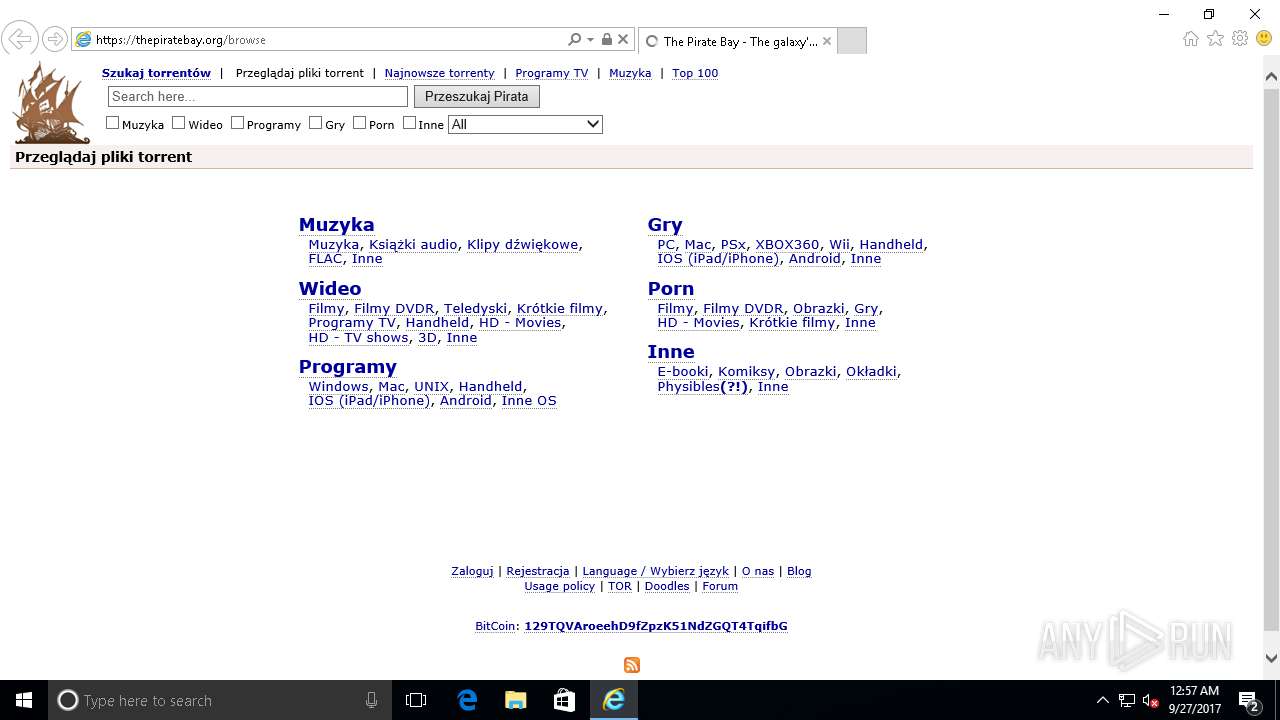
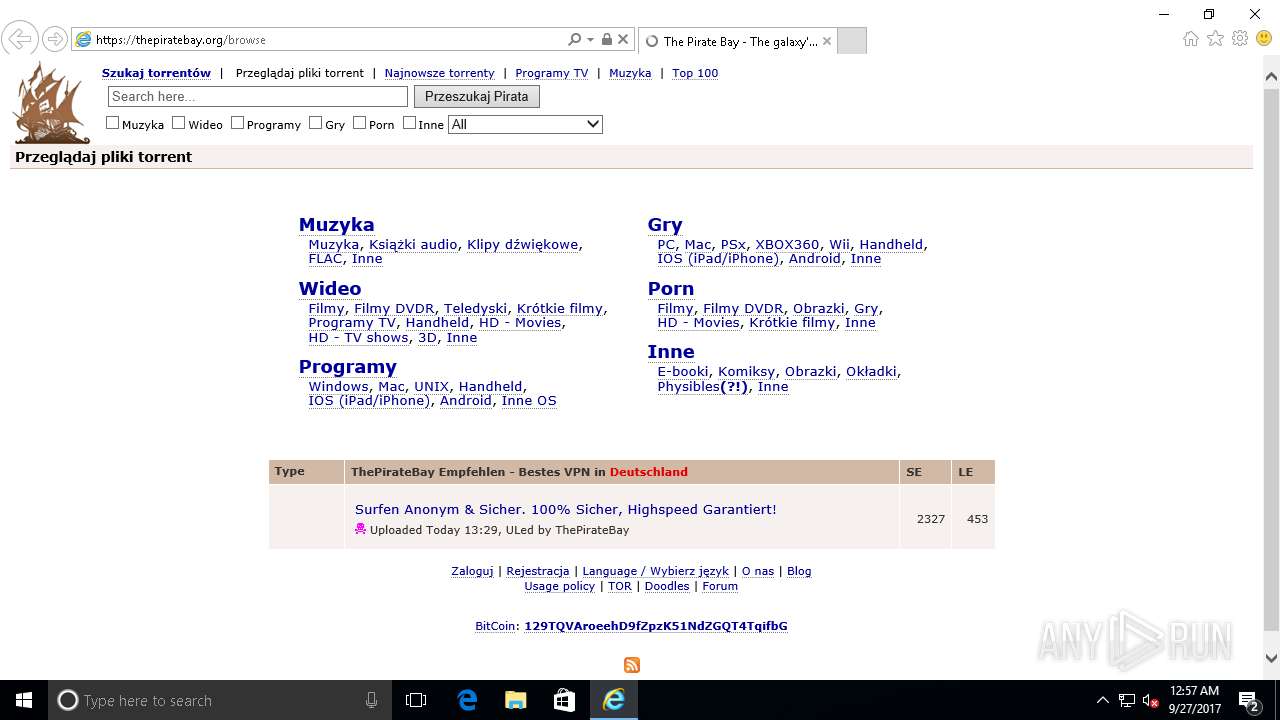
| URL: | https://thepiratebay.org/browse |
| Full analysis: | https://app.any.run/tasks/caa0f309-f9ef-49de-94d7-1a7c524d53ac |
| Verdict: | Suspicious |
| Analysis date: | September 27, 2017, 07:57:21 |
| OS: | Windows 10 Professional (build: 14393, 32 bit) |
| Indicators: | |
| MD5: | D248499E7B8F962AF638F2CDFA4F933B |
| SHA1: | 11BCD9705225FE0BD0F51220D4C7B2D5C6BBE83B |
| SHA256: | F54BFB4787E0FDC33133A7B934D19C5534378635657292ACB63C7810AE6E3D03 |
| SSDEEP: | 3:N8FAV0MZKSWA:27sWA |
MALICIOUS
Modifies internet zones
- iexplore.exe (PID: 5204)
SUSPICIOUS
Application launched itself
- iexplore.exe (PID: 5204)
Reads configuration files
- iexplore.exe (PID: 5204)
Reads internet explorer settings
- iexplore.exe (PID: 5584)
Starts Internet Explorer
- iexplore.exe (PID: 5204)
INFO
Dropped object can contents TOR URL's
- iexplore.exe (PID: 5584)
Dropped object can contents URL's
- iexplore.exe (PID: 5584)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
2
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5204 | "C:\Program Files\Internet Explorer\iexplore.exe" https://thepiratebay.org/browse | C:\Program Files\Internet Explorer\iexplore.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.14393.0 (rs1_release.160715-1616) Modules
| |||||||||||||||
| 5584 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:5204 CREDAT:75009 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.14393.0 (rs1_release.160715-1616) Modules
| |||||||||||||||
Total events
633
Read events
440
Write events
193
Delete events
0
Modification events
| (PID) Process: | (5204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (5204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (5204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000029000000090000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (5204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (5204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (5204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
