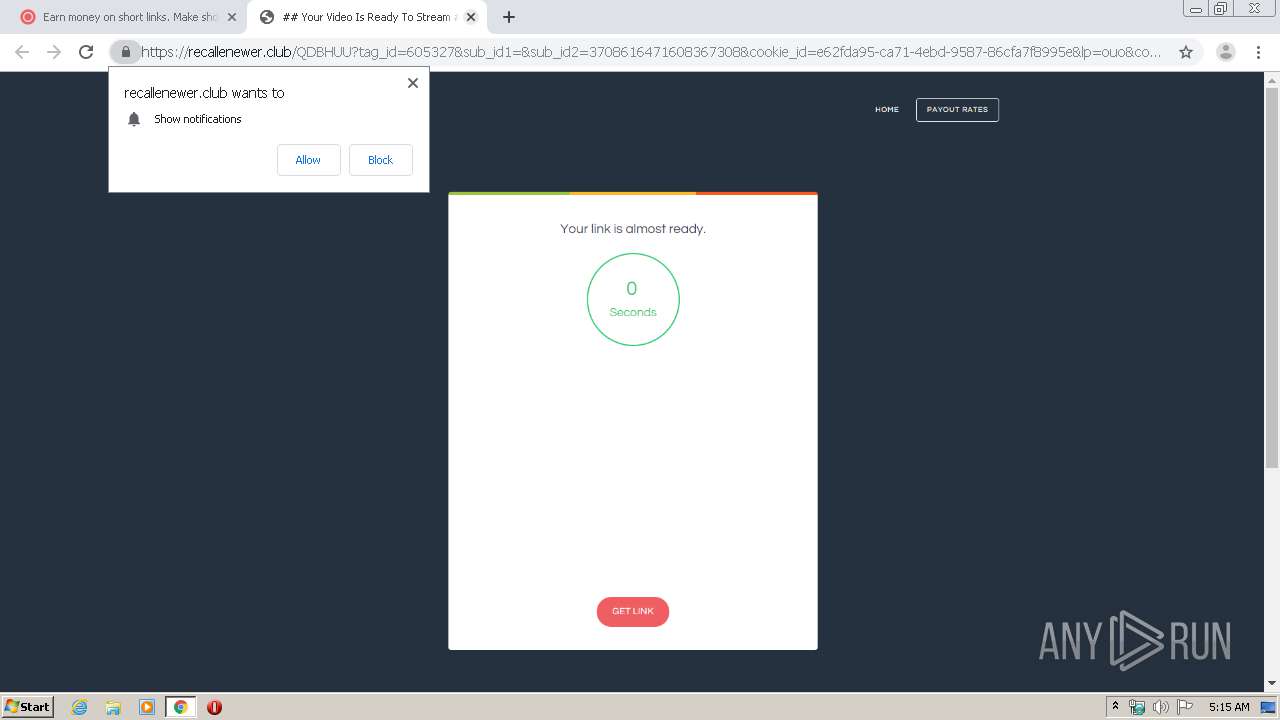
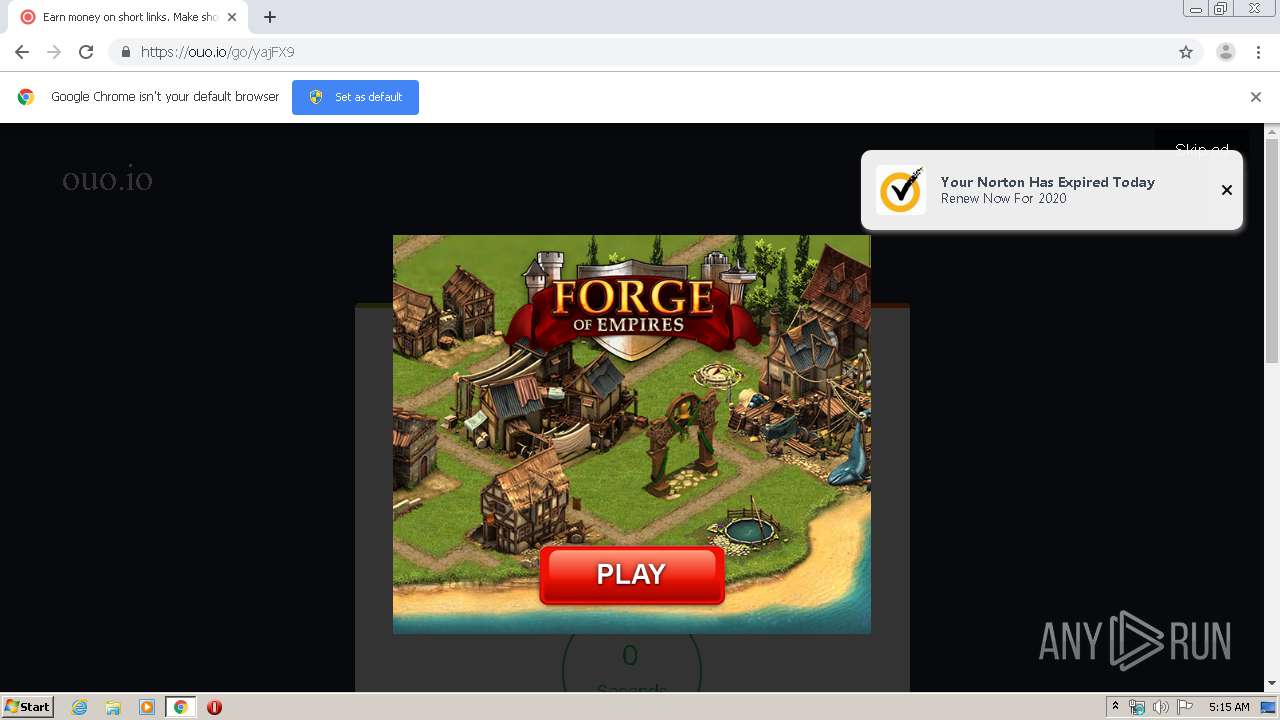
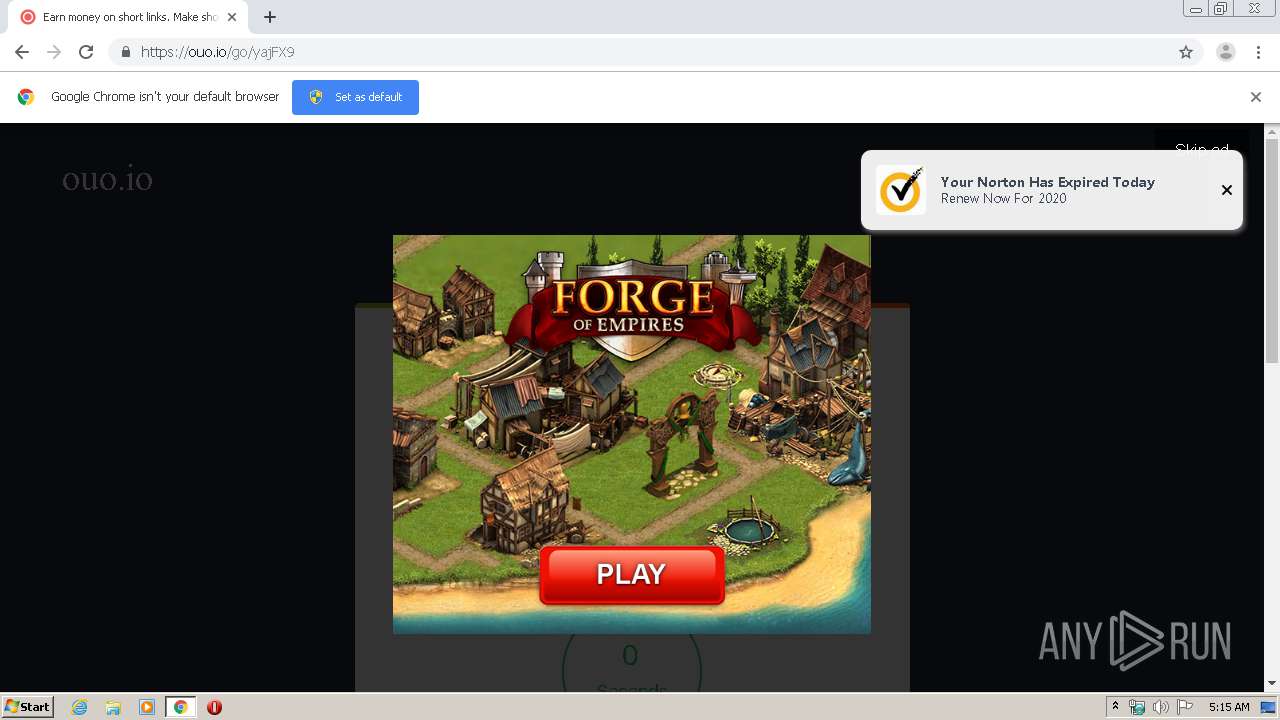
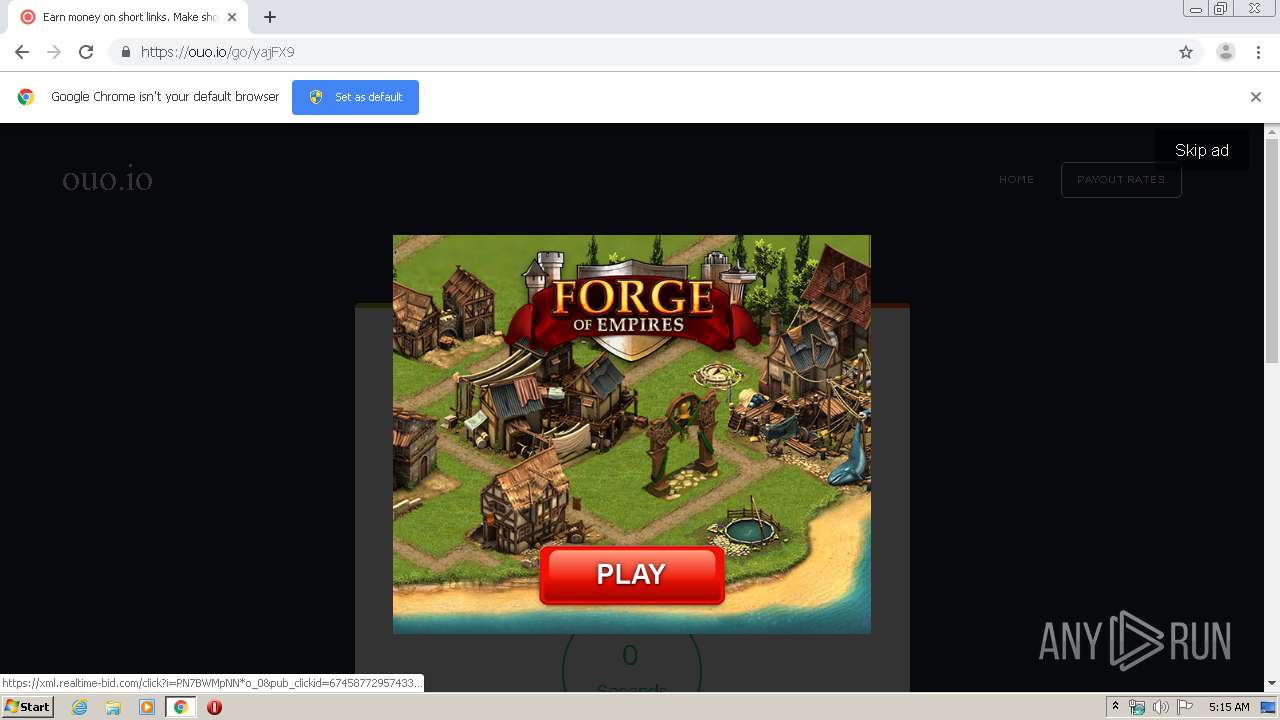
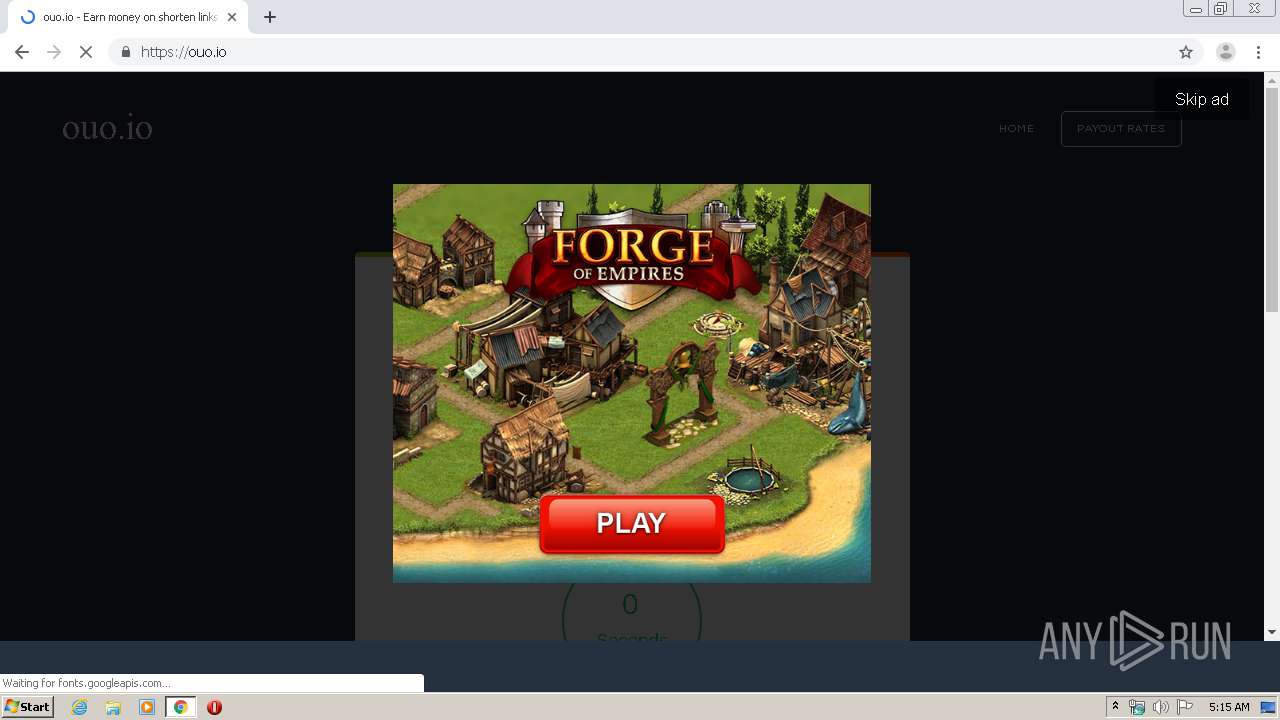
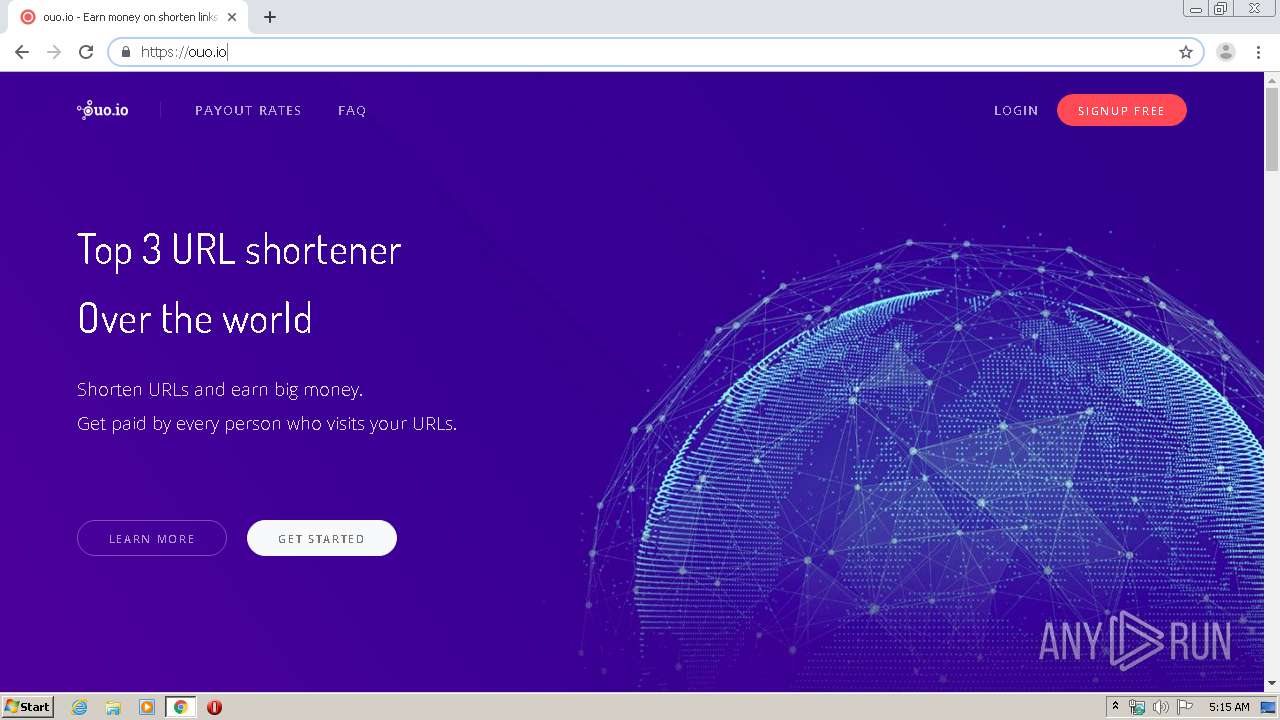
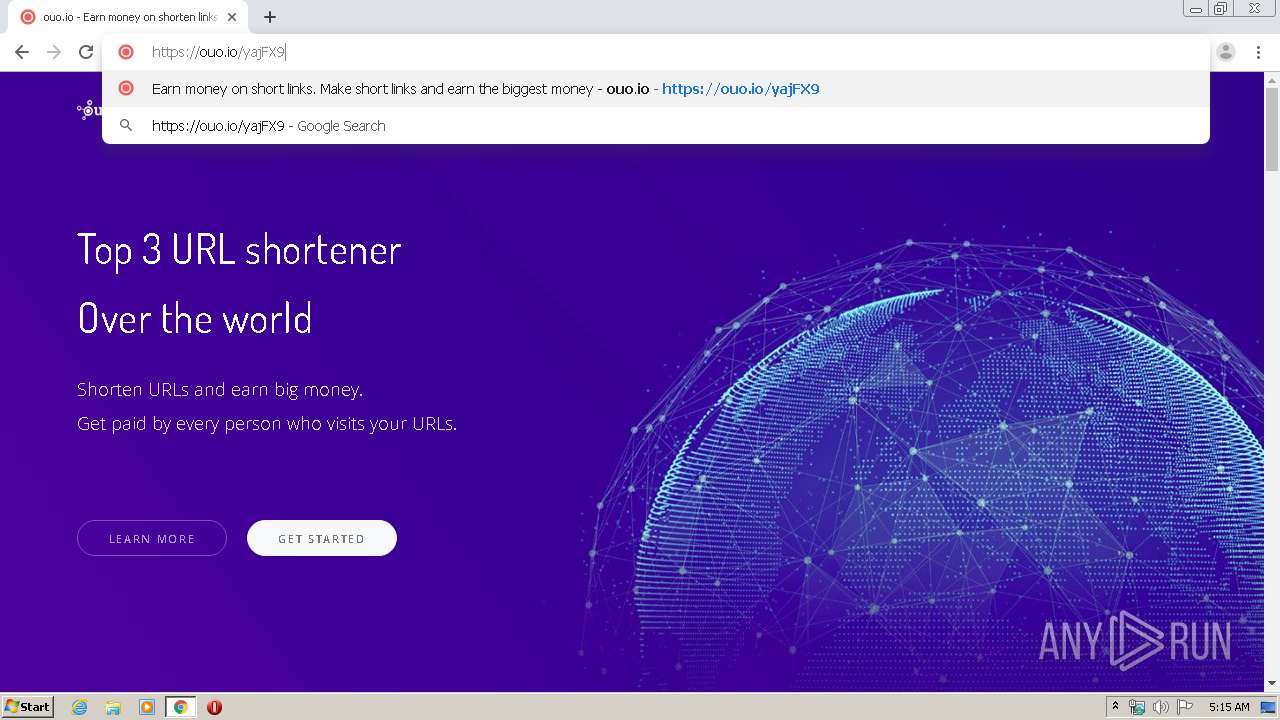
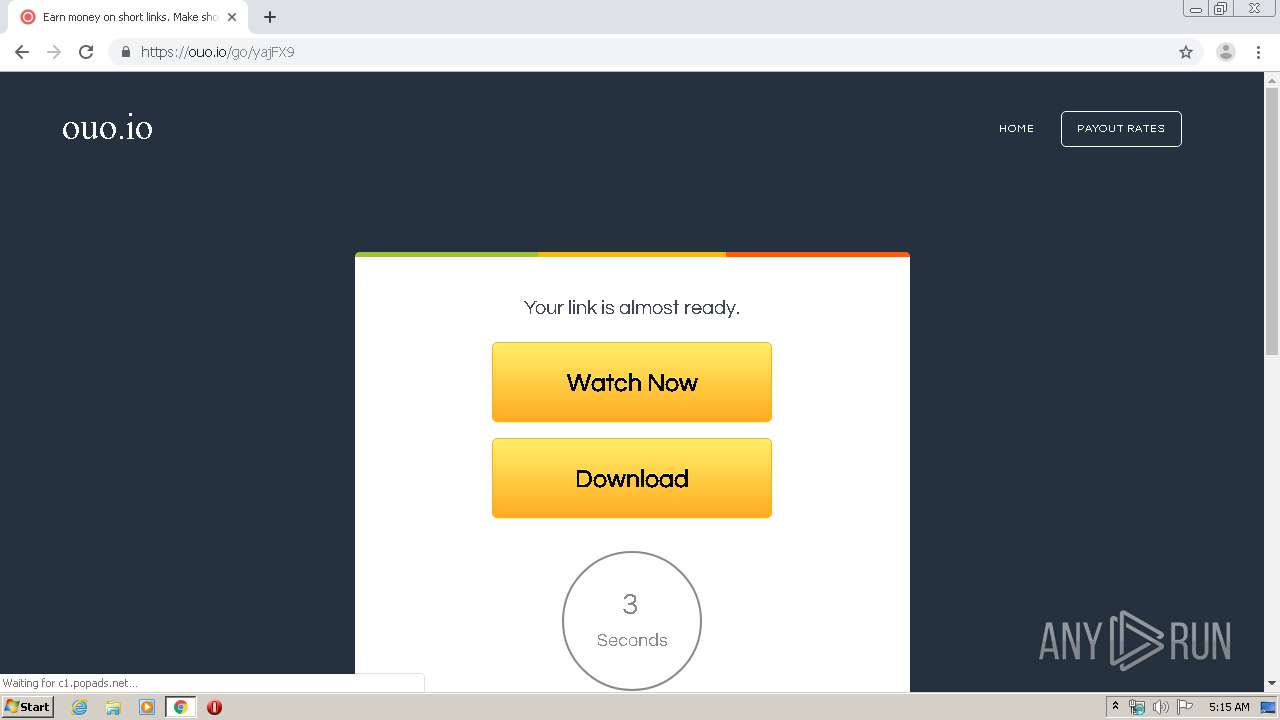
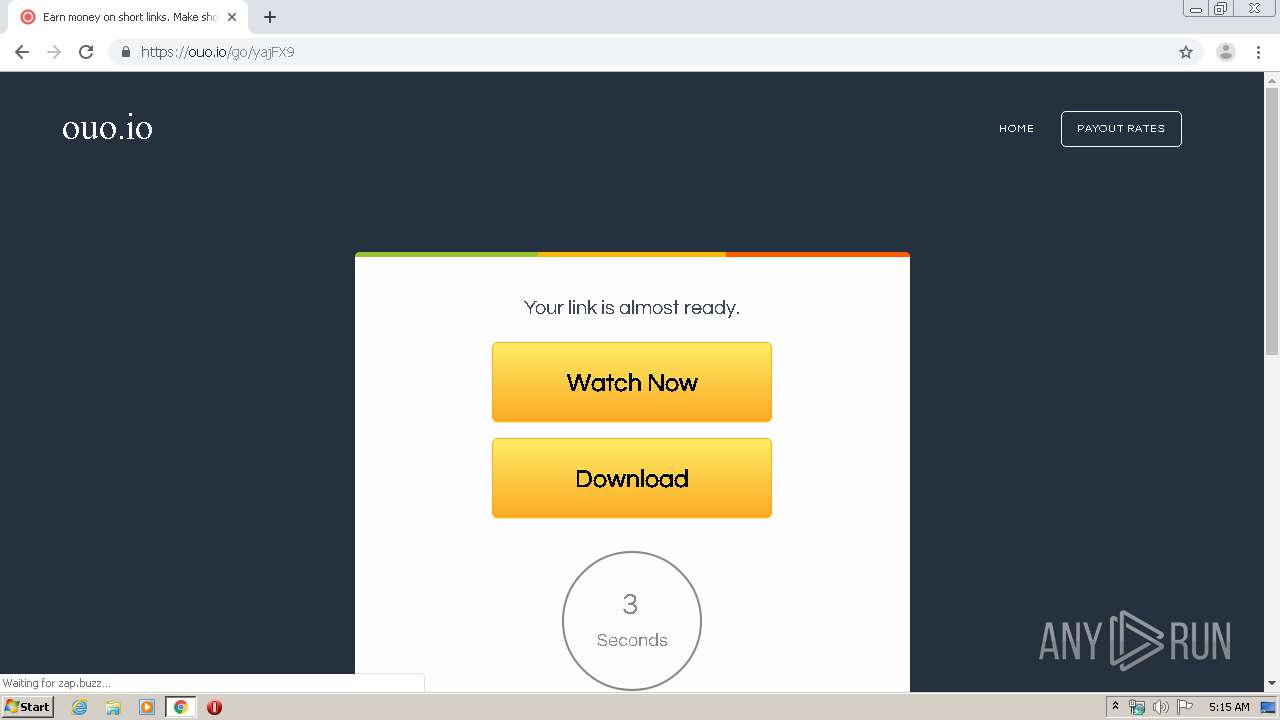
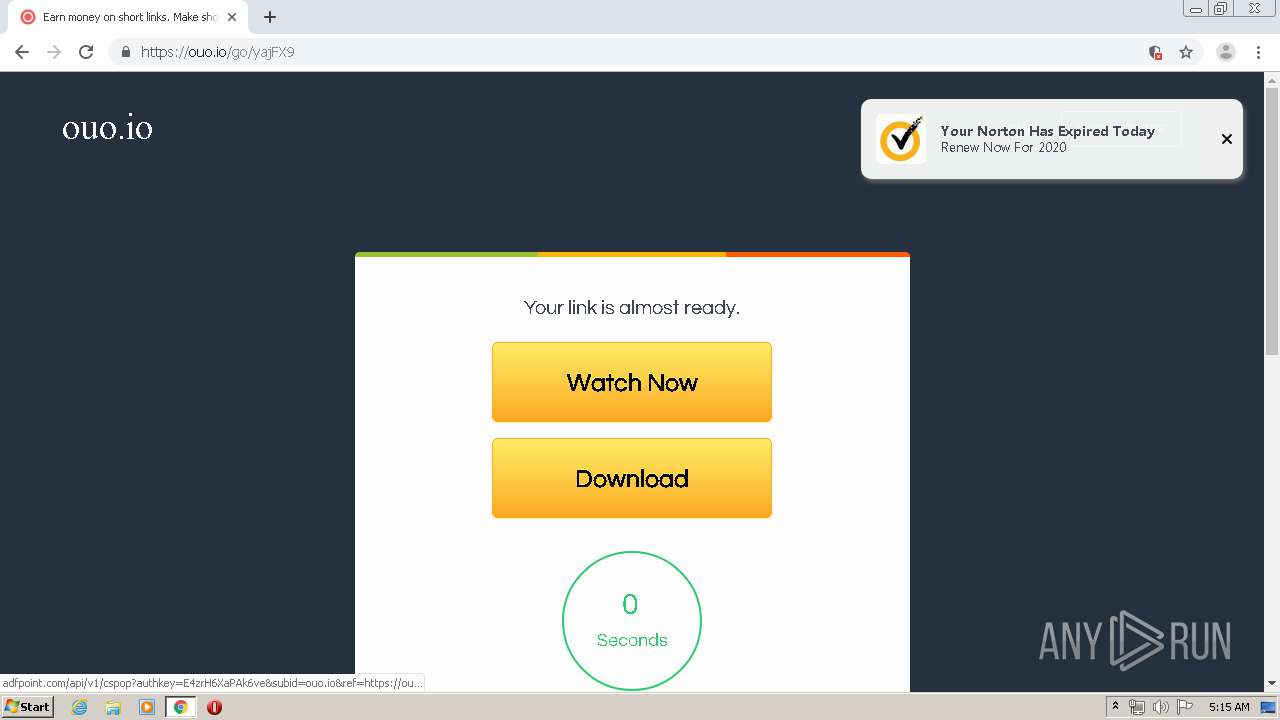
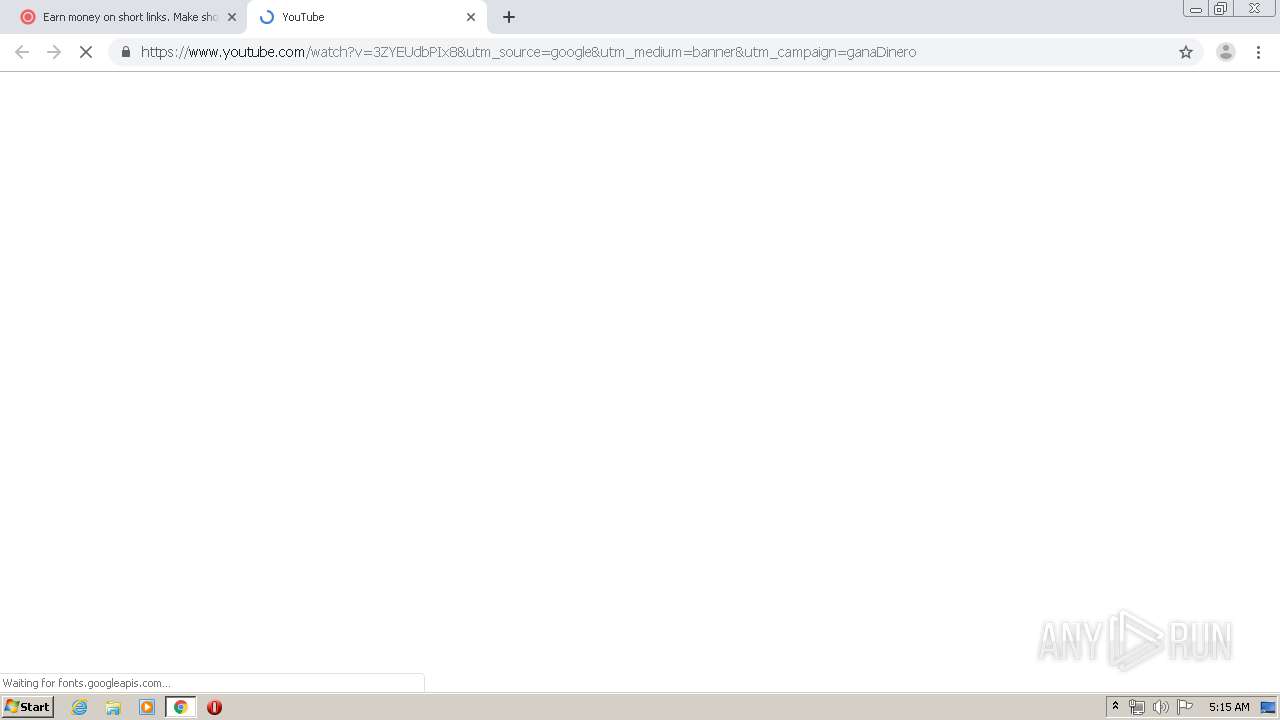
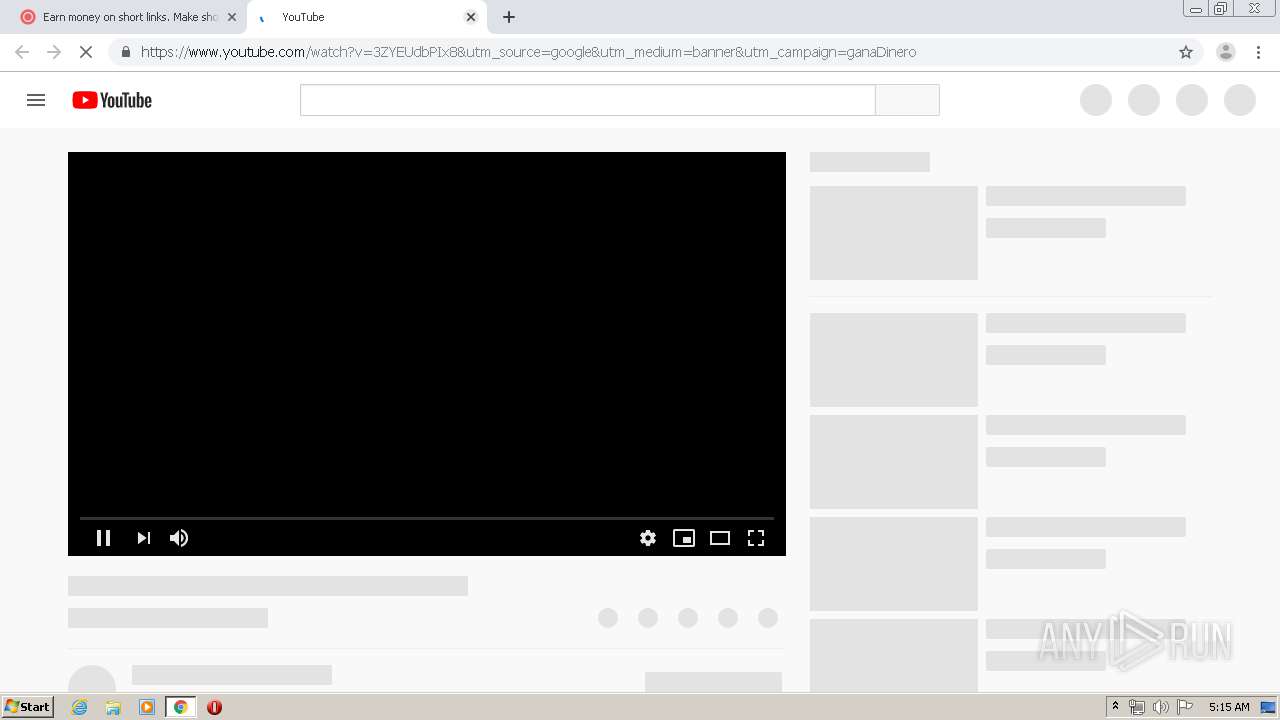
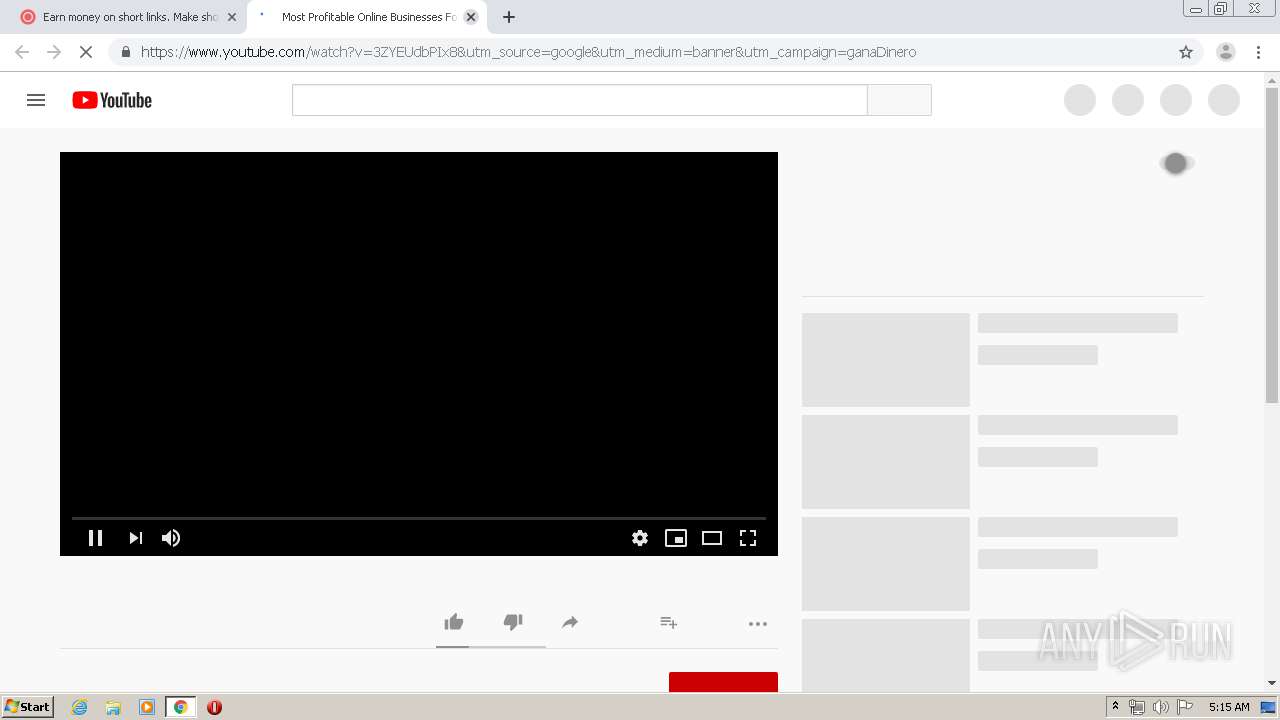
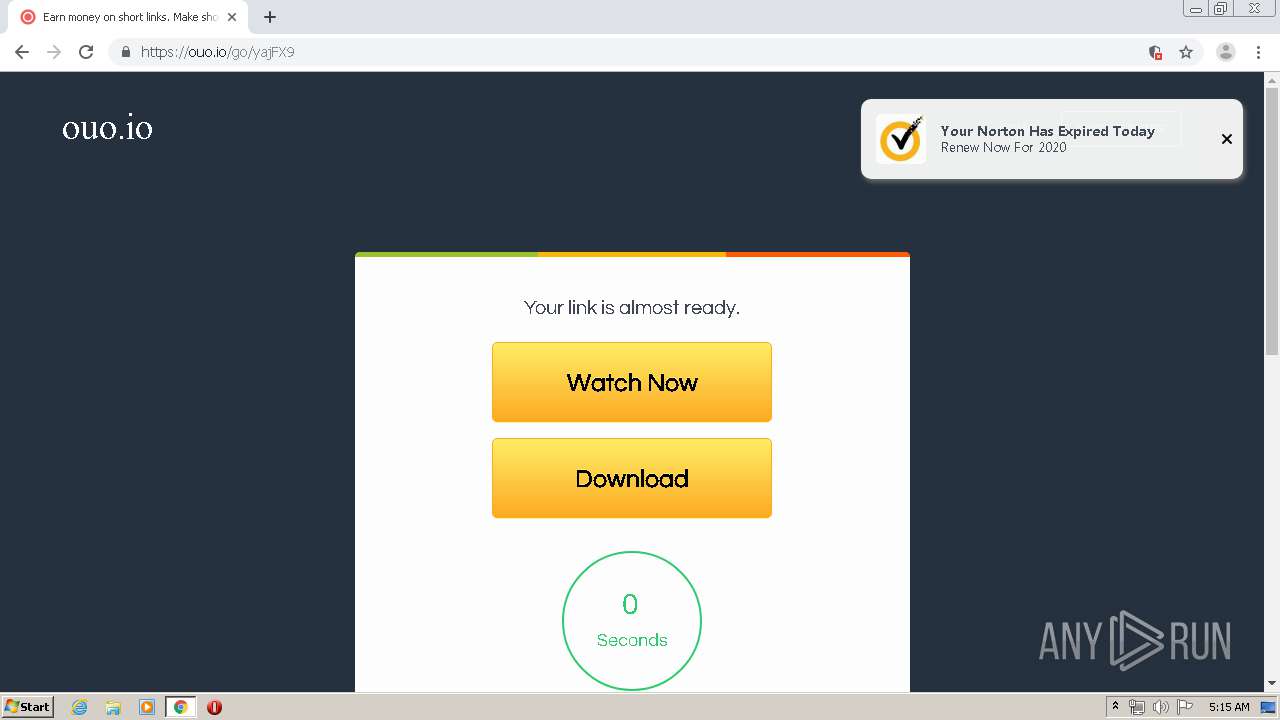
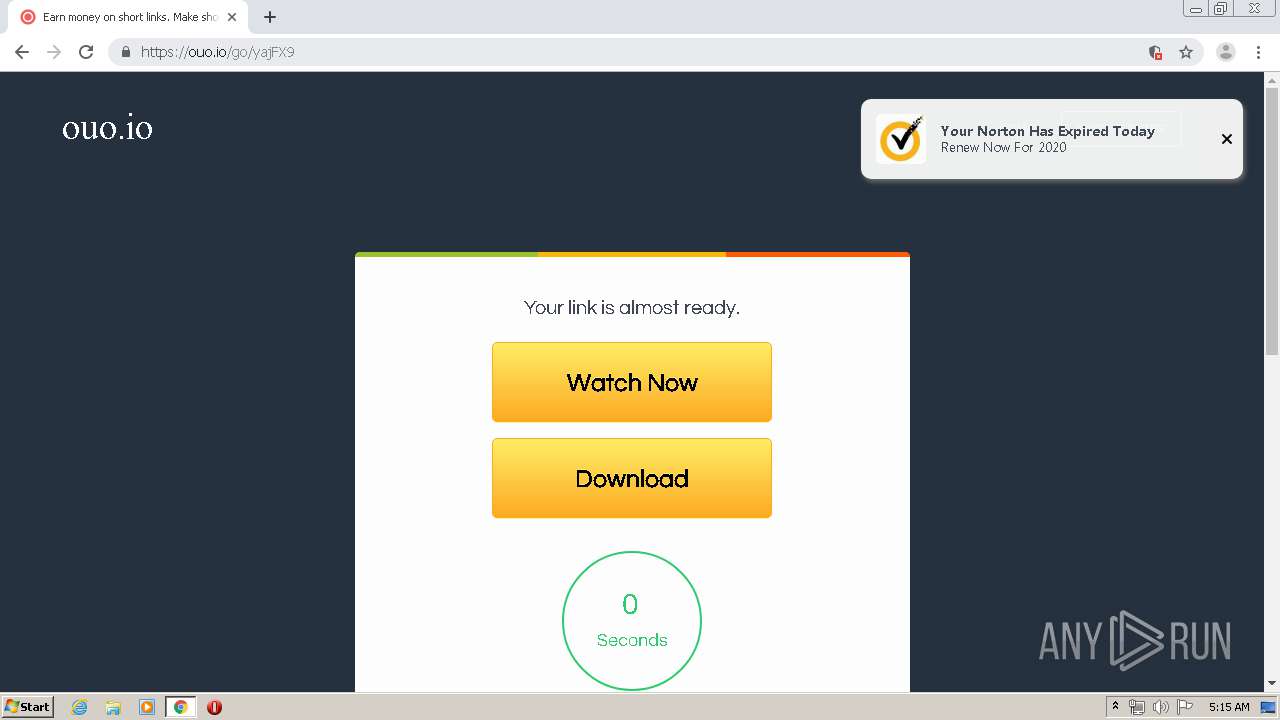
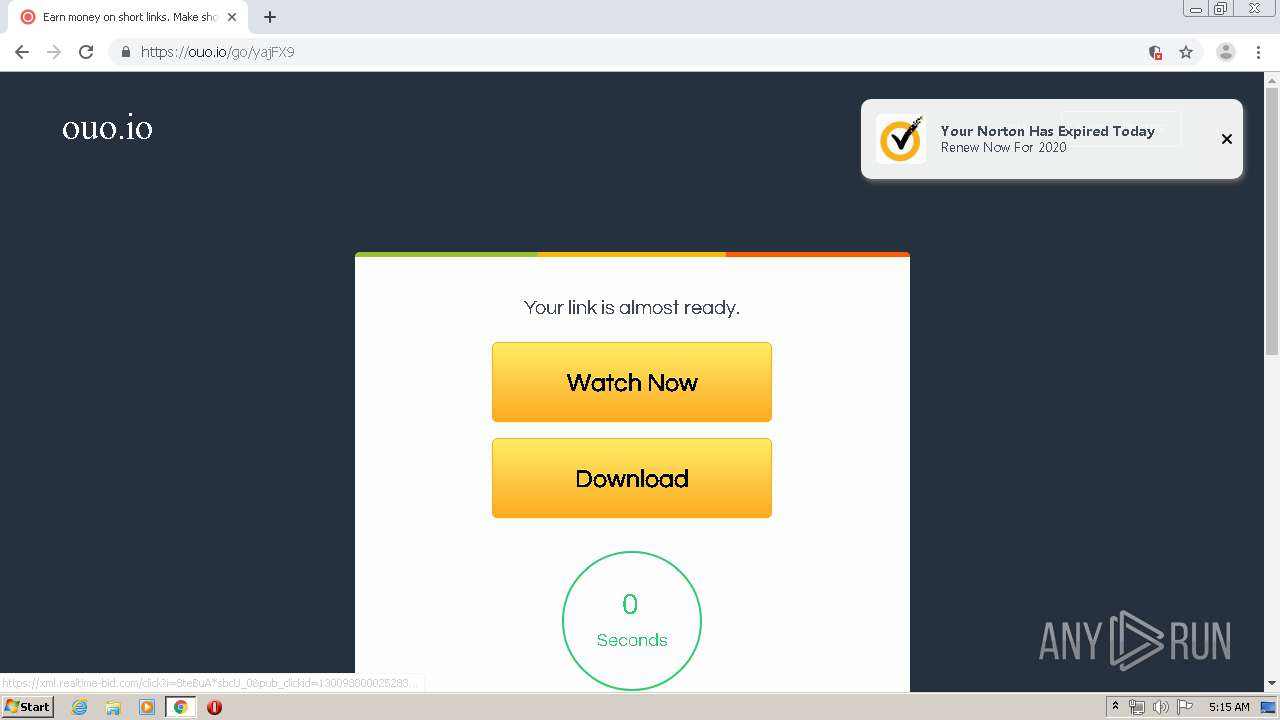
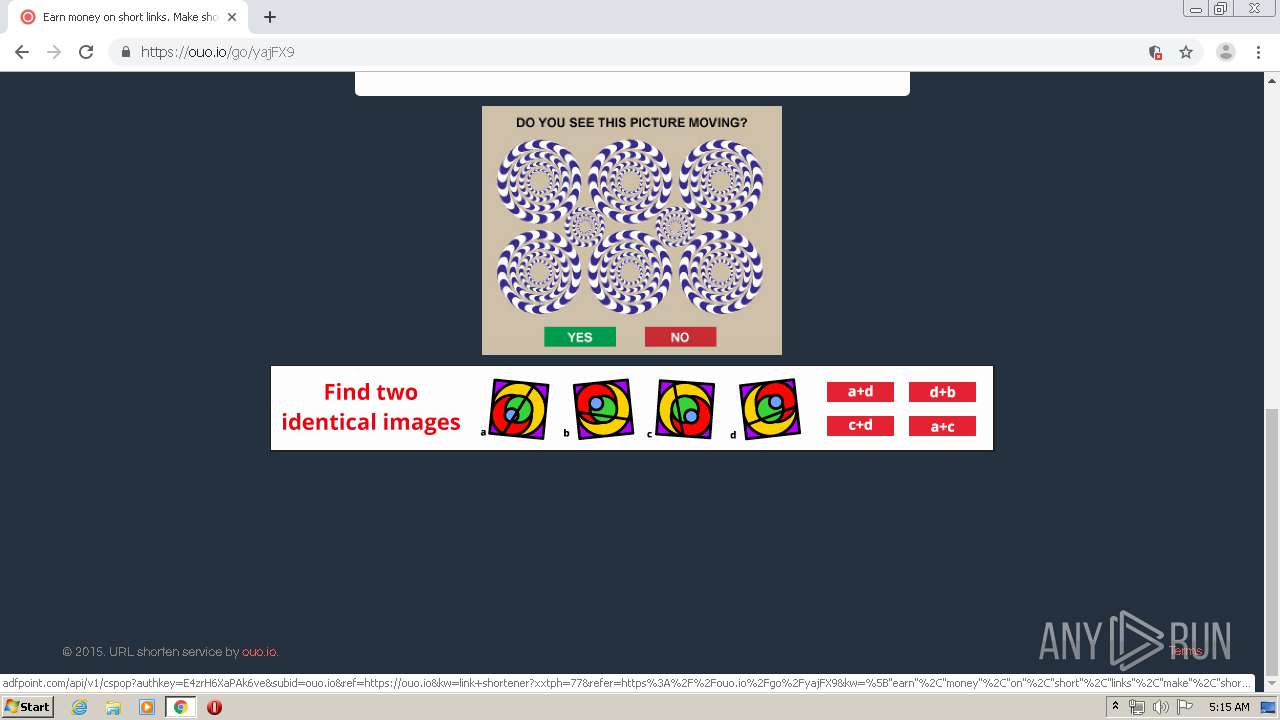
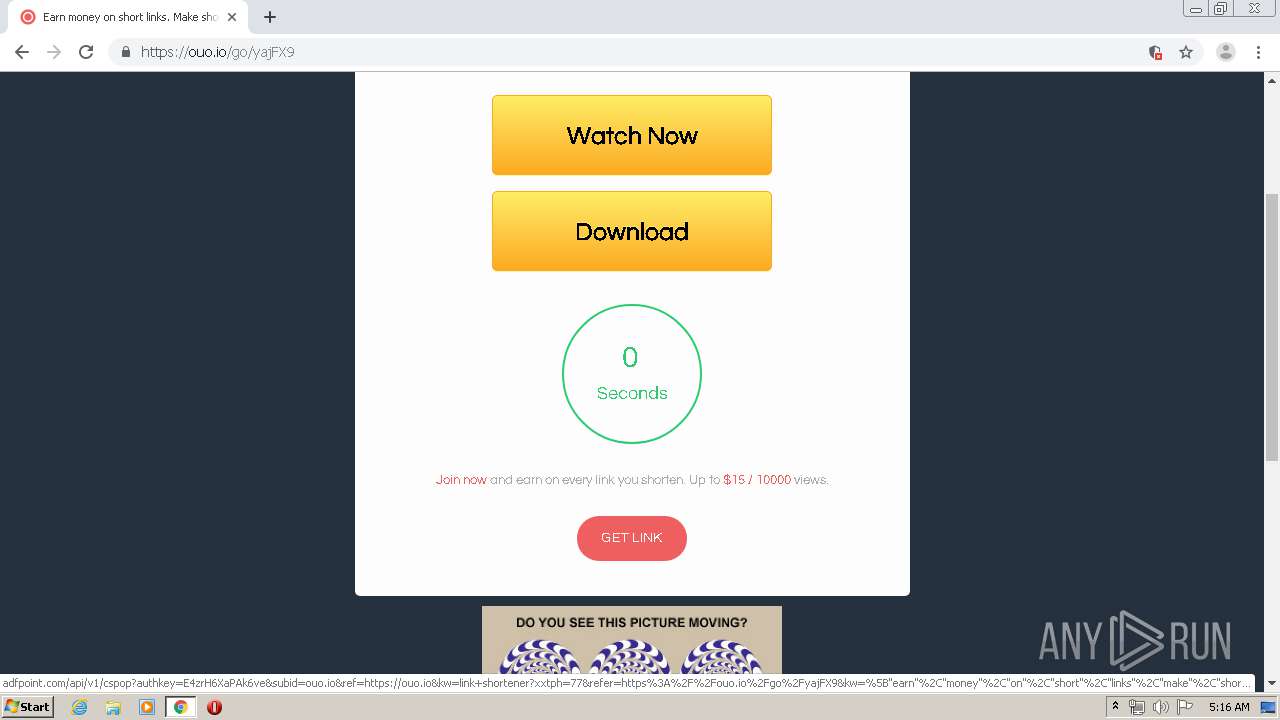
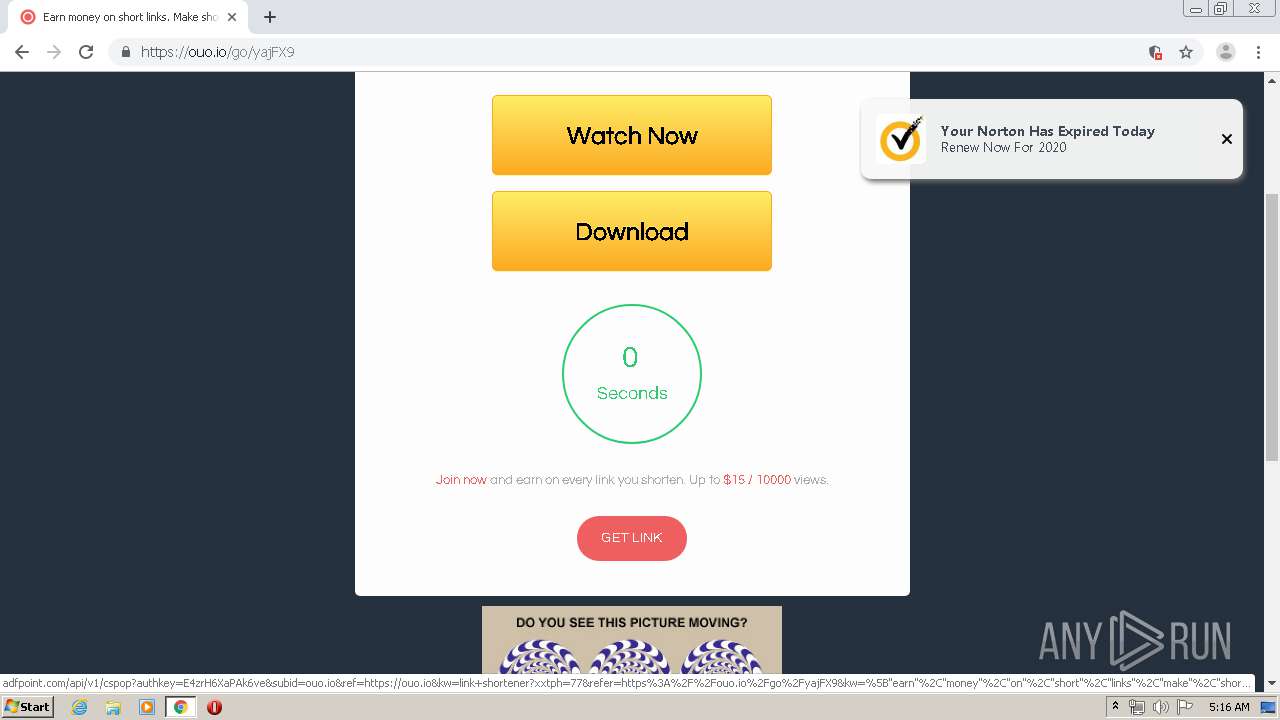
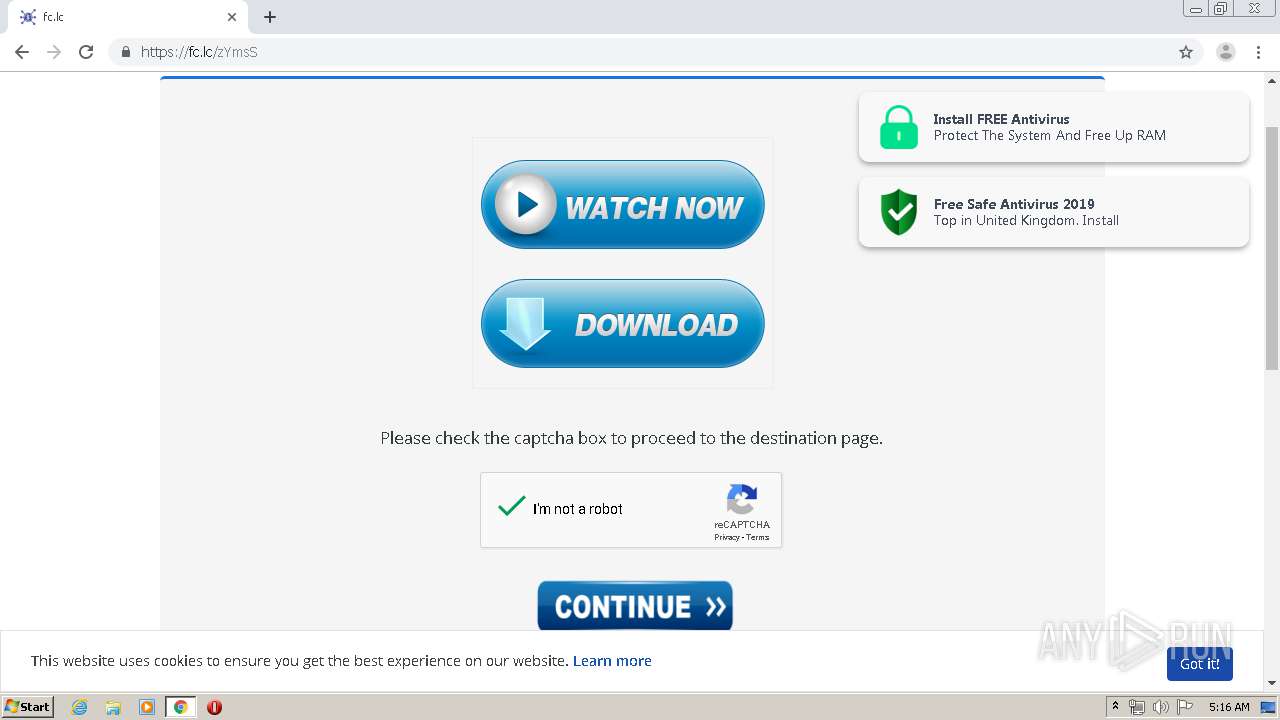
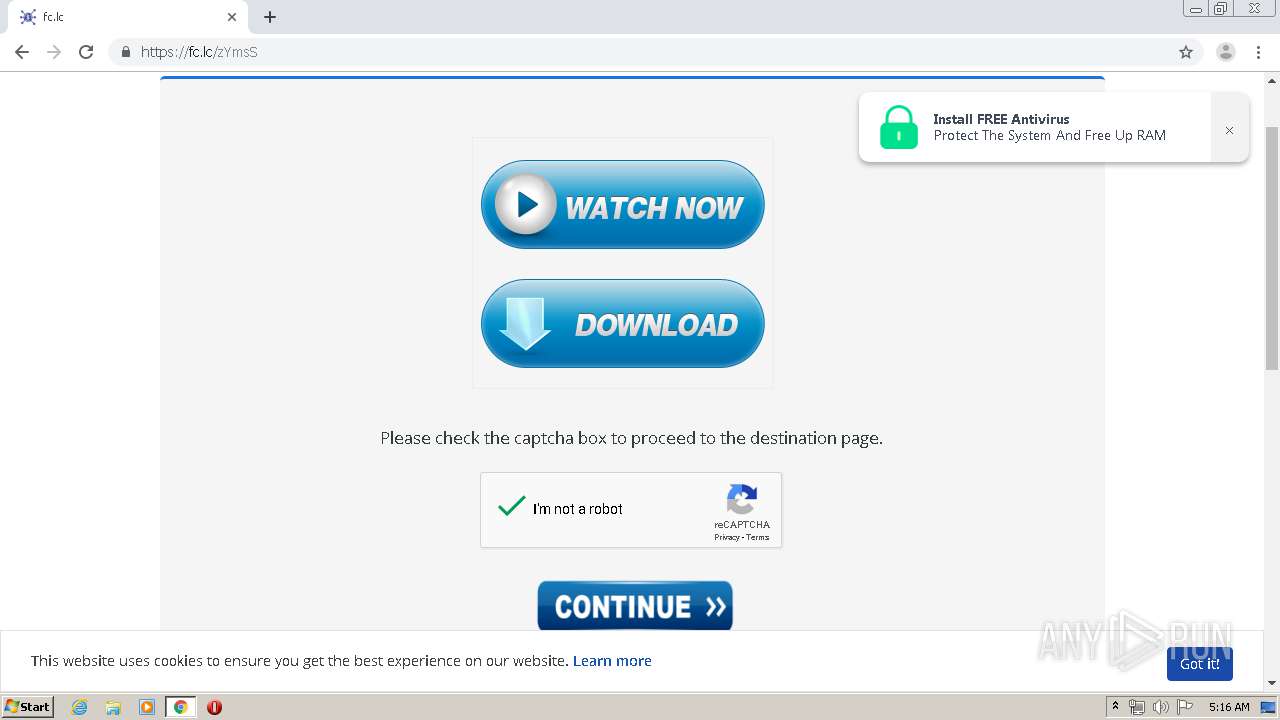
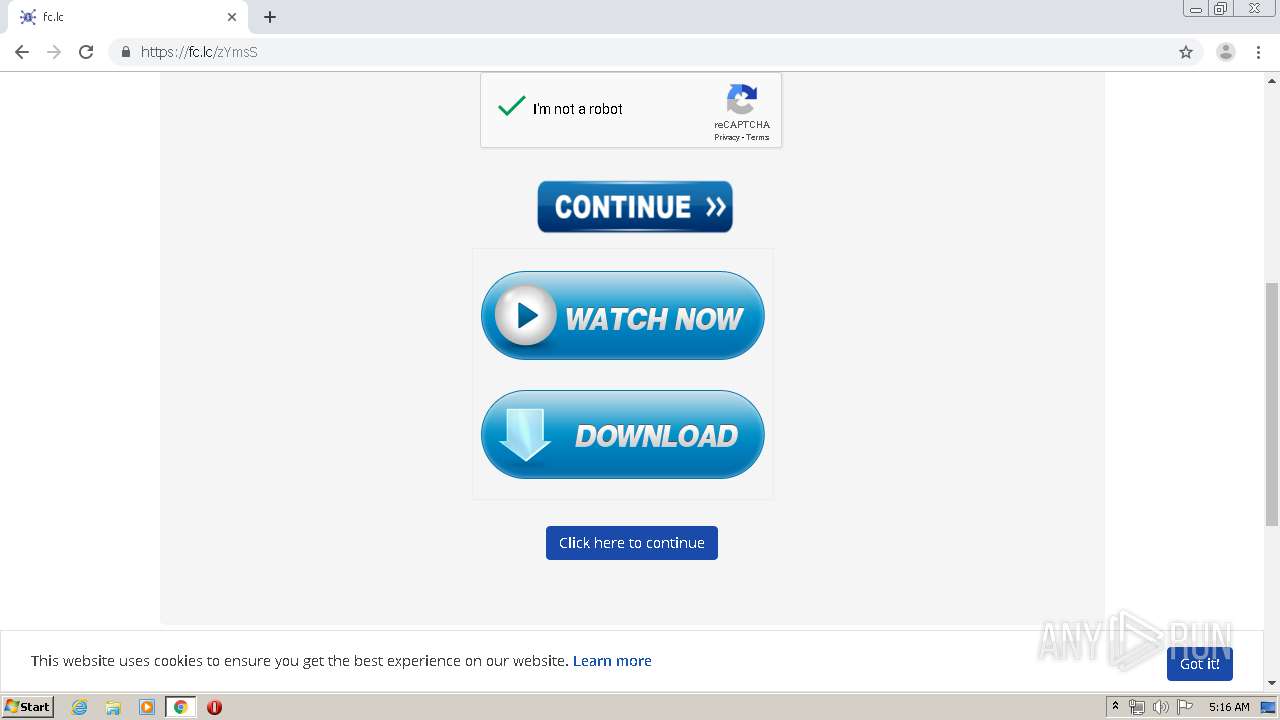
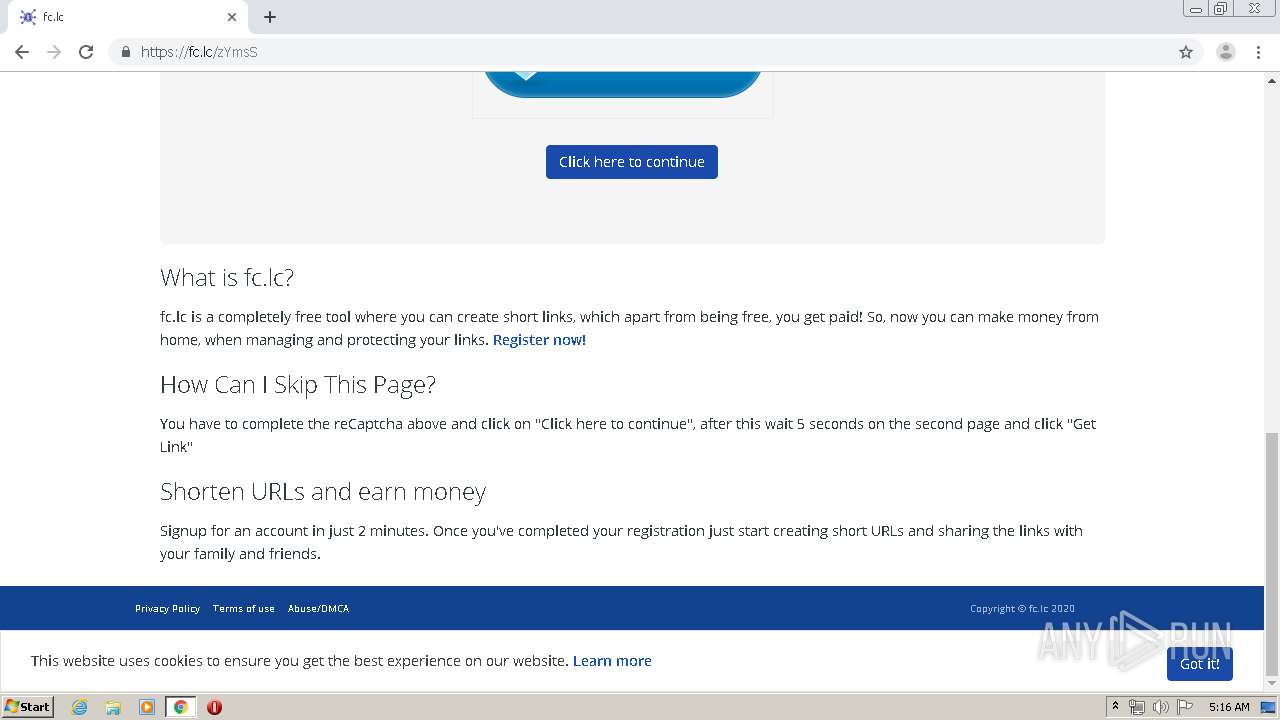
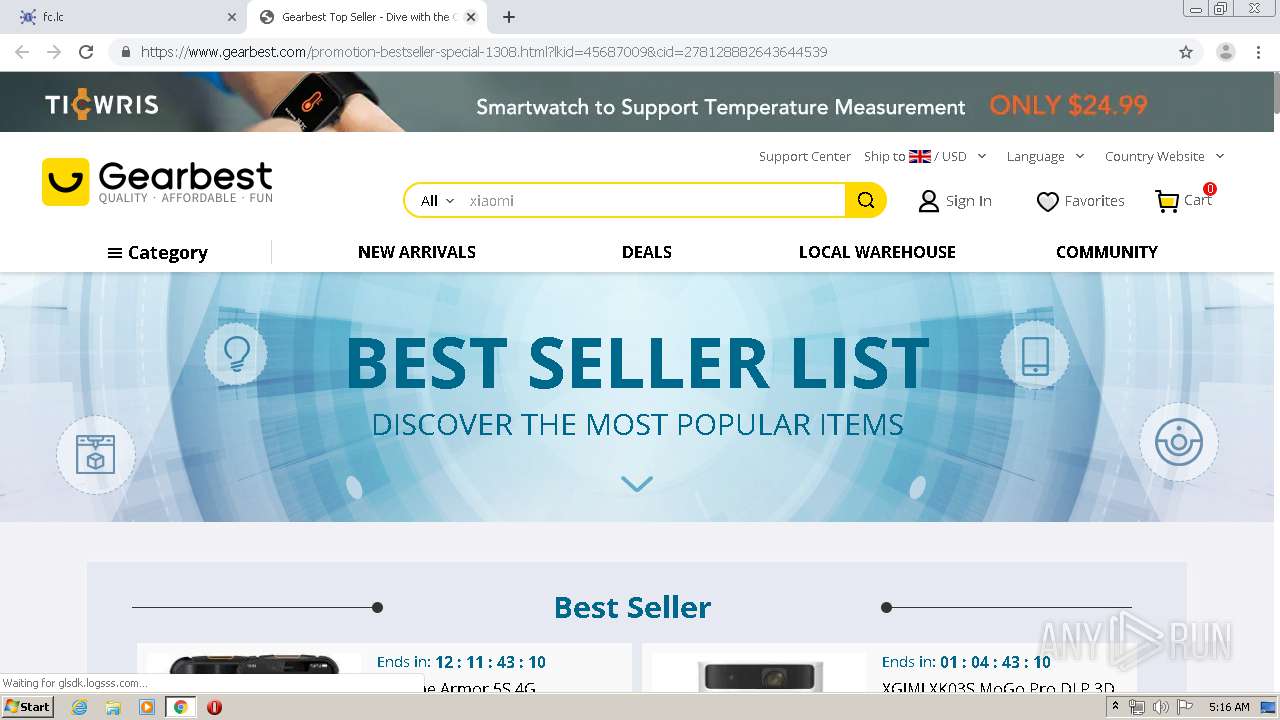
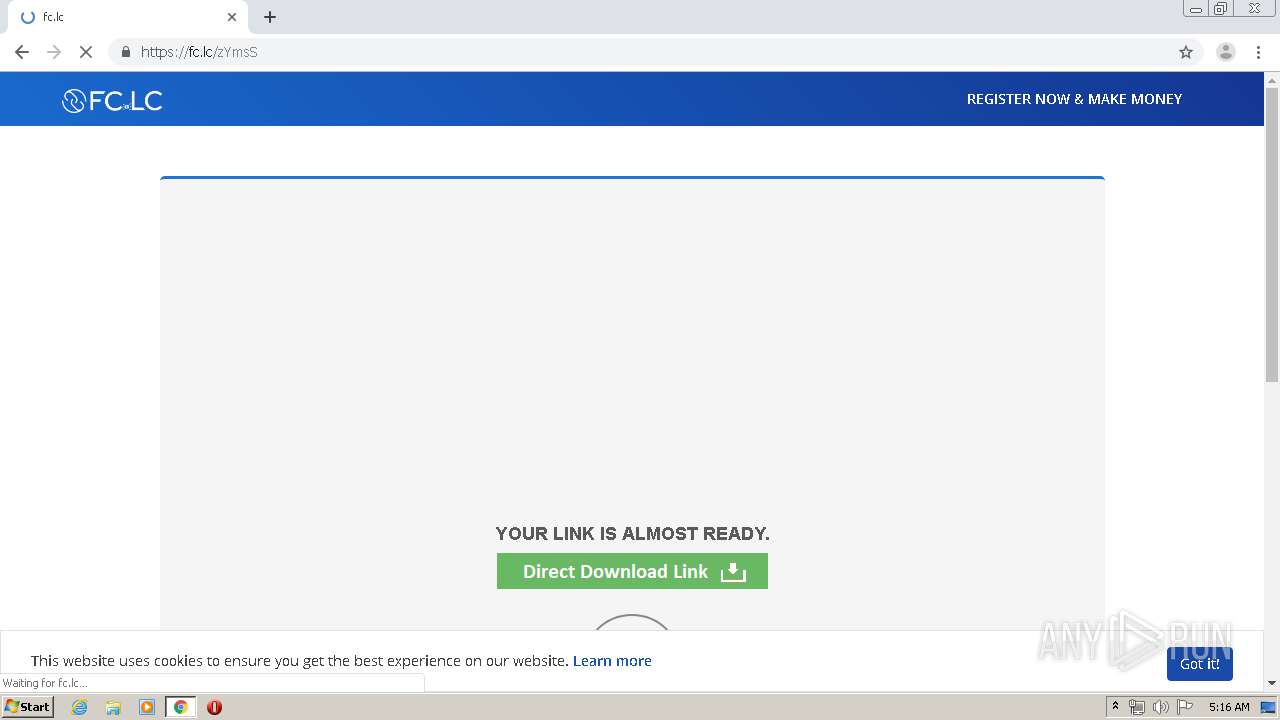
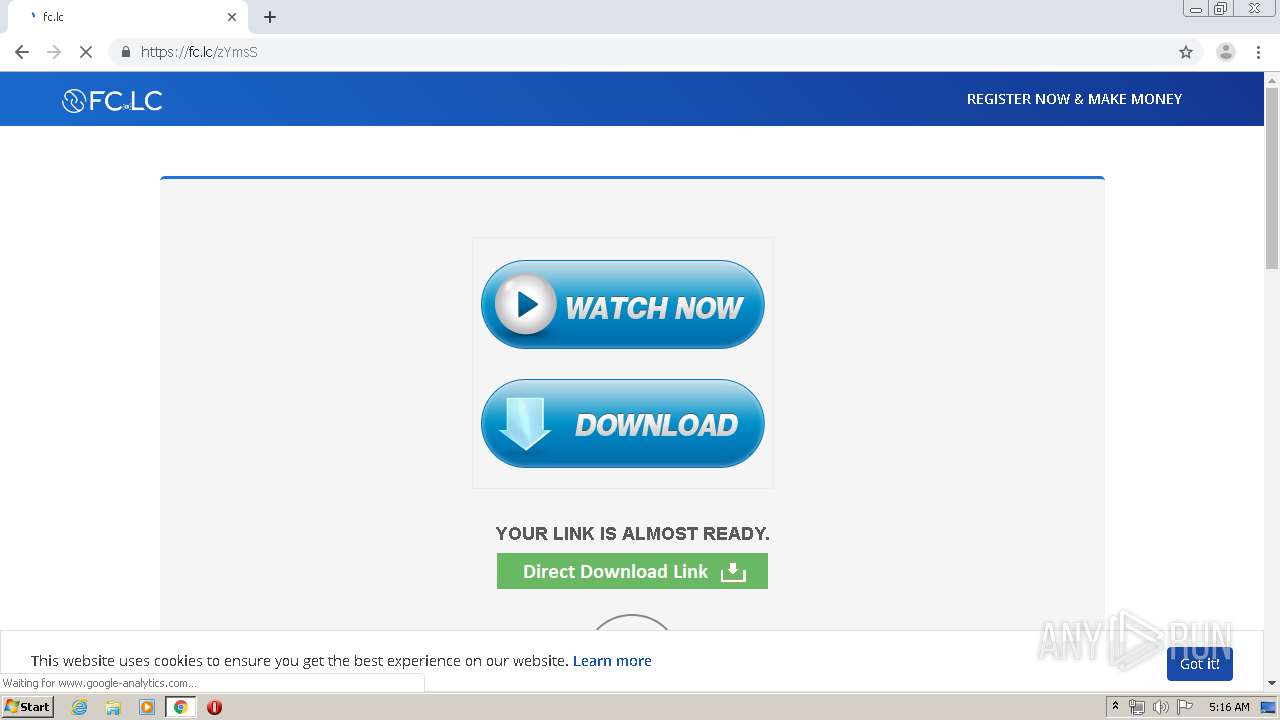
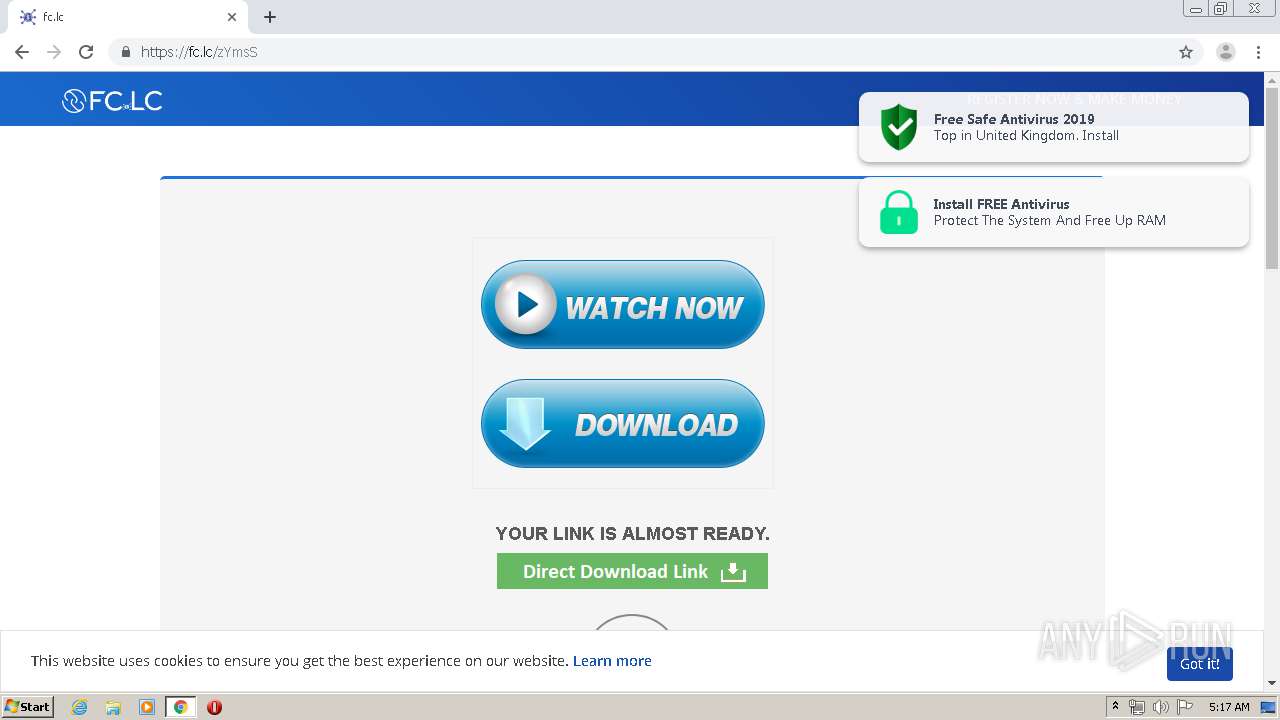
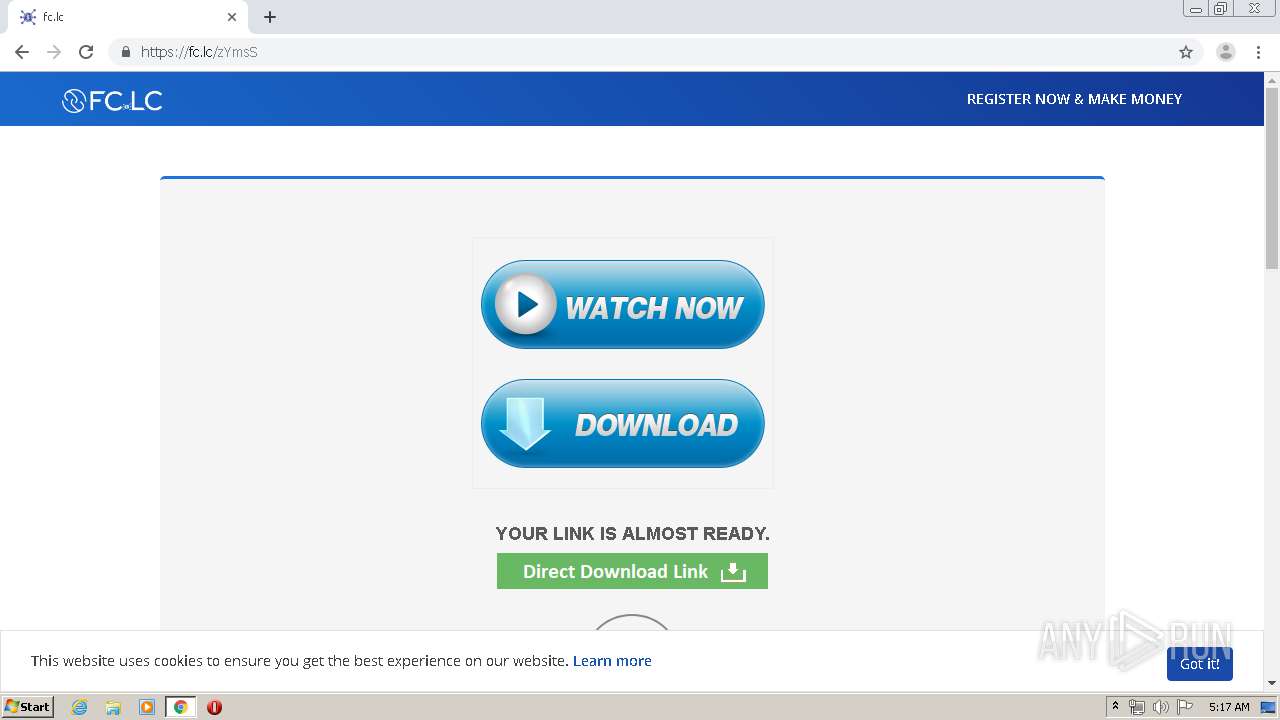
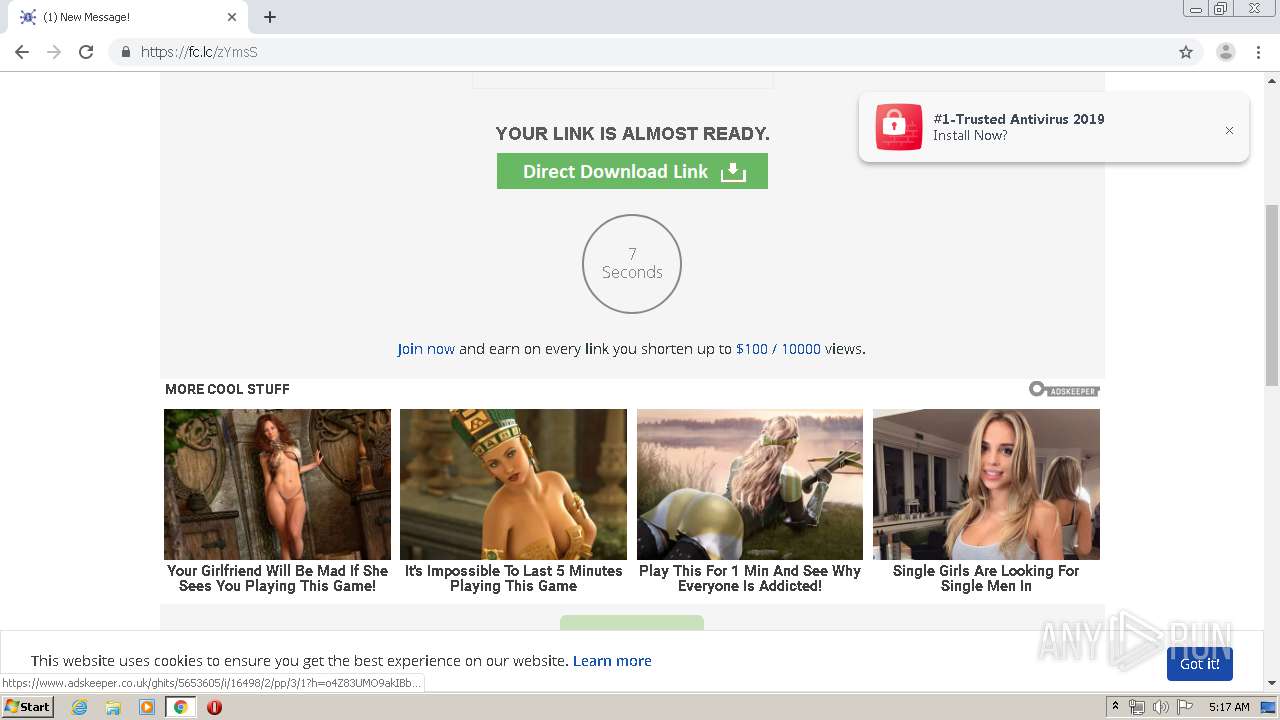
| URL: | https://ouo.io/yajFX9 |
| Full analysis: | https://app.any.run/tasks/572cb484-c033-4fd6-9d0b-51cb298c2666 |
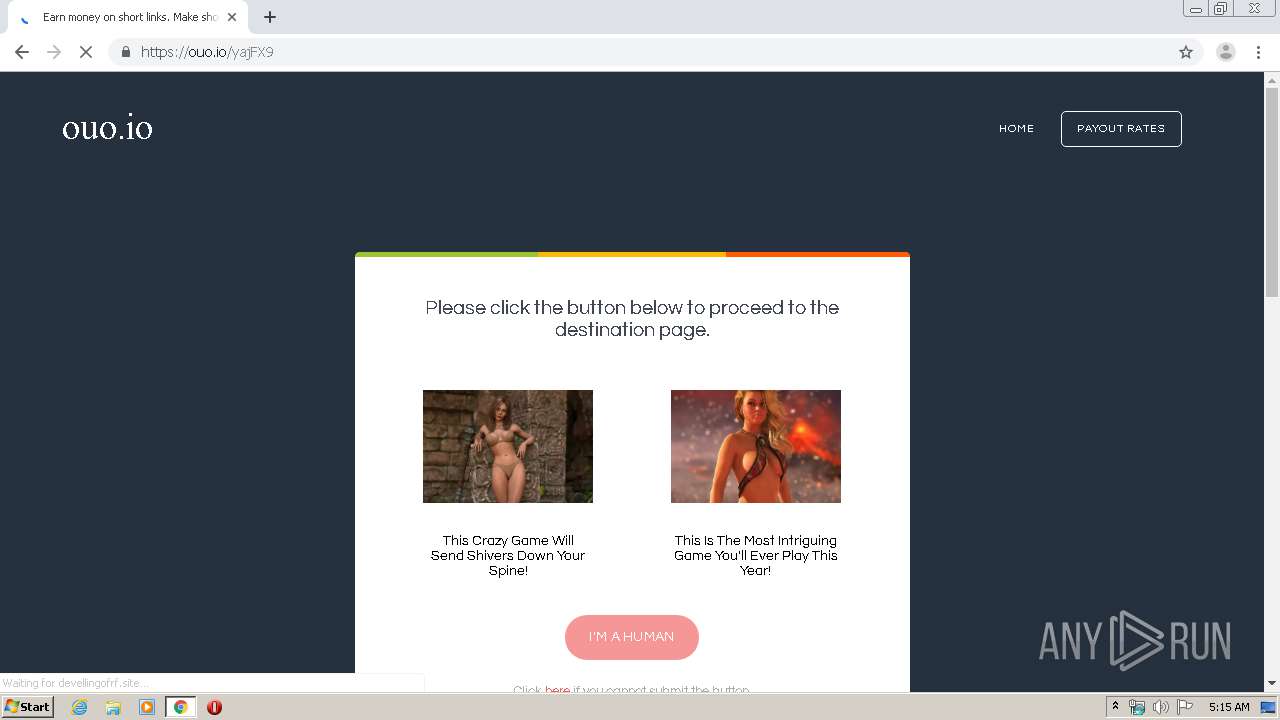
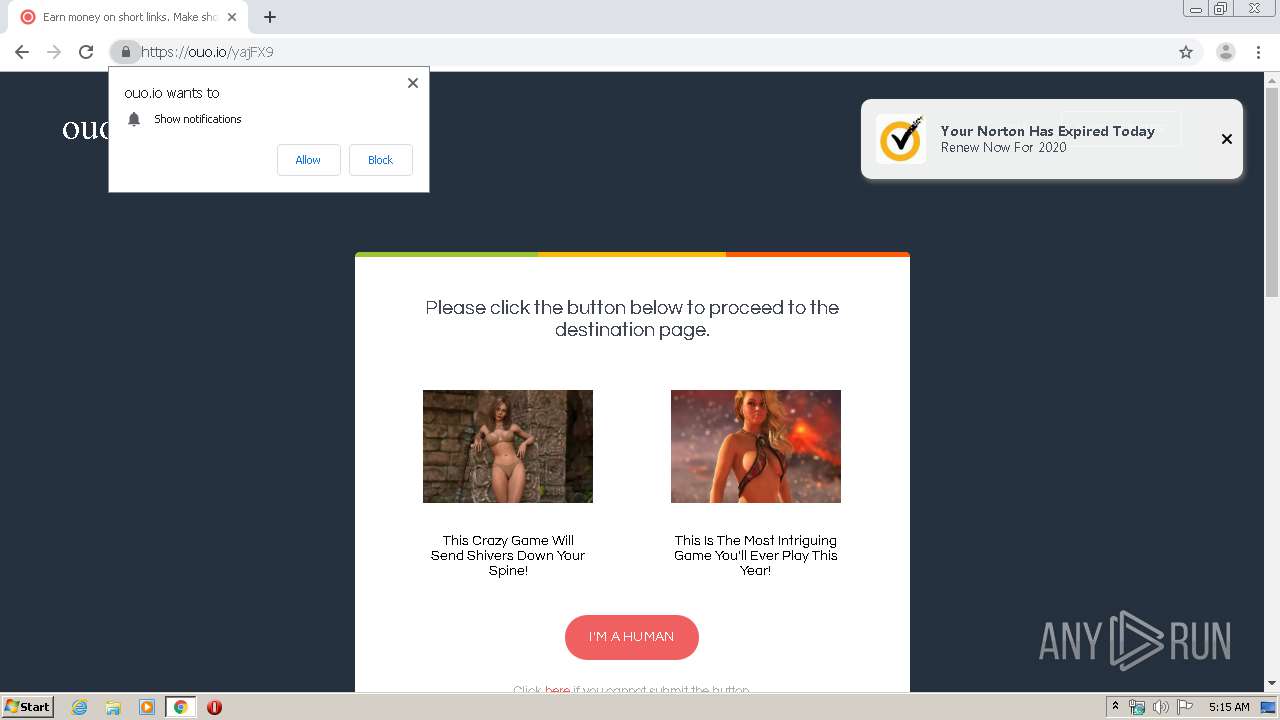
| Verdict: | Malicious activity |
| Analysis date: | April 26, 2020, 04:14:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 9E7DB571A4FC5F93FDD97BDD1B0A8864 |
| SHA1: | 9BD5D6B4A1937F2F32C6C4D92D8F30C96B8593C8 |
| SHA256: | F56AF9B8779347819494B2EE844EC3576182F4446A7C68518169970394828C76 |
| SSDEEP: | 3:N8ZKL+cEb+:20L+1i |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3392)
INFO
Reads the hosts file
- chrome.exe (PID: 3392)
- chrome.exe (PID: 3092)
Creates files in the user directory
- chrome.exe (PID: 3392)
Changes settings of System certificates
- chrome.exe (PID: 3092)
Application launched itself
- chrome.exe (PID: 3392)
Reads settings of System Certificates
- chrome.exe (PID: 3092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
124
Monitored processes
86
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16208564697393353396 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3896 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=660539497264927220 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2268 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8335347862678333682 --renderer-client-id=50 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5516 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15441969531860978089 --renderer-client-id=44 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1865245176441420295 --renderer-client-id=71 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3764 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3586861546484158161 --renderer-client-id=43 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5104 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13215236136862239973 --renderer-client-id=51 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5600 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7427693234686583885 --renderer-client-id=66 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4284 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9863355342254716449 --mojo-platform-channel-handle=4272 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16931427163225742219 --renderer-client-id=83 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1324 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
904
Read events
757
Write events
142
Delete events
5
Modification events
| (PID) Process: | (3524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3392-13232348088266375 |
Value: 259 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
268
Text files
379
Unknown types
35
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5EA50AB8-D40.pma | — | |
MD5:— | SHA256:— | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6eca5c8b-2e60-4de5-831f-4deca7fe9efd.tmp | — | |
MD5:— | SHA256:— | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa6e2f6.TMP | text | |
MD5:— | SHA256:— | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFa6e315.TMP | text | |
MD5:— | SHA256:— | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa6e2f6.TMP | text | |
MD5:— | SHA256:— | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa6e567.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
345
DNS requests
218
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
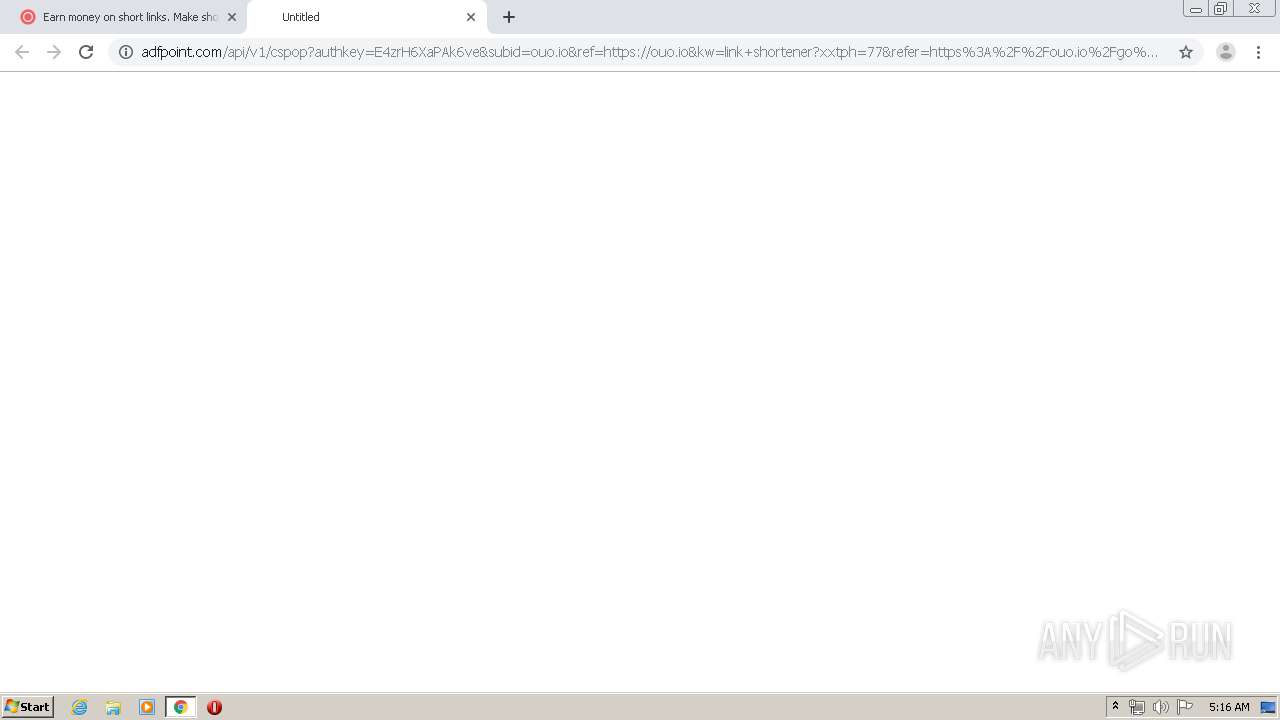
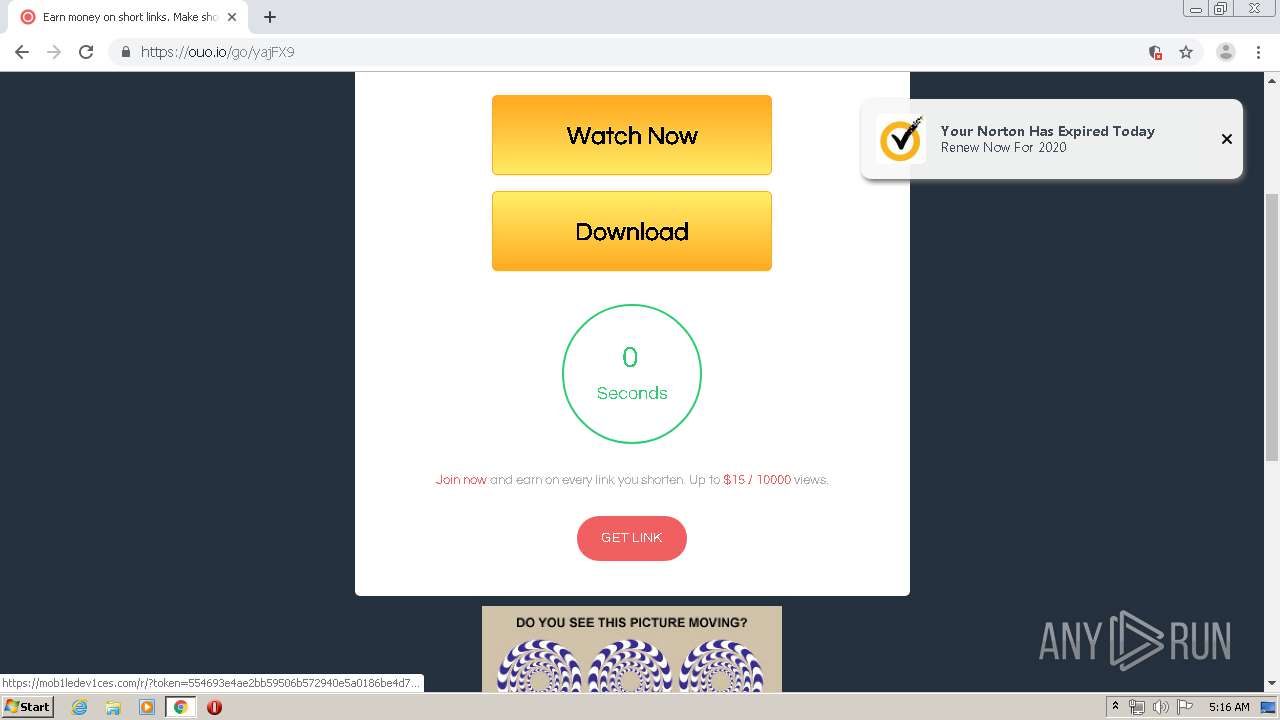
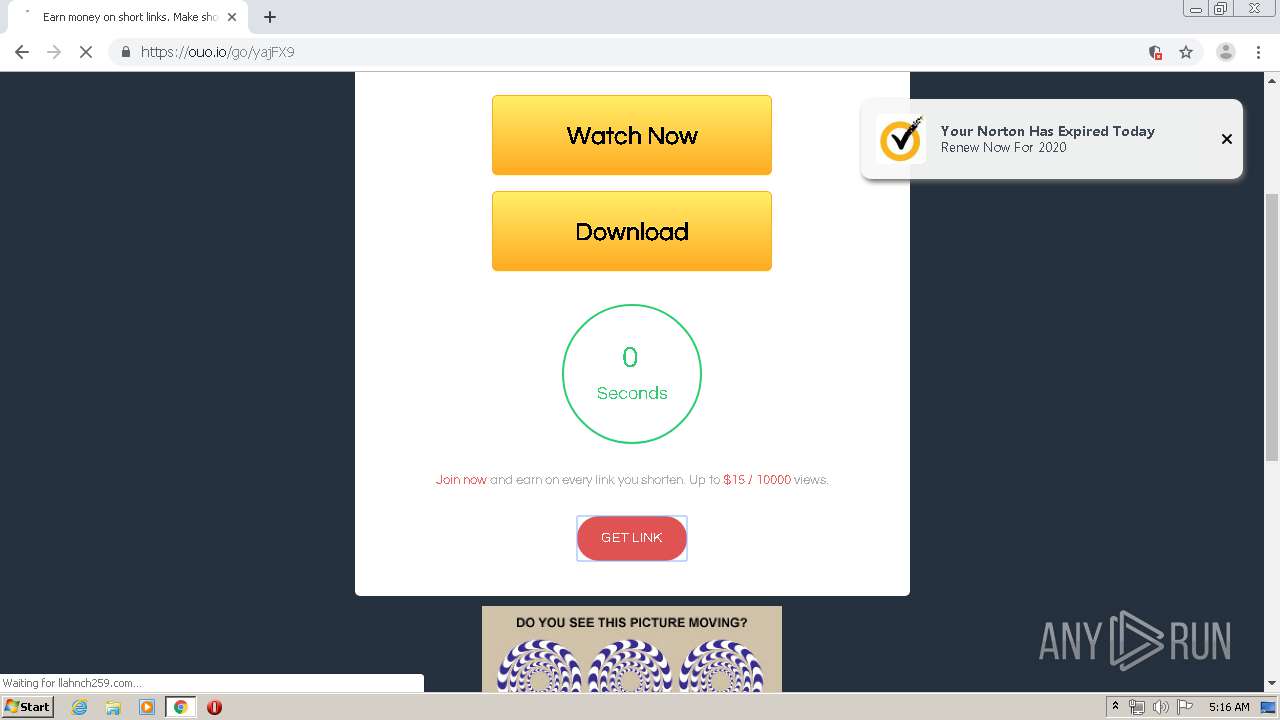
3092 | chrome.exe | GET | 204 | 45.55.104.44:80 | http://adfpoint.com/api/v1/cspop?authkey=E4zrH6XaPAk6ve&subid=ouo.io&ref=https://ouo.io&kw=link+shortener?xxtph=77&refer=https%3A%2F%2Fouo.io%2Fgo%2FyajFX9&kw=%5B%22earn%22%2C%22money%22%2C%22on%22%2C%22short%22%2C%22links%22%2C%22make%22%2C%22short%22%2C%22links%22%2C%22and%22%2C%22earn%22%2C%22the%22%2C%22biggest%22%2C%22money%22%2C%22-%22%2C%22ouo%22%2C%22io%22%5D&key=e5e8dd1c9c149a5e60b72911a0f16acf&scrWidth=1280&scrHeight=720&tz=1&ship=&pst=&v=19.11.v.7&res=7.31&dev=r&adb=n | US | — | — | unknown |
3092 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 520 b | whitelisted |
3092 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
3092 | chrome.exe | GET | 200 | 173.194.183.134:80 | http://r1---sn-aigl6ner.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Qx&mip=185.217.117.51&mm=28&mn=sn-aigl6ner&ms=nvh&mt=1587874393&mv=m&mvi=0&pl=24&shardbypass=yes | US | crx | 816 Kb | whitelisted |
3092 | chrome.exe | GET | 200 | 173.194.183.169:80 | http://r4---sn-aigl6ney.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=185.217.117.51&mm=28&mn=sn-aigl6ney&ms=nvh&mt=1587874451&mv=m&mvi=3&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
3092 | chrome.exe | GET | 302 | 185.75.254.28:80 | http://bongacams.com/track?c=386803&subid=12fe79af-99d4-f4ef-d8e4-0171b4b47a52.176305&subid2=176305 | NL | html | 138 b | suspicious |
3092 | chrome.exe | GET | 200 | 23.37.41.57:80 | http://cert.int-x3.letsencrypt.org/ | NL | der | 1.15 Kb | whitelisted |
3092 | chrome.exe | GET | 200 | 104.18.11.39:80 | http://cacerts.digicert.com/DigiCertSHA2HighAssuranceServerCA.crt | US | der | 1.18 Kb | whitelisted |
3092 | chrome.exe | GET | 200 | 104.18.10.39:80 | http://cacerts.rapidssl.com/RapidSSLRSACA2018.crt | US | der | 1.18 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
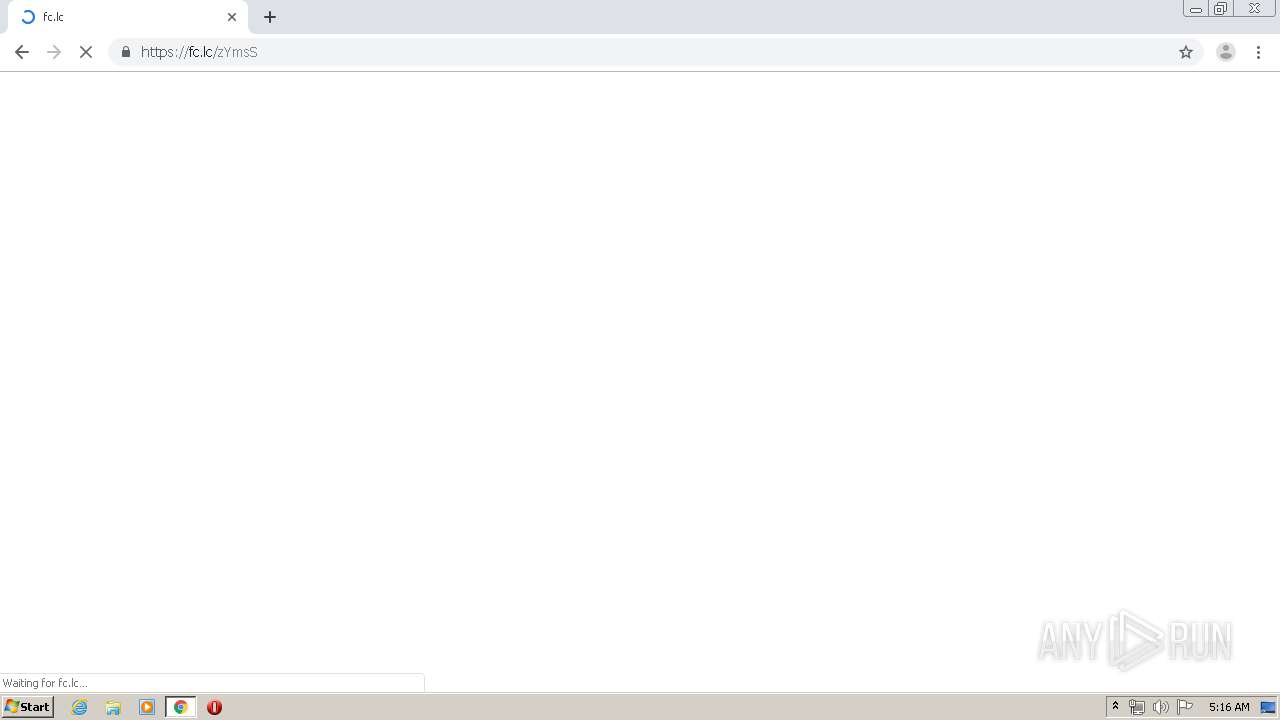
3092 | chrome.exe | 104.22.23.162:443 | ouo.io | Cloudflare Inc | US | unknown |
3092 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
3092 | chrome.exe | 172.217.22.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3092 | chrome.exe | 51.195.26.70:443 | fogayeown.com | — | GB | unknown |
3092 | chrome.exe | 216.58.212.132:443 | www.google.com | Google Inc. | US | whitelisted |
3092 | chrome.exe | 172.217.22.67:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3092 | chrome.exe | 104.16.107.195:443 | churchasisrev.site | Cloudflare Inc | US | suspicious |
3092 | chrome.exe | 104.16.107.147:443 | devellingofrf.site | Cloudflare Inc | US | suspicious |
3092 | chrome.exe | 104.24.96.44:443 | zap.buzz | Cloudflare Inc | US | shared |
3092 | chrome.exe | 104.31.64.251:443 | xml.revrtb.net | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ouo.io |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
fogayeown.com |
| unknown |
www.google.com |
| malicious |
dc5k8fg5ioc8s.cloudfront.net |
| shared |
widgets.outbrain.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
3092 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
3092 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
3092 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |