| File name: | Fortnite.exe |
| Full analysis: | https://app.any.run/tasks/e1897196-9c2f-4185-859a-e3cc774cbe06 |
| Verdict: | Malicious activity |
| Analysis date: | August 26, 2024, 01:29:15 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (console) x86-64, for MS Windows |
| MD5: | 2320D43B555E2EFECE383CD349663C8B |
| SHA1: | D3828101B9DC2F62FBB50B142CFE60093589E10A |
| SHA256: | F535D394B2B4B595945E8FA5B7699748E557B010B3AA6CCA91E710BA39F325F8 |
| SSDEEP: | 98304:eJTo9EHoZqkHGairLBFsg6BvIxD7U9pCOEpGPP7NWH9/caffffEIoGI6d0cPBxnC:9Zv |
MALICIOUS
Application was injected by another process
- RuntimeBroker.exe (PID: 4244)
Runs injected code in another process
- Fortnite.exe (PID: 6816)
SUSPICIOUS
Drops the executable file immediately after the start
- Fortnite.exe (PID: 6816)
Detected use of alternative data streams (AltDS)
- Fortnite.exe (PID: 6816)
Executable content was dropped or overwritten
- Fortnite.exe (PID: 6816)
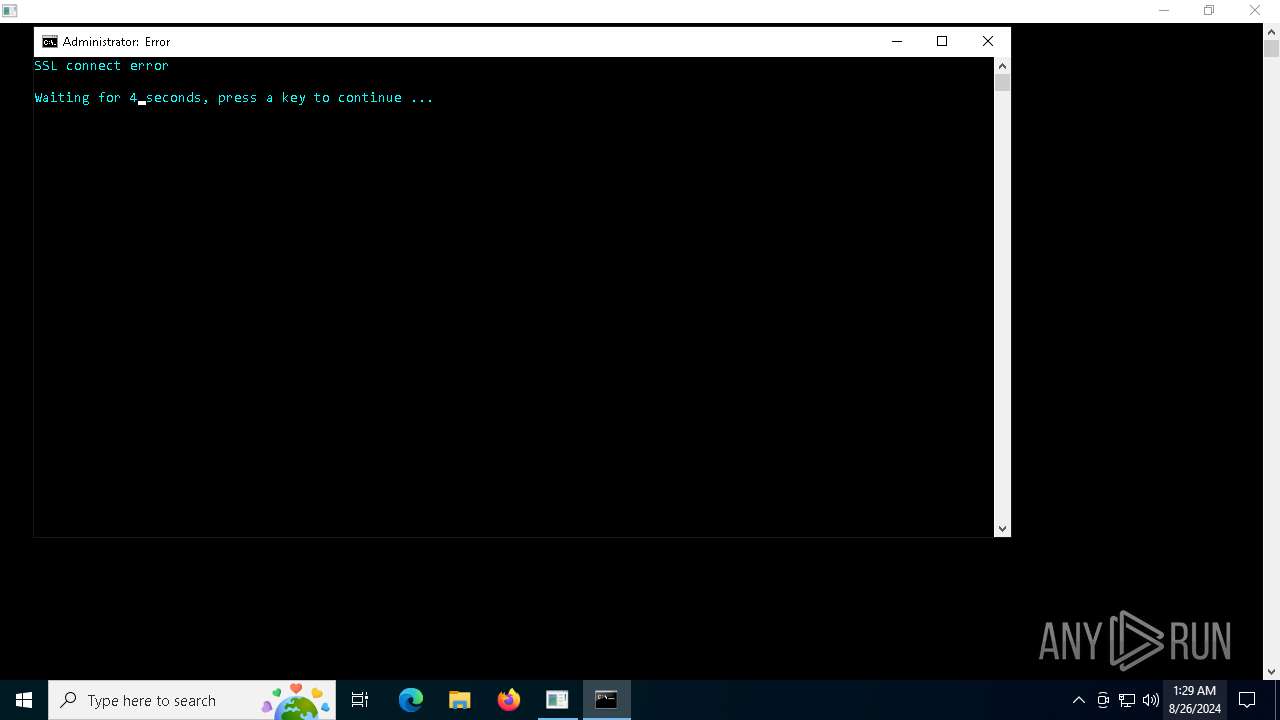
Starts CMD.EXE for commands execution
- Fortnite.exe (PID: 6816)
- cmd.exe (PID: 6272)
Reads security settings of Internet Explorer
- Fortnite.exe (PID: 6816)
Application launched itself
- cmd.exe (PID: 6272)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 6236)
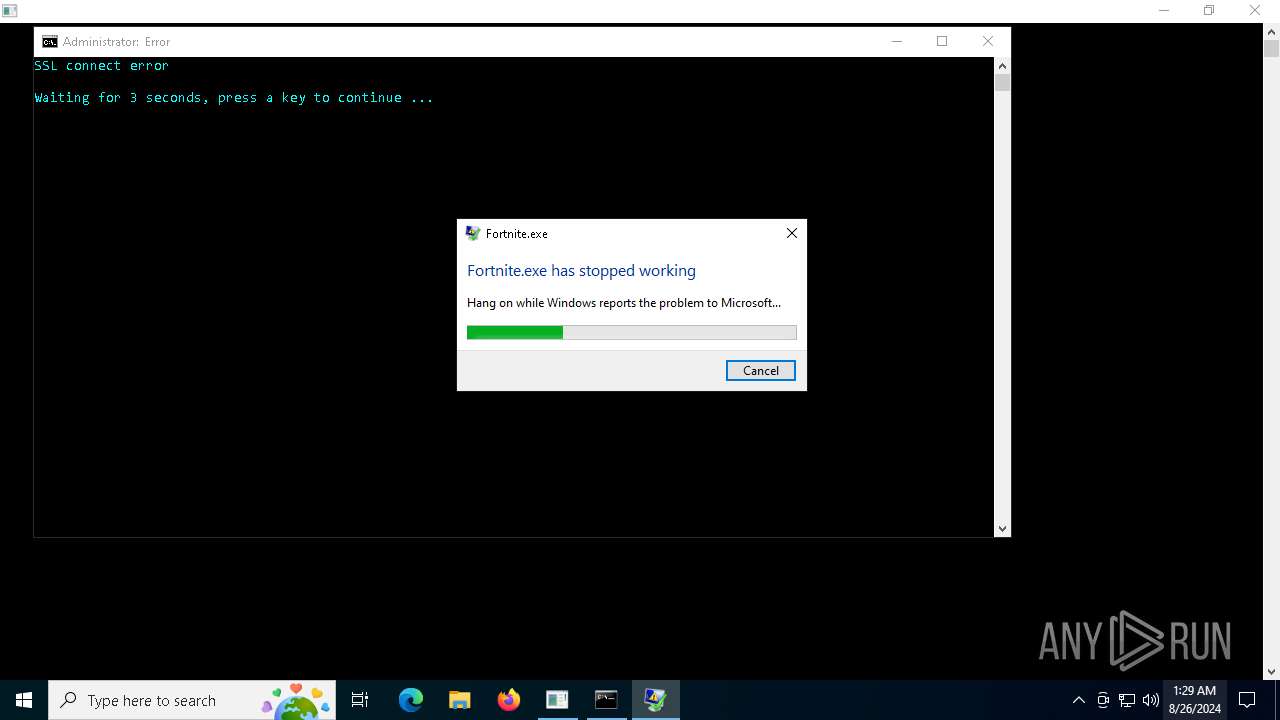
Executes application which crashes
- Fortnite.exe (PID: 6816)
INFO
Checks supported languages
- Fortnite.exe (PID: 6816)
Reads the computer name
- Fortnite.exe (PID: 6816)
Reads the machine GUID from the registry
- Fortnite.exe (PID: 6816)
Creates files or folders in the user directory
- Fortnite.exe (PID: 6816)
- WerFault.exe (PID: 6672)
Gets the hash of the file via CERTUTIL.EXE
- certutil.exe (PID: 6196)
Reads the software policy settings
- WerFault.exe (PID: 6672)
Checks proxy server information
- WerFault.exe (PID: 6672)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:08:25 16:28:06+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.4 |
| CodeSize: | 2281984 |
| InitializedDataSize: | 3066368 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x182b8c |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
136
Monitored processes
15
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4244 | C:\Windows\System32\RuntimeBroker.exe -Embedding | C:\Windows\System32\RuntimeBroker.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Runtime Broker Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6196 | certutil -hashfile "C:\Users\admin\Desktop\Fortnite.exe" MD5 | C:\Windows\System32\certutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: CertUtil.exe Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6236 | cmd /C "color b && title Error && echo SSL connect error && timeout /t 5" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6272 | C:\WINDOWS\system32\cmd.exe /c start cmd /C "color b && title Error && echo SSL connect error && timeout /t 5" | C:\Windows\System32\cmd.exe | — | Fortnite.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6300 | C:\WINDOWS\system32\cmd.exe /c certutil -hashfile "C:\Users\admin\Desktop\Fortnite.exe" MD5 | find /i /v "md5" | find /i /v "certutil" | C:\Windows\System32\cmd.exe | — | Fortnite.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6316 | find /i /v "md5" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6320 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6336 | find /i /v "certutil" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6460 | timeout /t 5 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
10 047
Read events
9 870
Write events
171
Delete events
6
Modification events
| (PID) Process: | (6816) Fortnite.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6816) Fortnite.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6816) Fortnite.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6816) Fortnite.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6816) Fortnite.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Speech_OneCore\Isolated\CLnGqfMahmU563Vr1loxV3uHjx5RqNVVZFaXJMMvESo\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech_OneCore\AudioInput |
| Operation: | write | Name: | DefaultDefaultTokenId |
Value: HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech_OneCore\AudioInput\TokenEnums\MMAudioIn\ | |||
| (PID) Process: | (6816) Fortnite.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Speech_OneCore\Isolated\CLnGqfMahmU563Vr1loxV3uHjx5RqNVVZFaXJMMvESo\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech_OneCore\AudioInput\TokenEnums\MMAudioIn |
| Operation: | write | Name: | CLSID |
Value: {14E74C62-DC97-43B0-8F2F-581496A65D60} | |||
| (PID) Process: | (6816) Fortnite.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Speech_OneCore\Isolated\CLnGqfMahmU563Vr1loxV3uHjx5RqNVVZFaXJMMvESo\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech_OneCore\AudioOutput |
| Operation: | write | Name: | DefaultDefaultTokenId |
Value: HKEY_LOCAL_MACHINE/SOFTWARE\Microsoft\Speech_OneCore\AudioOutput\TokenEnums\MMAudioOut\ | |||
| (PID) Process: | (6816) Fortnite.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Speech_OneCore\Isolated\CLnGqfMahmU563Vr1loxV3uHjx5RqNVVZFaXJMMvESo\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech_OneCore\AudioOutput\TokenEnums\MMAudioOut |
| Operation: | write | Name: | CLSID |
Value: {14E74C62-DC97-43B0-8F2F-581496A65D60} | |||
| (PID) Process: | (6816) Fortnite.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Speech_OneCore\Isolated\CLnGqfMahmU563Vr1loxV3uHjx5RqNVVZFaXJMMvESo\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech_OneCore\PhoneConverters\Tokens\Chinese |
| Operation: | write | Name: | CLSID |
Value: {C6FABB24-E332-46FB-BC91-FF331B2D51F0} | |||
| (PID) Process: | (6816) Fortnite.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Speech_OneCore\Isolated\CLnGqfMahmU563Vr1loxV3uHjx5RqNVVZFaXJMMvESo\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech_OneCore\PhoneConverters\Tokens\Chinese |
| Operation: | write | Name: | PhoneMap |
Value: - 0001 ! 0002 & 0003 , 0004 . 0005 ? 0006 _ 0007 + 0008 * 0009 1 000A 2 000B 3 000C 4 000D 5 000E a 000F ai 0010 an 0011 ang 0012 ao 0013 ba 0014 bai 0015 ban 0016 bang 0017 bao 0018 bei 0019 ben 001A beng 001B bi 001C bian 001D biao 001E bie 001F bin 0020 bing 0021 bo 0022 bu 0023 ca 0024 cai 0025 can 0026 cang 0027 cao 0028 ce 0029 cen 002A ceng 002B cha 002C chai 002D chan 002E chang 002F chao 0030 che 0031 chen 0032 cheng 0033 chi 0034 chong 0035 chou 0036 chu 0037 chuai 0038 chuan 0039 chuang 003A chui 003B chun 003C chuo 003D ci 003E cong 003F cou 0040 cu 0041 cuan 0042 cui 0043 cun 0044 cuo 0045 da 0046 dai 0047 dan 0048 dang 0049 dao 004A de 004B dei 004C den 004D deng 004E di 004F dia 0050 dian 0051 diao 0052 die 0053 ding 0054 diu 0055 dong 0056 dou 0057 du 0058 duan 0059 dui 005A dun 005B duo 005C e 005D ei 005E en 005F er 0060 fa 0061 fan 0062 fang 0063 fei 0064 fen 0065 feng 0066 fo 0067 fou 0068 fu 0069 ga 006A gai 006B gan 006C gang 006D gao 006E ge 006F gei 0070 gen 0071 geng 0072 gong 0073 gou 0074 gu 0075 gua 0076 guai 0077 guan 0078 guang 0079 gui 007A gun 007B guo 007C ha 007D hai 007E han 007F hang 0080 hao 0081 he 0082 hei 0083 hen 0084 heng 0085 hong 0086 hou 0087 hu 0088 hua 0089 huai 008A huan 008B huang 008C hui 008D hun 008E huo 008F ji 0090 jia 0091 jian 0092 jiang 0093 jiao 0094 jie 0095 jin 0096 jing 0097 jiong 0098 jiu 0099 ju 009A juan 009B jue 009C jun 009D ka 009E kai 009F kan 00A0 kang 00A1 kao 00A2 ke 00A3 kei 00A4 ken 00A5 keng 00A6 kong 00A7 kou 00A8 ku 00A9 kua 00AA kuai 00AB kuan 00AC kuang 00AD kui 00AE kun 00AF kuo 00B0 la 00B1 lai 00B2 lan 00B3 lang 00B4 lao 00B5 le 00B6 lei 00B7 leng 00B8 li 00B9 lia 00BA lian 00BB liang 00BC liao 00BD lie 00BE lin 00BF ling 00C0 liu 00C1 lo 00C2 long 00C3 lou 00C4 lu 00C5 luan 00C6 lue 00C7 lun 00C8 luo 00C9 lv 00CA ma 00CB mai 00CC man 00CD mang 00CE mao 00CF me 00D0 mei 00D1 men 00D2 meng 00D3 mi 00D4 mian 00D5 miao 00D6 mie 00D7 min 00D8 ming 00D9 miu 00DA mo 00DB mou 00DC mu 00DD na 00DE nai 00DF nan 00E0 nang 00E1 nao 00E2 ne 00E3 nei 00E4 nen 00E5 neng 00E6 ni 00E7 nian 00E8 niang 00E9 niao 00EA nie 00EB nin 00EC ning 00ED niu 00EE nong 00EF nou 00F0 nu 00F1 nuan 00F2 nue 00F3 nuo 00F4 nv 00F5 o 00F6 ou 00F7 pa 00F8 pai 00F9 pan 00FA pang 00FB pao 00FC pei 00FD pen 00FE peng 00FF pi 0100 pian 0101 piao 0102 pie 0103 pin 0104 ping 0105 po 0106 pou 0107 pu 0108 qi 0109 qia 010A qian 010B qiang 010C qiao 010D qie 010E qin 010F qing 0110 qiong 0111 qiu 0112 qu 0113 quan 0114 que 0115 qun 0116 ran 0117 rang 0118 rao 0119 re 011A ren 011B reng 011C ri 011D rong 011E rou 011F ru 0120 ruan 0121 rui 0122 run 0123 ruo 0124 sa 0125 sai 0126 san 0127 sang 0128 sao 0129 se 012A sen 012B seng 012C sha 012D shai 012E shan 012F shang 0130 shao 0131 she 0132 shei 0133 shen 0134 sheng 0135 shi 0136 shou 0137 shu 0138 shua 0139 shuai 013A shuan 013B shuang 013C shui 013D shun 013E shuo 013F si 0140 song 0141 sou 0142 su 0143 suan 0144 sui 0145 sun 0146 suo 0147 ta 0148 tai 0149 tan 014A tang 014B tao 014C te 014D tei 014E teng 014F ti 0150 tian 0151 tiao 0152 tie 0153 ting 0154 tong 0155 tou 0156 tu 0157 tuan 0158 tui 0159 tun 015A tuo 015B wa 015C wai 015D wan 015E wang 015F wei 0160 wen 0161 weng 0162 wo 0163 wu 0164 xi 0165 xia 0166 xian 0167 xiang 0168 xiao 0169 xie 016A xin 016B xing 016C xiong 016D xiu 016E xu 016F xuan 0170 xue 0171 xun 0172 ya 0173 yan 0174 yang 0175 yao 0176 ye 0177 yi 0178 yin 0179 ying 017A yo 017B yong 017C you 017D yu 017E yuan 017F yue 0180 yun 0181 za 0182 zai 0183 zan 0184 zang 0185 zao 0186 ze 0187 zei 0188 zen 0189 zeng 018A zha 018B zhai 018C zhan 018D zhang 018E zhao 018F zhe 0190 zhei 0191 zhen 0192 zheng 0193 zhi 0194 zhong 0195 zhou 0196 zhu 0197 zhua 0198 zhuai 0199 zhuan 019A zhuang 019B zhui 019C zhun 019D zhuo 019E zi 019F zong 01A0 zou 01A1 zu 01A2 zuan 01A3 zui 01A4 zun 01A5 zuo 01A6 | |||
Executable files
1
Suspicious files
3
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6672 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_Fortnite.exe_2ae485521f25f82ead50fe8bea7f5826c7a3436_00fdfb50_d0c99254-44df-4ccb-955e-60065f1da82f\Report.wer | — | |
MD5:— | SHA256:— | |||
| 6672 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\Fortnite.exe.6816.dmp | — | |
MD5:— | SHA256:— | |||
| 6816 | Fortnite.exe | C:\Windows\System32\Protection.dll | executable | |
MD5:7EB5561A8064CBF36A927711C083BF43 | SHA256:76C6EAD83695040A6CA6DED2AAE892F81AC8C94CD519C3A3737B3487DD737954 | |||
| 6672 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER901.tmp.dmp | binary | |
MD5:E0E9D0B3F2D3452D05132D8CA218061C | SHA256:6A761239729443B5AF470FED70B0898816FB7433C4129A4153D8A9A68CBC27FC | |||
| 6816 | Fortnite.exe | C:\Users\admin\AppData\Roaming\Microsoft\Speech\Files\UserLexicons\SP_E3E0B80FE7524E7AB9251BFDF4840FC4.dat | binary | |
MD5:2D7A2F6C8CCEDD062AA811F69EE2CEDA | SHA256:D33C55B5D6FCE600102549FB343A0E047F96E853FCD30B48362C793D97F5A89A | |||
| 6672 | WerFault.exe | C:\Windows\appcompat\Programs\Amcache.hve | binary | |
MD5:651BFF5F68D529E0FBE426365785FCC2 | SHA256:A6A438B2DE9716DC51B25C3708B428E89B578254F7A96DC66EAE6704963449A6 | |||
| 6672 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERAA9.tmp.xml | xml | |
MD5:1DECF334FC75C6B1BD04F3146068857F | SHA256:07A70AB40BB738CA746FDA8956F4680BB2BD5BB410176BE451024E02FAF0FB2C | |||
| 6672 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERA88.tmp.WERInternalMetadata.xml | xml | |
MD5:91A0342F7BA24106DCBE4FC153CB5F22 | SHA256:2E6C9469EADF977FED553A4EC47F0378195CD1916309AE1C4E77353DED01CBA7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
16
DNS requests
4
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2456 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4324 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6816 | Fortnite.exe | 104.26.1.5:443 | keyauth.win | CLOUDFLARENET | US | unknown |
6672 | WerFault.exe | 104.208.16.94:443 | watson.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
keyauth.win |
| malicious |
watson.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Potentially Bad Traffic | ET INFO Fake Game Cheat Related Domain in DNS Lookup (keyauth .win) |
6816 | Fortnite.exe | Potentially Bad Traffic | ET INFO Fake Game Cheat Related Domain (keyauth .win) in TLS SNI |
Process | Message |
|---|---|
Fortnite.exe | TLS callback: process attach |
Fortnite.exe | All seems fine for TLSCallbackProcess. |
Fortnite.exe | TLS callback: thread attach |
Fortnite.exe | TLS callback: thread attach |
Fortnite.exe | TLS callback: thread attach |
Fortnite.exe | TLS callback: thread attach |
Fortnite.exe | TLS callback: thread attach |
Fortnite.exe | TLS callback: thread attach |
Fortnite.exe | TLS callback: thread attach |
Fortnite.exe | TLS callback: thread attach |