8
Text files
42
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5584 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\6MX1CAPL\pirate6[1].css | text | |
MD5:— | SHA256:— | |||
| 5584 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\5Y4QH1JP\coinhive.min[1].js | text | |
MD5:— | SHA256:— | |||
| 5584 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\CY4KPKAI\ads[1].js | html | |
MD5:— | SHA256:— | |||
| 5584 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\GI2GK6SD\m[1].js | text | |
MD5:— | SHA256:— | |||
| 5584 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\5Y4QH1JP\tpb[1].js | text | |
MD5:— | SHA256:— | |||
| 5584 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\GI2GK6SD\browse[1].htm | html | |
MD5:— | SHA256:— | |||
| 5584 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCookies\Low\VARQ7E1X.cookie | text | |
MD5:— | SHA256:— | |||
| 5584 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\GI2GK6SD\cryptonight-asmjs.min.js[2].mem | binary | |
MD5:— | SHA256:— | |||
| 5584 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCookies\Low\XNXIBTZ2.cookie | text | |
MD5:— | SHA256:— | |||
| 5584 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\GI2GK6SD\cryptonight-asmjs.min.js[3].mem | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
31
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | — | 157.56.77.148:443 | https://sls.update.microsoft.com/SLS/%7B9482F4B4-E343-43B6-B170-9A65BC822C77%7D/x86/10.0.14393.0/0?CH=469&L=en-US&P=&PT=0x30&WUA=10.0.14393.1066 | US | — | — | whitelisted |
— | — | GET | — | 157.56.77.148:443 | https://sls.update.microsoft.com/SLS/%7B9482F4B4-E343-43B6-B170-9A65BC822C77%7D/x86/10.0.14393.0/0?CH=469&L=en-US&P=&PT=0x30&WUA=10.0.14393.1066 | US | — | — | whitelisted |
— | — | GET | 101 | 94.130.23.41:443 | https://ws027.coin-hive.com/proxy | UA | — | — | whitelisted |
— | — | POST | — | 134.170.58.118:443 | https://fe2.update.microsoft.com/v6/ClientWebService/client.asmx | US | — | — | whitelisted |
— | — | POST | — | 40.77.229.141:443 | https://tsfe.trafficshaping.dsp.mp.microsoft.com/TrafficShaping/ContentRegulation.asmx | US | — | — | whitelisted |
— | — | POST | — | 134.170.58.118:443 | https://fe2.update.microsoft.com/v6/ClientWebService/client.asmx | US | — | — | whitelisted |
— | — | POST | — | 40.77.229.141:443 | https://tsfe.trafficshaping.dsp.mp.microsoft.com/TrafficShaping/ContentRegulation.asmx | US | — | — | whitelisted |
— | — | POST | — | 40.77.229.141:443 | https://tsfe.trafficshaping.dsp.mp.microsoft.com/TrafficShaping/ContentRegulation.asmx | US | — | — | whitelisted |
— | — | POST | 200 | 65.55.163.78:443 | https://login.live.com/RST2.srf | US | xml | 9.77 Kb | whitelisted |
— | — | GET | 200 | 104.27.217.28:443 | https://thepiratebay.org/browse | US | html | 28.5 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.77.229.30:443 | DB5SCH103090608.wns.windows.com | — | US | whitelisted |
— | — | 40.77.229.141:443 | tsfe.trafficshaping.dsp.mp.microsoft.com | — | US | whitelisted |
— | — | 134.170.58.118:443 | — | — | US | whitelisted |
— | — | 157.56.77.148:443 | sls.update.microsoft.com | — | US | unknown |
— | — | 40.77.226.247:443 | client.wns.windows.com | — | IE | whitelisted |
— | — | 65.55.163.78:443 | login.live.com | — | US | whitelisted |
— | — | 40.77.226.250:443 | v10.vortex-win.data.microsoft.com | — | IE | whitelisted |
— | — | 104.27.217.28:443 | thepiratebay.org | — | US | shared |
— | — | 94.130.128.151:443 | coin-hive.com | — | UA | suspicious |
— | — | 104.31.9.156:443 | traffic.adxprts.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tsfe.trafficshaping.dsp.mp.microsoft.com |
| whitelisted |
DB5SCH103090608.wns.windows.com |
| unknown |
sls.update.microsoft.com |
| whitelisted |
thepiratebay.org |
| whitelisted |
login.live.com |
| whitelisted |
v10.vortex-win.data.microsoft.com |
| whitelisted |
traffic.adxprts.com |
| suspicious |
coin-hive.com |
| malicious |
ws027.coin-hive.com |
| unknown |
2468.go2cloud.org |
| malicious |