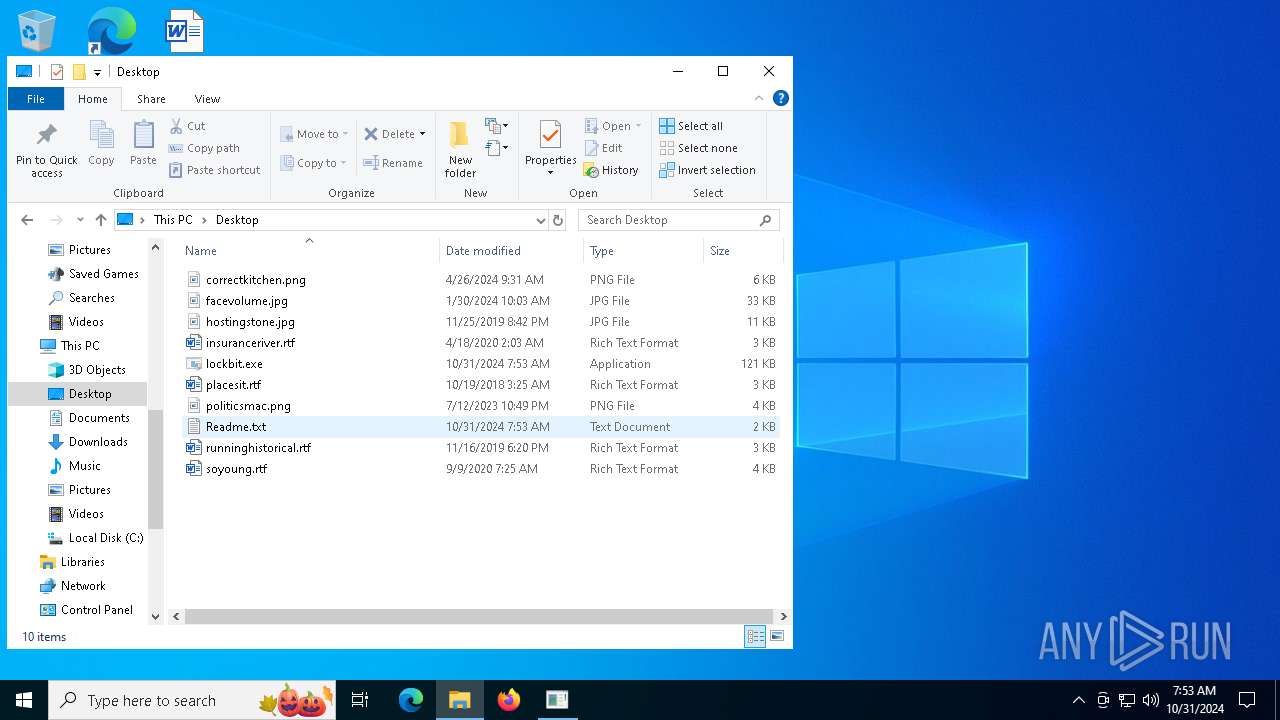
| File name: | lockbit.exe |
| Full analysis: | https://app.any.run/tasks/bca767dc-dd5d-4152-bb3c-fba9b2fa43f1 |
| Verdict: | Malicious activity |
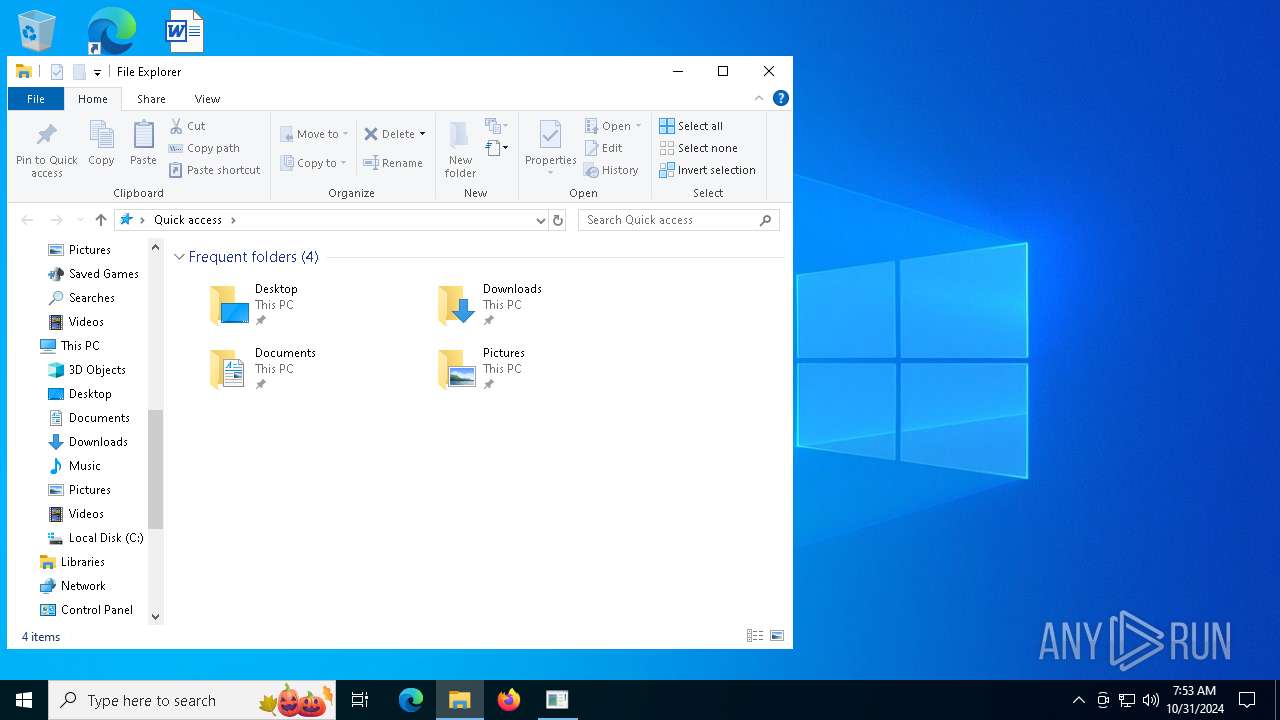
| Analysis date: | October 31, 2024, 07:53:03 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 164A227BB84D636200BE7F0505212C4D |
| SHA1: | 81C85B5A33CC33BEB3CBF9FF753ABBA7142310A5 |
| SHA256: | F53AC28E9B0EC8535333795AB9E0E52B17A77AD5EABC7B5172BD7E7AAC41DF12 |
| SSDEEP: | 384:R+2oio6RegFJy4UyLtyBor8E7xhL0vhLiz0ESDXSfOtw0vwkawqwq6vZJbSCFcGr:64f+4UwDwl+ZuXSisaM++AJVJp |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- lockbit.exe (PID: 540)
Possible usage of Discord/Telegram API has been detected (YARA)
- lockbit.exe (PID: 540)
INFO
Manual execution by a user
- notepad.exe (PID: 3972)
Attempting to use instant messaging service
- lockbit.exe (PID: 540)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
ims-api
(PID) Process(540) lockbit.exe
Telegram-Tokens (1)7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ
Telegram-Info-Links
7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ
Get info about bothttps://api.telegram.org/bot7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ/getMe
Get incoming updateshttps://api.telegram.org/bot7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ/getUpdates
Get webhookhttps://api.telegram.org/bot7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ/getWebhookInfo
Delete webhookhttps://api.telegram.org/bot7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ/deleteWebhook
Drop incoming updateshttps://api.telegram.org/bot7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ/deleteWebhook?drop_pending_updates=true
Telegram-Requests
Token7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ
End-PointsendMessage
Args
chat_id (1)7305863906
parse_mode (1)markdown
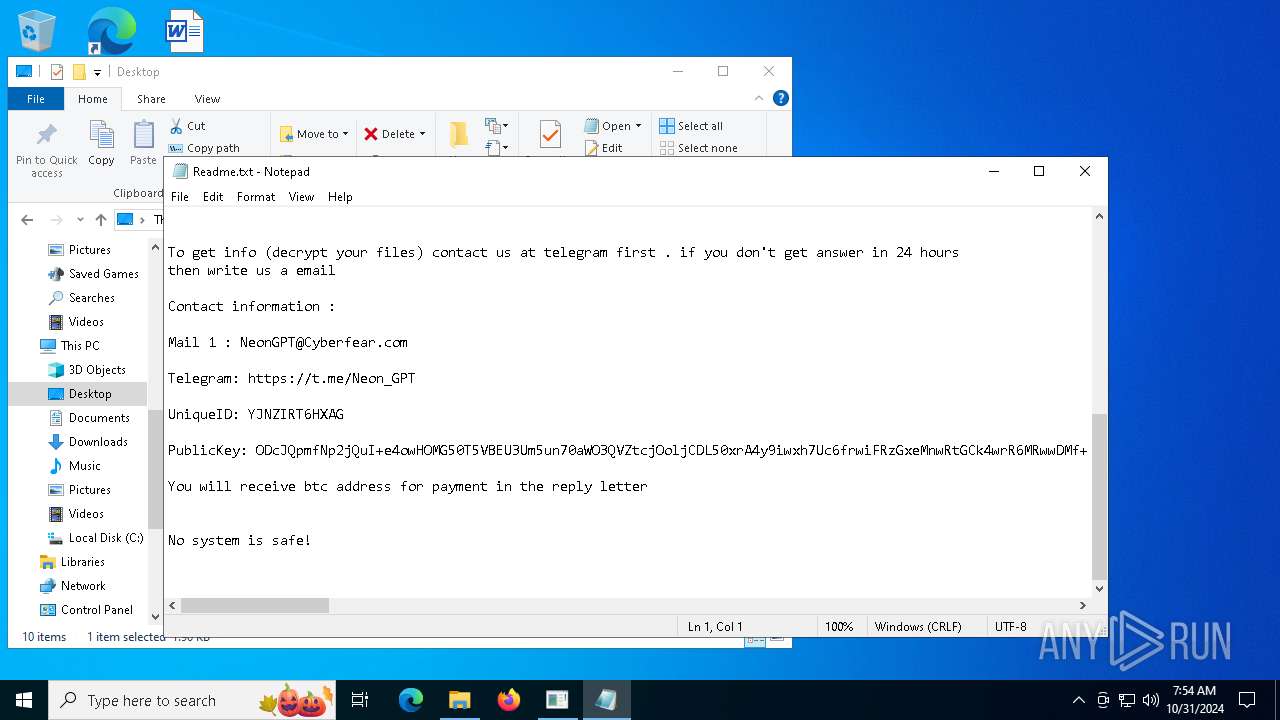
text (1)**Unique ID:**
```YJNZIRT6HXAG```
**--------------------**
**Personal ID:**
```ODcJQpmfNp2jQuI+e4ow
Token7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ
End-PointsendMessage
Args
chat_id (1)7305863906
parse_mode (1)markdown
Token7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ
End-PointsendMessage
Args
chat_id (1)7305863906
parse_mode (1)markdown
text (1)**Unique ID:**
```YJNZIRT6HXAG```
**--------------------**
**Personal ID:**
```ODcJQpmfNp2jQuI+e4owHOMG50T5VBEU3Um5un70aWO3QVZtcjOoljCDL50xrA4y9iwxh7Uc6frwiFRzGxeMnwRtGCk4wrR6MRwwDMf+6huwlq7DiUa25IVm220o9YaGDQwj8hoMIGdaEsuRMnQFBJjp05rnW9C3uhnAzvEjgkgHQFRxetDsBW8BLNK788NqM0MDejSmwZbr39E6PxJUFqo...
Telegram-Tokens (1)7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ
Telegram-Info-Links
7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ
Get info about bothttps://api.telegram.org/bot7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ/getMe
Get incoming updateshttps://api.telegram.org/bot7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ/getUpdates
Get webhookhttps://api.telegram.org/bot7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ/getWebhookInfo
Delete webhookhttps://api.telegram.org/bot7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ/deleteWebhook
Drop incoming updateshttps://api.telegram.org/bot7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ/deleteWebhook?drop_pending_updates=true
Telegram-Requests
Token7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ
End-PointsendMessage
Args
chat_id (1)7305863906
parse_mode (1)markdown
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:06:18 02:24:18+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 120832 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1f76e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 1.0.0.0 |
| InternalName: | NeonGPT.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | NeonGPT.exe |
| ProductName: | - |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
139
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
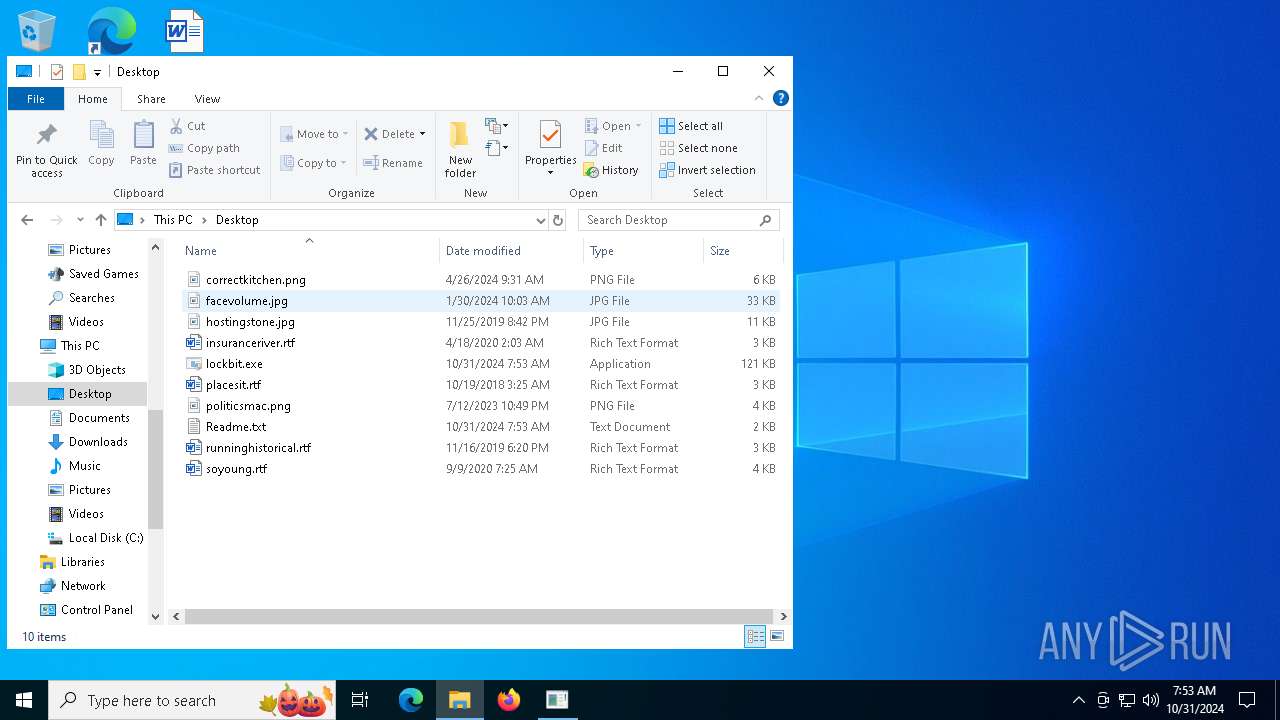
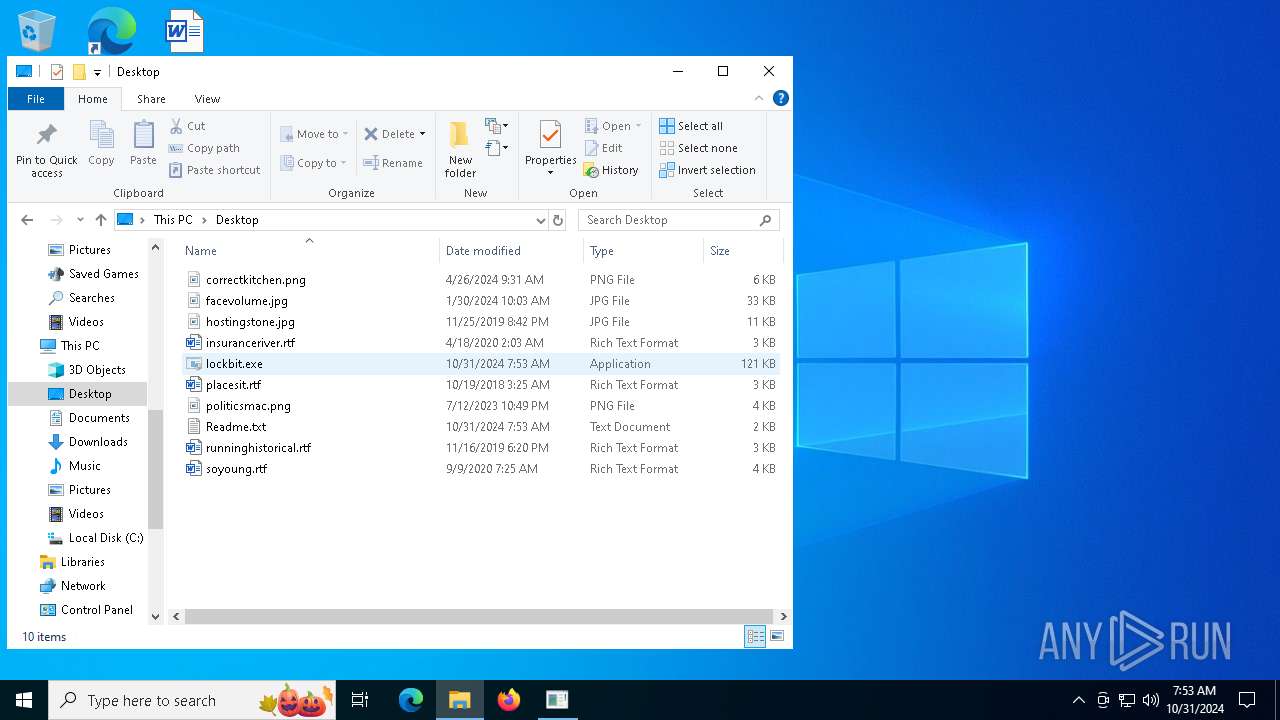
| 540 | "C:\Users\admin\Desktop\lockbit.exe" | C:\Users\admin\Desktop\lockbit.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Version: 1.0.0.0 Modules
ims-api(PID) Process(540) lockbit.exe Telegram-Tokens (1)7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ Telegram-Info-Links 7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ Get info about bothttps://api.telegram.org/bot7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ/getMe Get incoming updateshttps://api.telegram.org/bot7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ/getUpdates Get webhookhttps://api.telegram.org/bot7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ/getWebhookInfo Delete webhookhttps://api.telegram.org/bot7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ/deleteWebhook Drop incoming updateshttps://api.telegram.org/bot7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ/deleteWebhook?drop_pending_updates=true Telegram-Requests Token7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ End-PointsendMessage Args chat_id (1)7305863906 parse_mode (1)markdown text (1)**Unique ID:**
```YJNZIRT6HXAG```
**--------------------**
**Personal ID:**
```ODcJQpmfNp2jQuI+e4ow Token7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ End-PointsendMessage Args chat_id (1)7305863906 parse_mode (1)markdown Token7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ End-PointsendMessage Args chat_id (1)7305863906 parse_mode (1)markdown text (1)**Unique ID:**
```YJNZIRT6HXAG```
**--------------------**
**Personal ID:**
```ODcJQpmfNp2jQuI+e4owHOMG50T5VBEU3Um5un70aWO3QVZtcjOoljCDL50xrA4y9iwxh7Uc6frwiFRzGxeMnwRtGCk4wrR6MRwwDMf+6huwlq7DiUa25IVm220o9YaGDQwj8hoMIGdaEsuRMnQFBJjp05rnW9C3uhnAzvEjgkgHQFRxetDsBW8BLNK788NqM0MDejSmwZbr39E6PxJUFqo... (PID) Process(540) lockbit.exe Telegram-Tokens (1)7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ Telegram-Info-Links 7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ Get info about bothttps://api.telegram.org/bot7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ/getMe Get incoming updateshttps://api.telegram.org/bot7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ/getUpdates Get webhookhttps://api.telegram.org/bot7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ/getWebhookInfo Delete webhookhttps://api.telegram.org/bot7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ/deleteWebhook Drop incoming updateshttps://api.telegram.org/bot7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ/deleteWebhook?drop_pending_updates=true Telegram-Requests Token7396666136:AAF4CYFWOPRp3jtcgri8HNbxU7N3a1krEGQ End-PointsendMessage Args chat_id (1)7305863906 parse_mode (1)markdown | |||||||||||||||
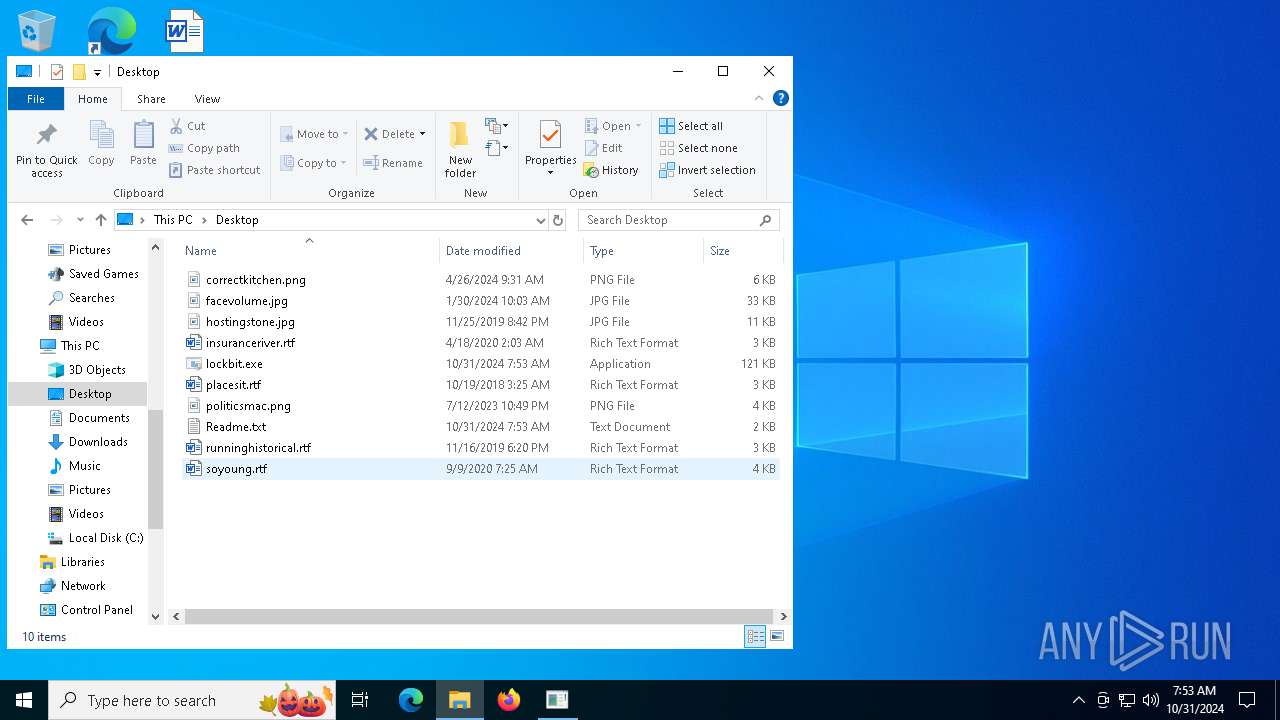
| 3972 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\Readme.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5828 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6164 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6192 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6764 | "C:\Users\admin\Desktop\lockbit.exe" | C:\Users\admin\Desktop\lockbit.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 6848 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | lockbit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7004 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 643
Read events
1 628
Write events
15
Delete events
0
Modification events
| (PID) Process: | (540) lockbit.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | NeonGPT |
Value: C:\Users\admin\Desktop\lockbit.exe | |||
| (PID) Process: | (540) lockbit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\lockbit_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (540) lockbit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\lockbit_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (540) lockbit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\lockbit_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (540) lockbit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\lockbit_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (540) lockbit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\lockbit_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (540) lockbit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\lockbit_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (540) lockbit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\lockbit_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (540) lockbit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\lockbit_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (540) lockbit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\lockbit_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
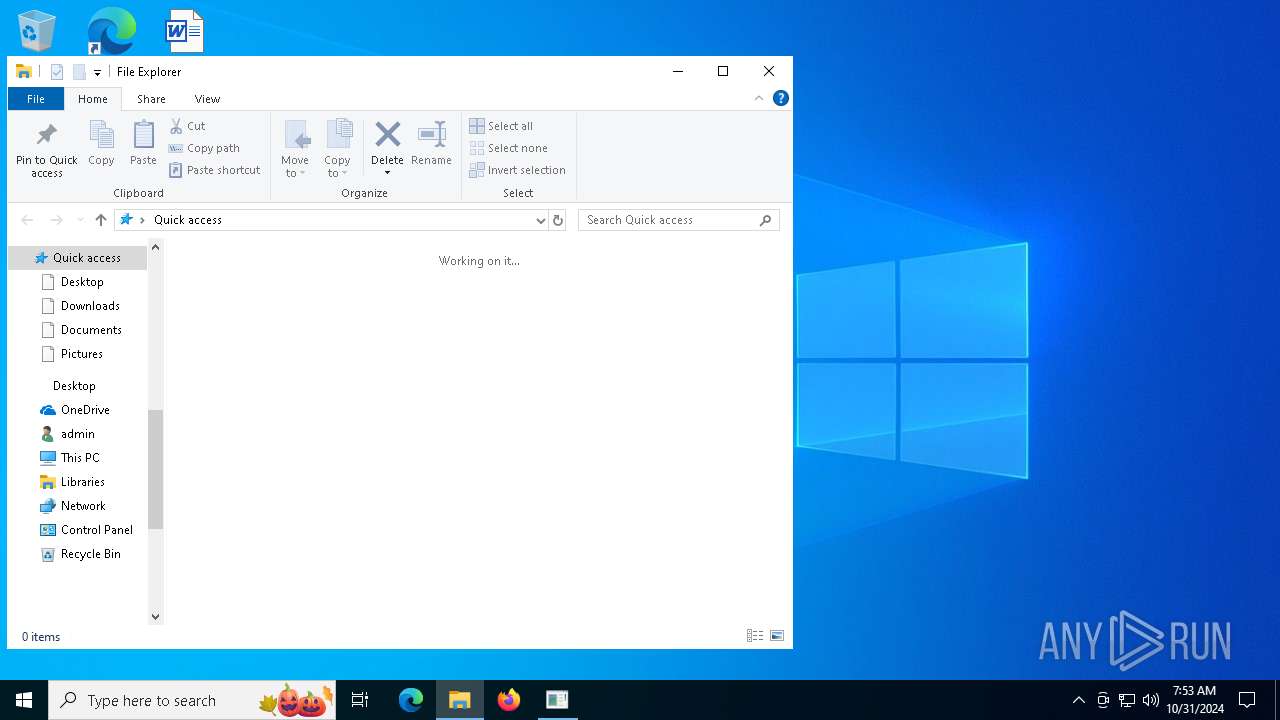
Executable files
0
Suspicious files
1 238
Text files
27
Unknown types
0
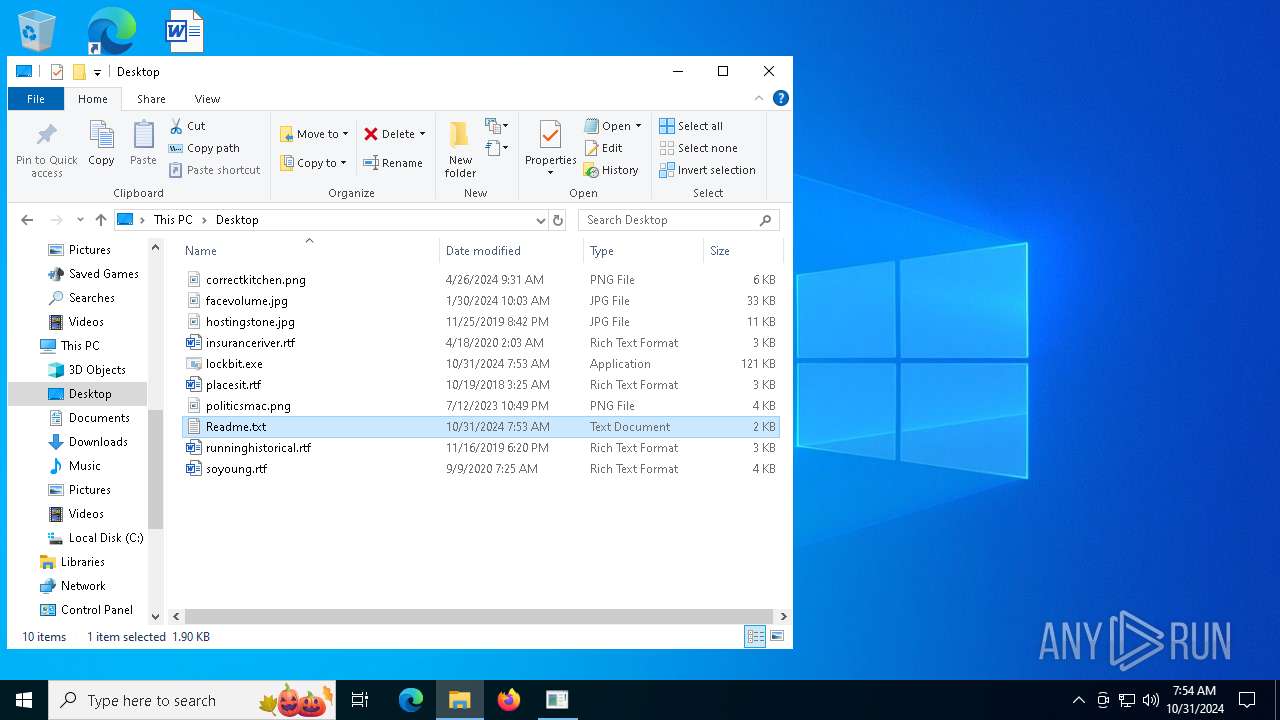
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
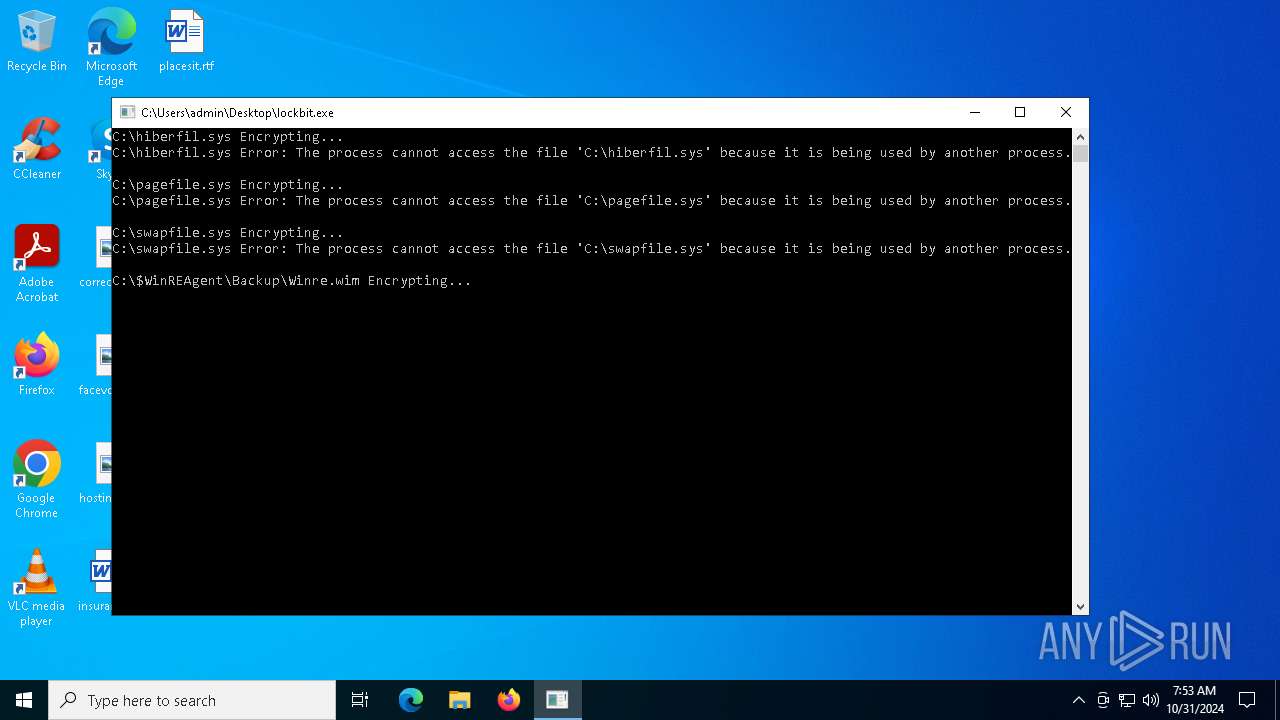
| 540 | lockbit.exe | C:\$WinREAgent\Backup\Winre.wim.NeonGPT@Cyberfear.com.YJNZIRT6HXAG.NeonGPT | — | |
MD5:— | SHA256:— | |||
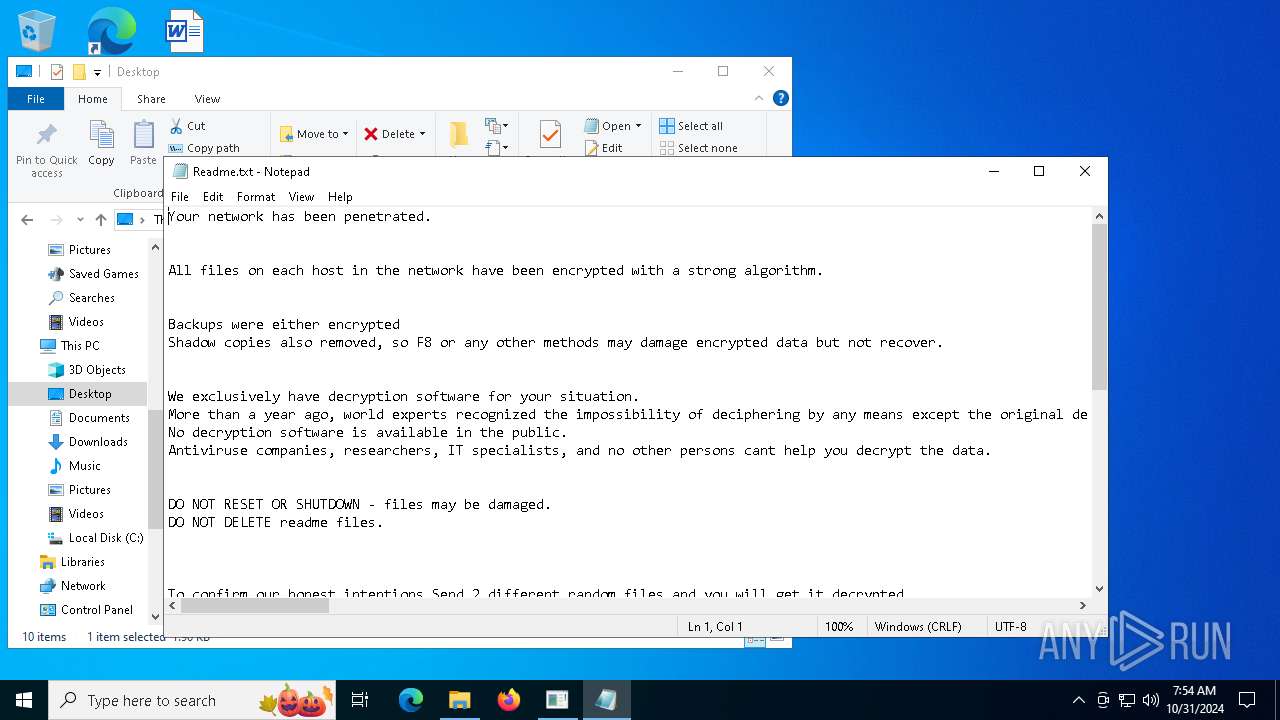
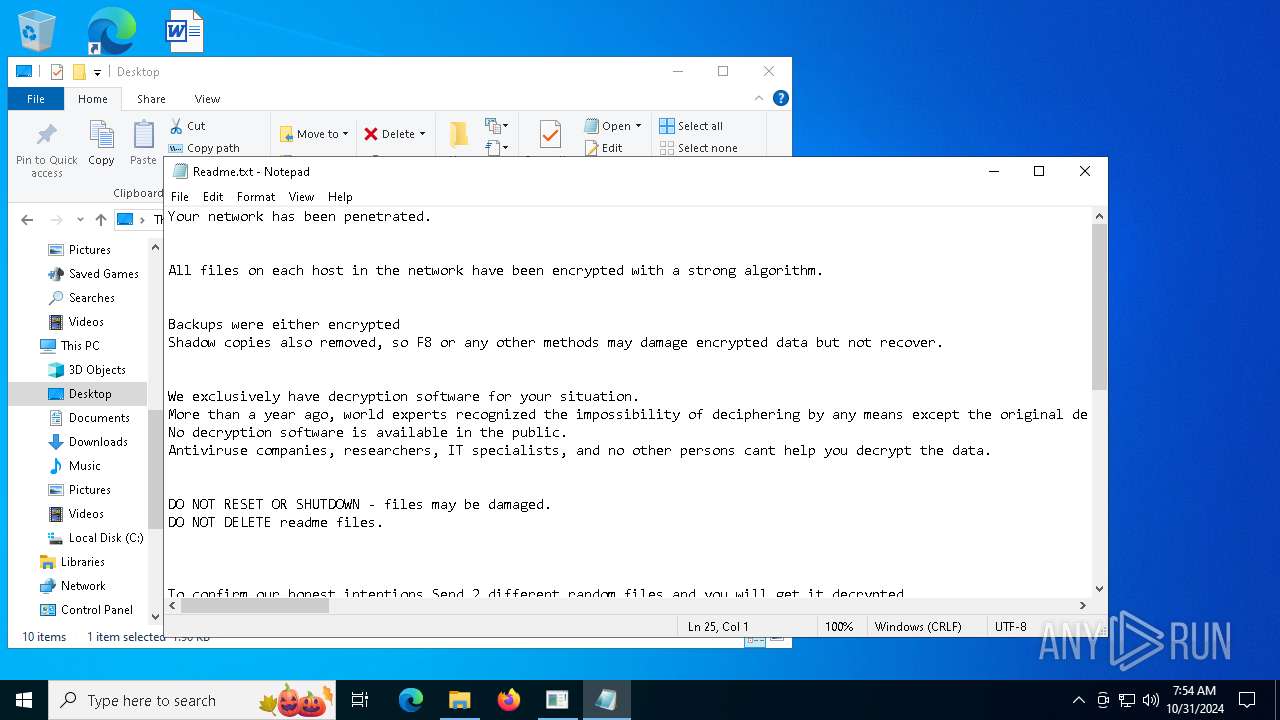
| 540 | lockbit.exe | C:\Readme.txt | text | |
MD5:873AFA5C74520D93E276FA8F01588597 | SHA256:1EFB6FCD0251721B0F890AB82629AE1399B105601875557A02076FA3BD92F600 | |||
| 540 | lockbit.exe | C:\BOOTNXT | binary | |
MD5:F4AA24B9CEE5B0ACF19F7C5B6FC6AB26 | SHA256:469C17342E3C3C43753DD222CF9989ACAB7BF2EF52B46B45067C3377FF212321 | |||
| 540 | lockbit.exe | C:\$WinREAgent\Rollback.xml | binary | |
MD5:81CC9568A2CB09F0C71C27C1B2721996 | SHA256:624C8DF90D1E5AB2E27E393BF9A68A6E2128C301A13C371C6ABEA7B9D58EEE6E | |||
| 540 | lockbit.exe | C:\bootTel.dat | binary | |
MD5:0C7F6E141D6A7008707887F9B23EEB72 | SHA256:BB7A8494AED3ED114BA6C692A58449F5B8F4C38A98FD6B011600391DC0E8BF2D | |||
| 540 | lockbit.exe | C:\Users\admin\Desktop\Readme.txt | text | |
MD5:873AFA5C74520D93E276FA8F01588597 | SHA256:1EFB6FCD0251721B0F890AB82629AE1399B105601875557A02076FA3BD92F600 | |||
| 540 | lockbit.exe | C:\bootTel.dat.NeonGPT@Cyberfear.com.YJNZIRT6HXAG.NeonGPT | binary | |
MD5:0C7F6E141D6A7008707887F9B23EEB72 | SHA256:BB7A8494AED3ED114BA6C692A58449F5B8F4C38A98FD6B011600391DC0E8BF2D | |||
| 540 | lockbit.exe | C:\BOOTNXT.NeonGPT@Cyberfear.com.YJNZIRT6HXAG.NeonGPT | binary | |
MD5:F4AA24B9CEE5B0ACF19F7C5B6FC6AB26 | SHA256:469C17342E3C3C43753DD222CF9989ACAB7BF2EF52B46B45067C3377FF212321 | |||
| 540 | lockbit.exe | C:\$RECYCLE.BIN\S-1-5-21-1693682860-607145093-2874071422-1001\desktop.ini.NeonGPT@Cyberfear.com.YJNZIRT6HXAG.NeonGPT | binary | |
MD5:719761CC514C1B84B39C4CA3A47D27E6 | SHA256:57B0081CA2454C79D33E1D2196F8707493287EDCE14F04CC0A4BEA06ADC372A1 | |||
| 540 | lockbit.exe | C:\$WinREAgent\Backup\ReAgent.xml | binary | |
MD5:533F5129EF54D121692D916E676E5AE3 | SHA256:624B29F1E775E8F5FBA3DE563B170AE3DE2FEC1B1296CFD9BE9EA31A1911A4E9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
47
DNS requests
22
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5488 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.9:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7136 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7136 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3728 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7060 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 2.16.164.9:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4020 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6944 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
540 | lockbit.exe | 149.154.167.220:443 | api.telegram.org | Telegram Messenger Inc | GB | shared |
— | — | 104.126.37.139:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
api.telegram.org |
| shared |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
540 | lockbit.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
540 | lockbit.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |